| File name: | 0fd |
| Full analysis: | https://app.any.run/tasks/00a463e0-efea-47e0-bfde-a994c8d92fee |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 09:23:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | BBE1F27389E3ABE94176A71F1B9D6E45 |
| SHA1: | 1A956BF0C7B84B70EC33EA829A3161287F8287AC |
| SHA256: | 0FDDBDAD539FEEB904E7FDFA0A1172BBDB64D74B5406C76A36EC30A1496AC463 |
| SSDEEP: | 49152:fytvjkR51HGhujN60iVU/o3O8dTMDoCAV:fovjWJ606Ug3O8d |
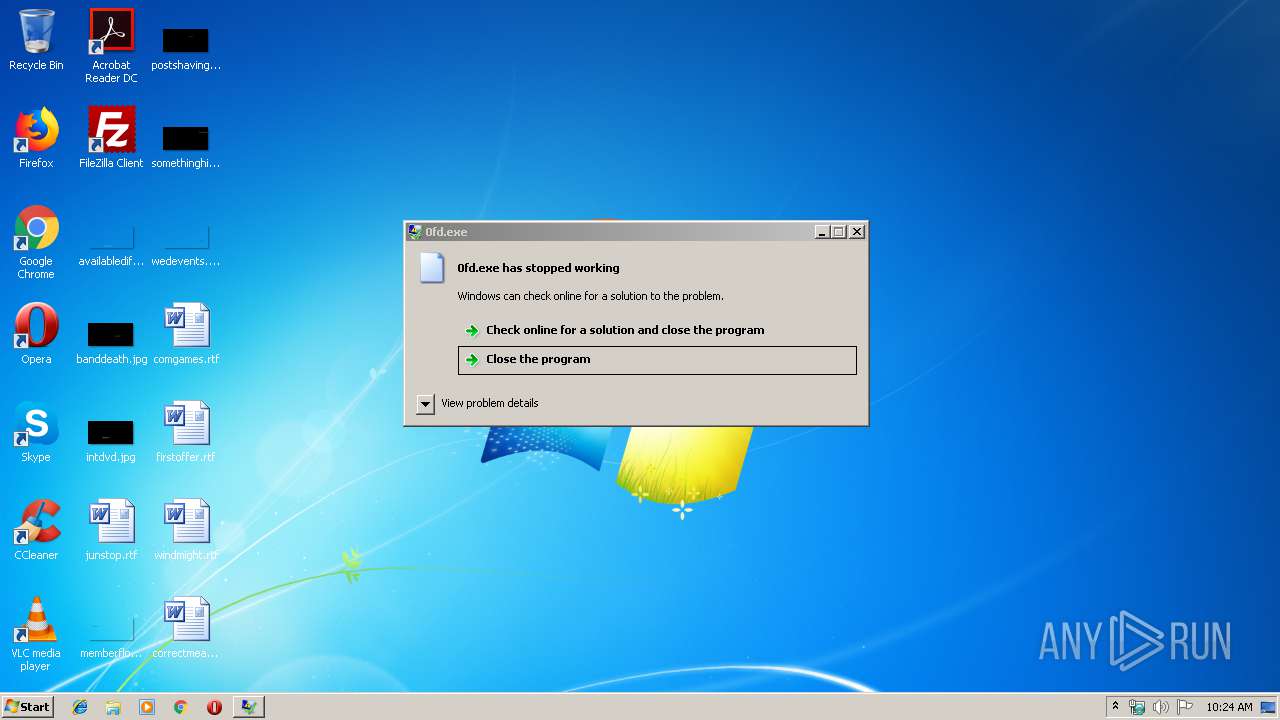
MALICIOUS
Loads dropped or rewritten executable
- WerFault.exe (PID: 3992)
SUSPICIOUS
Searches for installed software
- rundll32.exe (PID: 2040)
INFO
Loads main object executable
- rundll32.exe (PID: 2040)
Application was crashed
- rundll32.exe (PID: 2040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (70.7) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (11.2) |
| .exe | | | Win32 Executable (generic) (7.6) |
| .exe | | | Win16/32 Executable Delphi generic (3.5) |
| .exe | | | Generic Win/DOS Executable (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:30 20:41:35+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1887232 |
| InitializedDataSize: | 256512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ce7ac |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Sep-2019 18:41:35 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 30-Sep-2019 18:41:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001CB020 | 0x001CB200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53588 |
.itext | 0x001CD000 | 0x00001814 | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09901 |
.data | 0x001CF000 | 0x00016FB0 | 0x00017000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.70059 |
.bss | 0x001E6000 | 0x00007ED8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x001EE000 | 0x00002600 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1929 |
.didata | 0x001F1000 | 0x000001D4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.22228 |
.edata | 0x001F2000 | 0x000000AB | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.08727 |
.rdata | 0x001F3000 | 0x00000044 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.16606 |
.reloc | 0x001F4000 | 0x00020998 | 0x00020A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6995 |
.rsrc | 0x00215000 | 0x00004400 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.24477 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
4079 | 3.34782 | 976 | UNKNOWN | UNKNOWN | RT_STRING |
4080 | 3.3442 | 644 | UNKNOWN | UNKNOWN | RT_STRING |
4081 | 2.5 | 64 | UNKNOWN | UNKNOWN | RT_STRING |
4082 | 2.5 | 64 | UNKNOWN | UNKNOWN | RT_STRING |
4083 | 2.5 | 64 | UNKNOWN | UNKNOWN | RT_STRING |
4084 | 3.3035 | 680 | UNKNOWN | UNKNOWN | RT_STRING |
4085 | 3.33735 | 972 | UNKNOWN | UNKNOWN | RT_STRING |
4086 | 3.52387 | 920 | UNKNOWN | UNKNOWN | RT_STRING |
4087 | 3.23072 | 1176 | UNKNOWN | UNKNOWN | RT_STRING |
4088 | 3.30539 | 912 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
esent.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
netapi32.dll |
ntdll.dll |
ole32.dll |
oleaut32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x001E9634 |
__dbk_fcall_wrapper | 2 | 0x0000F018 |
TMethodImplementationIntercept | 3 | 0x00056070 |
MainProc | 4 | 0x001C3A8C |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2040 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\0fd.exe", dbkFCallWrapperAddr | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3992 | C:\Windows\system32\WerFault.exe -u -p 2040 -s 340 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
398
Read events
398
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3992 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\rundll32.exe.2040.dmp | dmp | |
MD5:— | SHA256:— | |||
| 3992 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_rundll32.exe_0fd_c05b3e67a3c6e7b4f86eb01267da97179066a3_0fa27de0\Report.wer | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report