| File name: | appnhost.msi |
| Full analysis: | https://app.any.run/tasks/af7275ee-f647-42ca-bf36-994ec4a0412e |
| Verdict: | Malicious activity |
| Analysis date: | October 02, 2019, 11:15:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Title: Installation Database, Subject: AppNHost 1.0.5.1, Author: Mixesoft Project, Keywords: Installer, Comments: Windows Installer Package, Template: Intel;1033, Revision Number: {275DBB89-40DC-48C7-9046-D6ACD90D439C}, Create Time/Date: Fri Aug 8 15:21:08 2014, Last Saved Time/Date: Fri Aug 8 15:21:08 2014, Number of Pages: 200, Number of Words: 10, Name of Creating Application: Windows Installer XML Toolset (3.8.1128.0), Security: 2 |
| MD5: | FA2051C7C35DA1DD9A518CE1F8F90ECA |
| SHA1: | 87573E225CEE8396712595AF04AA75386207F2F0 |
| SHA256: | 0F8D375B0EFA94D6C92D4573A6151C49A662827D2D97AEFCB6677903B83A0D09 |
| SSDEEP: | 3072:OYF3RVz6pPhsm1cuMdwrj5djSFmR5UR1qpb6vt9O/6beLUQ1DgPFAYUvufvvhNs:PVzG280mRQqBBFWHUW3vh |
MALICIOUS
Changes the autorun value in the registry
- appnhost.exe (PID: 3528)
Application was dropped or rewritten from another process
- appnhost.exe (PID: 3528)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 2696)
Executed via COM
- DrvInst.exe (PID: 3540)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2664)
Creates files in the user directory
- msiexec.exe (PID: 2664)
Modifies the open verb of a shell class
- appnhost.exe (PID: 3528)
INFO
Application launched itself
- msiexec.exe (PID: 2664)
Searches for installed software
- msiexec.exe (PID: 2664)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2696)
Creates a software uninstall entry
- msiexec.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | AppNHost 1.0.5.1 |
| Author: | Mixesoft Project |
| Keywords: | Installer |
| Comments: | Windows Installer Package |
| Template: | Intel;1033 |
| RevisionNumber: | {275DBB89-40DC-48C7-9046-D6ACD90D439C} |
| CreateDate: | 2014:08:08 14:21:08 |
| ModifyDate: | 2014:08:08 14:21:08 |
| Pages: | 200 |
| Words: | 10 |
| Software: | Windows Installer XML Toolset (3.8.1128.0) |
| Security: | Read-only recommended |
Total processes
39
Monitored processes
6
Malicious processes
1
Suspicious processes
2
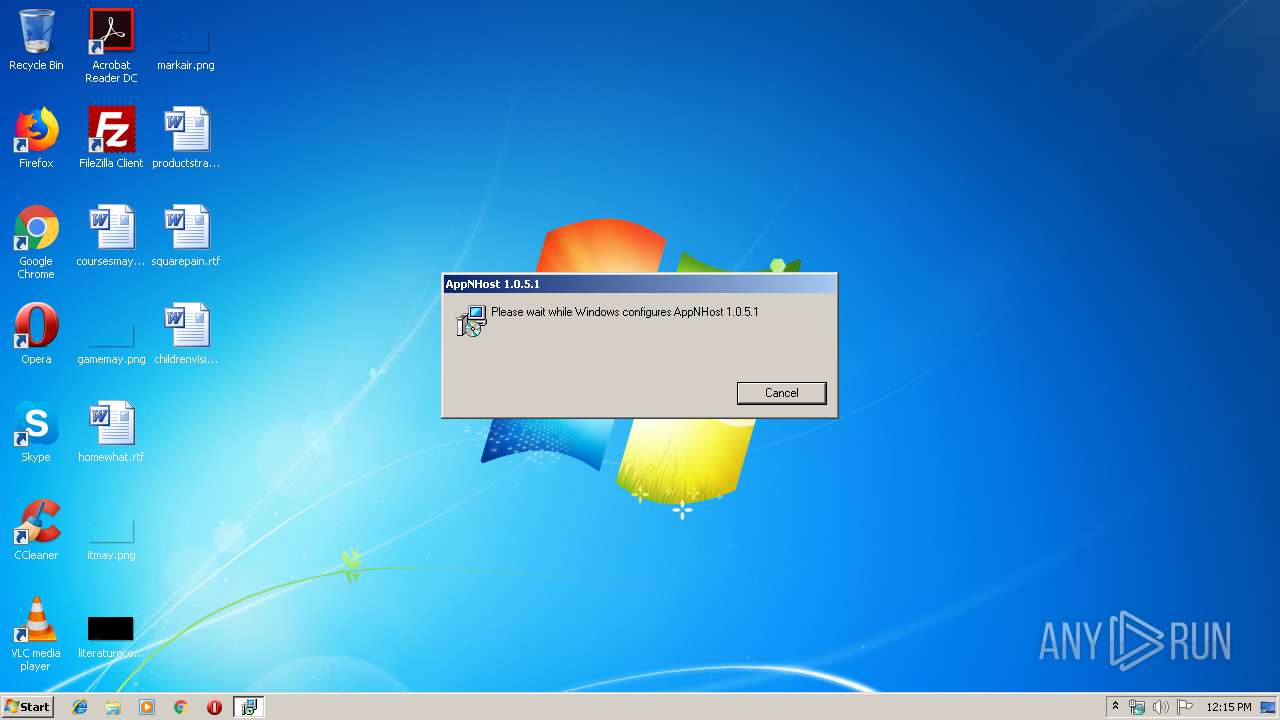
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2664 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\appnhost.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3528 | "C:\Users\admin\AppData\Local\Mixesoft\AppNHost\appnhost.exe" | C:\Users\admin\AppData\Local\Mixesoft\AppNHost\appnhost.exe | MsiExec.exe | ||||||||||||
User: admin Company: Mixesoft Project Integrity Level: MEDIUM Description: Native Host for Apps Exit code: 0 Version: 1.0.5.1 Modules
| |||||||||||||||
| 3540 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "00000550" "00000330" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | C:\Windows\system32\MsiExec.exe -Embedding AA38F481A8D05399340F4D275E4E24FC | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
960
Read events
680
Write events
268
Delete events
12
Modification events
| (PID) Process: | (3260) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2664) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000008275B9C31279D501680A0000AC090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2664) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000008275B9C31279D501680A0000AC090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2664) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 24 | |||
| (PID) Process: | (2664) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000A0FA1FC41279D501680A0000AC090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2664) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FA5C22C41279D501680A000064080000E8030000010000000000000000000000C5C68D18B296F4459420B2BDEF93FCF00000000000000000 | |||
| (PID) Process: | (2696) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000BC482EC41279D501880A0000DC080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2696) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000BC482EC41279D501880A0000A80C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2696) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000BC482EC41279D501880A0000AC0C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2696) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000BC482EC41279D501880A0000E8080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
7
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2664 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF54401434E9848CBC.TMP | — | |
MD5:— | SHA256:— | |||
| 2664 | msiexec.exe | C:\Windows\Installer\MSI4629.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | msiexec.exe | C:\Config.Msi\f4119.rbs | — | |
MD5:— | SHA256:— | |||
| 2664 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF09C1C9427802480A.TMP | — | |
MD5:— | SHA256:— | |||
| 2696 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2664 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 2664 | msiexec.exe | C:\Windows\Installer\f4118.ipi | binary | |
MD5:— | SHA256:— | |||
| 3540 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 3540 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report