| download: | 7tt_setup.exe |
| Full analysis: | https://app.any.run/tasks/0cdf2ae1-db3f-43c4-92cb-0304d775a6f9 |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2018, 22:56:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 7DBFB79EDD97A6DCD4219412E7F1D2D8 |
| SHA1: | A70E2531B1333E58D311B4741E11A52652539AD3 |
| SHA256: | 0FB4F9DD4CFE1635D75C26789ABCC78F26BD4DDA3AA12C460F716BAE694CEFA6 |
| SSDEEP: | 24576:y/WN6Ux6tpSXrIZuSLE367MB7QbaGNBPBvgeklxOAUZQpTTwmzHydQ/IAMVAQiPH:yIl6HYrIsSLEK7M2baqZ5geklpUZQpTR |
MALICIOUS
Loads dropped or rewritten executable
- 7tt_setup.exe (PID: 3484)
- explorer.exe (PID: 1676)
Runs injected code in another process
- 7+ Taskbar Tweaker.exe (PID: 1988)
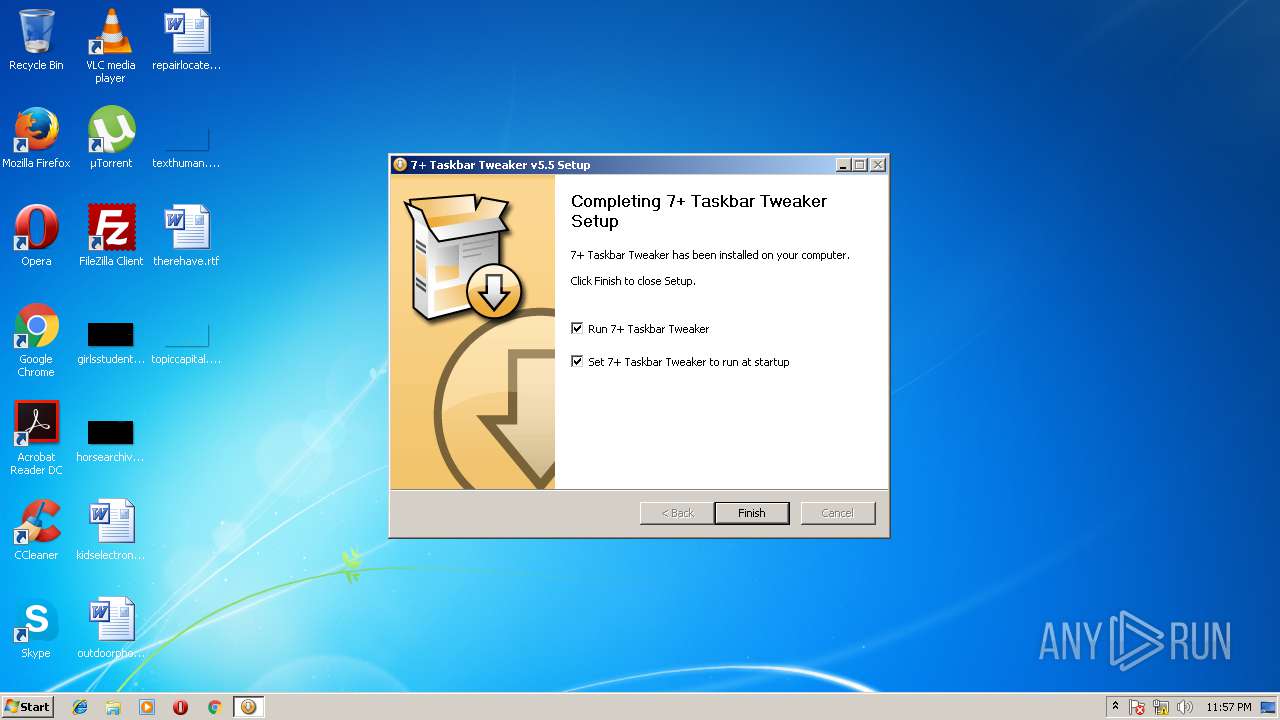
Changes the autorun value in the registry
- 7tt_setup.exe (PID: 3484)
Application was dropped or rewritten from another process
- 7+ Taskbar Tweaker.exe (PID: 1988)
Application was injected by another process
- explorer.exe (PID: 1676)
SUSPICIOUS
Executable content was dropped or overwritten
- 7tt_setup.exe (PID: 3484)
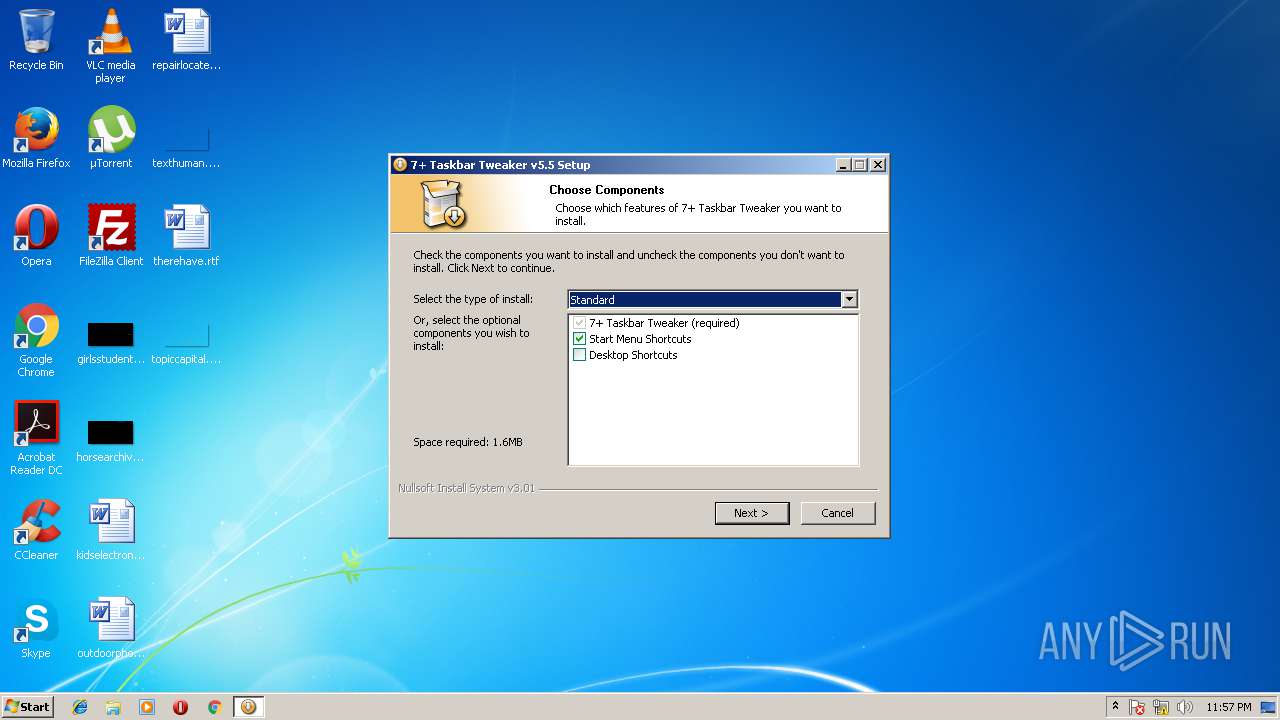
Creates a software uninstall entry
- 7tt_setup.exe (PID: 3484)
Creates files in the user directory
- 7tt_setup.exe (PID: 3484)
INFO
Dropped object may contain URL's
- 7tt_setup.exe (PID: 3484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 50176 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x344a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.5.0.0 |
| ProductVersionNumber: | 5.5.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
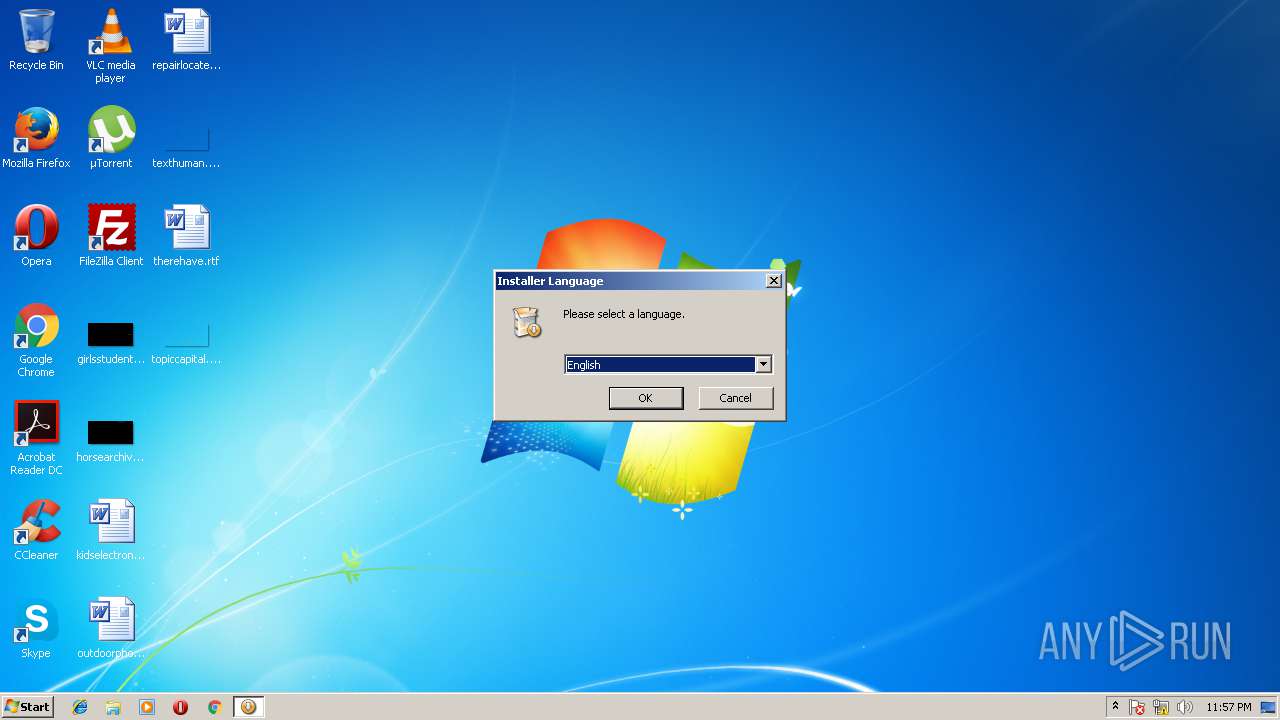
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | RaMMicHaeL |
| FileDescription: | 7+ Taskbar Tweaker |
| FileVersion: | 5.5 |
| LegalCopyright: | http://rammichael.com/ |
| ProductName: | 7+ Taskbar Tweaker |
| ProductVersion: | 5.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:48 |
| Detected languages: |
|
| CompanyName: | RaMMicHaeL |
| FileDescription: | 7+ Taskbar Tweaker |
| FileVersion: | 5.5 |
| LegalCopyright: | http://rammichael.com/ |
| ProductName: | 7+ Taskbar Tweaker |
| ProductVersion: | 5.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000061F1 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47707 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.97456 |
.ndata | 0x0002B000 | 0x0002D000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00058000 | 0x0000A87C | 0x0000AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22825 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27564 | 1187 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.61959 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.84061 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.16608 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.91942 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.42186 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.58096 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.74963 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.01957 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
103 | 2.73226 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
32
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1988 | "C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\7+ Taskbar Tweaker.exe" | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\7+ Taskbar Tweaker.exe | explorer.exe | ||||||||||||
User: admin Company: RaMMicHaeL Integrity Level: MEDIUM Description: 7+ Taskbar Tweaker Exit code: 0 Version: 5.5 Modules
| |||||||||||||||
| 3484 | "C:\Users\admin\AppData\Local\Temp\7tt_setup.exe" | C:\Users\admin\AppData\Local\Temp\7tt_setup.exe | explorer.exe | ||||||||||||
User: admin Company: RaMMicHaeL Integrity Level: MEDIUM Description: 7+ Taskbar Tweaker Exit code: 0 Version: 5.5 Modules
| |||||||||||||||
Total events
1 209
Read events
1 137
Write events
71
Delete events
1
Modification events
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\7gg_frghc.rkr |
Value: 000000000000000000000000A3110000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000A0000000E000000D5930A000400000001000000190801004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000000000000000000000000230000000000000000000000000000000000000000000000000000002A0C580260E9180213005802E20B58026FA9A5750600000005000000E20B580230B5580204E91802E8AAA5757B030119F8E8180200EB180230B55802000000000500000001000000DCE918026229A8757B03011930B5580206000000C80C58020000000000EB180208EB180210A65802CC0A580210000000000000000000000000000000000000000600000000000000230000006C61746E64666C740000000040000000AC54A57500000000C054A5757B03011930B55802000000000000000000000000E00B580230B55802ACE9183138EE18023F0400009021230038EA18021100000010471E0008471E00000000003F040000D6160E747B03011928EA0000150DB2ADD8E918028291E67528EA1802448B0000010DB2ADECE91802B69CE675488B25004C06000004EA1802B886250010EA1802789CE6753691E67540B018761100000010471E0008471E00D88625007CEA0000C10EB2AD2CEA18028291E6757CEA180230EA18022795E67500000000448B250058EA1802CD94E675448B250004EB1802B8862500E194E67500000000B886250004EB180260EA180200000000070000003FE402007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000005802EC0A5802D0E818025869A67500000000D0075802F0E818020B8CA5750100000000000000537AA575560401020020000000000000010000003CE918023617DB7556040102100858020500000000000000FFFFFFFFD00758020000000038E9180264E9180200000000000000000000000090E9180218EC2300000000004091A4750900800188E918023559DB7556040102D09028000500000070E91802506AA6751CC0AA7501000000EF7AA575560401021D0000000020000088E918026359DB7590E918020000000000000000560401024066A07501000000F4E91802A13673750000000000000000C80B2300F4E91802B8367375E09276750000000000001B00D090280000000000F0E91802070014006AC2C1C10000000000000000CF6771758890280001000000C8902800FCE91802E82C0677C80B2300CF67717518EC1802C89028001100000010471E0008471E00000000007CEA0000C10EB2AD2CEA18028291E6757CEA180230EA18022795E67500000000448B250058EA1802CD94E675448B250004EB1802B8862500E194E67500000000B886250004EB180260EA180200000000070000003FE402007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000005802EC0A5802D0E818025869A67500000000D0075802F0E818020B8CA5750100000000000000537AA575560401020020000000000000010000003CE918023617DB7556040102100858020500000000000000FFFFFFFFD00758020000000038E9180264E9180200000000000000000000000090E9180218EC2300000000004091A4750900800188E918023559DB7556040102D09028000500000070E91802506AA6751CC0AA7501000000EF7AA575560401021D0000000020000088E918026359DB7590E918020000000000000000560401024066A07501000000F4E91802A13673750000000000000000C80B2300F4E91802B8367375E09276750000000000001B00D090280000000000F0E91802070014006AC2C1C10000000000000000CF6771758890280001000000C8902800FCE91802E82C0677C80B2300CF67717518EC1802C89028001100000010471E0008471E00000000007CEA0000C10EB2AD2CEA18028291E6757CEA180230EA18022795E67500000000448B250058EA1802CD94E675448B250004EB1802B8862500E194E67500000000B886250004EB180260EA1802 | |||
| (PID) Process: | (3484) 7tt_setup.exe | Key: | HKEY_CURRENT_USER\Software\7 Taskbar Tweaker |
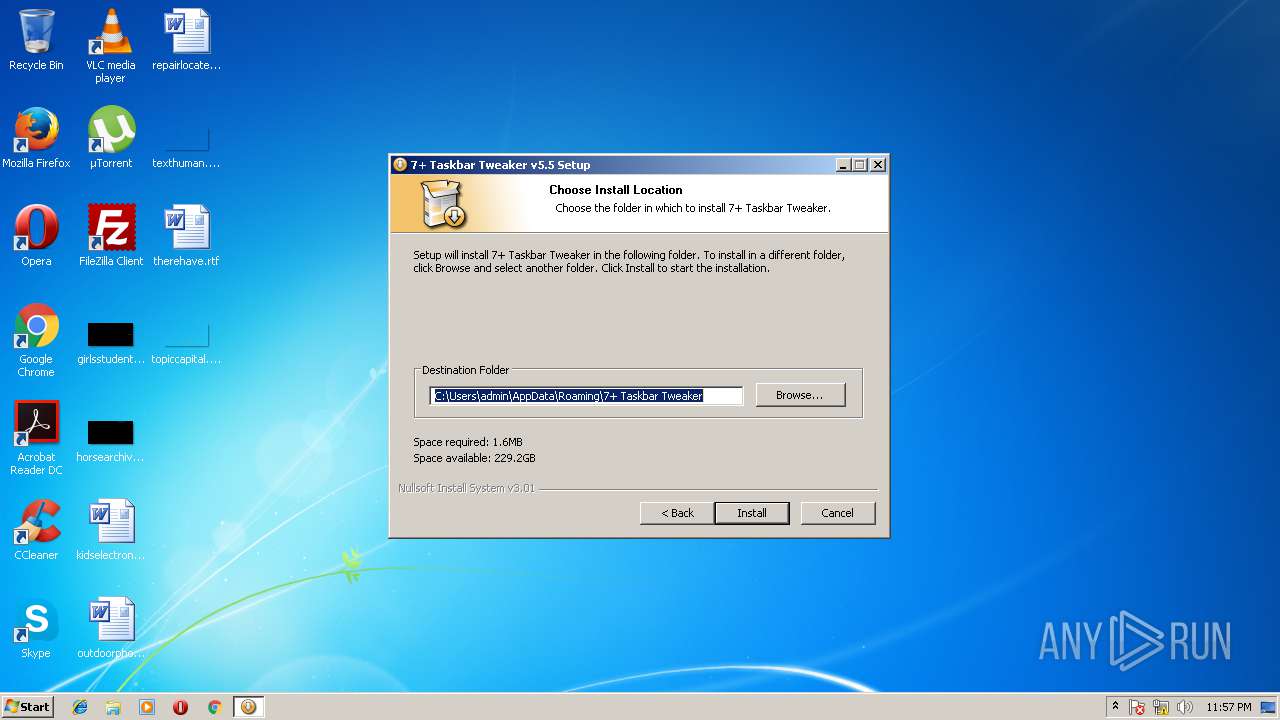
| Operation: | write | Name: | install_dir |
Value: C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker | |||
| (PID) Process: | (3484) 7tt_setup.exe | Key: | HKEY_CURRENT_USER\Software\7 Taskbar Tweaker |
| Operation: | write | Name: | language |
Value: 1033 | |||
| (PID) Process: | (3484) 7tt_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\7 Taskbar Tweaker |
| Operation: | write | Name: | DisplayName |
Value: 7+ Taskbar Tweaker v5.5 | |||
| (PID) Process: | (3484) 7tt_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\7 Taskbar Tweaker |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\uninstall.exe" | |||
| (PID) Process: | (3484) 7tt_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\7 Taskbar Tweaker |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker | |||
| (PID) Process: | (3484) 7tt_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\7 Taskbar Tweaker |
| Operation: | write | Name: | Publisher |
Value: RaMMicHaeL | |||
| (PID) Process: | (3484) 7tt_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\7 Taskbar Tweaker |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\7+ Taskbar Tweaker.exe | |||
| (PID) Process: | (3484) 7tt_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\7 Taskbar Tweaker |
| Operation: | write | Name: | DisplayVersion |
Value: 5.5 | |||
Executable files
7
Suspicious files
0
Text files
94
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\inject.dll | executable | |
MD5:— | SHA256:— | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\help\nl-NL.chm | chm | |
MD5:— | SHA256:— | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\help\en-US.chm | chm | |
MD5:— | SHA256:— | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\help\es-VE.chm | chm | |
MD5:— | SHA256:— | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\help\fi-FI.chm | chm | |
MD5:— | SHA256:— | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\help\fr-FR.chm | chm | |
MD5:— | SHA256:— | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\help\tr-TR.chm | chm | |
MD5:— | SHA256:— | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\help\zh-CN.chm | chm | |
MD5:— | SHA256:— | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Local\Temp\nssF736.tmp\System.dll | executable | |
MD5:17ED1C86BD67E78ADE4712BE48A7D2BD | SHA256:BD046E6497B304E4EA4AB102CAB2B1F94CE09BDE0EEBBA4C59942A732679E4EB | |||
| 3484 | 7tt_setup.exe | C:\Users\admin\AppData\Local\Temp\nssF736.tmp\modern-header.bmp | image | |
MD5:583C38FB0F5AF5FE584D9A9B01D6A3E7 | SHA256:4C9E804CE1A391F8E603B7B9C732A6529C1E81BE4D12F125C8562EA9D49095C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1988 | 7+ Taskbar Tweaker.exe | POST | — | 148.251.139.228:80 | http://rammichael.com/downloads/7tt_setup.exe?version&changelog=5.5 | DE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1988 | 7+ Taskbar Tweaker.exe | 148.251.139.228:80 | rammichael.com | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rammichael.com |
| malicious |