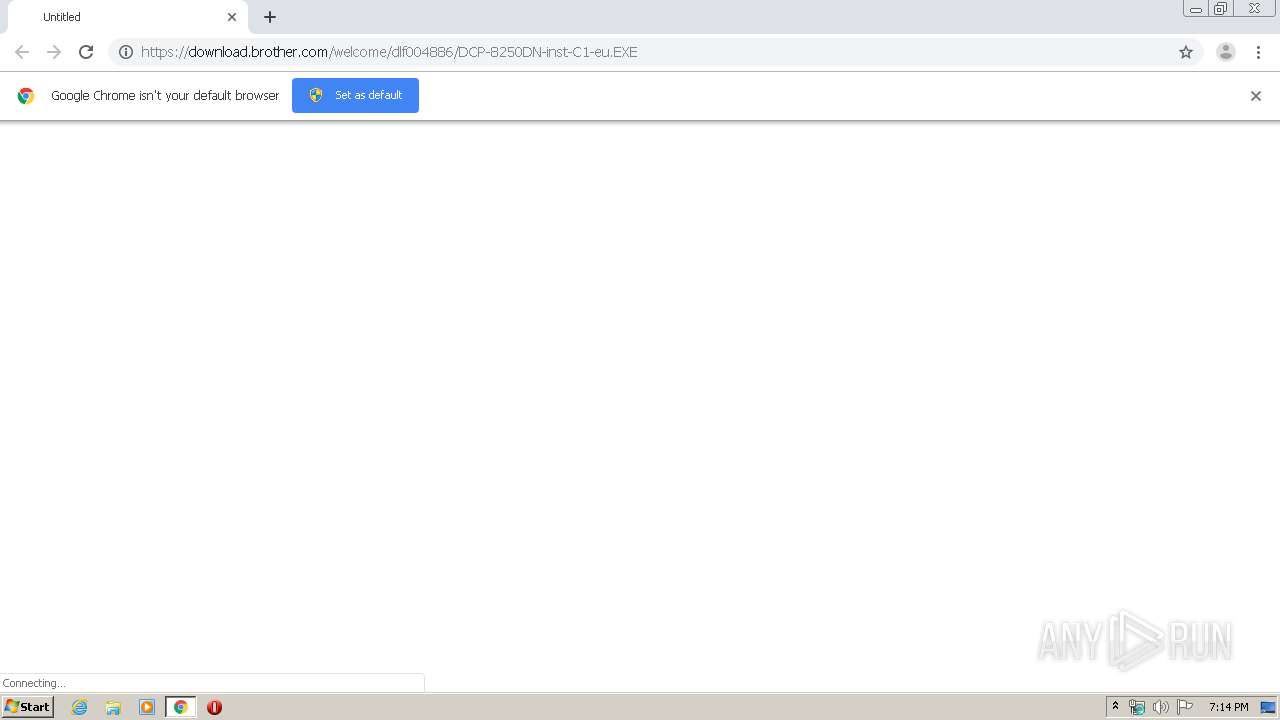
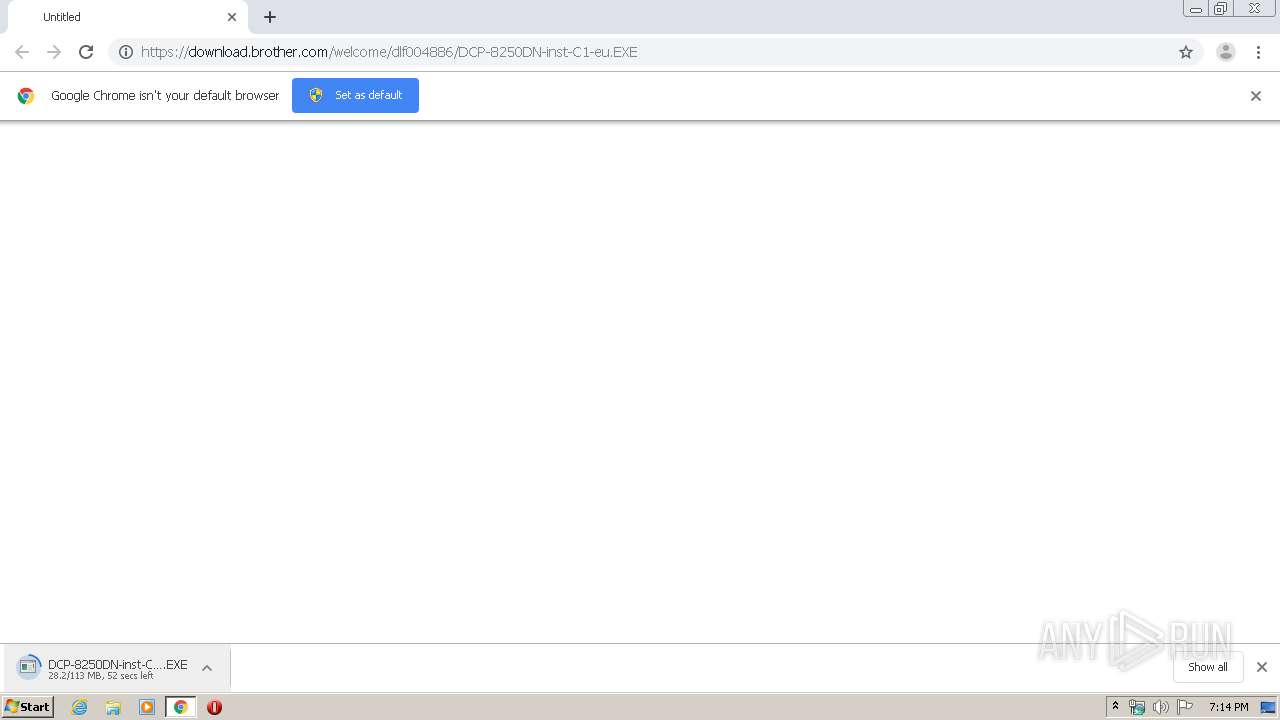
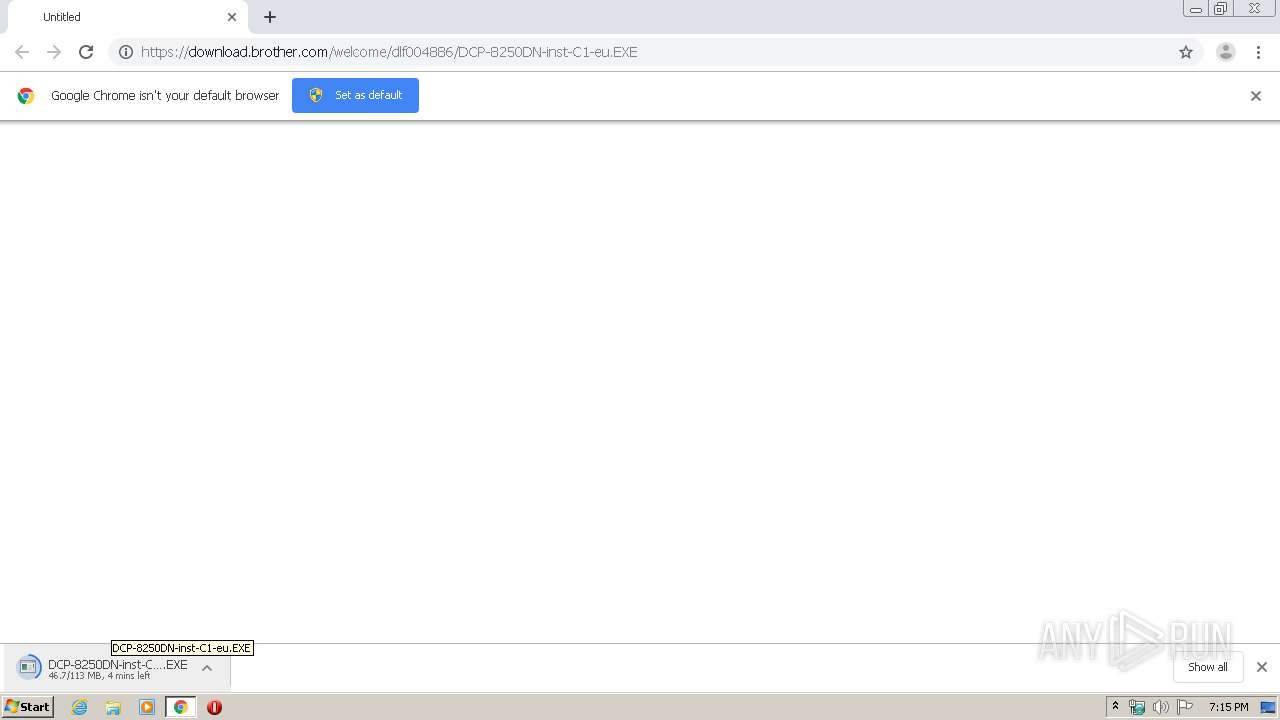
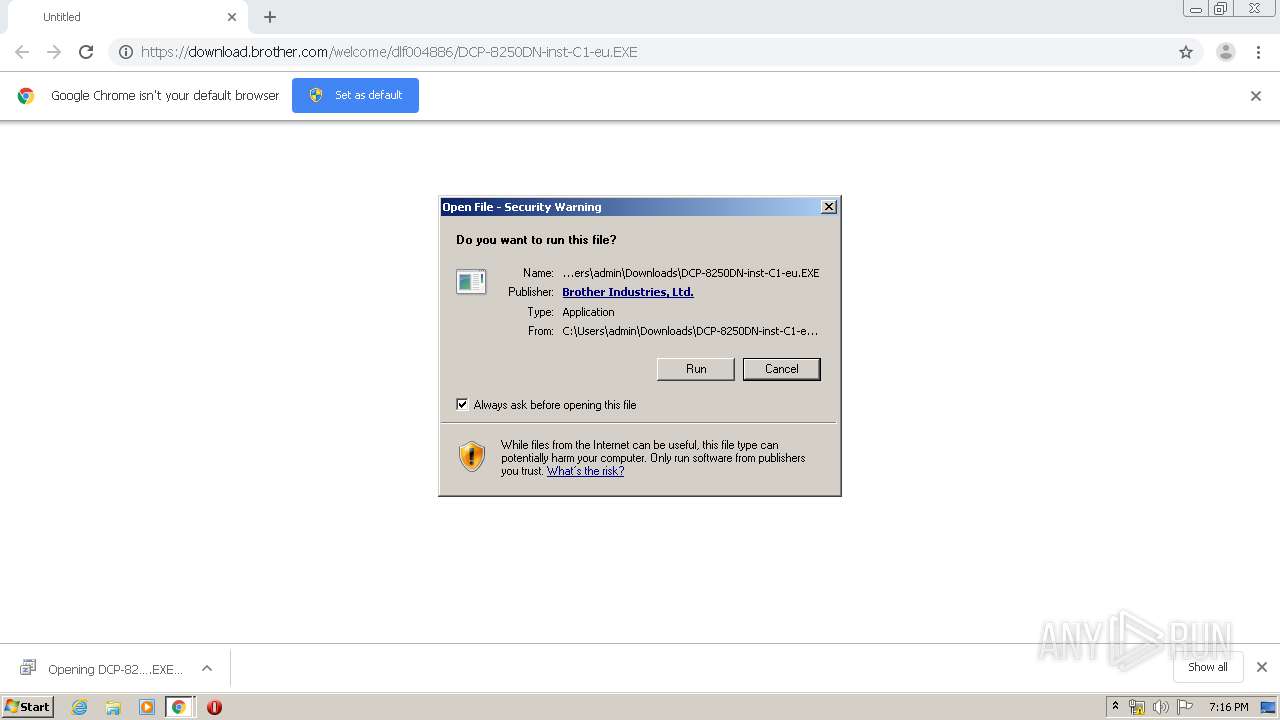
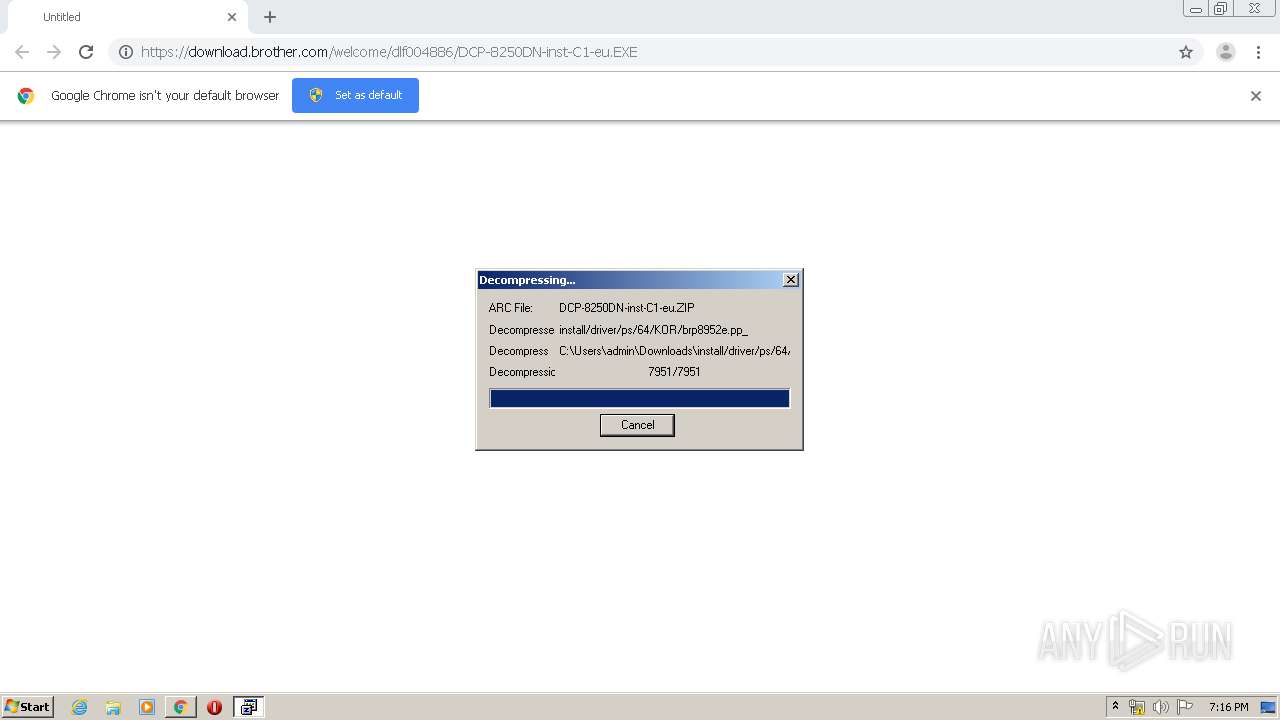
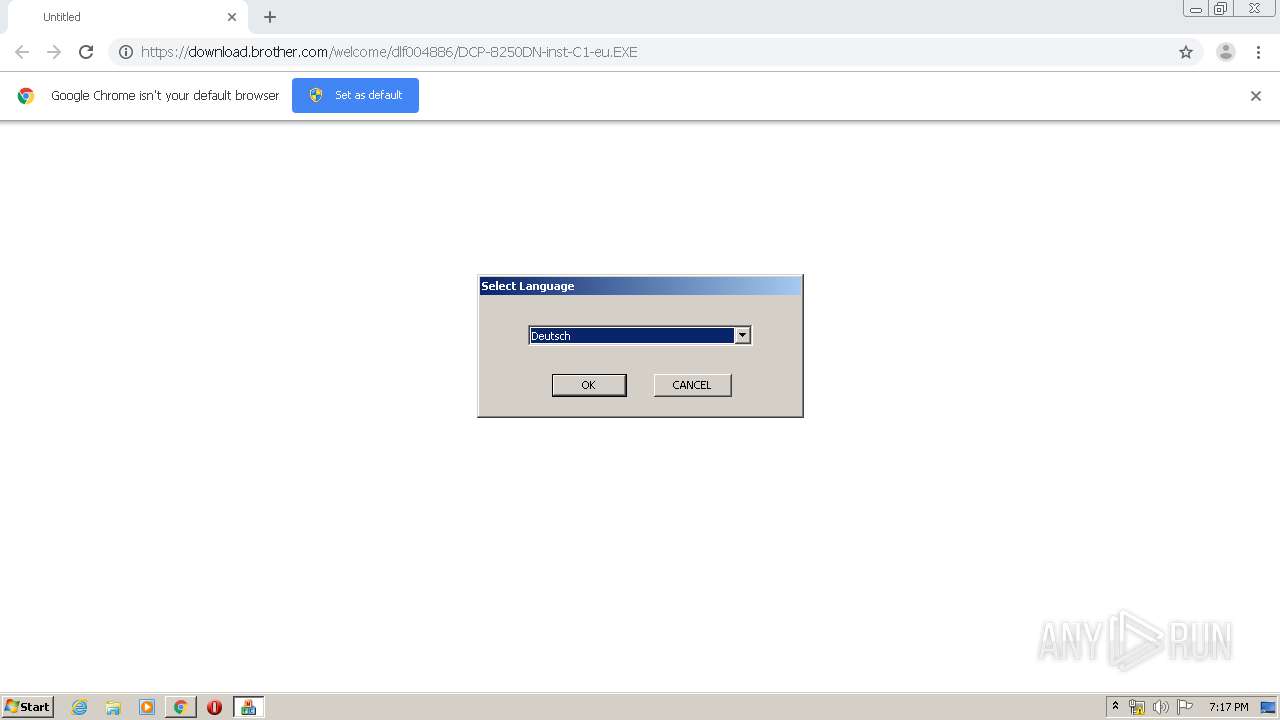
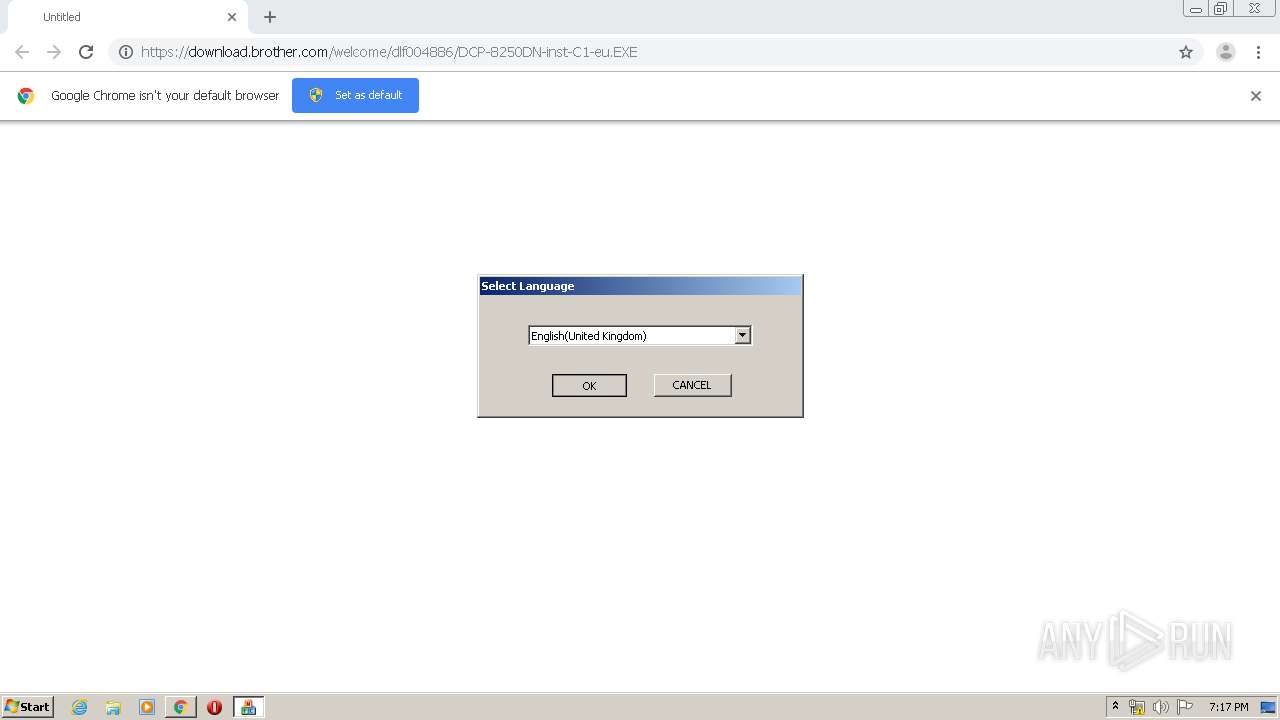
| URL: | https://download.brother.com/welcome/dlf004886/DCP-8250DN-inst-C1-eu.EXE |
| Full analysis: | https://app.any.run/tasks/bba448a0-d772-423f-92e6-415cce7c0d8b |
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2020, 19:14:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B5771808BB8F9623877296C93DA52370 |
| SHA1: | E4546DA3A9768D038A8AA6474C328D9856DBAEAC |
| SHA256: | 0FE94DF3B124A0532F3673481A50408C5397CCC32652970B14CBC81EBED4DE7D |
| SSDEEP: | 3:N8SEl3ViRN1gXCERgCn:2SK3+eyrC |
MALICIOUS
Application was dropped or rewritten from another process
- Setup.exe (PID: 2156)
- DCP-8250DN-inst-C1-eu.EXE (PID: 3588)
- Setup.exe (PID: 2424)
- Setup.exe (PID: 2908)
- BrLogRx.exe (PID: 780)
- BrLogRx.exe (PID: 3324)
- BrRemoveYNSvc.exe (PID: 2800)
- BrLogRx.exe (PID: 3100)
- InstView.exe (PID: 3908)
- BrRemPnP.exe (PID: 3796)
- BrLogRx.exe (PID: 2908)
- BrLogRx.exe (PID: 1460)
- BrDifxapi.exe (PID: 2916)
- BrLogRx.exe (PID: 2844)
- BrLogRx.exe (PID: 3552)
- BrDifxapi.exe (PID: 772)
- BrLogRx.exe (PID: 3000)
- BrDifxapi.exe (PID: 3948)
- BrLogRx.exe (PID: 1492)
- BrDifxapi.exe (PID: 3988)
- BrLogRx.exe (PID: 580)
- BrLogRx.exe (PID: 1352)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3548)
- Setup.exe (PID: 2424)
- BrRemPnP.exe (PID: 3796)
- BrDifxapi.exe (PID: 2916)
- BrDifxapi.exe (PID: 772)
- BrDifxapi.exe (PID: 3948)
- BrDifxapi.exe (PID: 3988)
SUSPICIOUS
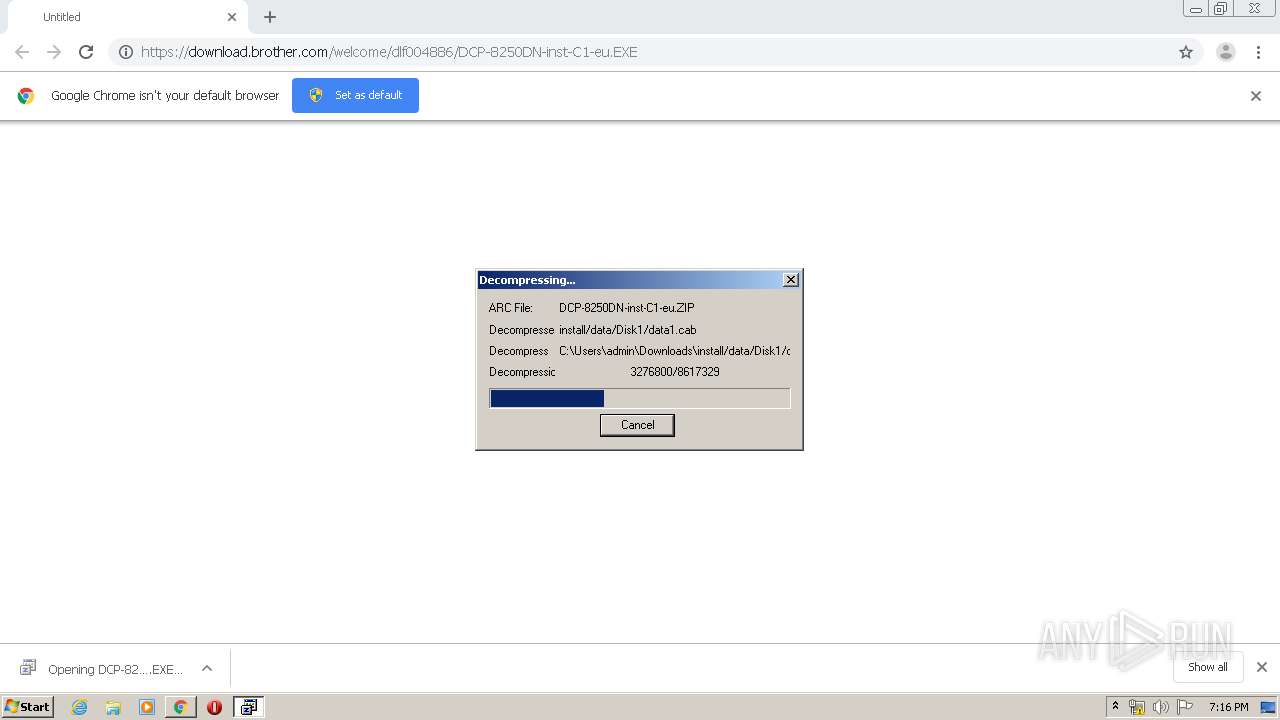
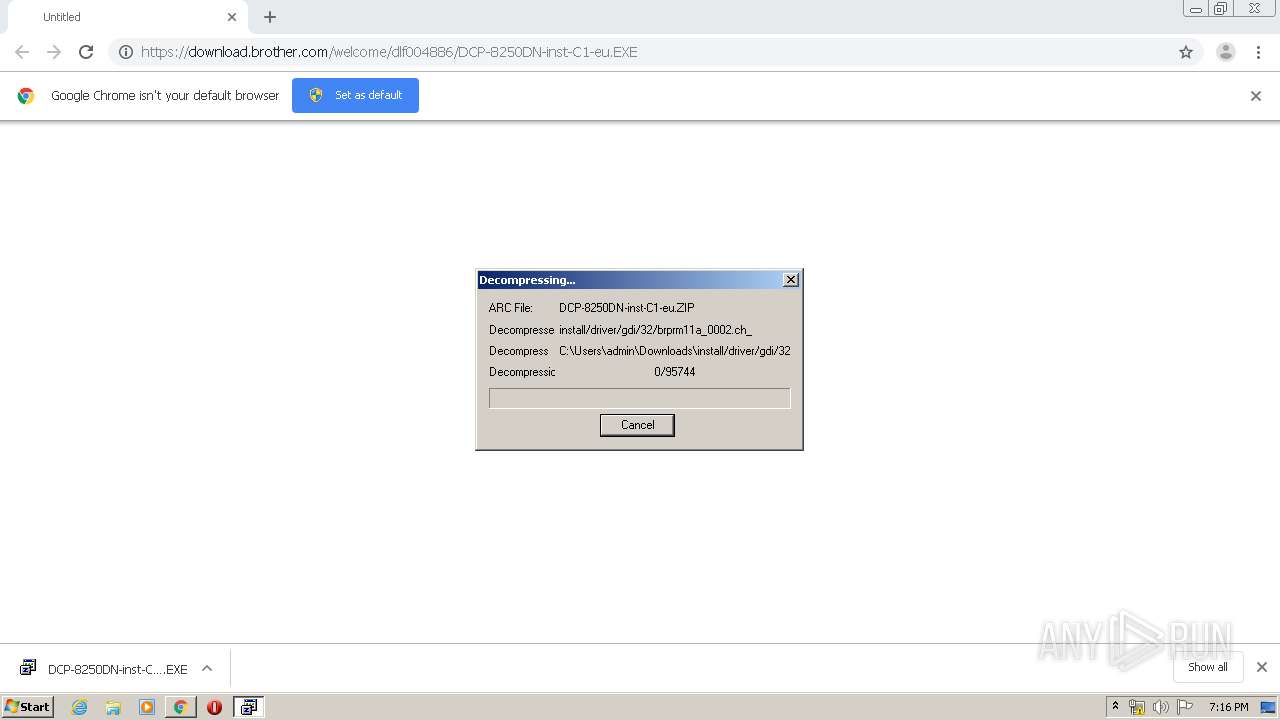
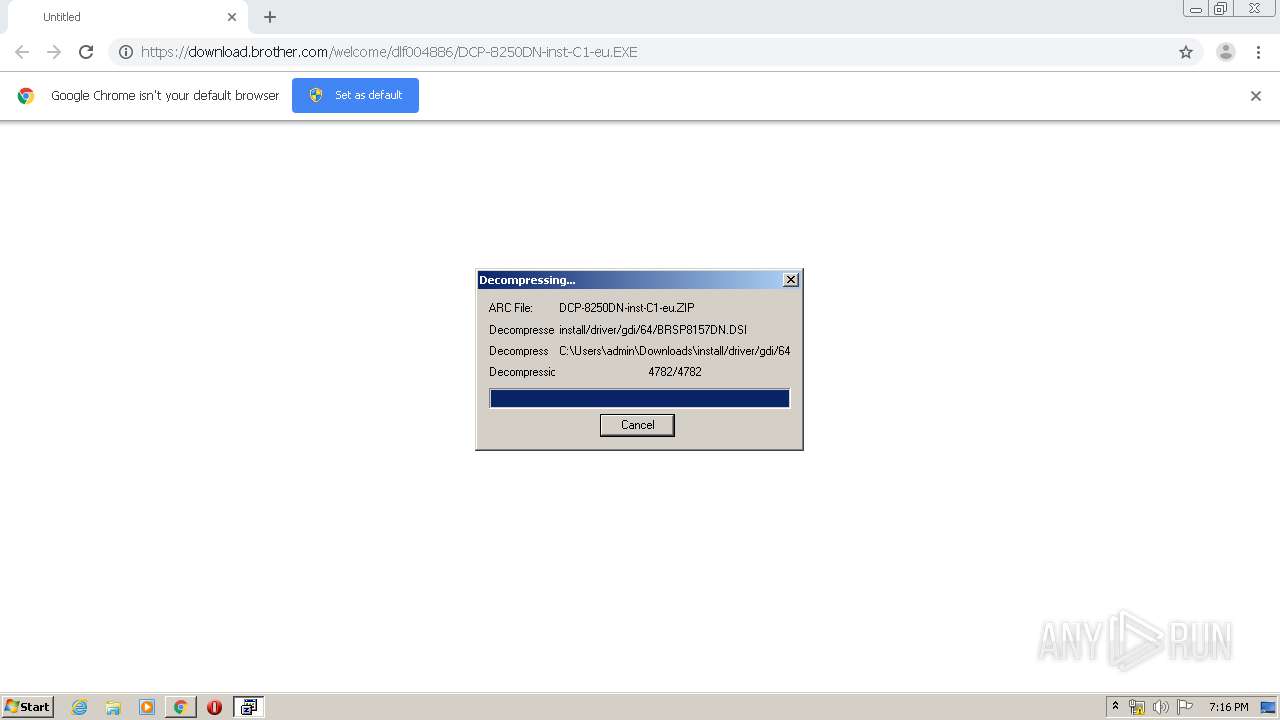
Executable content was dropped or overwritten
- chrome.exe (PID: 2976)
- DCP-8250DN-inst-C1-eu.EXE (PID: 3588)
- Setup.exe (PID: 2424)
- BrDifxapi.exe (PID: 2916)
- DrvInst.exe (PID: 2140)
- BrDifxapi.exe (PID: 772)
- DrvInst.exe (PID: 1460)
Creates files in the user directory
- Setup.exe (PID: 2424)
Creates files in the program directory
- BrLogRx.exe (PID: 3324)
- Setup.exe (PID: 2424)
Executed as Windows Service
- vssvc.exe (PID: 1604)
Searches for installed software
- Setup.exe (PID: 2424)
Executed via COM
- DllHost.exe (PID: 2680)
- DrvInst.exe (PID: 2140)
- DrvInst.exe (PID: 1460)
Creates files in the Windows directory
- Setup.exe (PID: 2424)
- DrvInst.exe (PID: 2140)
- DrvInst.exe (PID: 1460)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2976)
Removes files from Windows directory
- DrvInst.exe (PID: 2140)
- DrvInst.exe (PID: 1460)
Creates files in the driver directory
- DrvInst.exe (PID: 2140)
- DrvInst.exe (PID: 1460)
Creates a software uninstall entry
- Setup.exe (PID: 2424)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2976)
Application launched itself
- chrome.exe (PID: 2976)
Reads the hosts file
- chrome.exe (PID: 2976)
- chrome.exe (PID: 3148)
Reads settings of System Certificates
- chrome.exe (PID: 3148)
- DrvInst.exe (PID: 2140)
Dropped object may contain Bitcoin addresses
- Setup.exe (PID: 2424)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1604)
Changes settings of System certificates
- DrvInst.exe (PID: 2140)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
53
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,16528086209210992509,11284356386140967760,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9975117780395862508 --mojo-platform-channel-handle=3956 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 580 | "C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrLogRx.exe" /function=WTDRV /path="C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrDbgOut.INI" | C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrLogRx.exe | — | Setup.exe | |||||||||||
User: admin Company: Brother Industries, Ltd. Integrity Level: HIGH Description: Brother MFC Windows Software Standard Debug Log Receive Process Exit code: 0 Version: 1, 1, 0, 0 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,16528086209210992509,11284356386140967760,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3954292803781186039 --mojo-platform-channel-handle=4444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrDifxapi.exe -i "C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\..\Drivers\BRPRM11A.INF" 0 | C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrDifxapi.exe | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: BrDifxapi Exit code: 0 Version: 1, 0, 2, 2 Modules
| |||||||||||||||
| 780 | "C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrLogRx.exe" /function=INST /path="C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrDbgOut.INI" | C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrLogRx.exe | — | Setup.exe | |||||||||||
User: admin Company: Brother Industries, Ltd. Integrity Level: HIGH Description: Brother MFC Windows Software Standard Debug Log Receive Process Exit code: 0 Version: 1, 1, 0, 0 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,16528086209210992509,11284356386140967760,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=994818190441299788 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,16528086209210992509,11284356386140967760,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2571169882388698749 --mojo-platform-channel-handle=4672 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,16528086209210992509,11284356386140967760,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5277846881963340370 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrLogRx.exe" /function=MFPRT /path="C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrDbgOut.INI" | C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\{37372D85-4945-4B6B-AC87-7BC5D1AB9F5C}\BrLogRx.exe | — | Setup.exe | |||||||||||
User: admin Company: Brother Industries, Ltd. Integrity Level: HIGH Description: Brother MFC Windows Software Standard Debug Log Receive Process Exit code: 0 Version: 1, 1, 0, 0 Modules
| |||||||||||||||
| 1460 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{09a2b9c6-01f9-4d36-f2ff-4a110e5de70f}\BRPRM11A.INF" "0" "69b786563" "00000558" "WinSta0\Default" "000003C0" "208" "C:\Users\admin\AppData\Local\Temp\{4BE2B014-BFF4-48E2-AA11-FCD2F305A1E1}\Drivers" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 987
Read events
1 769
Write events
2 202
Delete events
16
Modification events
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2976-13227650072889125 |
Value: 259 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
599
Suspicious files
113
Text files
737
Unknown types
3 362
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E5D5B19-BA0.pma | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ab176f06-a720-4306-a513-3625155b58e8.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c20.TMP | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e14.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3148 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
3148 | chrome.exe | GET | 200 | 74.125.110.170:80 | http://r5---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=196.244.192.14&mm=28&mn=sn-5go7yner&ms=nvh&mt=1583176575&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 74.125.110.167:80 | http://r2---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=196.244.192.14&mm=28&mn=sn-5go7yner&ms=nvh&mt=1583176575&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3148 | chrome.exe | 92.122.253.242:443 | download.brother.com | GTT Communications Inc. | — | suspicious |
3148 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.23.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.23.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.22.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 74.125.110.167:80 | r2---sn-5go7yner.gvt1.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 216.58.207.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 74.125.110.170:80 | r5---sn-5go7yner.gvt1.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.brother.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |