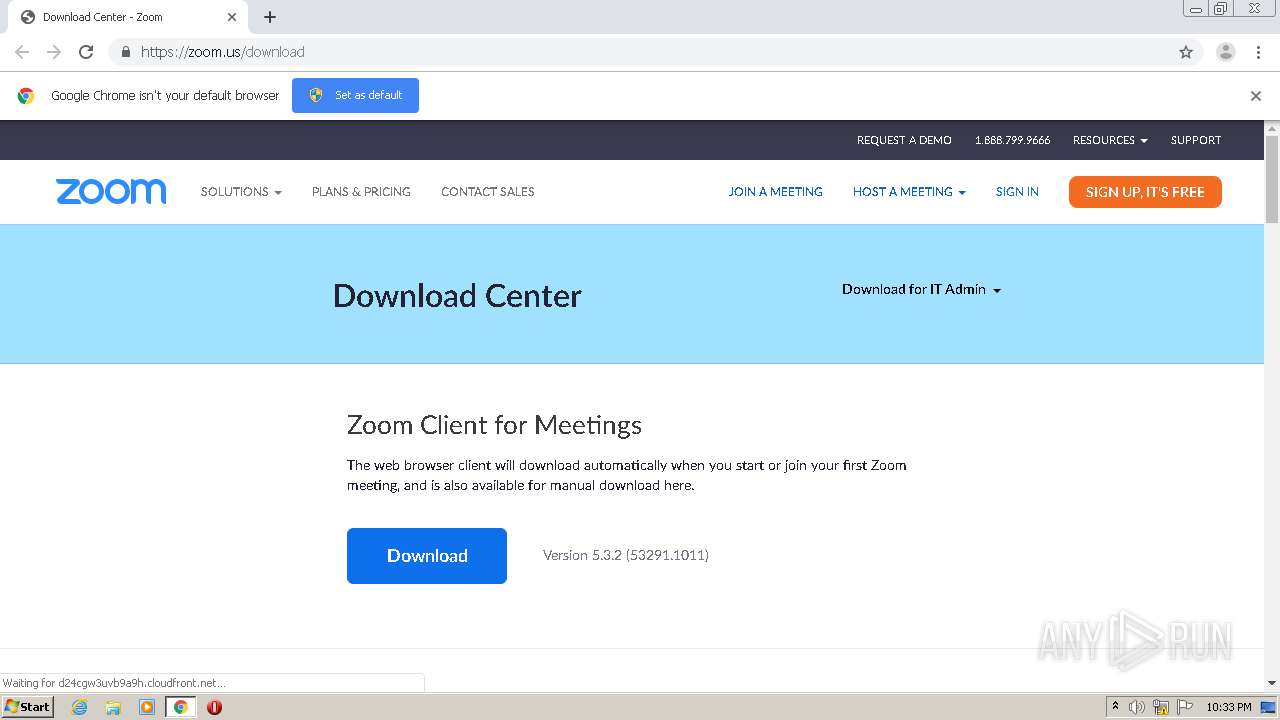
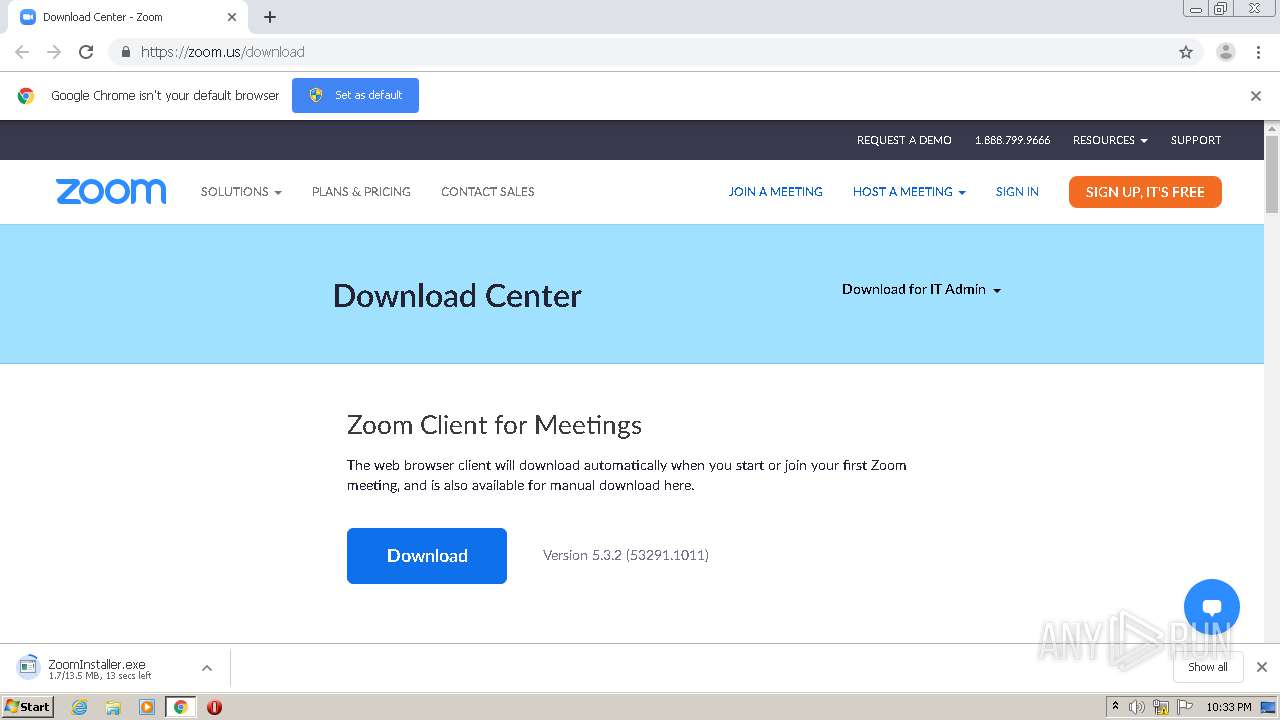
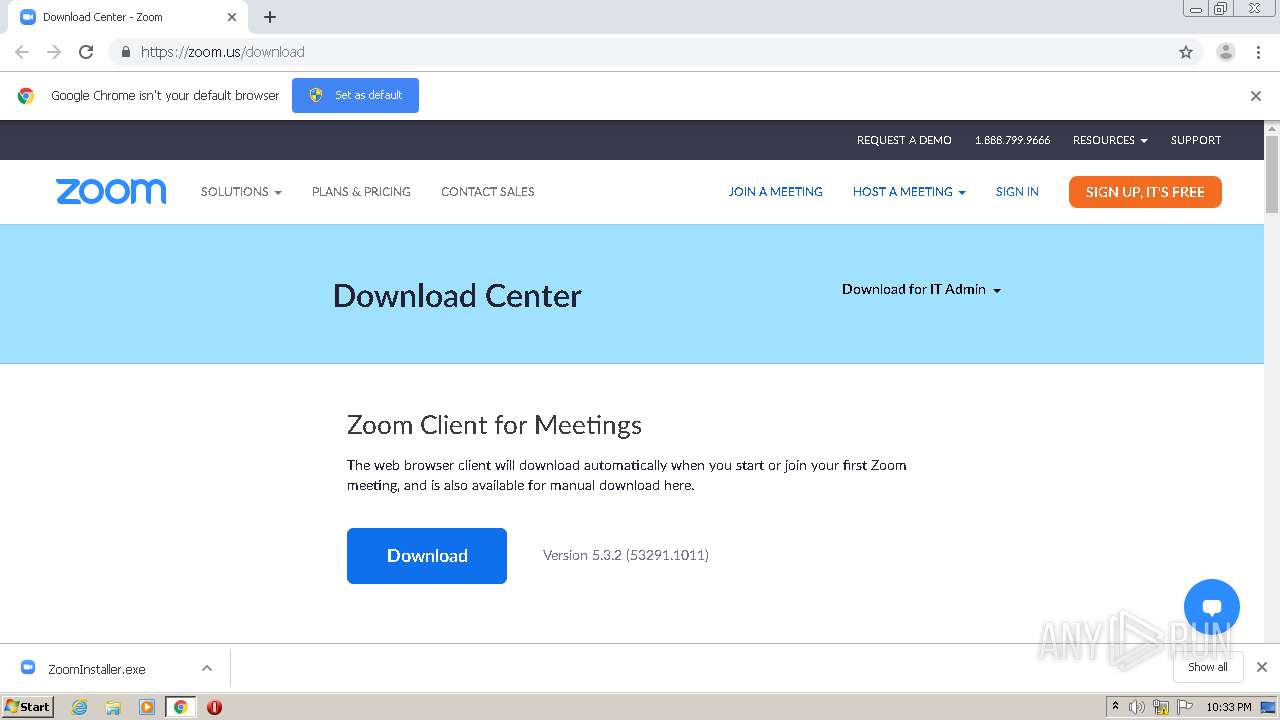
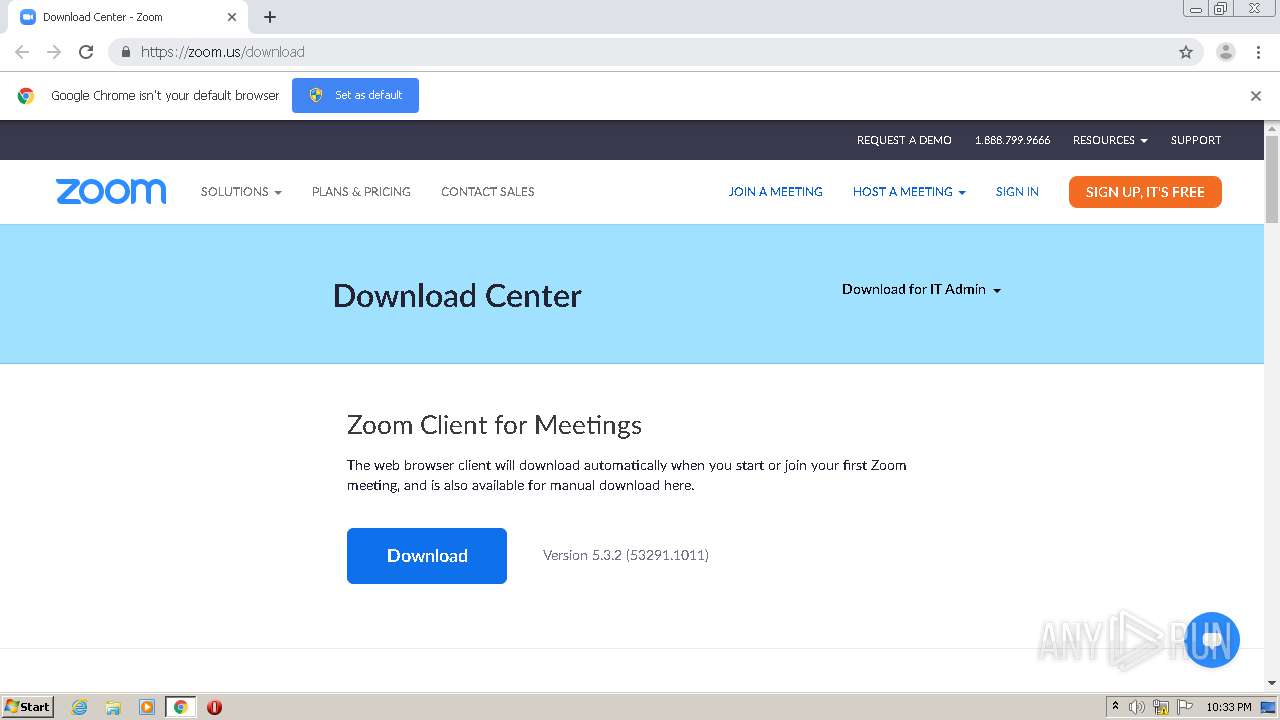
| URL: | https://zoom.us/download |
| Full analysis: | https://app.any.run/tasks/a7cd2b29-c2d9-405a-bfe9-234f249d4fe1 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 21:32:39 |
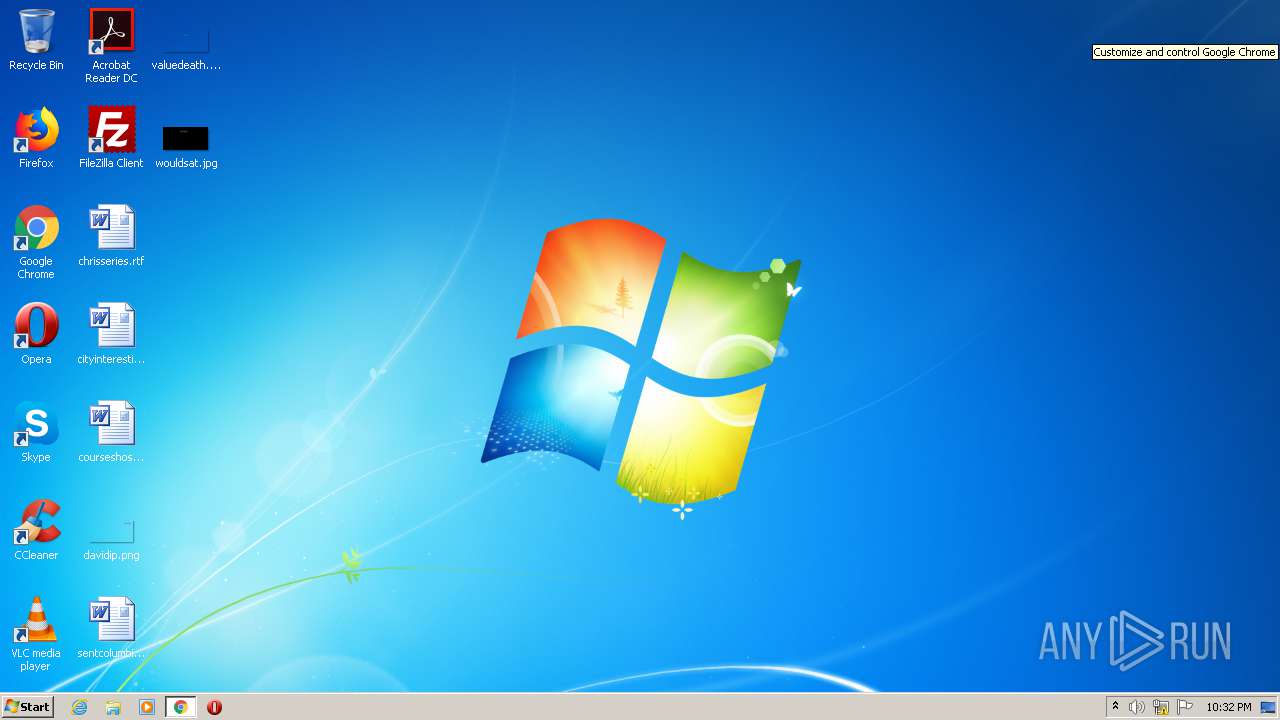
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 41363F334D7D65A496F70DFF9534A87D |
| SHA1: | BBD883BBE24089AE507329898A267B11CE7645B2 |
| SHA256: | 0F849765756CF76166EE7F7440EA3D64AE4C3E02309BE81AE7A81DE3A93832D3 |
| SSDEEP: | 3:N88LWDLz:28LWj |
MALICIOUS
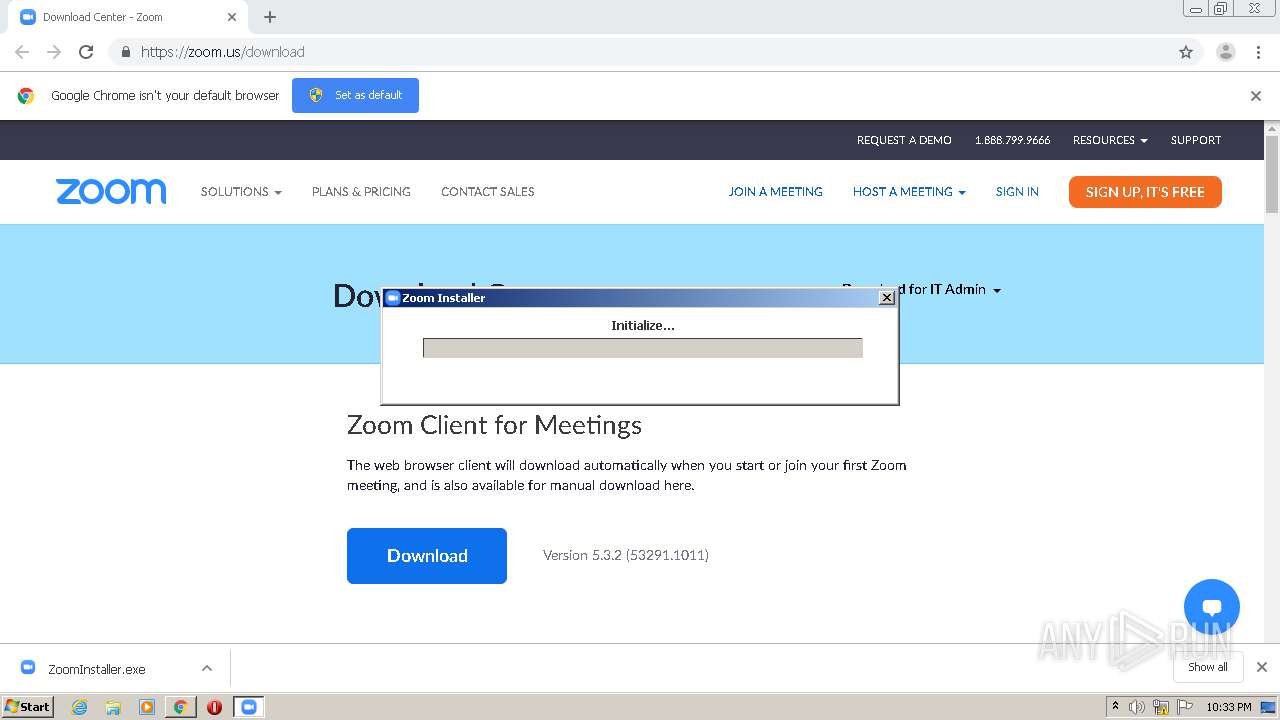
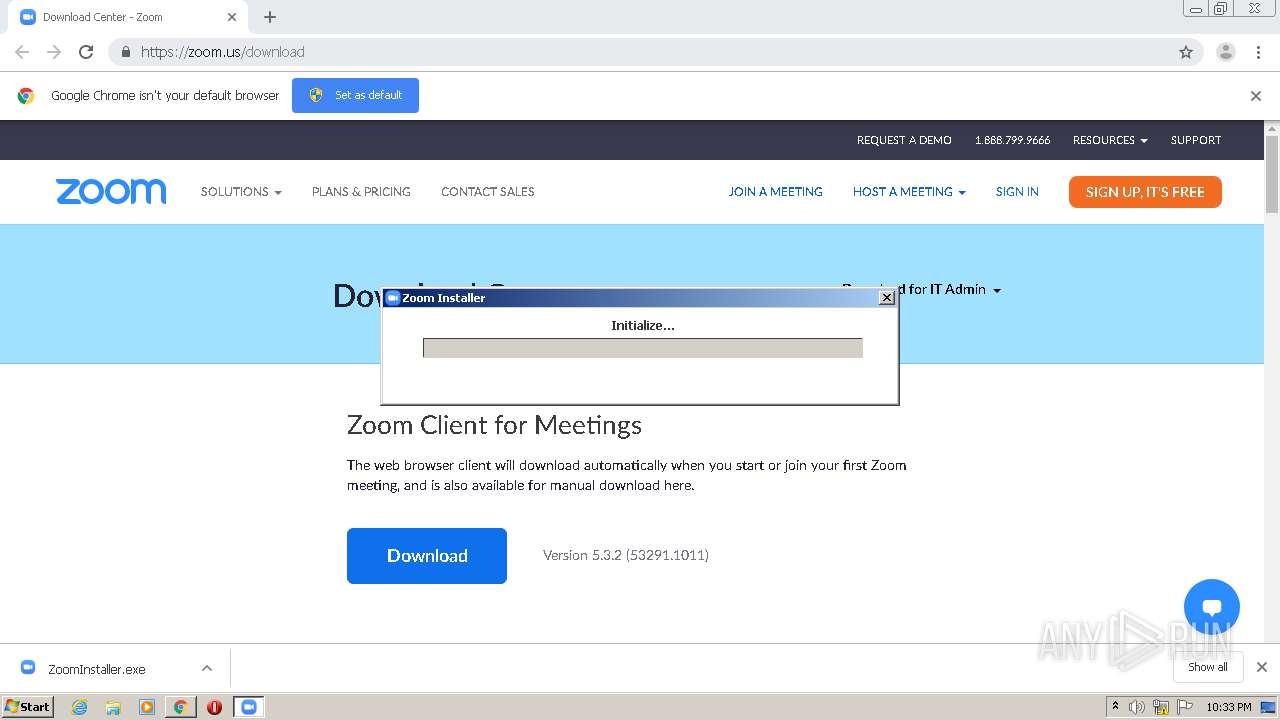
Application was dropped or rewritten from another process
- Installer.exe (PID: 3748)
- ZoomInstaller.exe (PID: 3412)
- Installer.exe (PID: 3892)
- ZoomInstaller.exe (PID: 1144)
- Zoom.exe (PID: 1696)
- Zoom.exe (PID: 3392)
- Installer.exe (PID: 2016)
- Zoom.exe (PID: 1176)
- Zoom.exe (PID: 2936)
Loads dropped or rewritten executable
- Zoom.exe (PID: 1696)
- Installer.exe (PID: 3748)
- Zoom.exe (PID: 3392)
- Zoom.exe (PID: 2936)
- Zoom.exe (PID: 1176)
- Installer.exe (PID: 2016)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3968)
- chrome.exe (PID: 2556)
- ZoomInstaller.exe (PID: 3412)
- Installer.exe (PID: 3748)
- ZoomInstaller.exe (PID: 1144)
- Installer.exe (PID: 2016)
Application launched itself
- Installer.exe (PID: 3748)
- Zoom.exe (PID: 1696)
- Zoom.exe (PID: 1176)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 3748)
- Installer.exe (PID: 2016)
Modifies the open verb of a shell class
- Installer.exe (PID: 3748)
- Installer.exe (PID: 2016)
Creates a software uninstall entry
- Installer.exe (PID: 3748)
- Installer.exe (PID: 2016)
Creates files in the user directory
- Zoom.exe (PID: 1696)
- Installer.exe (PID: 3748)
- Zoom.exe (PID: 3392)
- Zoom.exe (PID: 1176)
- Zoom.exe (PID: 2936)
- Installer.exe (PID: 2016)
INFO
Application launched itself
- chrome.exe (PID: 2556)
Reads the hosts file
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3968)
Reads Internet Cache Settings
- chrome.exe (PID: 2556)
Reads settings of System Certificates
- Installer.exe (PID: 3748)
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 3748)
- Installer.exe (PID: 2016)
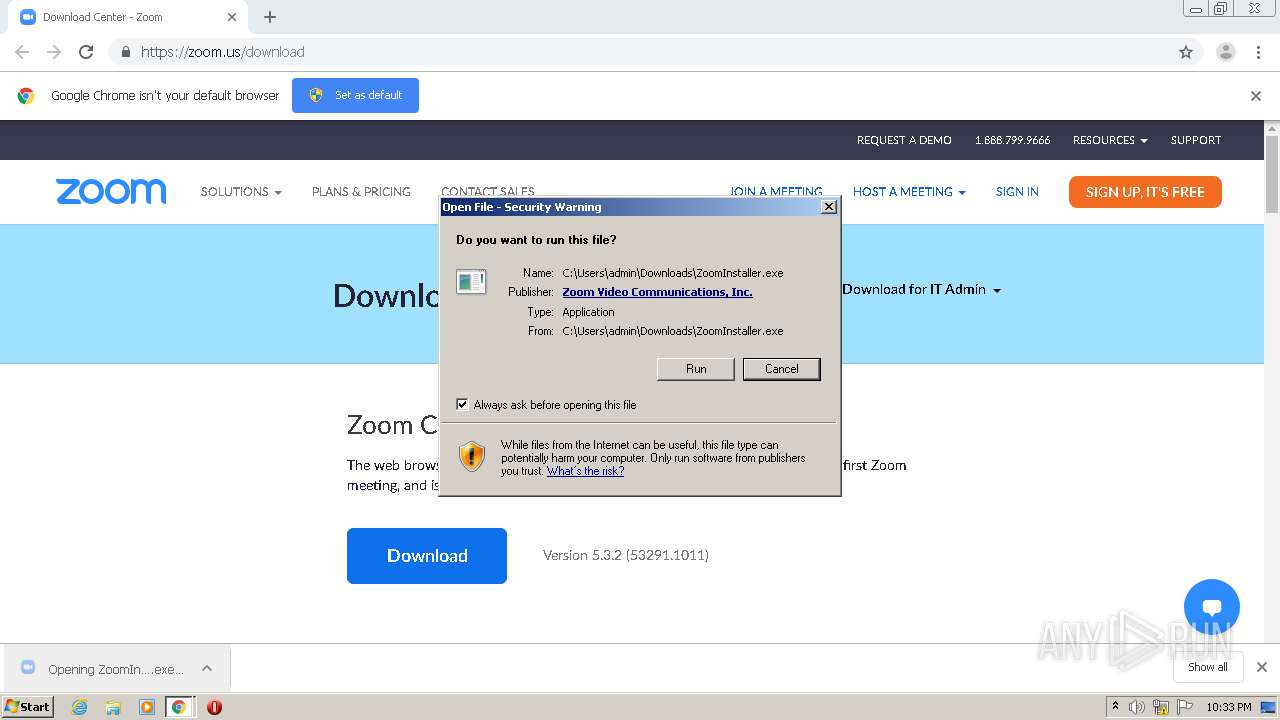
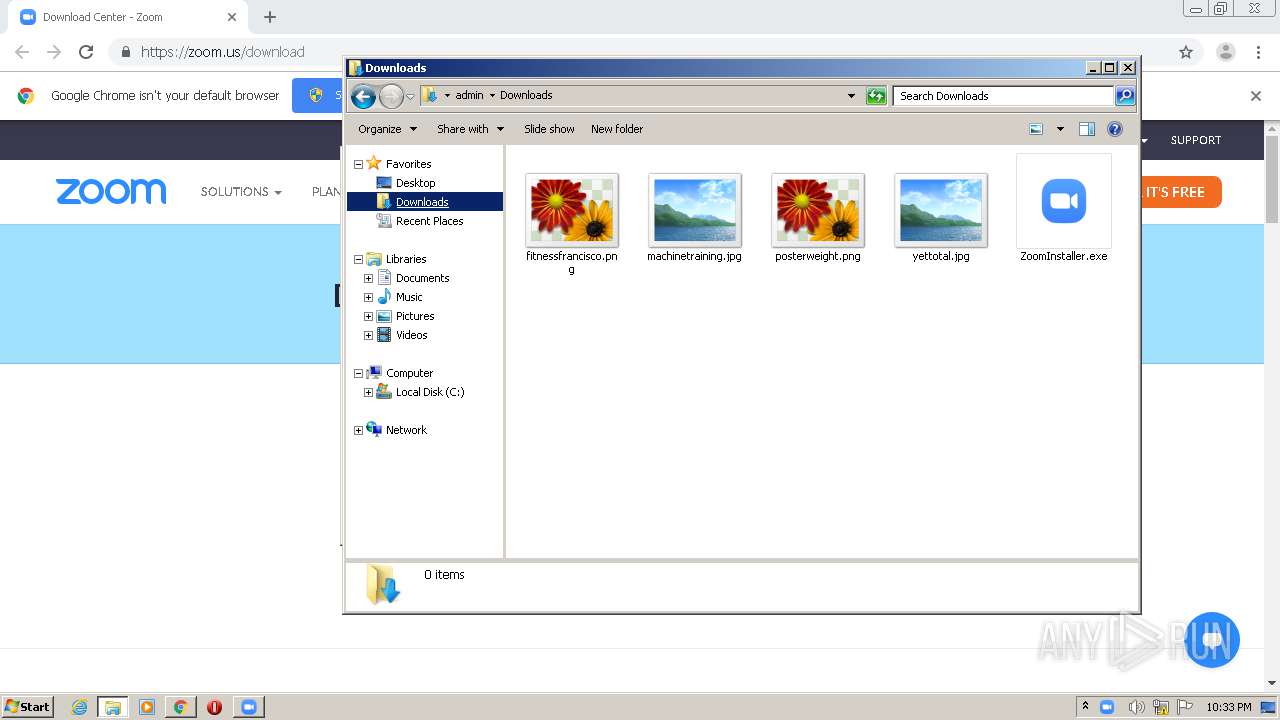
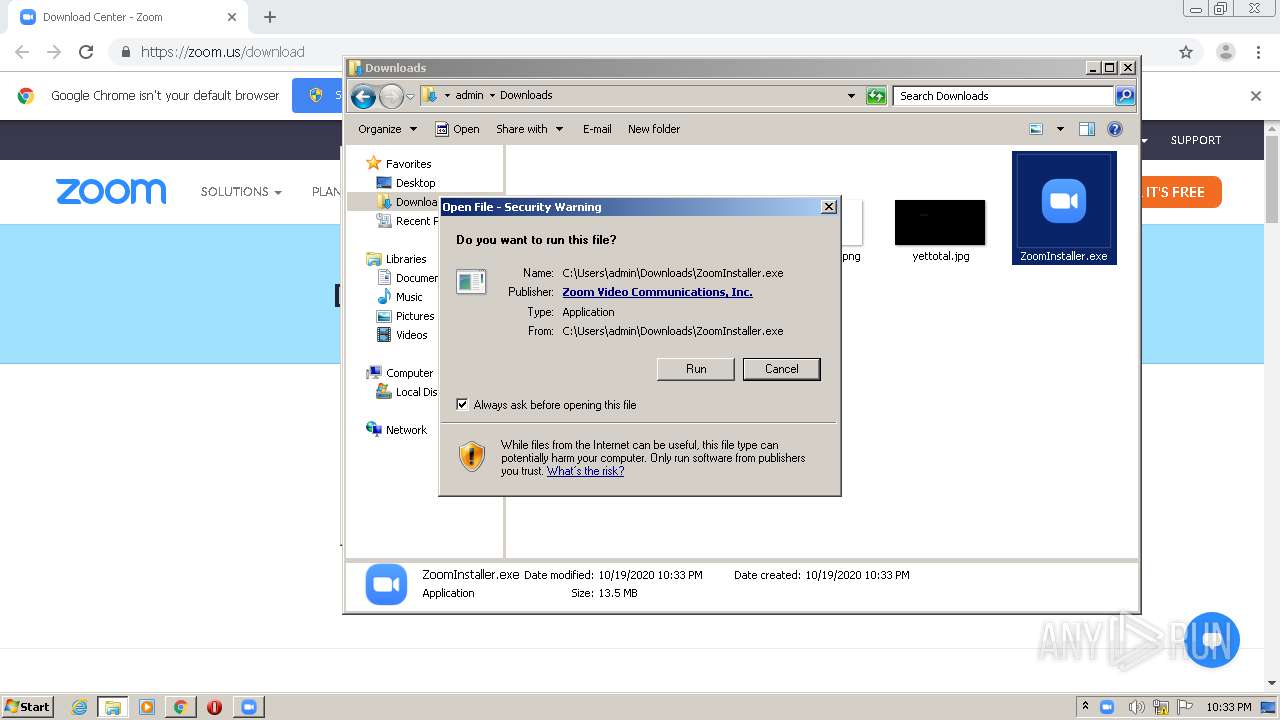
Manual execution by user
- explorer.exe (PID: 1452)
- ZoomInstaller.exe (PID: 1144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
30
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,3045288960570123851,14546346525780450085,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=871326673302105049 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3045288960570123851,14546346525780450085,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5465830014337574867 --mojo-platform-channel-handle=3804 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3045288960570123851,14546346525780450085,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13325774096328701871 --mojo-platform-channel-handle=3856 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2544 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
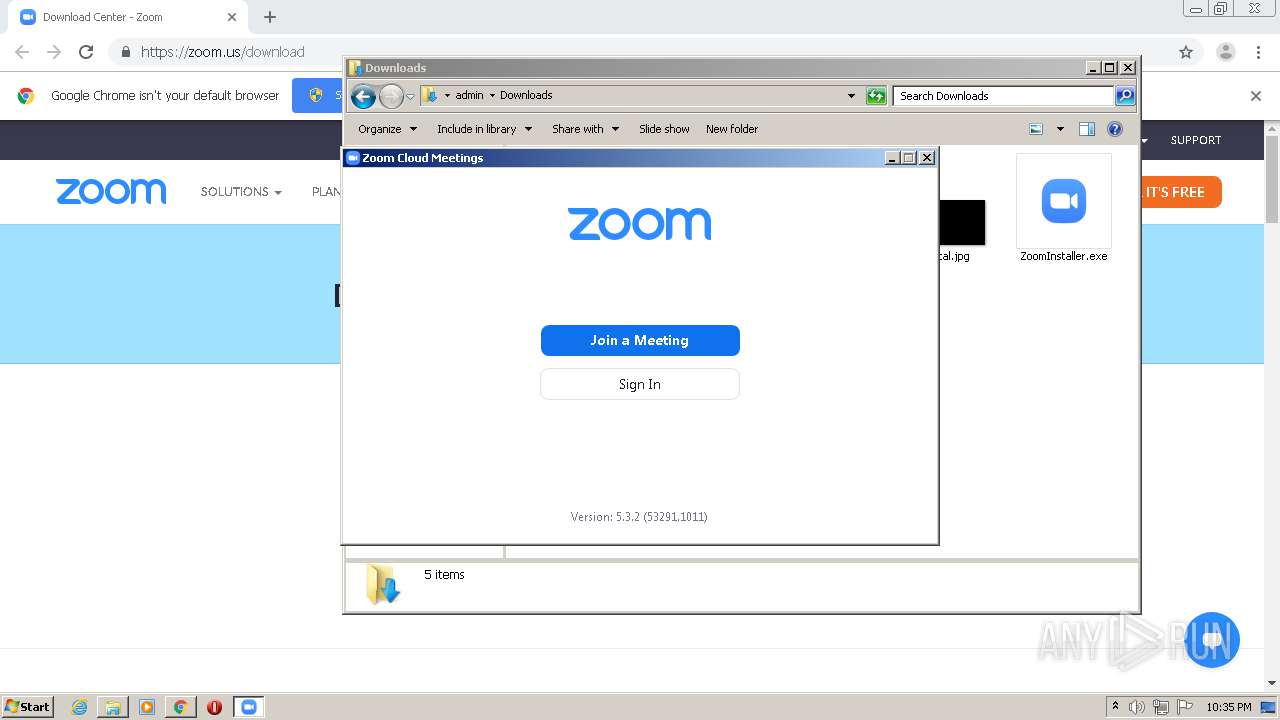
| 1144 | "C:\Users\admin\Downloads\ZoomInstaller.exe" | C:\Users\admin\Downloads\ZoomInstaller.exe | explorer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Installer Exit code: 0 Version: 5,2,0,0 Modules
| |||||||||||||||
| 1176 | "C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe" C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Installer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 5,3,53291,1011 Modules
| |||||||||||||||
| 1452 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3045288960570123851,14546346525780450085,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15045196566979566302 --mojo-platform-channel-handle=496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe" C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Installer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 5,3,53291,1011 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3045288960570123851,14546346525780450085,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2704161113079825001 --mojo-platform-channel-handle=1100 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 843
Read events
2 534
Write events
280
Delete events
29
Modification events
| (PID) Process: | (984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2556-13247616774173000 |
Value: 259 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2556-13247616774173000 |
Value: 259 | |||
Executable files
305
Suspicious files
73
Text files
106
Unknown types
8
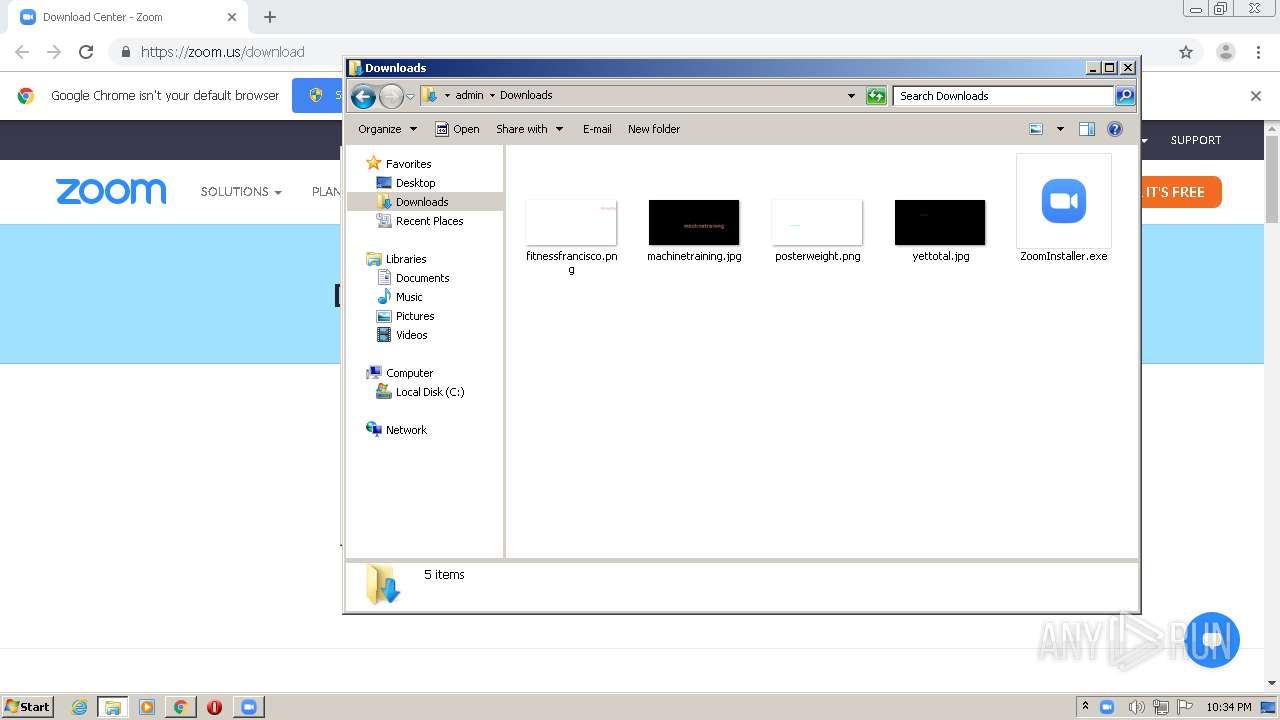
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E0606-9FC.pma | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fb901af2-2558-4f11-a27a-80e9442b8392.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2d41f0.TMP | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF2d41f0.TMP | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d4124.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
35
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 52.202.62.233:443 | zoom.us | Amazon.com, Inc. | US | unknown |
3968 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 13.35.253.6:443 | d24cgw3uvb9a9h.cloudfront.net | — | US | suspicious |
3968 | chrome.exe | 99.86.7.4:443 | static.ada.support | AT&T Services, Inc. | US | malicious |
3968 | chrome.exe | 99.86.7.88:443 | zoom.ada.support | AT&T Services, Inc. | US | unknown |
3968 | chrome.exe | 99.86.7.5:443 | d11yldzmag5yn.cloudfront.net | AT&T Services, Inc. | US | suspicious |
— | — | 99.86.7.34:443 | static.ada.support | AT&T Services, Inc. | US | suspicious |
1696 | Zoom.exe | 52.202.62.233:443 | zoom.us | Amazon.com, Inc. | US | unknown |
1696 | Zoom.exe | 198.251.234.30:3478 | — | InnSys Incorporated | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zoom.us |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
d24cgw3uvb9a9h.cloudfront.net |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
static.ada.support |
| whitelisted |
rollout.ada.support |
| shared |
zoom.ada.support |
| whitelisted |
d11yldzmag5yn.cloudfront.net |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\uninstall |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\bin |
Installer.exe | |
Installer.exe | [CZoomProductPathHelper::RecursiveRemoveDirA] Path is: |