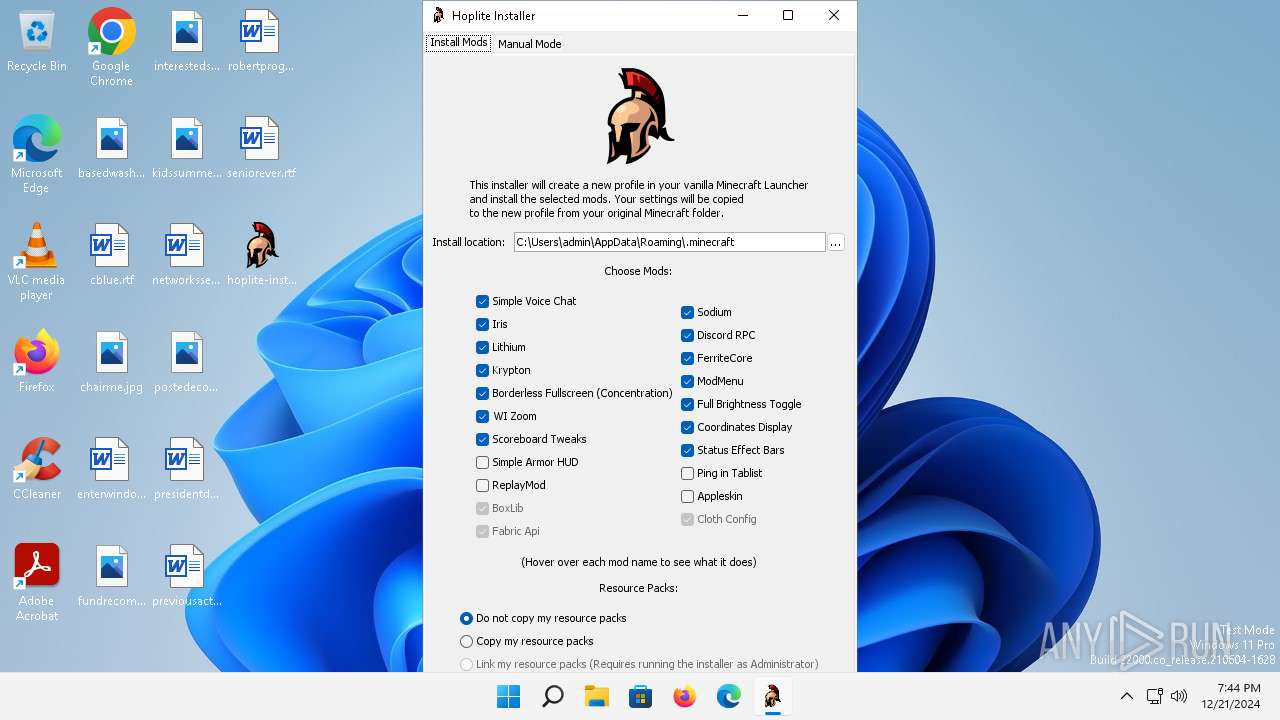
| File name: | hoplite-installer-1.1.2.exe |
| Full analysis: | https://app.any.run/tasks/6a6be43a-2540-496f-ac86-fb7acfce02a6 |
| Verdict: | Malicious activity |
| Analysis date: | December 21, 2024, 19:44:09 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive, with extra data prepended |
| MD5: | 830D17BBA977D824292E1322E5E3253B |
| SHA1: | 8D392D80610E7A20CDDD9E4048334F66EA72EA66 |
| SHA256: | 0FD8F8BD3E463A0E174EA583533C14689FE2219BE5184C7E16FC62D7AB1CE9EE |
| SSDEEP: | 98304:k0rKj3JPAOVgGpxDv/PH+Zue6sB+5UDqc6YPq8bAP2qz4WwJfn5TCu615VGcn9xC:29llfcR0Sk5Gdvr6bps |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for Java to be installed
- javaw.exe (PID: 3796)
- javaw.exe (PID: 2848)
Reads settings of System Certificates
- javaw.exe (PID: 2848)
INFO
The sample compiled with english language support
- hoplite-installer-1.1.2.exe (PID: 3808)
Create files in a temporary directory
- javaw.exe (PID: 3796)
- javaw.exe (PID: 2848)
Checks supported languages
- hoplite-installer-1.1.2.exe (PID: 3808)
- javaw.exe (PID: 3796)
- javaw.exe (PID: 2848)
Creates files in the program directory
- javaw.exe (PID: 3796)
Reads the machine GUID from the registry
- javaw.exe (PID: 2848)
Creates files or folders in the user directory
- javaw.exe (PID: 2848)
Reads the computer name
- javaw.exe (PID: 2848)
Reads the software policy settings
- javaw.exe (PID: 2848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:04 13:51:30+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.35 |
| CodeSize: | 134656 |
| InitializedDataSize: | 381952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa780 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| CompanyName: | Fabric Team |
| FileDescription: | Fabric Installer |
| FileVersion: | 1.0.0.1 |
| InternalName: | fabric-i.exe |
| LegalCopyright: | Copyright (C) 2022 |
| OriginalFileName: | fabric-installer-native-bootstrap.exe |
| ProductName: | Fabric Installer |
| ProductVersion: | 1.0.0.1 |
Total processes
121
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1900 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2848 | "javaw.exe" "-jar" "C:\Users\admin\Desktop\hoplite-installer-1.1.2.exe" "-fabricInstallerBootstrap" "true" | C:\Program Files (x86)\Common Files\Oracle\Java\javapath_target_81281\javaw.exe | hoplite-installer-1.1.2.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Version: 8.0.3510.10 Modules
| |||||||||||||||
| 3796 | "javaw.exe" "-version" | C:\Program Files (x86)\Common Files\Oracle\Java\javapath_target_81281\javaw.exe | — | hoplite-installer-1.1.2.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.3510.10 Modules
| |||||||||||||||
| 3808 | "C:\Users\admin\Desktop\hoplite-installer-1.1.2.exe" | C:\Users\admin\Desktop\hoplite-installer-1.1.2.exe | — | explorer.exe | |||||||||||
User: admin Company: Fabric Team Integrity Level: MEDIUM Description: Fabric Installer Version: 1.0.0.1 Modules
| |||||||||||||||
| 6660 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 458
Read events
6 458
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio385375605254306347.tmp | image | |
MD5:F78DA948ED67779F62C079E53354B51F | SHA256:FEA4AD86EE3539B98029383DB705C18AEFA8A2BCFAB5D964975987BC32250FB5 | |||
| 2848 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-166304369-59083888-3082702900-1001\83aa4cc77f591dfc2374580bbd95f6ba_c058e375-e15a-4784-84e6-145044762c88 | binary | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 3796 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c83e4.timestamp | text | |
MD5:1E2778AD9A339670CF4E608BEEC5B731 | SHA256:C3AD30ADE8ADD98C3C69EEA1486ED28A8A0C26C57DAE2C4F46A2888AF84C65B6 | |||
| 2848 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio3507162669276796137.tmp | image | |
MD5:F78DA948ED67779F62C079E53354B51F | SHA256:FEA4AD86EE3539B98029383DB705C18AEFA8A2BCFAB5D964975987BC32250FB5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
41
DNS requests
34
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.4:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
4308 | MoUsoCoreWorker.exe | GET | 200 | 2.16.10.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5e3503ccb86672f9 | unknown | — | — | whitelisted |
3932 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
3932 | firefox.exe | POST | 200 | 95.100.146.66:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
3932 | firefox.exe | POST | 200 | 95.100.146.41:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.35.236.109:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
3932 | firefox.exe | POST | 200 | 95.100.146.66:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 52.113.194.132:443 | https://ecs.office.com/config/v2/Office/officeclicktorun/16.0.16626.20134/Production/CC?&Clientid=%7b80C2A92B-EDEE-479E-8470-DBC6C547F2FB%7d&Application=officeclicktorun&Platform=win32&Version=16.0.16626.20134&MsoVersion=16.0.16626.20134&ProcessName=officec2rclient.exe&Audience=Production&Build=ship&Architecture=x64&OsVersion=10.0&OsBuild=22000&Channel=CC&InstallType=C2R&SessionId=%7bE7017A7E-D25E-43C3-A03B-D31701B0737D%7d&LabMachine=false | unknown | binary | 355 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.17:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 210 b | whitelisted |
— | — | GET | 200 | 13.107.6.156:443 | https://mrodevicemgr.officeapps.live.com/mrodevicemgrsvc/api/v1/C2RTargetAudienceData?omid=97560490bafb0d49bca6f8f0df91025d&susid=c408ee57-2103-4c34-9e6f-30bdf6c87e50&audienceFFN=492350f6-3a01-4f97-b9c0-c7c6ddf67d60&tid=&osver=Client%7C10.0.22000&offver=16.0.16626.20134&ring=Production&aud=Production&ch=CC&osarch=x64&manstate=6 | unknown | binary | 188 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
1744 | rundll32.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6688 | OfficeC2RClient.exe | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
3932 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
3932 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
— | — | 184.24.77.4:80 | — | Akamai International B.V. | DE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4308 | MoUsoCoreWorker.exe | 2.16.10.172:80 | ctldl.windowsupdate.com | Akamai International B.V. | AT | unknown |
— | — | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1592 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
login.live.com |
| unknown |
ecs.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |