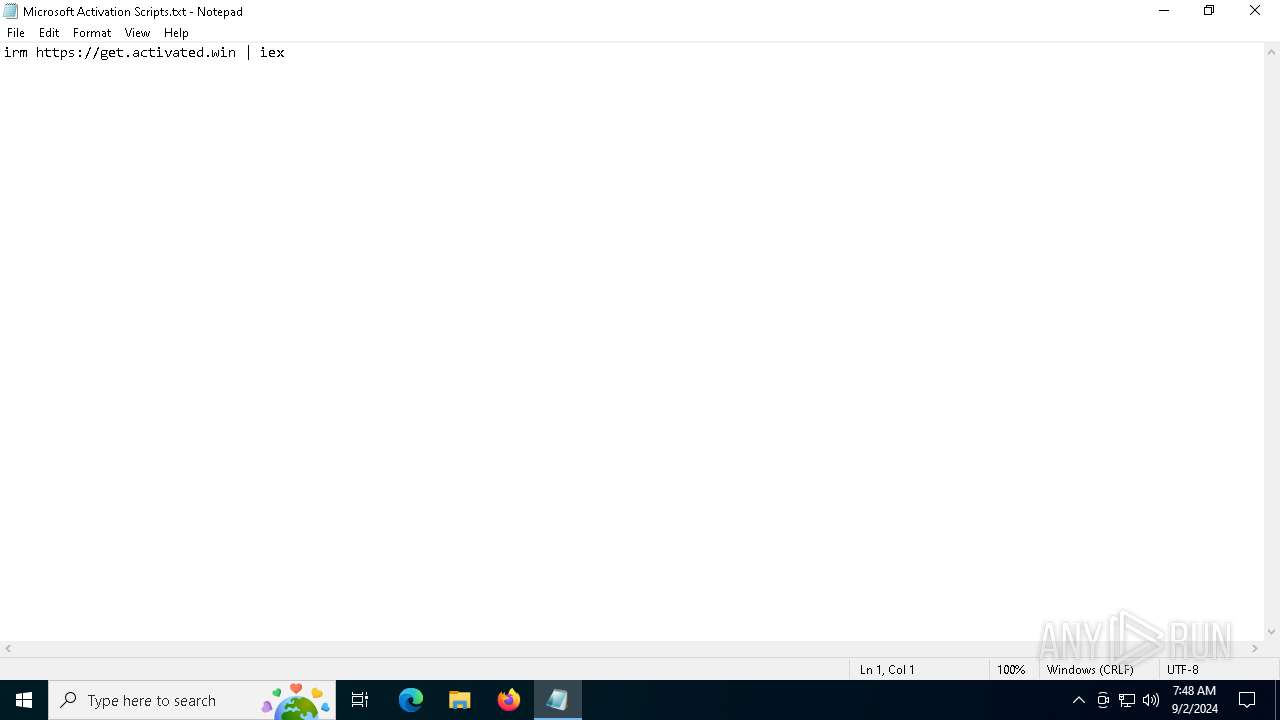
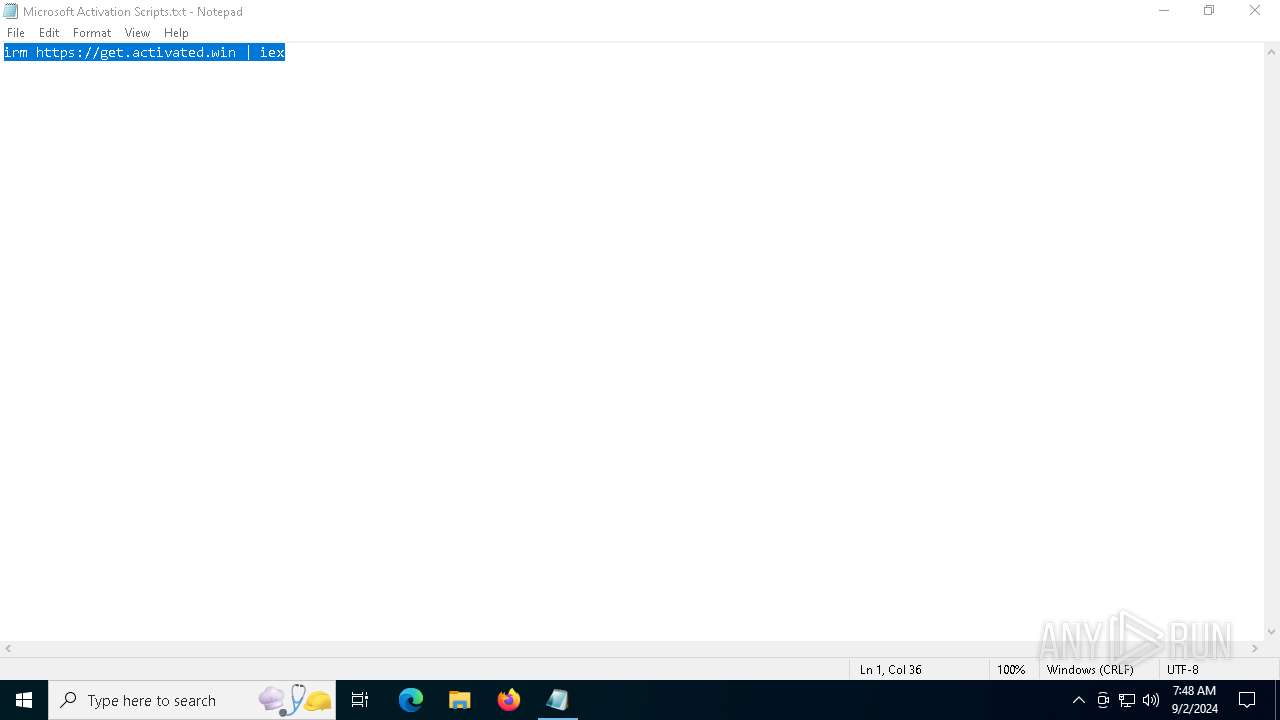
| File name: | Microsoft Activation Scripts.txt |
| Full analysis: | https://app.any.run/tasks/066b94eb-1cd2-431e-8d8c-49d48cc6838e |
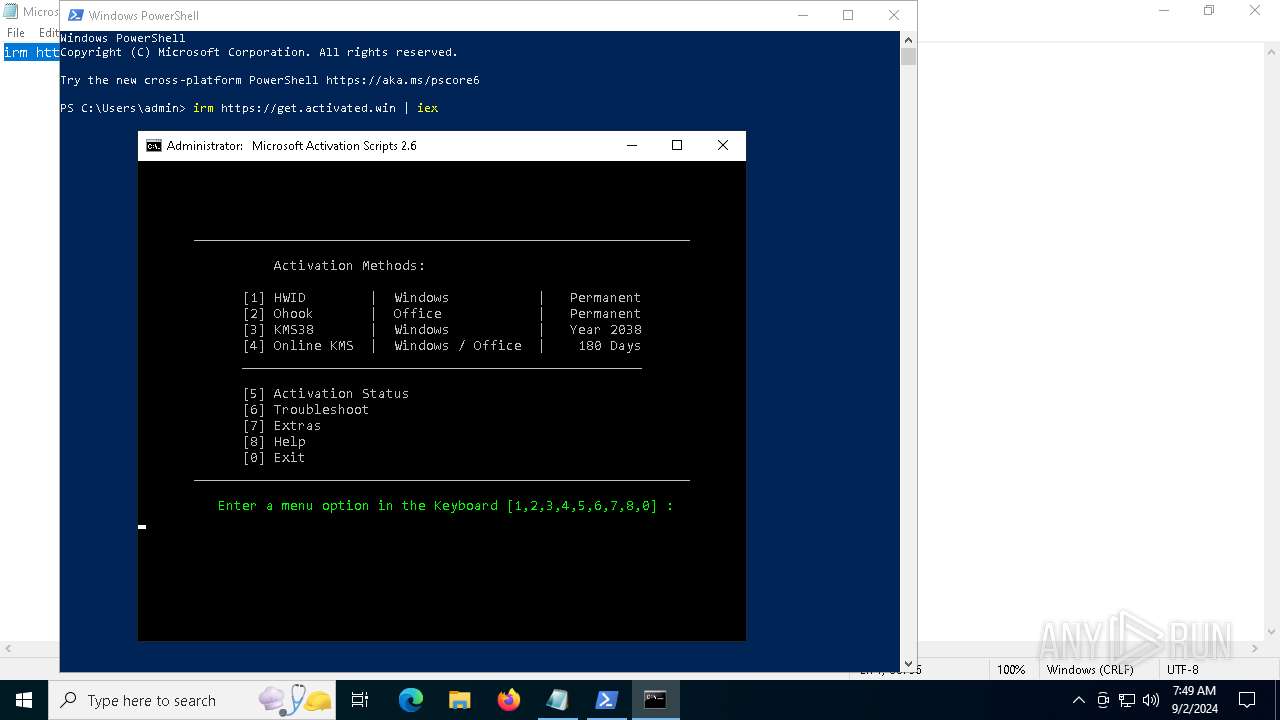
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2024, 07:48:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 206946295B10FCF003BD1BB6288EDBE0 |
| SHA1: | 504155F51C075CEDB5718BEE3AEFFB93AB80DF23 |
| SHA256: | 0FBD7D092FA230EE22935B919F783AA0D51FB03B93483C85A211076DAF2CE116 |
| SSDEEP: | 3:WIuJsTE2mMVn:WIuAmgn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6980)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 6184)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 6184)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 6980)
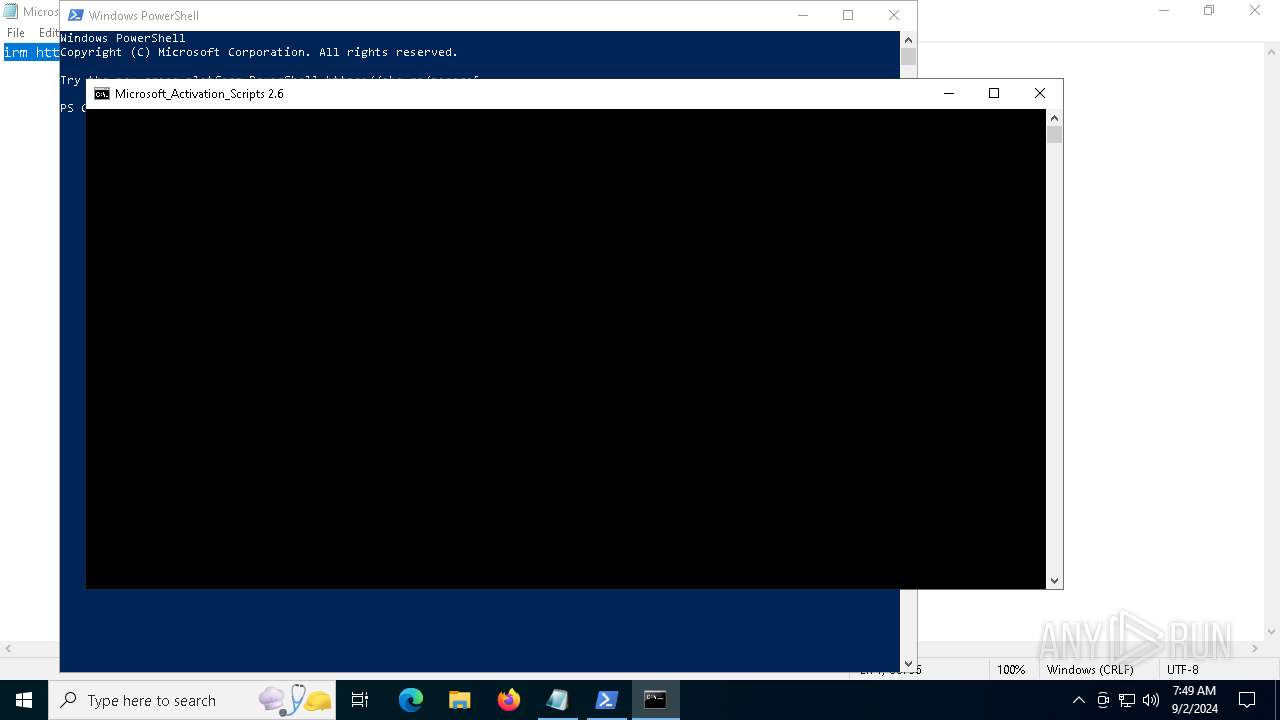
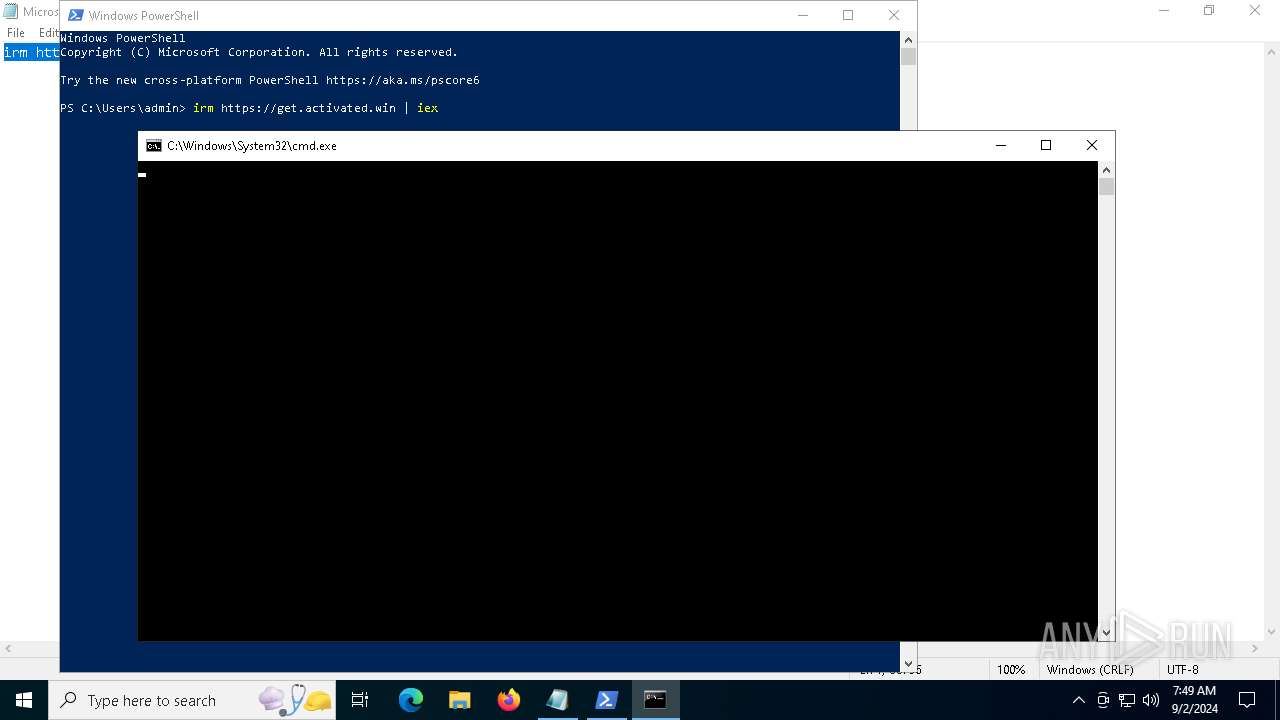
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6980)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 5128)
- powershell.exe (PID: 4132)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 7032)
Executing commands from ".cmd" file
- powershell.exe (PID: 6980)
- powershell.exe (PID: 4132)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 5128)
- cmd.exe (PID: 7032)
Starts SC.EXE for service management
- cmd.exe (PID: 5128)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 7032)
Application launched itself
- cmd.exe (PID: 5128)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 6112)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5128)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 6332)
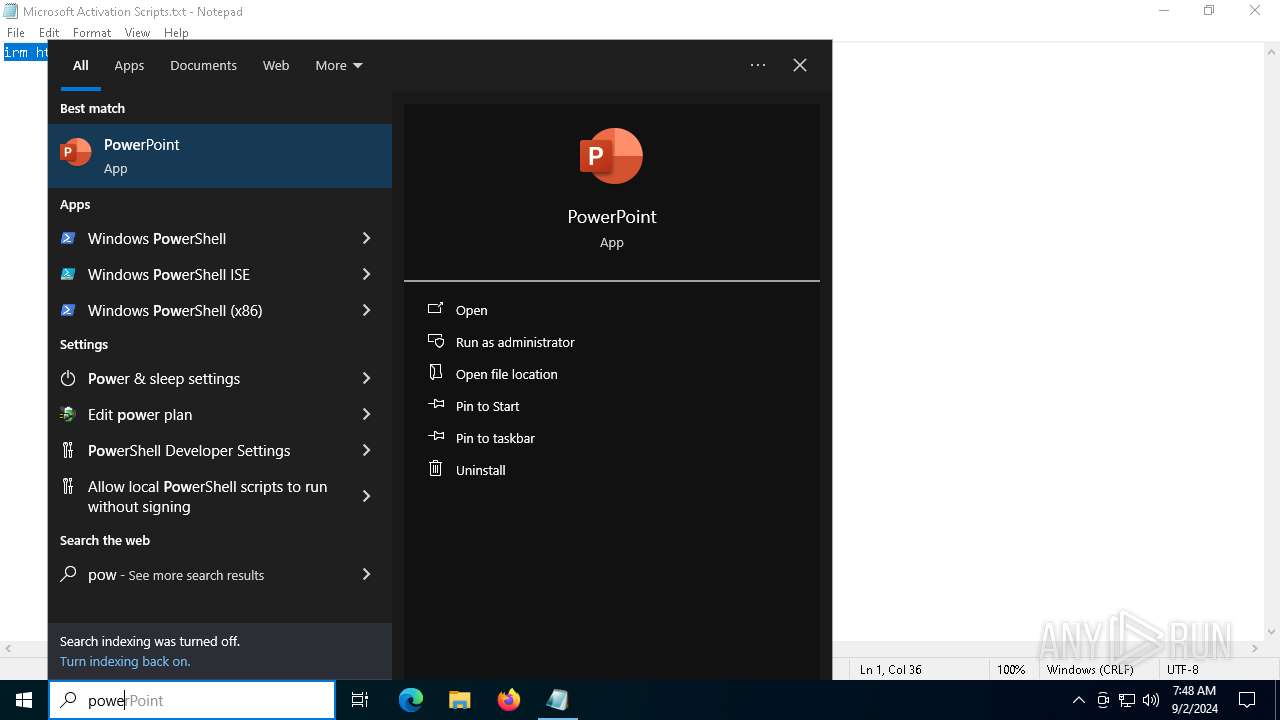
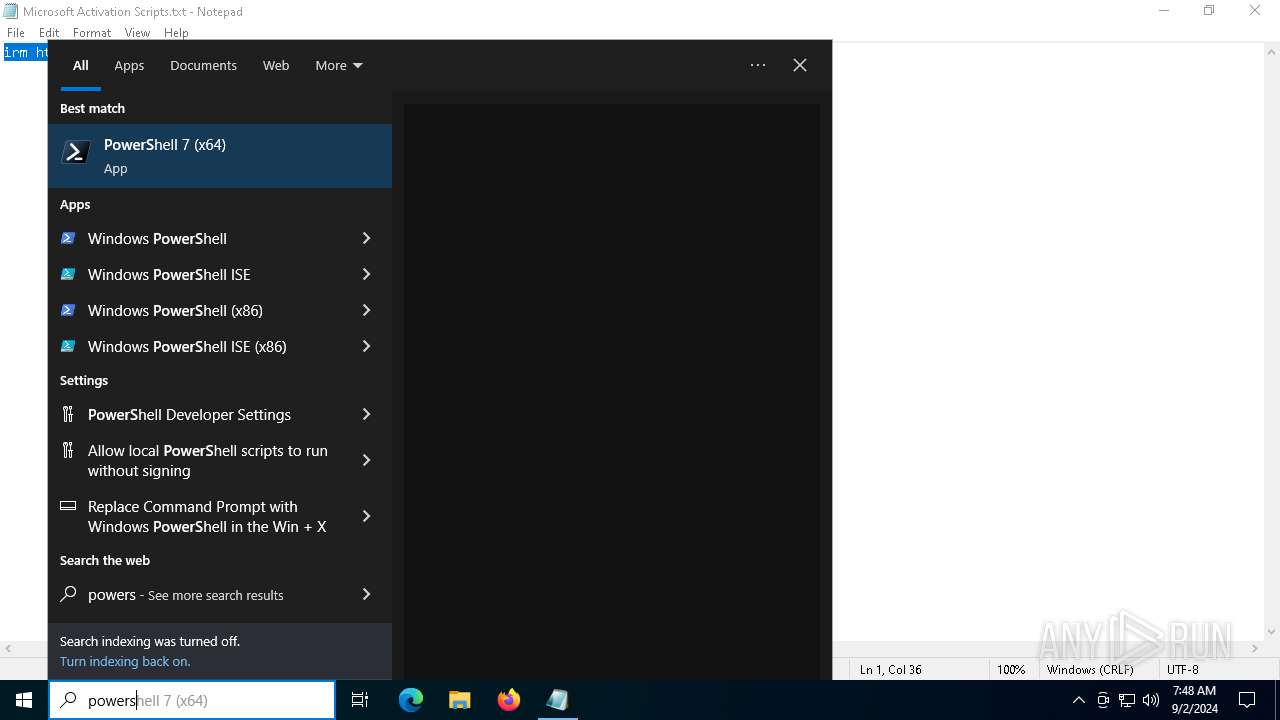
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5128)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 208)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6400)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 6332)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7032)
Hides command output
- cmd.exe (PID: 208)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 568)
- cmd.exe (PID: 4820)
- cmd.exe (PID: 3104)
- cmd.exe (PID: 6124)
- cmd.exe (PID: 3832)
- cmd.exe (PID: 568)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 6120)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 448)
- cmd.exe (PID: 4276)
- cmd.exe (PID: 4732)
- cmd.exe (PID: 5732)
- cmd.exe (PID: 2248)
- cmd.exe (PID: 4876)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 6332)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 208)
Executable content was dropped or overwritten
- Dism.exe (PID: 2524)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 208)
Process drops legitimate windows executable
- Dism.exe (PID: 2524)
The process creates files with name similar to system file names
- Dism.exe (PID: 2524)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 1752)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4820)
- cmd.exe (PID: 2248)
The process executes VB scripts
- cmd.exe (PID: 7032)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 1616)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 1616)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 1616)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 7032)
INFO
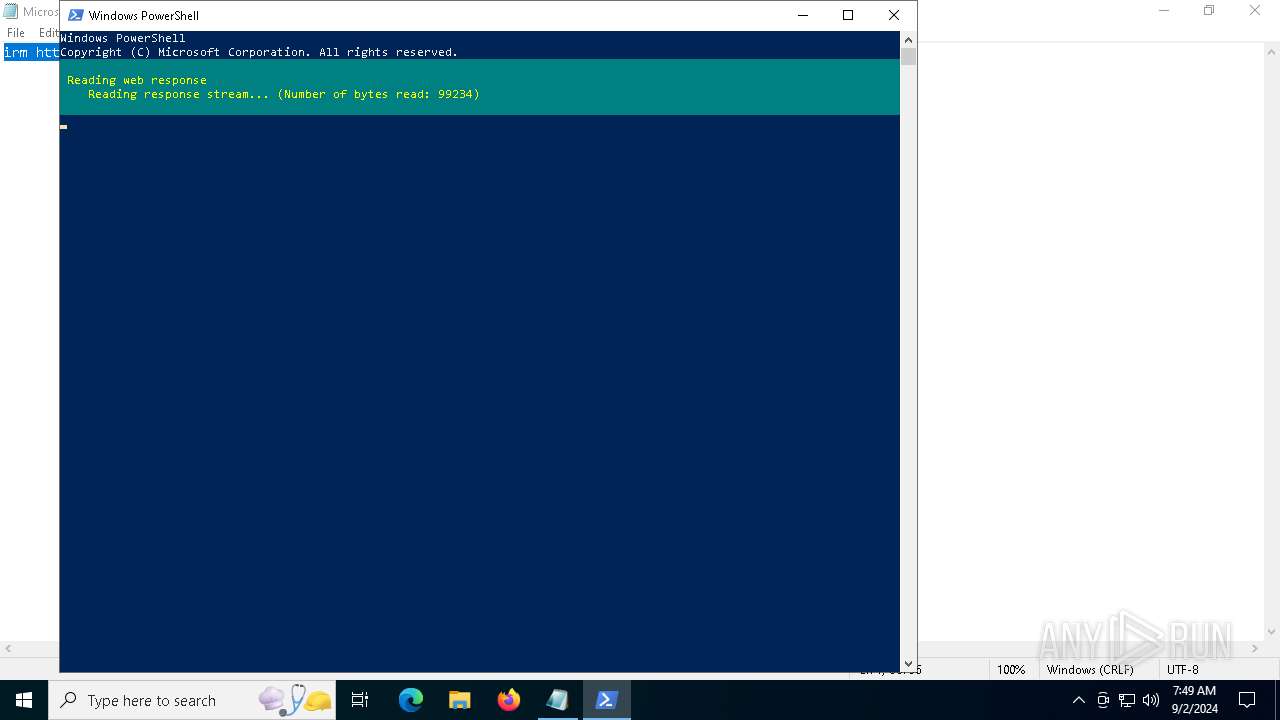
The process uses the downloaded file
- powershell.exe (PID: 6980)
- powershell.exe (PID: 4132)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6684)
- WMIC.exe (PID: 608)
- WMIC.exe (PID: 3672)
- WMIC.exe (PID: 7156)
- cscript.exe (PID: 1616)
- WMIC.exe (PID: 5724)
- WMIC.exe (PID: 1184)
- WMIC.exe (PID: 1480)
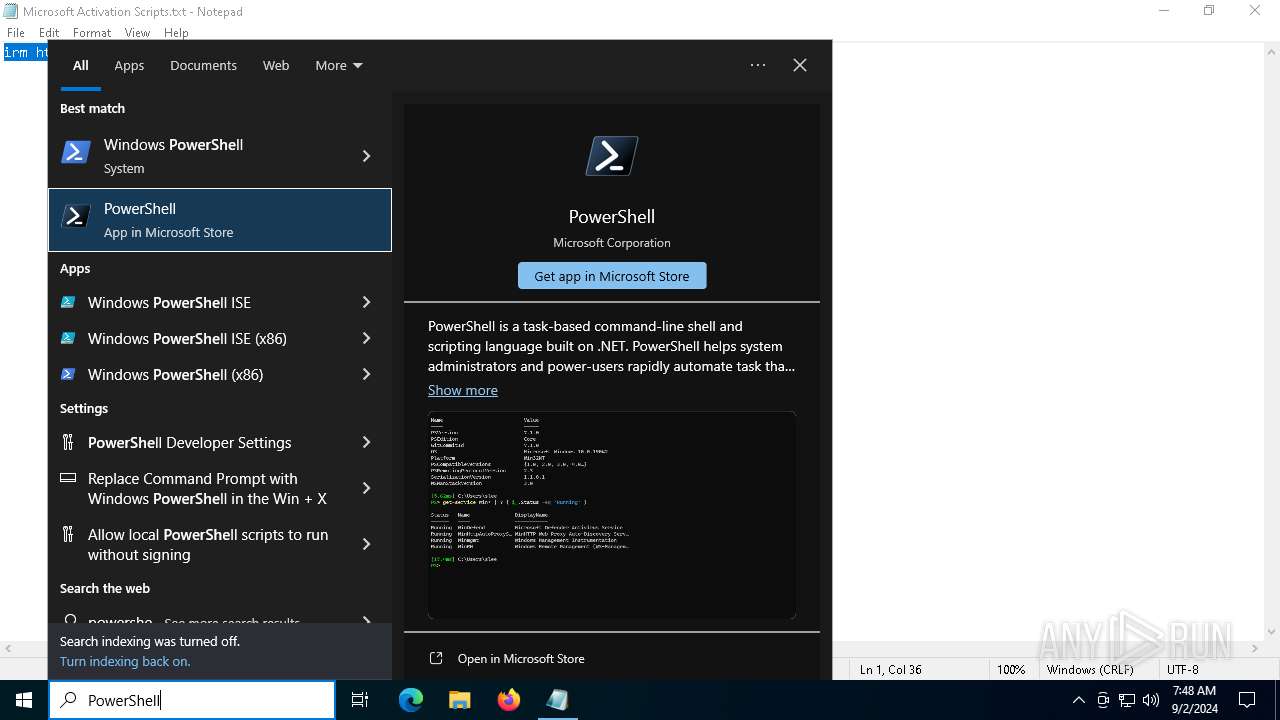
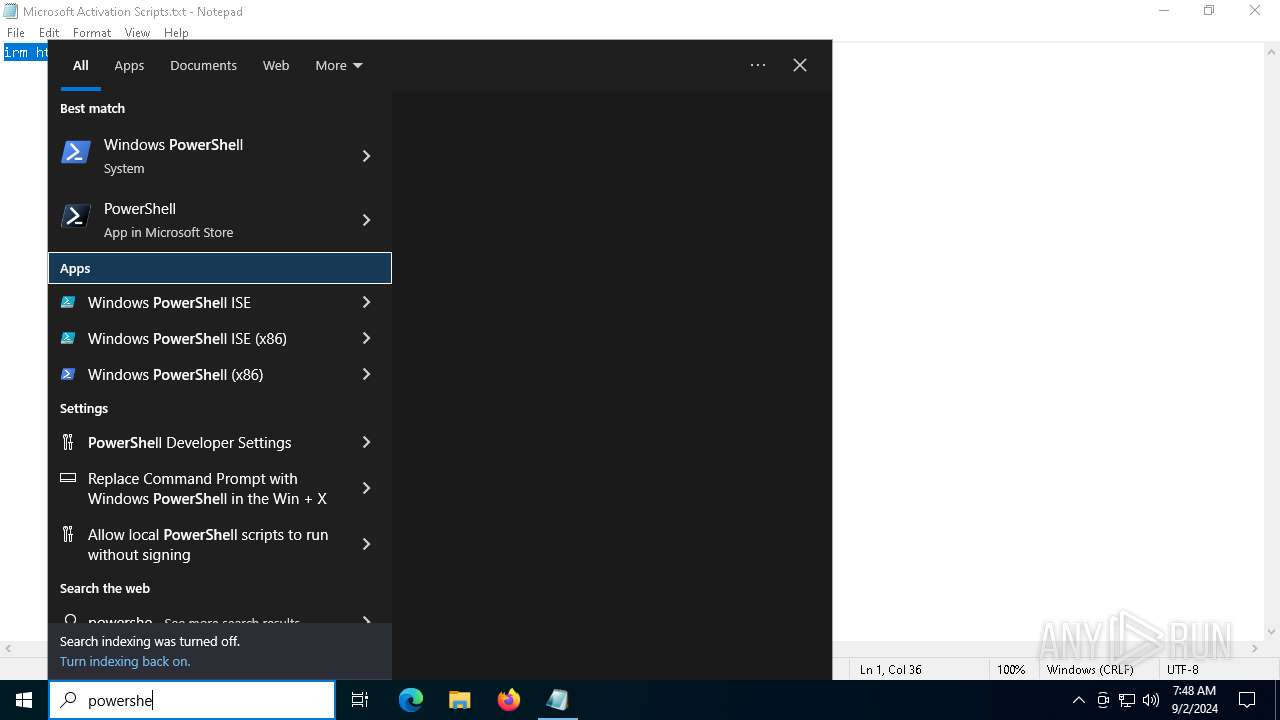
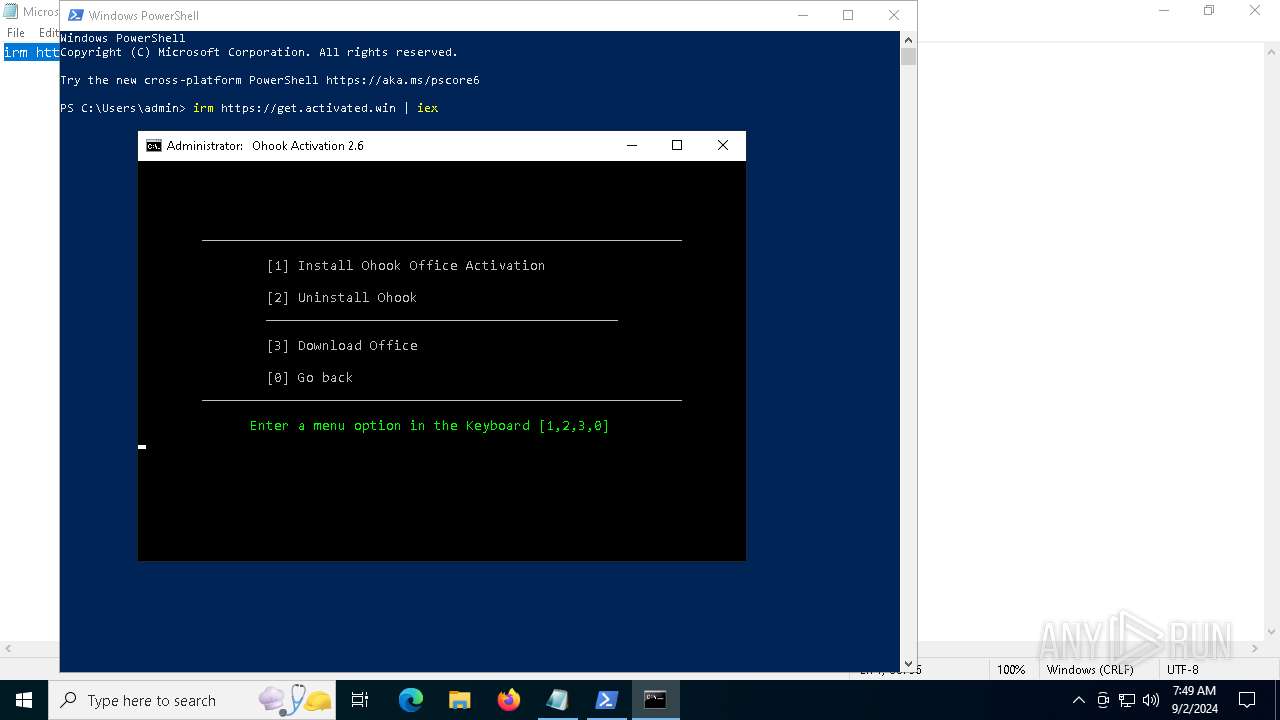
Manual execution by a user
- powershell.exe (PID: 6980)
Disables trace logs
- powershell.exe (PID: 6980)
Checks proxy server information
- powershell.exe (PID: 6980)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 6184)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6980)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 6184)
Checks operating system version
- cmd.exe (PID: 5128)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 7032)
Checks supported languages
- mode.com (PID: 6928)
- mode.com (PID: 6328)
- mode.com (PID: 6864)
- DismHost.exe (PID: 1752)
Create files in a temporary directory
- Dism.exe (PID: 2524)
Reads the computer name
- DismHost.exe (PID: 1752)
Reads Environment values
- DismHost.exe (PID: 1752)
Reads Microsoft Office registry keys
- reg.exe (PID: 6444)
- reg.exe (PID: 6208)
- reg.exe (PID: 6256)
- reg.exe (PID: 5184)
- reg.exe (PID: 4440)
- reg.exe (PID: 5484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
335
Monitored processes
207
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "MAS_43b3cd82-4596-450c-8344-3f394847c5e9.cmd" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\WINDOWS\system32\cmd.exe /c powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_43b3cd82-4596-450c-8344-3f394847c5e9.cmd') -split ':wpatest\:.*';iex ($f[1]);" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "MAS_43b3cd82-4596-450c-8344-3f394847c5e9.cmd" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | C:\WINDOWS\system32\cmd.exe /c "reg query HKLM\SOFTWARE\Microsoft\Office\ClickToRun /v InstallPath" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 568 | C:\WINDOWS\system32\cmd.exe /c reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /v TokenStore 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 568 | C:\WINDOWS\system32\cmd.exe /c "reg query HKLM\SOFTWARE\Microsoft\Office\15.0\Common\InstallRoot /v Path" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | wmic path Win32_ComputerSystem get CreationClassName /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | reg query "HKLM\SOFTWARE\Microsoft\Windows Script Host\Settings" /v Enabled | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 940 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 940 | cmd /c exit /b 0 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
60 797
Read events
60 762
Write events
35
Delete events
0
Modification events
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6980) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
50
Suspicious files
4
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:682F3F716F732F92E92554385BE3B9DA | SHA256:38645B2924FC916012DB8589373FEE51A2F7236758BB6A675B31B92BDBACC3B9 | |||
| 4132 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1b5rhxlw.2az.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\MAS_43b3cd82-4596-450c-8344-3f394847c5e9.cmd | text | |
MD5:F52AECA905CB256B5DA3B332267701EC | SHA256:05E2467EE020434FAE0B89D5881C3824AC236DFD91E0DE33452EFE3B2142FC1D | |||
| 6980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF12e1cd.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6184 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tr1aqemk.fec.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6204 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5oyj5pk4.wh0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZF5V4YB6NETU589QB4Z2.temp | binary | |
MD5:682F3F716F732F92E92554385BE3B9DA | SHA256:38645B2924FC916012DB8589373FEE51A2F7236758BB6A675B31B92BDBACC3B9 | |||
| 4132 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h0s3x2l2.fgh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2684 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wot2kyz1.yze.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6204 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hcniqjdw.v5w.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
51
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAFSnug2jwtdcrpDPi2Opi0%3D | unknown | — | — | whitelisted |
6204 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6204 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6052 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6268 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1944 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1944 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5336 | SearchApp.exe | 104.126.37.186:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
store-images.s-microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
Process | Message |
|---|---|
Dism.exe | PID=2524 TID=6952 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=2524 TID=6952 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=2524 TID=6952 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=2524 TID=6952 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=2524 TID=6952 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=2524 TID=6952 Connecting to the provider located at C:\Windows\System32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |
DismHost.exe | PID=1752 TID=5220 Disconnecting the provider store - CDISMImageSession::Final_OnDisconnect |
DismHost.exe | PID=1752 TID=5220 Encountered a loaded provider DISMLogger. - CDISMProviderStore::Internal_DisconnectProvider |
DismHost.exe | PID=1752 TID=5220 Disconnecting Provider: DISMLogger - CDISMProviderStore::Internal_DisconnectProvider |
Dism.exe | PID=2524 TID=6952 Disconnecting the provider store - CDISMImageSession::Final_OnDisconnect |