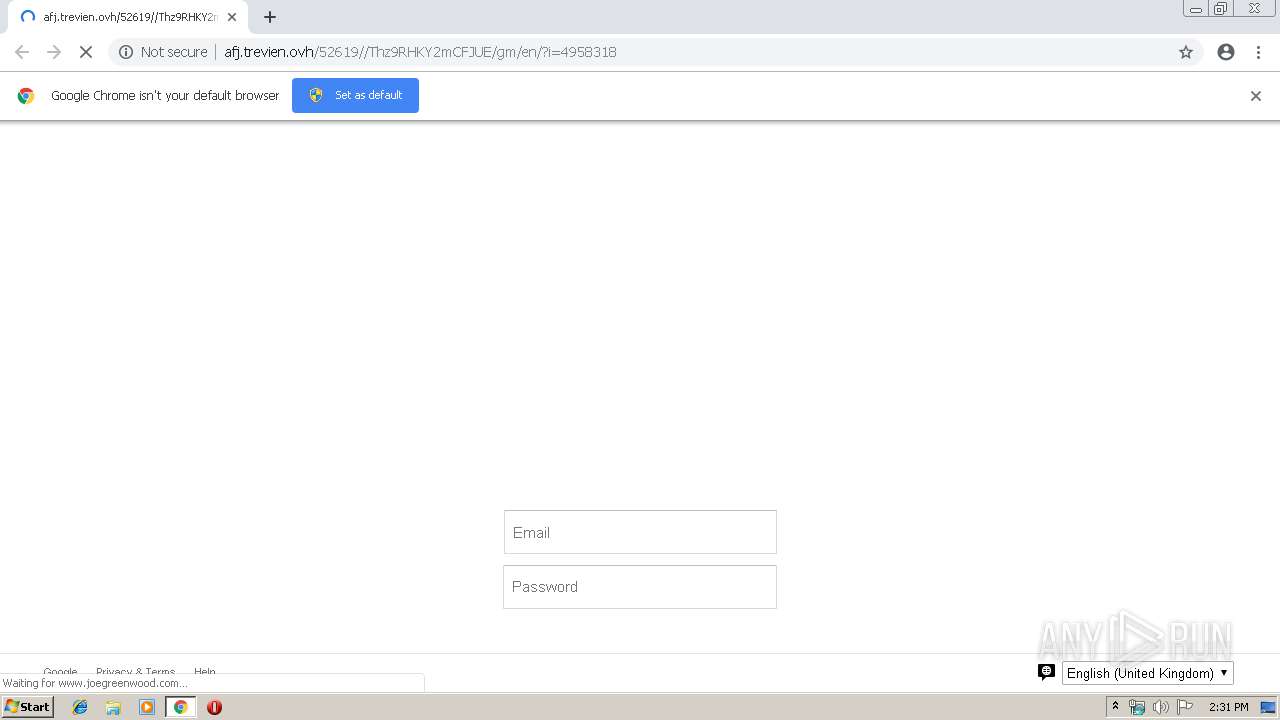
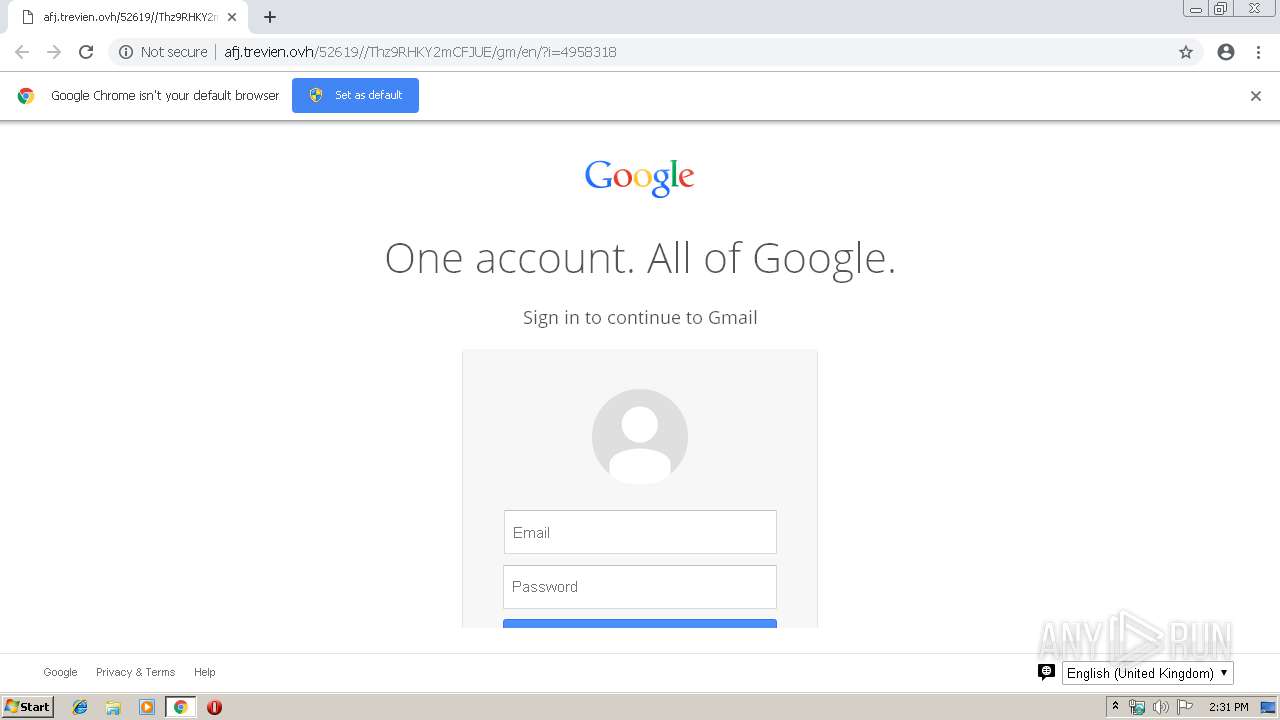
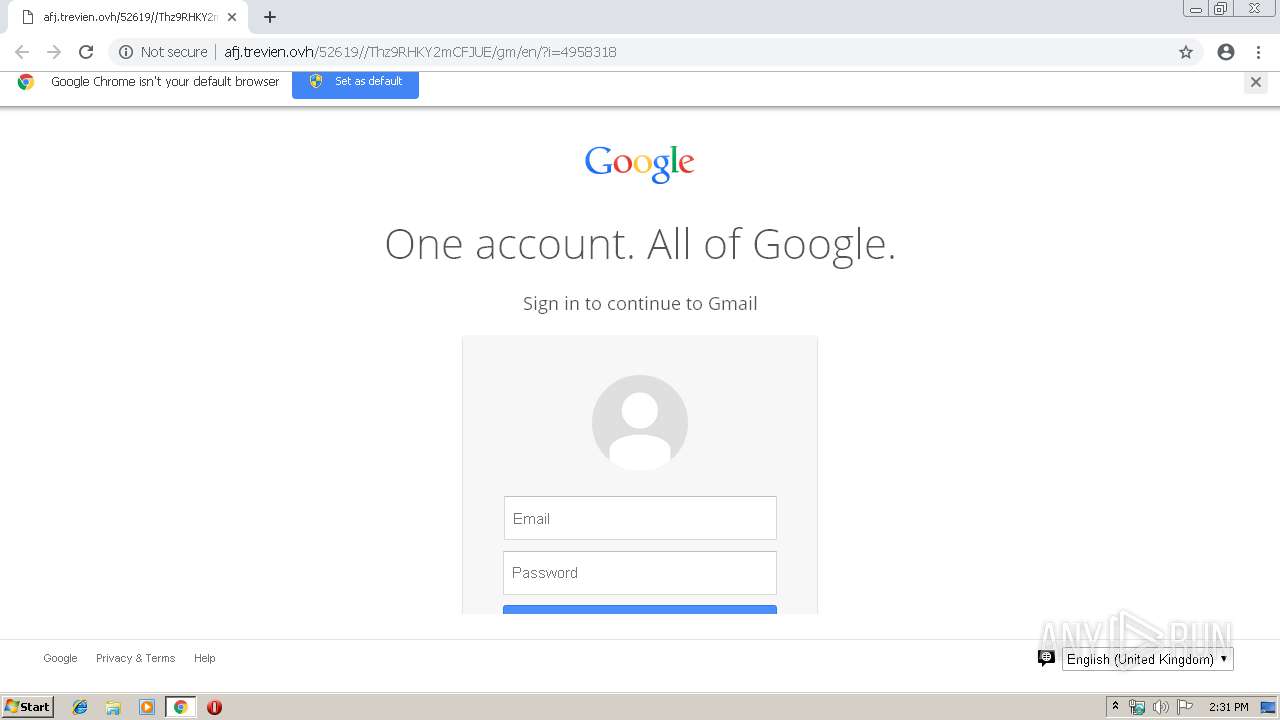
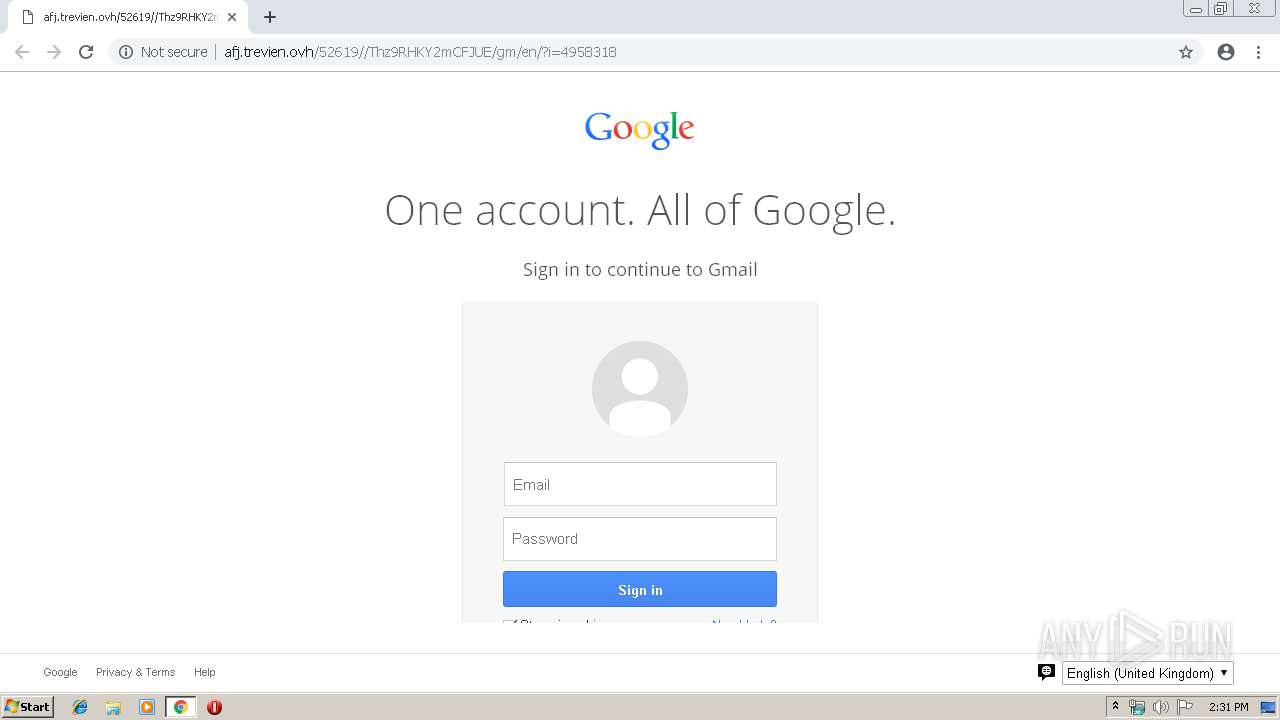
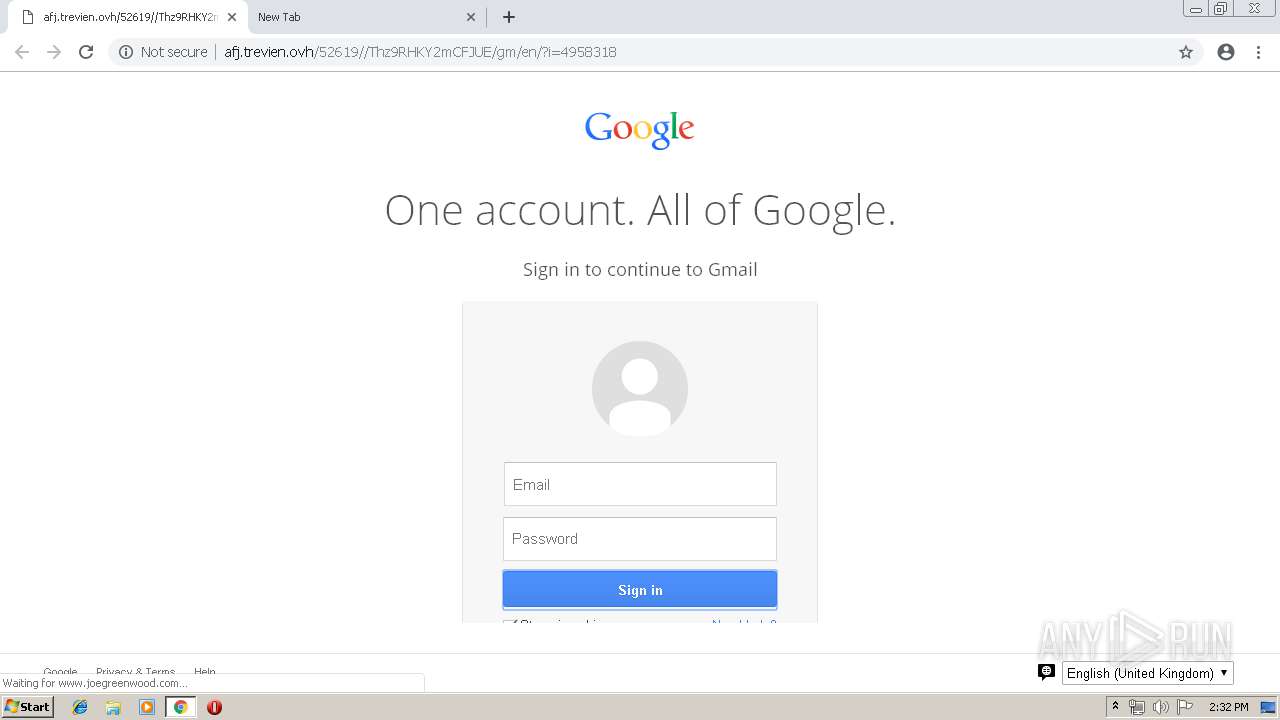
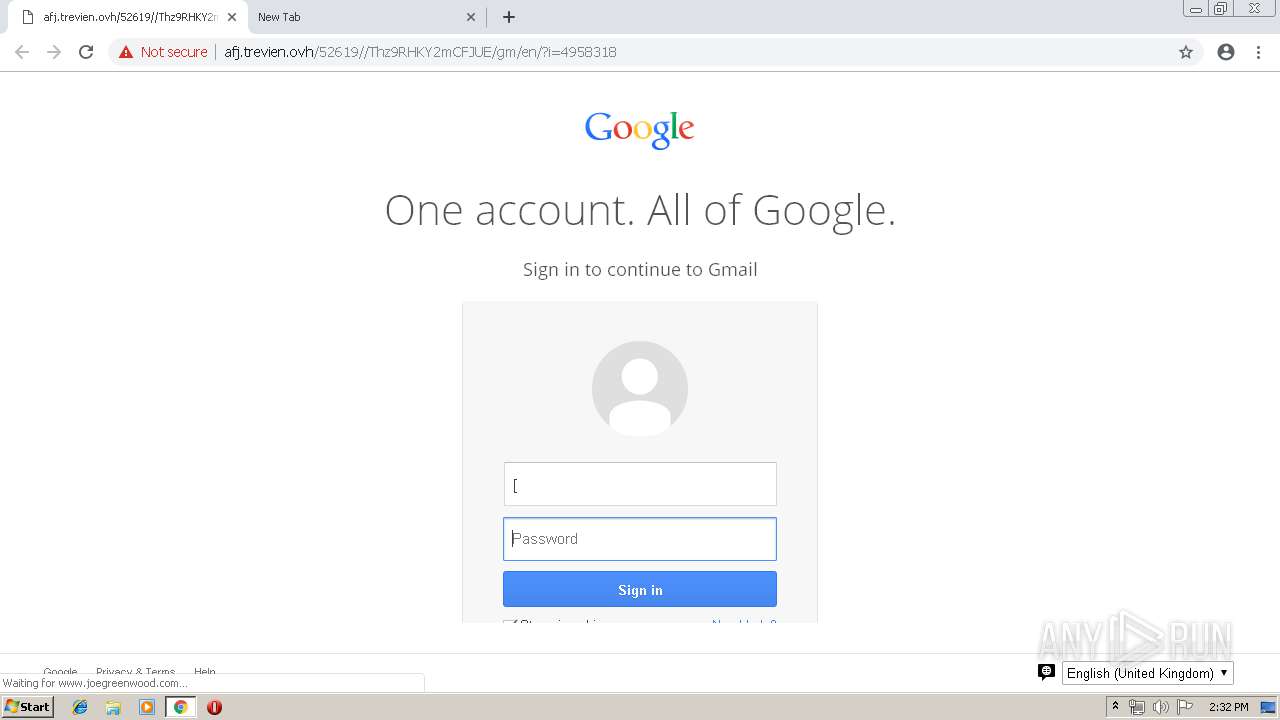
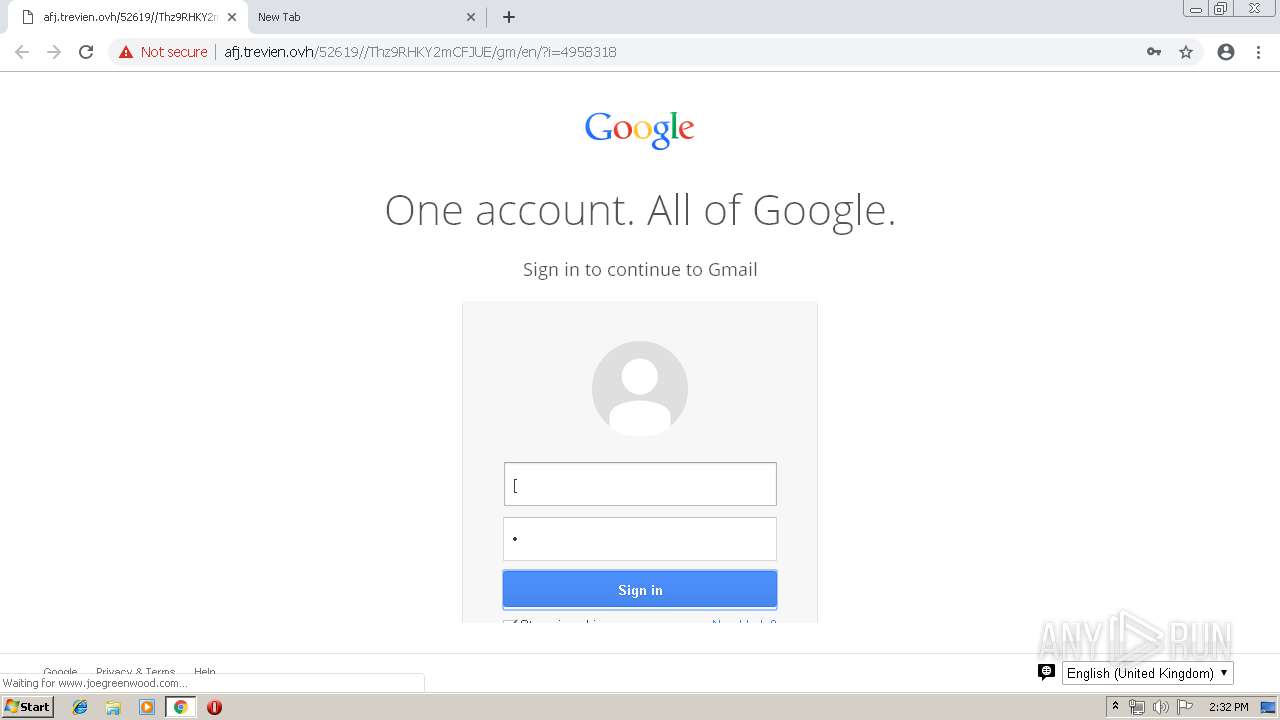
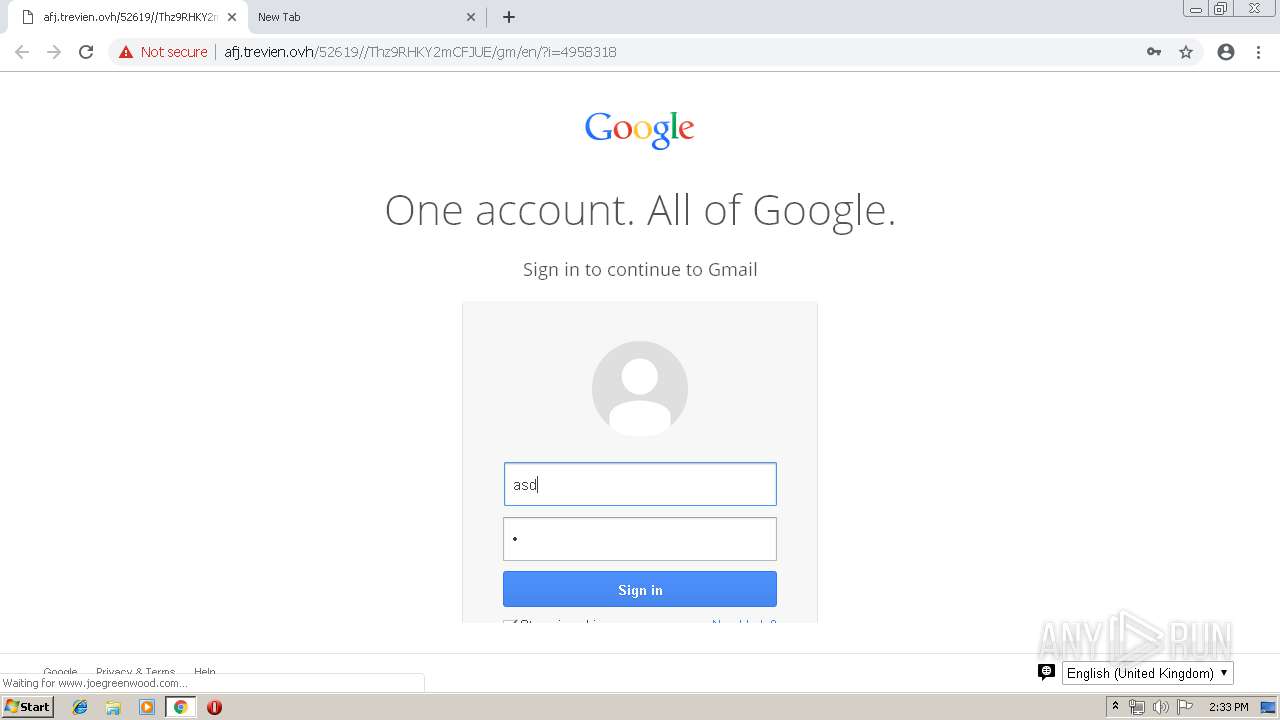
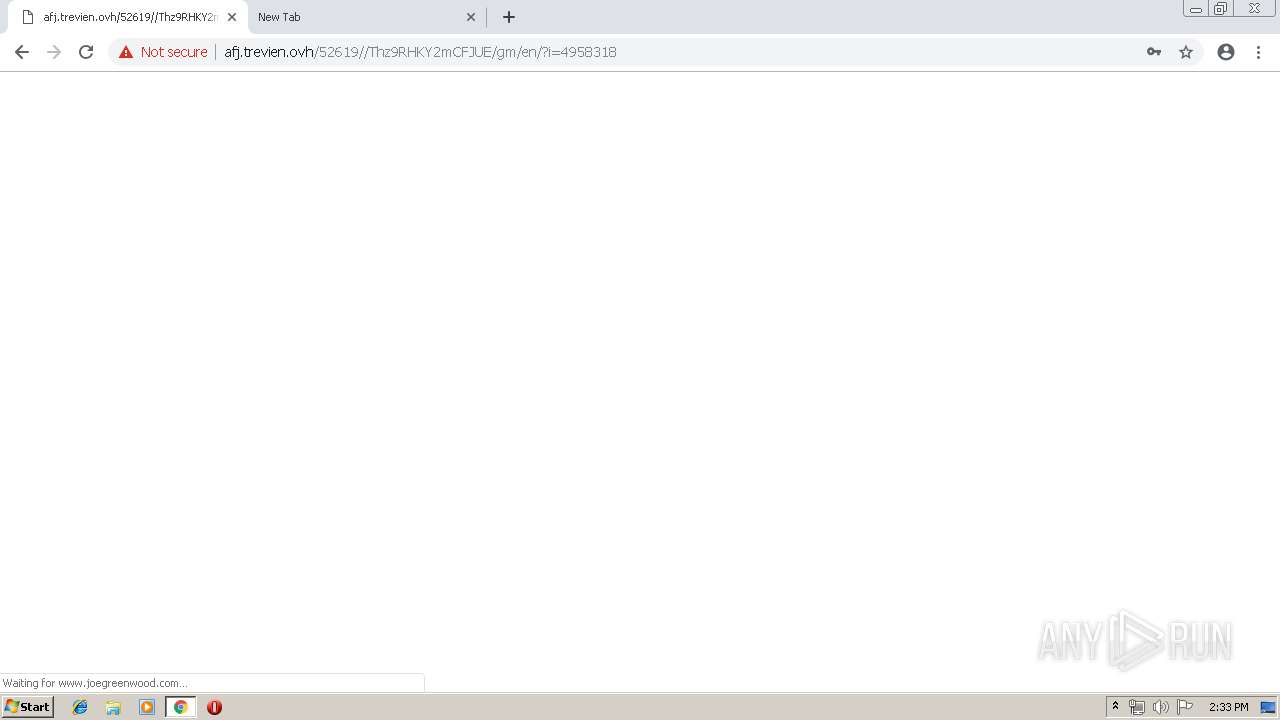
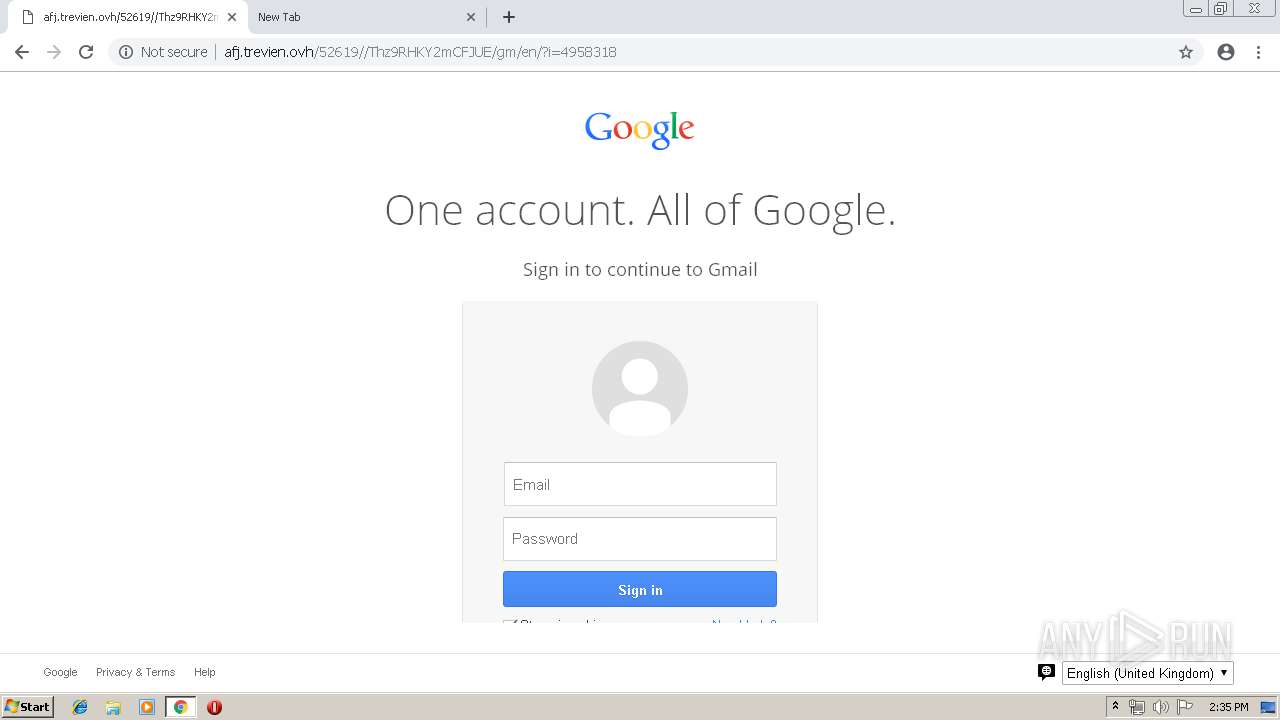
| URL: | http://afj.trevien.ovh/52619//Thz9RHKY2mCFJUE/gm/en/?i=4958318 |
| Full analysis: | https://app.any.run/tasks/60c877f8-1632-4841-ae2c-114b55a121c1 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 14:30:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9FBA4494EEF59407A8485F058A7053DE |
| SHA1: | 17B4C333F5D56366C9E4FB43D924EAE05CD06A2F |
| SHA256: | 0F909A9754EEA05FA61CB42AD9F64BB43BA52A8A43B61323F24903579DAFB4D0 |
| SSDEEP: | 3:N1KfTNH8CTTGc8XH92S4Tn:CbNl62S2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
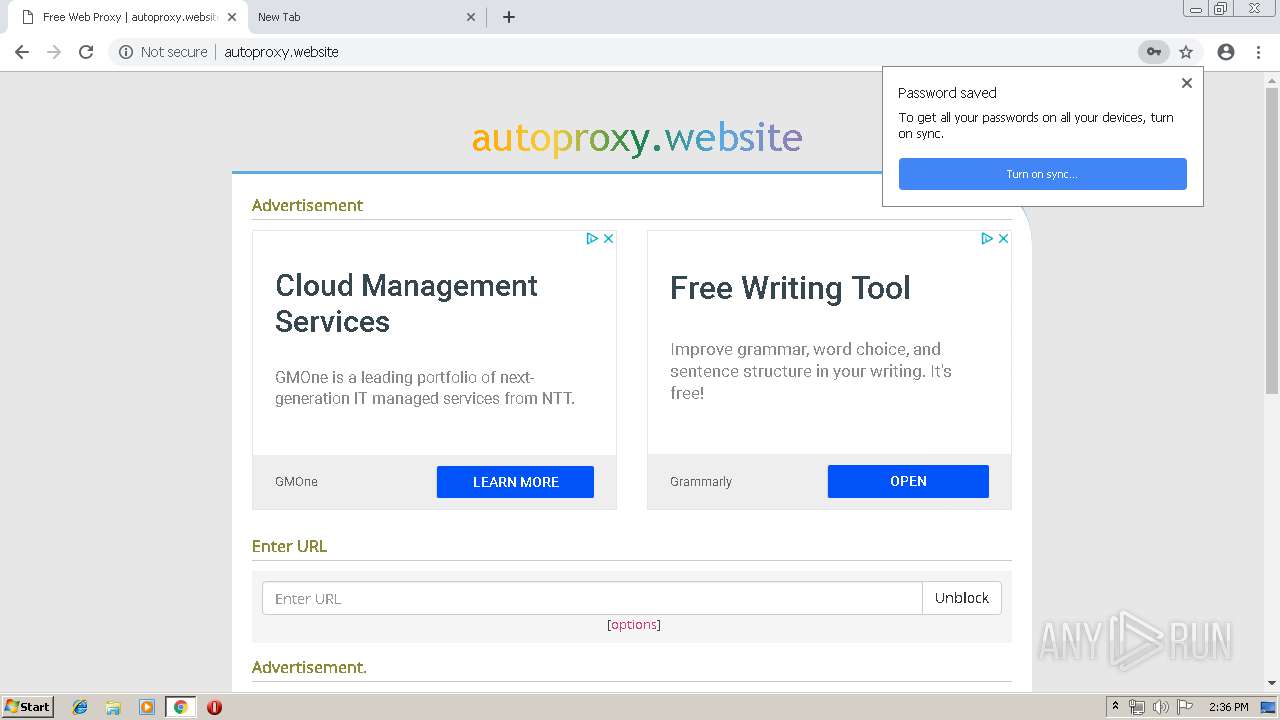
Modifies files in Chrome extension folder
- chrome.exe (PID: 2712)
INFO
Application launched itself
- chrome.exe (PID: 2712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4214815521643006567 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4214815521643006567 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5420683437387595308 --mojo-platform-channel-handle=1512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15115089148686377301 --mojo-platform-channel-handle=3716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7164262105981903010 --mojo-platform-channel-handle=2728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5905755432690978347 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5905755432690978347 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=759442959885748760 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=759442959885748760 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11955242351071359232 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11955242351071359232 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --service-pipe-token=660373475742593076 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=660373475742593076 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,10010276139939924636,14124210703773309779,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2771211536395869137 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2771211536395869137 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://afj.trevien.ovh/52619//Thz9RHKY2mCFJUE/gm/en/?i=4958318 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
578
Read events
468
Write events
105
Delete events
5
Modification events
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2712-13197652269053375 |
Value: 259 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
124
Text files
180
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0e474fac-b40b-4863-b1c4-eb99cea9edbe.tmp | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2712 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
67
DNS requests
31
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
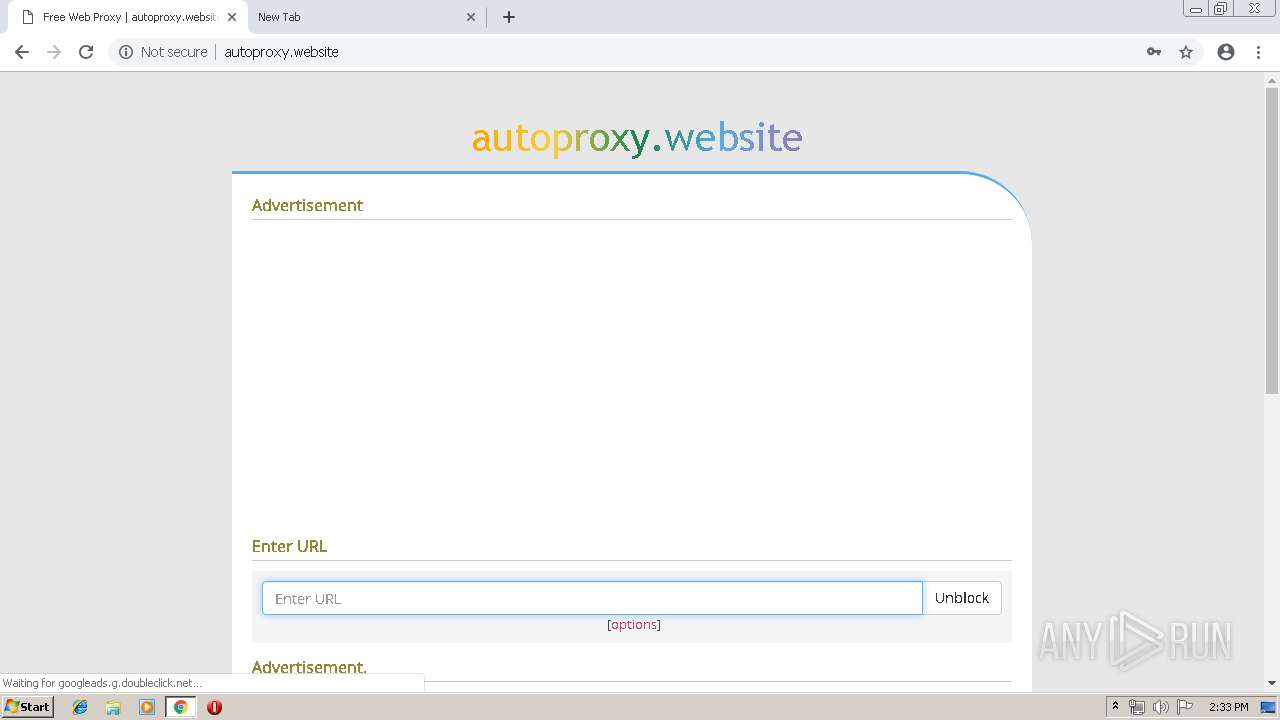
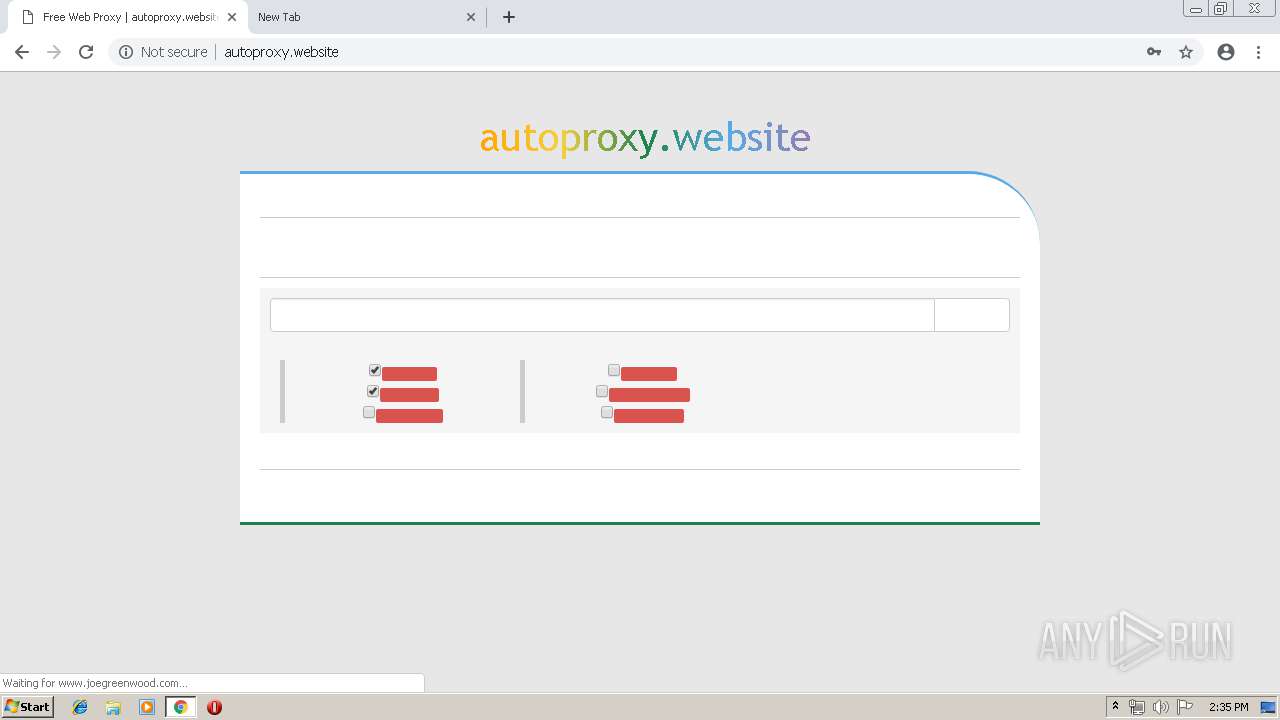
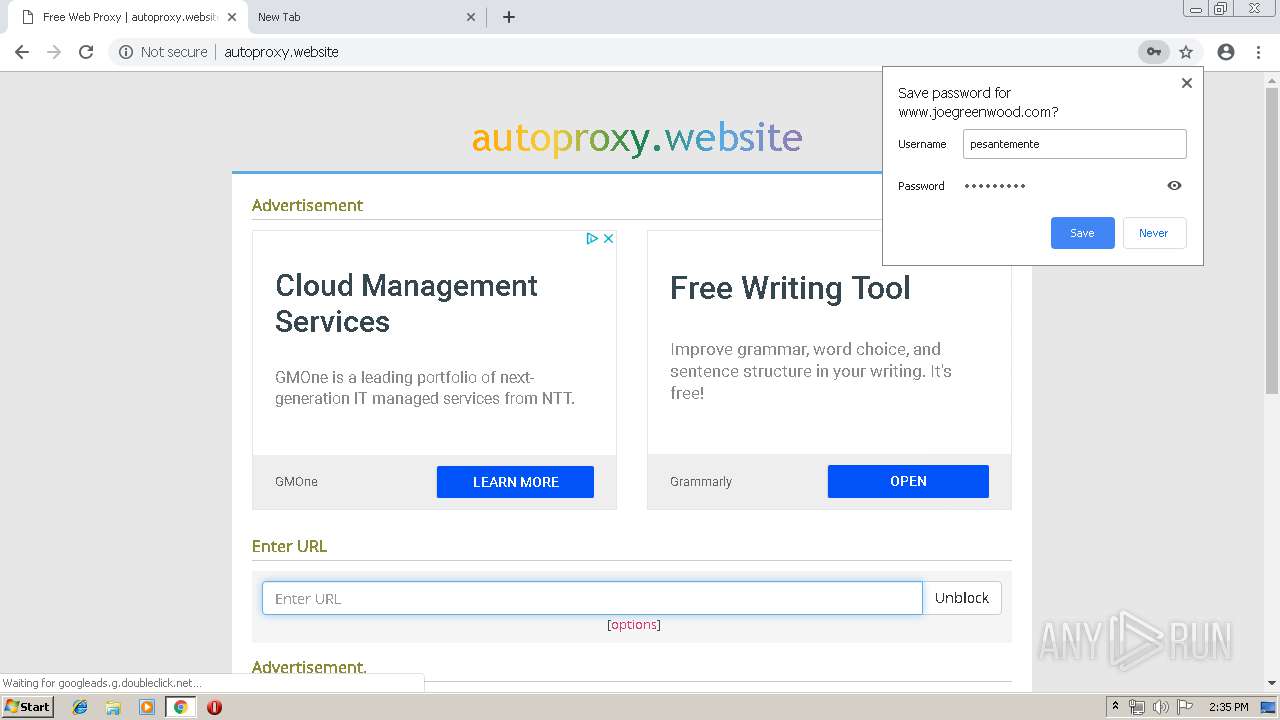
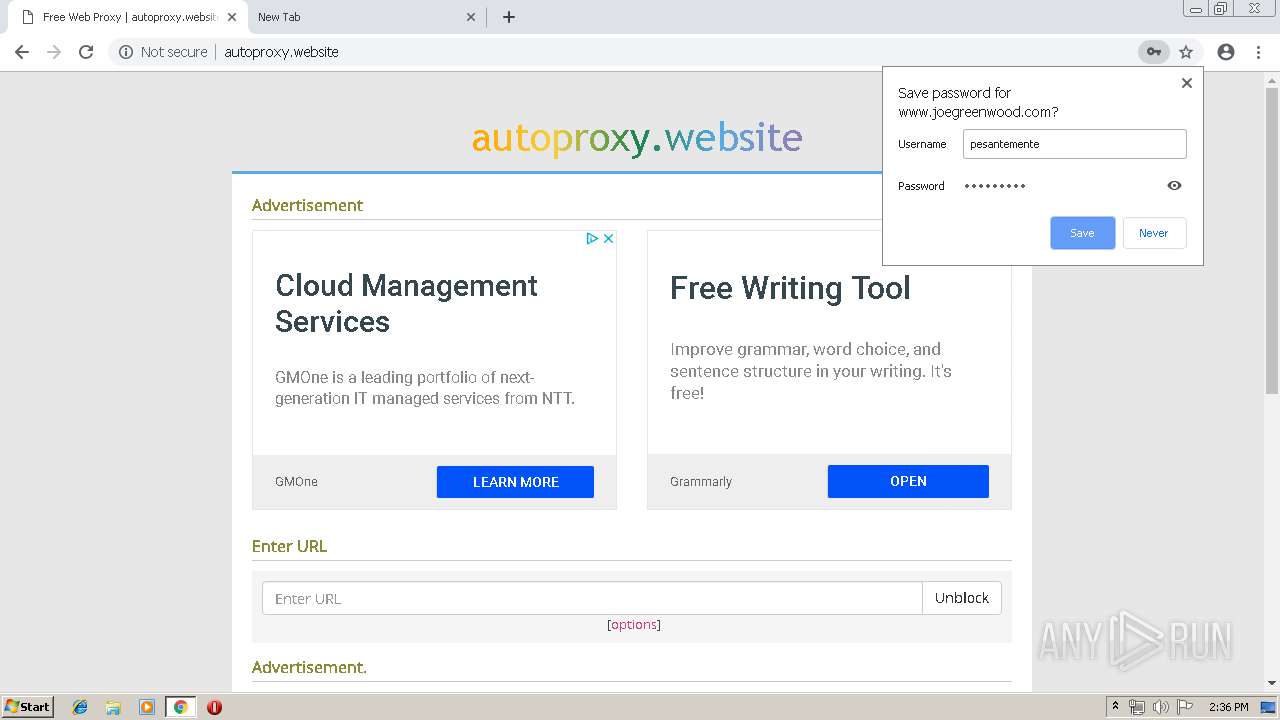
2132 | chrome.exe | GET | — | 46.101.254.41:80 | http://autoproxy.website/ | DE | — | — | whitelisted |
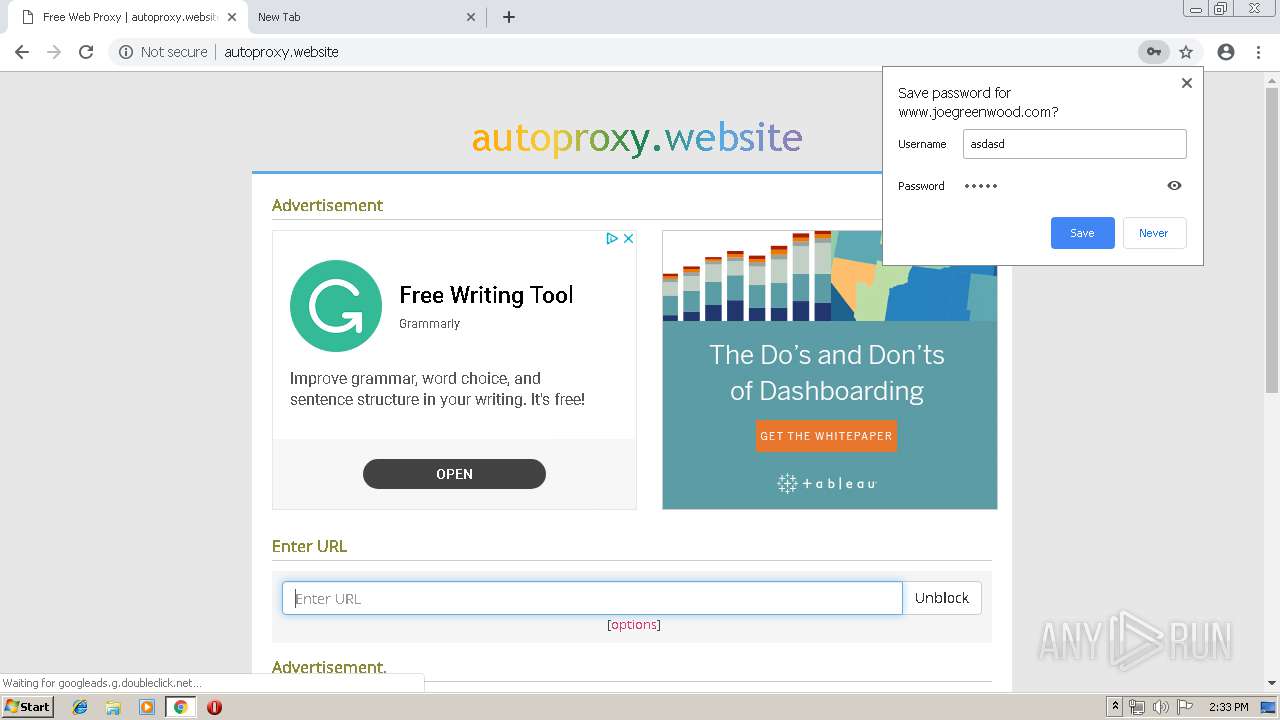
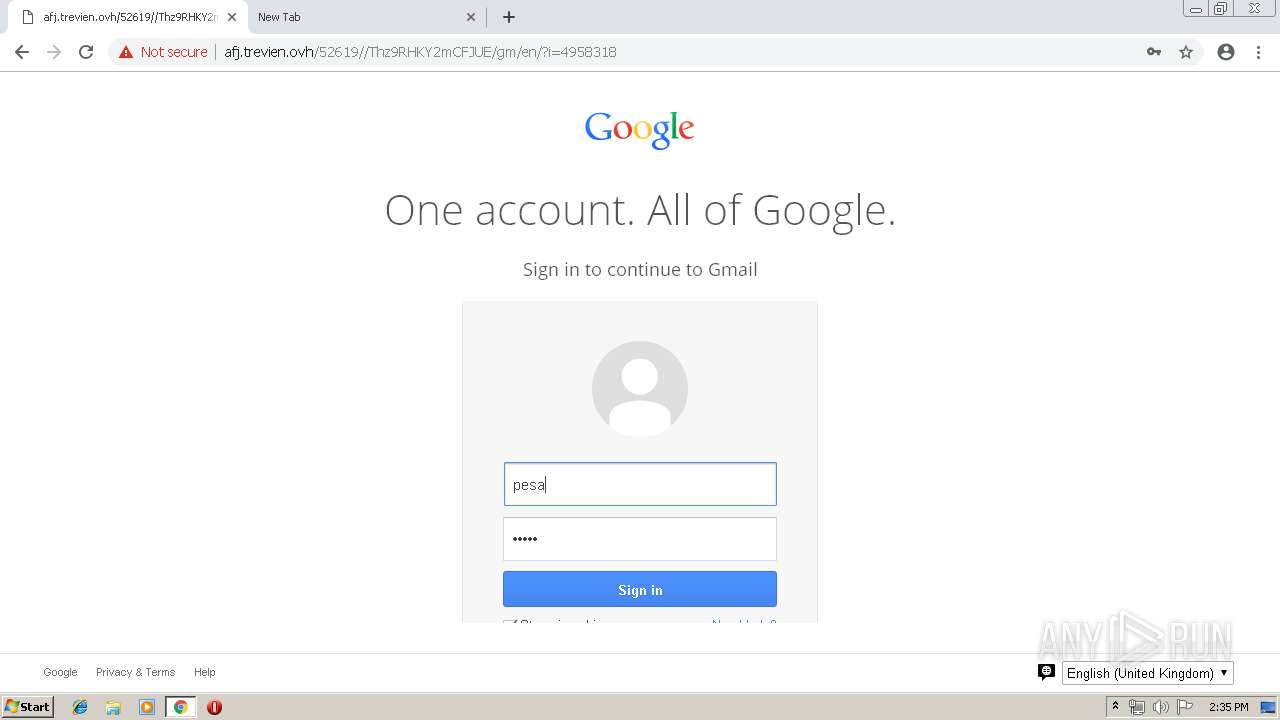
2132 | chrome.exe | POST | — | 208.113.175.1:80 | http://www.joegreenwood.com/zsnl.php | US | — | — | suspicious |
2132 | chrome.exe | POST | 200 | 208.113.175.1:80 | http://www.joegreenwood.com/zsnl.php | US | html | 87 b | suspicious |
2132 | chrome.exe | GET | 200 | 46.101.254.41:80 | http://autoproxy.website/ | DE | html | 3.96 Kb | whitelisted |
2132 | chrome.exe | GET | 200 | 46.101.254.41:80 | http://autoproxy.website/includes/main.js?1.4.15 | DE | html | 11.9 Kb | whitelisted |
2132 | chrome.exe | GET | 200 | 172.217.16.130:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 31.0 Kb | whitelisted |
2132 | chrome.exe | GET | 404 | 46.101.254.41:80 | http://autoproxy.website/favicon.ico | DE | html | 697 b | whitelisted |
2132 | chrome.exe | GET | 200 | 213.186.33.4:80 | http://afj.trevien.ovh/52619//Thz9RHKY2mCFJUE/gm/en/?i=4958318 | FR | html | 188 b | malicious |
2132 | chrome.exe | GET | 200 | 208.113.175.1:80 | http://www.joegreenwood.com///Thz9RHKY2mCFJUE/gm/en/?i=4958318 | US | html | 1.31 Kb | suspicious |
2132 | chrome.exe | GET | 200 | 213.186.33.4:80 | http://afj.trevien.ovh/favicon.ico | FR | html | 161 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2132 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 213.186.33.4:80 | afj.trevien.ovh | OVH SAS | FR | malicious |
2132 | chrome.exe | 208.113.175.1:80 | www.joegreenwood.com | New Dream Network, LLC | US | suspicious |
2132 | chrome.exe | 216.58.207.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 172.217.23.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 173.194.151.88:80 | r2---sn-4g5e6nez.gvt1.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 46.101.254.41:80 | autoproxy.website | Digital Ocean, Inc. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
afj.trevien.ovh |
| malicious |
accounts.google.com |
| shared |
www.joegreenwood.com |
| suspicious |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-4g5e6nez.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2132 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
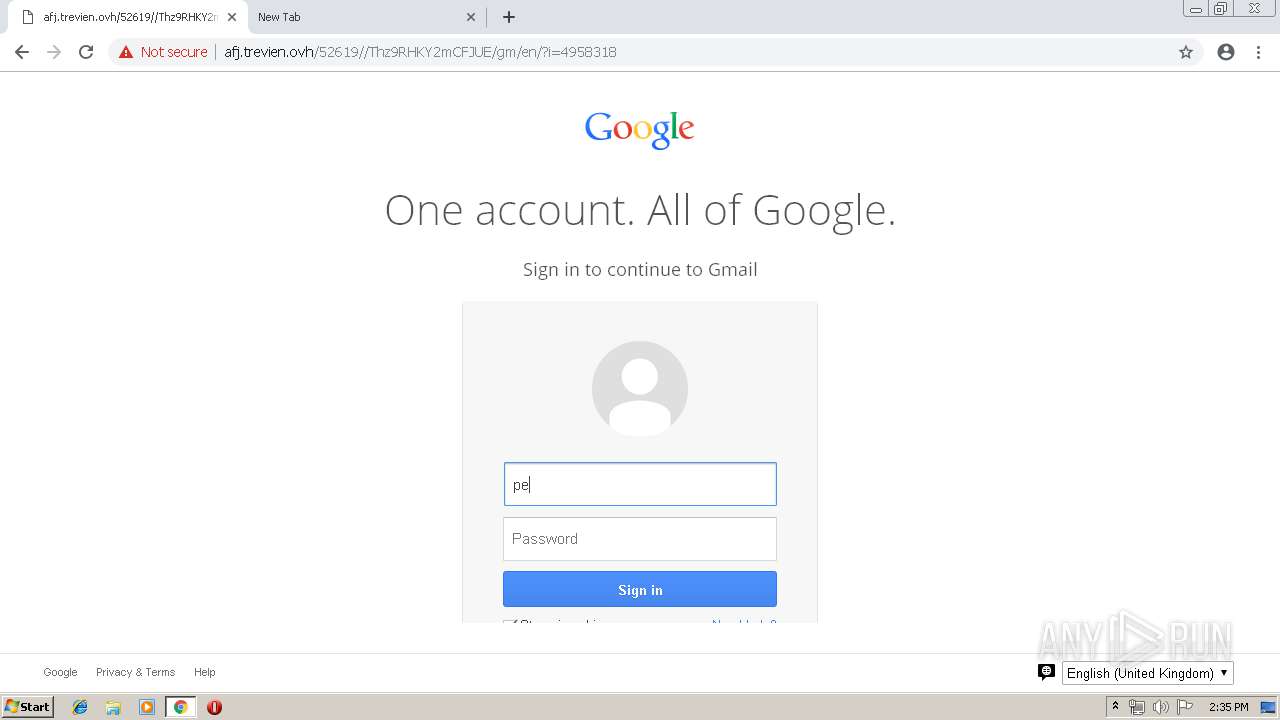
2132 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2132 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2132 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2132 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
4 ETPRO signatures available at the full report