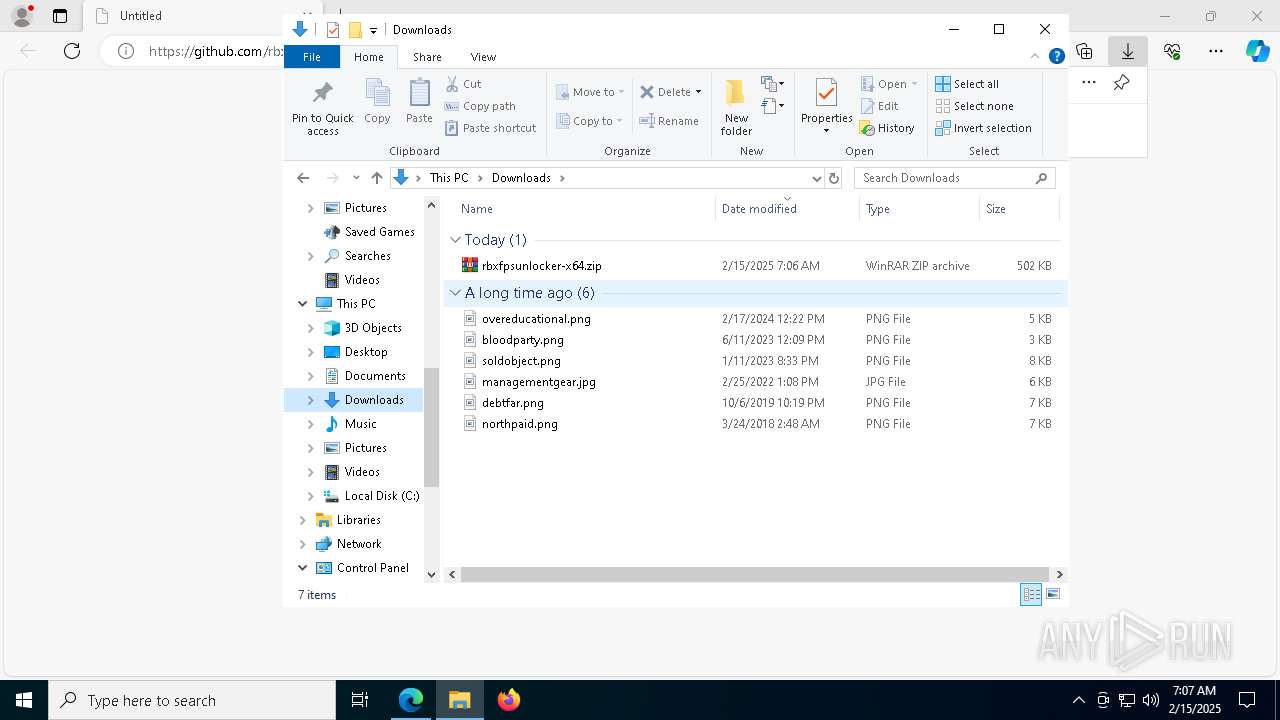
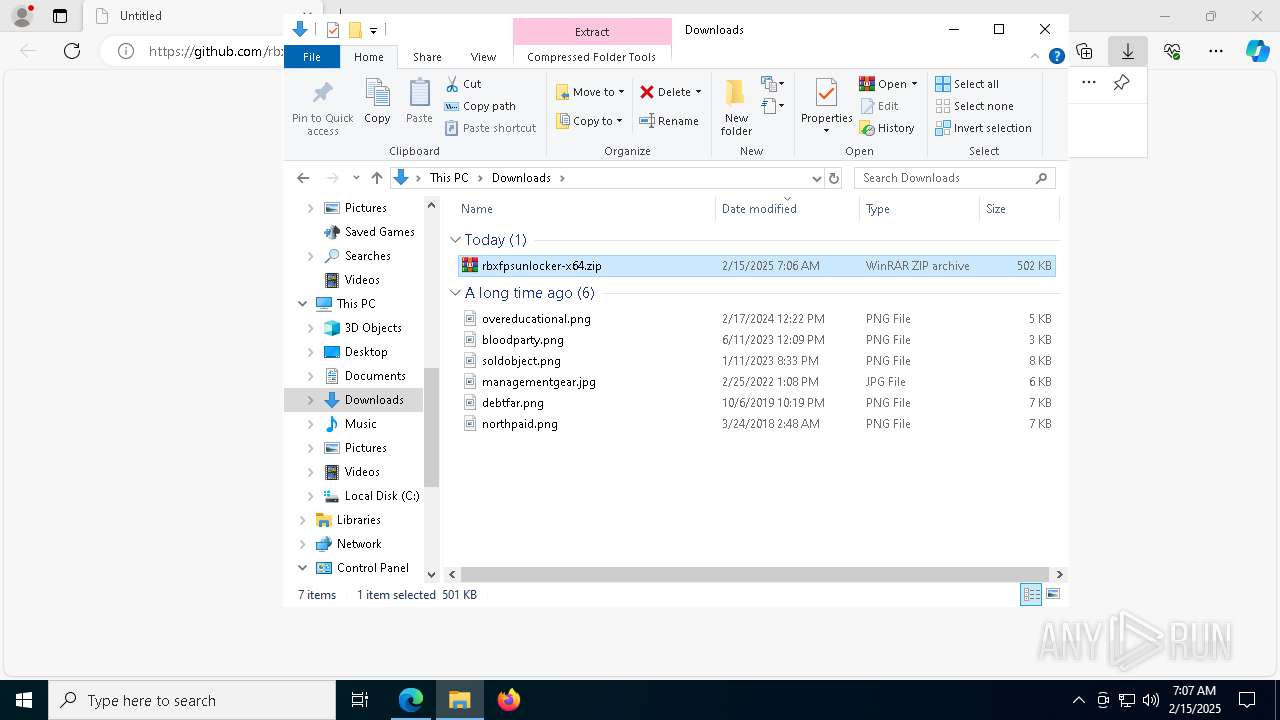
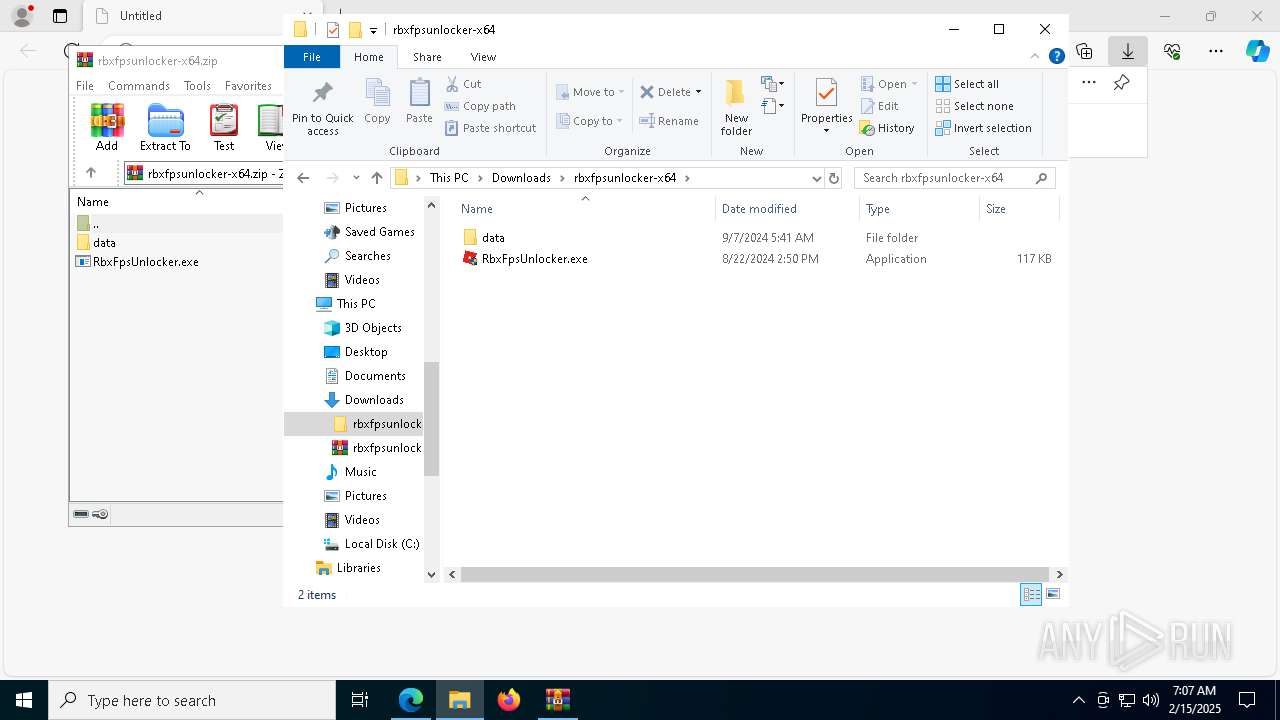
| URL: | https://github.com/rbxfps/roblox-fps-unlocker/releases/download/v5.2/rbxfpsunlocker-x64.zip |
| Full analysis: | https://app.any.run/tasks/e4cd6ce4-0c9e-4123-a33d-0c991c00642b |
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2025, 07:06:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | D4DC6E594A5A9460FE5ECDBA4785D986 |
| SHA1: | 7463D49A024AA9FA436FD0687C3ED21DC2CBF3B1 |
| SHA256: | 0F8E96D29D14ECC499D7963AFD7BF498D350AFB471E59496D04315D30A68E14C |
| SSDEEP: | 3:N8tEdn9Jr6e6XhE2kC6XMHdDBLEGwI:2uFrSXhrYcHdpvwI |
MALICIOUS
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 7620)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 7620)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7620)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7620)
Application was injected by another process
- svchost.exe (PID: 2952)
- svchost.exe (PID: 376)
- explorer.exe (PID: 4488)
- svchost.exe (PID: 2500)
- svchost.exe (PID: 1768)
- svchost.exe (PID: 1364)
- svchost.exe (PID: 1564)
- svchost.exe (PID: 1176)
- svchost.exe (PID: 2360)
- svchost.exe (PID: 2748)
- svchost.exe (PID: 2944)
- svchost.exe (PID: 2340)
- svchost.exe (PID: 4696)
- svchost.exe (PID: 2528)
- svchost.exe (PID: 1764)
- svchost.exe (PID: 2920)
- svchost.exe (PID: 1316)
- svchost.exe (PID: 3160)
- svchost.exe (PID: 2892)
- svchost.exe (PID: 1908)
- svchost.exe (PID: 1880)
- svchost.exe (PID: 2272)
- svchost.exe (PID: 3668)
- svchost.exe (PID: 1128)
- svchost.exe (PID: 1500)
- svchost.exe (PID: 2288)
- svchost.exe (PID: 320)
- svchost.exe (PID: 1076)
- svchost.exe (PID: 892)
- svchost.exe (PID: 2256)
- svchost.exe (PID: 3056)
- svchost.exe (PID: 2660)
- svchost.exe (PID: 3704)
- svchost.exe (PID: 4456)
- svchost.exe (PID: 2064)
- svchost.exe (PID: 4436)
- svchost.exe (PID: 1268)
- svchost.exe (PID: 3032)
- svchost.exe (PID: 1660)
- svchost.exe (PID: 1452)
- svchost.exe (PID: 1260)
- svchost.exe (PID: 1068)
- svchost.exe (PID: 4200)
- svchost.exe (PID: 1340)
- svchost.exe (PID: 2192)
- svchost.exe (PID: 1972)
- svchost.exe (PID: 3600)
- svchost.exe (PID: 2224)
- svchost.exe (PID: 4000)
- svchost.exe (PID: 2364)
- svchost.exe (PID: 4984)
- svchost.exe (PID: 3016)
- svchost.exe (PID: 3592)
- svchost.exe (PID: 1916)
- svchost.exe (PID: 3824)
- svchost.exe (PID: 2816)
- svchost.exe (PID: 1424)
- svchost.exe (PID: 3976)
- svchost.exe (PID: 1008)
- svchost.exe (PID: 1980)
- svchost.exe (PID: 3164)
- svchost.exe (PID: 1784)
- svchost.exe (PID: 2852)
- svchost.exe (PID: 812)
- svchost.exe (PID: 4168)
- svchost.exe (PID: 2372)
- svchost.exe (PID: 1776)
- svchost.exe (PID: 1276)
- svchost.exe (PID: 4176)
- svchost.exe (PID: 7080)
- svchost.exe (PID: 4052)
- svchost.exe (PID: 3696)
Runs injected code in another process
- powershell.exe (PID: 7620)
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 7620)
SUSPICIOUS
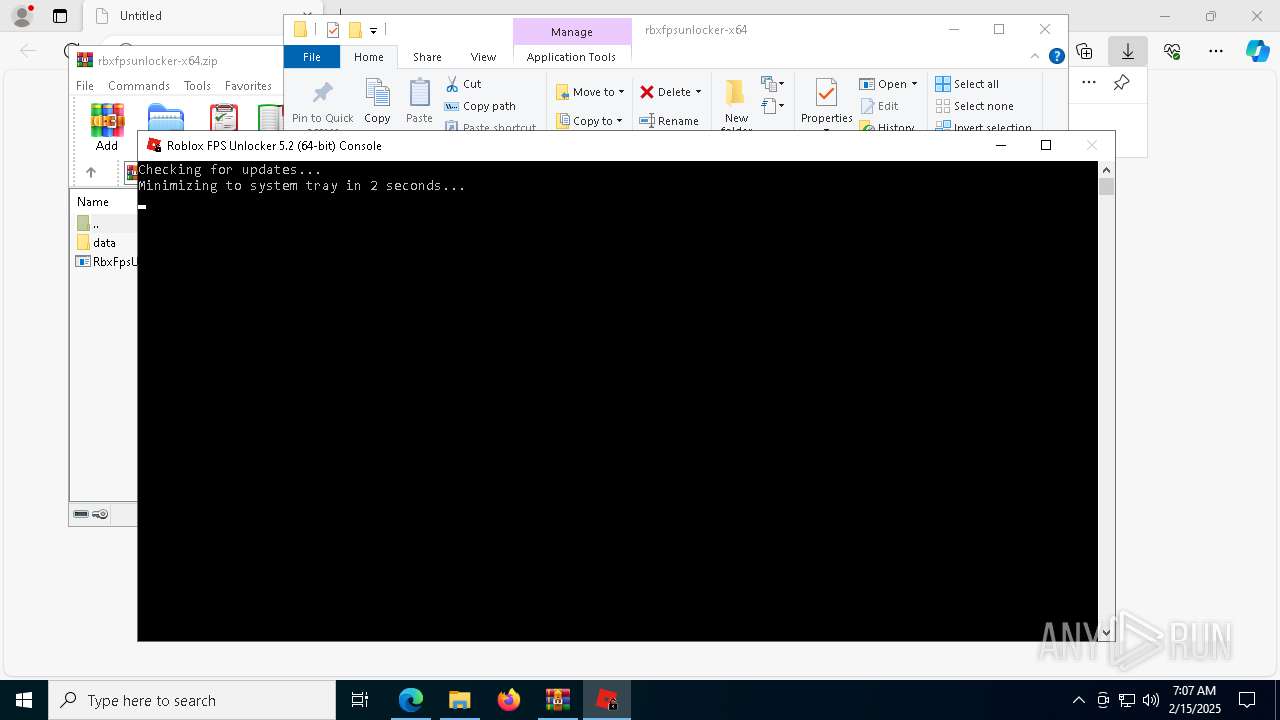
Checks Windows Trust Settings
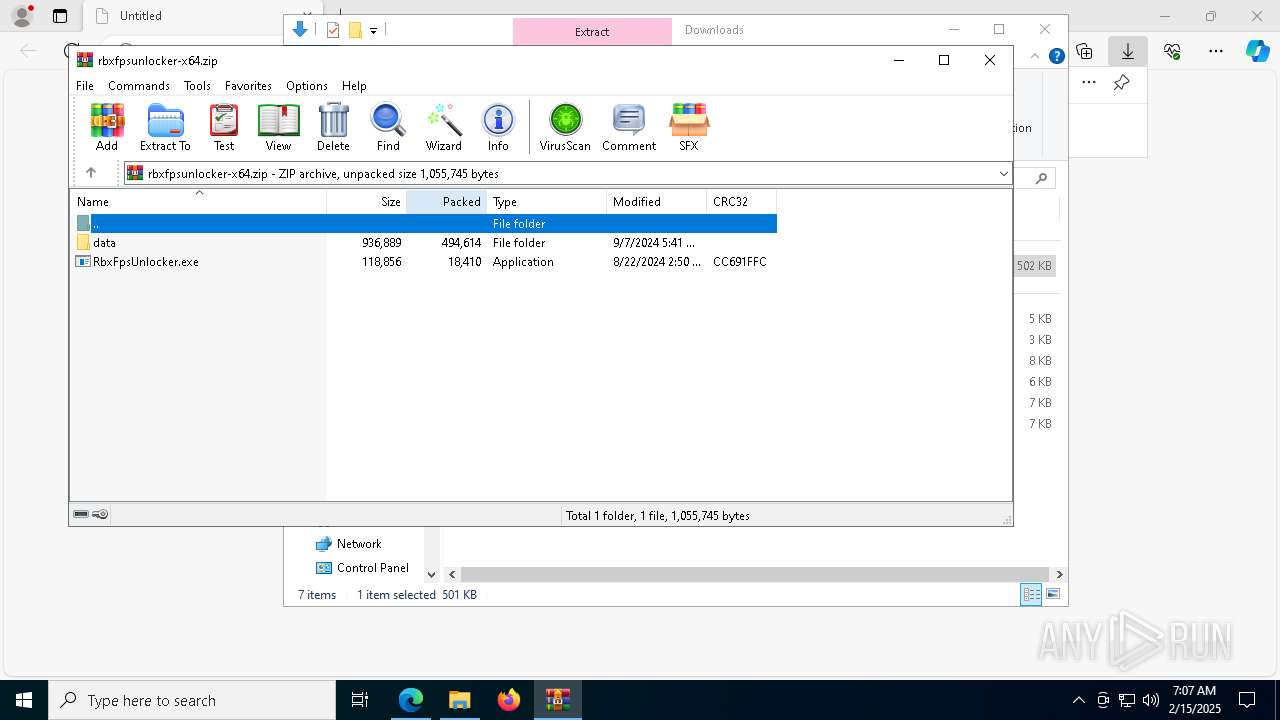
- RbxFpsUnlocker.exe (PID: 4052)
- rbx.exe (PID: 7172)
Reads security settings of Internet Explorer
- RbxFpsUnlocker.exe (PID: 4052)
- rbx.exe (PID: 7172)
Adds/modifies Windows certificates
- RbxFpsUnlocker.exe (PID: 4052)
Reads the date of Windows installation
- RbxFpsUnlocker.exe (PID: 4052)
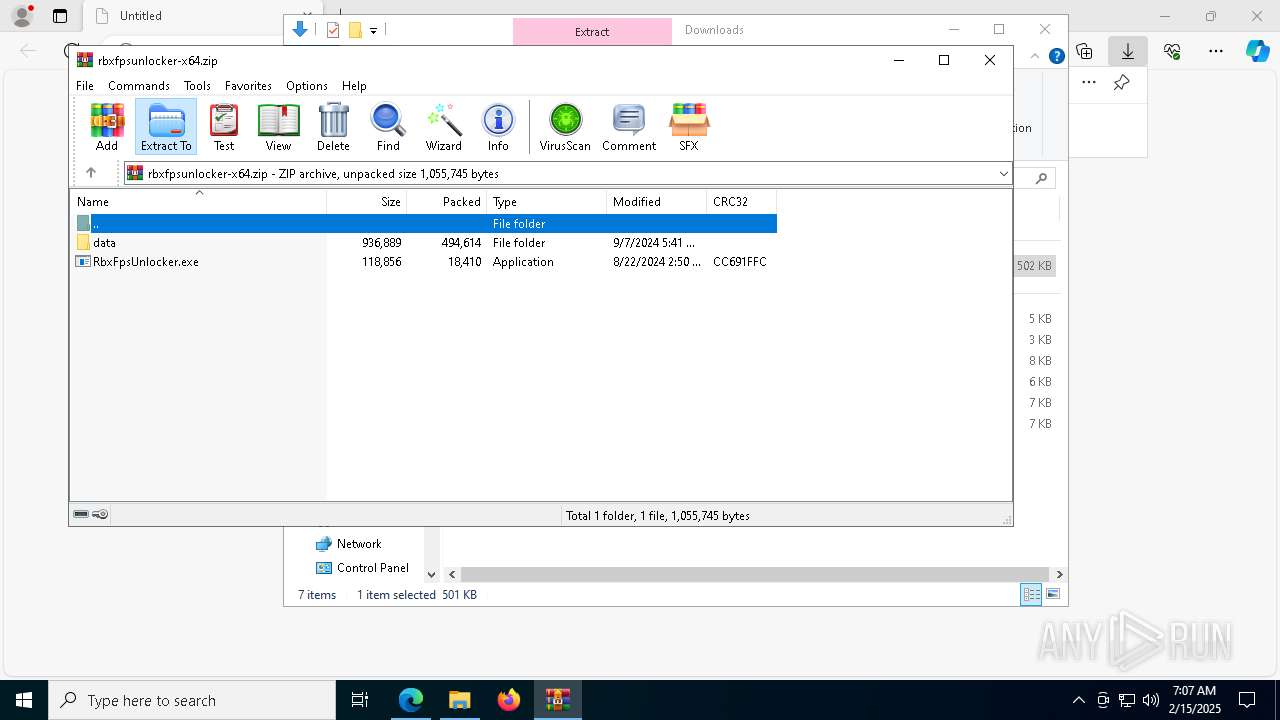
Starts CMD.EXE for commands execution
- RbxFpsUnlocker.exe (PID: 4052)
- cmd.exe (PID: 6992)
Executing commands from a ".bat" file
- cmd.exe (PID: 6992)
- RbxFpsUnlocker.exe (PID: 4052)
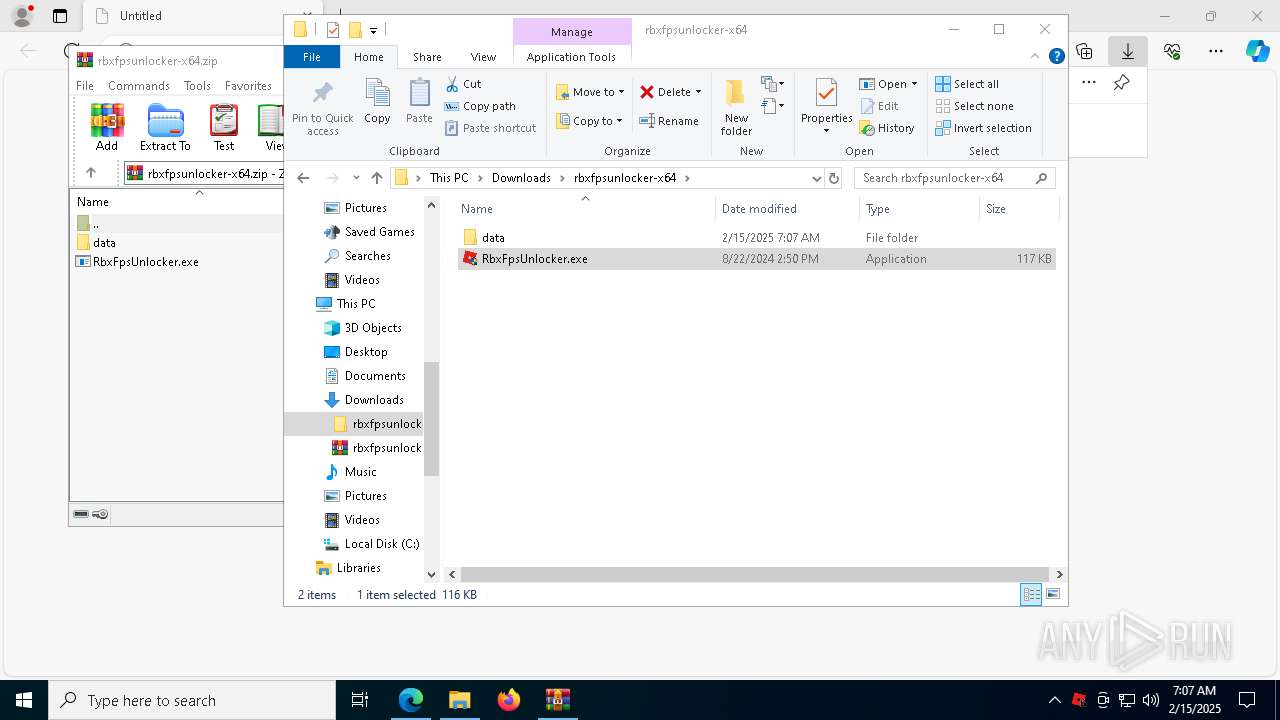
Executable content was dropped or overwritten
- RbxFpsUnlocker.exe (PID: 4052)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6992)
- powershell.exe (PID: 7620)
Process checks specific path in scheduled tasks
- powershell.exe (PID: 7808)
Application launched itself
- powershell.exe (PID: 7620)
- cmd.exe (PID: 6992)
Cryptography encrypted command line is found
- cmd.exe (PID: 7584)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7620)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 7620)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 7620)
Connects to unusual port
- powershell.exe (PID: 7620)
INFO
Reads security settings of Internet Explorer
- svchost.exe (PID: 2364)
- explorer.exe (PID: 4488)
- WWAHost.exe (PID: 6316)
Reads Environment values
- identity_helper.exe (PID: 7400)
- RbxFpsUnlocker.exe (PID: 4052)
Checks supported languages
- identity_helper.exe (PID: 7400)
- RbxFpsUnlocker.exe (PID: 4052)
- rbx.exe (PID: 7172)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4488)
Reads the computer name
- identity_helper.exe (PID: 7400)
- RbxFpsUnlocker.exe (PID: 4052)
- rbx.exe (PID: 7172)
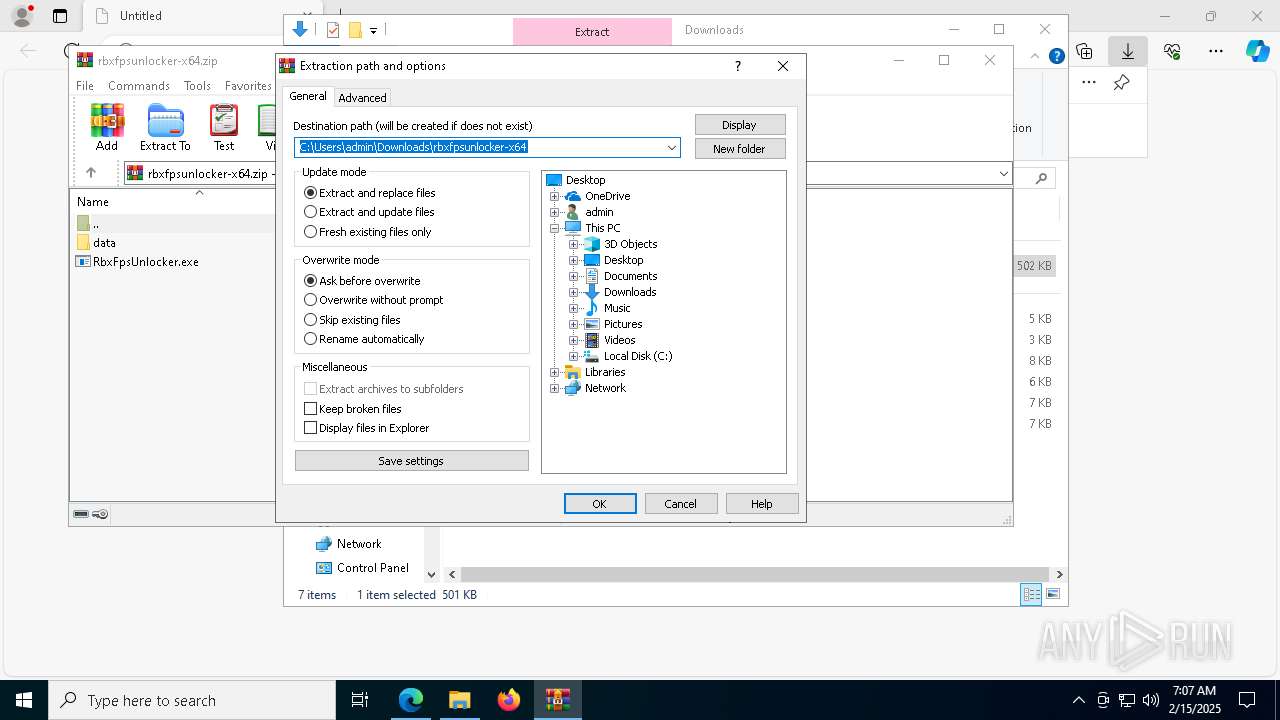
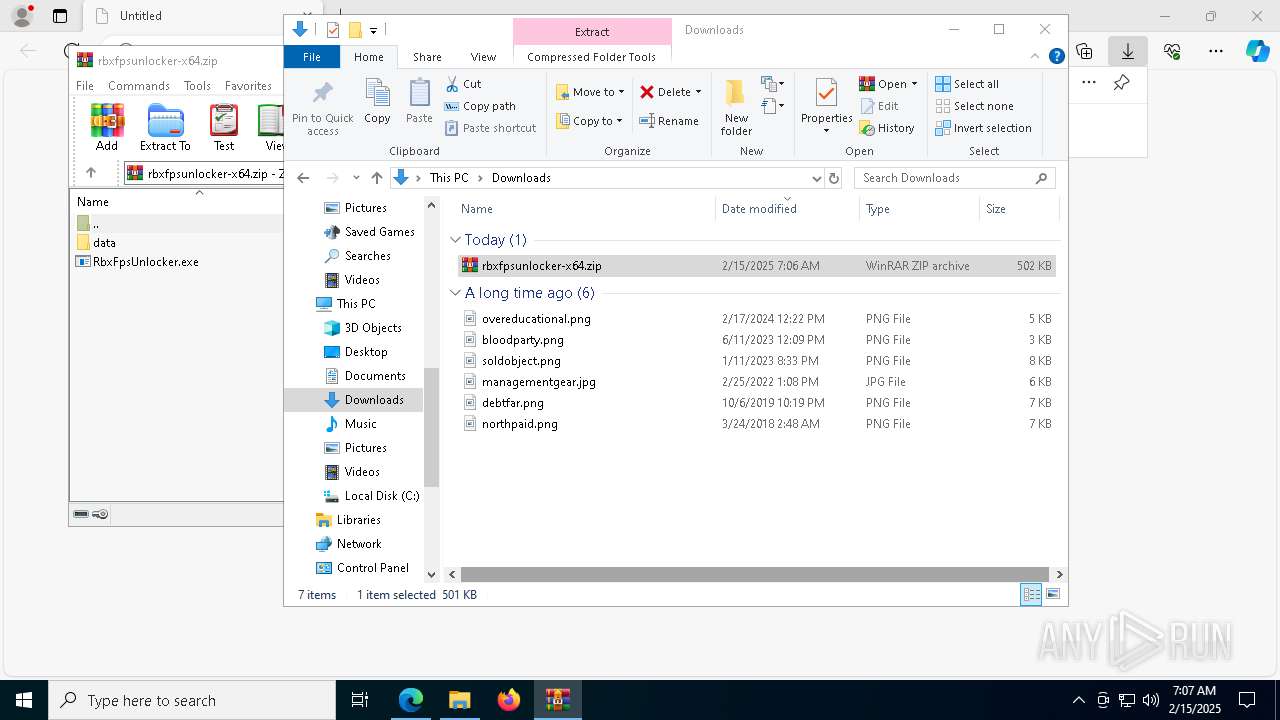
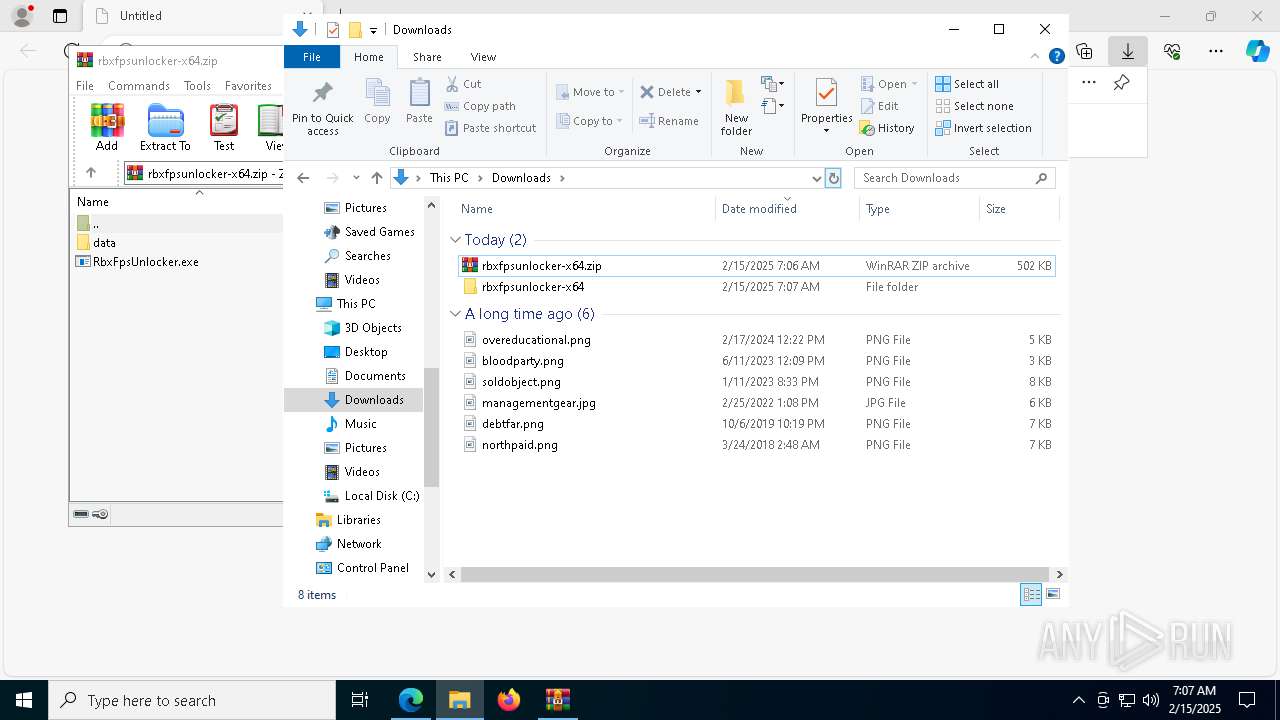
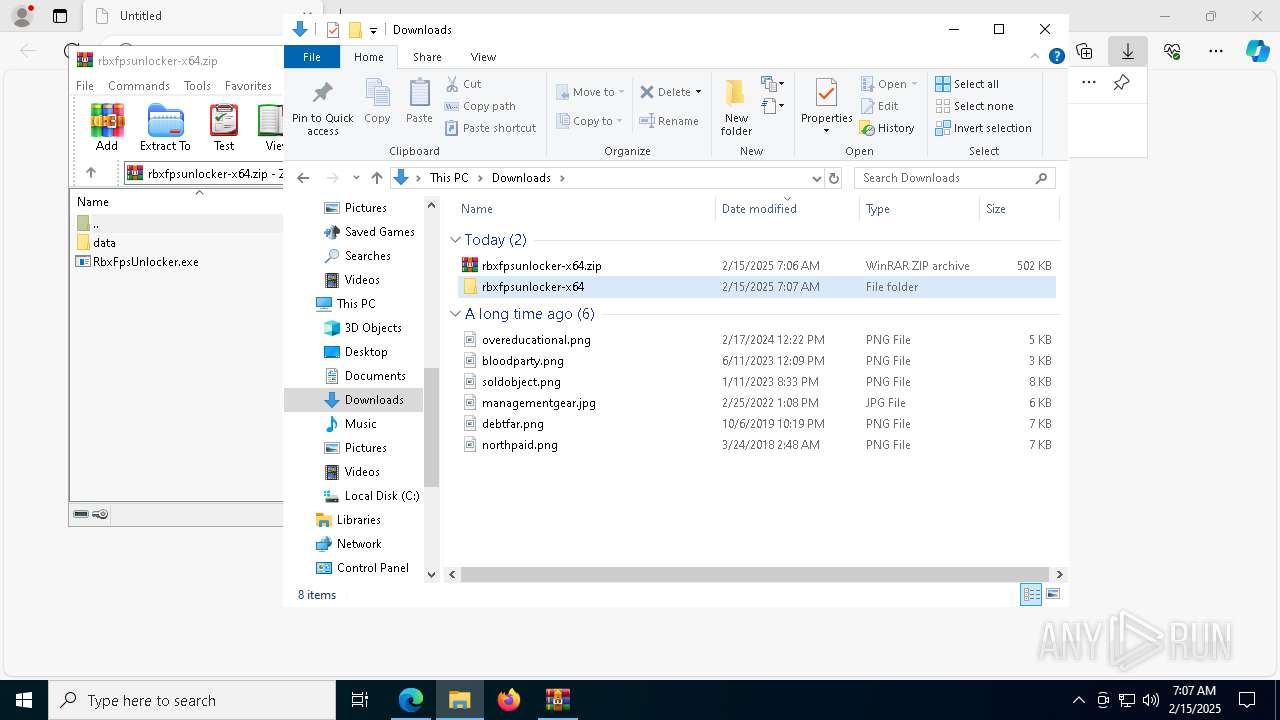
Manual execution by a user
- WinRAR.exe (PID: 8160)
- RbxFpsUnlocker.exe (PID: 5880)
- RbxFpsUnlocker.exe (PID: 4052)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8160)
- msedge.exe (PID: 7400)
Create files in a temporary directory
- RbxFpsUnlocker.exe (PID: 4052)
- svchost.exe (PID: 7080)
Reads the machine GUID from the registry
- RbxFpsUnlocker.exe (PID: 4052)
- rbx.exe (PID: 7172)
Creates files or folders in the user directory
- RbxFpsUnlocker.exe (PID: 4052)
- rbx.exe (PID: 7172)
- WWAHost.exe (PID: 6316)
Checks proxy server information
- RbxFpsUnlocker.exe (PID: 4052)
- rbx.exe (PID: 7172)
- WWAHost.exe (PID: 6316)
Reads the software policy settings
- RbxFpsUnlocker.exe (PID: 4052)
- rbx.exe (PID: 7172)
- WWAHost.exe (PID: 6316)
Checks if a key exists in the options dictionary (POWERSHELL)
- RbxFpsUnlocker.exe (PID: 4052)
- powershell.exe (PID: 7808)
- powershell.exe (PID: 7548)
- powershell.exe (PID: 2136)
Process checks computer location settings
- RbxFpsUnlocker.exe (PID: 4052)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7620)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7620)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7620)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7620)
Application launched itself
- msedge.exe (PID: 1296)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2136)
Creates files in the program directory
- svchost.exe (PID: 1076)
Reads the time zone
- svchost.exe (PID: 2816)
The sample compiled with english language support
- msedge.exe (PID: 7400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
220
Monitored processes
157
Malicious processes
4
Suspicious processes
71
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=904 --field-trial-handle=2388,i,12300286966613091970,11166980168265871319,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=5808 --field-trial-handle=2388,i,12300286966613091970,11166980168265871319,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 320 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | C:\WINDOWS\System32\svchost.exe -k LocalSystemNetworkRestricted -p -s WdiSystemHost | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5664 --field-trial-handle=2388,i,12300286966613091970,11166980168265871319,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RbxFpsUnlocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | C:\WINDOWS\System32\svchost.exe -k LocalSystemNetworkRestricted -p -s StorSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3716 --field-trial-handle=2388,i,12300286966613091970,11166980168265871319,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1008 | C:\WINDOWS\system32\svchost.exe -k RPCSS -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
98 558
Read events
97 643
Write events
572
Delete events
343
Modification events
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7B6A4038BF8C2F00 | |||
| (PID) Process: | (892) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001_Classes\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppModel\SystemAppData\Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy\HAM\AUI\App\V1\LU |
| Operation: | write | Name: | PCT |
Value: 8F453C33787FDB01 | |||
| (PID) Process: | (892) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\TermReason\6868 |
| Operation: | write | Name: | Terminator |
Value: HAM | |||
| (PID) Process: | (892) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\TermReason\6868 |
| Operation: | write | Name: | Reason |
Value: 4 | |||
| (PID) Process: | (892) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\TermReason\6868 |
| Operation: | write | Name: | CreationTime |
Value: 82F05B33787FDB01 | |||
| (PID) Process: | (892) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\Windows NT\CurrentVersion\HostActivityManager\CommitHistory\Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy!App |
| Operation: | write | Name: | Pure |
Value: FFFF3F0100000000 | |||
Executable files
50
Suspicious files
1 097
Text files
175
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF134ae7.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF134ad7.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF134ad7.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF134ad7.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF134b25.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
274
DNS requests
230
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4052 | RbxFpsUnlocker.exe | GET | 200 | 18.173.205.43:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7172 | rbx.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
7172 | rbx.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CECoW9cIBGAf3CpJj3Tw5qfI%3D | unknown | — | — | whitelisted |
7172 | rbx.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
7268 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7500 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
880 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
132 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 23.212.110.154:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1296 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6404 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6404 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
6404 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.now-dns .net Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.now-dns .net Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.now-dns .net Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.now-dns .net Domain |
6404 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6404 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6404 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6404 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.now-dns .net Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.now-dns .net Domain |