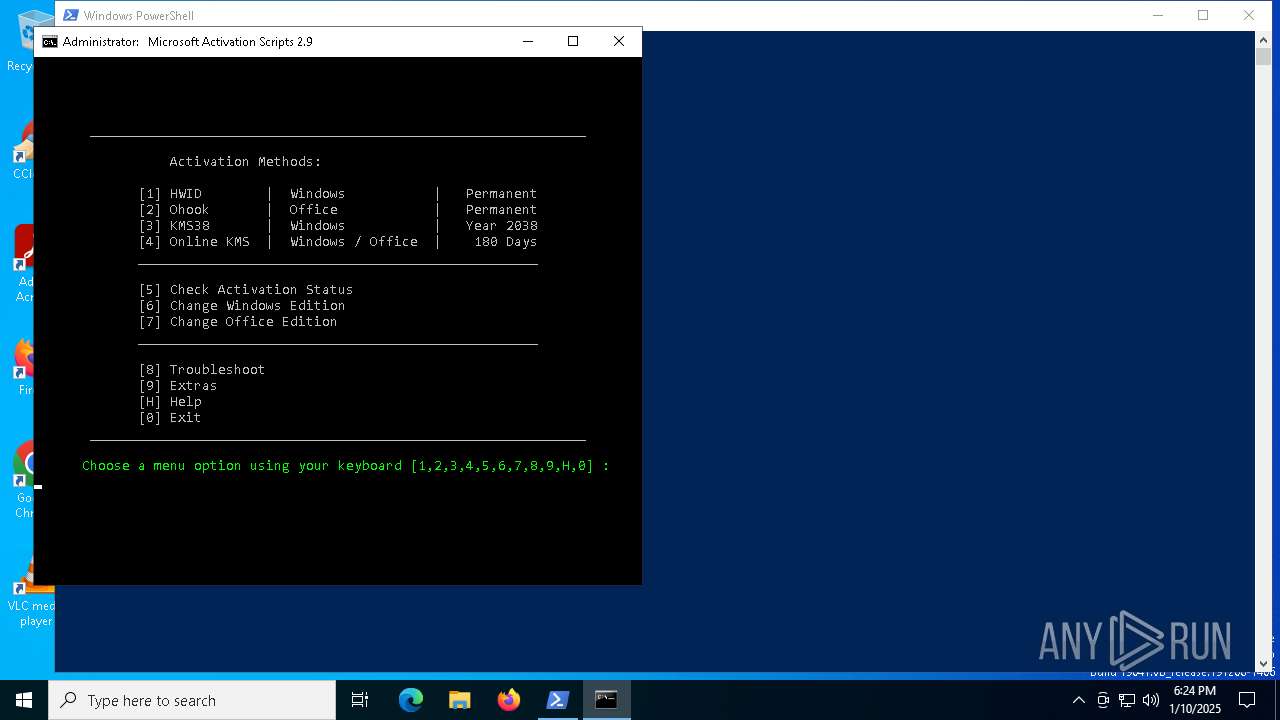
| File name: | get.activated.ps1 |
| Full analysis: | https://app.any.run/tasks/12d9e73f-71e5-4d6e-8053-c24b5f3af010 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 18:24:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 206946295B10FCF003BD1BB6288EDBE0 |
| SHA1: | 504155F51C075CEDB5718BEE3AEFFB93AB80DF23 |
| SHA256: | 0FBD7D092FA230EE22935B919F783AA0D51FB03B93483C85A211076DAF2CE116 |
| SSDEEP: | 3:WIuJsTE2mMVn:WIuAmgn |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6292)
SUSPICIOUS
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6292)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 3928)
- powershell.exe (PID: 2224)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6292)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6292)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 3928)
- powershell.exe (PID: 2224)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 6292)
Executing commands from ".cmd" file
- powershell.exe (PID: 6292)
- cmd.exe (PID: 7016)
- powershell.exe (PID: 396)
- cmd.exe (PID: 6184)
- powershell.exe (PID: 4076)
- cmd.exe (PID: 6800)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6292)
- cmd.exe (PID: 4872)
- cmd.exe (PID: 7016)
- powershell.exe (PID: 396)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 6284)
- powershell.exe (PID: 4076)
- cmd.exe (PID: 1144)
- cmd.exe (PID: 6800)
Windows service management via SC.EXE
- sc.exe (PID: 7088)
- sc.exe (PID: 6820)
- sc.exe (PID: 5748)
- sc.exe (PID: 7032)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 6800)
Application launched itself
- cmd.exe (PID: 7016)
- cmd.exe (PID: 4872)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 6284)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 1144)
Starts SC.EXE for service management
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 6800)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2632)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 7132)
- cmd.exe (PID: 6800)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2632)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7132)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2632)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7132)
Get information on the list of running processes
- cmd.exe (PID: 6800)
- cmd.exe (PID: 4244)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6800)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4052)
Hides command output
- cmd.exe (PID: 4244)
INFO
Checks proxy server information
- powershell.exe (PID: 6292)
Disables trace logs
- powershell.exe (PID: 6292)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6292)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 3928)
- powershell.exe (PID: 2224)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 6292)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 3928)
- powershell.exe (PID: 2224)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6292)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 3928)
- powershell.exe (PID: 2224)
The process uses the downloaded file
- powershell.exe (PID: 6292)
- powershell.exe (PID: 396)
Checks operating system version
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 6184)
Checks supported languages
- mode.com (PID: 6056)
- mode.com (PID: 3812)
- mode.com (PID: 876)
Starts MODE.COM to configure console settings
- mode.com (PID: 3812)
- mode.com (PID: 6056)
- mode.com (PID: 876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
255
Monitored processes
125
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | find /i "-groove.exe-" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 204 | find /i "-outlook.exe-" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | powershell.exe "start cmd.exe -arg '/c \""""C:\Users\admin\AppData\Local\Temp\MAS_dc390a75-8f89-42a0-be08-5a72b7ad74b2.cmd""" -el \"' -verb runas" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | C:\WINDOWS\System32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo -smss.exe- -csrss.exe- -wininit.exe- -csrss.exe- -winlogon.exe- -services.exe- -lsass.exe- -svchost.exe- -fontdrvhost.exe- -fontdrvhost.exe- -svchost.exe- -svchost.exe- -dwm.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -spoolsv.exe- -svchost.exe- -svchost.exe- -svchost.exe- -OfficeClickToRun.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -dasHost.exe- -svchost.exe- -svchost.exe- -sihost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -ctfmon.exe- -svchost.exe- -explorer.exe- -svchost.exe- -RuntimeBroker.exe- -SearchApp.exe- -RuntimeBroker.exe- -dllhost.exe- -RuntimeBroker.exe- -dllhost.exe- -SystemSettings.exe- -ApplicationFrameHost.exe- -svchost.exe- -MoUsoCoreWorker.exe- -UserOOBEBroker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -uhssvc.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -TextInputHost.exe- -dllhost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -backgroundTaskHost.exe- -backgroundTaskHost.exe- -powershell.exe- -conhost.exe- -svchost.exe- -RuntimeBroker.exe- -cmd.exe- -conhost.exe- -WmiPrvSE.exe- -powershell.exe- -cmd.exe- -cmd.exe- -tasklist.exe- -findstr.exe- " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | C:\WINDOWS\System32\cmd.exe /c reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /v Desktop | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | find /i "/S" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | mode 130, 32 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | C:\WINDOWS\System32\cmd.exe /c echo prompt $E | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
46 065
Read events
46 065
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
4
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF135cc9.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\F64RBJE5EAR7JL7WL770.temp | binary | |
MD5:C104C8DBD8FE1D7A5367D7B4DB62F05E | SHA256:4AF18F9970298986E43F8F2961584FC3F9DA2F1130BBB58B0528DD47428E28C7 | |||
| 6292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0o1pkiha.wqx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fdvbz33r.hnq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6932 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4dzlpzhf.2dn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:C104C8DBD8FE1D7A5367D7B4DB62F05E | SHA256:4AF18F9970298986E43F8F2961584FC3F9DA2F1130BBB58B0528DD47428E28C7 | |||
| 3928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ckatc4sw.yds.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6932 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2p5jmygh.x40.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4076 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_izdigg5e.pzg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1qlipz42.ba4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
34
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5972 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 418 b | whitelisted |
6152 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
5972 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4712 | MoUsoCoreWorker.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
— | — | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5064 | SearchApp.exe | 104.126.37.185:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
crl.microsoft.com |
| unknown |
www.microsoft.com |
| unknown |
www.bing.com |
| unknown |
ocsp.digicert.com |
| unknown |
login.live.com |
| unknown |
go.microsoft.com |
| unknown |
get.activated.win |
| unknown |
git.activated.win |
| unknown |