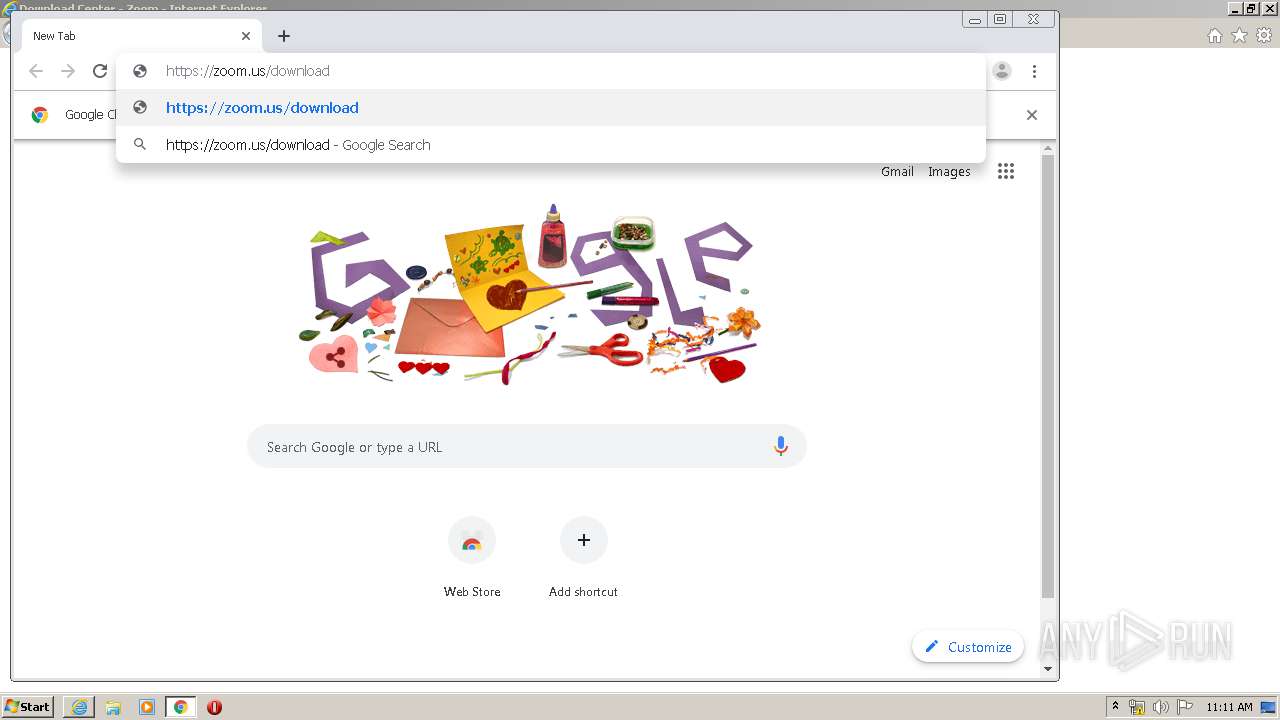
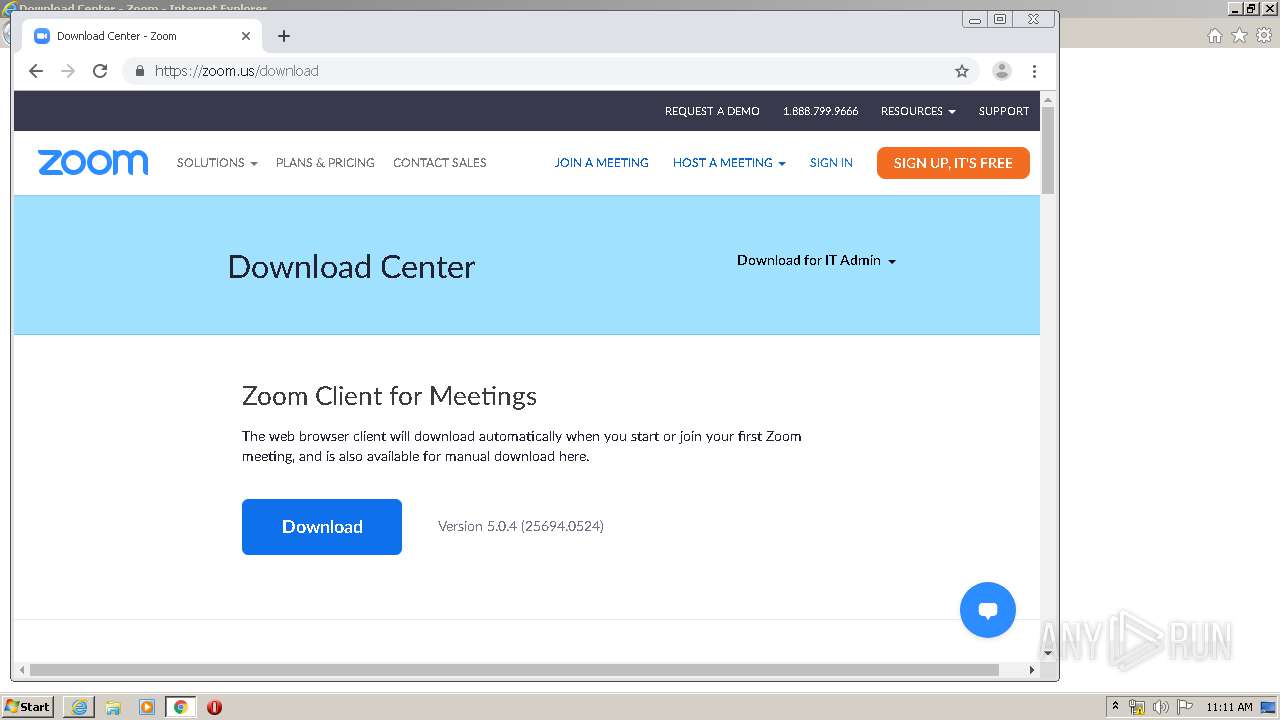
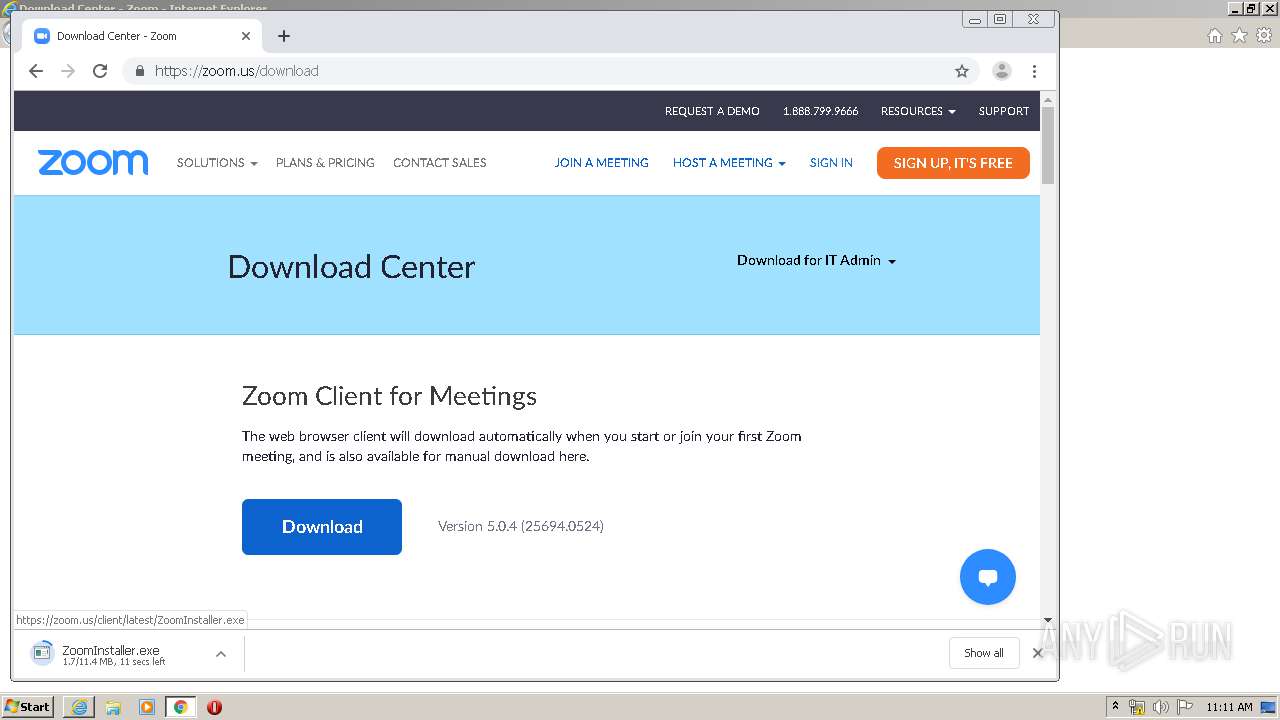
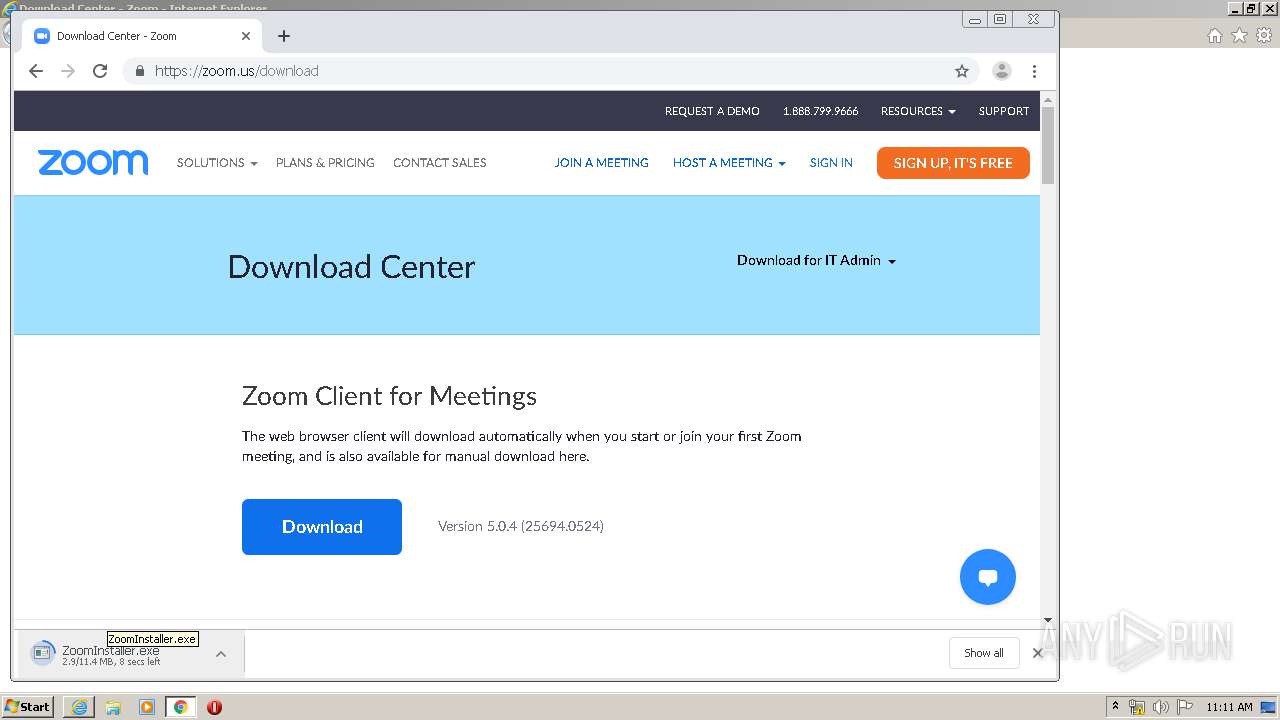
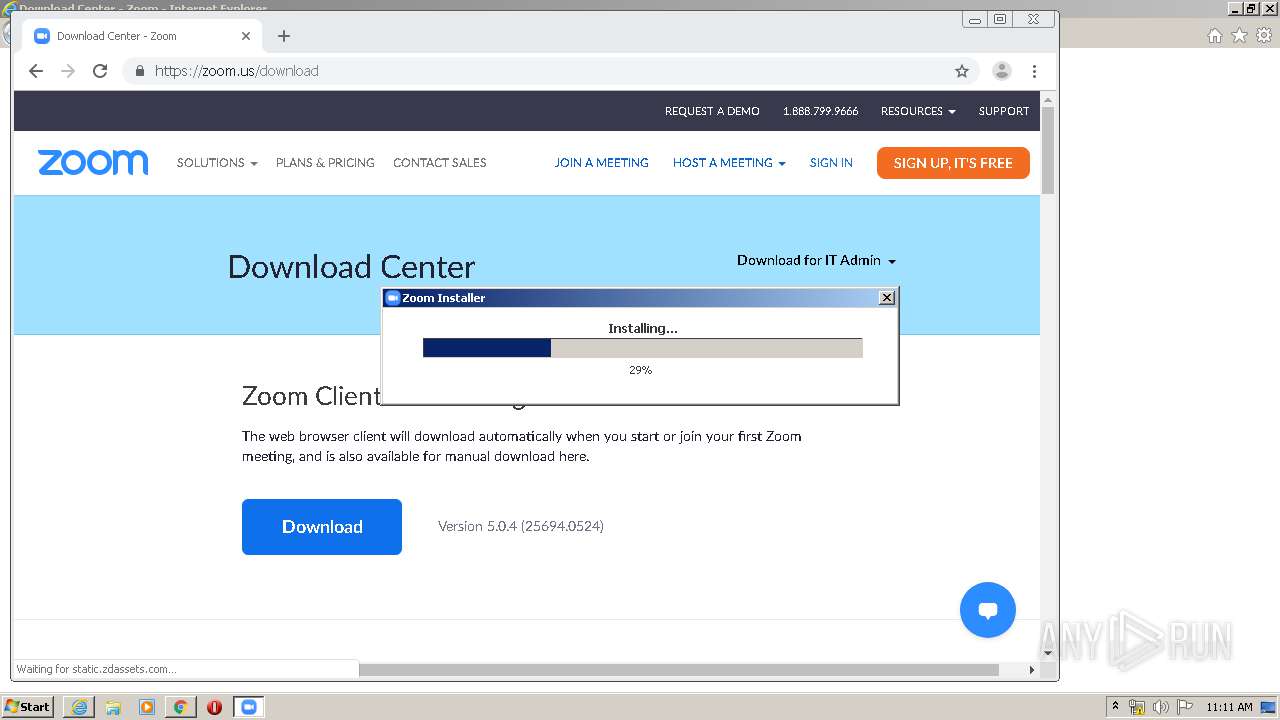
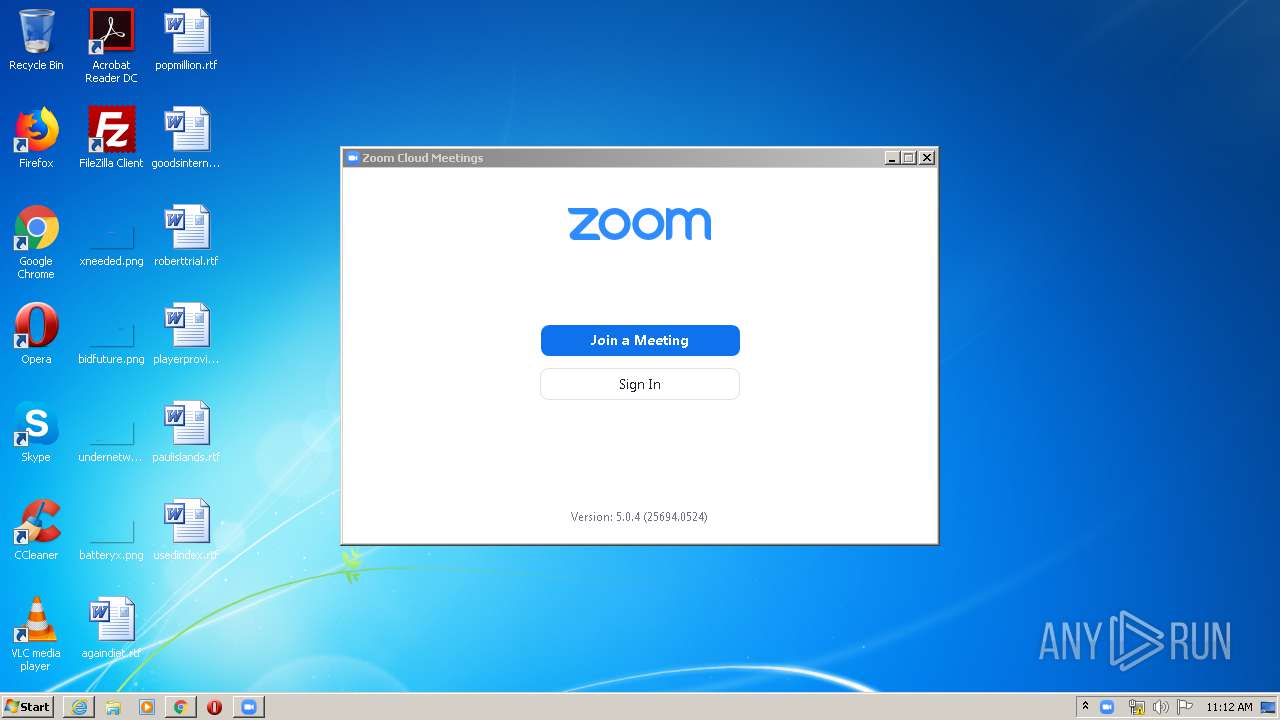
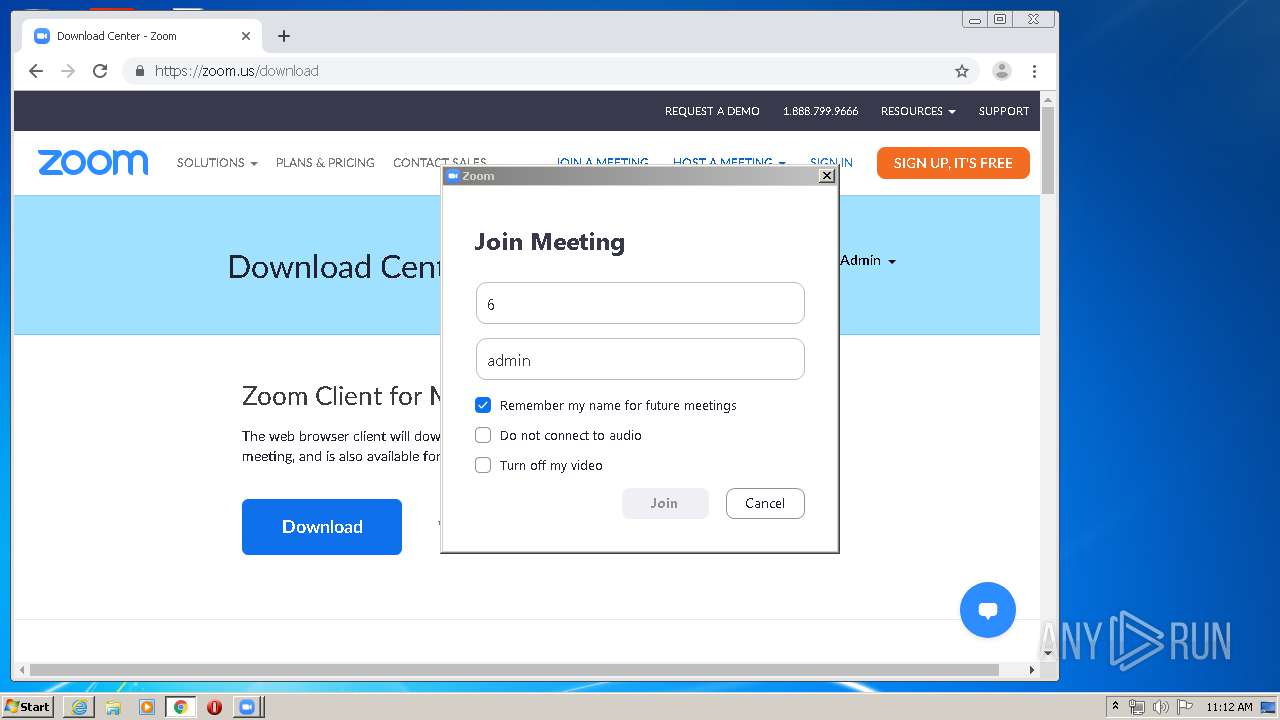
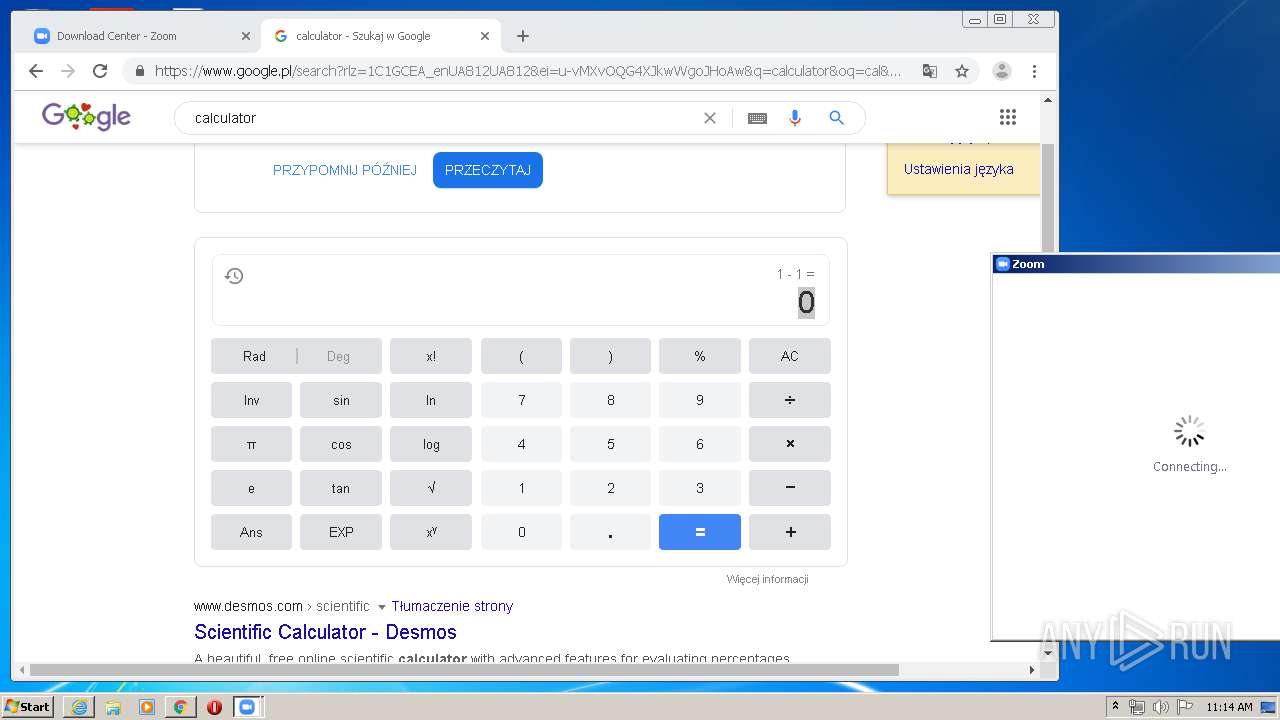
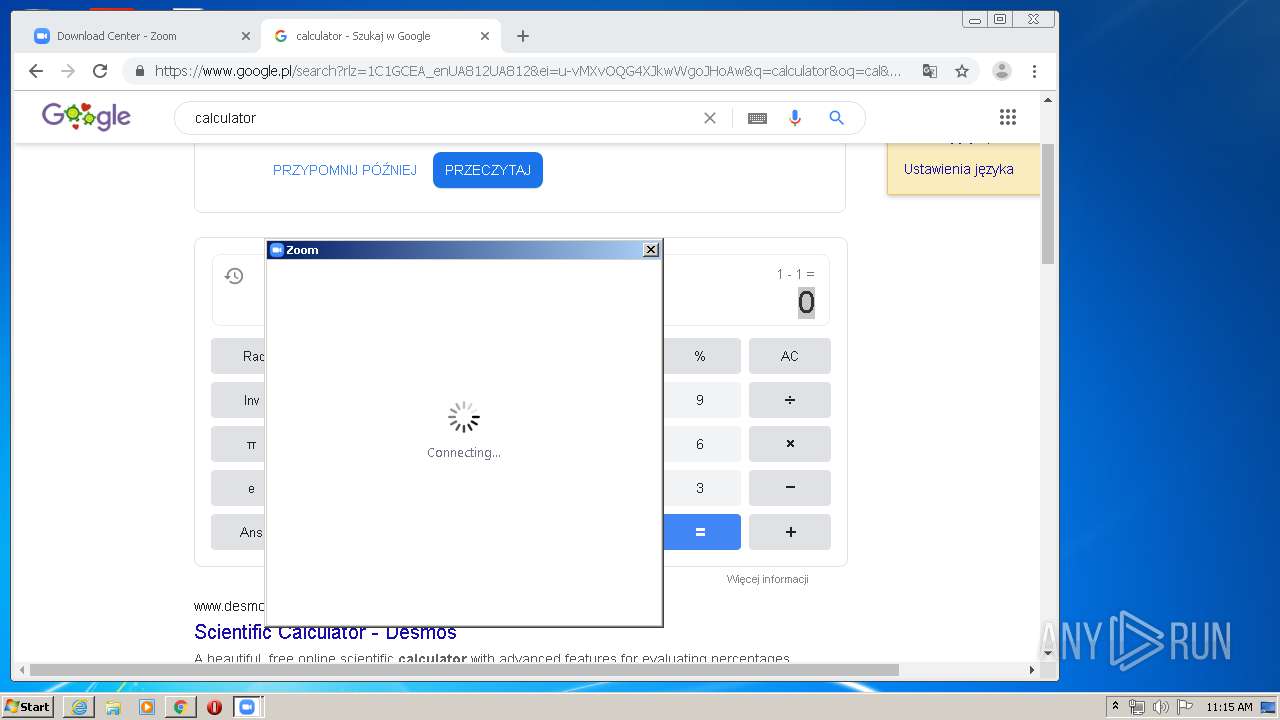
| URL: | https://zoom.us/download |
| Full analysis: | https://app.any.run/tasks/c48c5c63-84af-49d6-a8e7-1e6920a3bc3c |
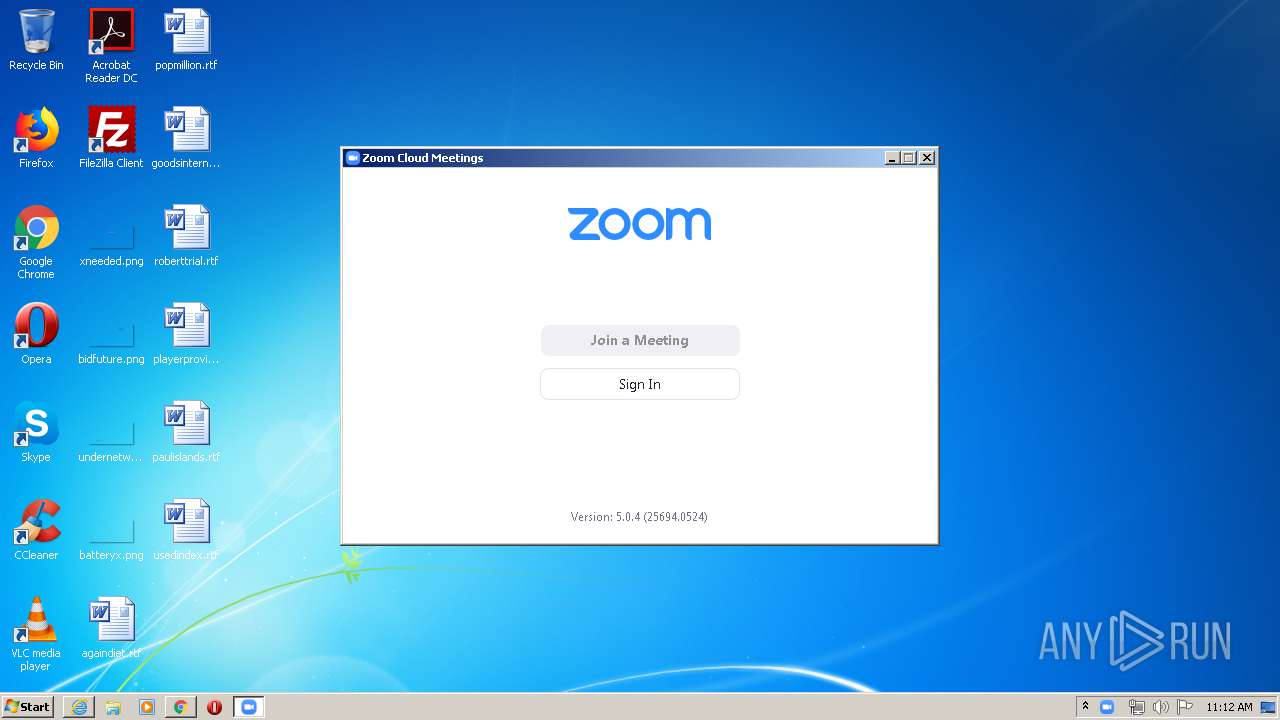
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2020, 10:10:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 41363F334D7D65A496F70DFF9534A87D |
| SHA1: | BBD883BBE24089AE507329898A267B11CE7645B2 |
| SHA256: | 0F849765756CF76166EE7F7440EA3D64AE4C3E02309BE81AE7A81DE3A93832D3 |
| SSDEEP: | 3:N88LWDLz:28LWj |
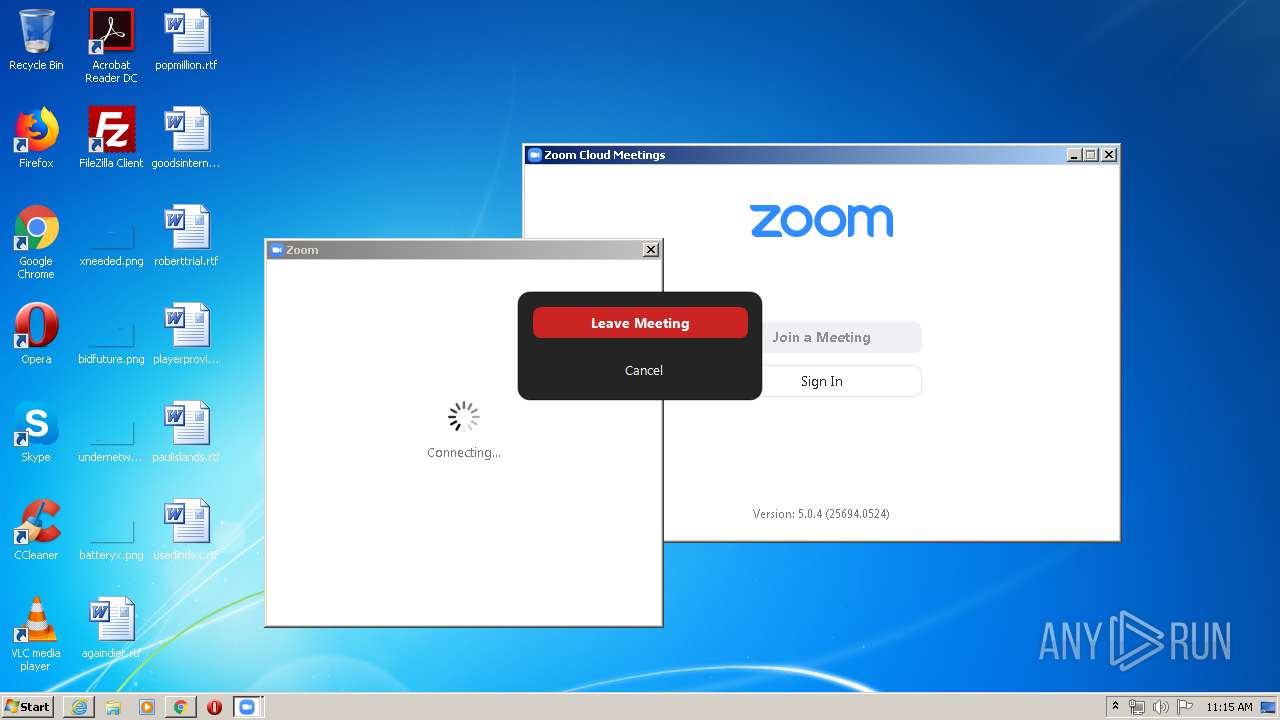
MALICIOUS
Application was dropped or rewritten from another process
- ZoomInstaller.exe (PID: 848)
- Installer.exe (PID: 316)
- Installer.exe (PID: 1896)
- Zoom.exe (PID: 2864)
- Zoom.exe (PID: 1992)
- Zoom.exe (PID: 604)
- Zoom.exe (PID: 1076)
- Zoom.exe (PID: 3984)
Actions looks like stealing of personal data
- Installer.exe (PID: 1896)
Loads dropped or rewritten executable
- Zoom.exe (PID: 1992)
- Installer.exe (PID: 1896)
- Zoom.exe (PID: 2864)
- Zoom.exe (PID: 604)
- Zoom.exe (PID: 3984)
- Zoom.exe (PID: 1076)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2440)
Executable content was dropped or overwritten
- chrome.exe (PID: 2676)
- chrome.exe (PID: 2440)
- ZoomInstaller.exe (PID: 848)
- Installer.exe (PID: 1896)
Application launched itself
- Installer.exe (PID: 1896)
- Zoom.exe (PID: 1992)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 1896)
Modifies the open verb of a shell class
- Installer.exe (PID: 1896)
Creates a software uninstall entry
- Installer.exe (PID: 1896)
Creates files in the user directory
- Zoom.exe (PID: 1992)
- Installer.exe (PID: 1896)
- Zoom.exe (PID: 604)
- Zoom.exe (PID: 3984)
- Zoom.exe (PID: 2864)
INFO
Reads the hosts file
- chrome.exe (PID: 2676)
- chrome.exe (PID: 2440)
Application launched itself
- iexplore.exe (PID: 2268)
- chrome.exe (PID: 2440)
Changes internet zones settings
- iexplore.exe (PID: 2268)
Creates files in the user directory
- iexplore.exe (PID: 1788)
- iexplore.exe (PID: 2268)
Reads internet explorer settings
- iexplore.exe (PID: 1788)
Reads Internet Cache Settings
- chrome.exe (PID: 2440)
- iexplore.exe (PID: 2268)
- iexplore.exe (PID: 1788)
Reads settings of System Certificates
- iexplore.exe (PID: 2268)
- chrome.exe (PID: 2440)
- iexplore.exe (PID: 1788)
- chrome.exe (PID: 2676)
- Installer.exe (PID: 1896)
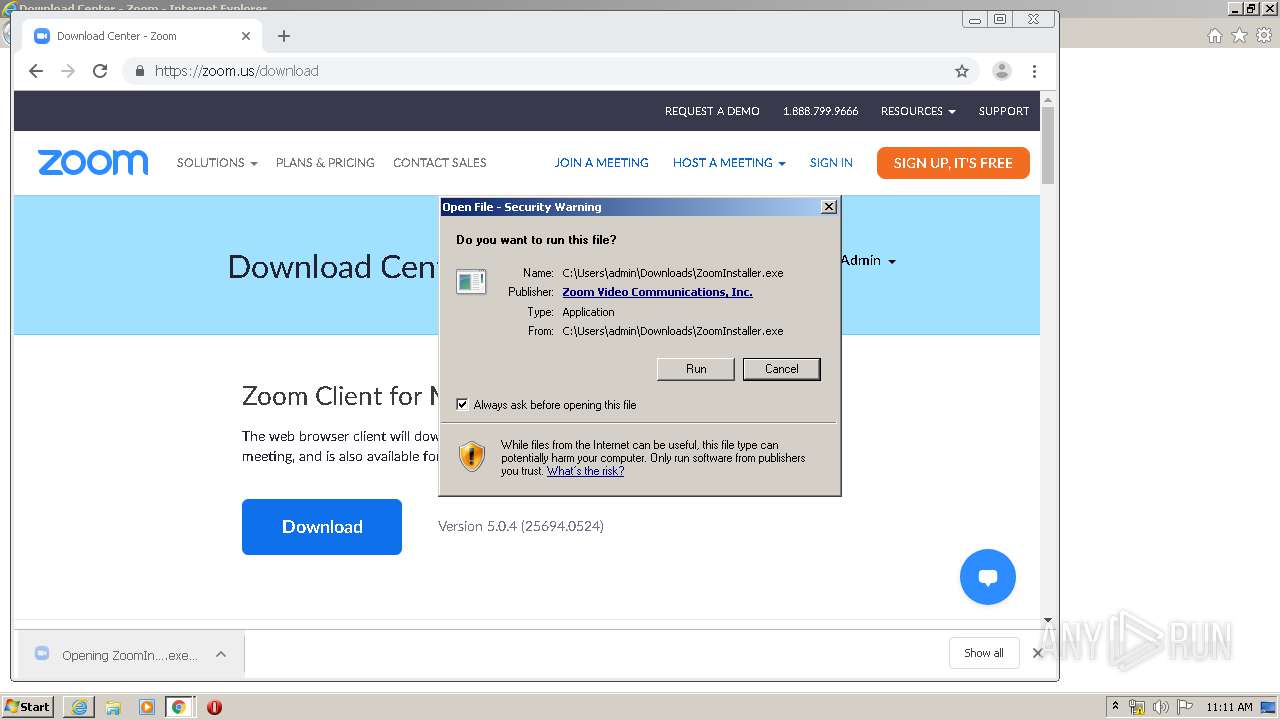
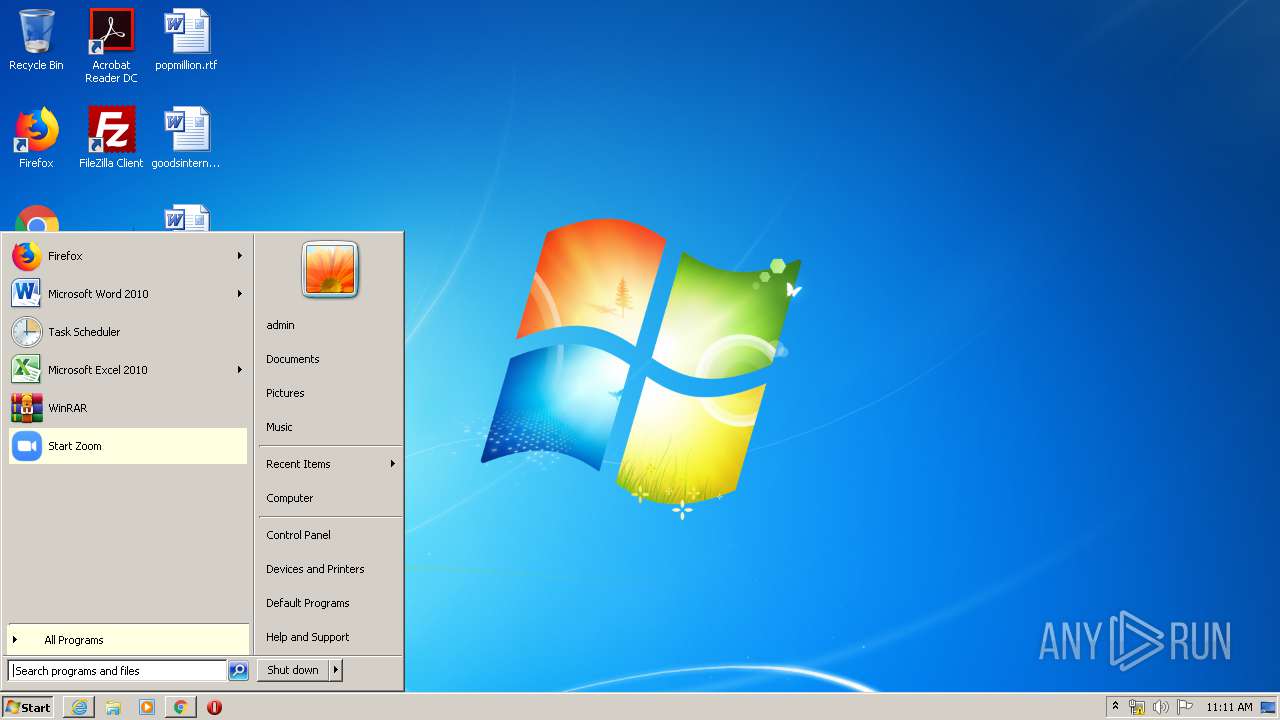
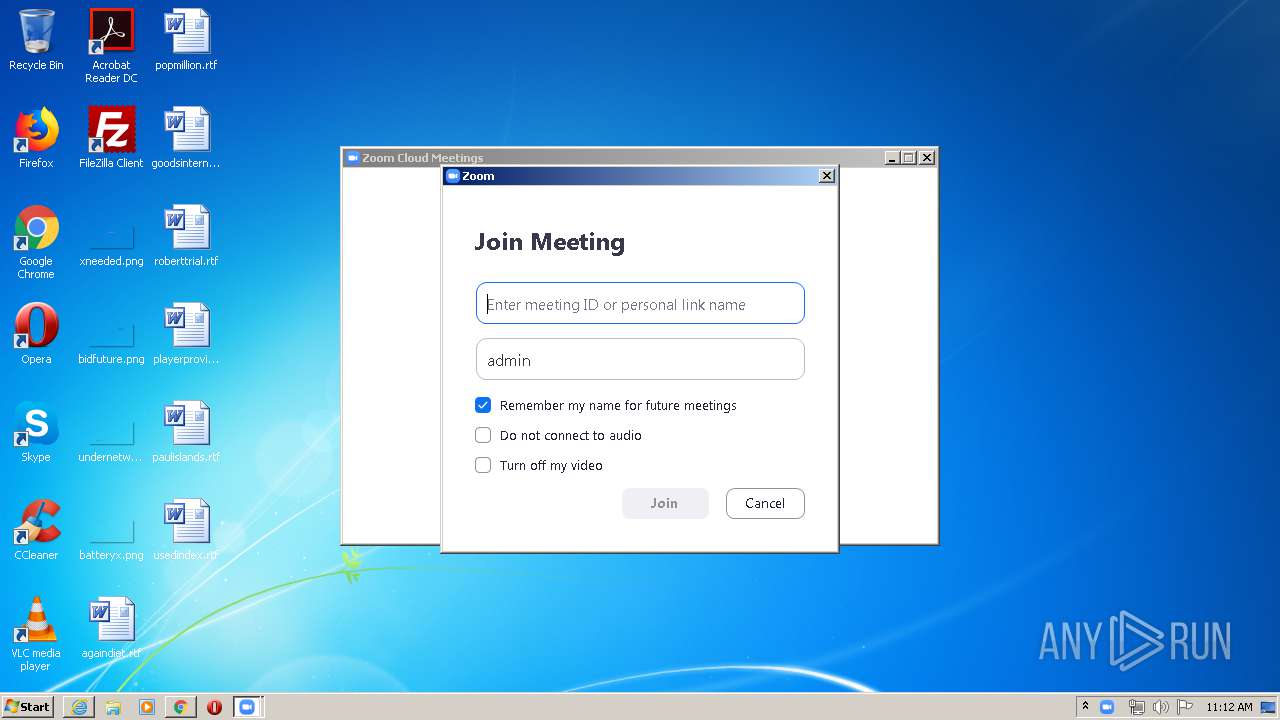
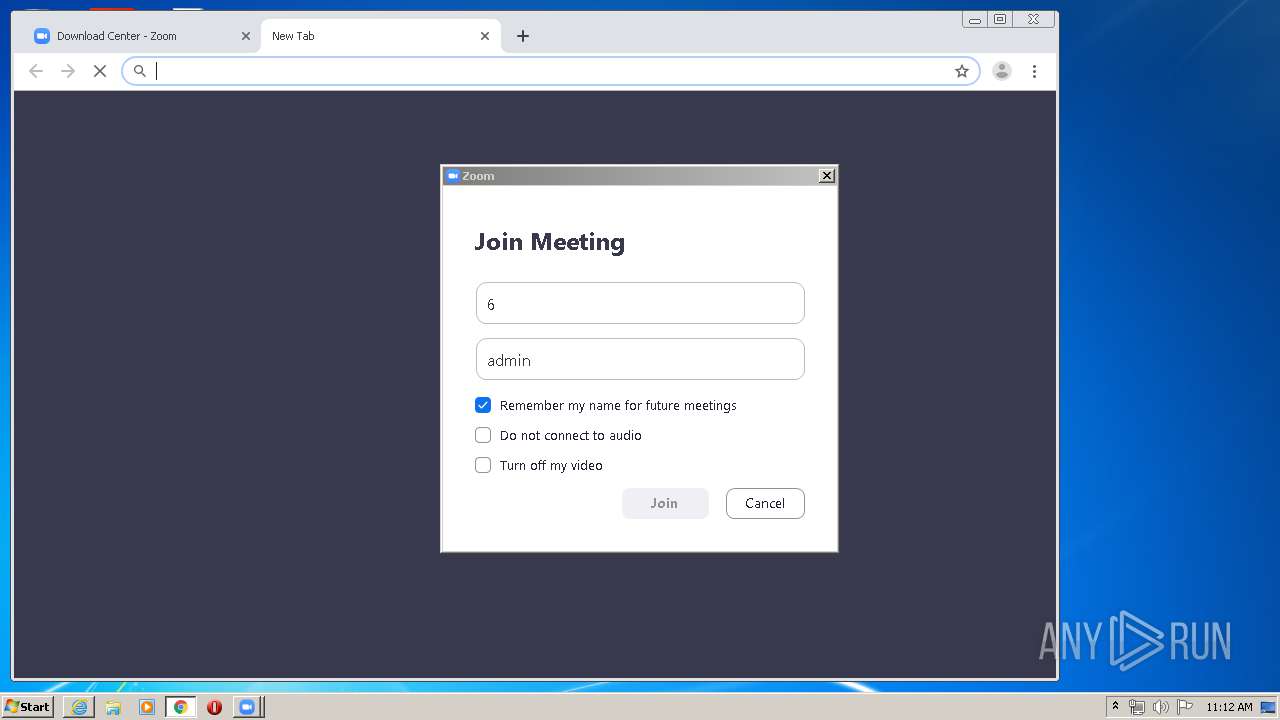
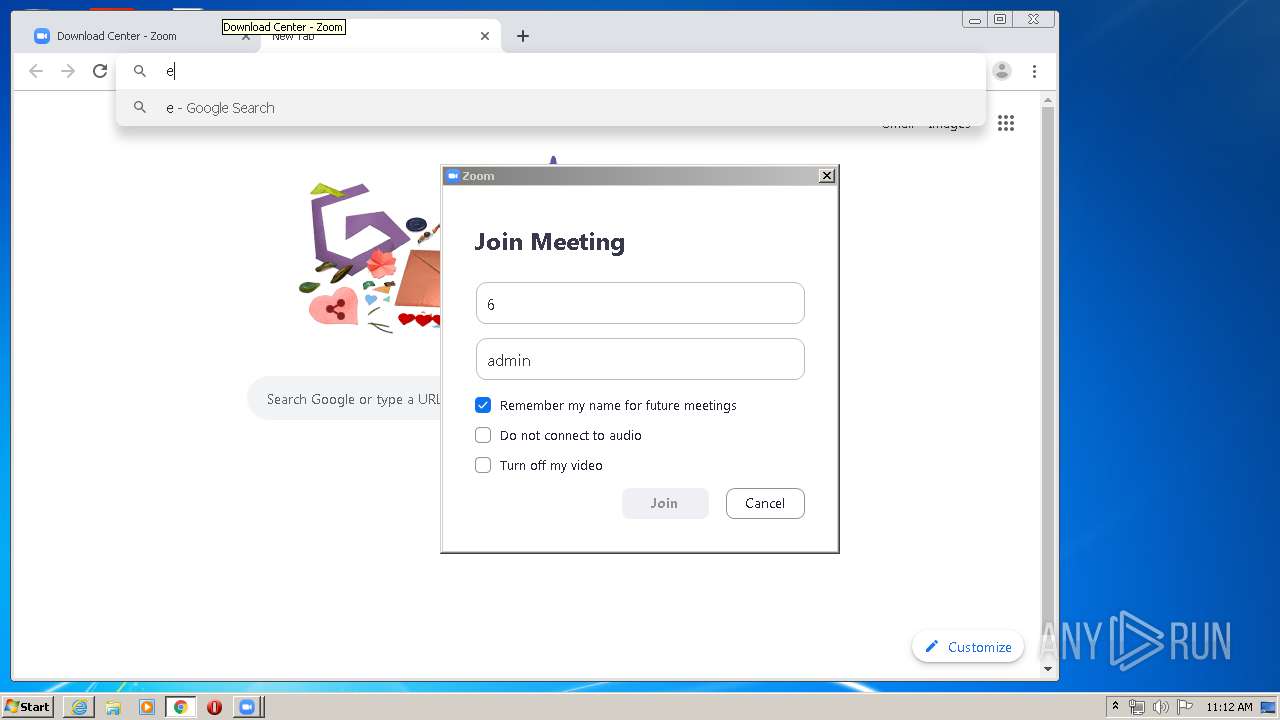
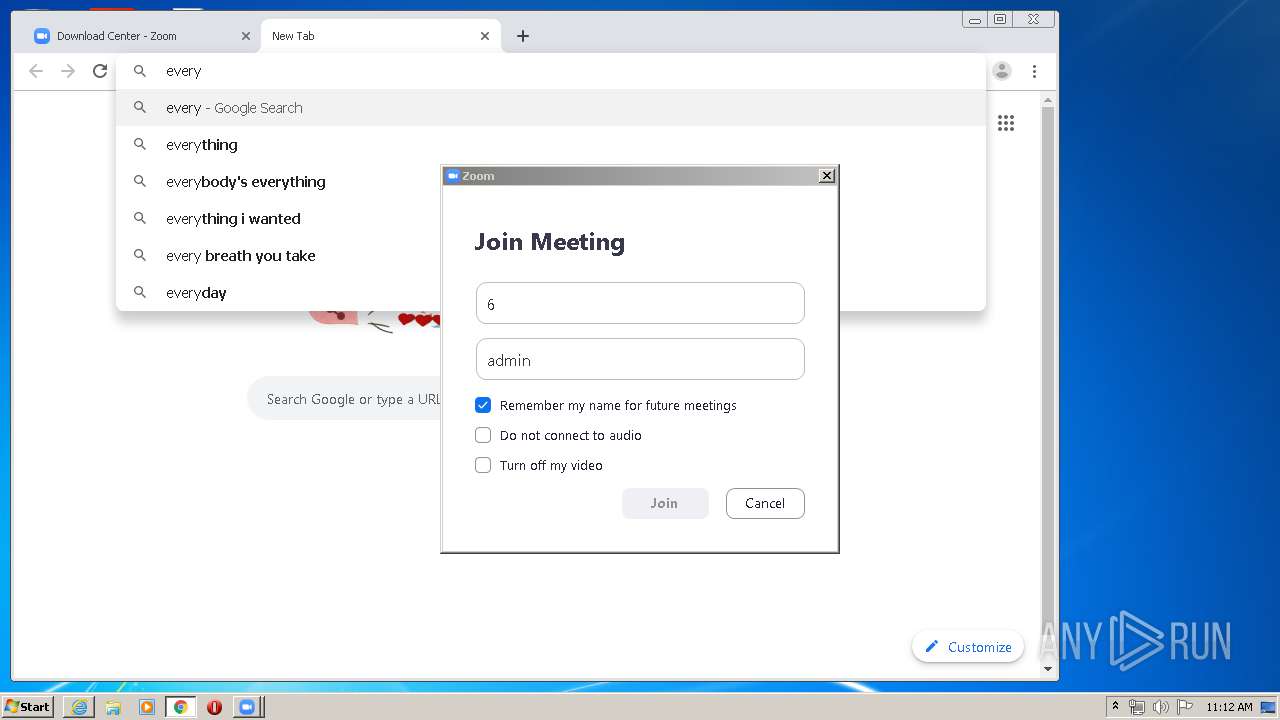
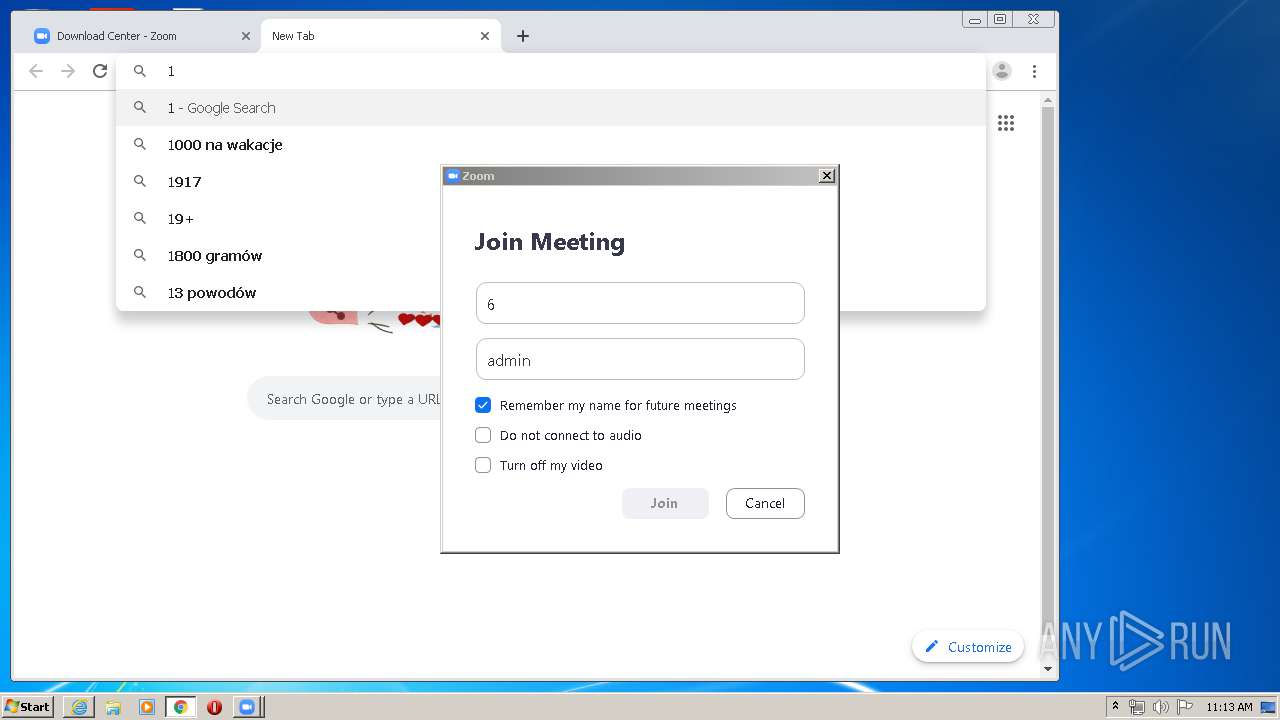
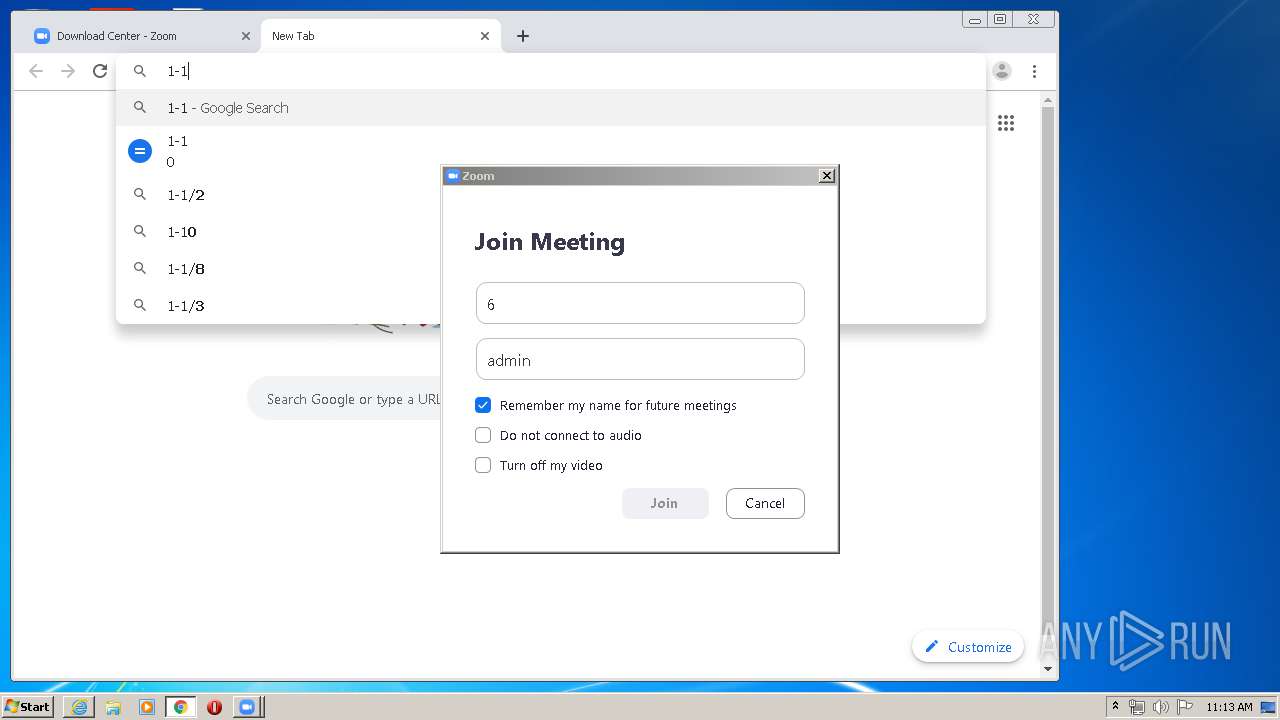
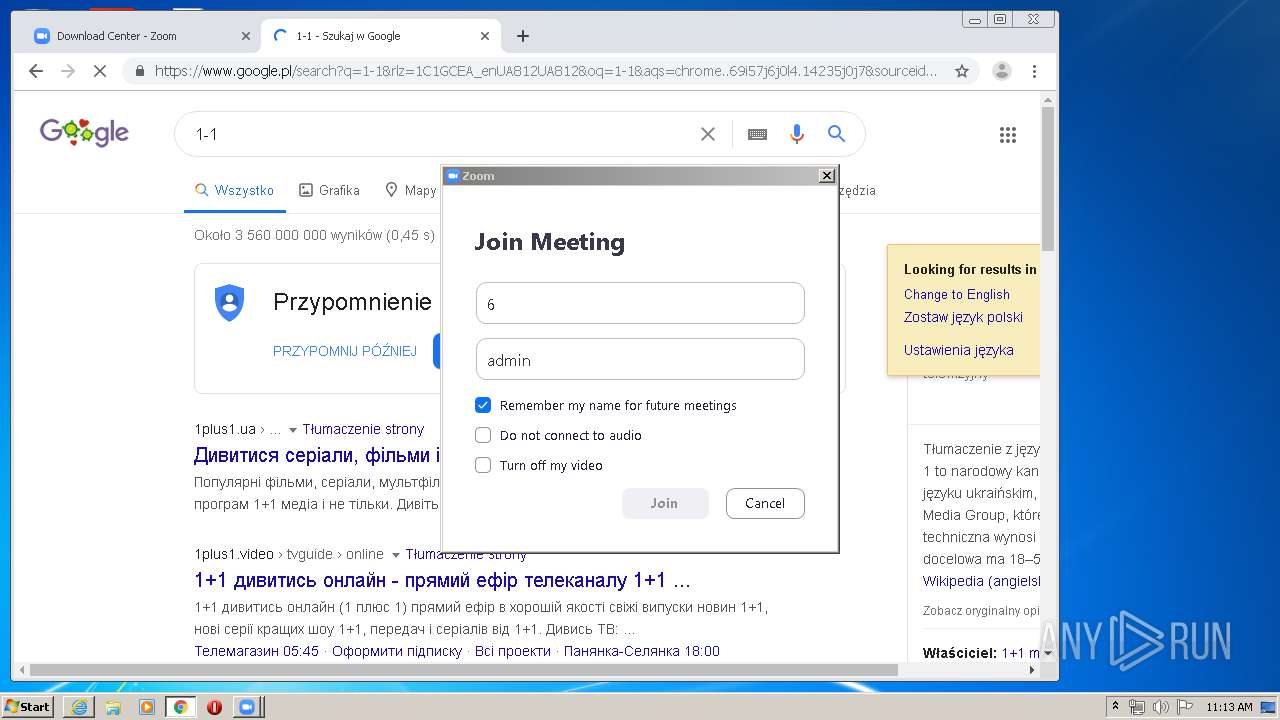
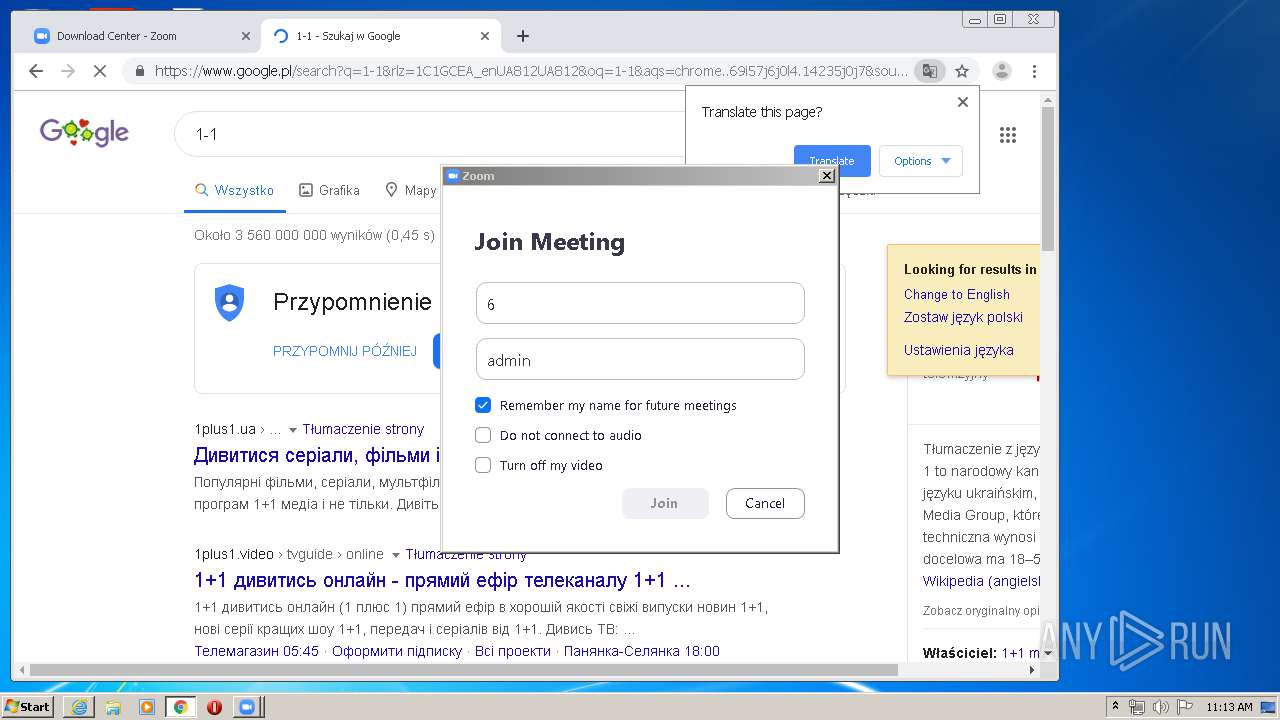
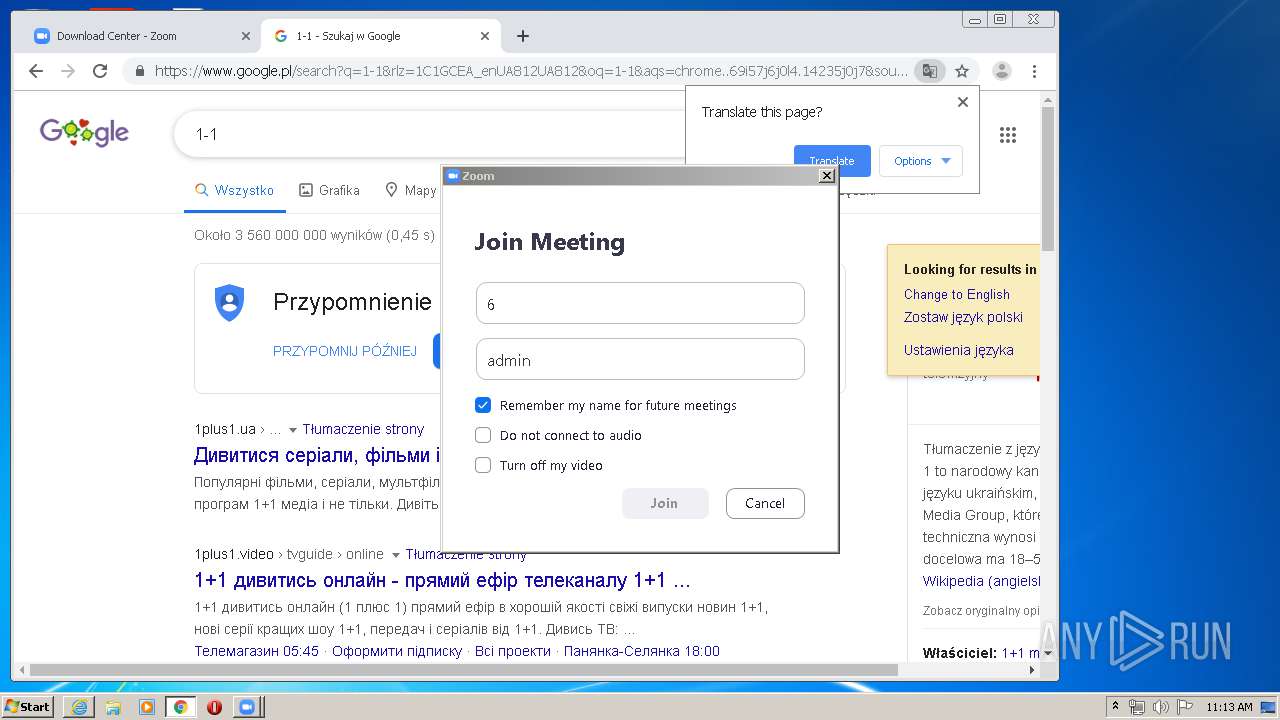
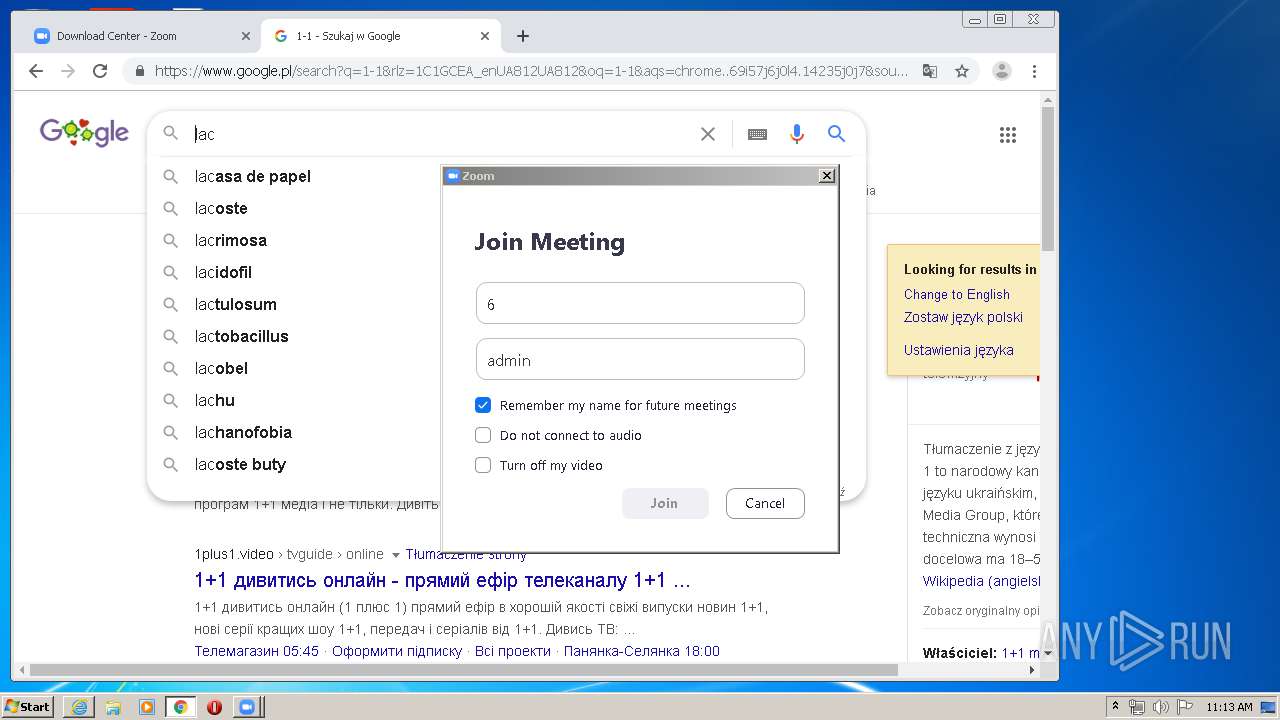
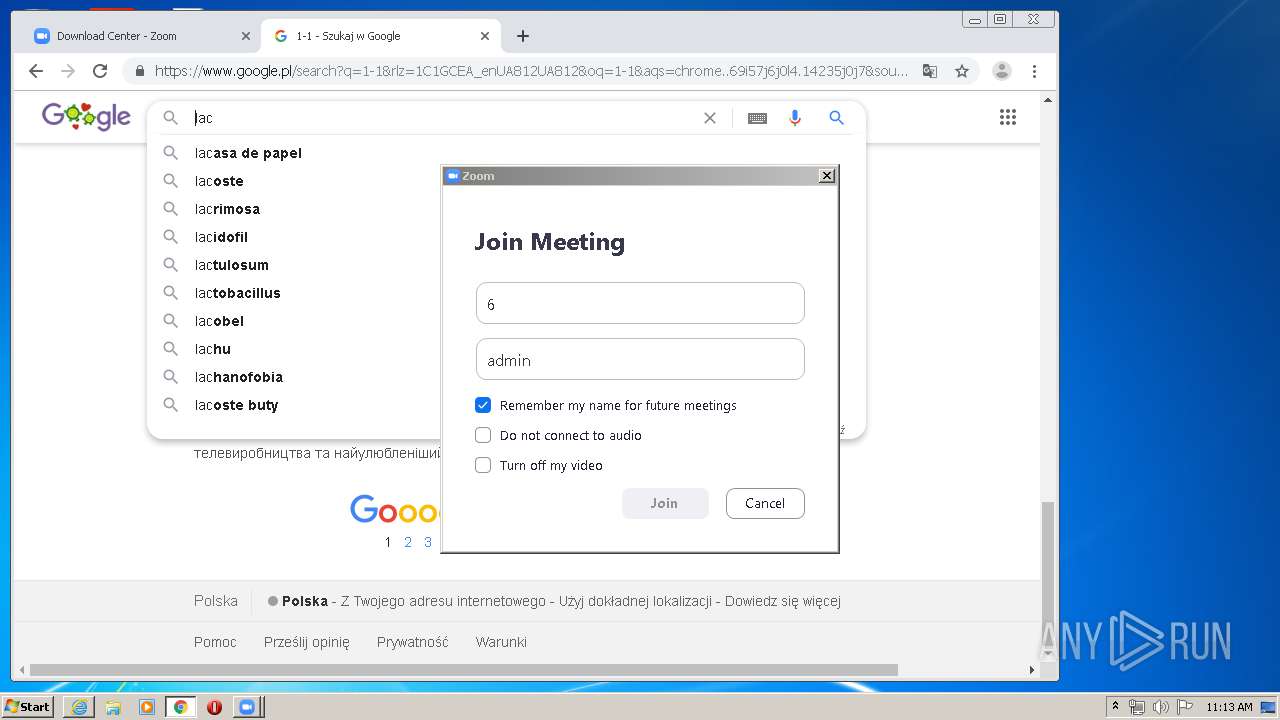
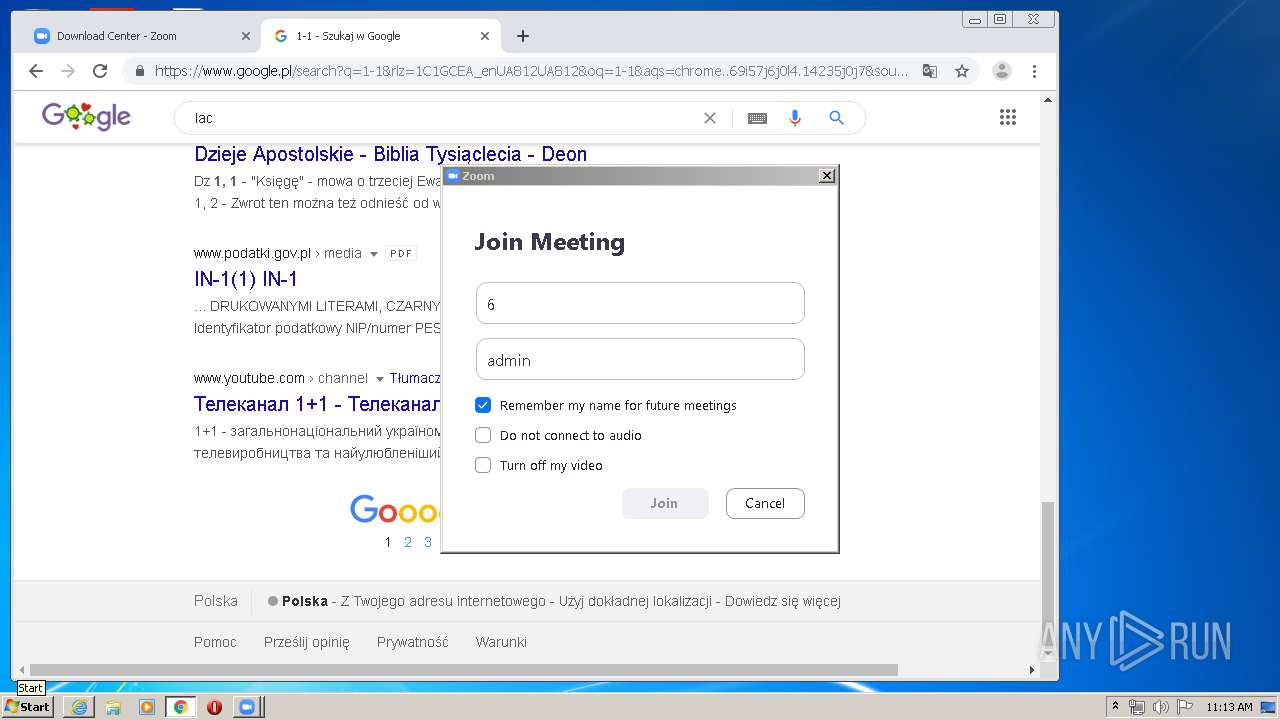
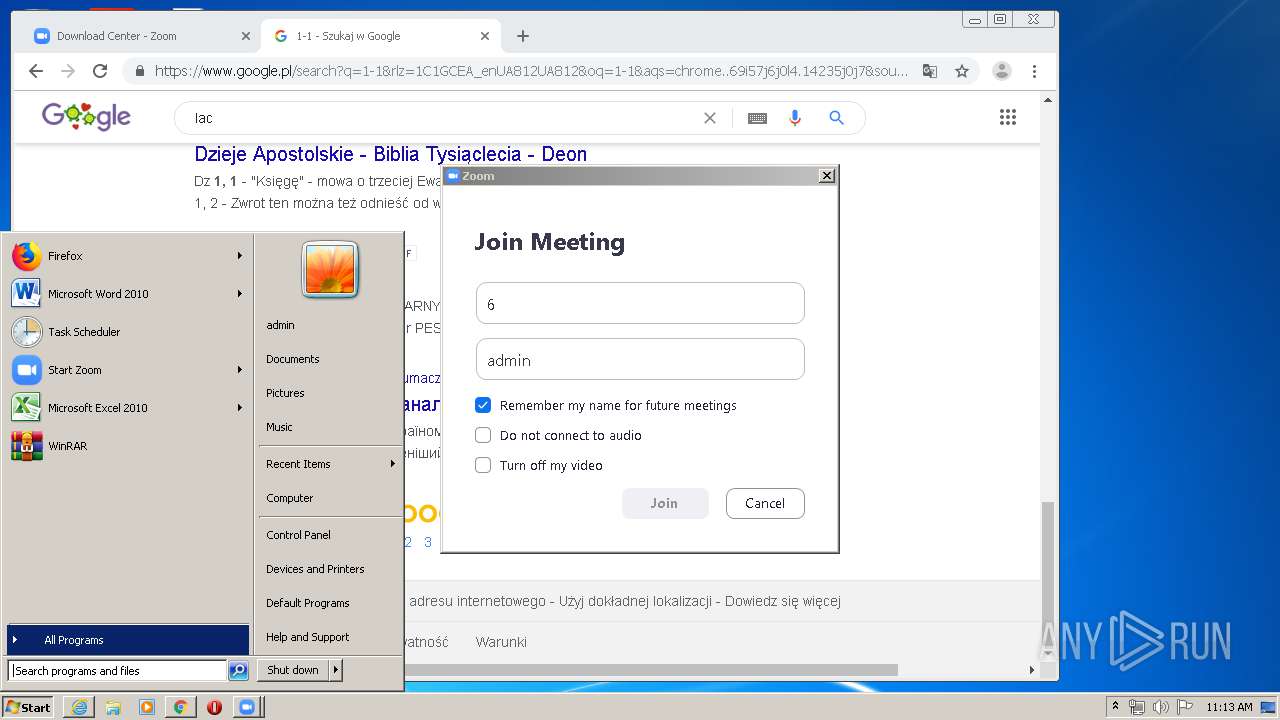
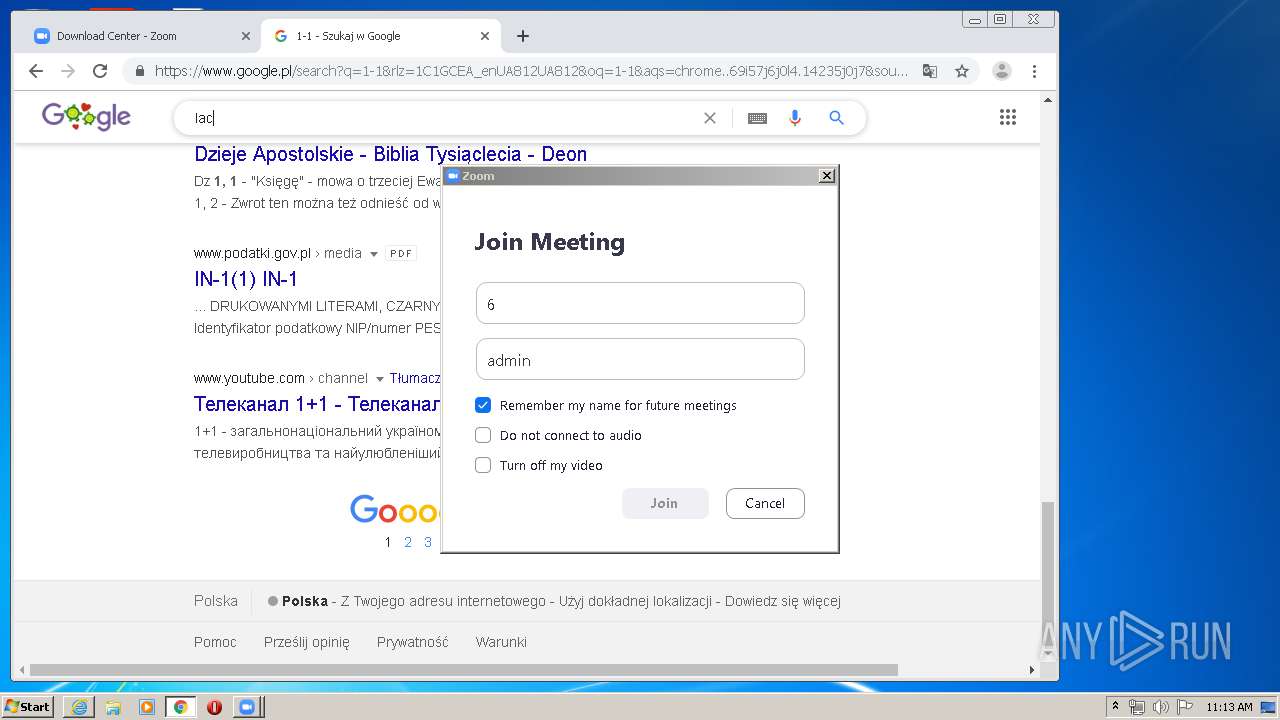
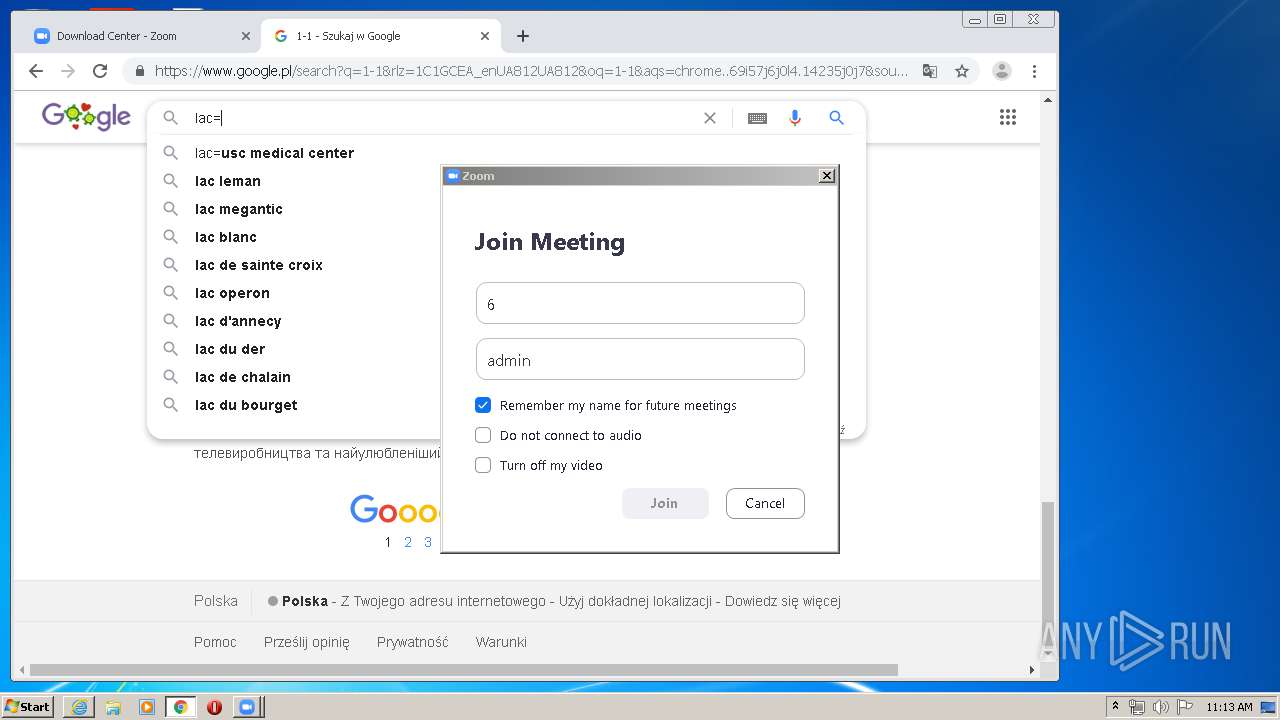
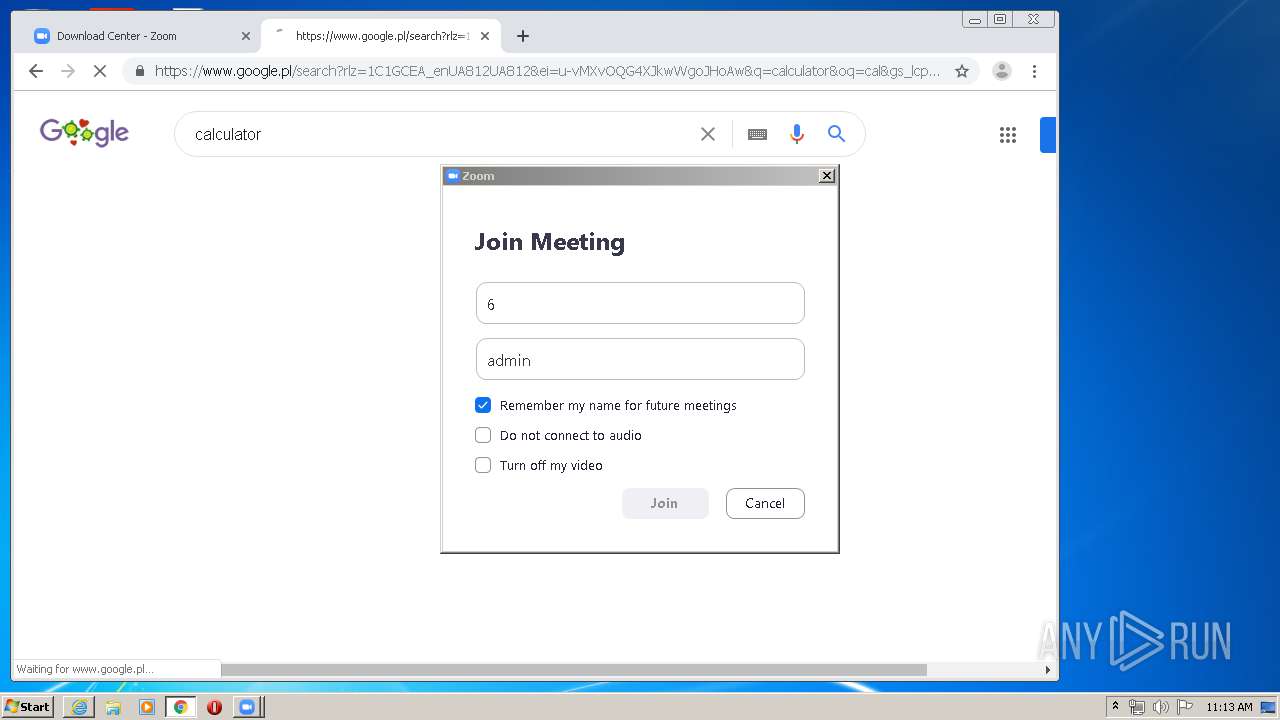
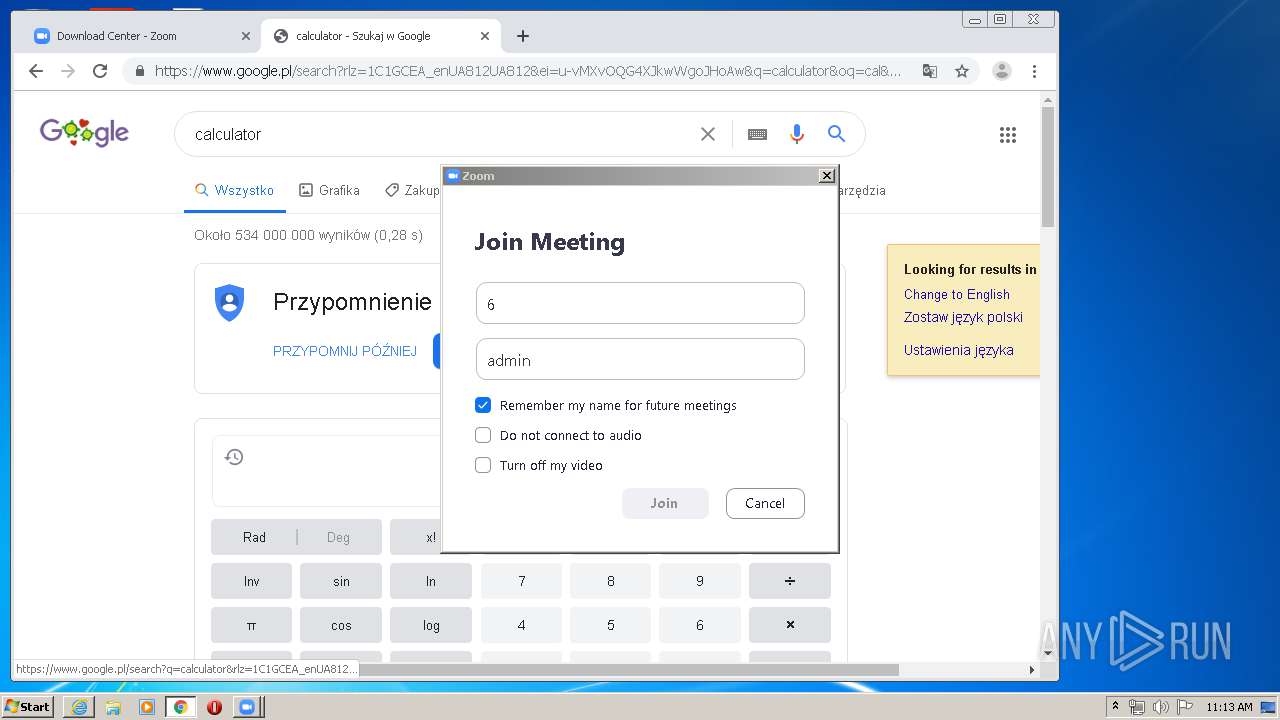
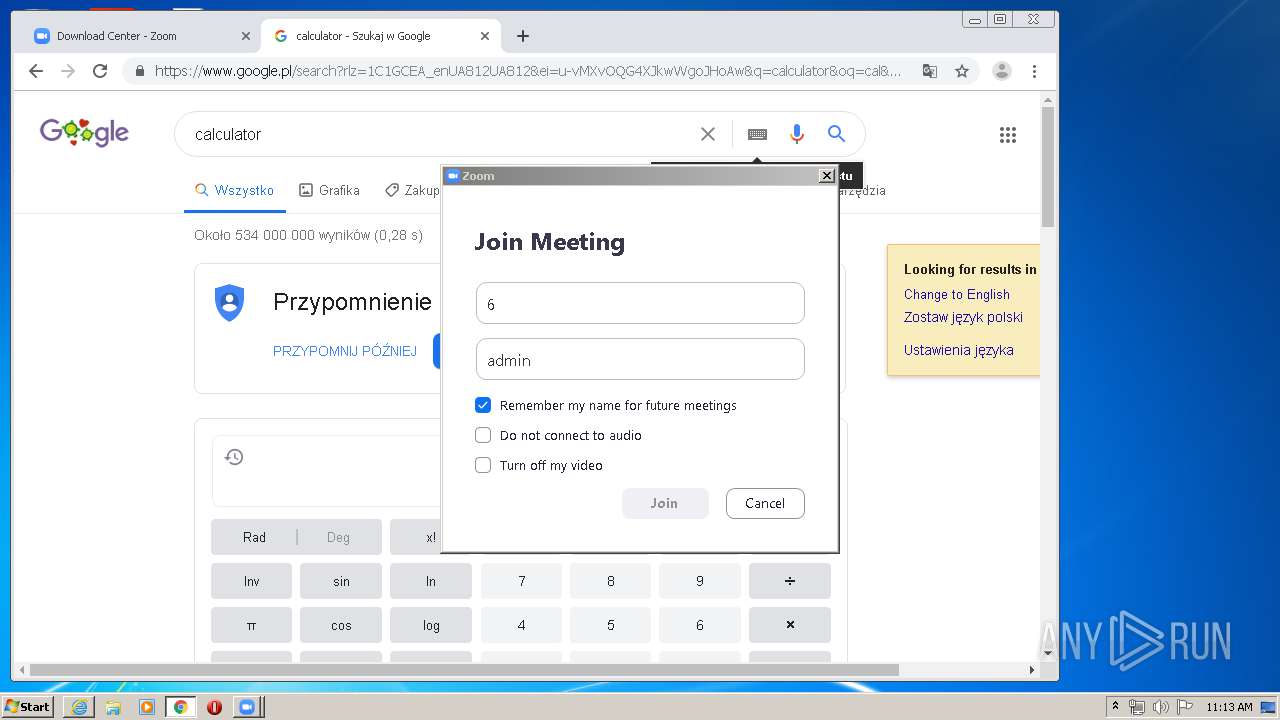
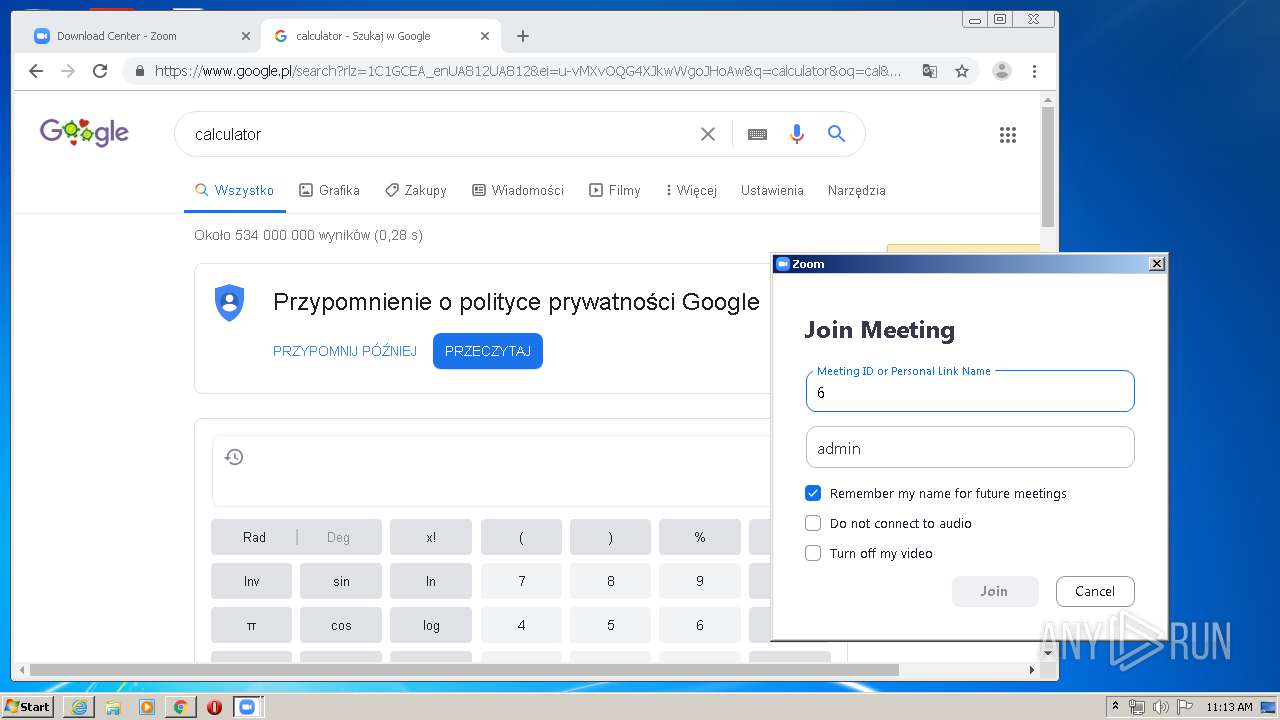
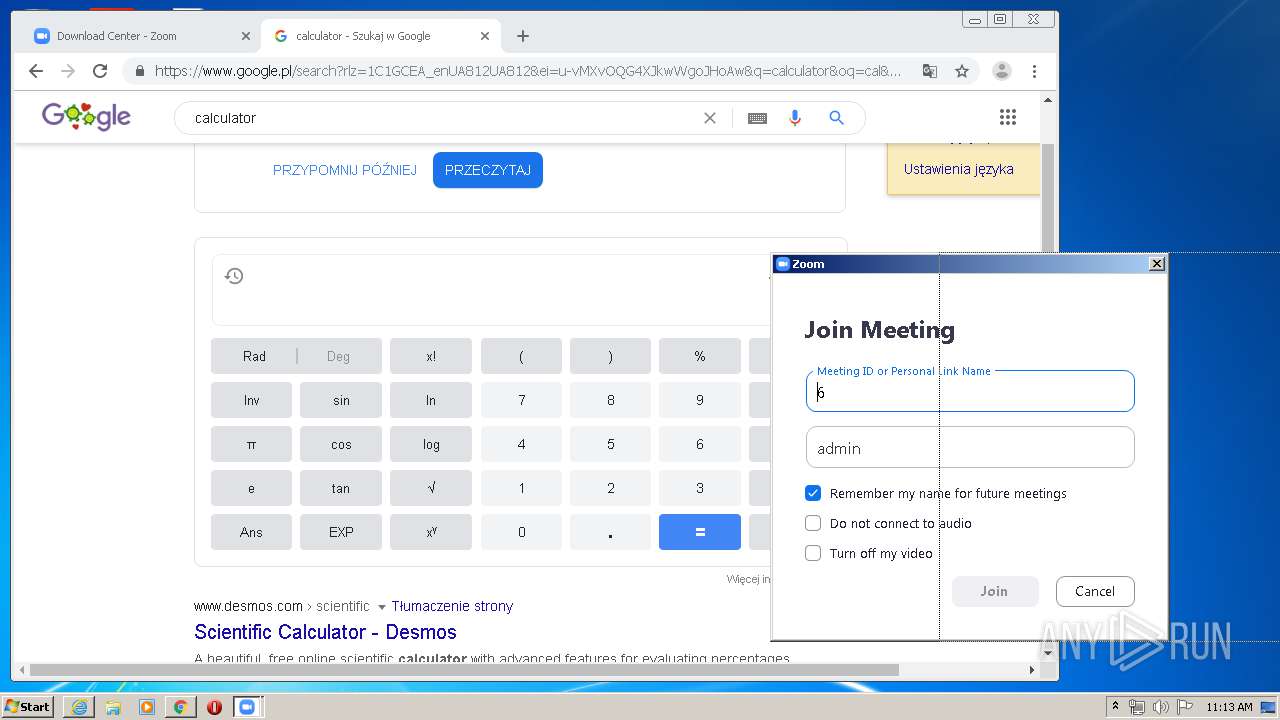
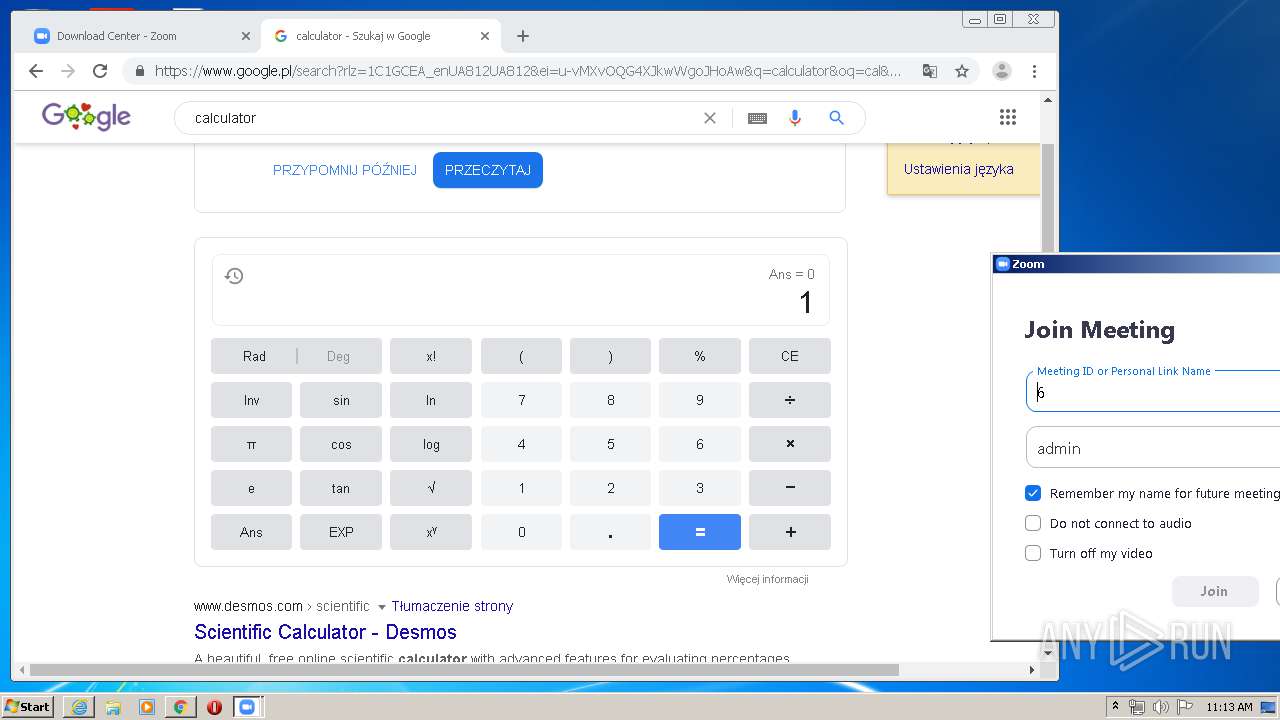
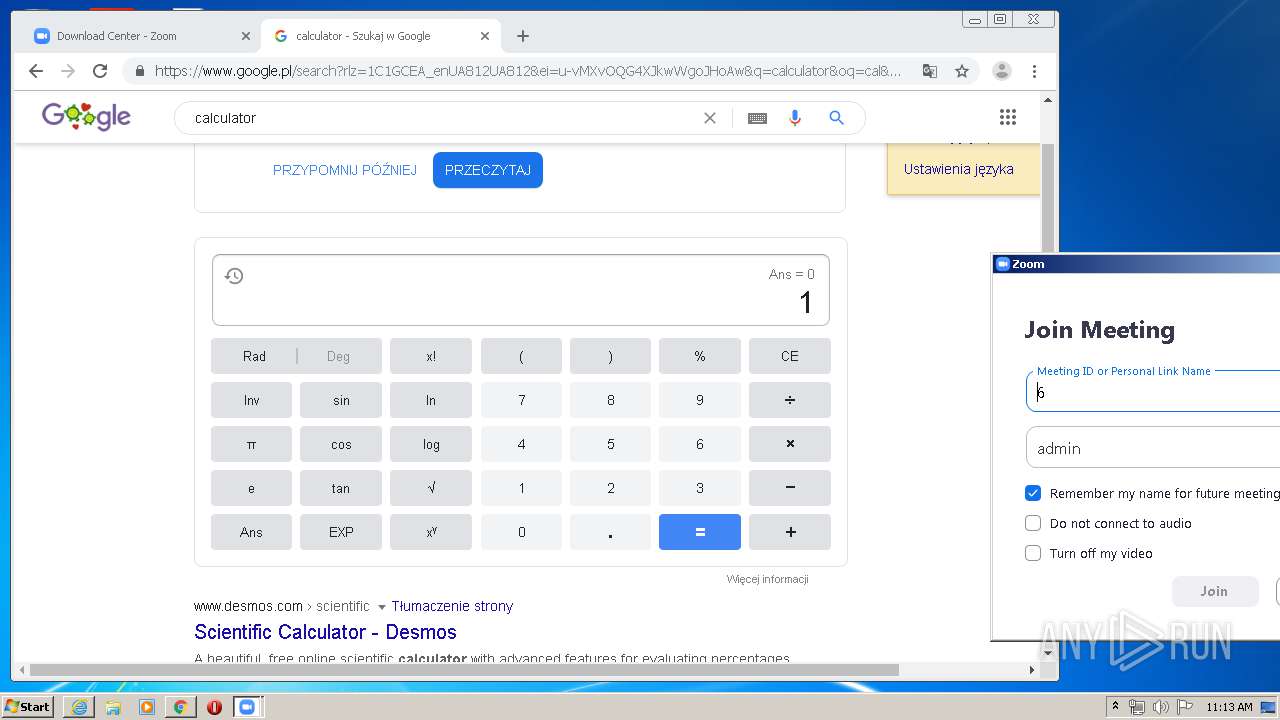
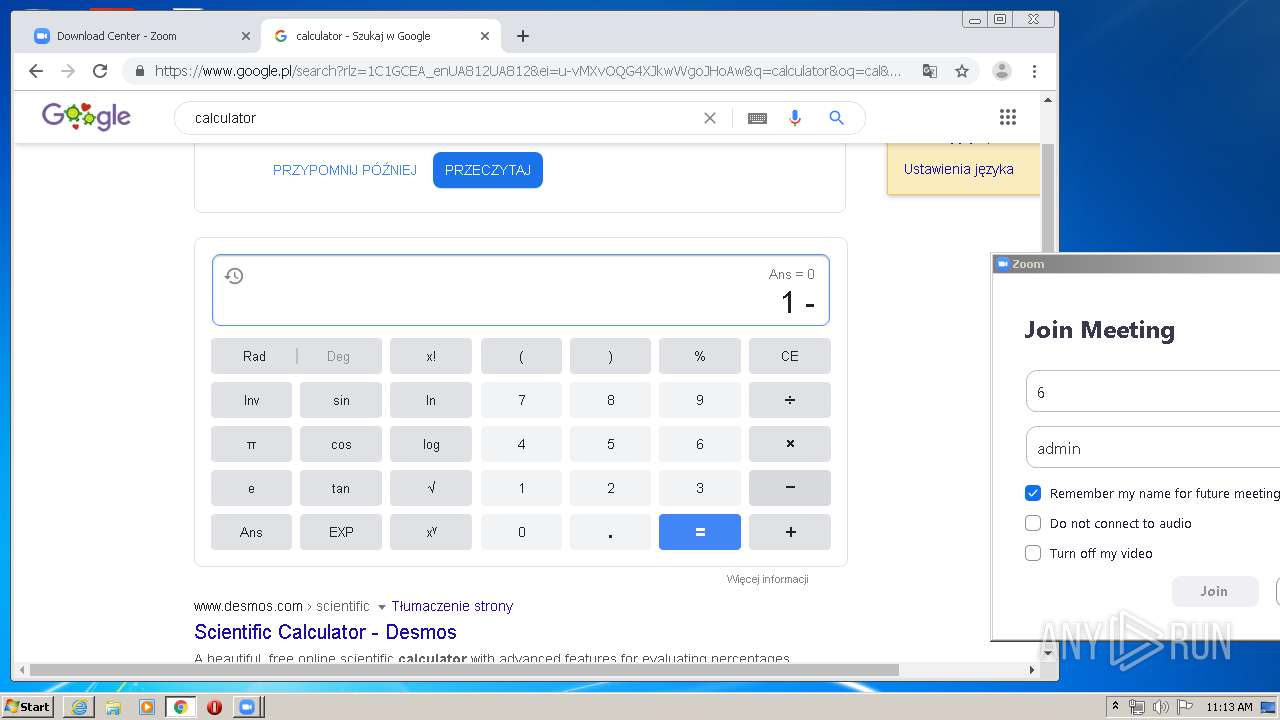
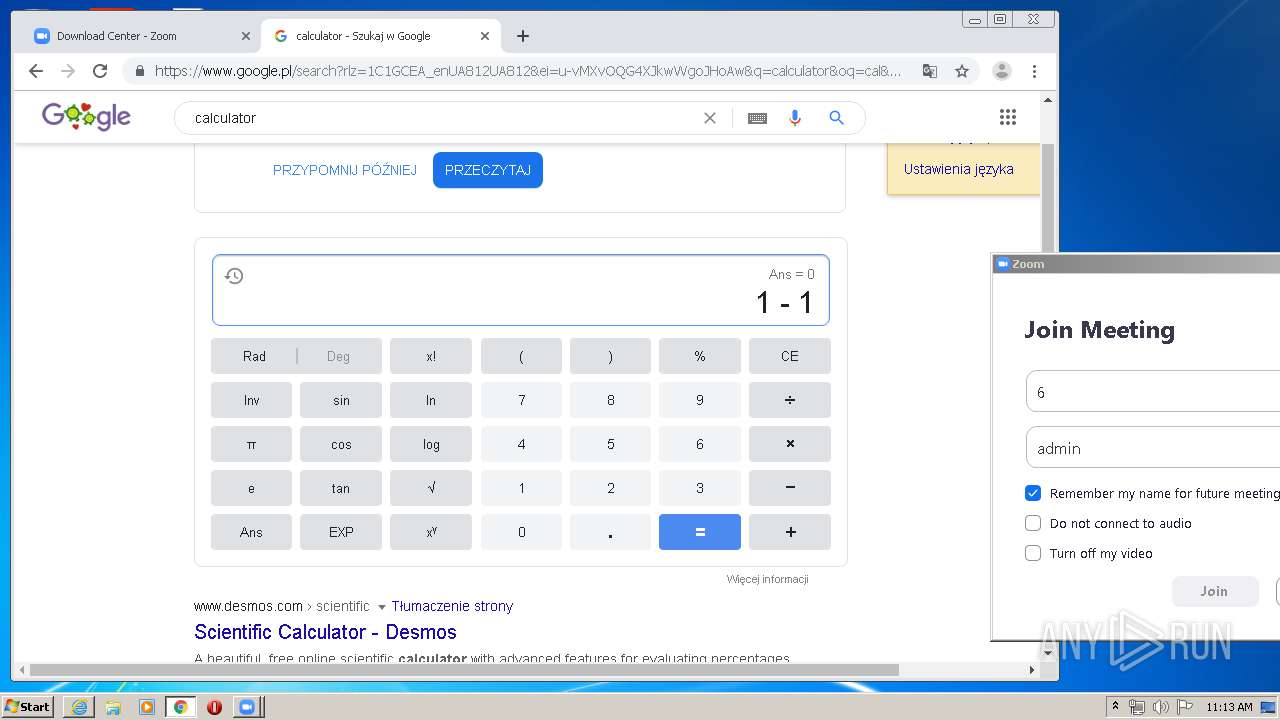
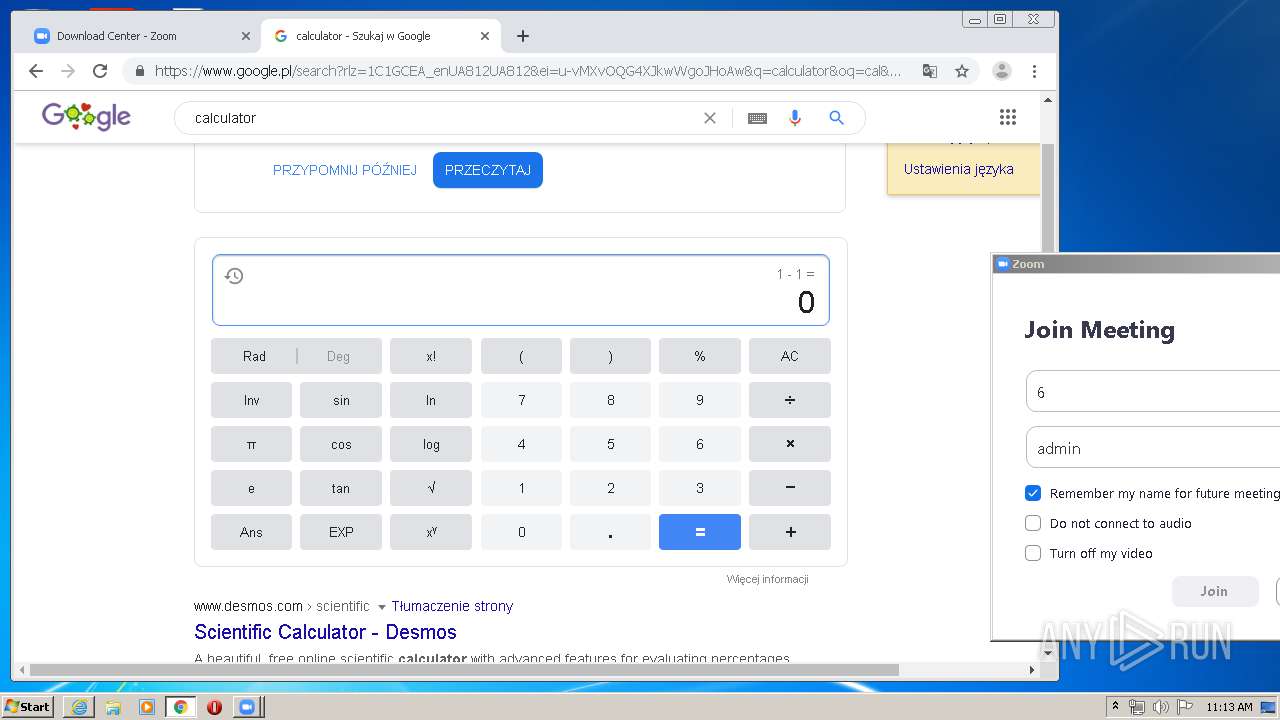
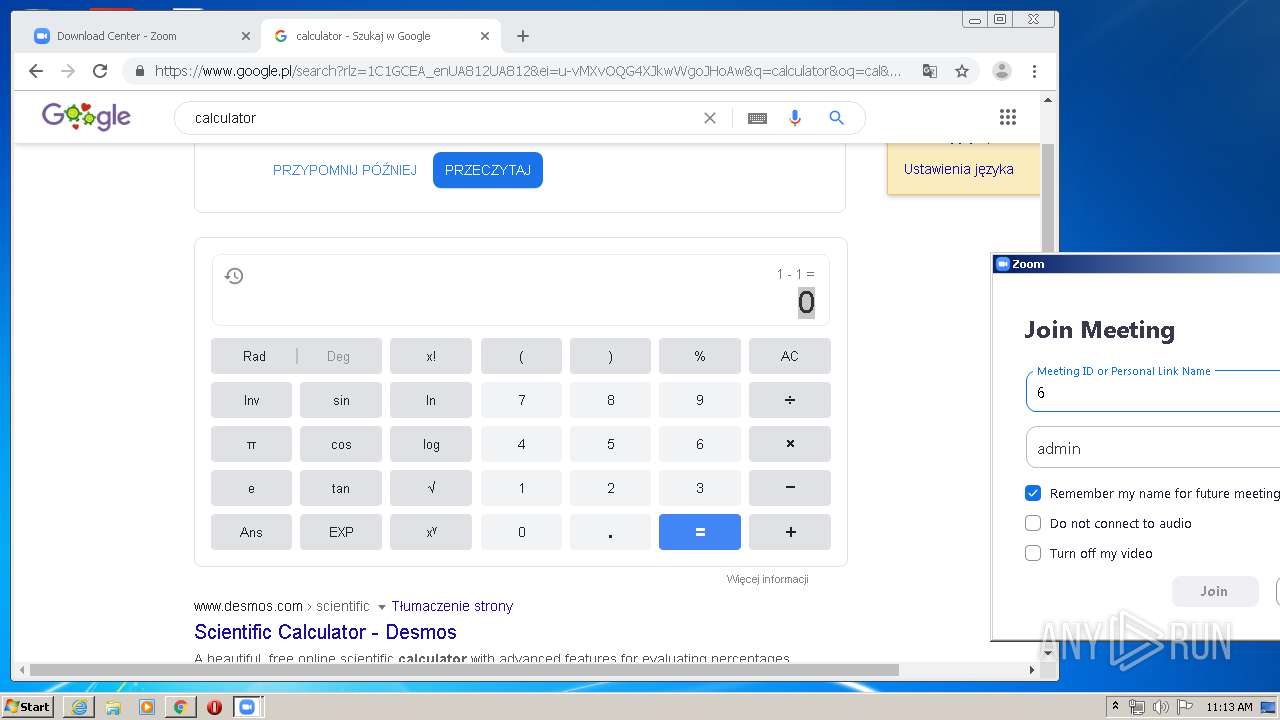
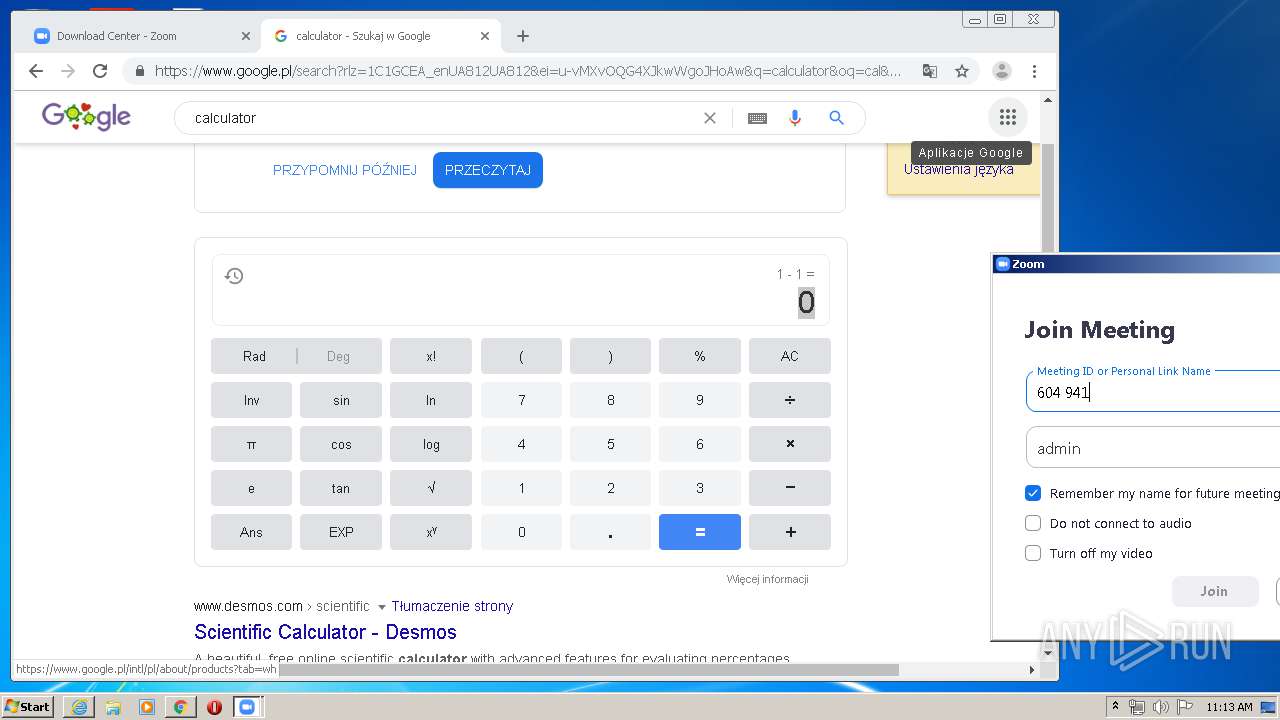
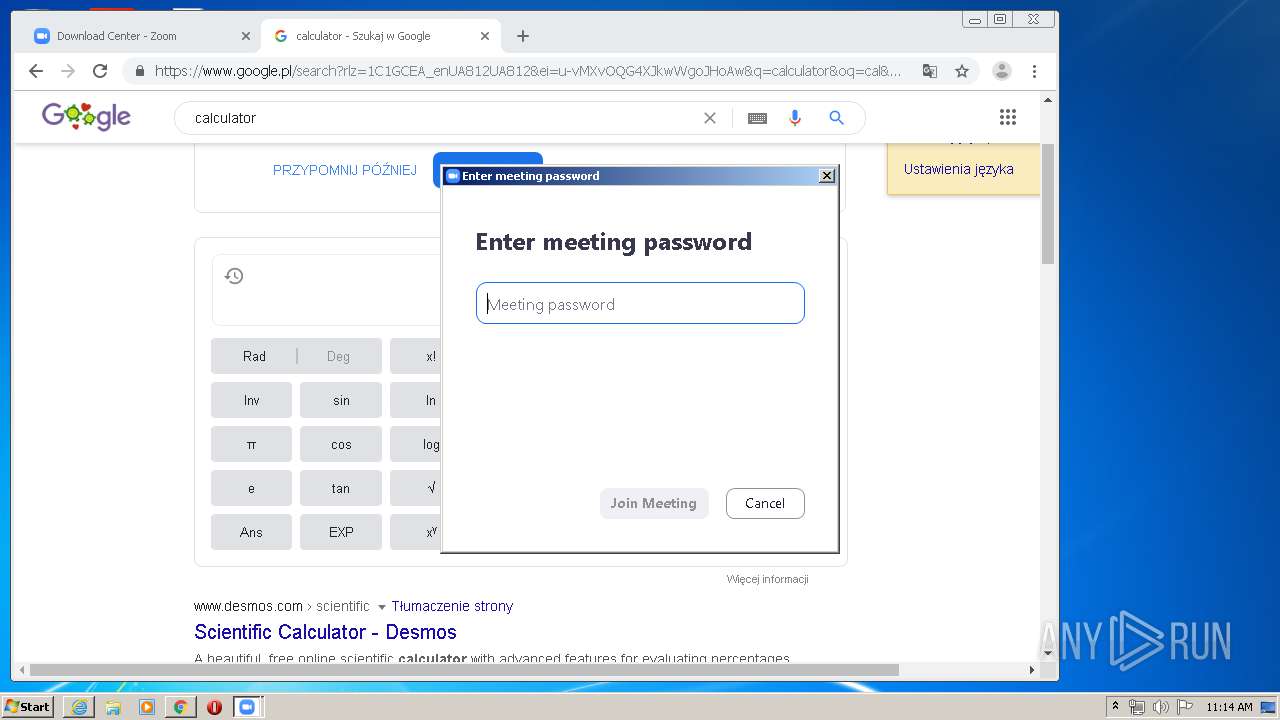
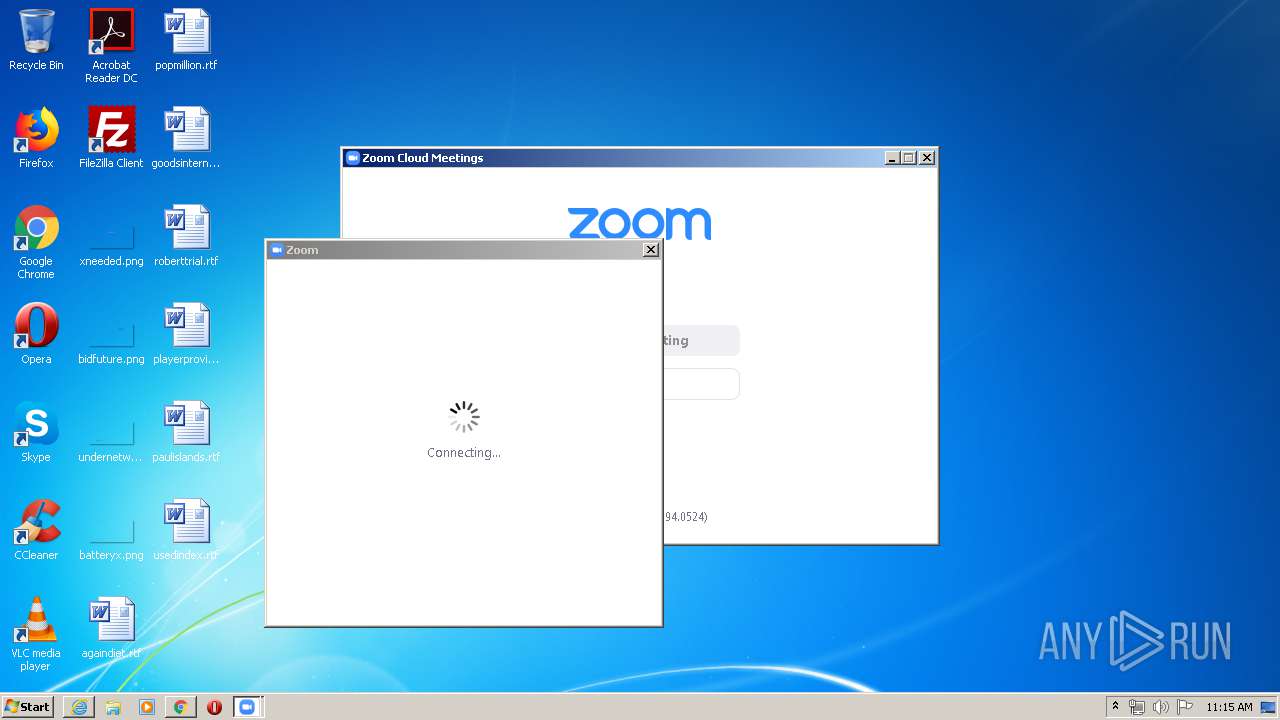
Manual execution by user
- chrome.exe (PID: 2440)
- Zoom.exe (PID: 1076)
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 1896)
Changes settings of System certificates
- iexplore.exe (PID: 2268)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
50
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
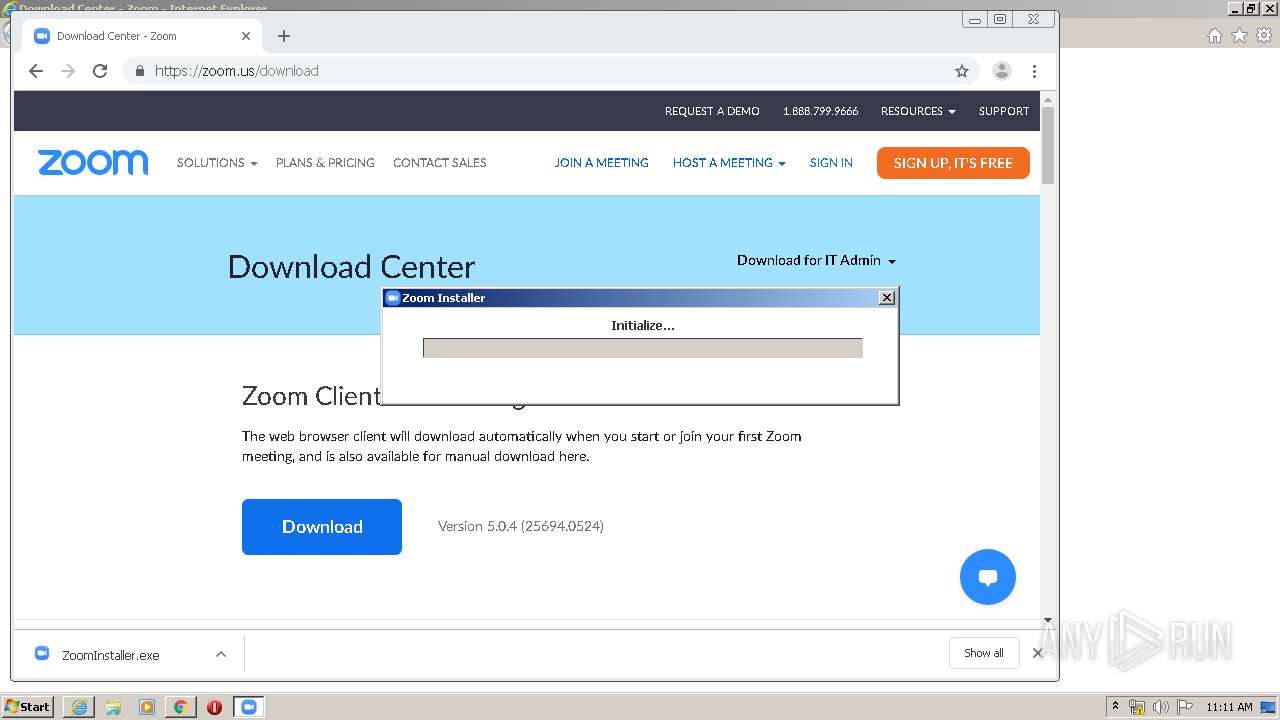
| 316 | "C:\Users\admin\AppData\Local\Temp\7zS053832F1\Installer.exe" /addfwexception --bin_home="C:\Users\admin\AppData\Roaming\Zoom\bin" | C:\Users\admin\AppData\Local\Temp\7zS053832F1\Installer.exe | Installer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: HIGH Description: Zoom Installer Exit code: 0 Version: 5,0,25694,0524 Modules
| |||||||||||||||
| 604 | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe --action=preload --runaszvideo=TRUE | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Zoom.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 5,0,25694,0524 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,4447105663500679127,14045012148458790975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3541536838711507551 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
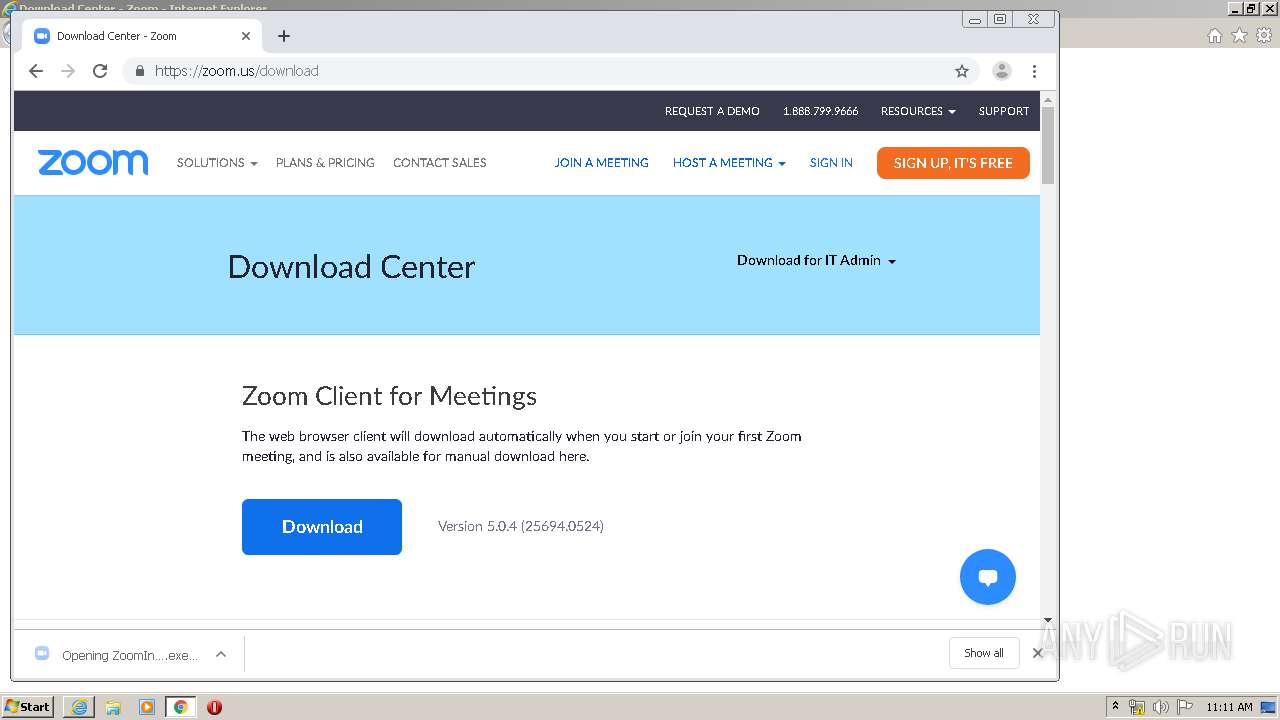
| 848 | "C:\Users\admin\Downloads\ZoomInstaller.exe" | C:\Users\admin\Downloads\ZoomInstaller.exe | chrome.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Installer Exit code: 0 Version: 5,0,0,0 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,4447105663500679127,14045012148458790975,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16286445575405661837 --mojo-platform-channel-handle=4704 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
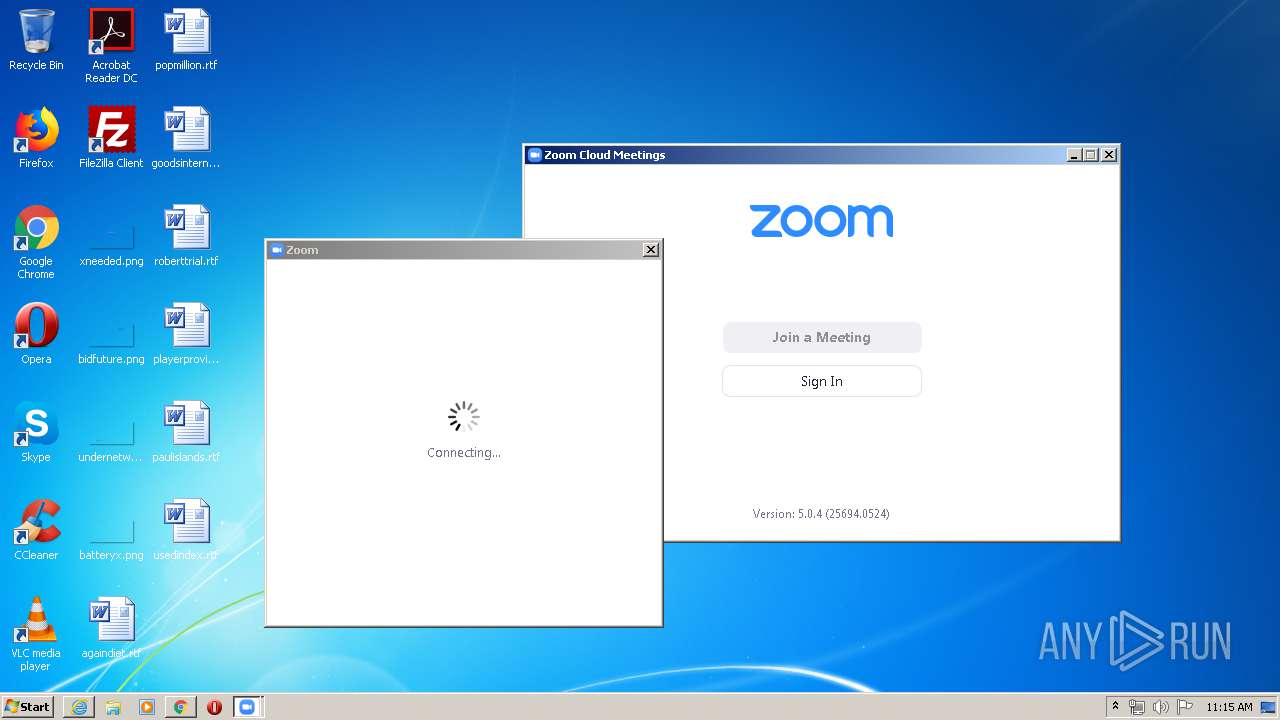
| 1076 | "C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe" | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | — | explorer.exe | |||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 5,0,25694,0524 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,4447105663500679127,14045012148458790975,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13309980740953673309 --mojo-platform-channel-handle=2752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,4447105663500679127,14045012148458790975,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1729966731784068924 --mojo-platform-channel-handle=4940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,4447105663500679127,14045012148458790975,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16902589601556306114 --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,4447105663500679127,14045012148458790975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14000577011525239089 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
7 316
Read events
2 590
Write events
3 233
Delete events
1 493
Modification events
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4238255430 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30815045 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
93
Suspicious files
162
Text files
326
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1788 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab22F6.tmp | — | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar22F7.tmp | — | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\J18SU7O5.txt | — | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8ODHBB6L.txt | — | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download[1].htm | html | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:— | SHA256:— | |||
| 1788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
134
DNS requests
72
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1788 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
1788 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
1788 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1788 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
1788 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2676 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
2676 | chrome.exe | GET | 200 | 176.126.58.207:80 | http://r4---sn-x2pm-3ufk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=84.17.55.74&mm=28&mn=sn-x2pm-3ufk&ms=nvh&mt=1590487810&mv=m&mvi=3&pl=26&shardbypass=yes | PL | crx | 816 Kb | whitelisted |
1788 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
1788 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
1788 | iexplore.exe | GET | 200 | 143.204.208.160:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1788 | iexplore.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
1788 | iexplore.exe | 52.202.62.233:443 | zoom.us | Amazon.com, Inc. | US | unknown |
1788 | iexplore.exe | 13.35.253.14:443 | d24cgw3uvb9a9h.cloudfront.net | — | US | unknown |
1788 | iexplore.exe | 143.204.201.115:443 | static.ada.support | — | US | malicious |
1788 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2268 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1788 | iexplore.exe | 104.16.55.111:443 | zoomus.zendesk.com | Cloudflare Inc | US | shared |
2268 | iexplore.exe | 13.35.253.14:443 | d24cgw3uvb9a9h.cloudfront.net | — | US | unknown |
1788 | iexplore.exe | 143.204.208.160:80 | o.ss2.us | — | US | malicious |
1788 | iexplore.exe | 13.35.253.198:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zoom.us |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
d24cgw3uvb9a9h.cloudfront.net |
| shared |
static.ada.support |
| whitelisted |
static.zdassets.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
s.symcd.com |
| shared |
o.ss2.us |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Installer.exe | |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\uninstall |
Installer.exe | |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\bin |
Installer.exe | [CZoomProductPathHelper::RecursiveRemoveDirA] Path is: |