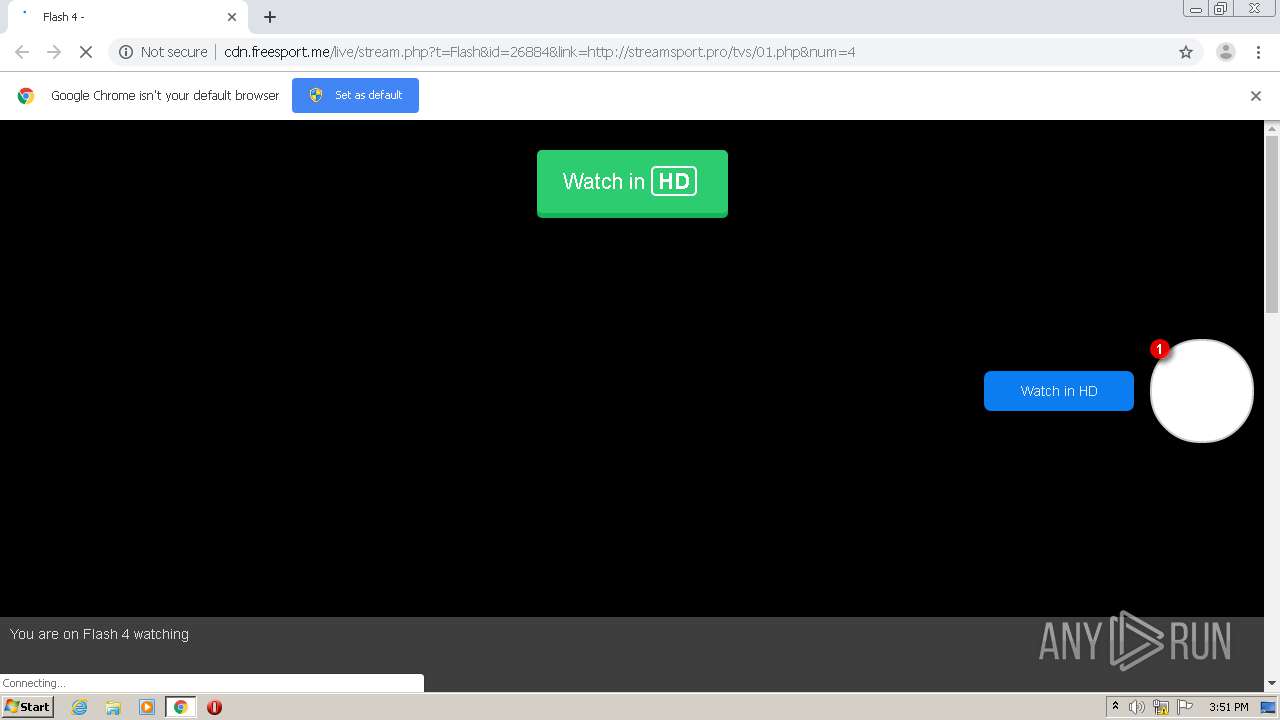
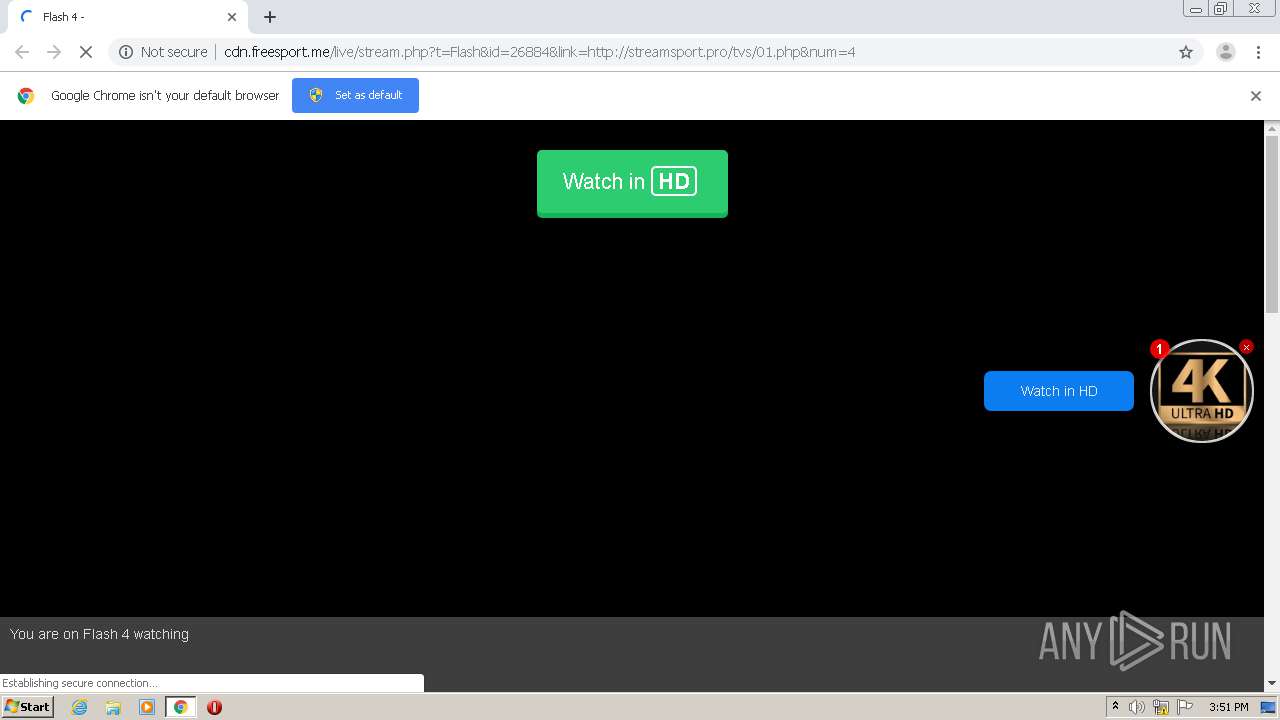
| URL: | http://cdn.freesport.me/live/stream.php?t=Flash&id=26884&link=http://streamsport.pro/tvs/01.php&num=4 |
| Full analysis: | https://app.any.run/tasks/7551bcb9-281c-4199-87b5-7892829106bc |
| Verdict: | Malicious activity |
| Analysis date: | October 06, 2020, 14:50:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DA1E00ECAFC3036A650E1FD69B344D59 |
| SHA1: | 7F6A3CCF9B2759D45B3807B329FFAA16ED9AA71B |
| SHA256: | 0FD7BFB7FEDA5F326B12ECA85C2174D4F3E672815603964D5982E7B0502E75E0 |
| SSDEEP: | 3:N1KdBLAzS6AKgVEYXRxVgRR1wRR83BRTN0DB8:CXAO6ABrg31s83TN6e |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 3368)
- chrome.exe (PID: 1940)
Application launched itself
- chrome.exe (PID: 1940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13472912997461532427,12824282160591048823,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7049048322199148695 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13472912997461532427,12824282160591048823,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2248549324906994943 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13472912997461532427,12824282160591048823,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1634511013446403073 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13472912997461532427,12824282160591048823,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2825447930503140882 --mojo-platform-channel-handle=4468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13472912997461532427,12824282160591048823,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3786447724401194801 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://cdn.freesport.me/live/stream.php?t=Flash&id=26884&link=http://streamsport.pro/tvs/01.php&num=4" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6cdba9d0,0x6cdba9e0,0x6cdba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13472912997461532427,12824282160591048823,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15303216218660009756 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13472912997461532427,12824282160591048823,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5072210394641802275 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13472912997461532427,12824282160591048823,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1237538943045449869 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
621
Read events
546
Write events
71
Delete events
4
Modification events
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1940-13246469468609750 |
Value: 259 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (1940) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1940-13246469468609750 |
Value: 259 | |||
Executable files
0
Suspicious files
54
Text files
87
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7C845D-794.pma | — | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1ff8ad53-763e-407d-b5bc-b717bc6cf843.tmp | — | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1ab121.TMP | text | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1ab121.TMP | text | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1940 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1ab16f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
147
DNS requests
77
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
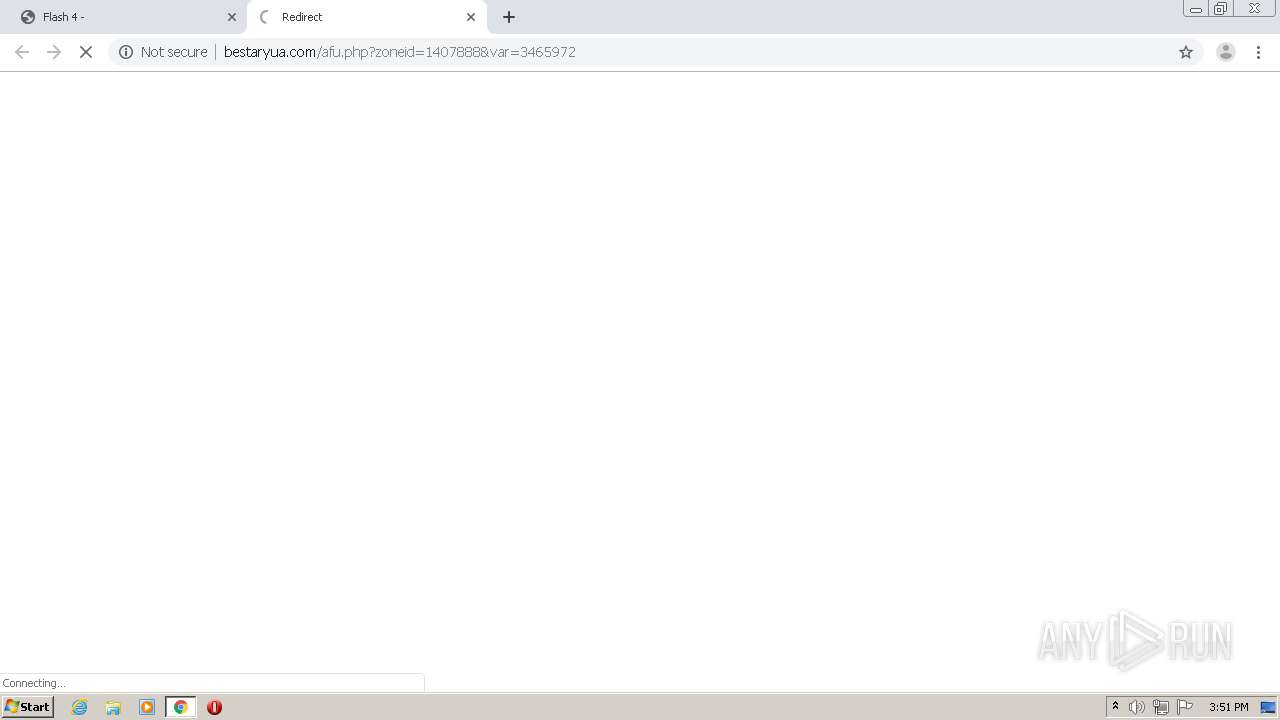
3368 | chrome.exe | GET | 204 | 139.45.196.108:80 | http://bestaryua.com/fac.php | US | — | — | malicious |
3368 | chrome.exe | GET | 200 | 143.204.208.94:80 | http://d10lumateci472.cloudfront.net/?cdlad=885260 | US | compressed | 57.2 Kb | whitelisted |
3368 | chrome.exe | GET | 200 | 208.93.230.22:80 | http://st.chatango.com/js/gz/emb.js | US | text | 24.0 Kb | whitelisted |
3368 | chrome.exe | GET | 200 | 143.204.201.65:80 | http://roughthos.top/R3NyRkYmEREreSZOEGAzNR9PY3QBVkAAInAXCCd+NEQYdCcqRVwlKigGFiA0KB0GaCgiB1d0ADMnGXcsHTQnMg8gQzERLCgYMHcqIxccLhQSJUMpDD8yPgU8cgQ8Fw8XOTEhDQknN3InPxAXBx4JSyAXIQI6MTYjFhQzIQorRiQXP38DMxAqFRI2LRIEBEc8DAYmNQUsc0I3MQckPCU1EQUlFSwPLxg8BRUOACAqHy0WQAgSFiUWY3QFKSAXCAQKHS8ABRczIA53PTcDBH8VJBANETQWKRMRIjcWLHcjMxQPNT8FIQgCJAZjdAE5JAARIiQ8FxMsMUogE2oAIgISKBQ2dgAfNyUuFBEyGSgMICkwEHVzAjAhJQg6JRQBER8nMgwVNj4FBTMcJxUMFBZACBIUHyhzIys9ORAOckogKhwRIyExAAUhESgnATYbEw52RSYQIhMSNi4jEUI8dSIGJSQHdXccJyoUFBYbLhcfMiMyDXY2NRAvN1ZABBMrKjYKPzQ0JCElYRkBKSg3TiQgLC0WGxcSMQ | US | compressed | 1.20 Kb | suspicious |
3368 | chrome.exe | GET | 200 | 143.204.201.65:80 | http://roughthos.top/VFJ1Rms1MBYrVDVvF2AeJj5IY1kSd0cAD2M2DydTJ2UfdAo5ZFslBzsnESAZOzwBaAUxJlB0LR0AMhAYDgcWKCgzGzEjLxUfNgADcWAzIC0aCyN1OT0WDX4gHwYnHygFFyIEAh0QOwRfBBo0HDMWO0UWL2QfDxYMEgAjAS47EDQPKDE/PAcqMwhDIj4ZHDQVPWEHICk6HjweDyosagANKj8cJA4+FwcwDD0NPC8QORYbAA0MERYwLDk8BEQxJxlgMx4zEhwFIj4sGCN1CDgUJzEhHTg4By8zZgALLhY3PHUhZwceDDw3BTMeMxFiBgopERA2ESFmGB5rBww2DCEmFiU3Lw84BzkHKAUkNi09FTYtFywWEBYpIAUQPxAcEiggAyECMy0iOANjIzYPAgQWFyMCYjMhWxAYHx8mBwQWBAgCCBcVWAYrJD4HDTY9DAgCAzt0IjgLPxAjMCggFwcDNAwTLBc+FioPIxQTECMBOzcHBBU2Jh9NPiEaKBtpNxEXKRM/JB8gLThHBwI+MQ | US | compressed | 1.20 Kb | suspicious |
3368 | chrome.exe | GET | 200 | 143.204.201.65:80 | http://roughthos.top/aGdOV0cJBS06eAlaLHEyGgtzcnUuQnwRI1lXIiIqCRMrNC5cUHx5JAQIOzMhGgggI2kGAjpydS4THwABHQMJIC4sAA8EEhIyBxQsBDIrASMJNSI/KSsffjUGAiEtGQMlDwg+fxwjDTxwIxAtGQQPDwYQIFwuKBEFISAPZzEqCwAEBDtfDQJ3PiwHFhIlNBg/KS4mdx0GO1MsFT8PJgcSFQsqIjsxPTI6EB8vDBkVPwcuAj8eDDIYYj8sHz4FHwYhFgYCPiEUEQkNIRwgPyw2PRMEOyoFFTAqLS0uIwo1fyMxPQsmBR8GIQQVFR8+AhZ2JDUnbiw9VmNjHio0IRIUWD0tHSA5KQYgCQc1CC8CLB4lAwY6DAQNASUIH2YrHjIbFQ8/VBQFFi0xLTQSOgQcFX8PJTlvACowHAMMLSEoMyxRAx88KFg/CGYEPj8pHx8QLSgdASoCH2YgAzIiDhEsHioDAy0EBzQrKgQLMHcGJQggEE4NPTgpGFoUEAo/KQ0vAhItJy4hIQ | US | compressed | 1.20 Kb | suspicious |
3368 | chrome.exe | GET | 200 | 143.204.208.82:80 | http://d3dq1nh1l1pzqy.cloudfront.net/?hnqdd=899427 | US | text | 52.9 Kb | whitelisted |
3368 | chrome.exe | GET | 200 | 143.204.208.190:80 | http://d3m4hp4bp4w996.cloudfront.net/ENXFFNVhWHitTZ0EYIQhgDUdxB2wTGzZaNkVMKWETfCIsYzxvPwhiCWFIIhMsTxV4BH5ZECtSZRMUK1ZlBFckUToIRWNAOQgcKk8xWR0kEGpzRGsFfQdBbUIxWxUqQisQQ3VbLBBDdQN2BFhgB2hUATVZPUIUJ14xQVR3c20GRmsGbhBDdR0zXQUoWX0HMm-AHaFkYLlB9B0EiUDteHmwQagUSLUc3WBRgBx4CRGsFdgZGcgV2BEF1EGoFAiRTOUcYYAceAEJyG2sDVzAIawNIfFNpU0IgBGgCRSAGYFQSIwc6BhV2BGpTECNQalc | US | text | 188 b | whitelisted |
3368 | chrome.exe | GET | 200 | 143.204.208.94:80 | http://d10lumateci472.cloudfront.net/tQWFudGwiDgASUzUICklUeVdaRlhnCx0bAjFcNDMhFi8tDCk7KwcNCghHGg4IfFBIGA0vBlNSCS8CU0VKIAUMSVhnFA9JAS4bBxgAIERcMllvUUtGXGkWBxoILhYdUV5xDxpRXnFXQEVFZFNeFRwxDQsDCSMKBwBJcydbR1tvUlhRXnFJBRwYLA1LRi9kU1-4YBSoES0ZcJgQNHwNoRFxEDykTARkJZFMoQ1lvUUBHW3ZRQEVccURcRB8gBw8GBWRTKEFfdk9dQko0XF1CVXgHXxJfJFBeQ1gkUlYVDydTDEcIclBcEg0nBFwW | US | compressed | 187 b | whitelisted |
3368 | chrome.exe | GET | 200 | 143.204.208.190:80 | http://d3m4hp4bp4w996.cloudfront.net/rVlZZVmFpIjAyXG5ubGRXZg%3D%3D | US | text | 57.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3368 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3368 | chrome.exe | 104.18.61.197:80 | cdn.freesport.me | Cloudflare Inc | US | shared |
3368 | chrome.exe | 104.18.35.235:443 | cdn.sports-streams-online.best | Cloudflare Inc | US | shared |
3368 | chrome.exe | 172.217.21.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3368 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3368 | chrome.exe | 172.217.22.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3368 | chrome.exe | 104.31.70.25:80 | streamsport.pro | Cloudflare Inc | US | suspicious |
3368 | chrome.exe | 172.67.157.119:443 | cdn.sport-play.tv | — | US | unknown |
3368 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3368 | chrome.exe | 172.255.6.32:80 | hulkflugarb.com | — | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.freesport.me |
| unknown |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.sports-streams-online.best |
| suspicious |
st.chatango.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
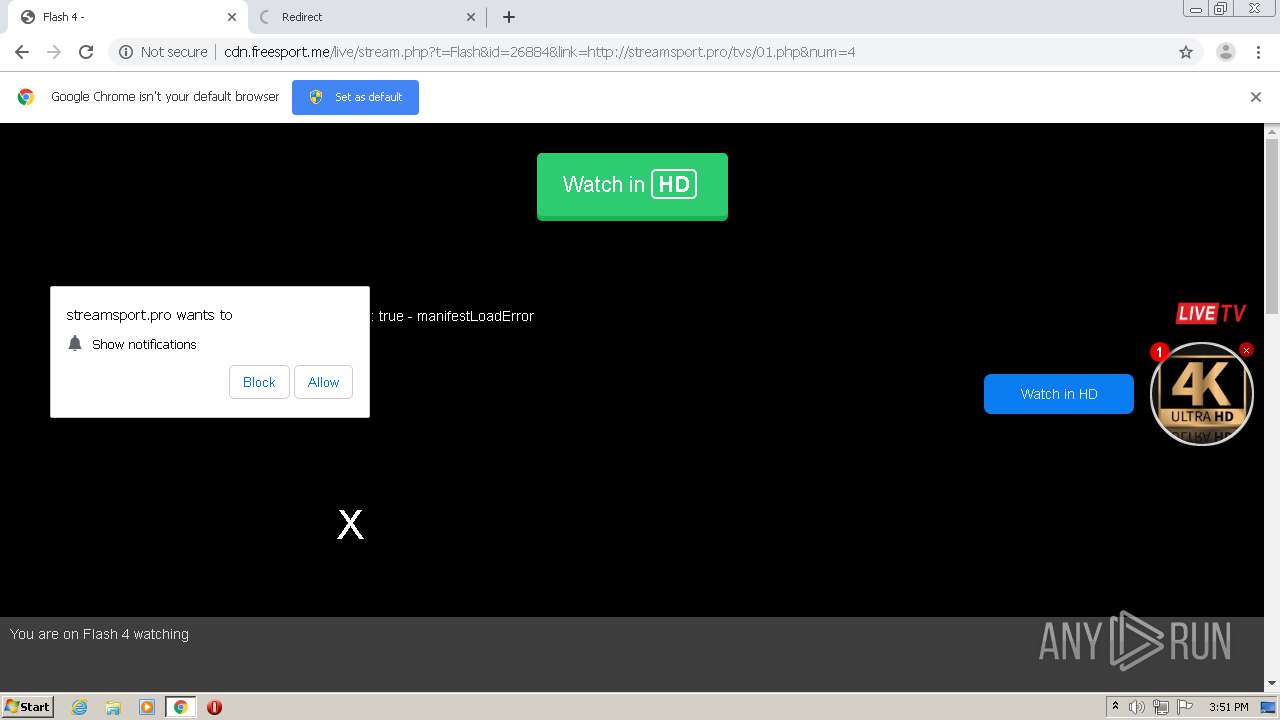
streamsport.pro |
| suspicious |
cdn.sport-play.tv |
| malicious |
trck.sport-play.tv |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3368 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3368 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |
3368 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |
3368 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |
3368 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |