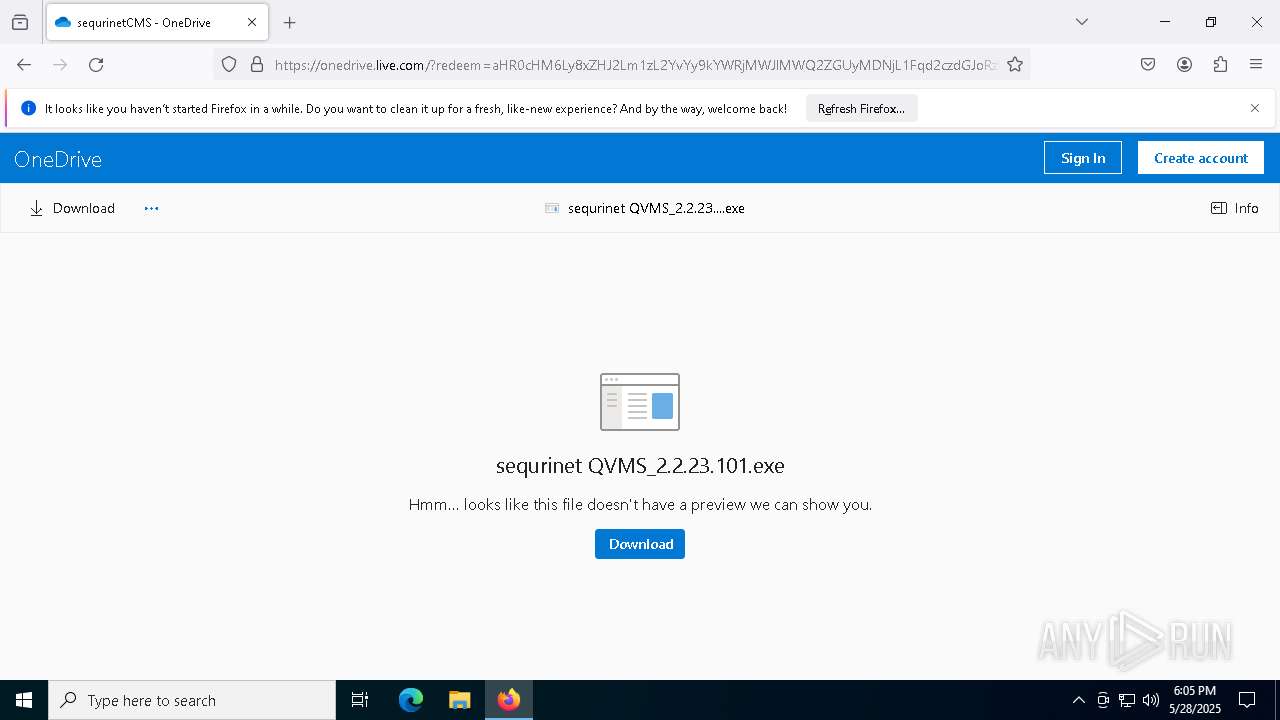
| download: | / |
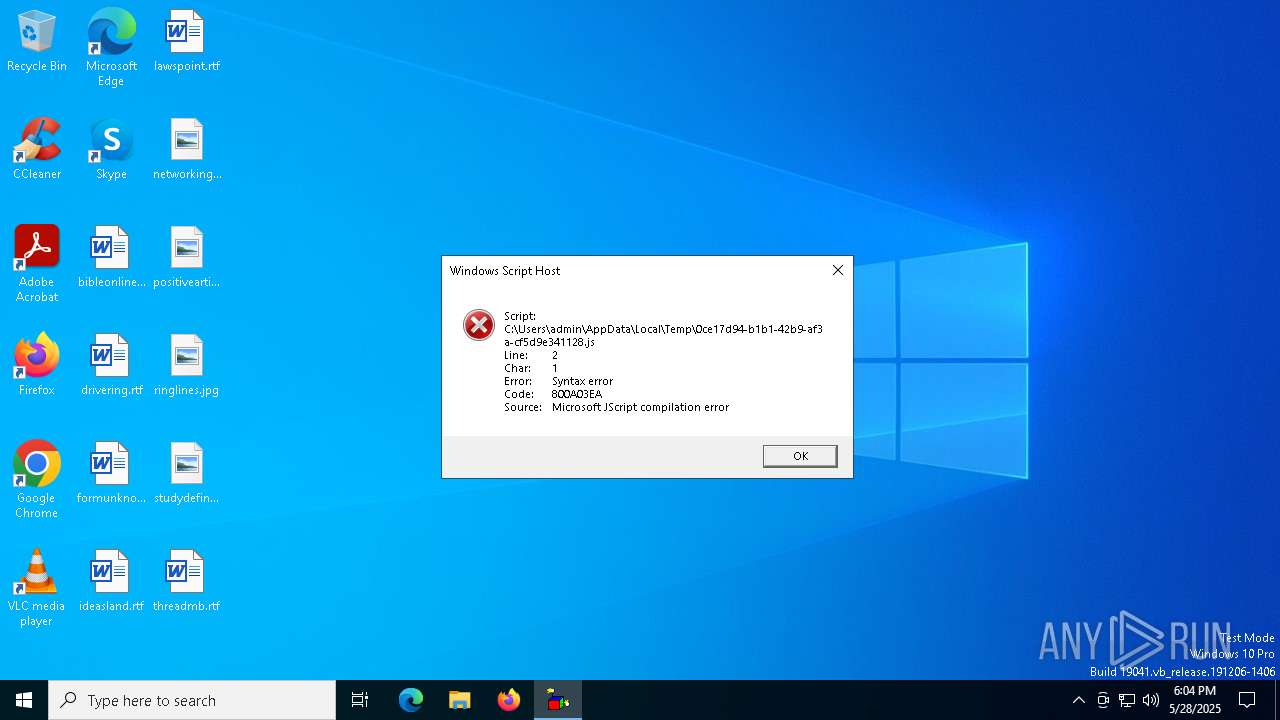
| Full analysis: | https://app.any.run/tasks/0ce17d94-b1b1-42b9-af3a-cf5d9e341128 |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 18:04:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines (63933), with CRLF line terminators |
| MD5: | 38354BCD84B1A2396CE7F17FE4411E72 |
| SHA1: | CFEBBBCCD0B5EA41BE9486BE52EAA2FB23B15827 |
| SHA256: | 0F8DD1FE17ABDF36CC11ACF43475925C6879F0AECBBF73F891F71C5D254F60C2 |
| SSDEEP: | 6144:vcFeO6xD+yFNgQ2h/DK3qBz6RHgTtIshj6gyr6mL0V2dQ7kXDmzlRvKMsKRVAY/e:+E4iGvffkTcVsKRVTkNeYt |
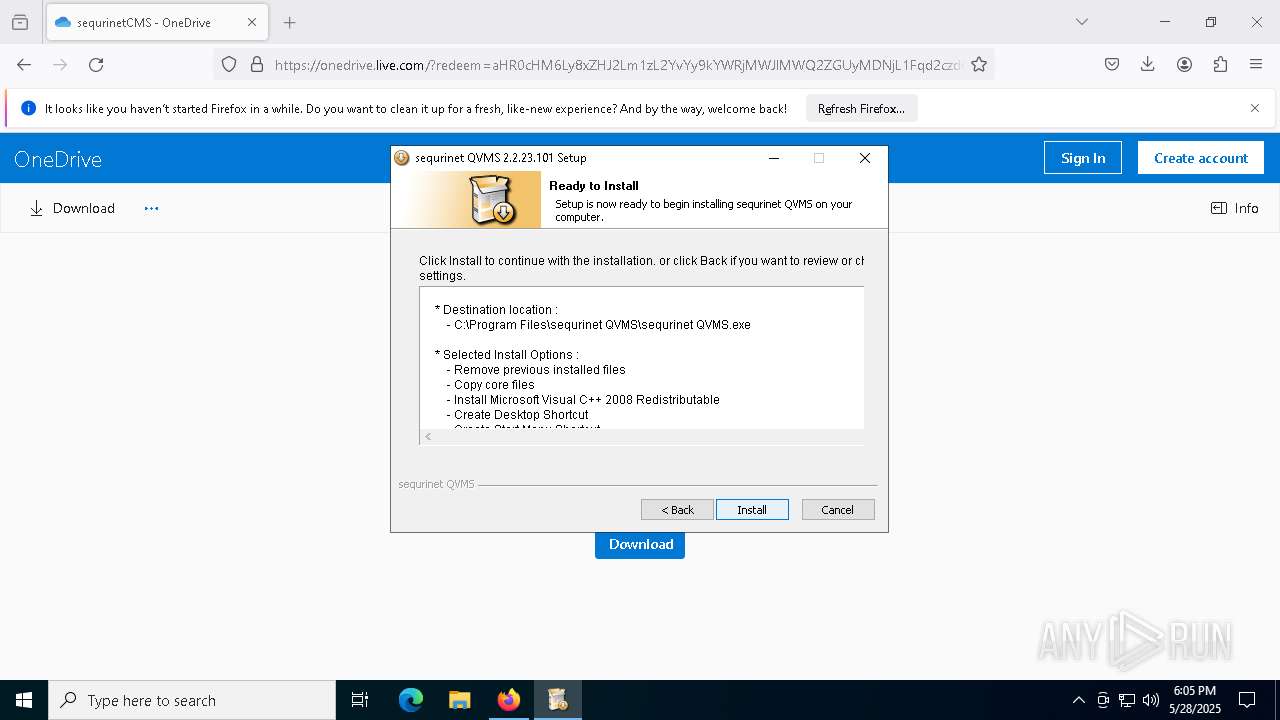
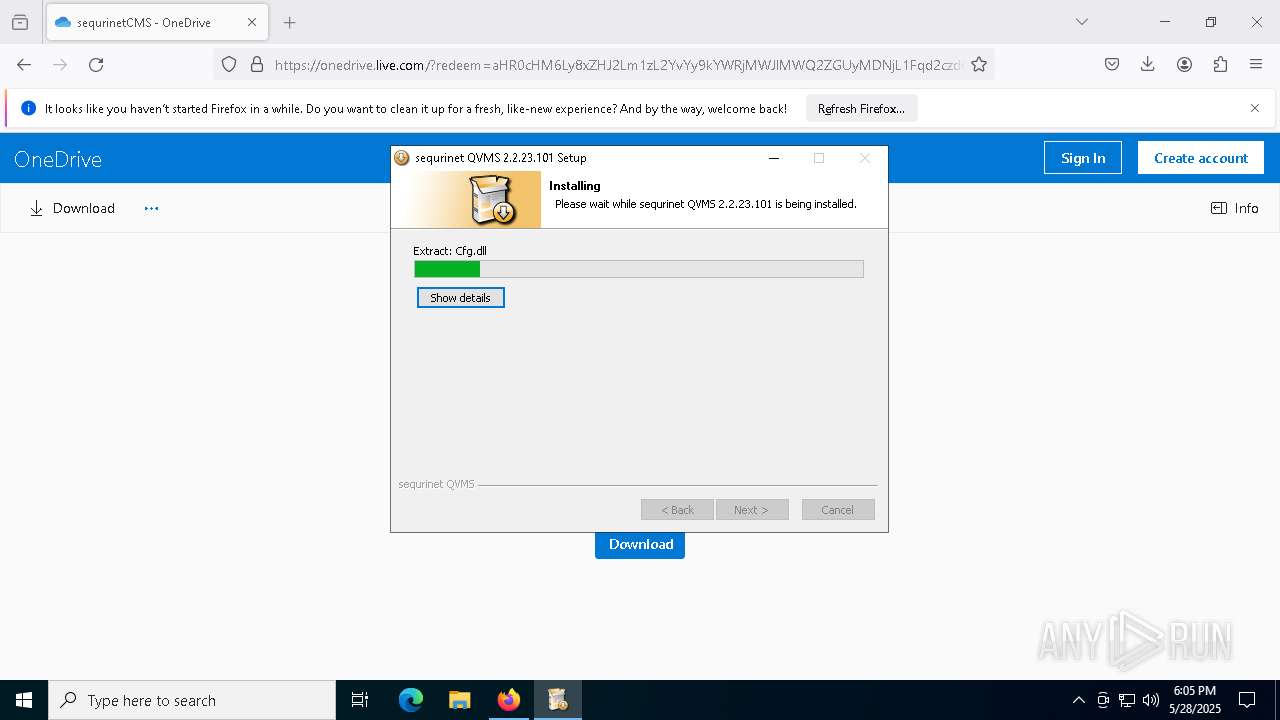
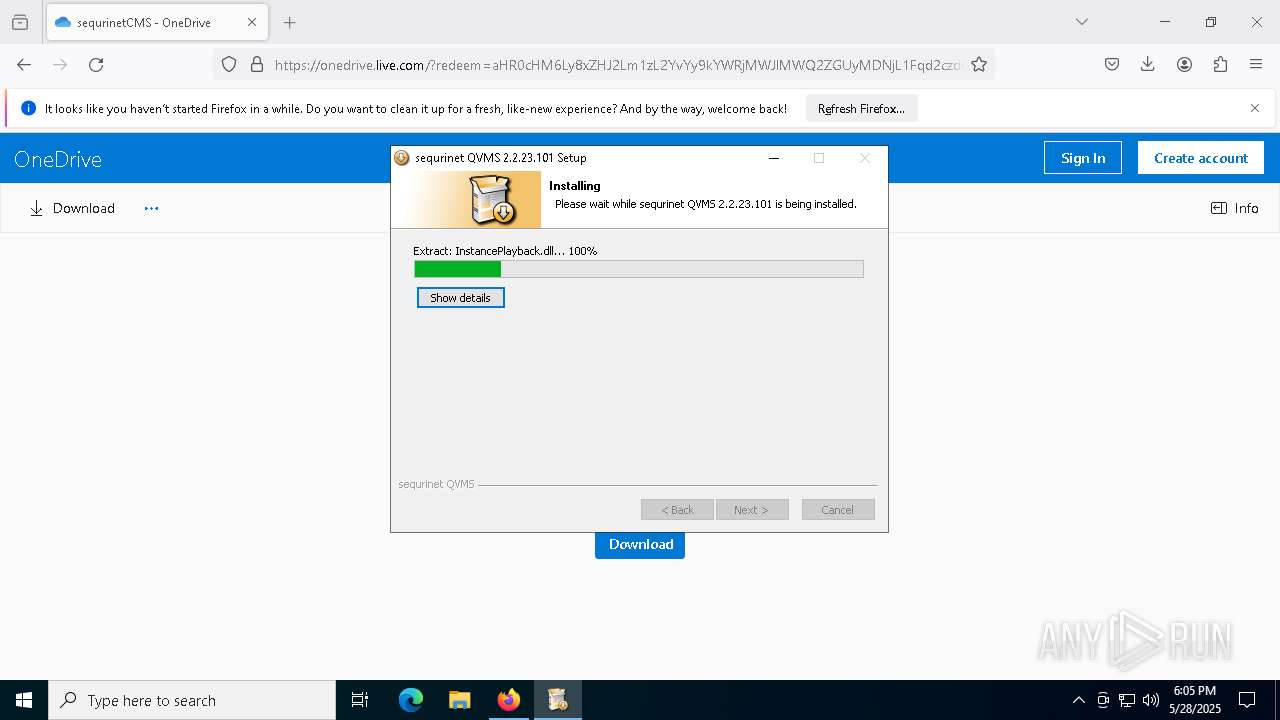
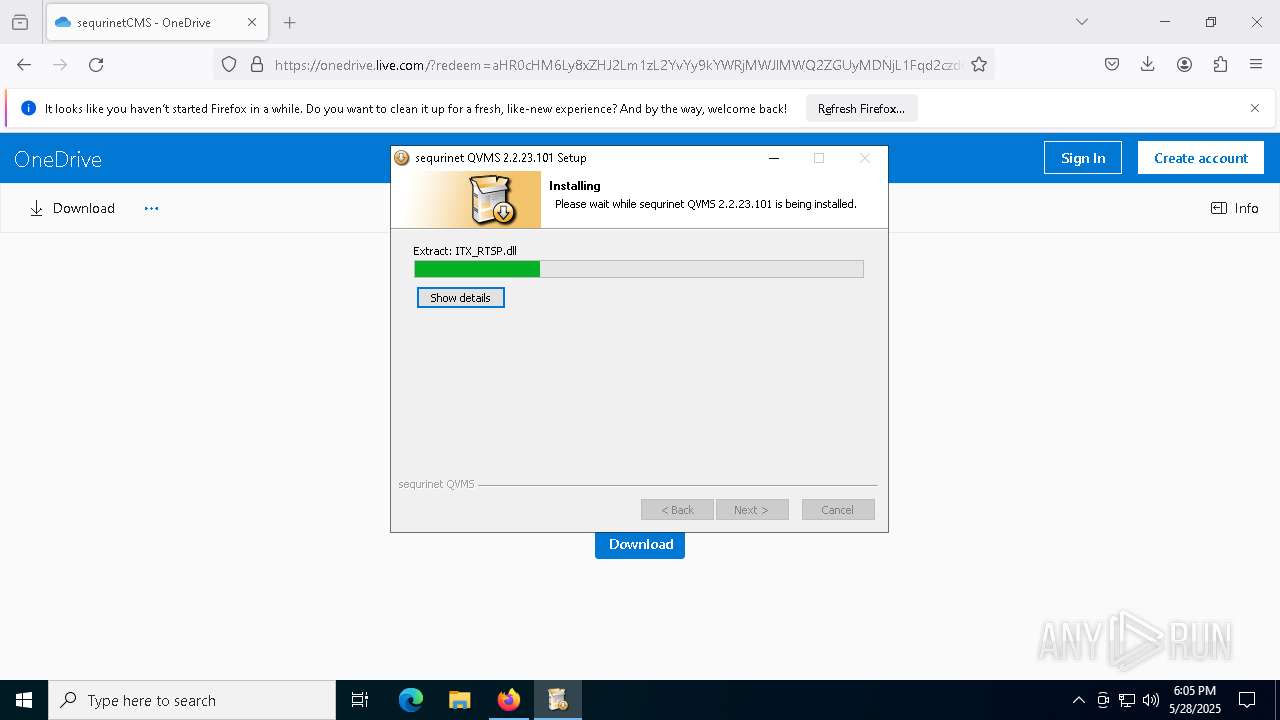
MALICIOUS
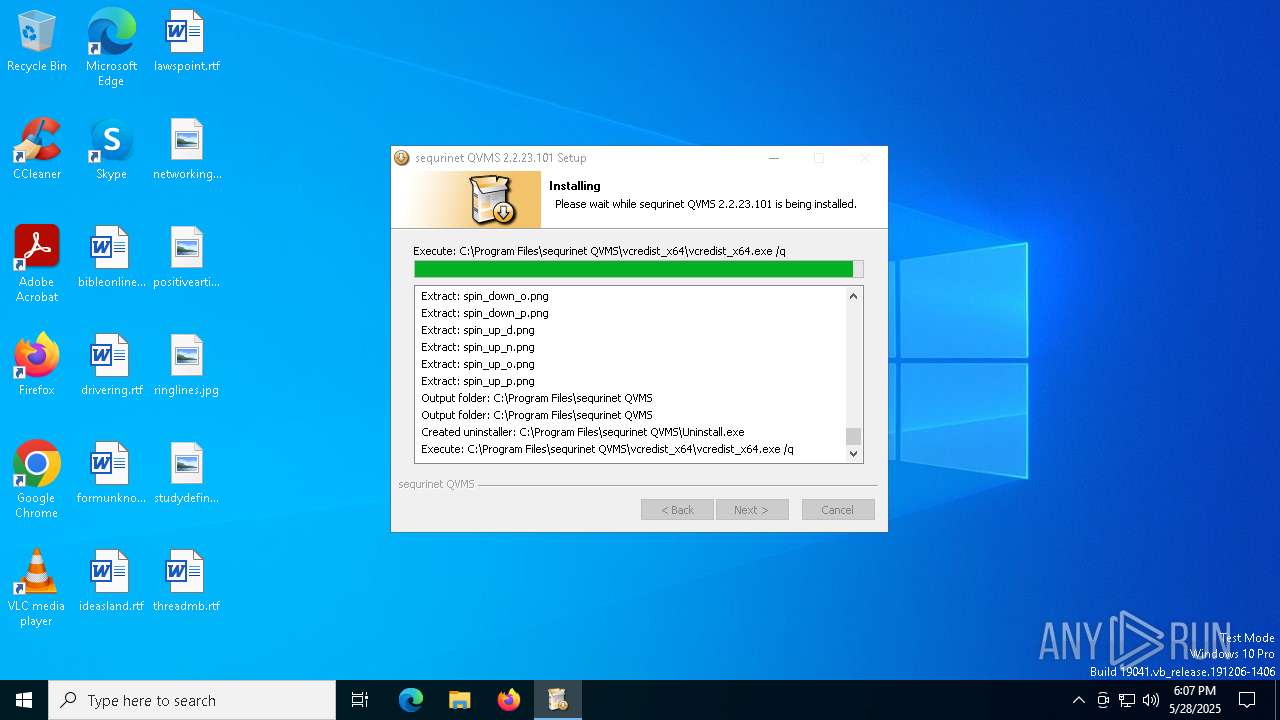
Executing a file with an untrusted certificate
- vcredist_x64.exe (PID: 5376)
- install.exe (PID: 7900)
SUSPICIOUS
Process drops legitimate windows executable
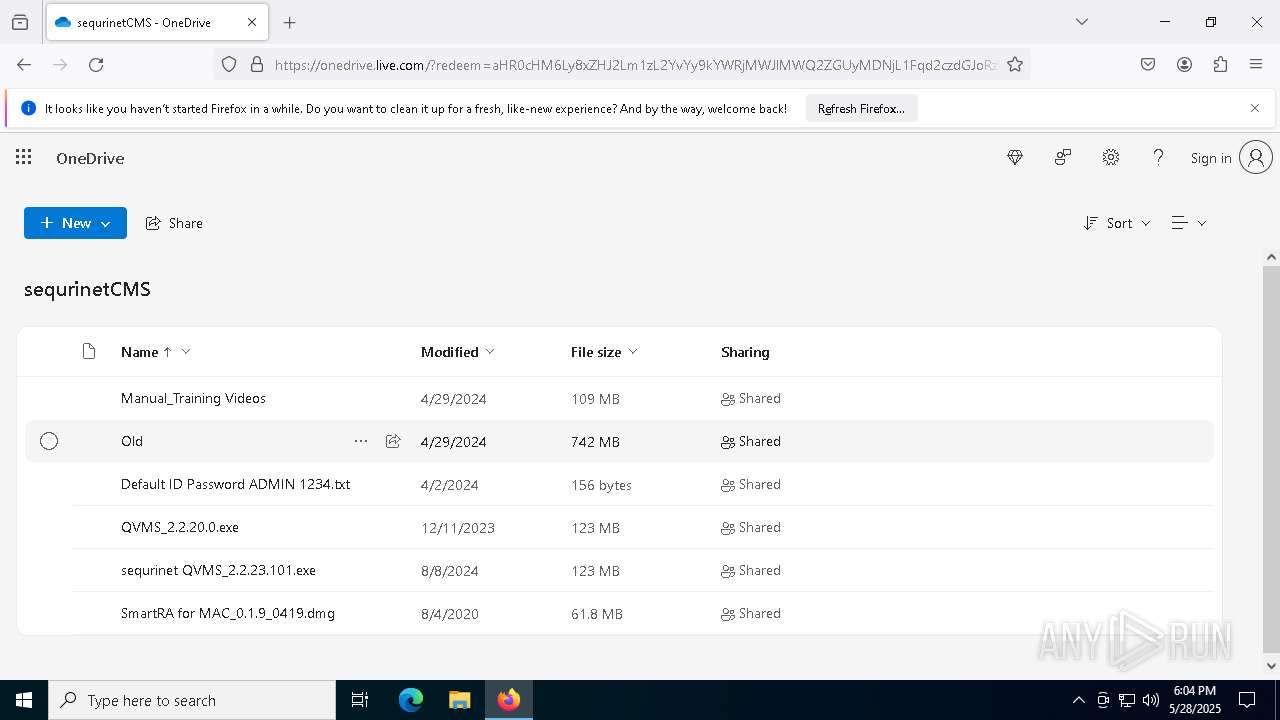
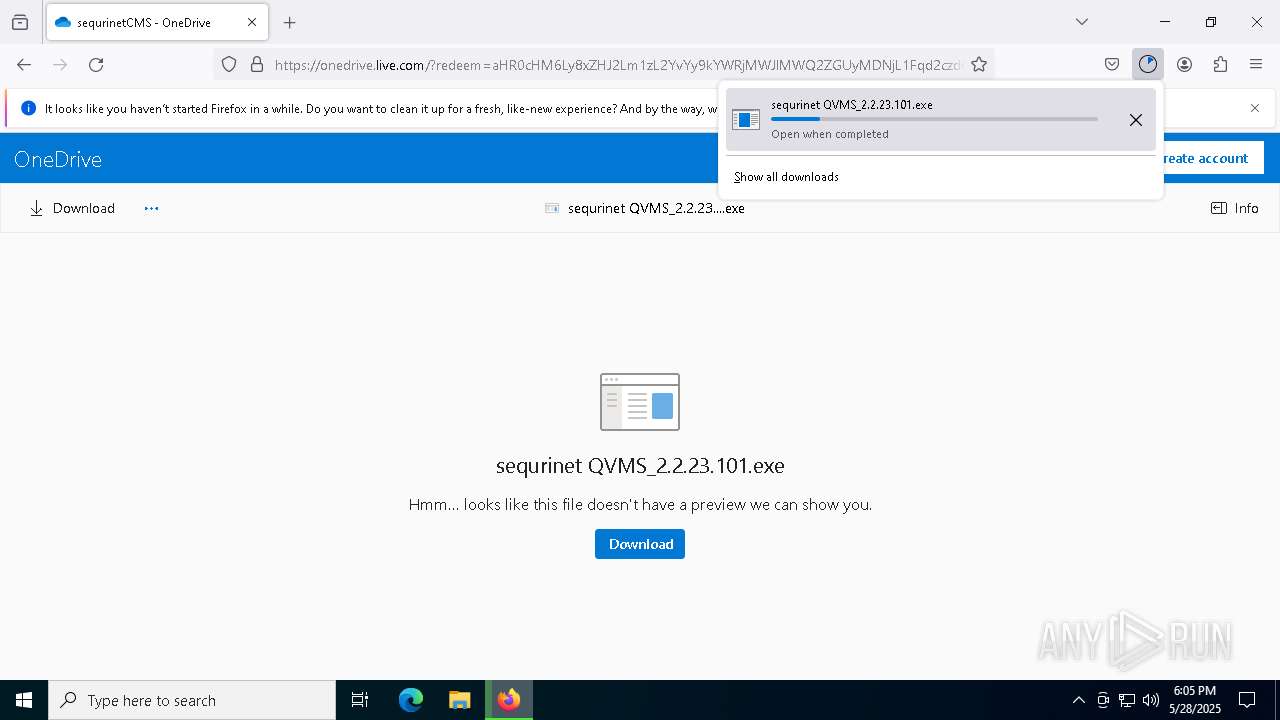
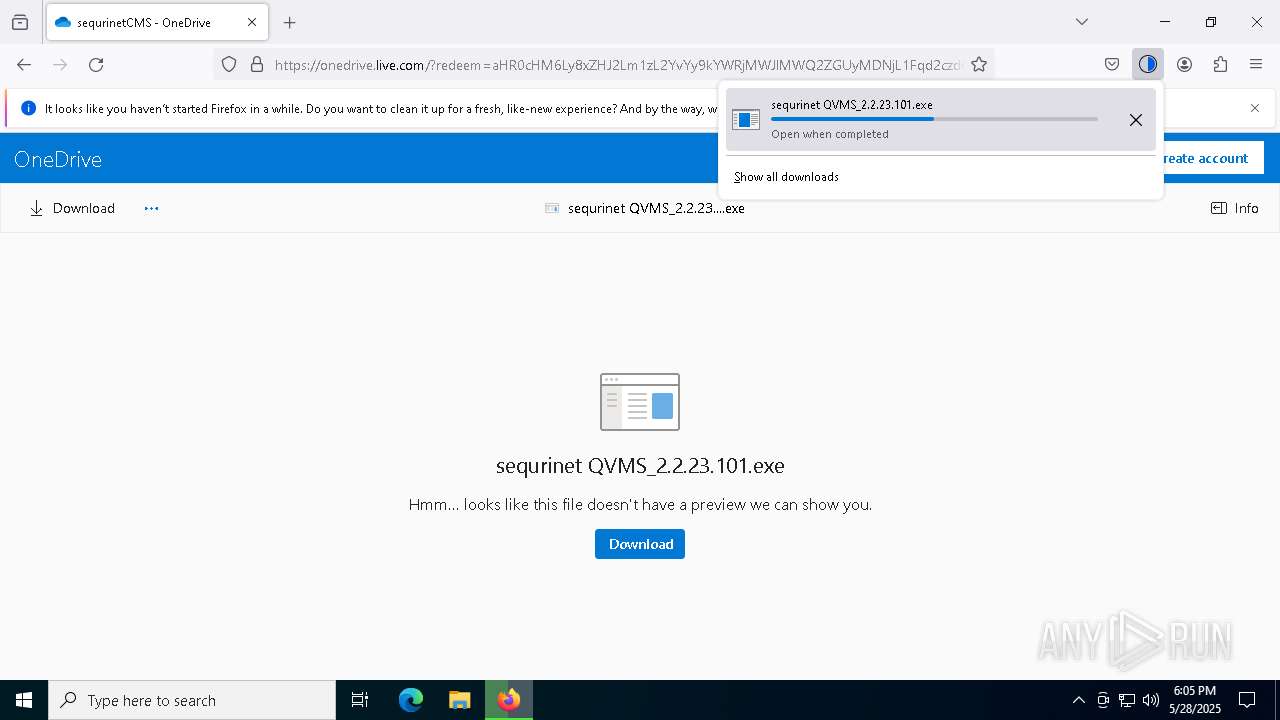
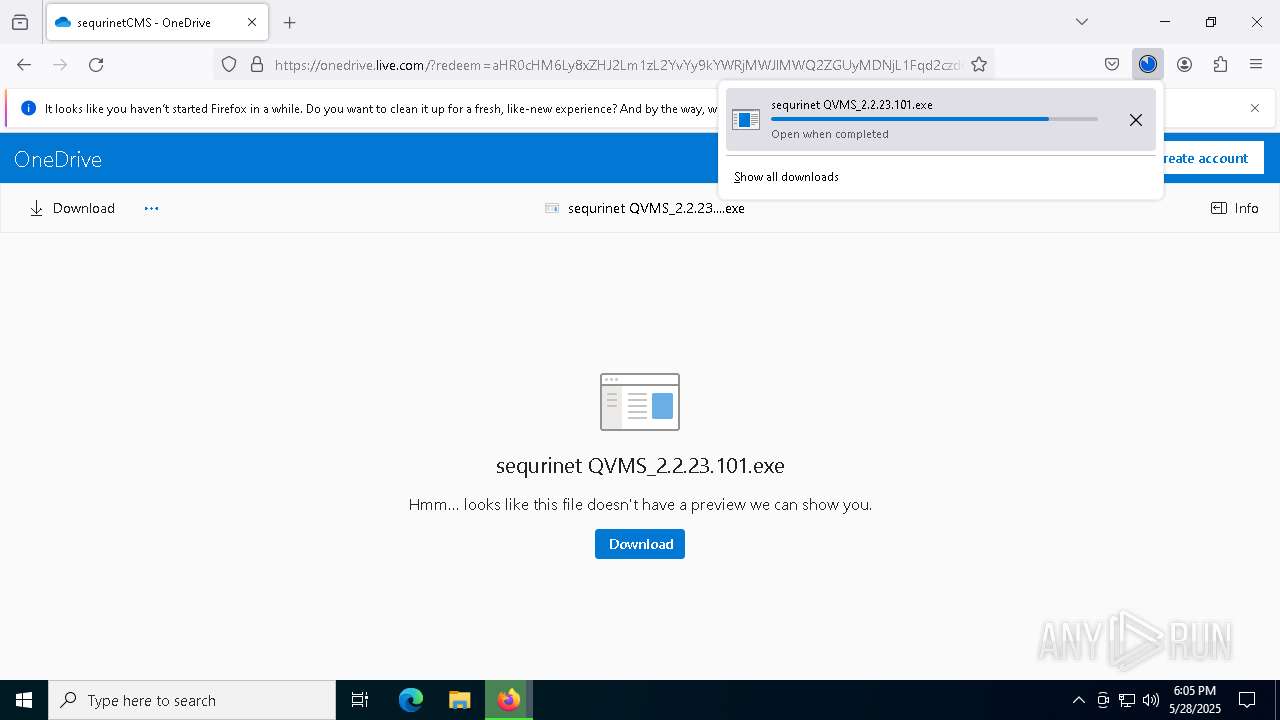
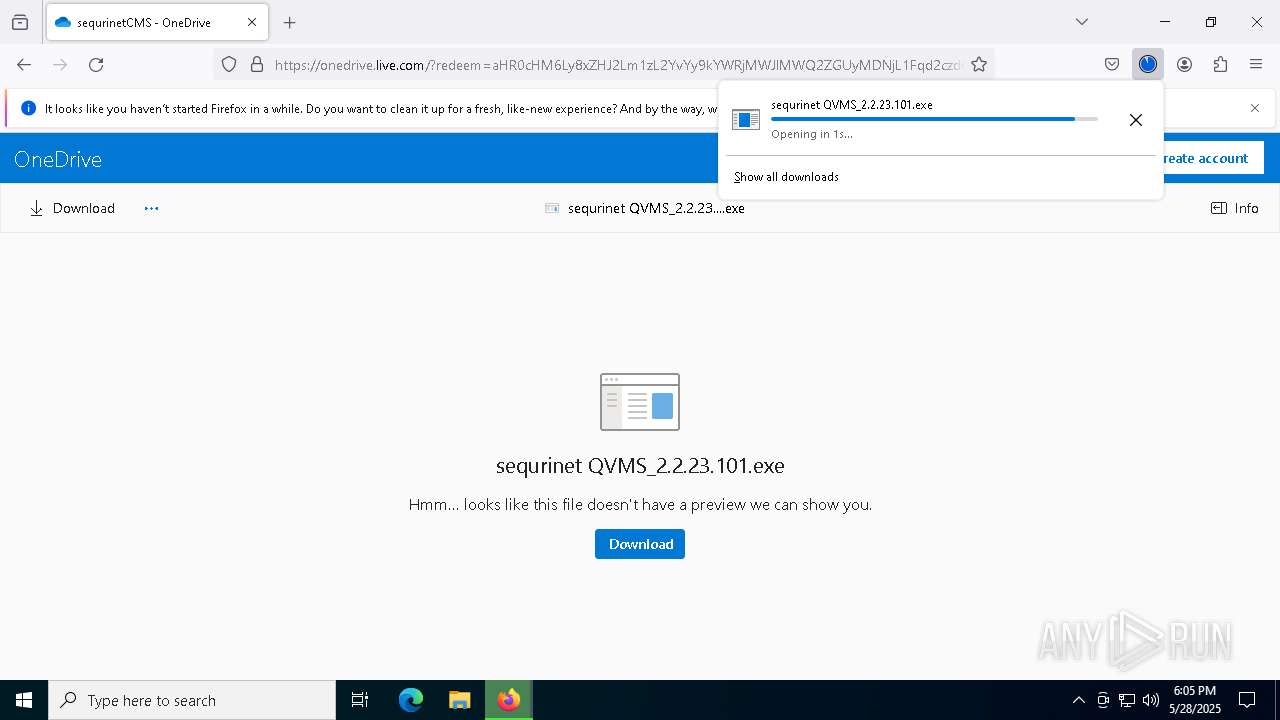
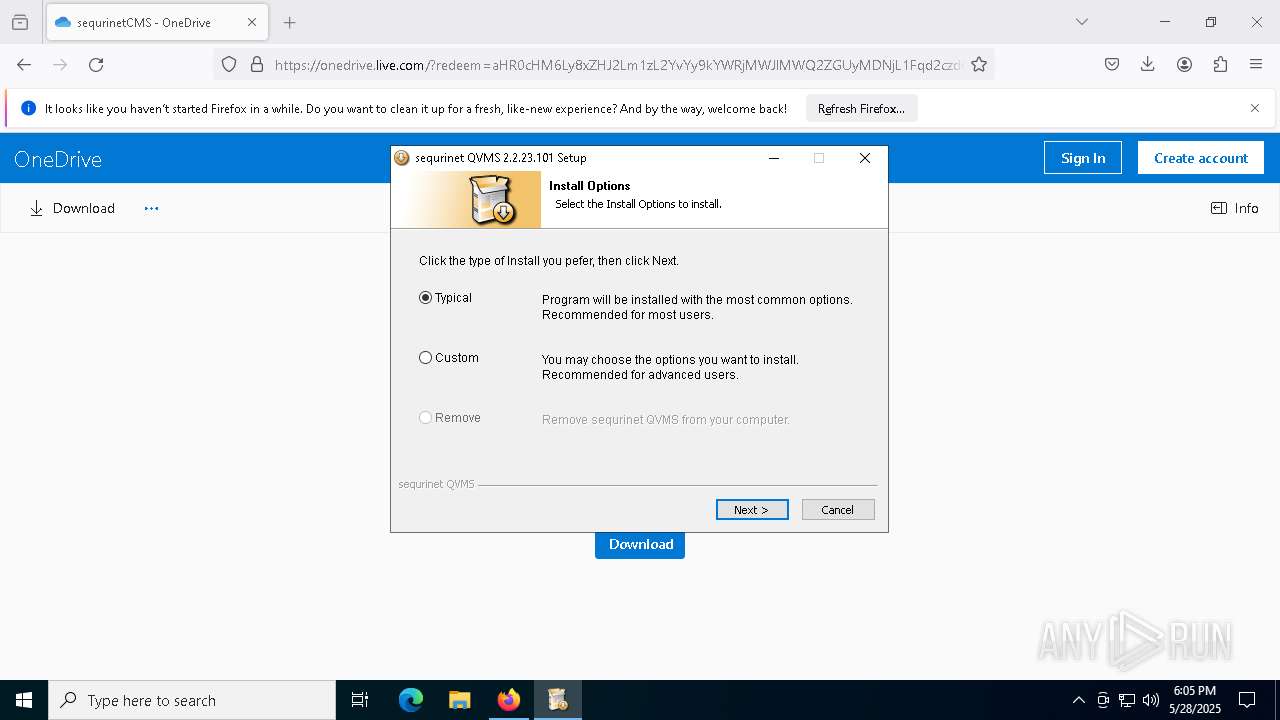
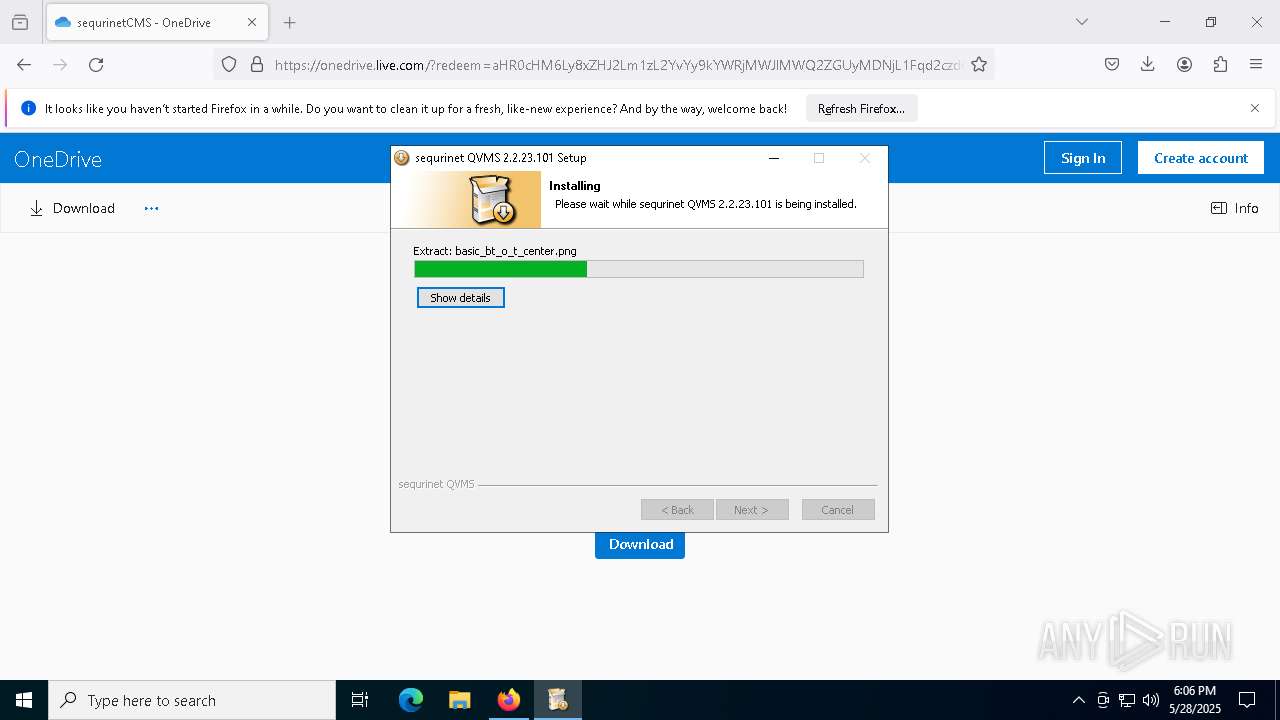
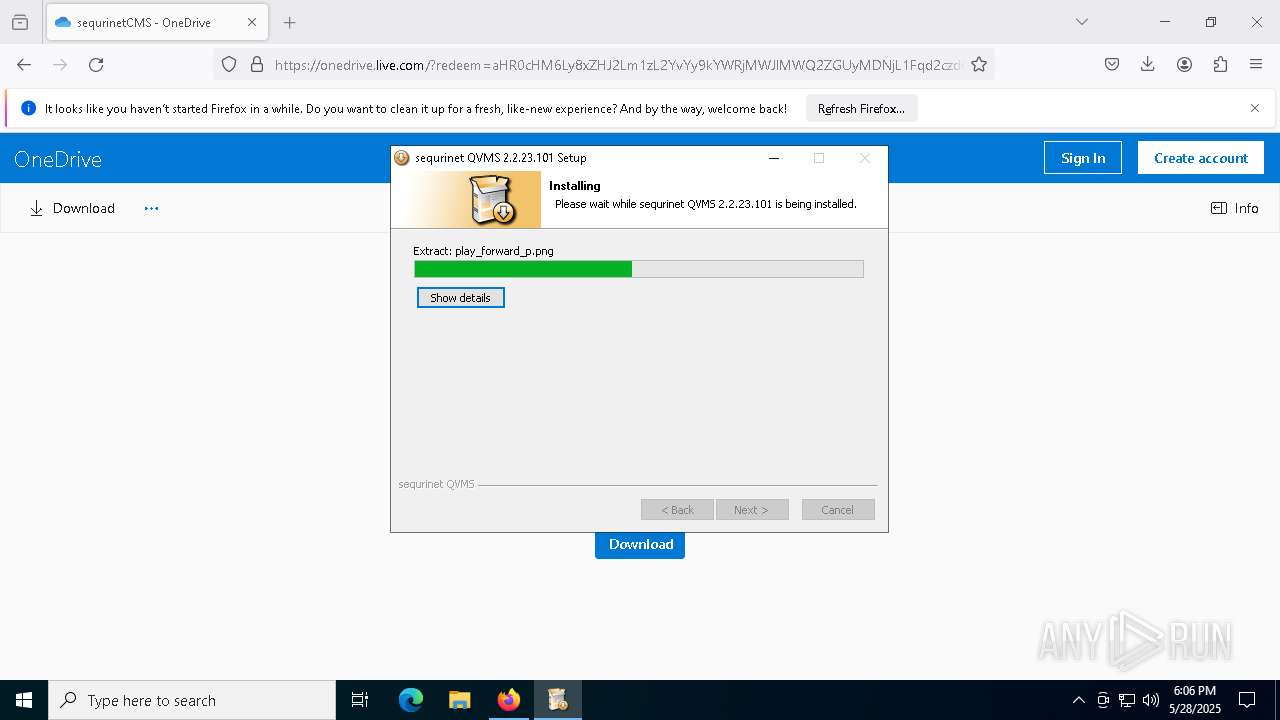
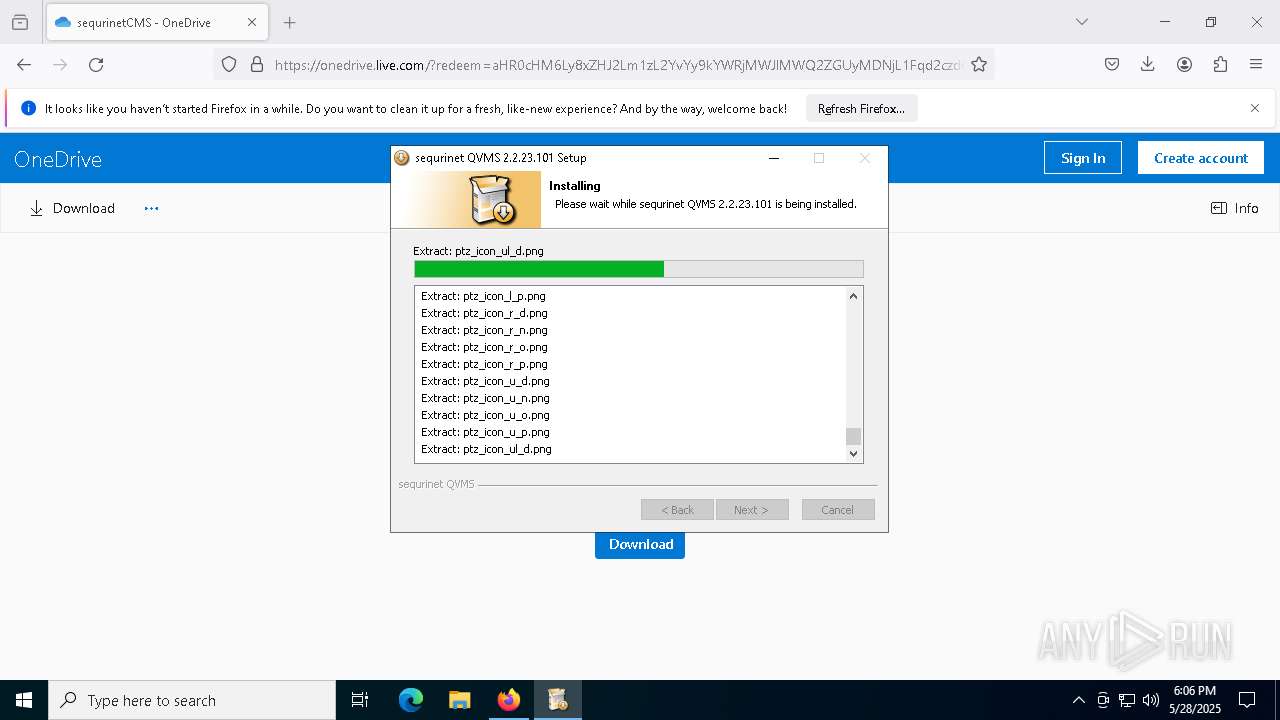
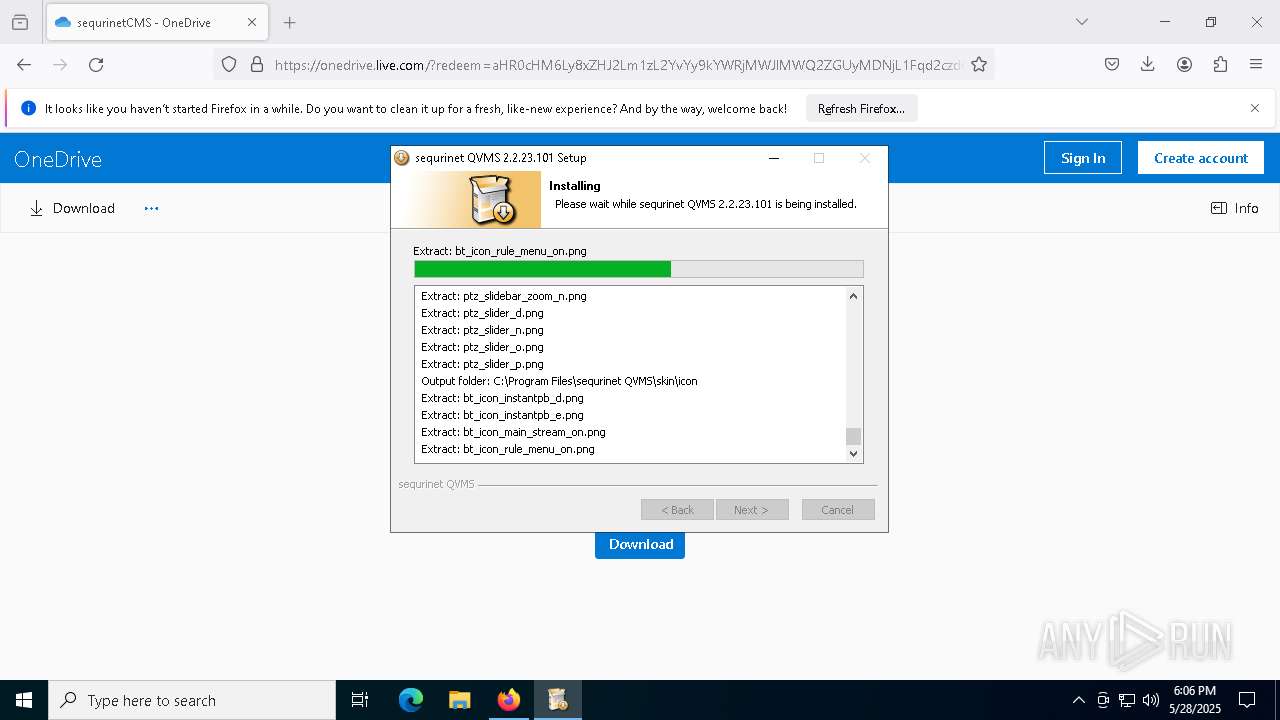
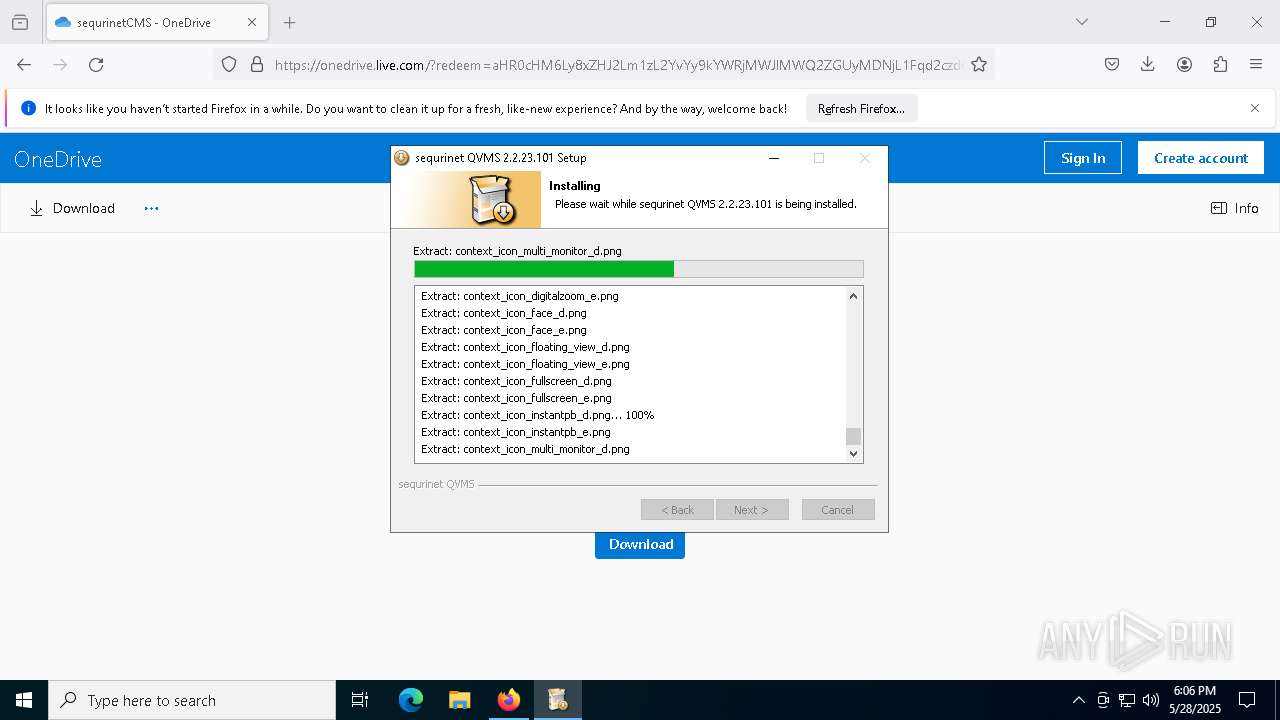
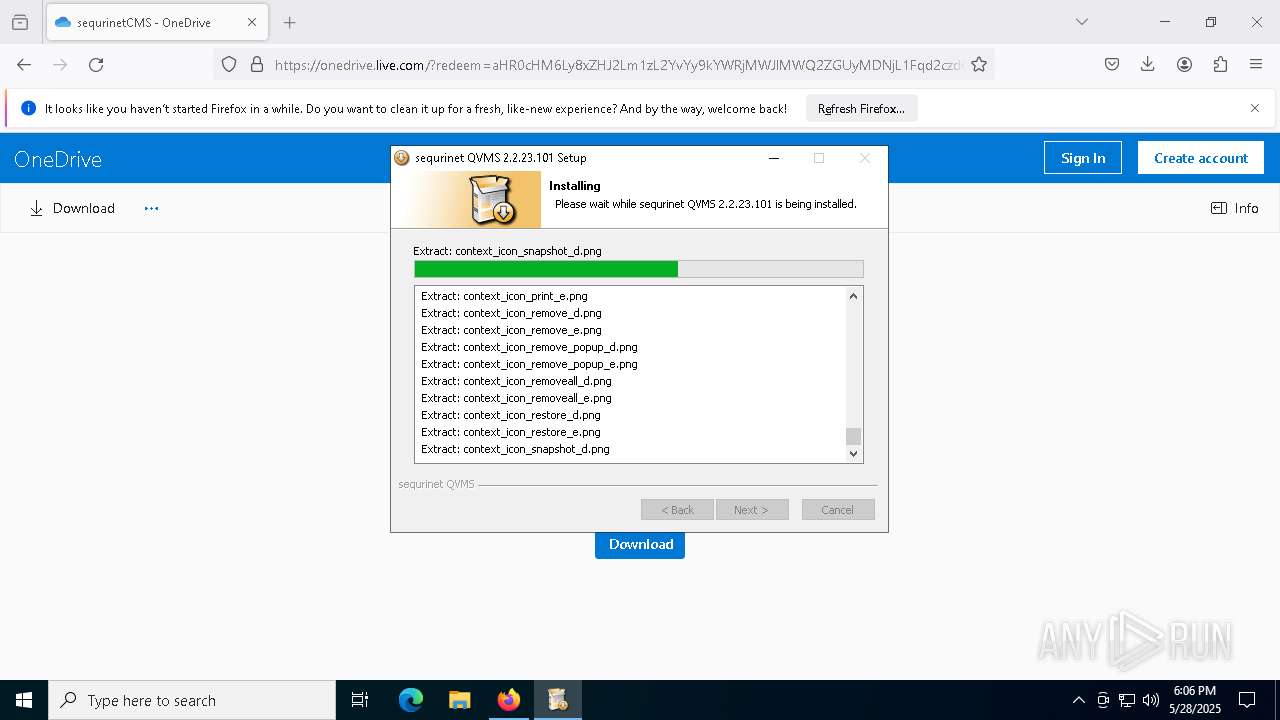
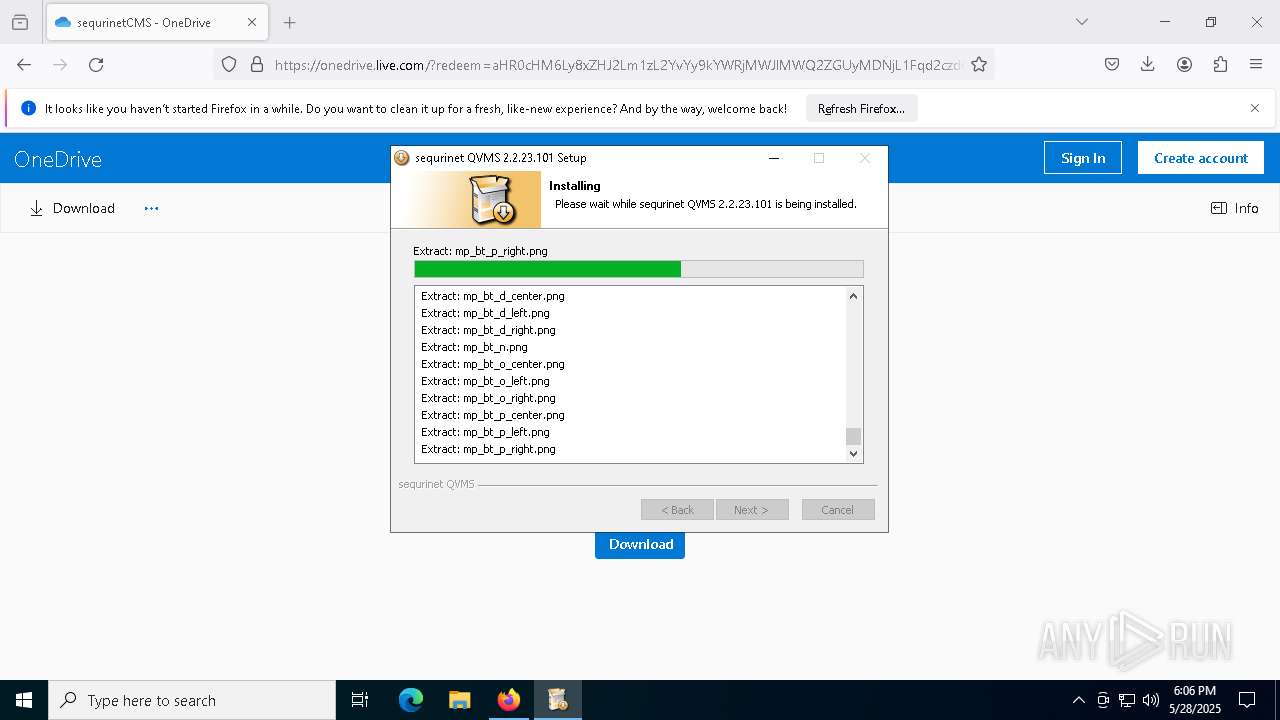
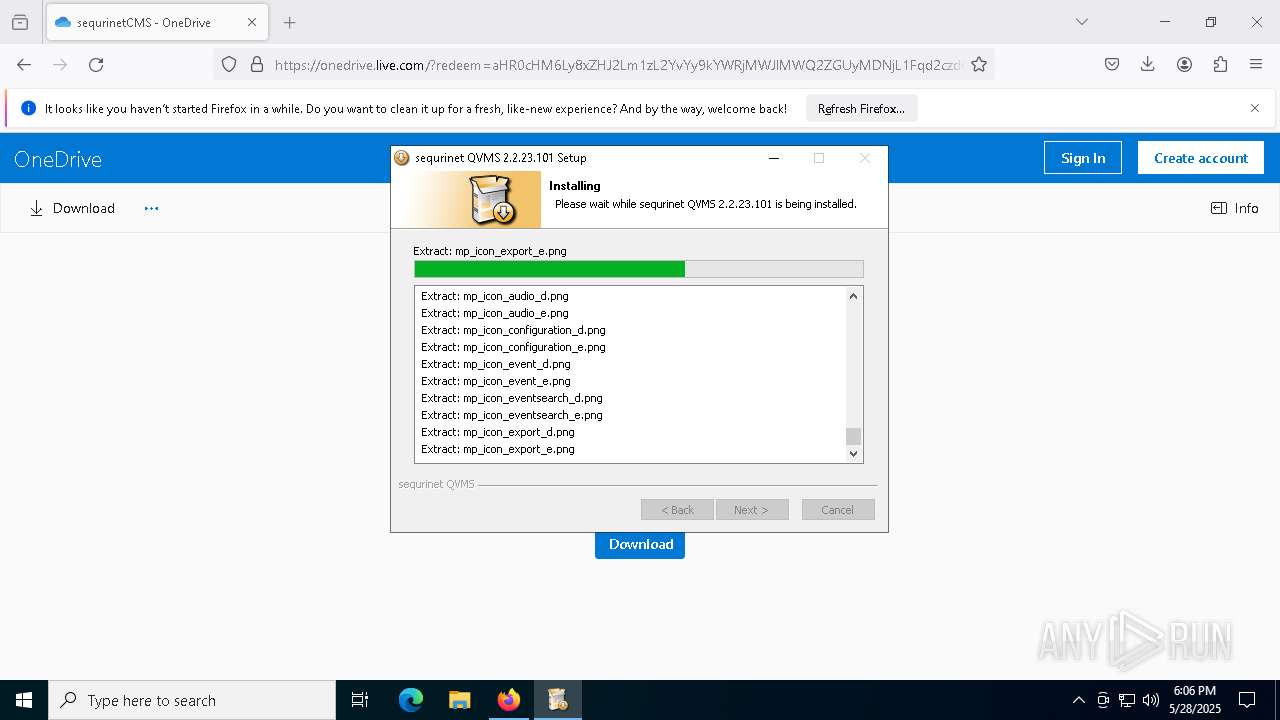
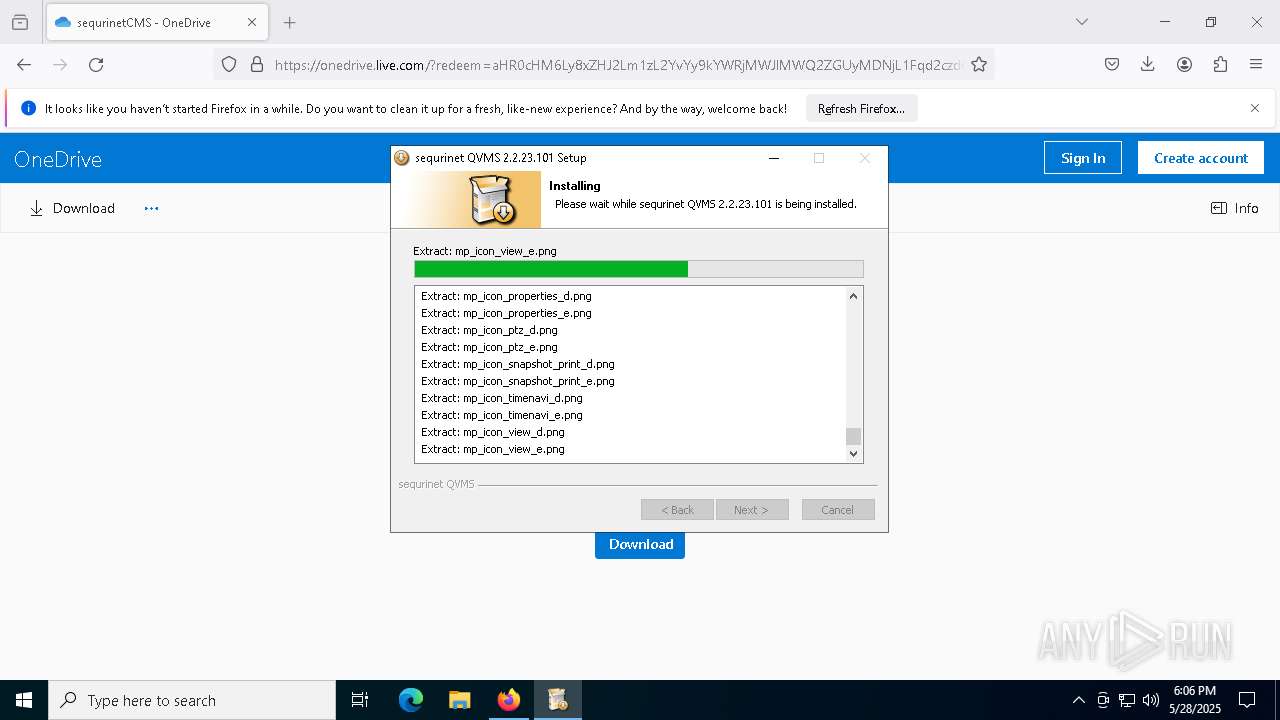
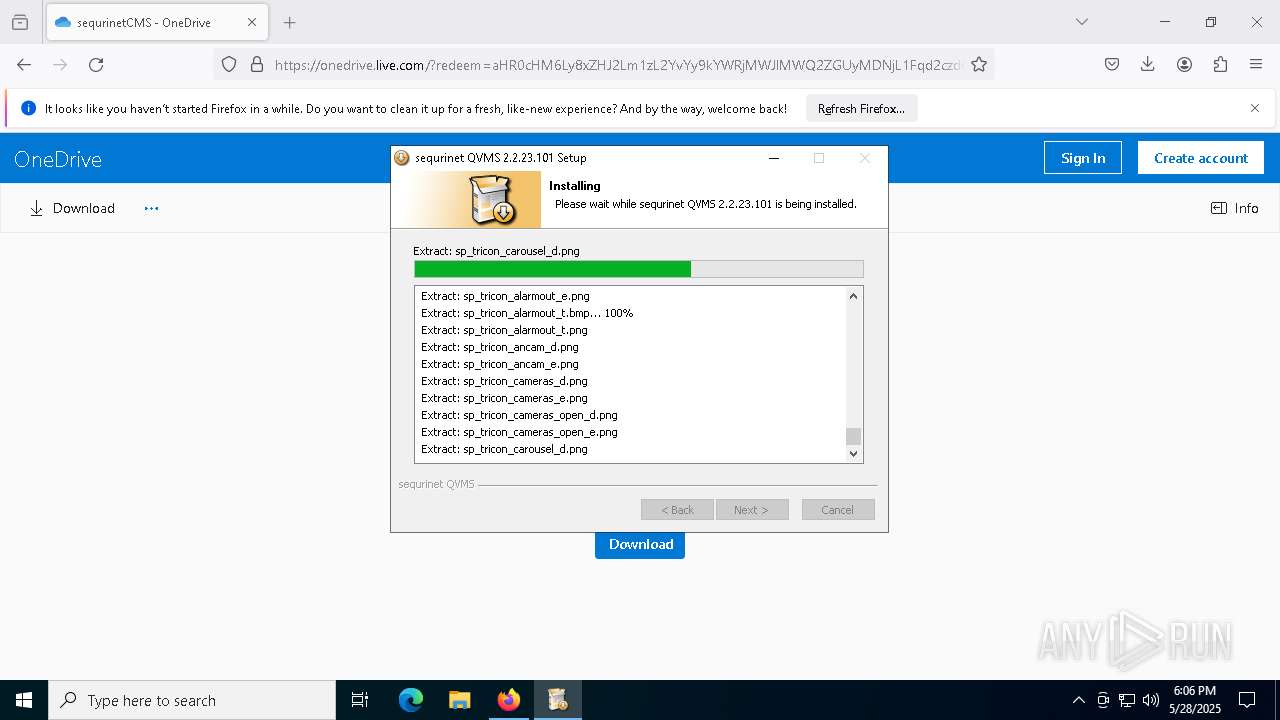
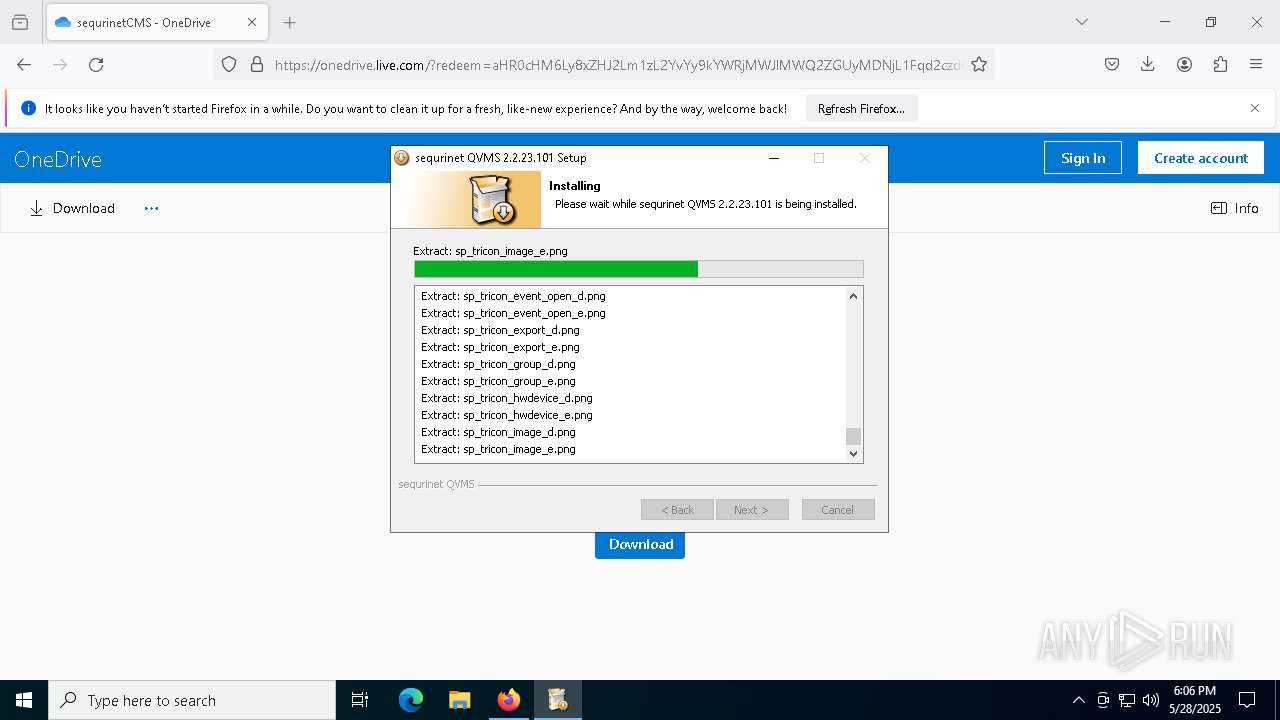
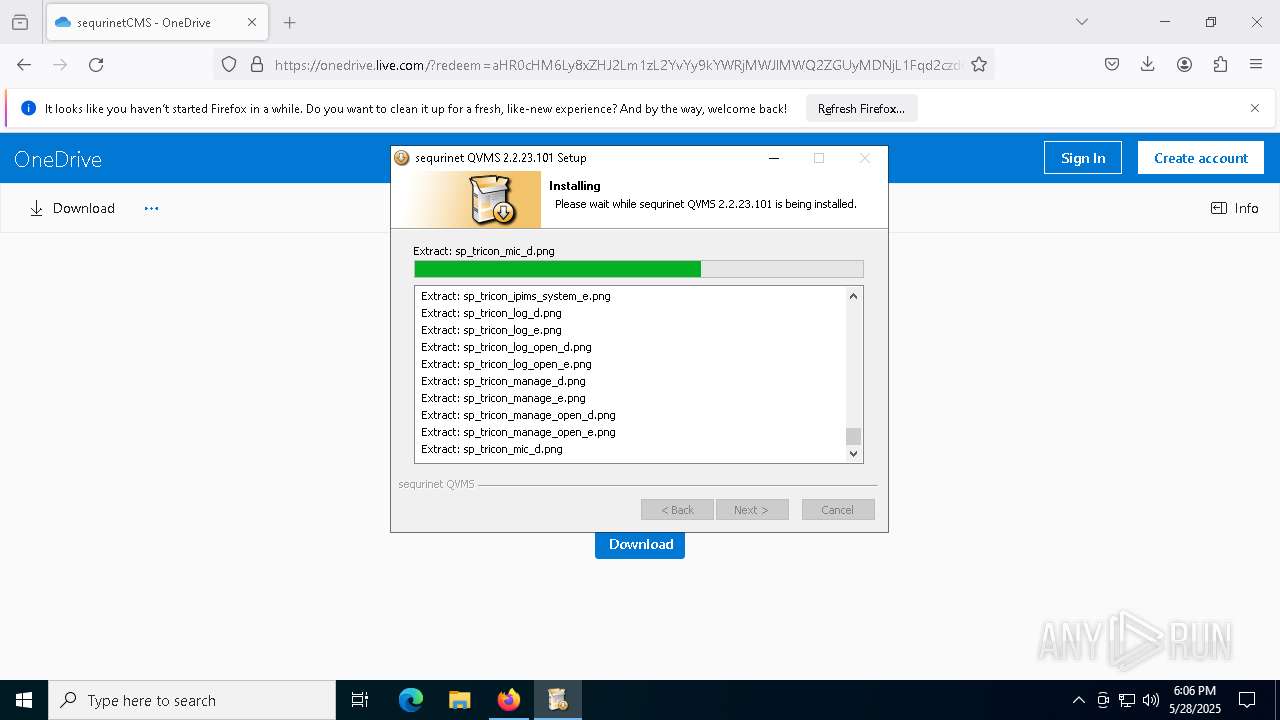
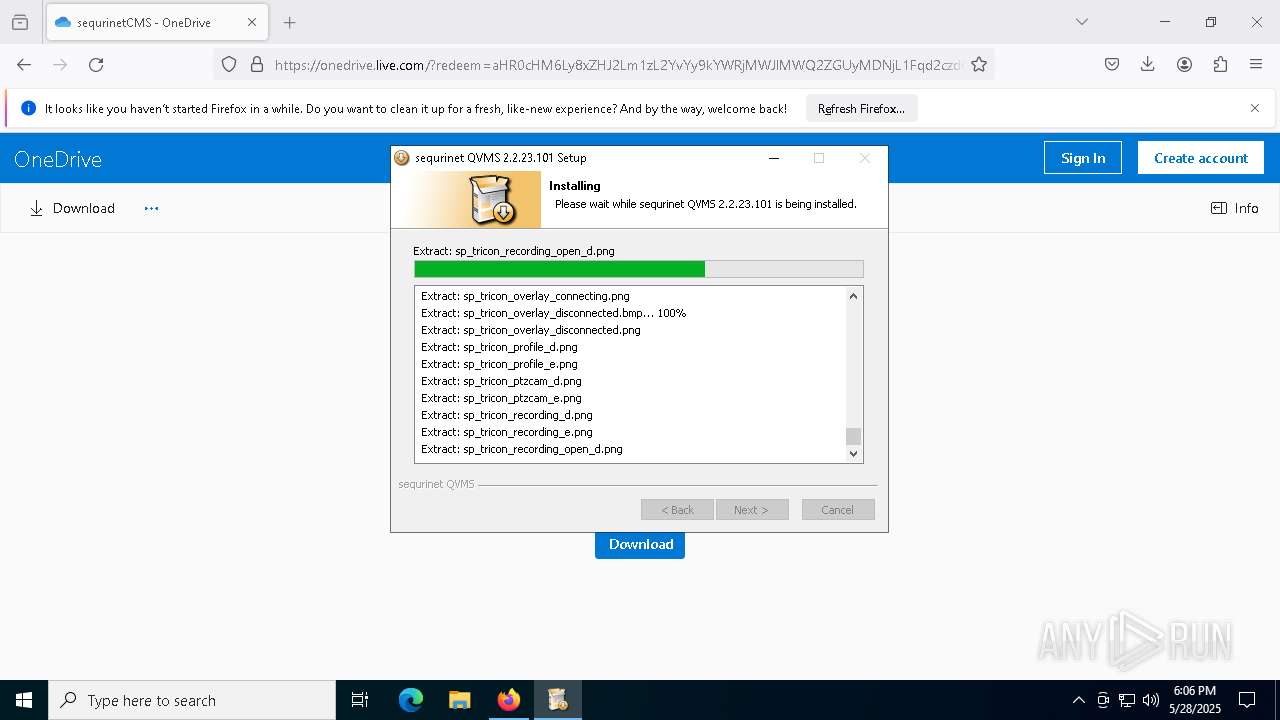
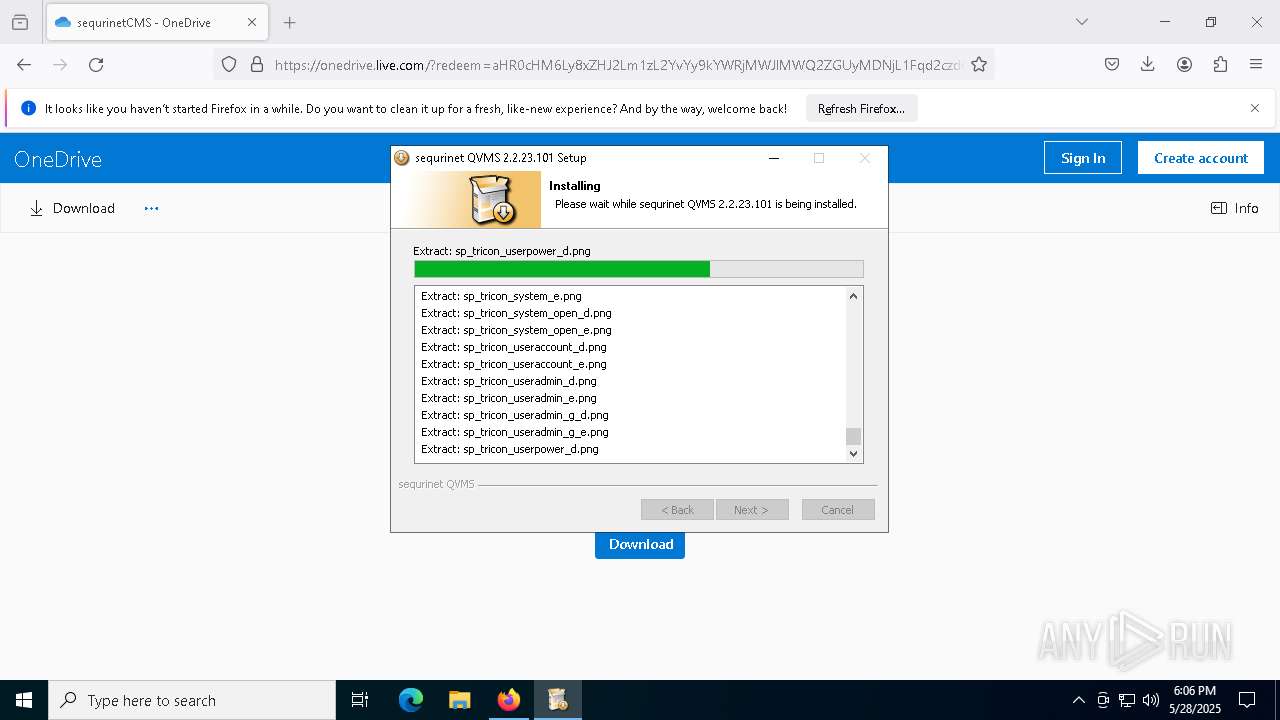
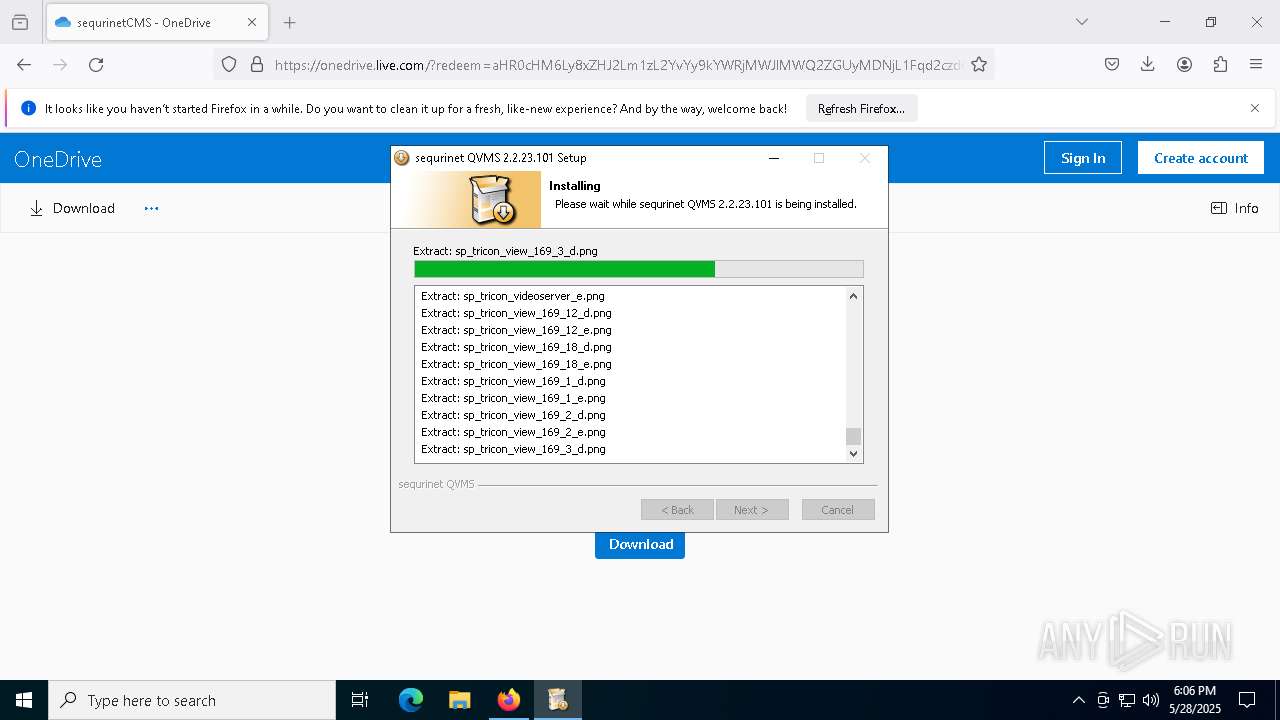
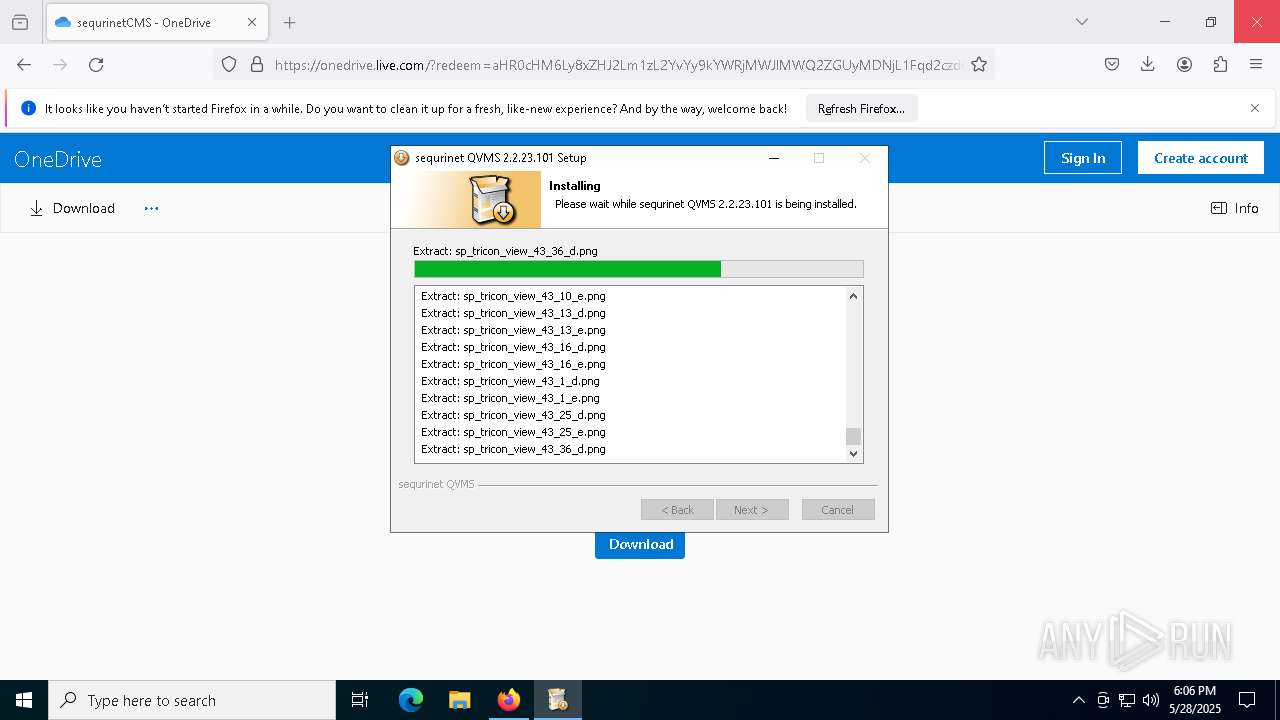
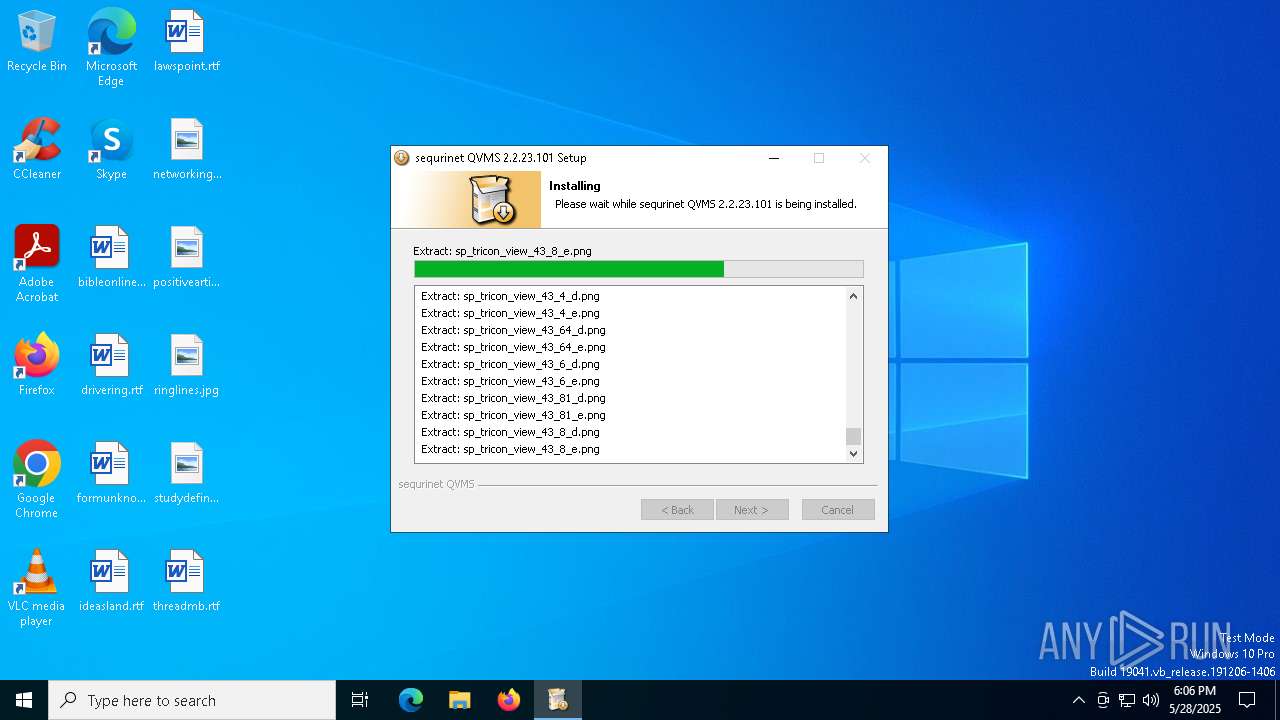
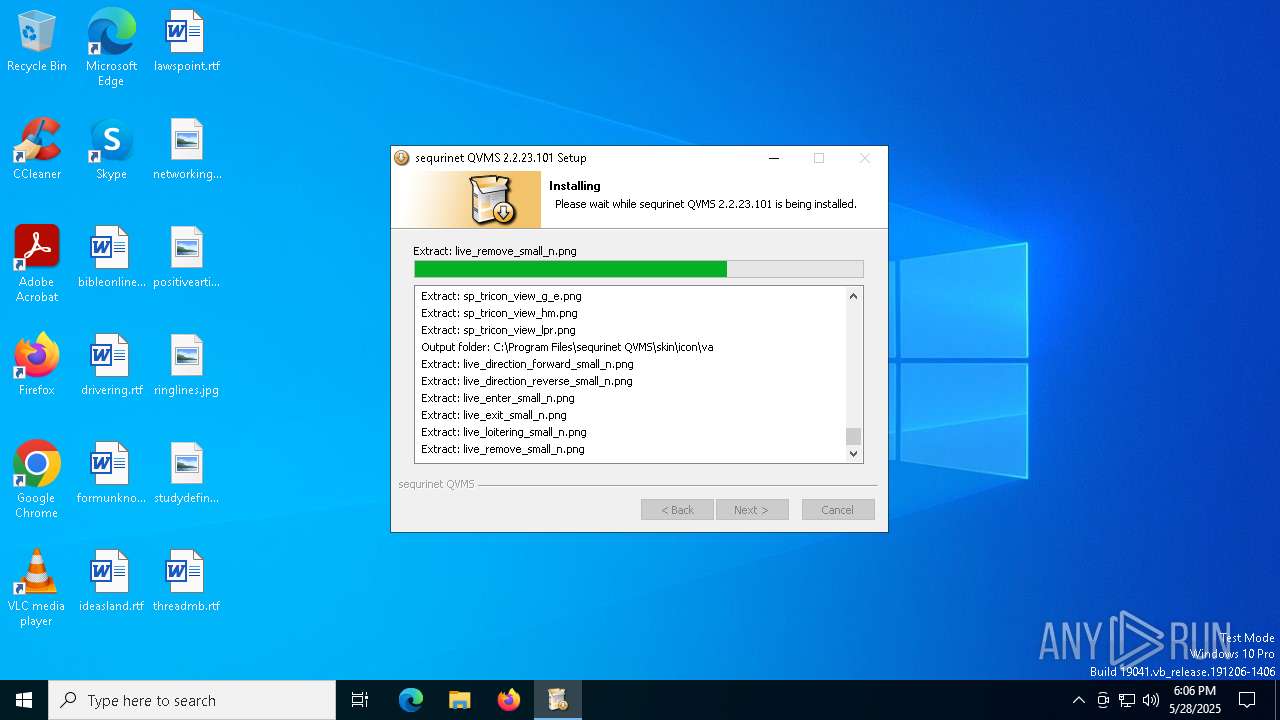
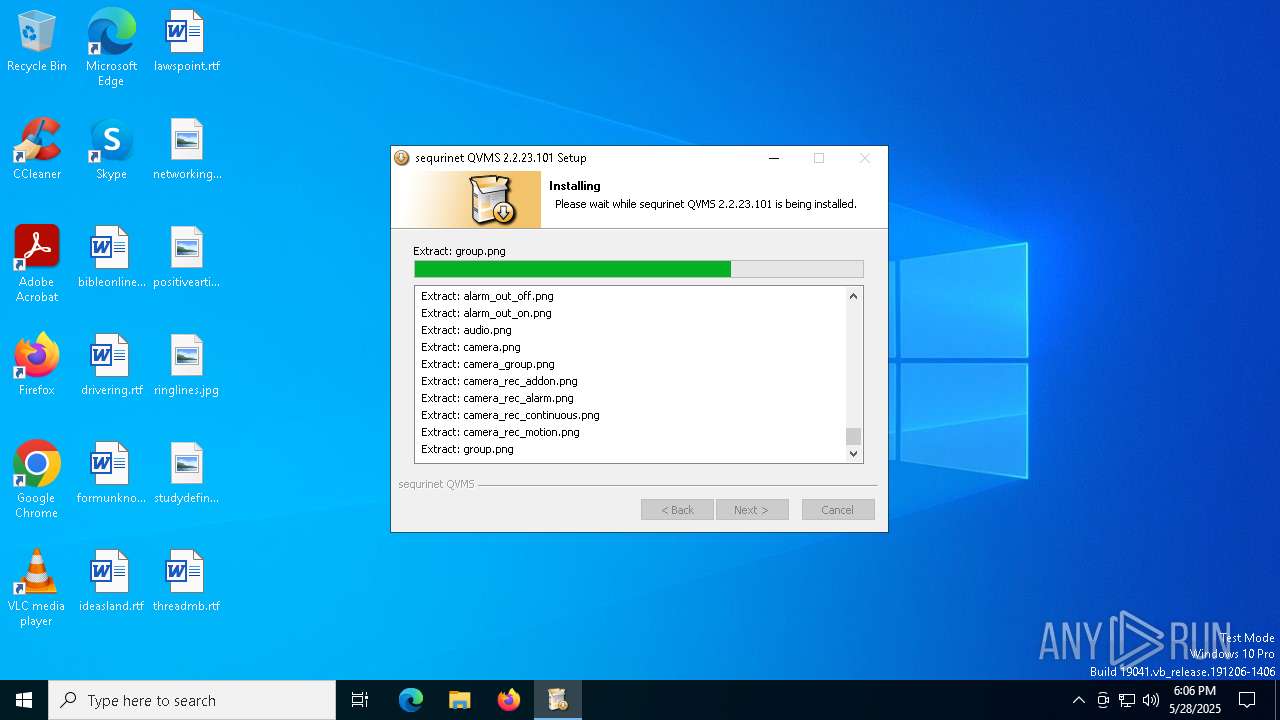
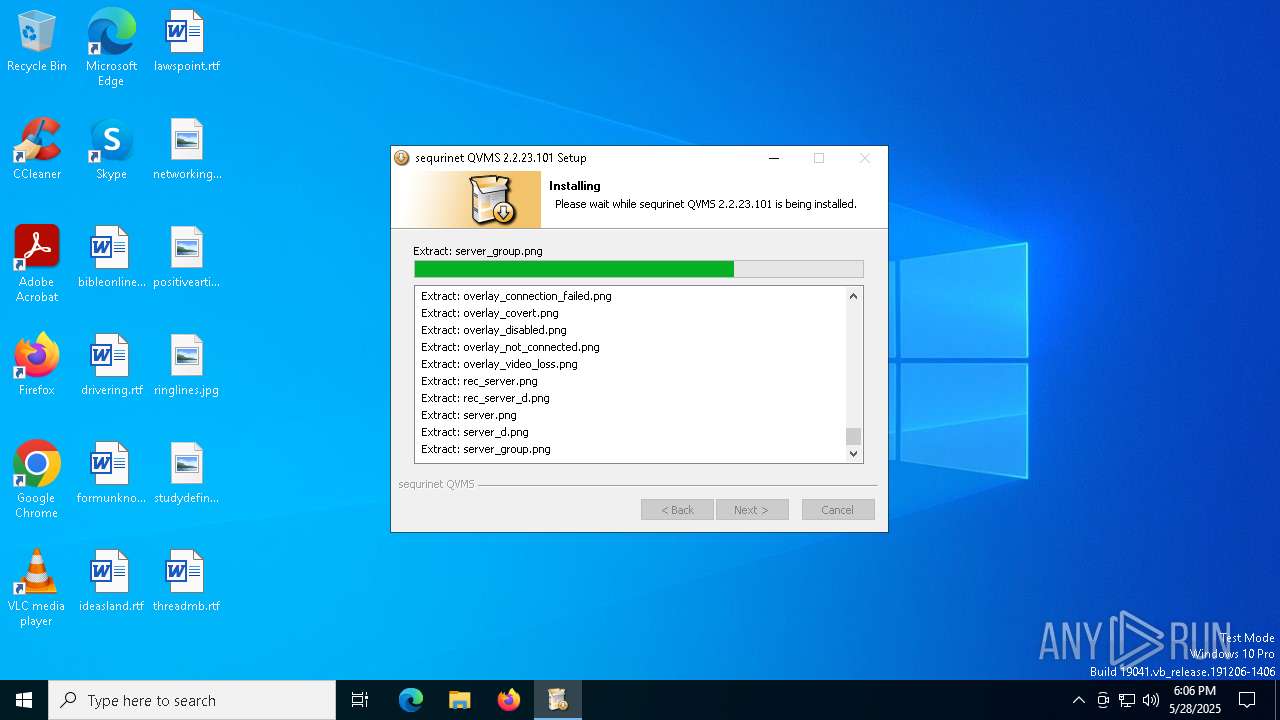
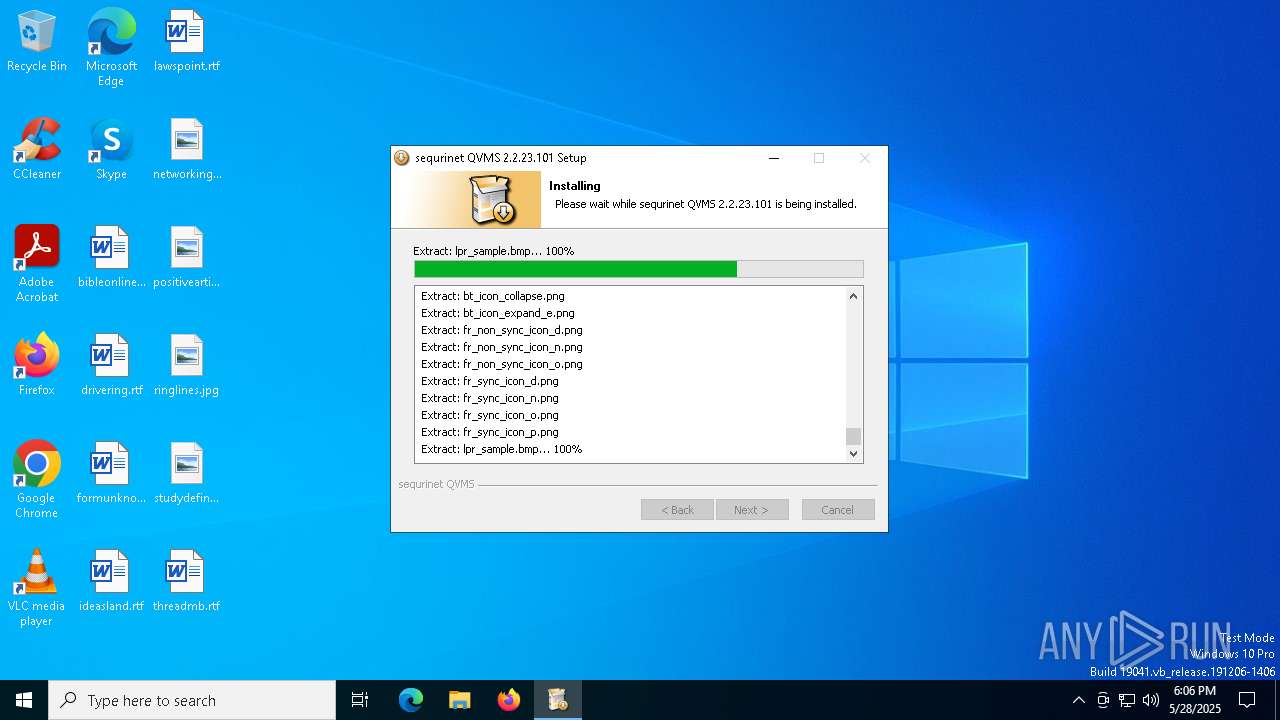
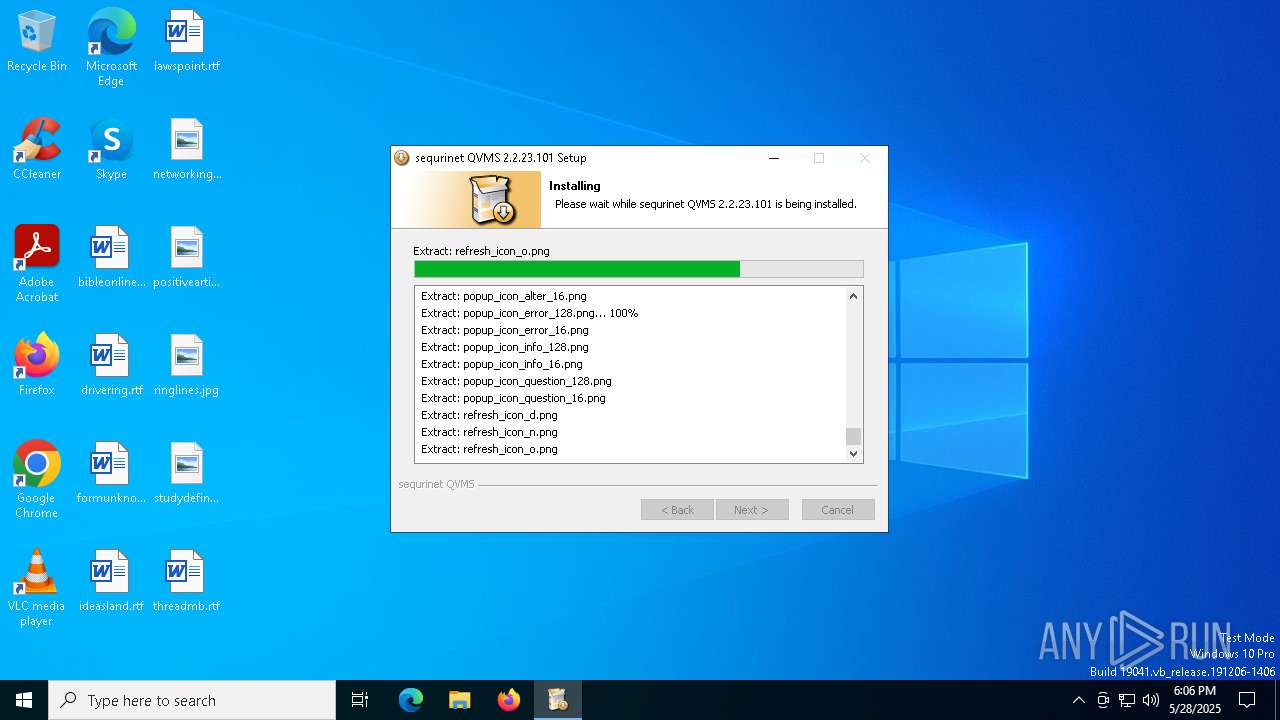
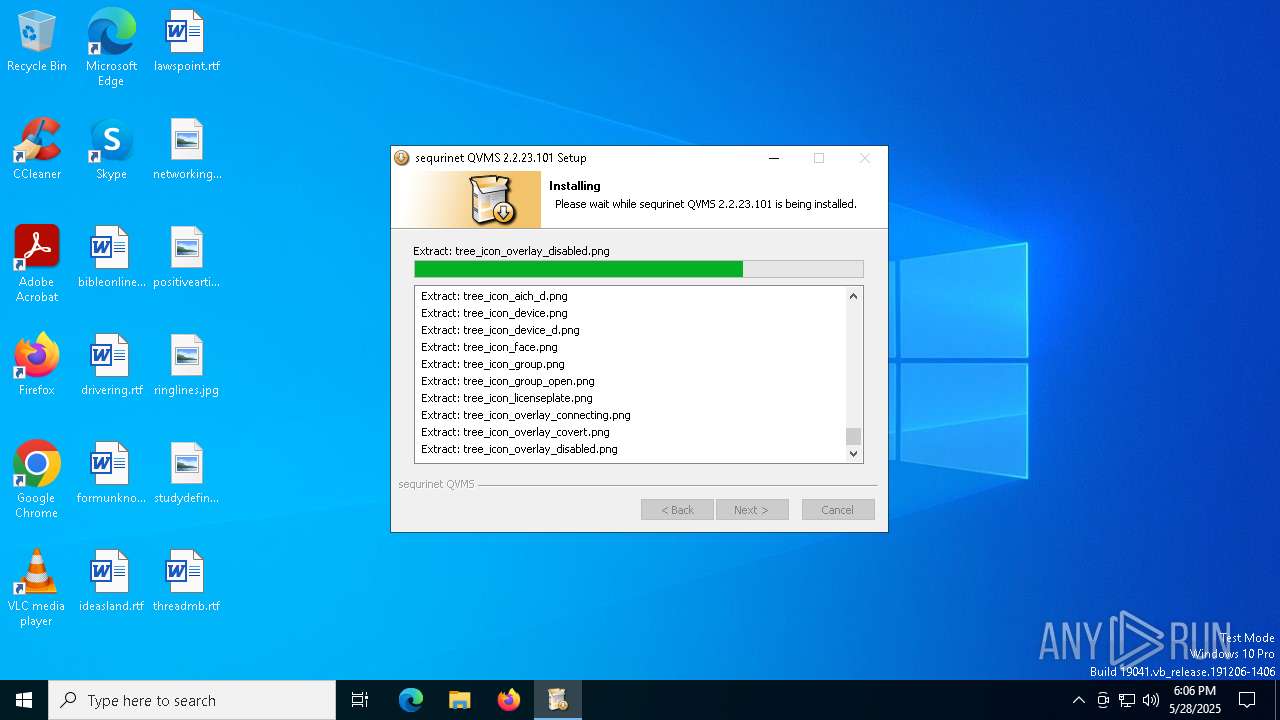
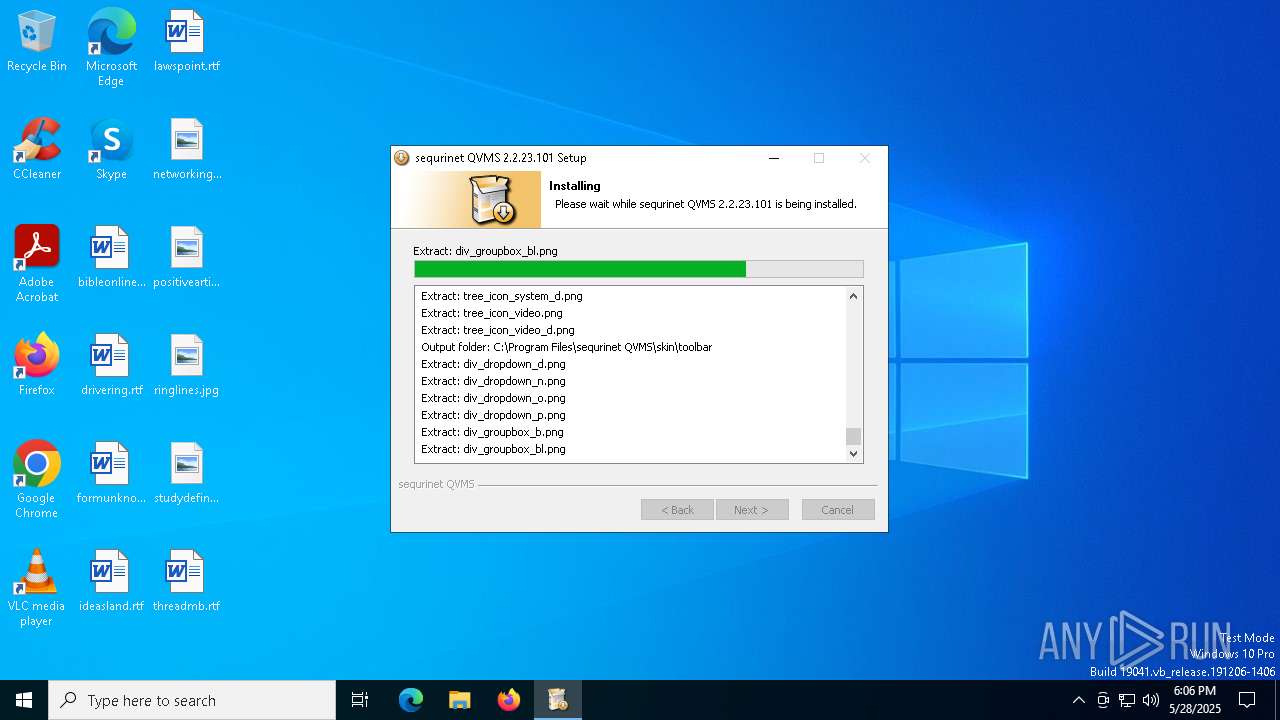
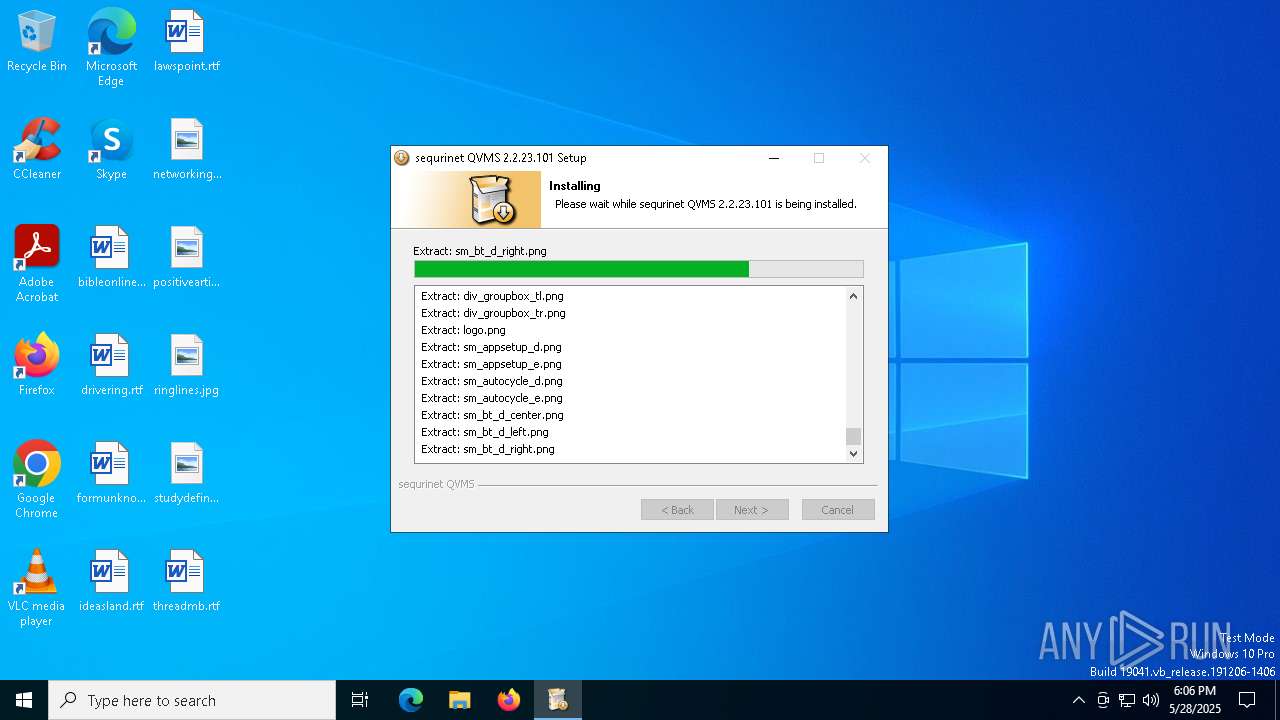
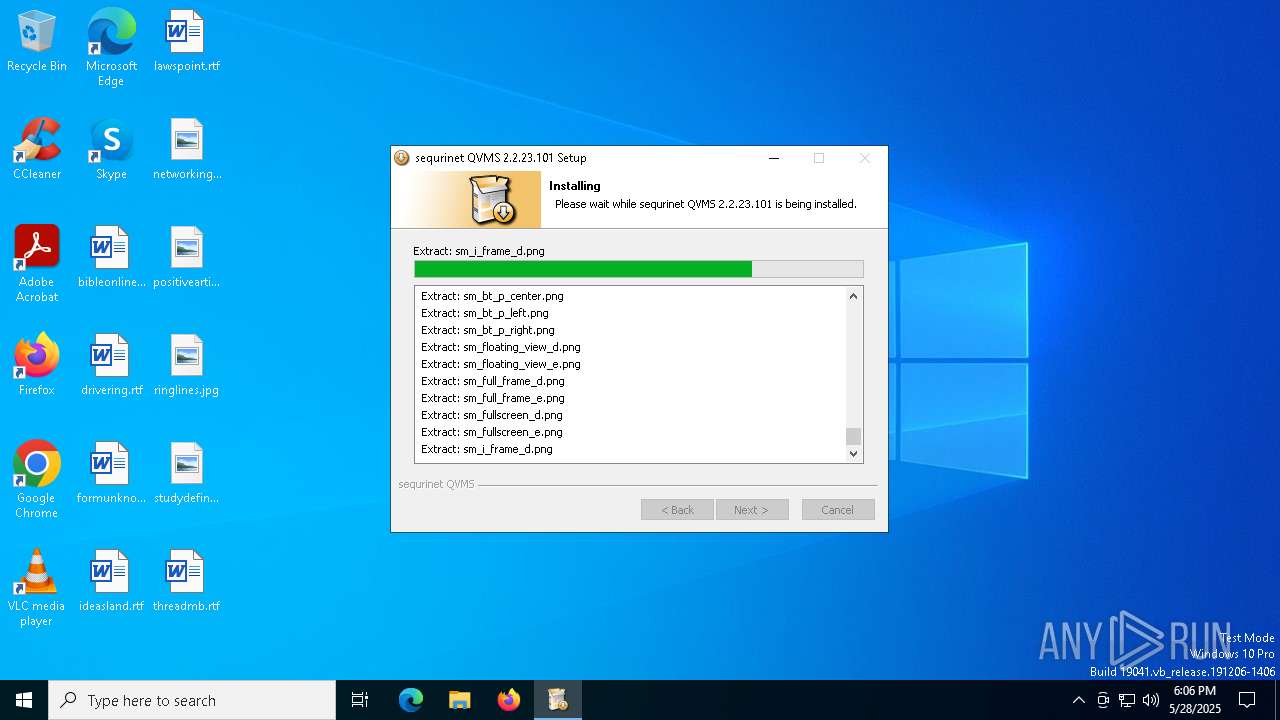
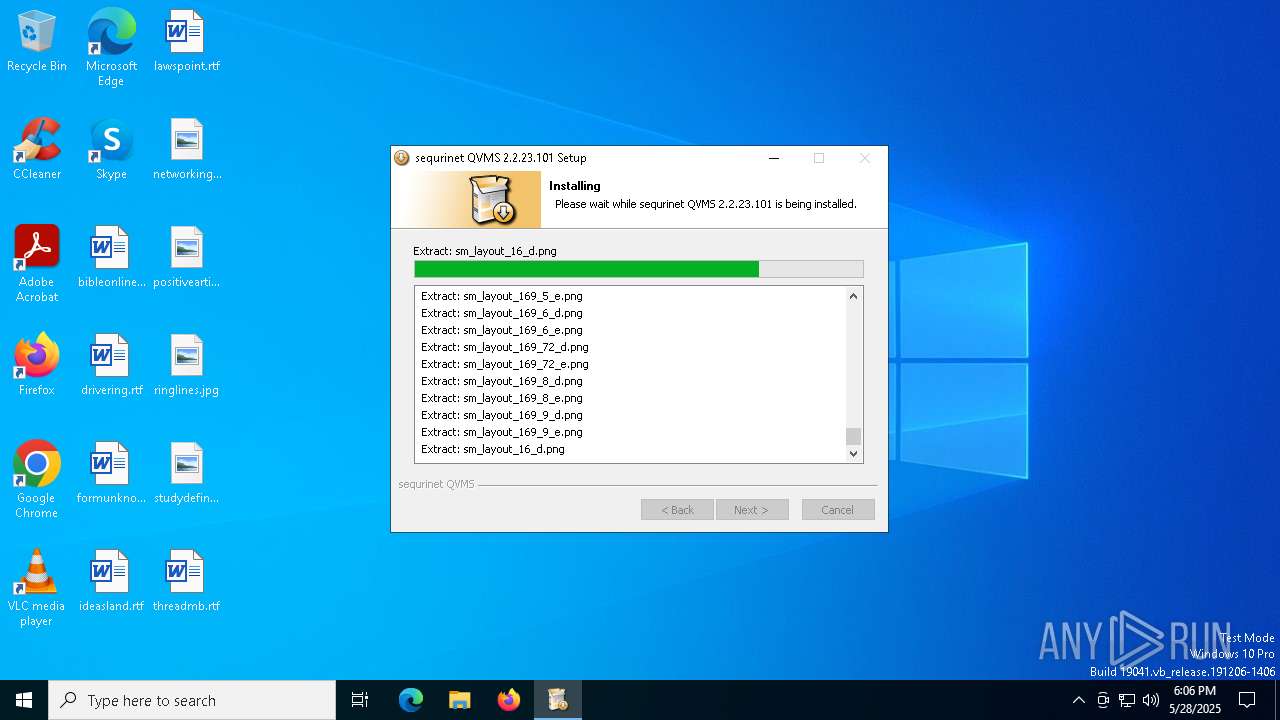
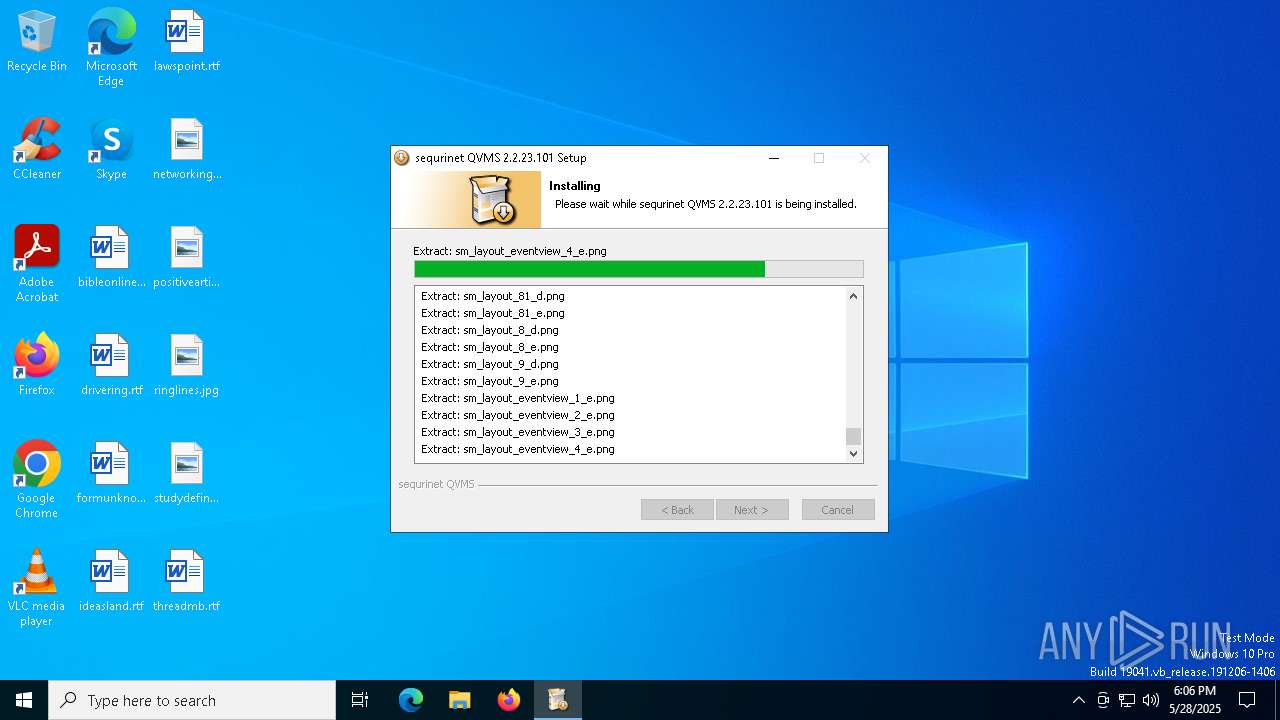
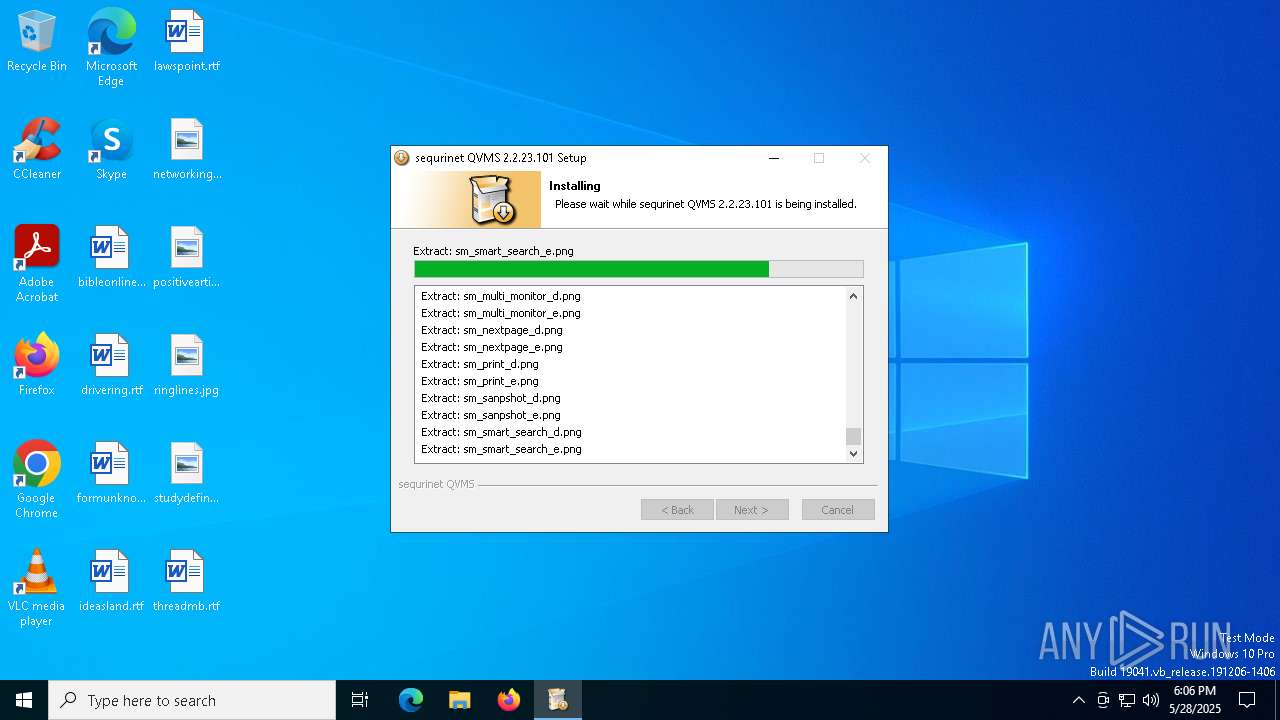
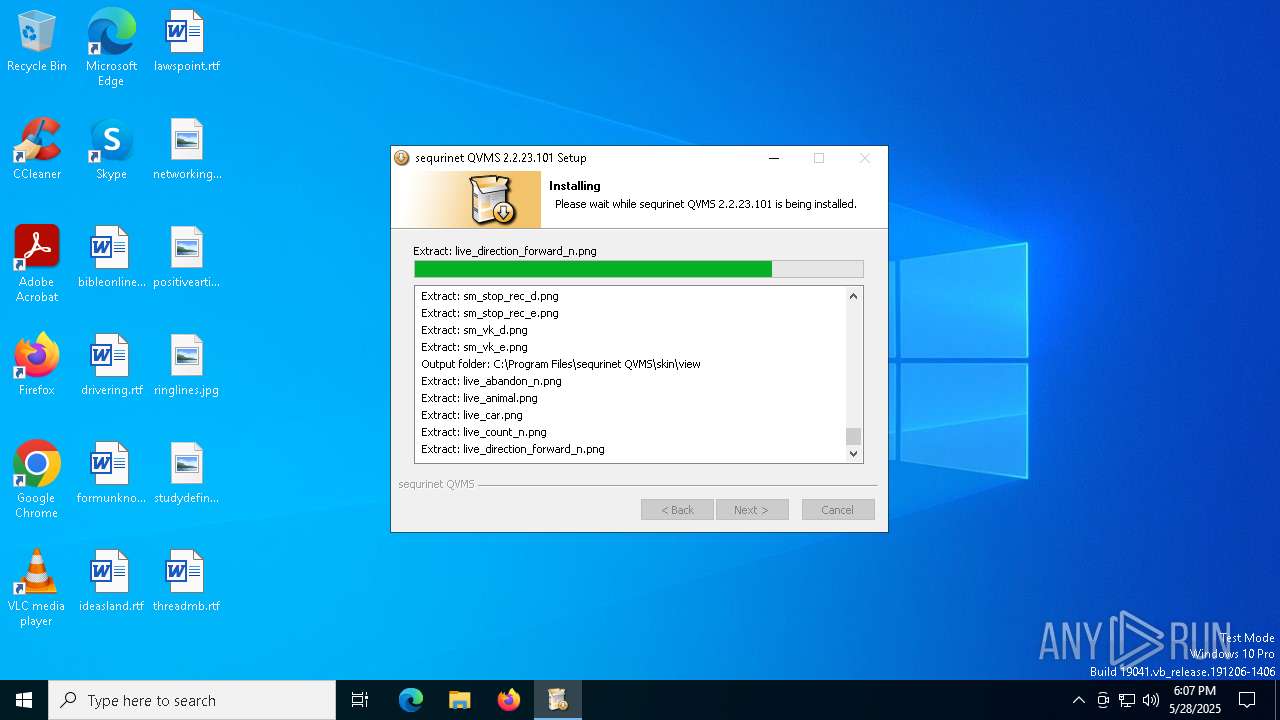
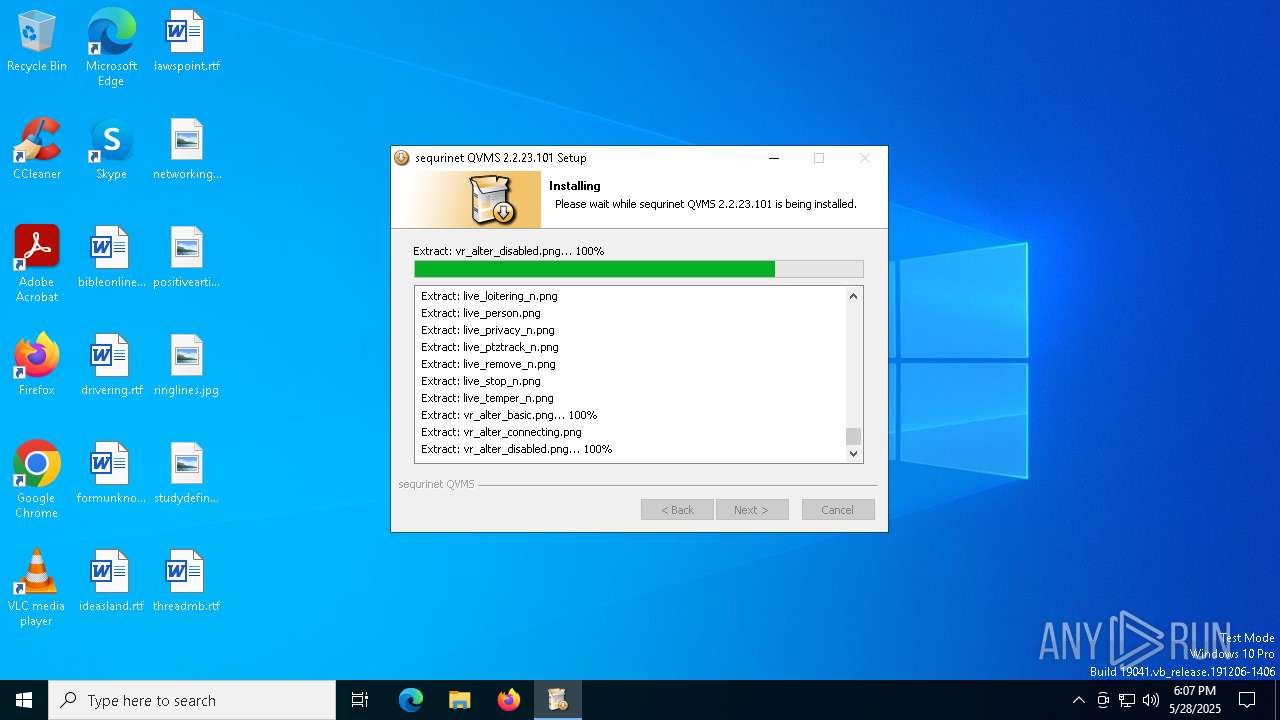
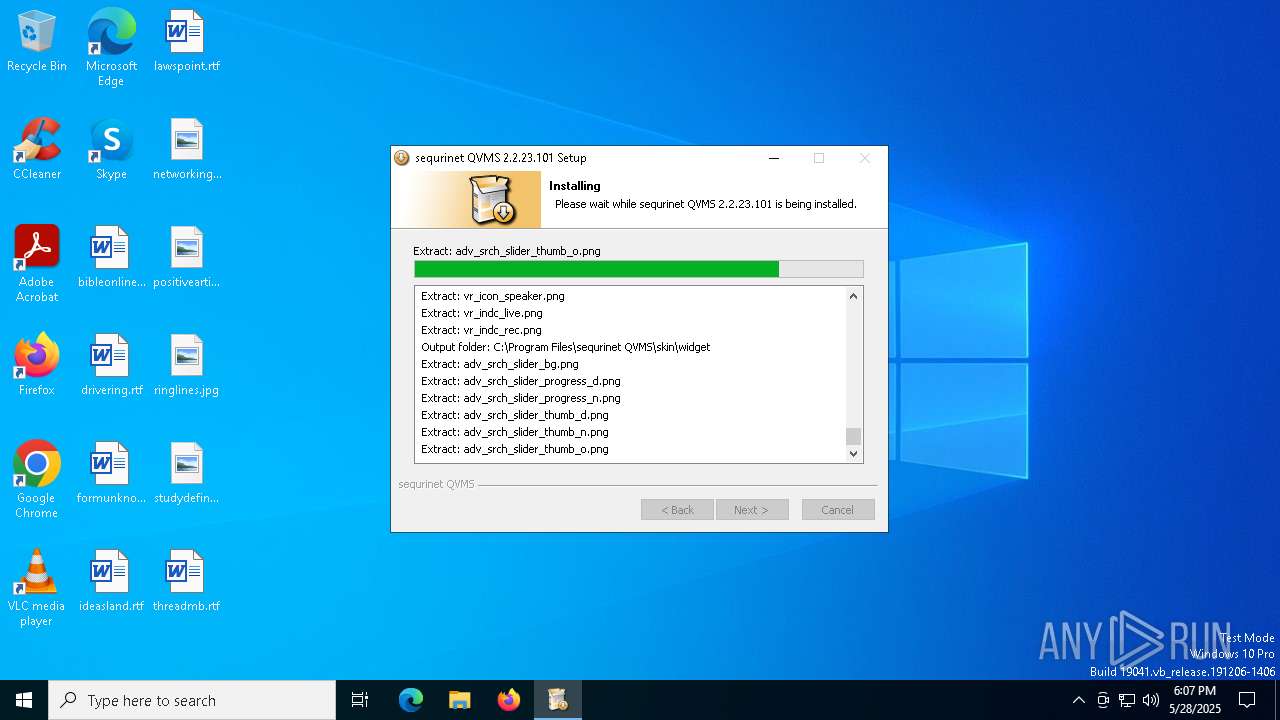
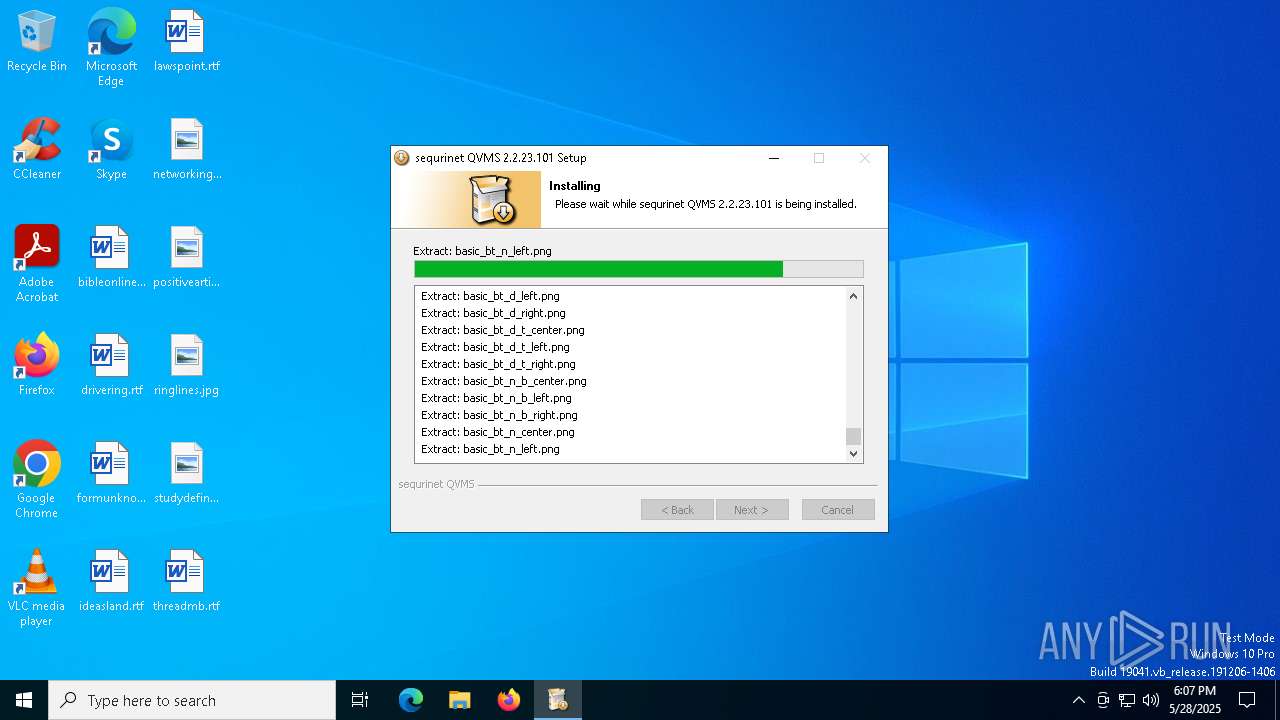
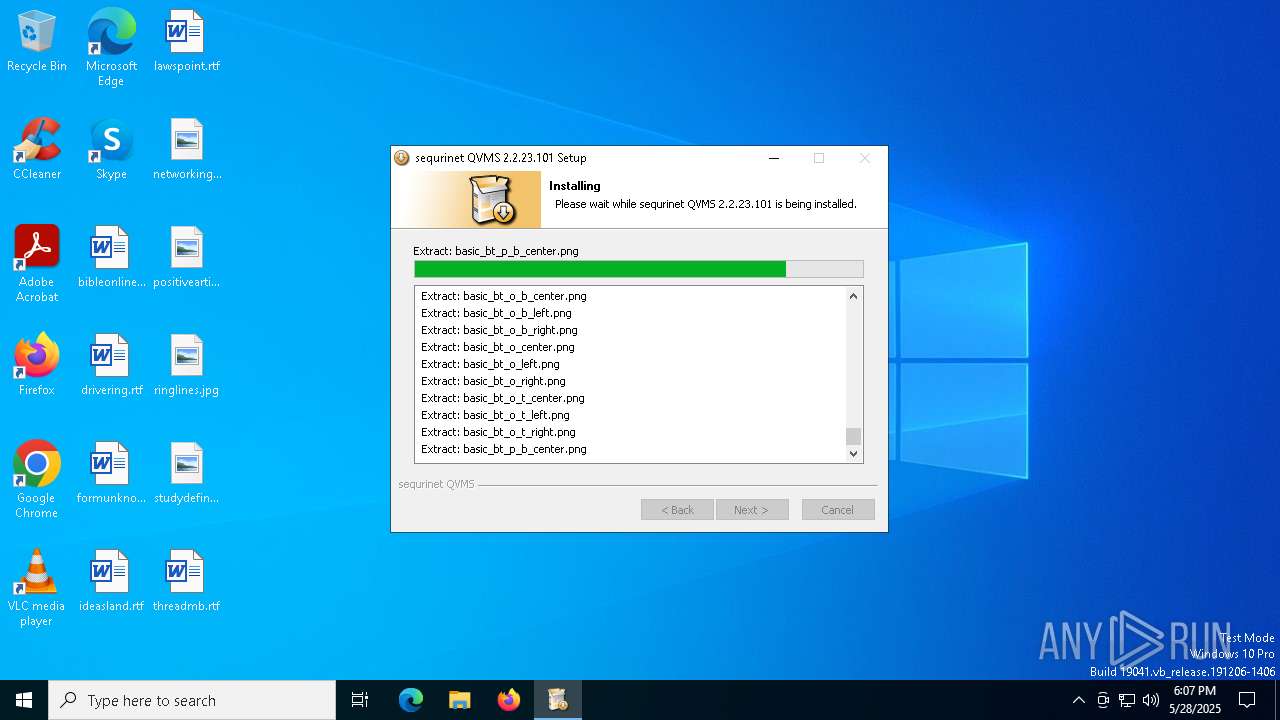
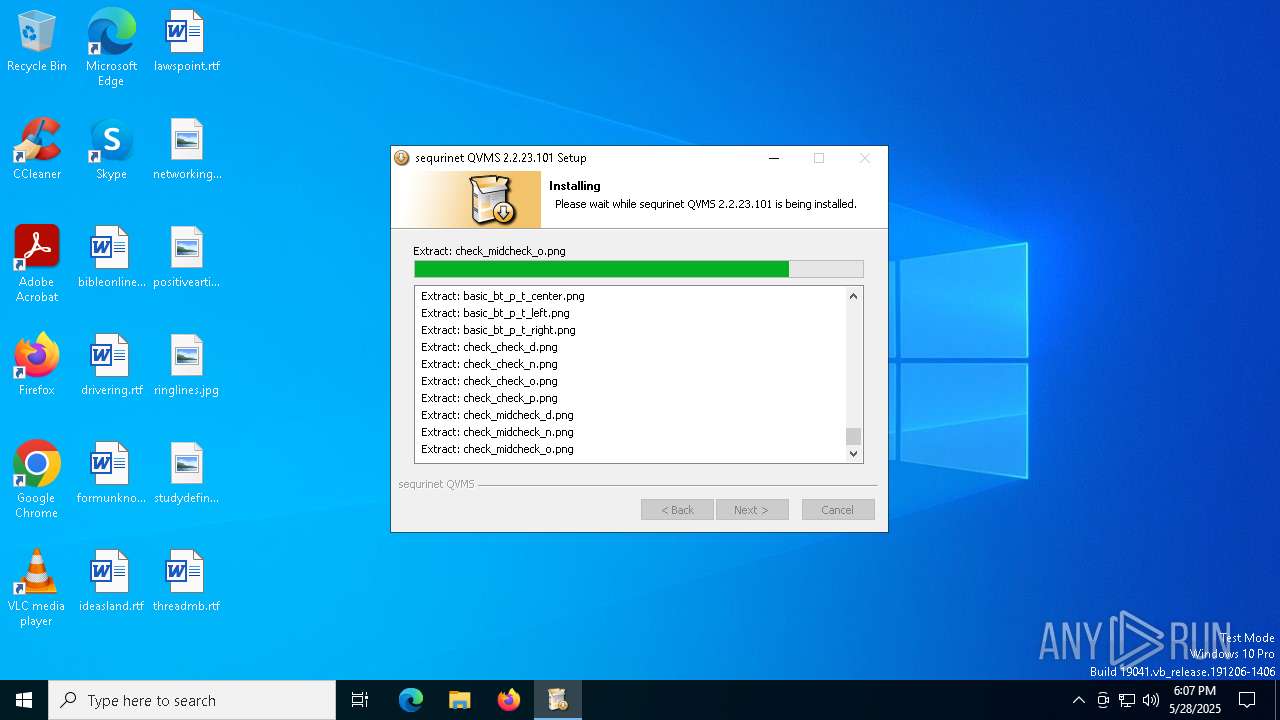
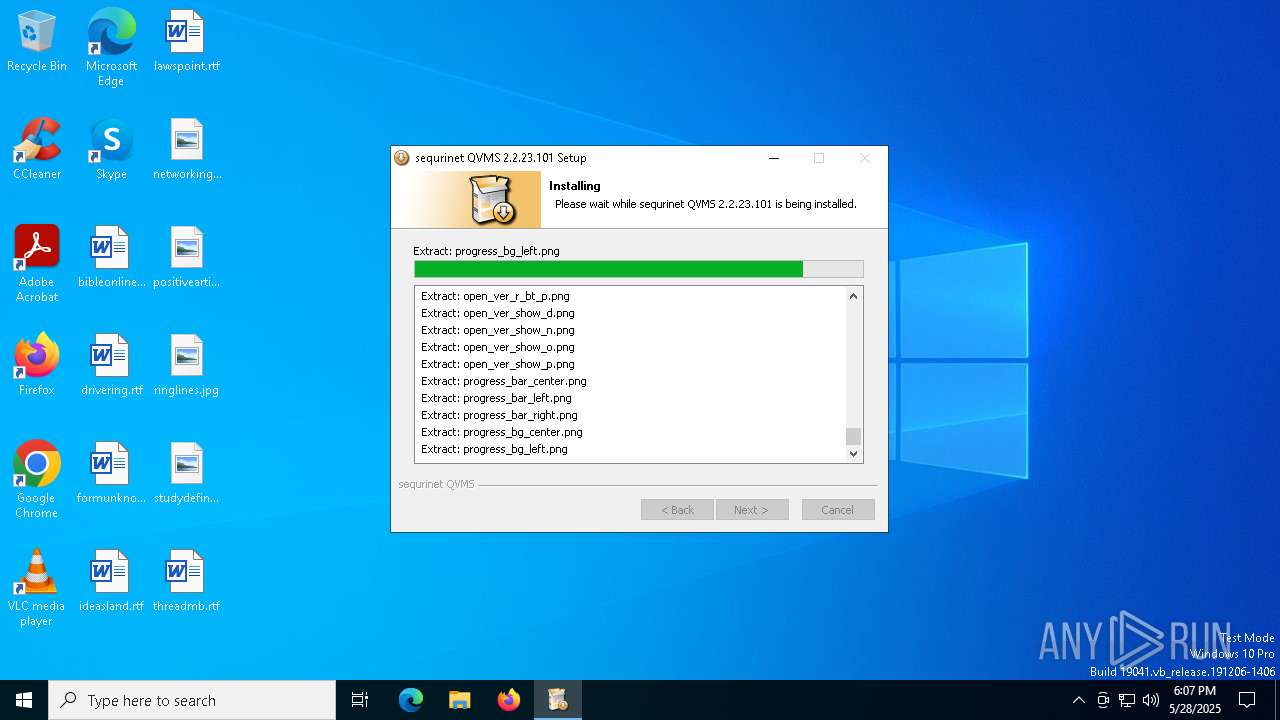
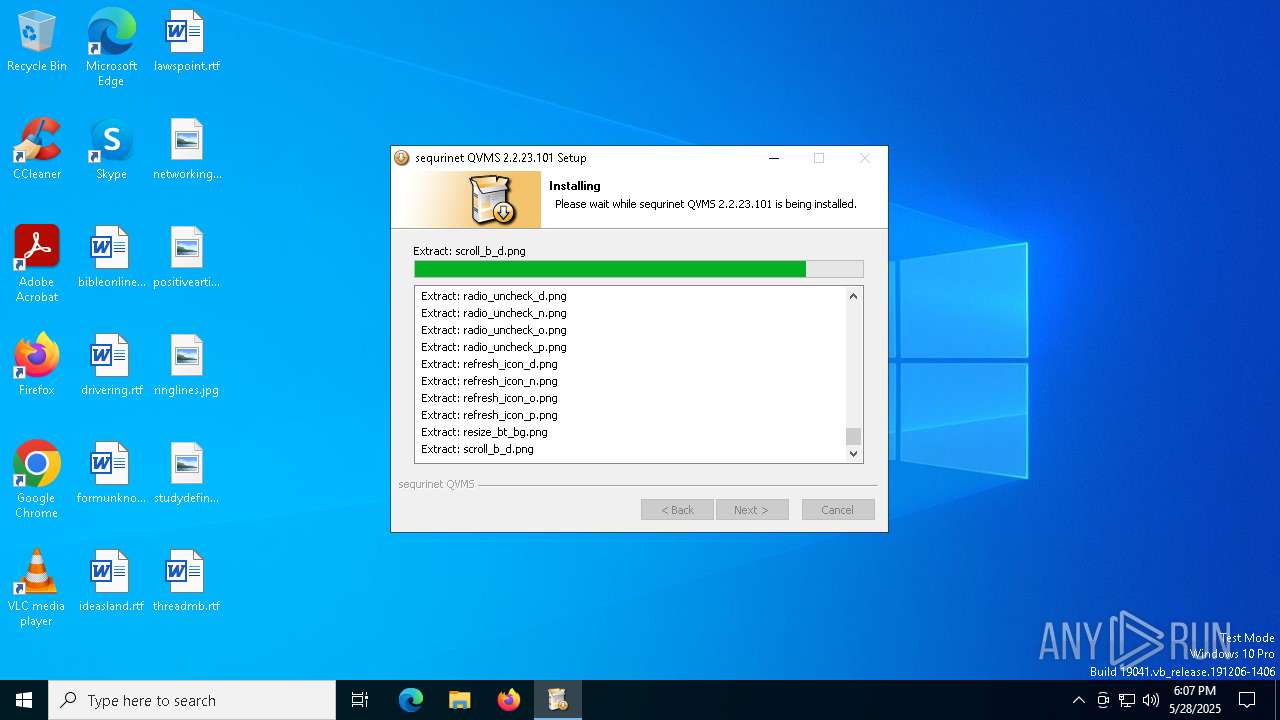
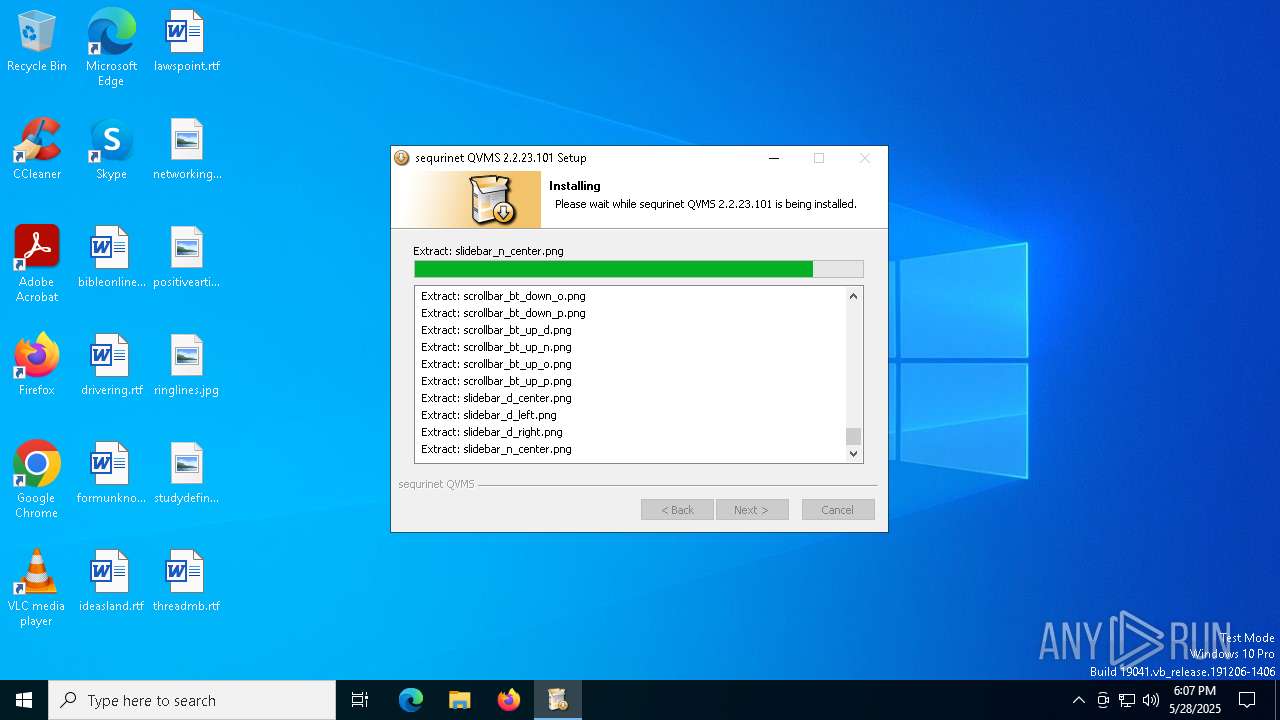
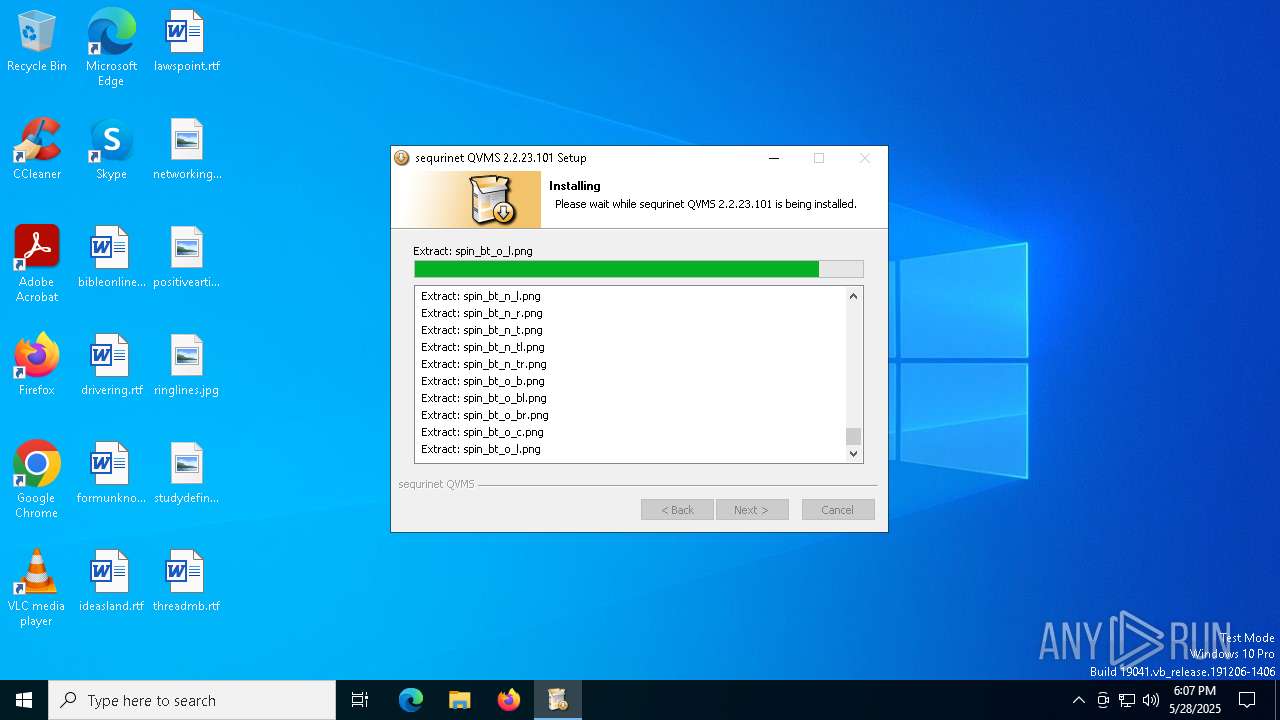
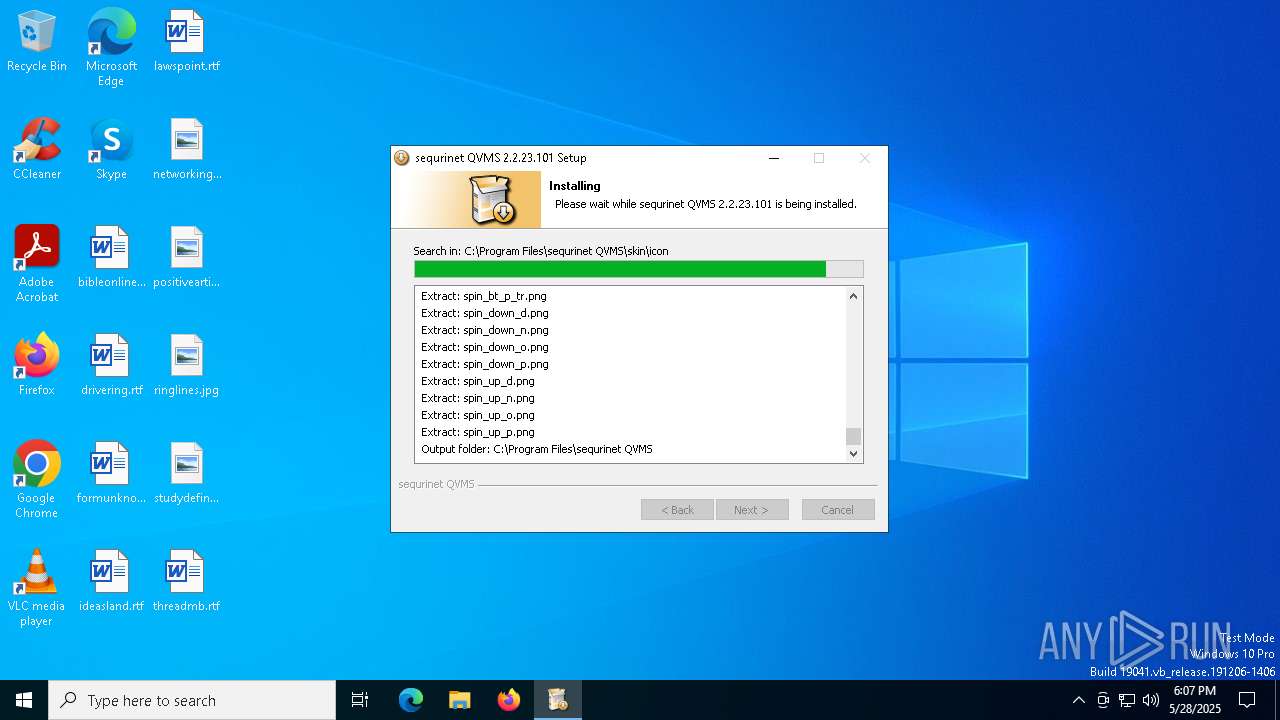
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- vcredist_x64.exe (PID: 5376)
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
The process creates files with name similar to system file names
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
The process drops C-runtime libraries
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- TiWorker.exe (PID: 5796)
- msiexec.exe (PID: 668)
There is functionality for taking screenshot (YARA)
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
Drops 7-zip archiver for unpacking
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
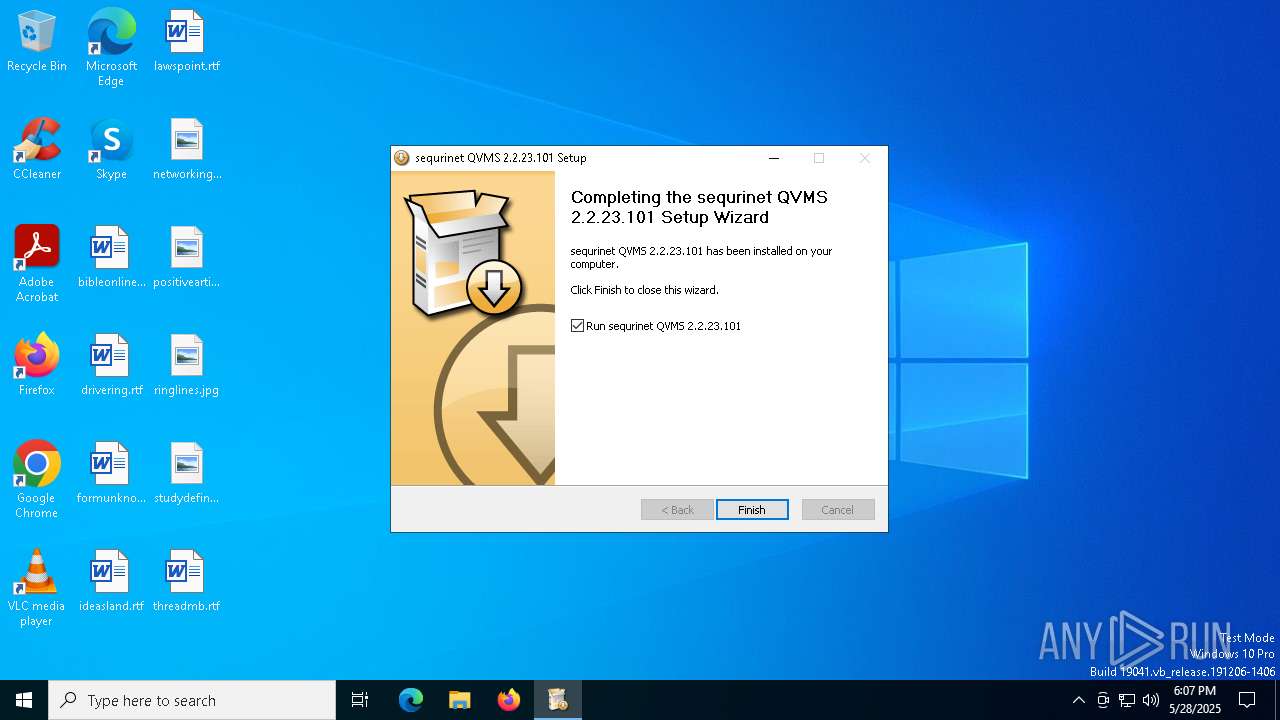
Creates a software uninstall entry
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
Executable content was dropped or overwritten
- vcredist_x64.exe (PID: 5376)
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- TiWorker.exe (PID: 5796)
Malware-specific behavior (creating "System.dll" in Temp)
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 668)
Starts CMD.EXE for commands execution
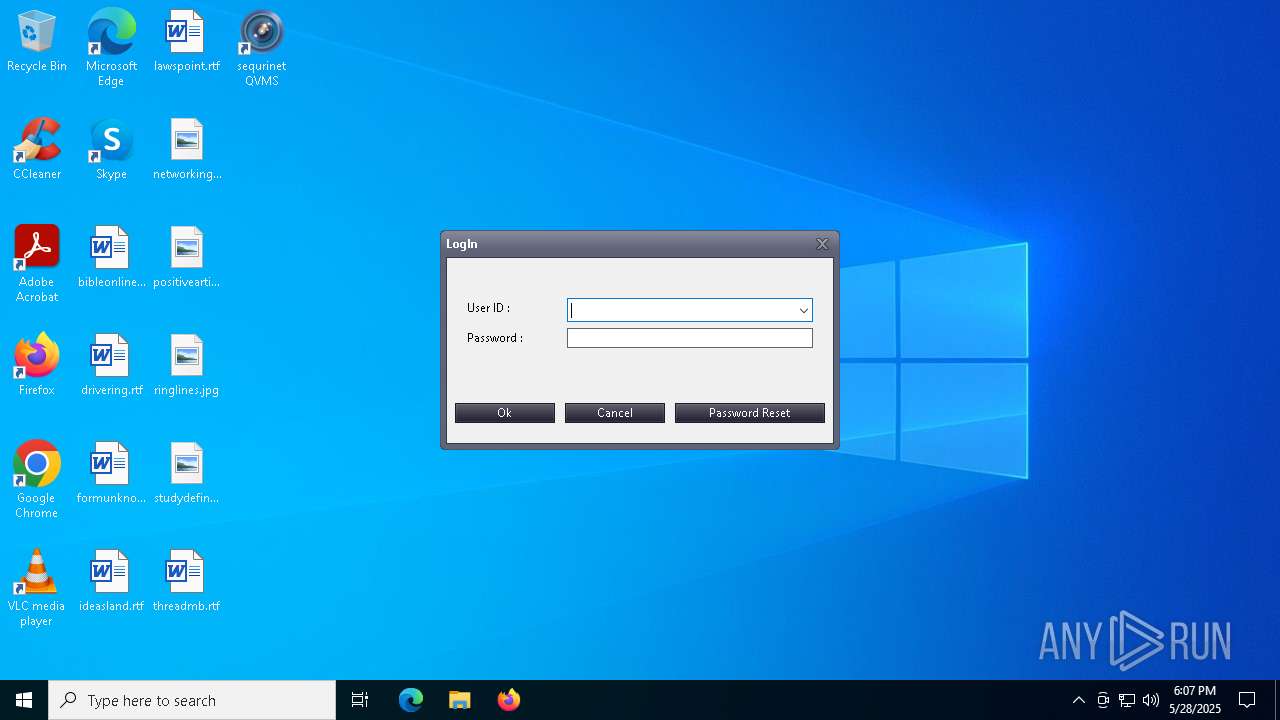
- sequrinet QVMS.exe (PID: 4620)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7784)
Likely accesses (executes) a file from the Public directory
- icacls.exe (PID: 7644)
- cmd.exe (PID: 7784)
INFO
Application launched itself
- firefox.exe (PID: 8052)
- firefox.exe (PID: 8032)
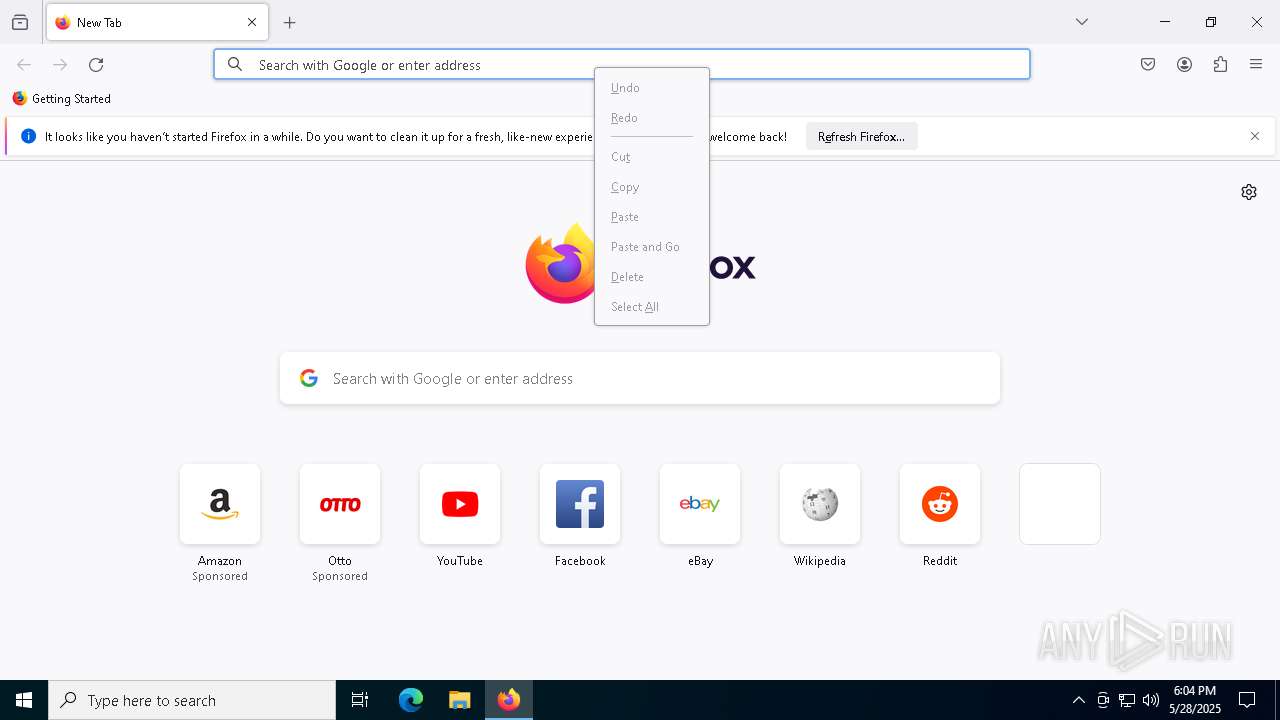
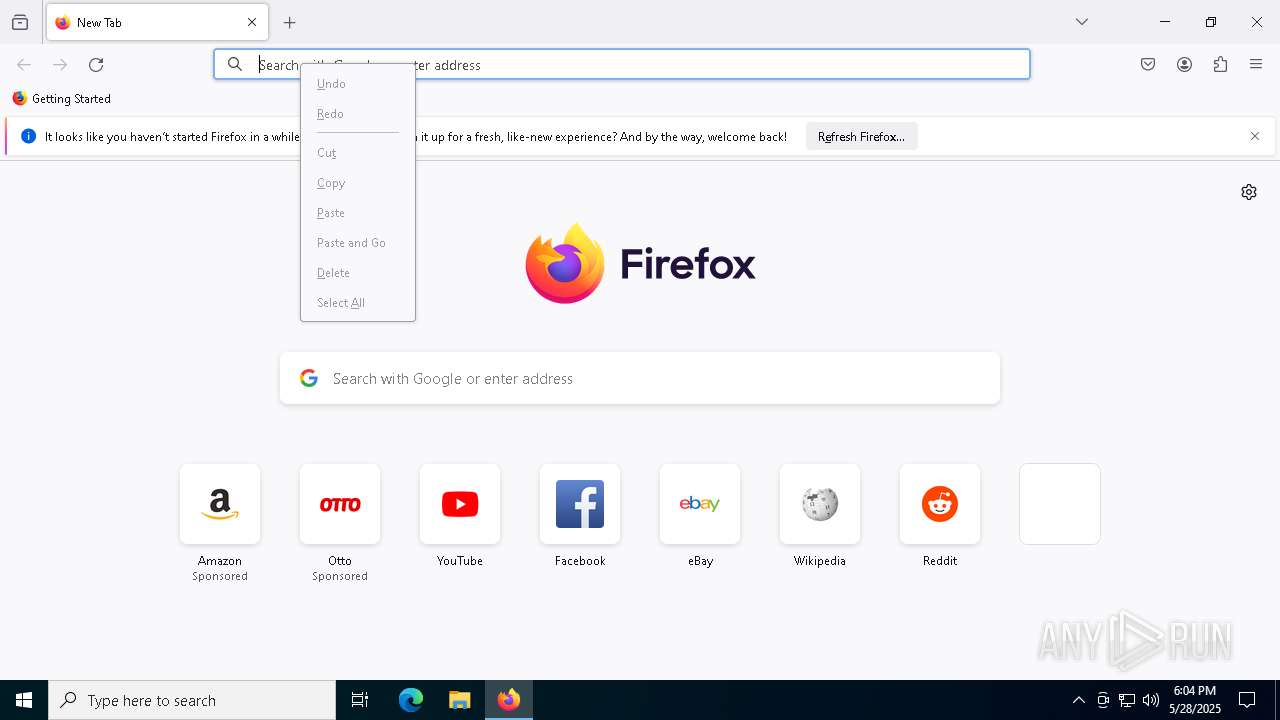
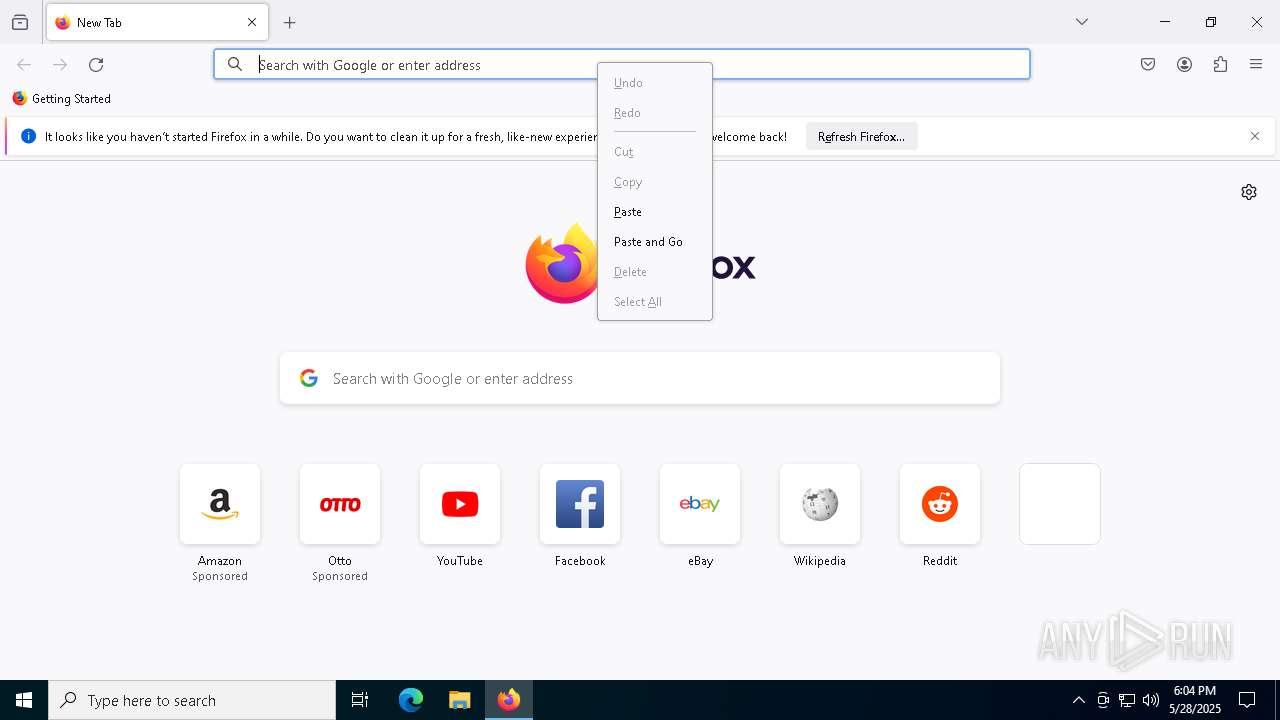
Manual execution by a user
- firefox.exe (PID: 8032)
Checks supported languages
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- install.exe (PID: 7900)
- vcredist_x64.exe (PID: 5376)
- msiexec.exe (PID: 668)
Reads the computer name
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- vcredist_x64.exe (PID: 5376)
- install.exe (PID: 7900)
- msiexec.exe (PID: 668)
Executable content was dropped or overwritten
- firefox.exe (PID: 8052)
- msiexec.exe (PID: 668)
Create files in a temporary directory
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- install.exe (PID: 7900)
Creates files in the program directory
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
The sample compiled with french language support
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
Checks proxy server information
- slui.exe (PID: 6108)
The sample compiled with korean language support
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- vcredist_x64.exe (PID: 5376)
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
Reads the software policy settings
- slui.exe (PID: 6108)
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
Launch of the file from Downloads directory
- firefox.exe (PID: 8052)
The sample compiled with english language support
- vcredist_x64.exe (PID: 5376)
- sequrinet QVMS_2.2.23.101.exe (PID: 5364)
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
Reads the machine GUID from the registry
- vcredist_x64.exe (PID: 5376)
- msiexec.exe (PID: 668)
Creates files or folders in the user directory
- msiexec.exe (PID: 668)
The sample compiled with spanish language support
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
The sample compiled with Italian language support
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
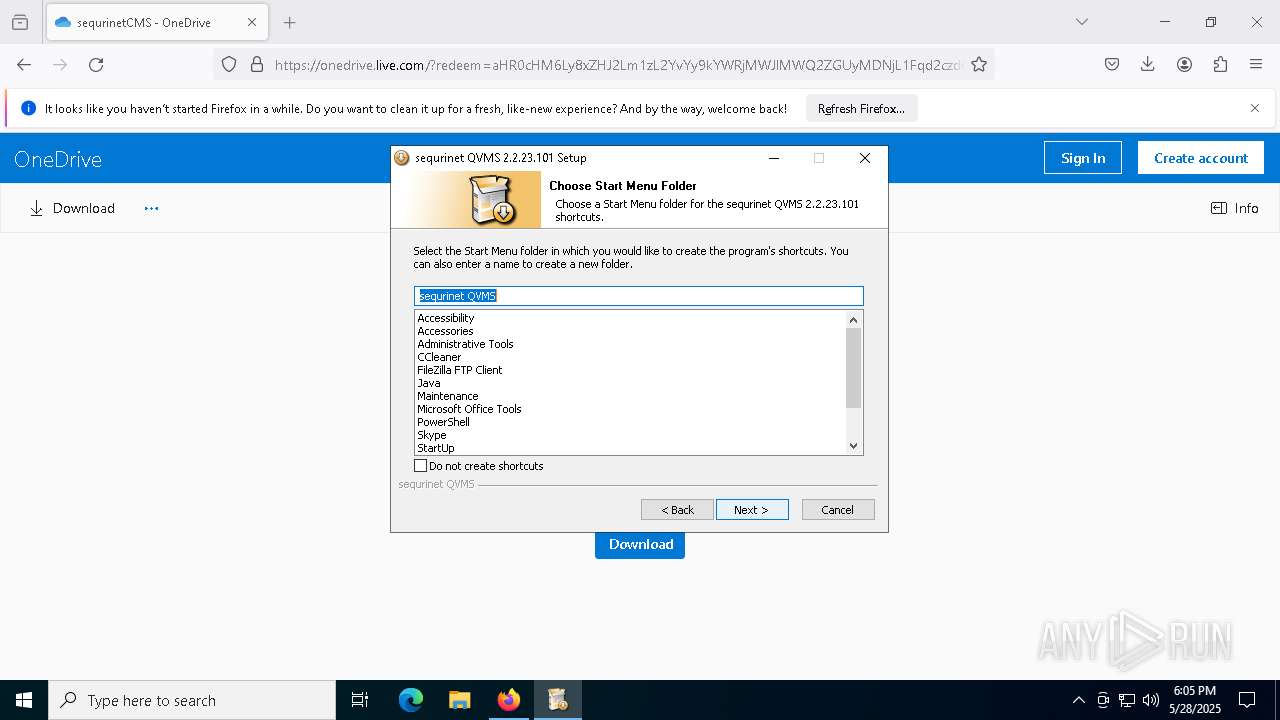
Creates a software uninstall entry
- msiexec.exe (PID: 668)
The sample compiled with japanese language support
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
The sample compiled with chinese language support
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
The sample compiled with german language support
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
The sample compiled with russian language support
- msiexec.exe (PID: 668)
- TiWorker.exe (PID: 5796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
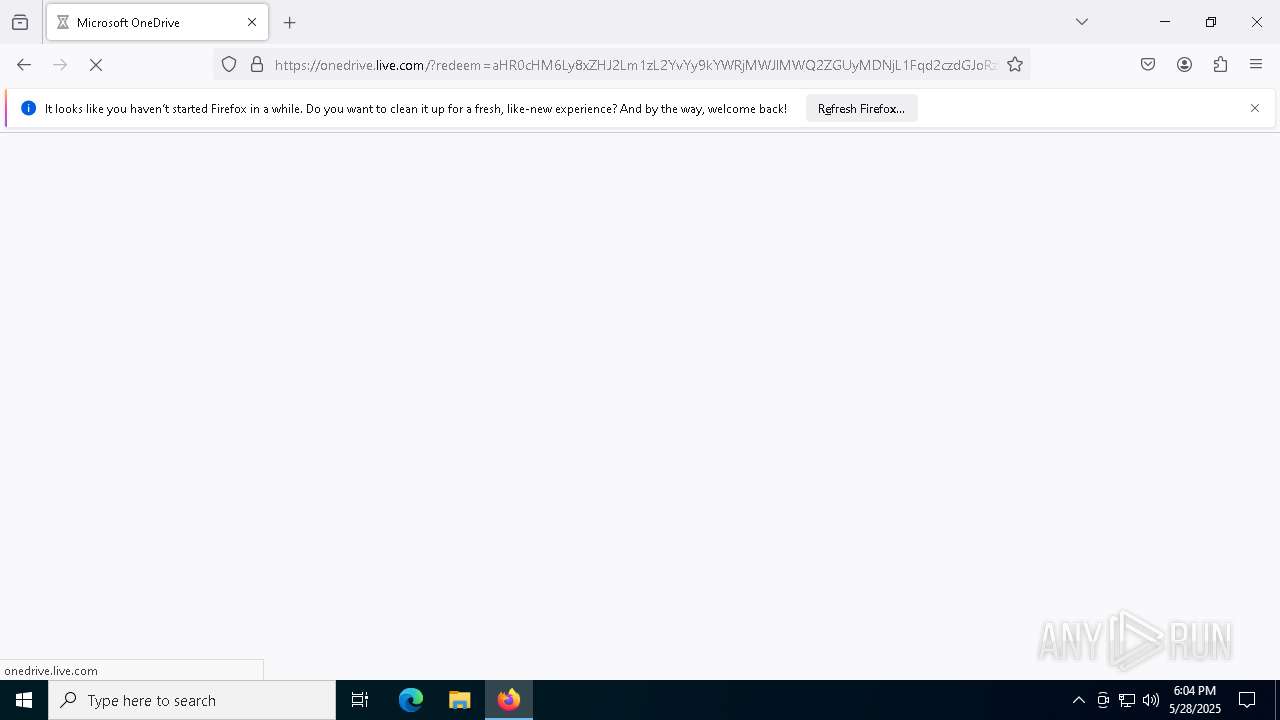
| ContentType: | text/html; charset=utf-8 |
|---|---|
| Viewport: | width=device-width, initial-scale=1.0, maximum-scale=1.0, minimum-scale=1.0, user-scalable=no |
| Title: | Microsoft OneDrive |
Total processes
164
Monitored processes
25
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4232 -childID 2 -isForBrowser -prefsHandle 4228 -prefMapHandle 4224 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {85ea7b83-5a68-43b0-9c51-2a073529696a} 8052 "\\.\pipe\gecko-crash-server-pipe.8052" 1db51f37a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 668 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
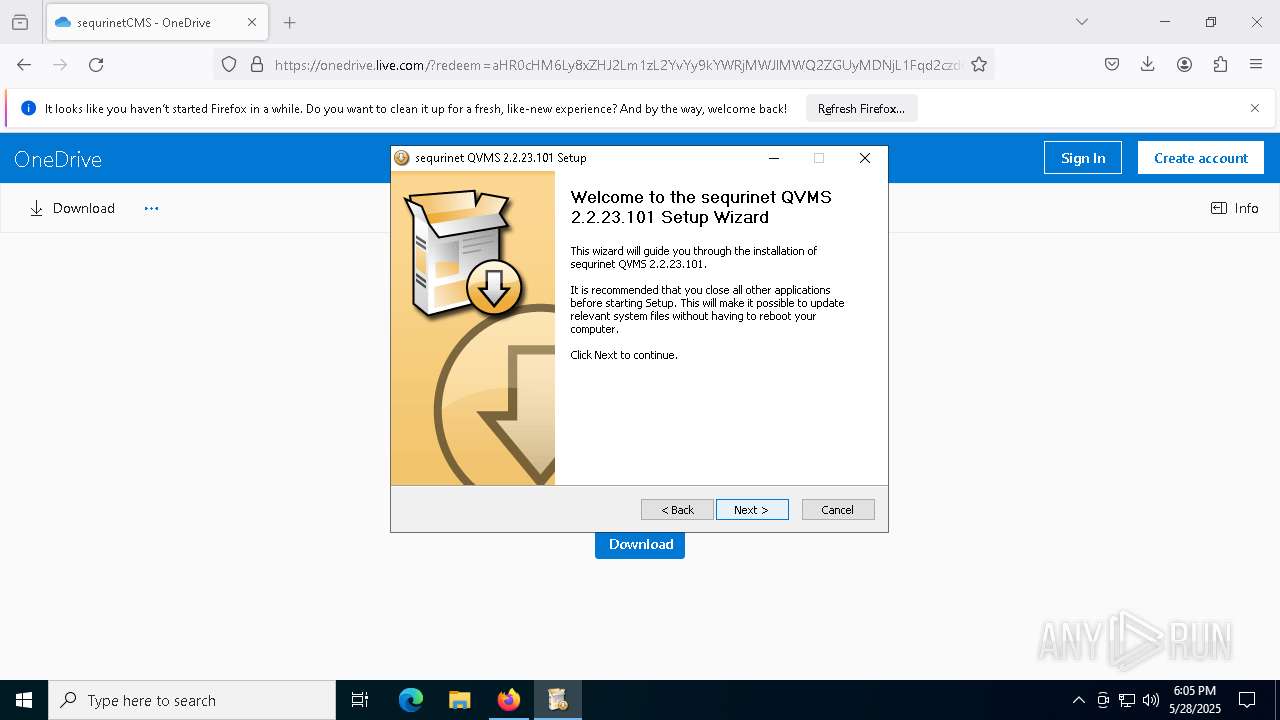
| 716 | "C:\Users\admin\Downloads\sequrinet QVMS_2.2.23.101.exe" | C:\Users\admin\Downloads\sequrinet QVMS_2.2.23.101.exe | — | firefox.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4572 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4880 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4932 -prefMapHandle 4848 -prefsLen 38177 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {63b56ce0-4ec0-4f2e-a1d3-9c929681b378} 8052 "\\.\pipe\gecko-crash-server-pipe.8052" 1db530e7b10 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
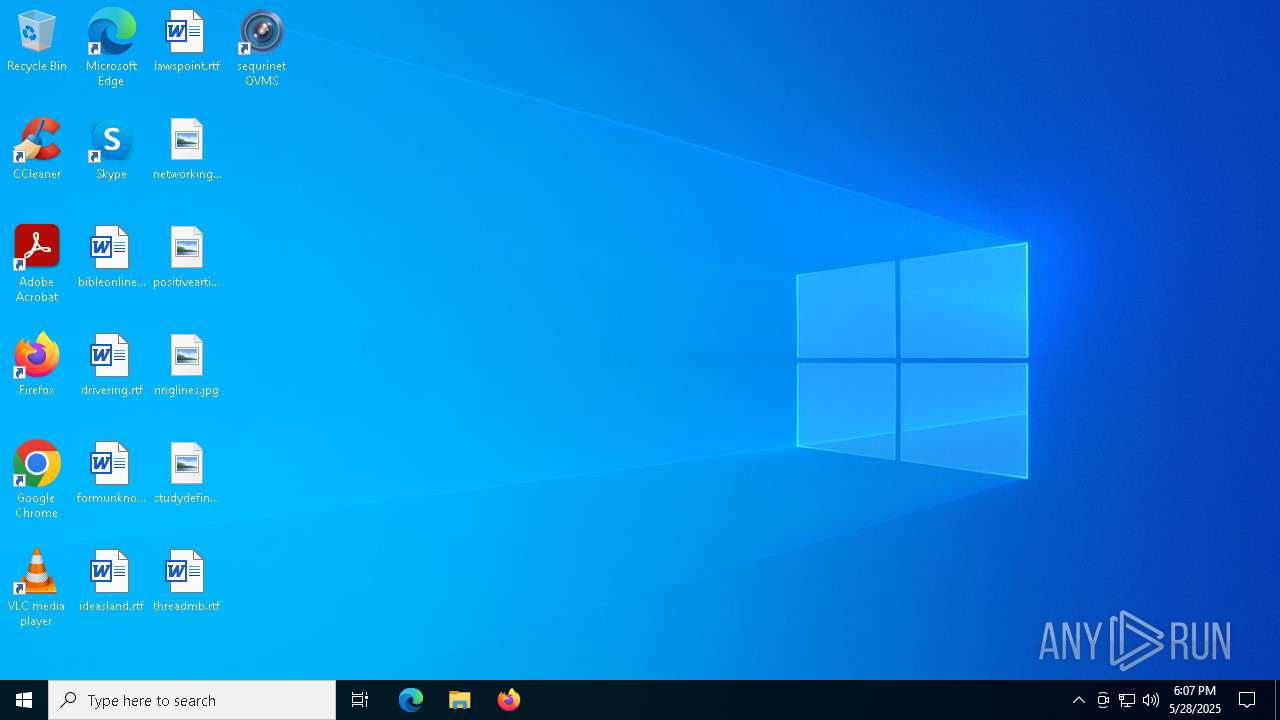
| 4620 | "C:\Program Files\sequrinet QVMS\sequrinet QVMS.exe" | C:\Program Files\sequrinet QVMS\sequrinet QVMS.exe | — | sequrinet QVMS_2.2.23.101.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2, 2, 23, 101 Modules
| |||||||||||||||
| 5364 | "C:\Users\admin\Downloads\sequrinet QVMS_2.2.23.101.exe" | C:\Users\admin\Downloads\sequrinet QVMS_2.2.23.101.exe | firefox.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5376 | "C:\Program Files\sequrinet QVMS\vcredist_x64\vcredist_x64.exe" /q | C:\Program Files\sequrinet QVMS\vcredist_x64\vcredist_x64.exe | sequrinet QVMS_2.2.23.101.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2008 Redistributable Setup Exit code: 0 Version: 9.0.30729.01 Modules
| |||||||||||||||
| 5796 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6108 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
58 134
Read events
57 665
Write events
399
Delete events
70
Modification events
| (PID) Process: | (8052) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8052) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5364) sequrinet QVMS_2.2.23.101.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List |
| Operation: | write | Name: | C:\Program Files\sequrinet QVMS\sequrinet QVMS.exe |
Value: C:\Program Files\sequrinet QVMS\sequrinet QVMS.exe:*:Enabled:sequrinet QVMS | |||
| (PID) Process: | (5364) sequrinet QVMS_2.2.23.101.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List |
| Operation: | write | Name: | C:\Program Files\sequrinet QVMS\UpnpServiceAgent.exe |
Value: C:\Program Files\sequrinet QVMS\UpnpServiceAgent.exe:*:Enabled:sequrinet QVMS | |||
| (PID) Process: | (5364) sequrinet QVMS_2.2.23.101.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\sequrinet QVMS |
| Operation: | write | Name: | path |
Value: C:\Program Files\sequrinet QVMS | |||
| (PID) Process: | (5364) sequrinet QVMS_2.2.23.101.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\sequrinet QVMS |
| Operation: | write | Name: | DisplayName |
Value: sequrinet QVMS (x64) | |||
| (PID) Process: | (5364) sequrinet QVMS_2.2.23.101.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\sequrinet QVMS |
| Operation: | write | Name: | DisplayVersion |
Value: 2.2.23.101 | |||
| (PID) Process: | (5364) sequrinet QVMS_2.2.23.101.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\sequrinet QVMS |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\sequrinet QVMS\Uninstall.exe | |||
| (PID) Process: | (5364) sequrinet QVMS_2.2.23.101.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\sequrinet QVMS |
| Operation: | write | Name: | HelpLink |
Value: | |||
| (PID) Process: | (5364) sequrinet QVMS_2.2.23.101.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\sequrinet QVMS |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\sequrinet QVMS | |||
Executable files
197
Suspicious files
231
Text files
1 488
Unknown types
98
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8052 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:506C9CC0A665CEF45493631CAB3FF35D | SHA256:53FD1DE78799A5187BCB42C34C95A719A5E6F9EA3826D3CBF581BEC825ED2076 | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:634A4516378A801EE3C31BEC2B2FA783 | SHA256:7F969F70C7BA890FFD5D953D66A0562772CCD5A8D26679307FF02057821212CB | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:D92BC5A36DEF9808D0E171805BA2F8B5 | SHA256:B4D70FA5EE67F1360130BDBDDCC991E7E85E1A98D4D7746E671610199FA546A1 | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | dbf | |
MD5:F759EB25271E6A6F0A3500520813E5FE | SHA256:015E515D432DD64FDC9502ABE9C723EEF544E7AF11C36BDFE8B38412597CA1EC | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\protections.sqlite-journal | binary | |
MD5:47DDA55CA92C4C816425DA4420AAC19C | SHA256:D19D597BE55F4092F870145A90A98C824B90C0A38A7AE49A5AFDCA23A9C57EDA | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | sqlite | |
MD5:65E92AAB6FE69530AB5548097A585D42 | SHA256:A5C1BCF06C8B9470C0536F72297A147F013B95B000E71AFF328901E53B1C5DF1 | |||
| 8052 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
113
DNS requests
148
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8052 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8052 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
8052 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
8052 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
8052 | firefox.exe | POST | 200 | 184.24.77.52:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1240 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5796 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Suspected Malicious Domain ( .spo-msedge .net) |
2196 | svchost.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Suspected Malicious Domain ( .spo-msedge .net) |