| File name: | Get-NetAdapterVmq.ps1 |
| Full analysis: | https://app.any.run/tasks/987ed72f-8b50-4c6c-99fb-741016e14bf5 |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2023, 06:10:36 |
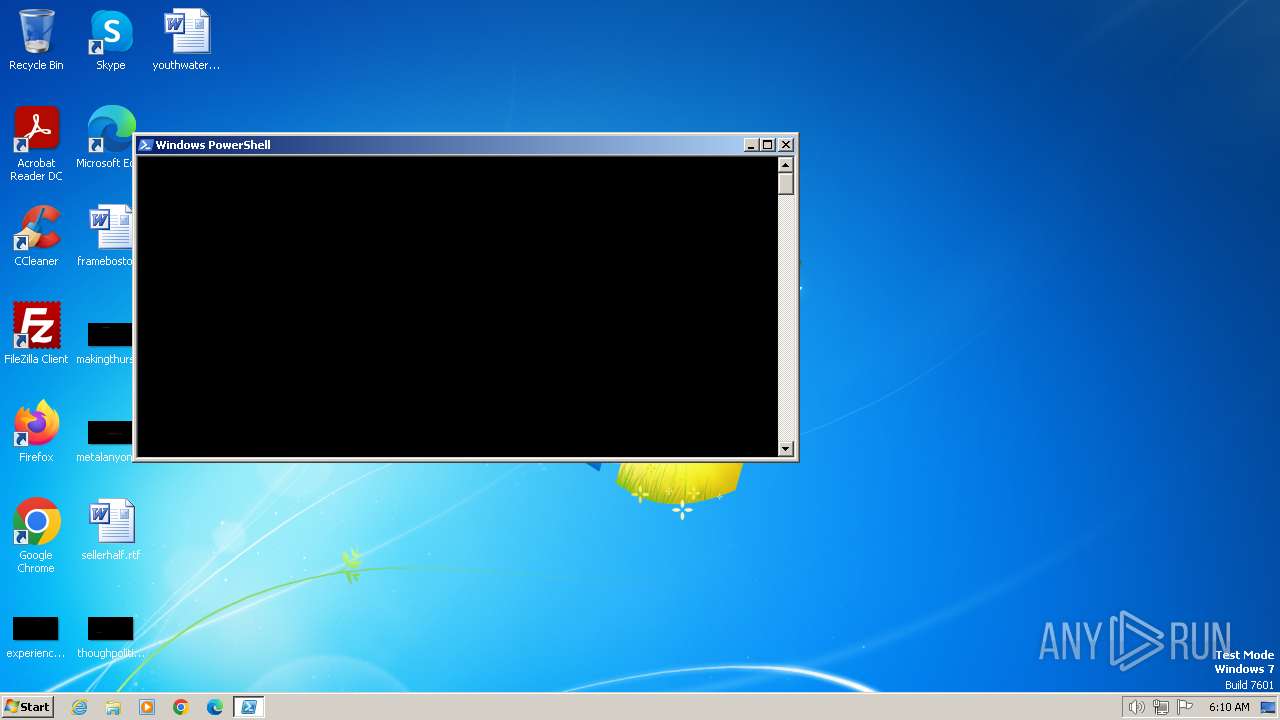
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | 42F04BFE695CF78438B7B2E2A5516B3C |
| SHA1: | 78FD853C07AE237A0BC5A5E6F6E2927EA066F55E |
| SHA256: | 0F7F8FC74E711251B7110E93DE717D4E075E2D55A807F8D80D2FCEC2CF9FB582 |
| SSDEEP: | 6144:eyzYp1YMobdrBn3iCvHjTeShhZAMuq/Et8kMJzHVLkSiAuACmEqunz:/nl8Xq5fMz |
MALICIOUS
Starts Visual C# compiler
- powershell.exe (PID: 2124)
Drops the executable file immediately after the start
- csc.exe (PID: 2072)
SUSPICIOUS
Reads the Internet Settings
- powershell.exe (PID: 2124)
Uses .NET C# to load dll
- powershell.exe (PID: 2124)
The Powershell connects to the Internet
- powershell.exe (PID: 2124)
Connects to unusual port
- powershell.exe (PID: 2124)
Unusual connection from system programs
- powershell.exe (PID: 2124)
INFO
Checks supported languages
- csc.exe (PID: 2072)
- cvtres.exe (PID: 2080)
Reads the machine GUID from the registry
- csc.exe (PID: 2072)
- cvtres.exe (PID: 2080)
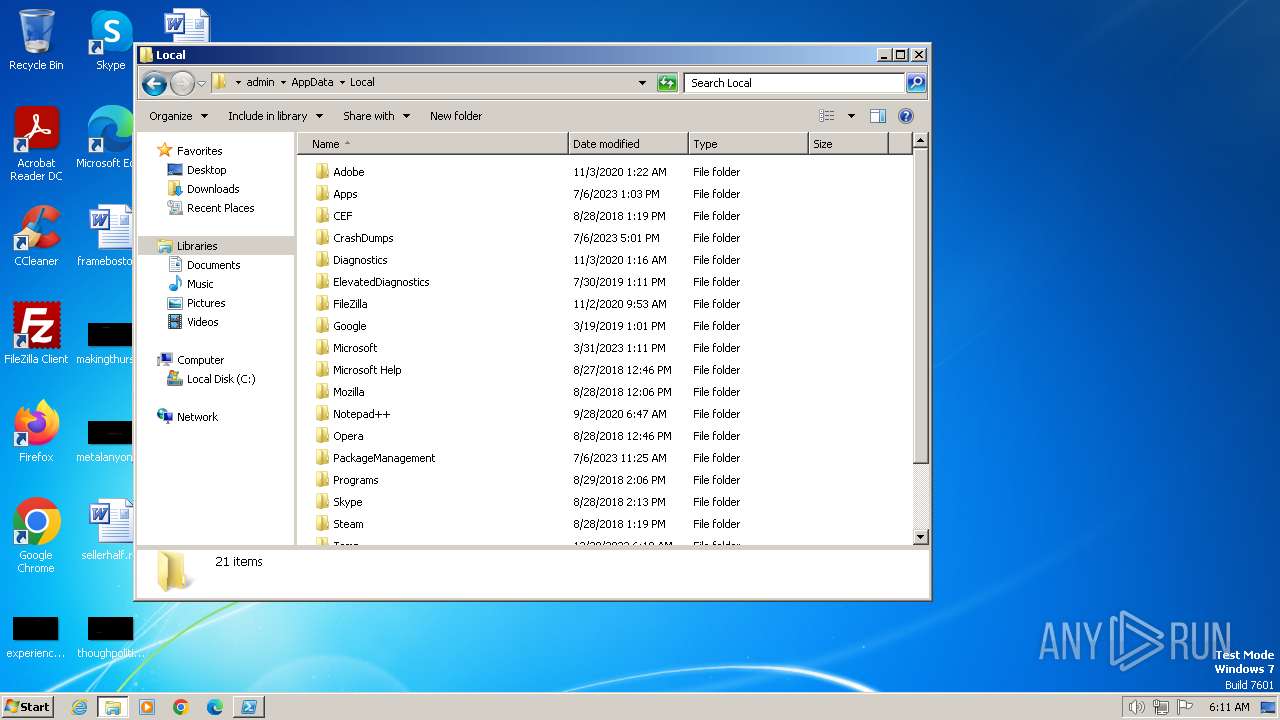
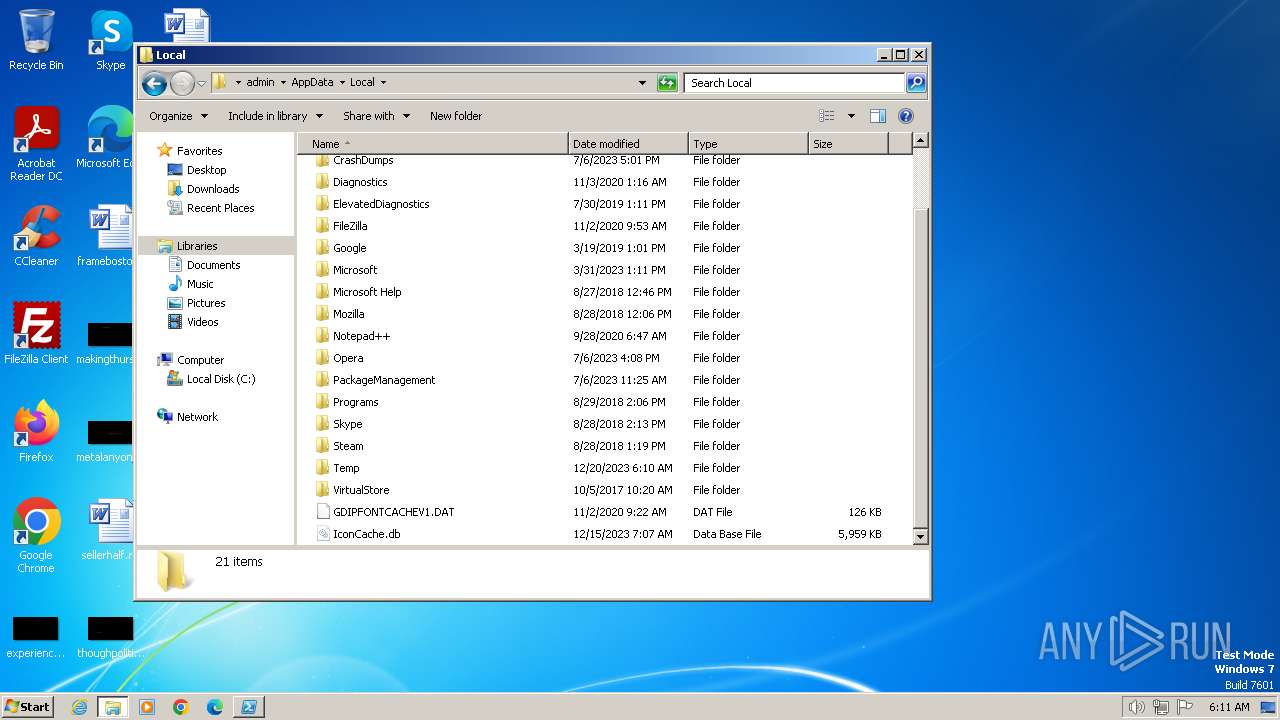
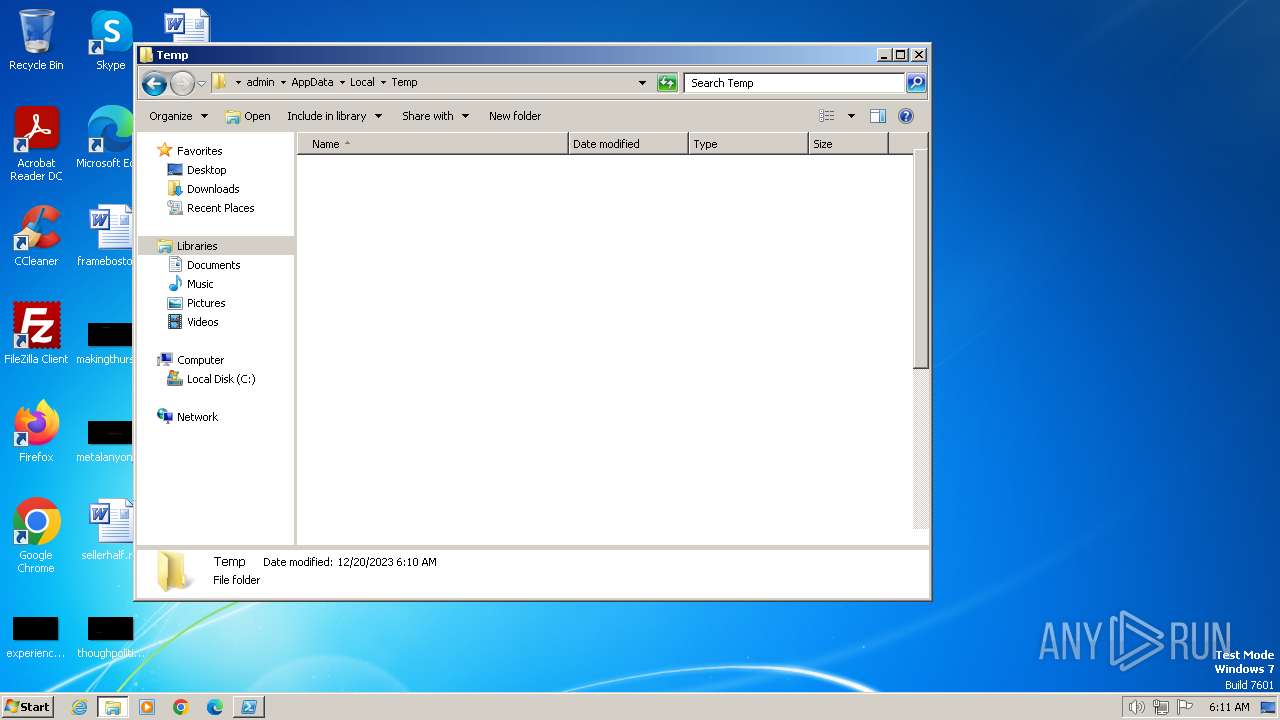
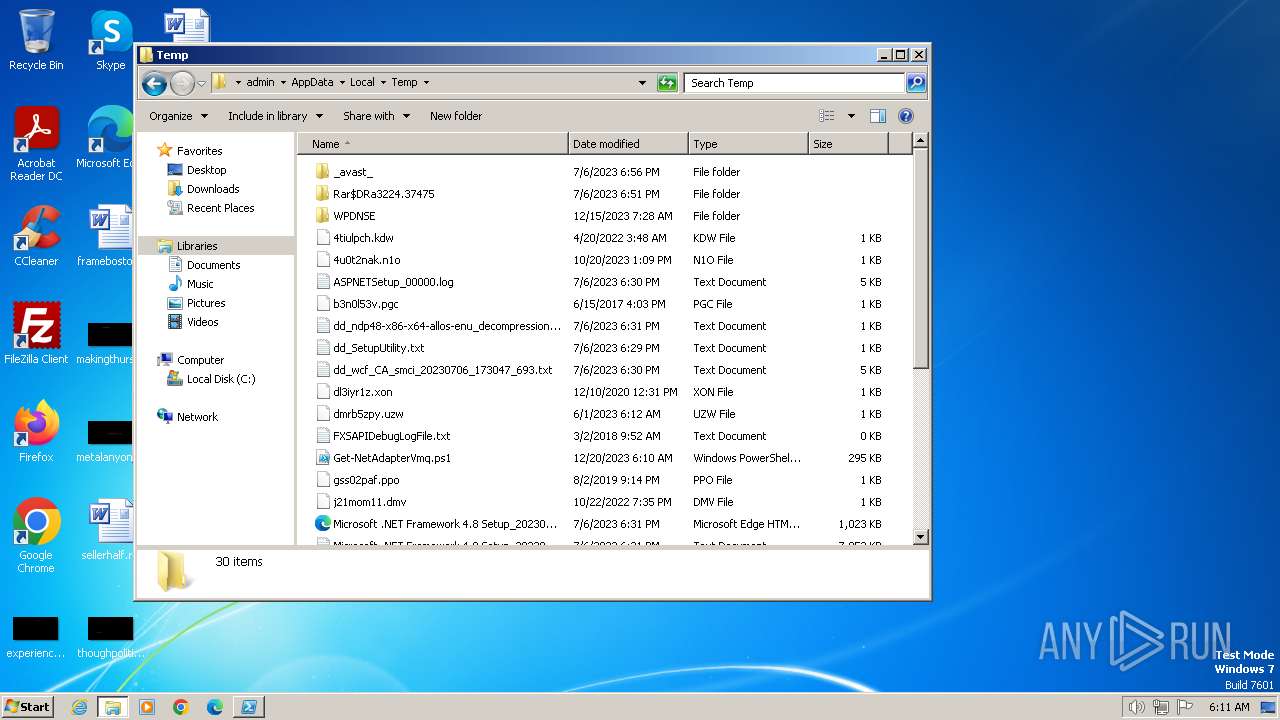
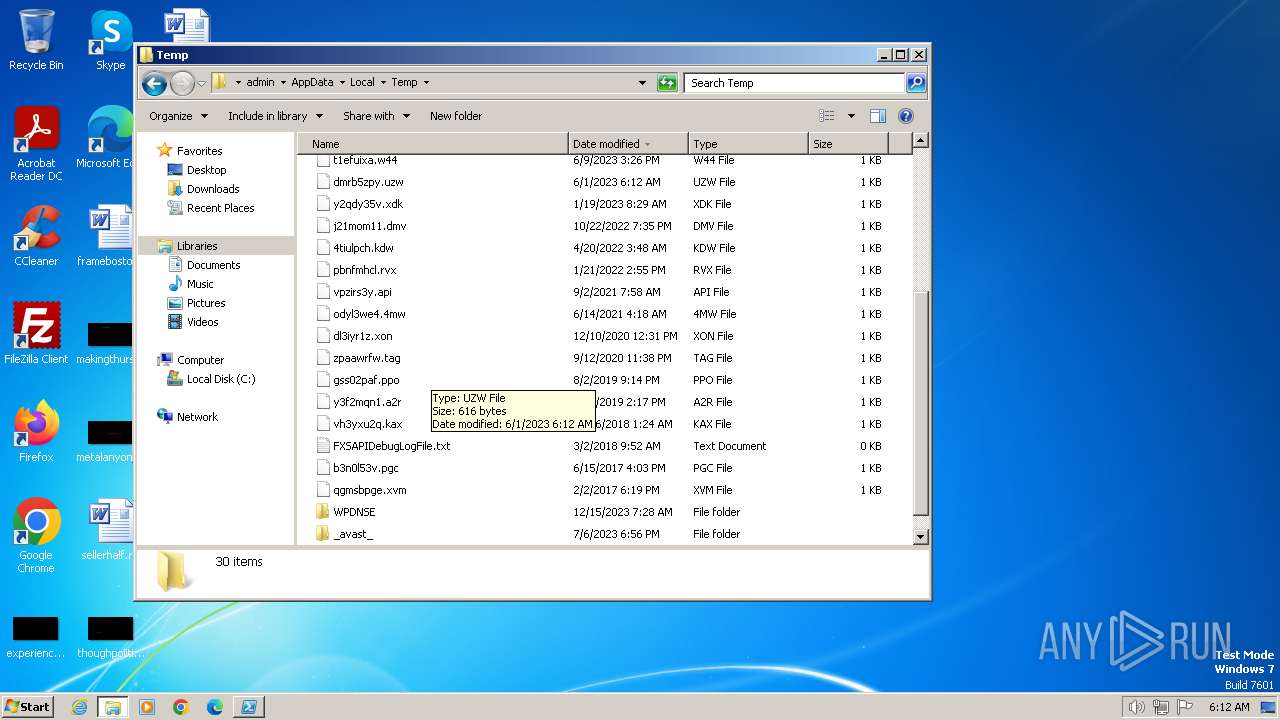
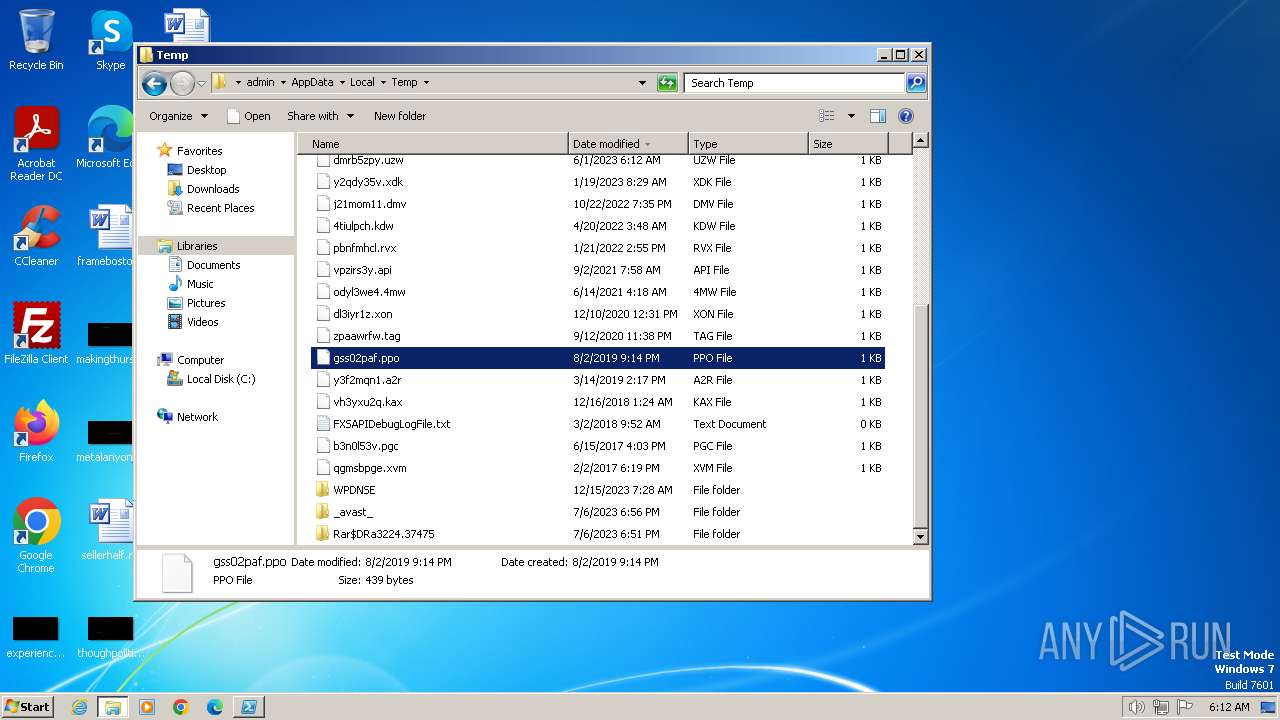
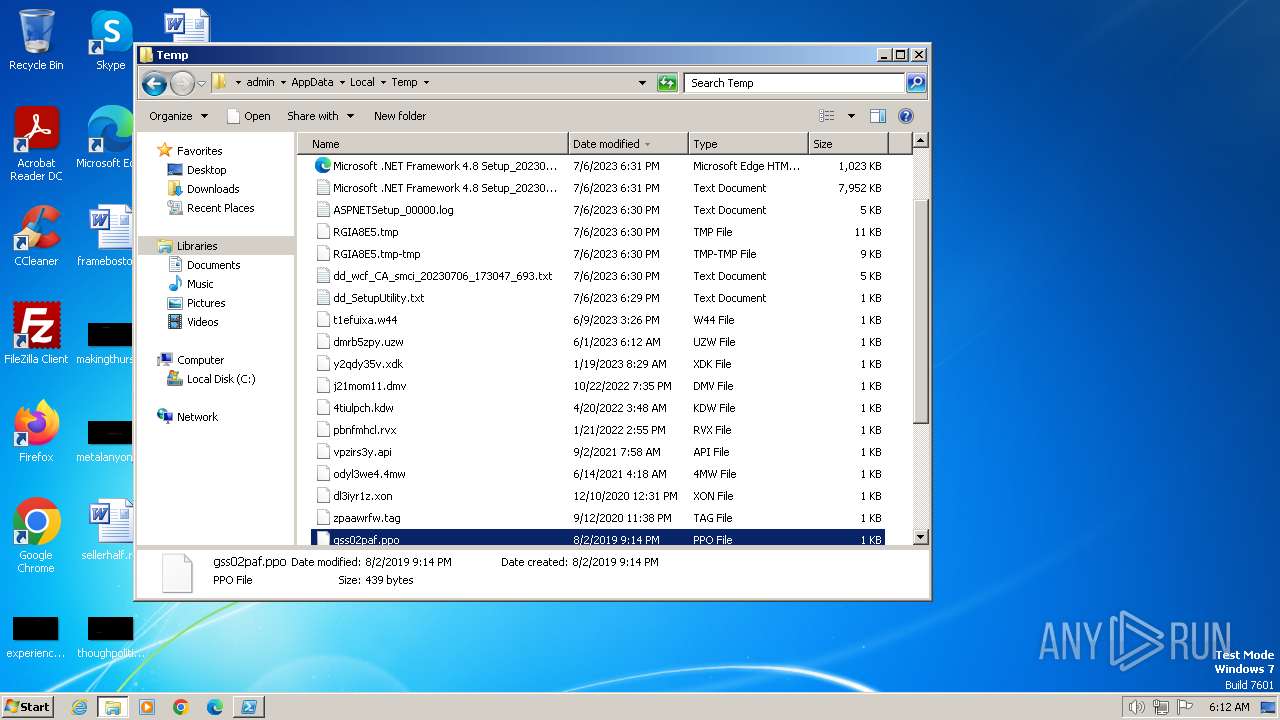
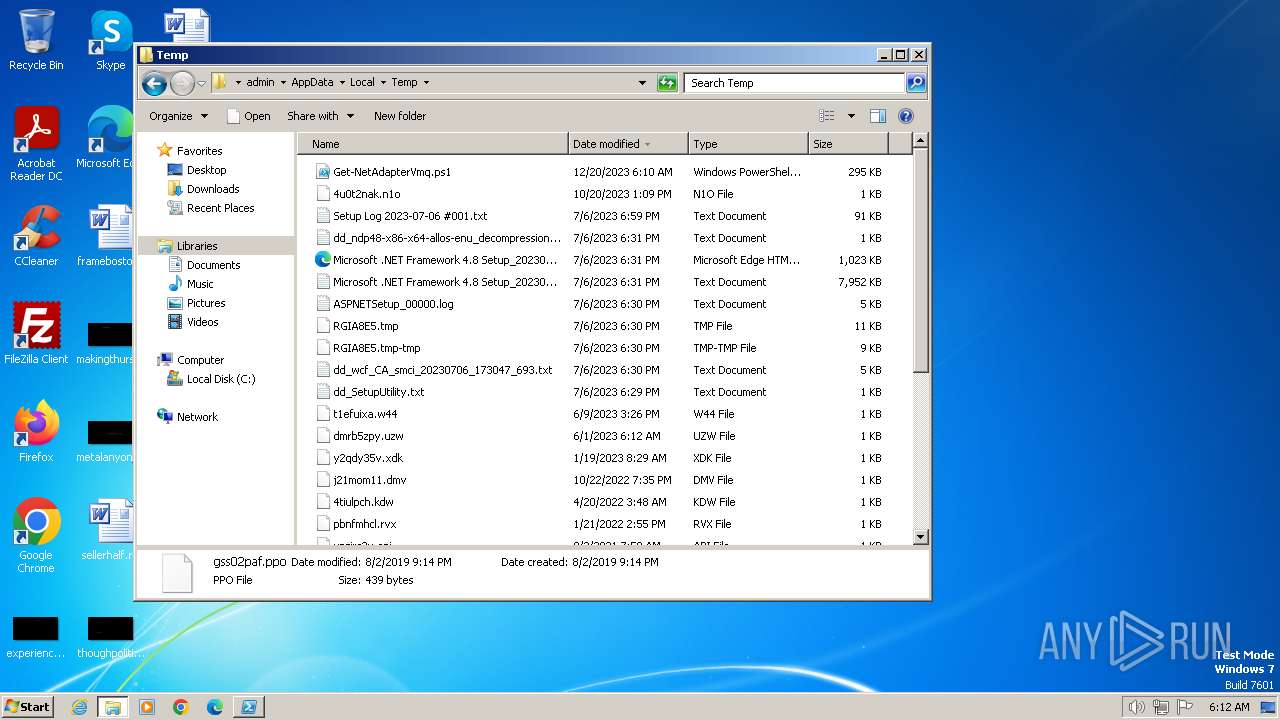
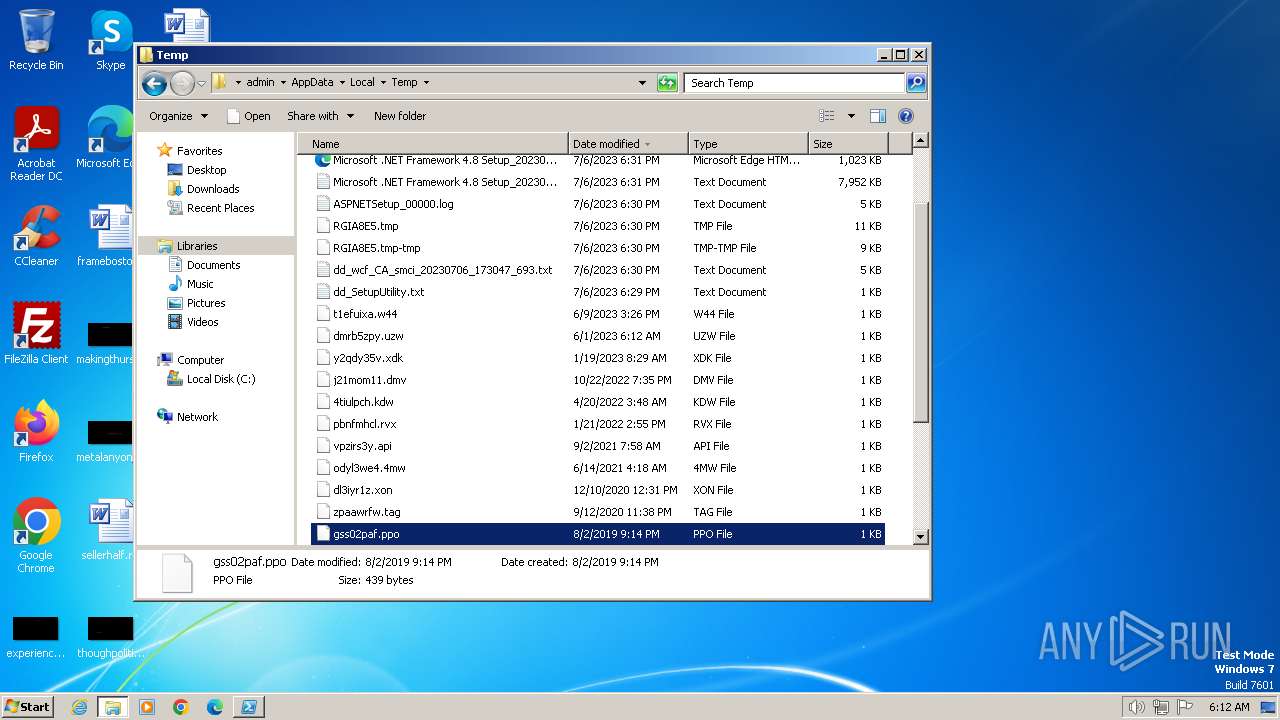
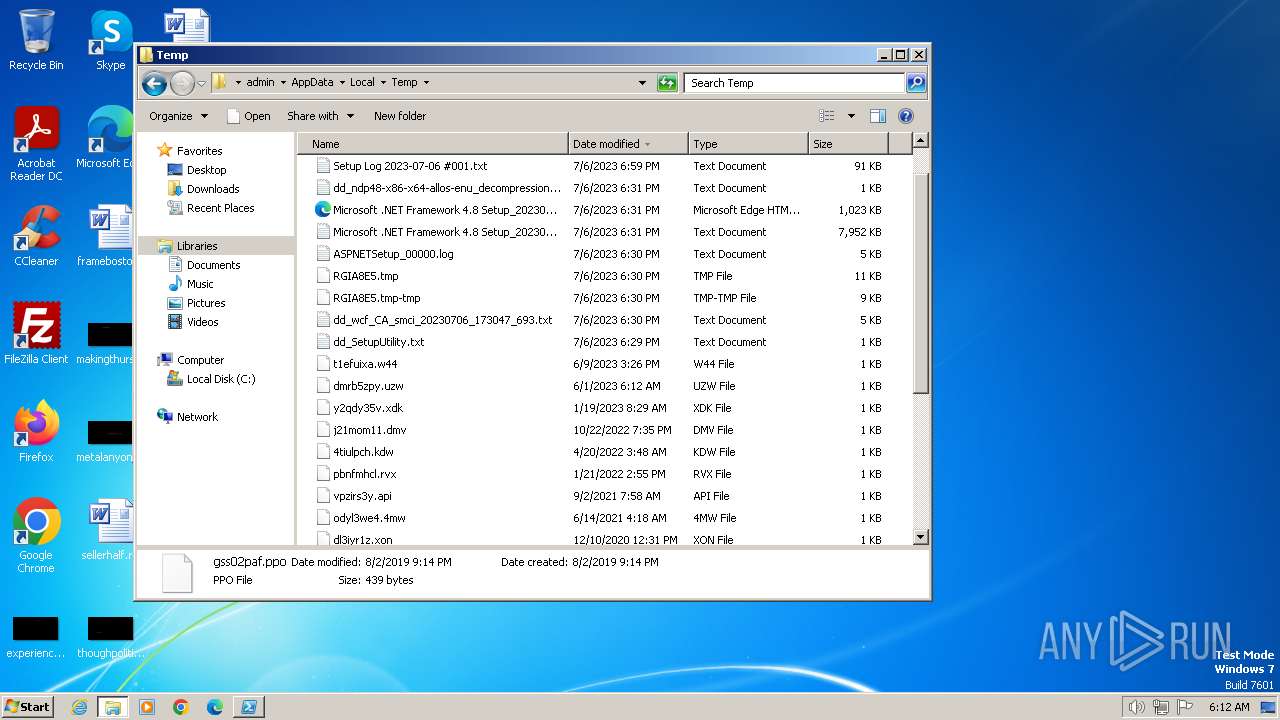
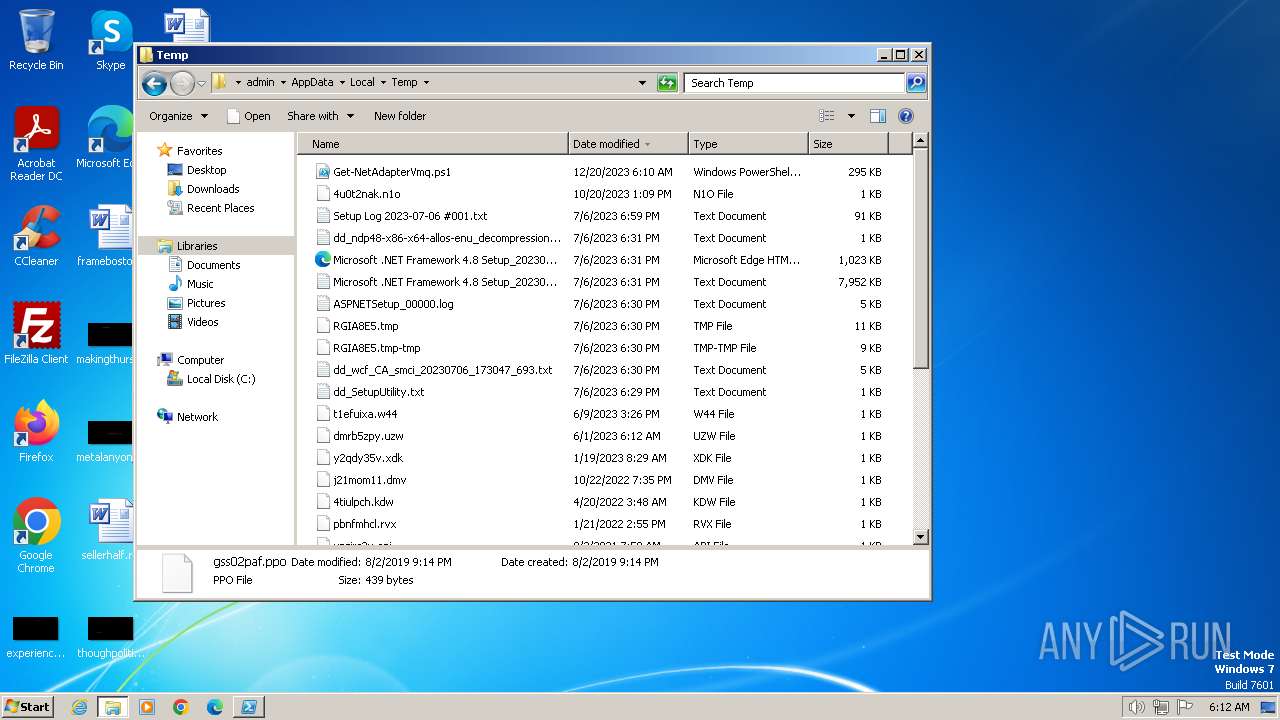
Create files in a temporary directory
- csc.exe (PID: 2072)
- cvtres.exe (PID: 2080)
Manual execution by a user
- explorer.exe (PID: 548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ux5xfbjm.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 2080 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES599.tmp" "c:\Users\admin\AppData\Local\Temp\CSC30D66F0E38E84CDBBFF7AB11F25499D4.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 2124 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\Get-NetAdapterVmq.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
2 824
Read events
2 762
Write events
62
Delete events
0
Modification events
| (PID) Process: | (2124) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2124) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2124) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2124) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2124) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
8
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:F500255BDC0DD45A0934243E38529D10 | SHA256:AD4304402753CEF71770C63692428001309617BDA00D87E229D197721D29496E | |||
| 2124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ct1unibb.rje.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BWMN4EBNIE8WHJZDKJ0S.temp | binary | |
MD5:F500255BDC0DD45A0934243E38529D10 | SHA256:AD4304402753CEF71770C63692428001309617BDA00D87E229D197721D29496E | |||
| 2124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFdf463.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 2124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\odnmgnfb.p4j.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2124 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 2124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ux5xfbjm.cmdline | text | |
MD5:48286DF183DF22BEBD8B78A788496957 | SHA256:F8D7F053EB8FC93112DF1EBEB5EFE4A0FD7FD12681A77A37E793DE18CE226F81 | |||
| 2072 | csc.exe | C:\Users\admin\AppData\Local\Temp\ux5xfbjm.dll | executable | |
MD5:C3F7A7F220874E312C30D137390EB545 | SHA256:578B7D6BE9573F1633BDA5BE5015B43DDD1F8BF0A0FD82D5636823440974745F | |||
| 2080 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES599.tmp | binary | |
MD5:4208E7979C4DA1CF6C97744548D422C7 | SHA256:3F6E5EE327AF45C9EAFBF28FD5884CBEC452CD4845B570ECAD2018A4F11FEACA | |||
| 2072 | csc.exe | C:\Users\admin\AppData\Local\Temp\ux5xfbjm.out | text | |
MD5:A2A8A8AC3D890EB412A934B0968EEA85 | SHA256:57F1F5F05A84CEACA89577010F400FE9ED9112F326407004F595B455E4019ABA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
8
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2124 | powershell.exe | 49.13.77.253:14235 | cuf4hw1umerulqy.top | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cuf4hw1umerulqy.top |
| unknown |
dns.msftncsi.com |
| shared |
cuf4hw1umerulqy.fun |
| unknown |
cuf4hw1umerulqy.com |
| unknown |
cuf4hw1umerulqy.cn |
| unknown |
8n7ueitwixjnyot.top |
| unknown |
8n7ueitwixjnyot.fun |
| unknown |
8n7ueitwixjnyot.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |