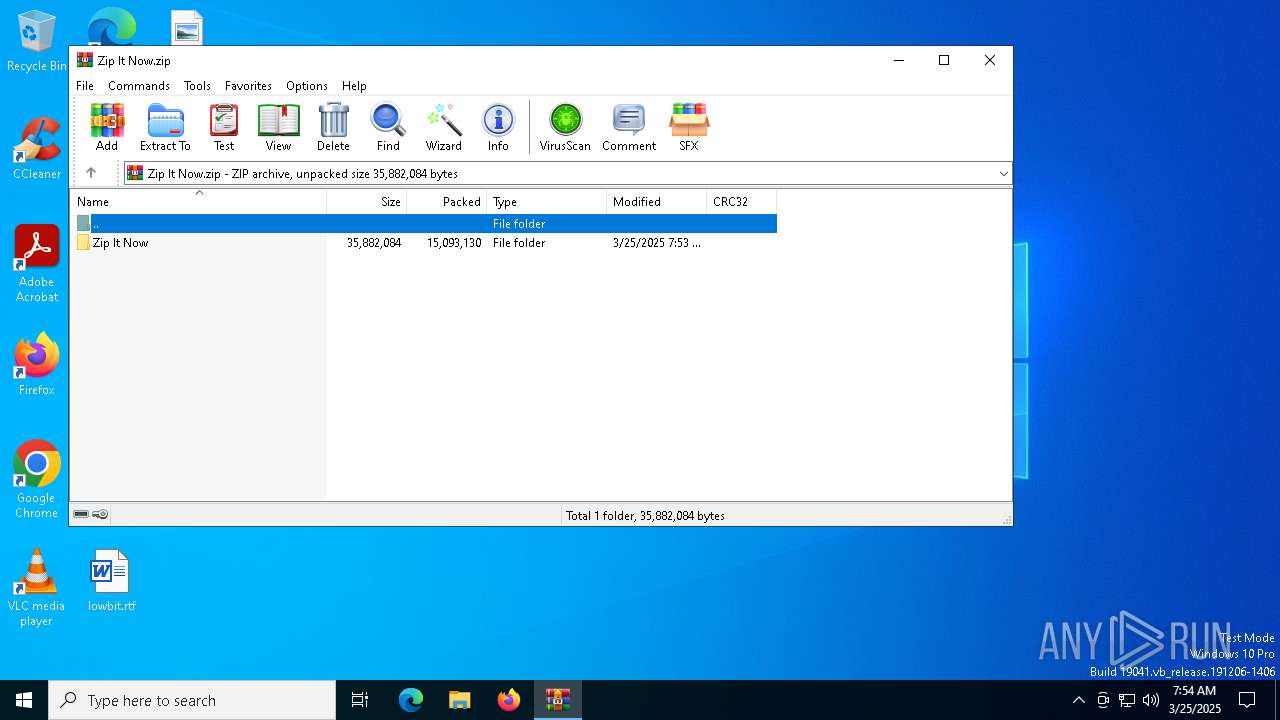
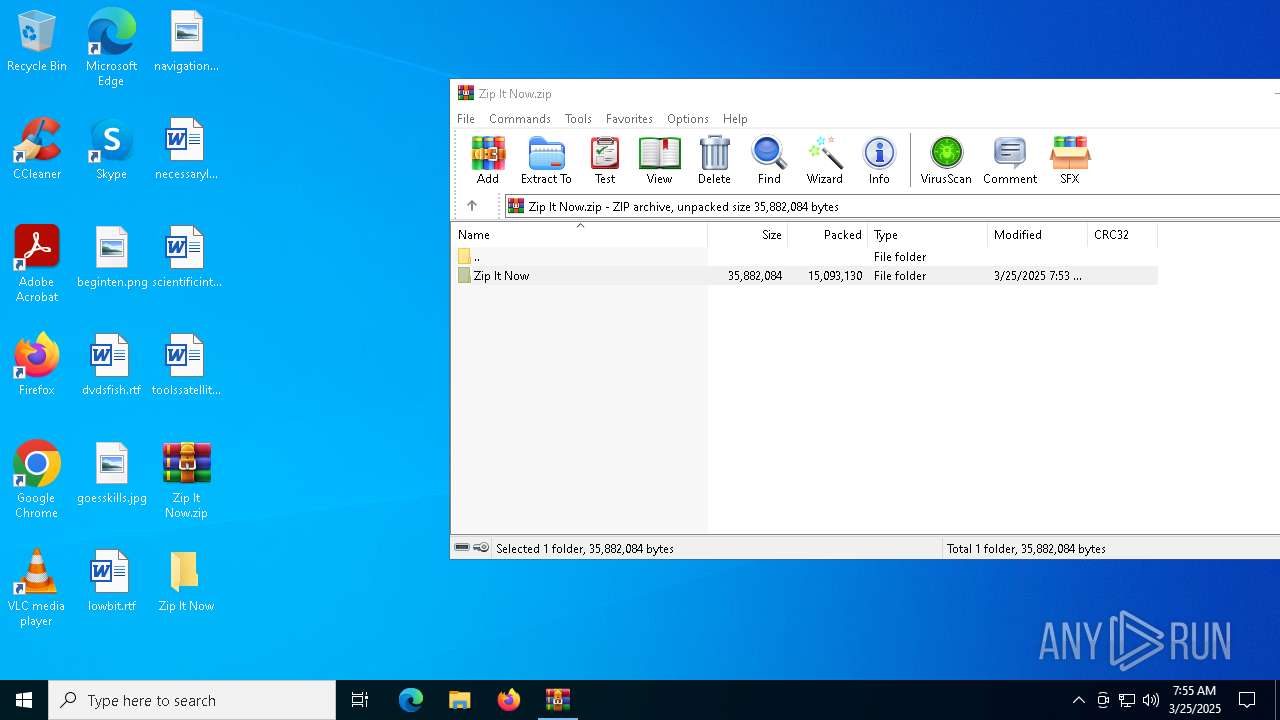
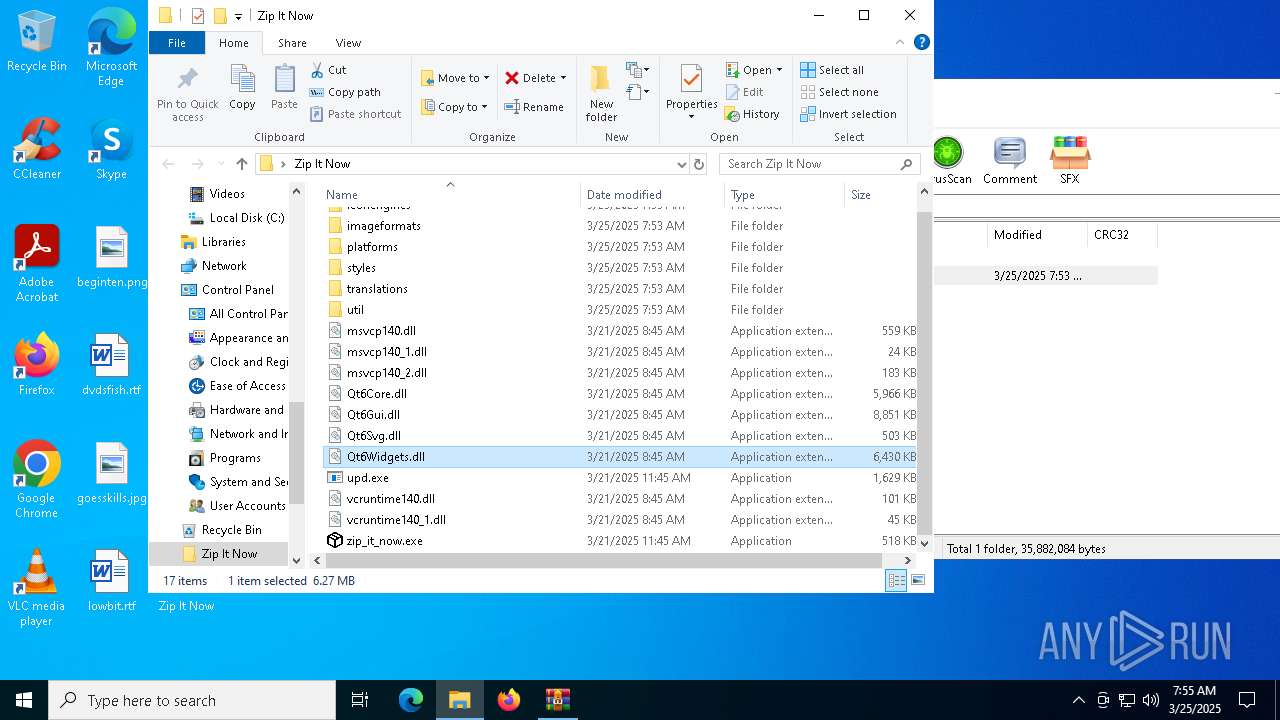
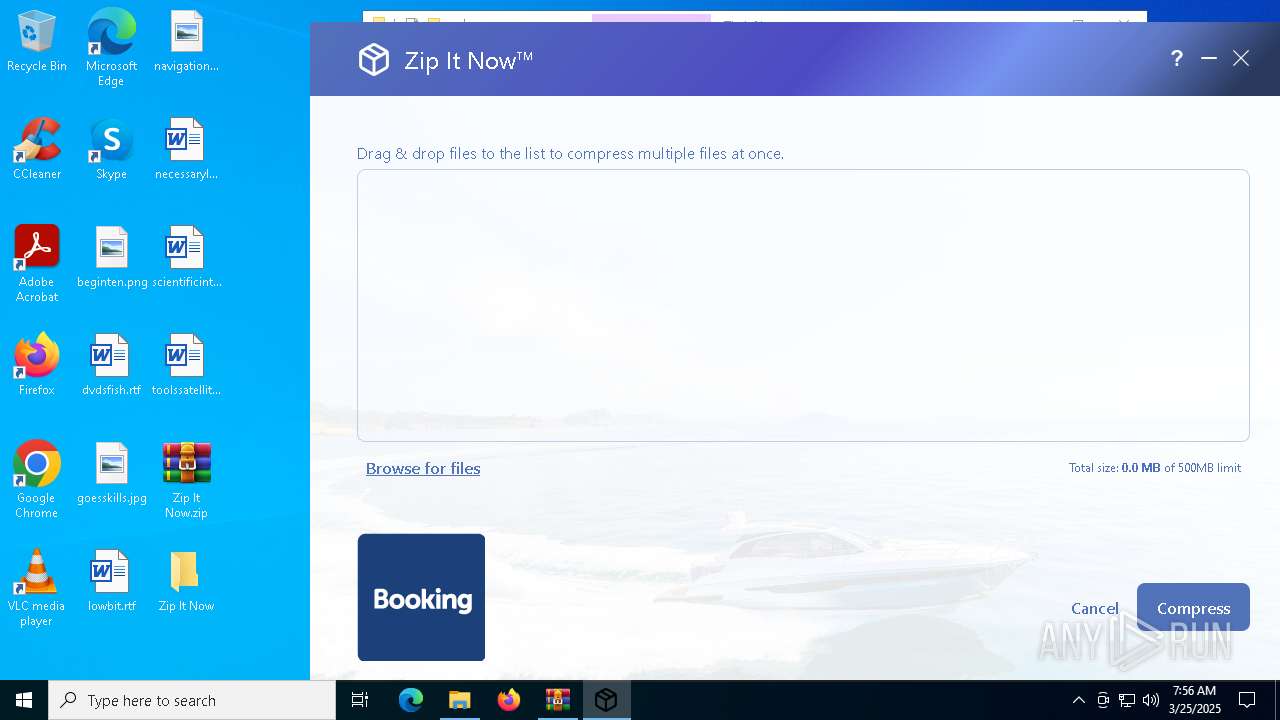
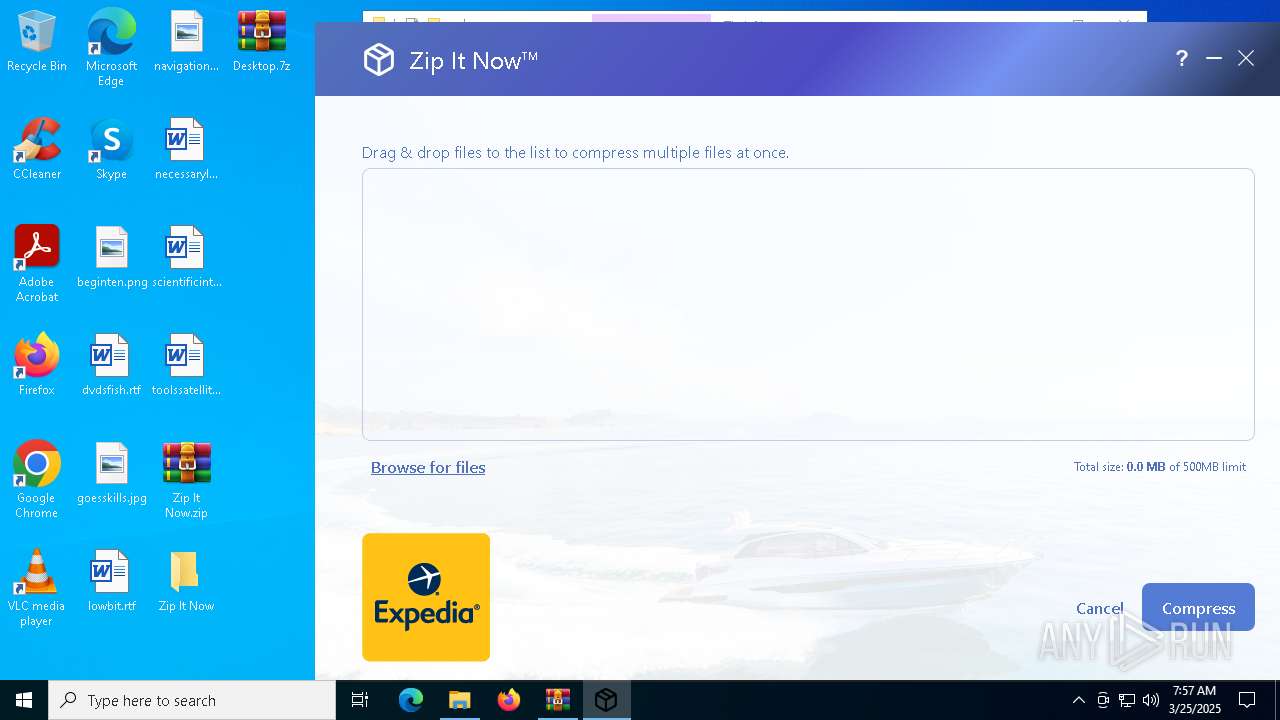
| File name: | Zip It Now.zip |
| Full analysis: | https://app.any.run/tasks/1e1d5098-b685-43b7-8b0a-12f00fa87f06 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 07:54:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | F1814C9242E45CA391A35DEEA116464A |
| SHA1: | BE869FA587E2708E7E24403906919BFCBBCFFA2A |
| SHA256: | 0F66418DC258DC10CA92EF9B6BA8CBE269383765A89E81FE0C801FC2554F7EFB |
| SSDEEP: | 196608:uDkbGt8rYcgU/74XrcWCY2z8VJA2lmorY:uDkbGtHU/74XgWq6AOG |
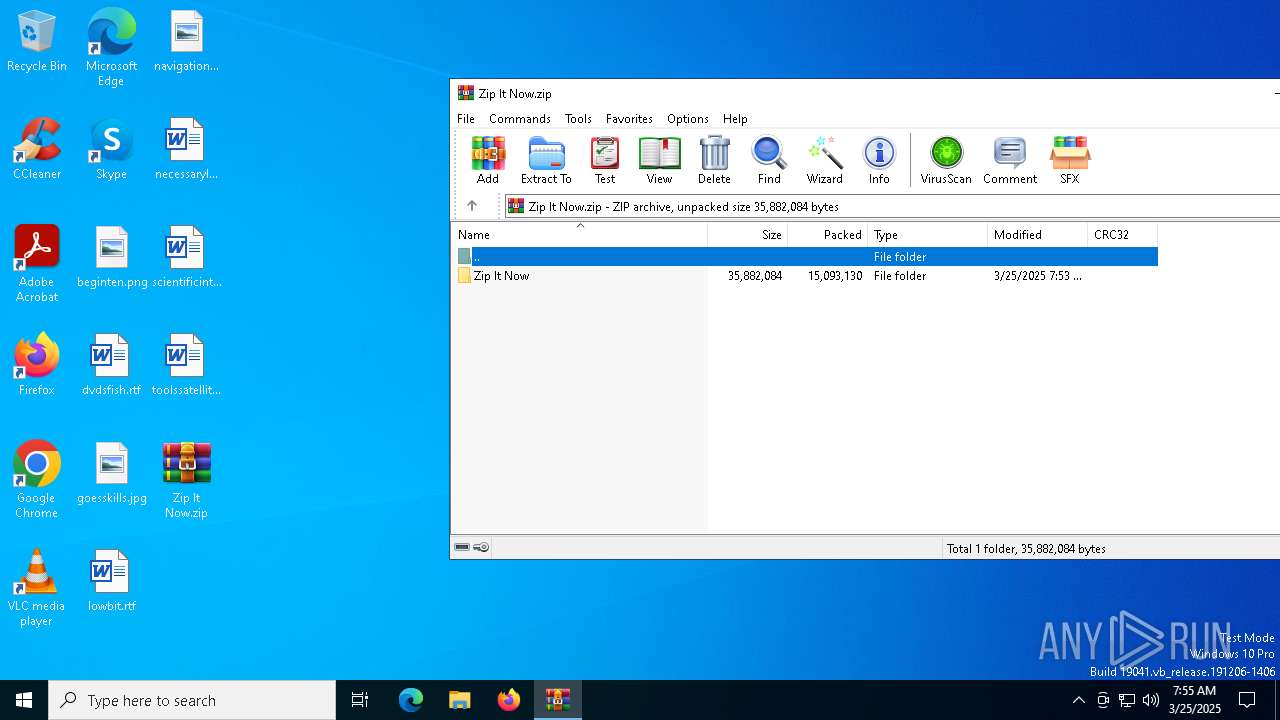
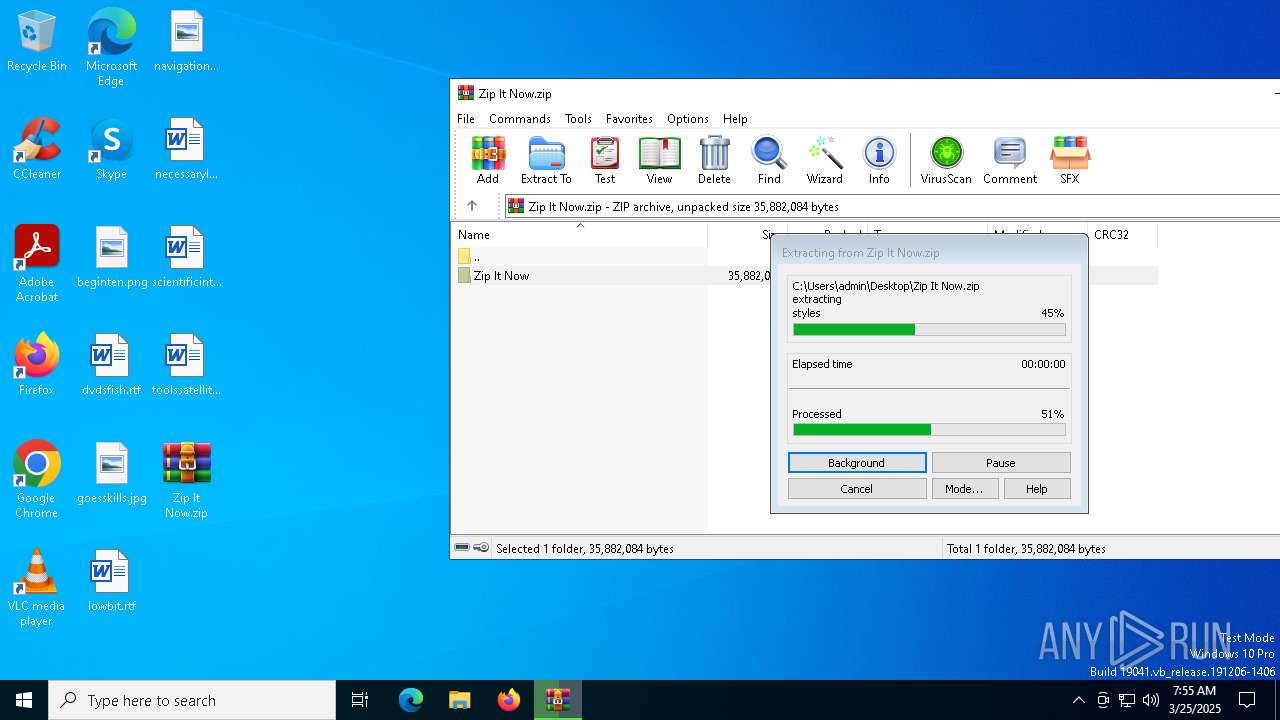
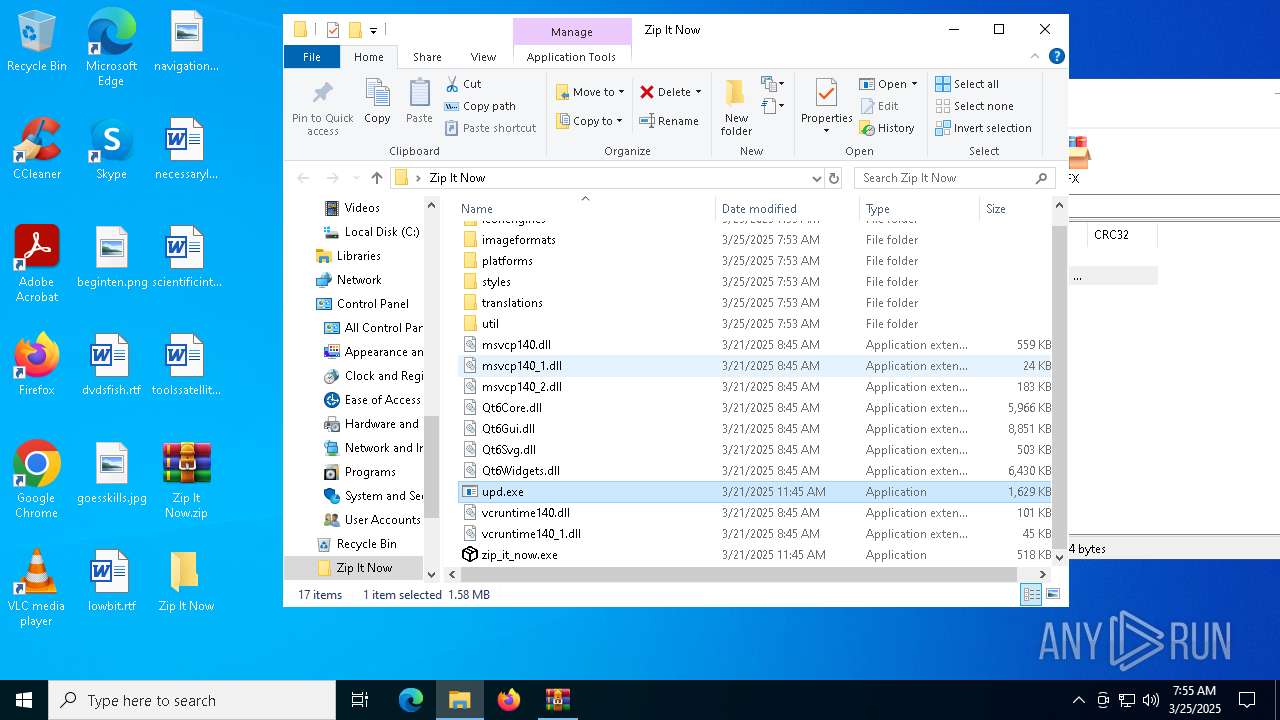
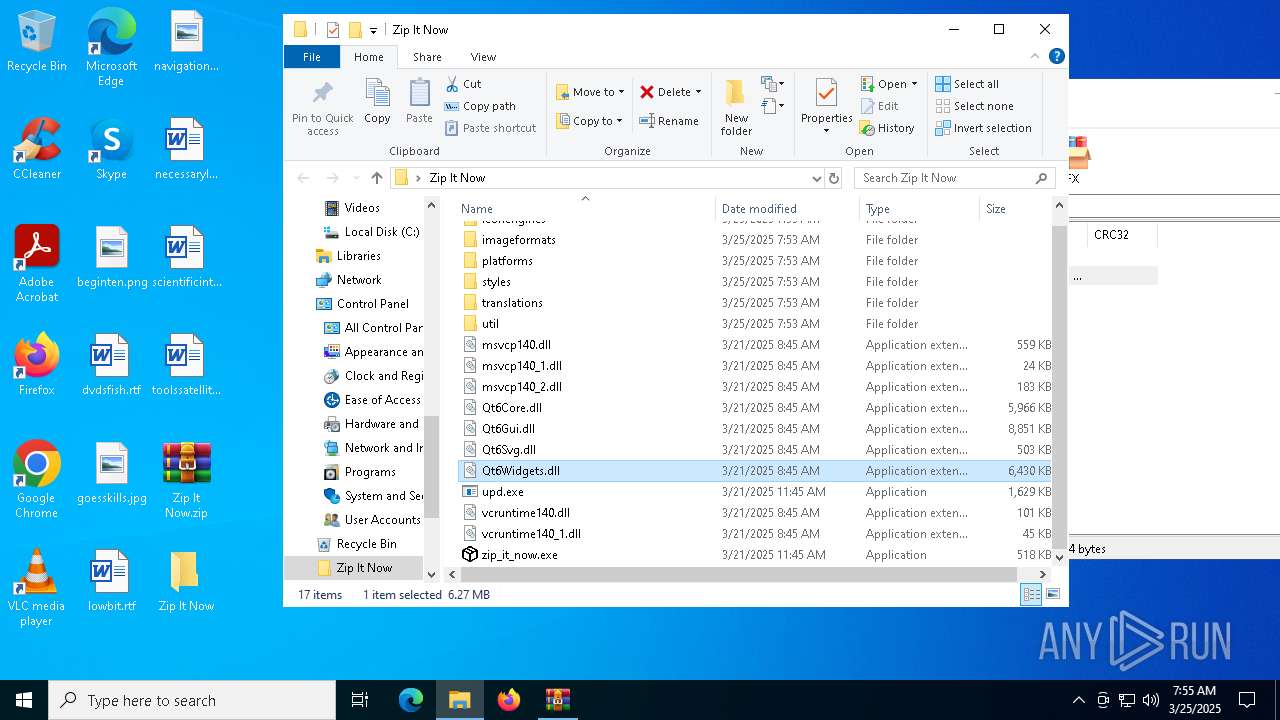
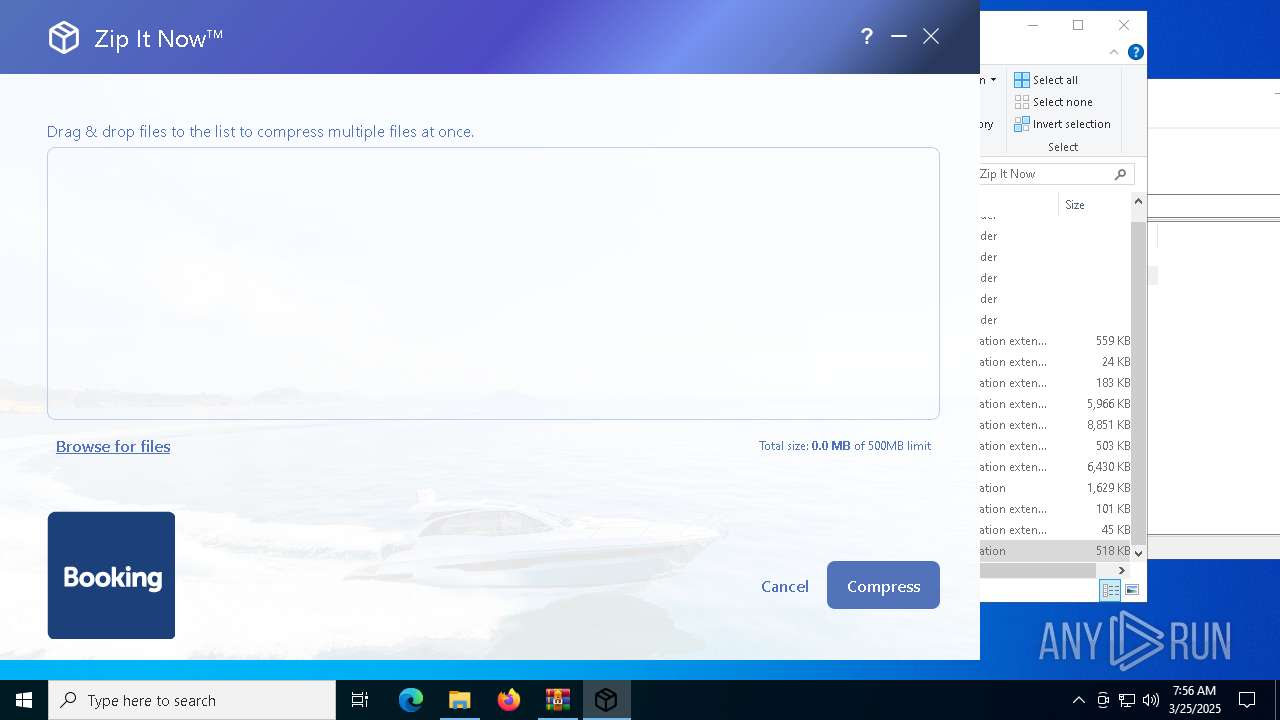
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5556)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 5556)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5556)
Executes application which crashes
- upd.exe (PID: 2560)
Reads security settings of Internet Explorer
- zip_it_now.exe (PID: 2040)
There is functionality for taking screenshot (YARA)
- zip_it_now.exe (PID: 5256)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5556)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5556)
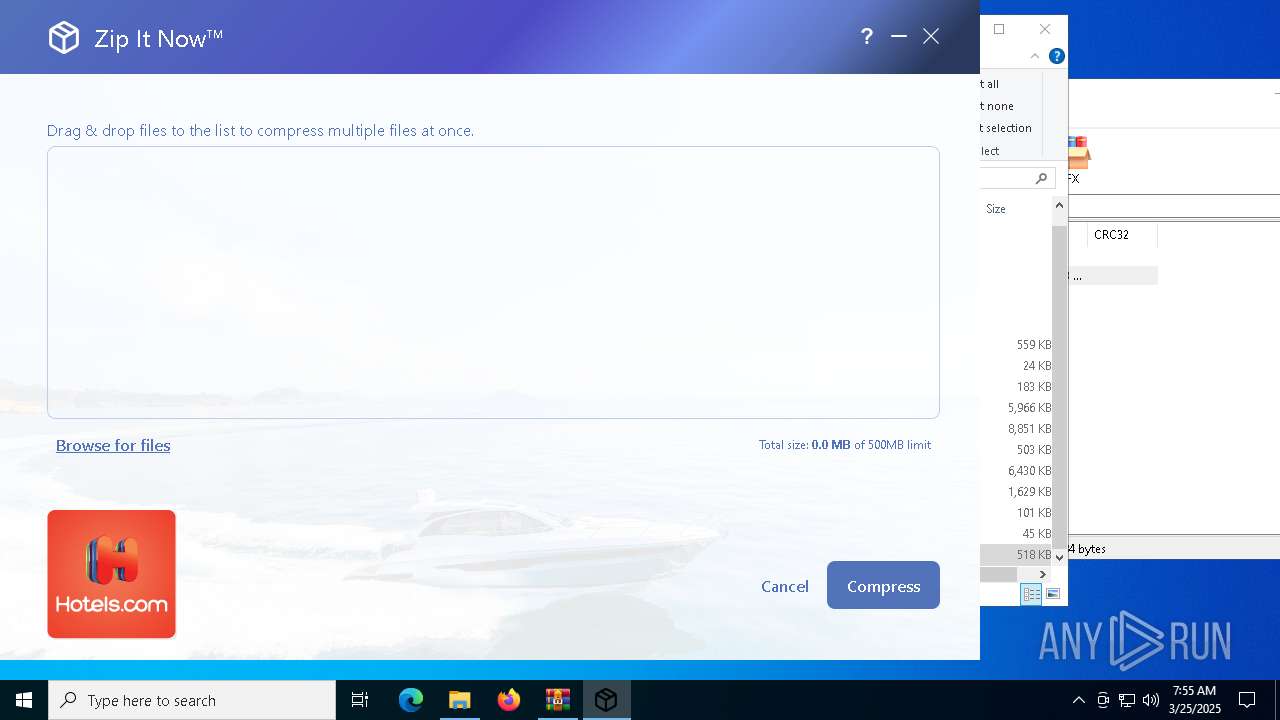
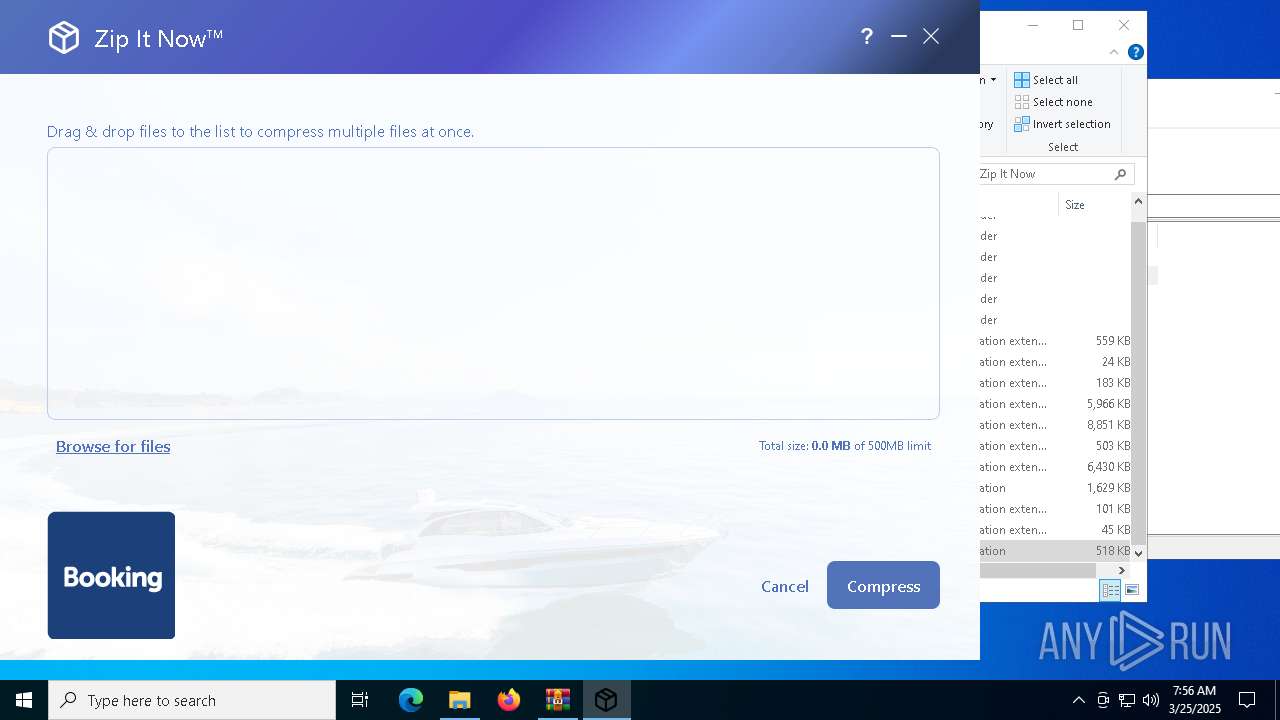
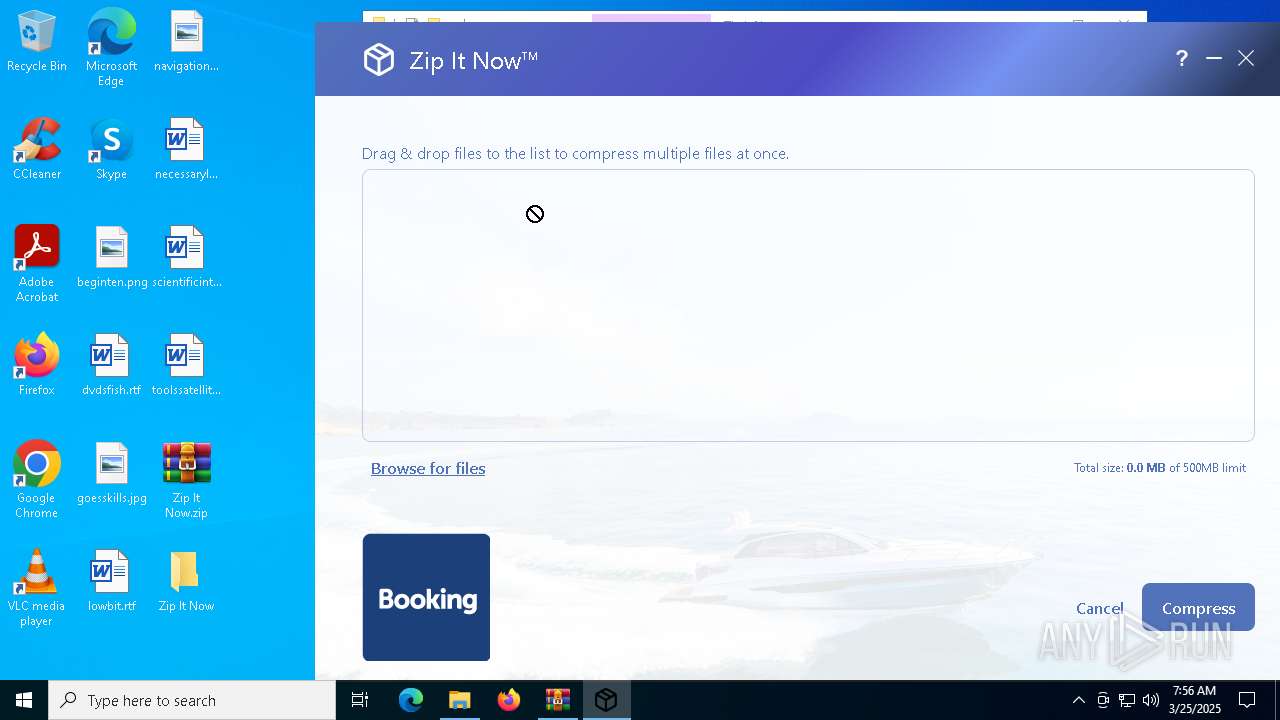
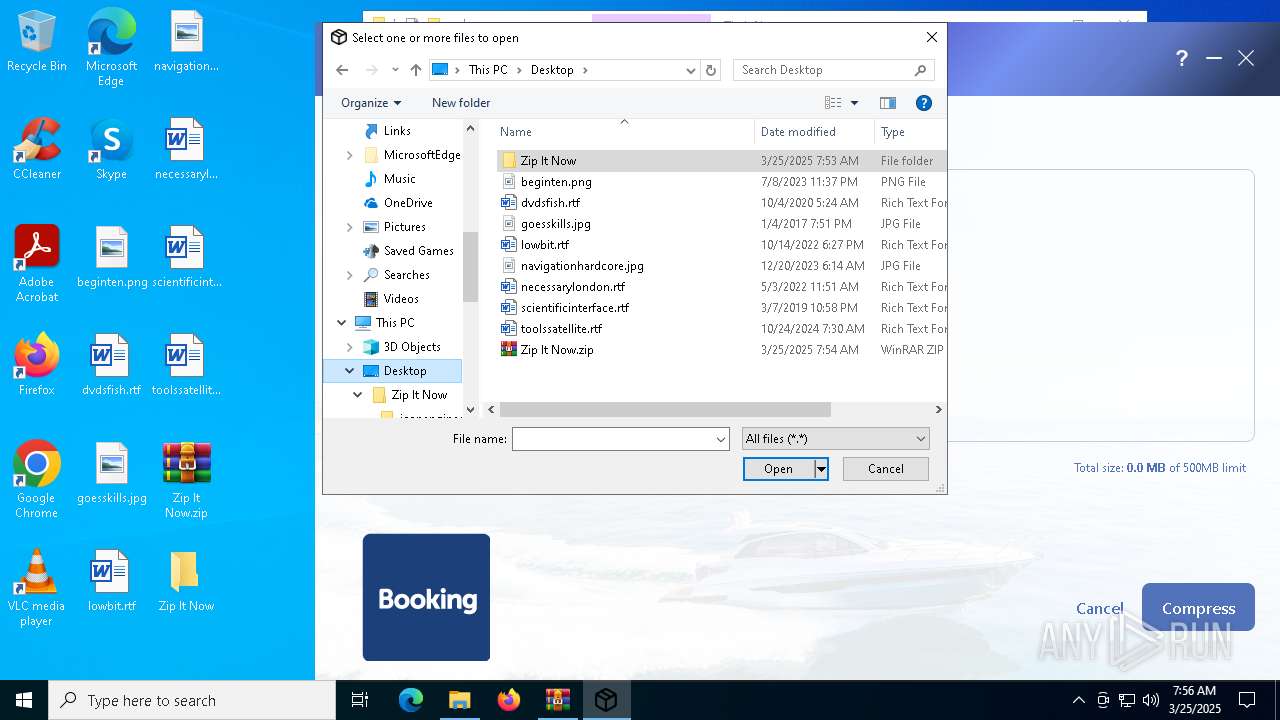
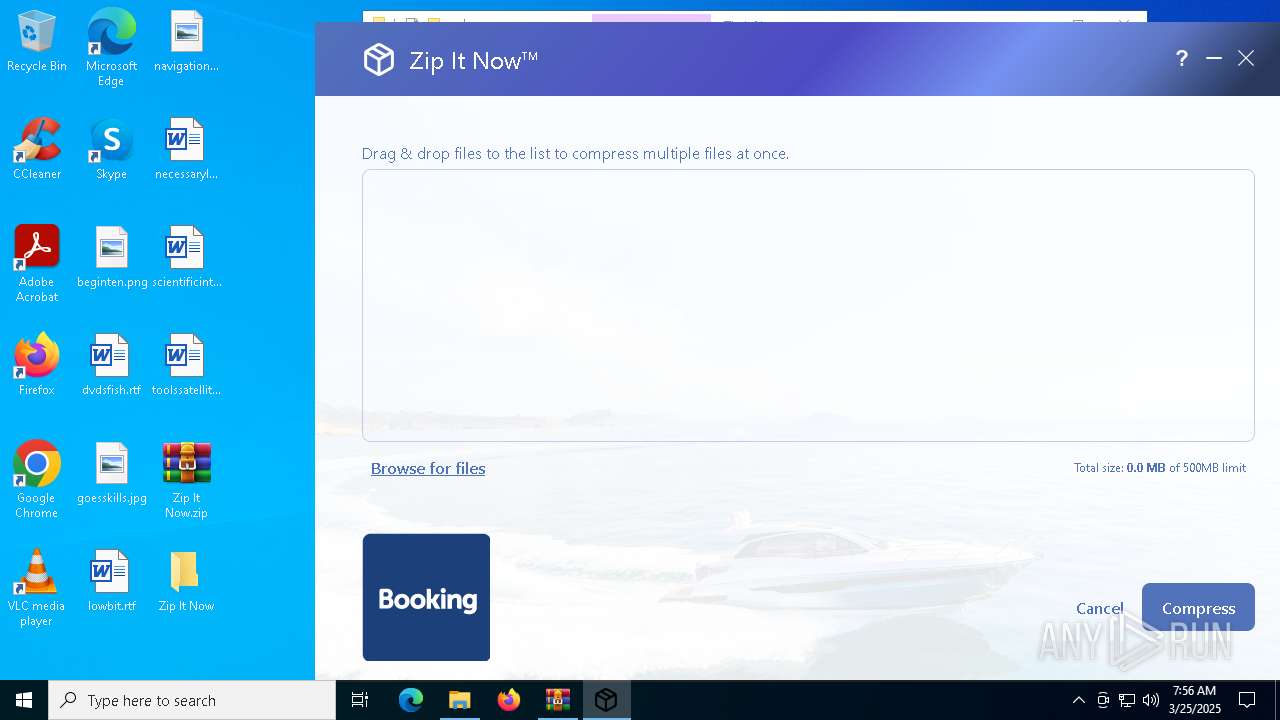
Manual execution by a user
- zip_it_now.exe (PID: 2904)
- upd.exe (PID: 2560)
- zip_it_now.exe (PID: 2040)
- WinRAR.exe (PID: 4452)
- zip_it_now.exe (PID: 5256)
Reads the computer name
- zip_it_now.exe (PID: 2904)
- upd.exe (PID: 2560)
- zip_it_now.exe (PID: 5256)
- 7z.exe (PID: 3008)
- zip_it_now.exe (PID: 2040)
- 7z.exe (PID: 536)
Checks supported languages
- zip_it_now.exe (PID: 2904)
- zip_it_now.exe (PID: 5256)
- 7z.exe (PID: 536)
- upd.exe (PID: 2560)
- 7z.exe (PID: 3008)
Checks proxy server information
- slui.exe (PID: 5384)
Reads the software policy settings
- slui.exe (PID: 5384)
Reads the machine GUID from the registry
- upd.exe (PID: 2560)
Creates files or folders in the user directory
- WerFault.exe (PID: 6108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:03:25 08:53:42 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Zip It Now/ |
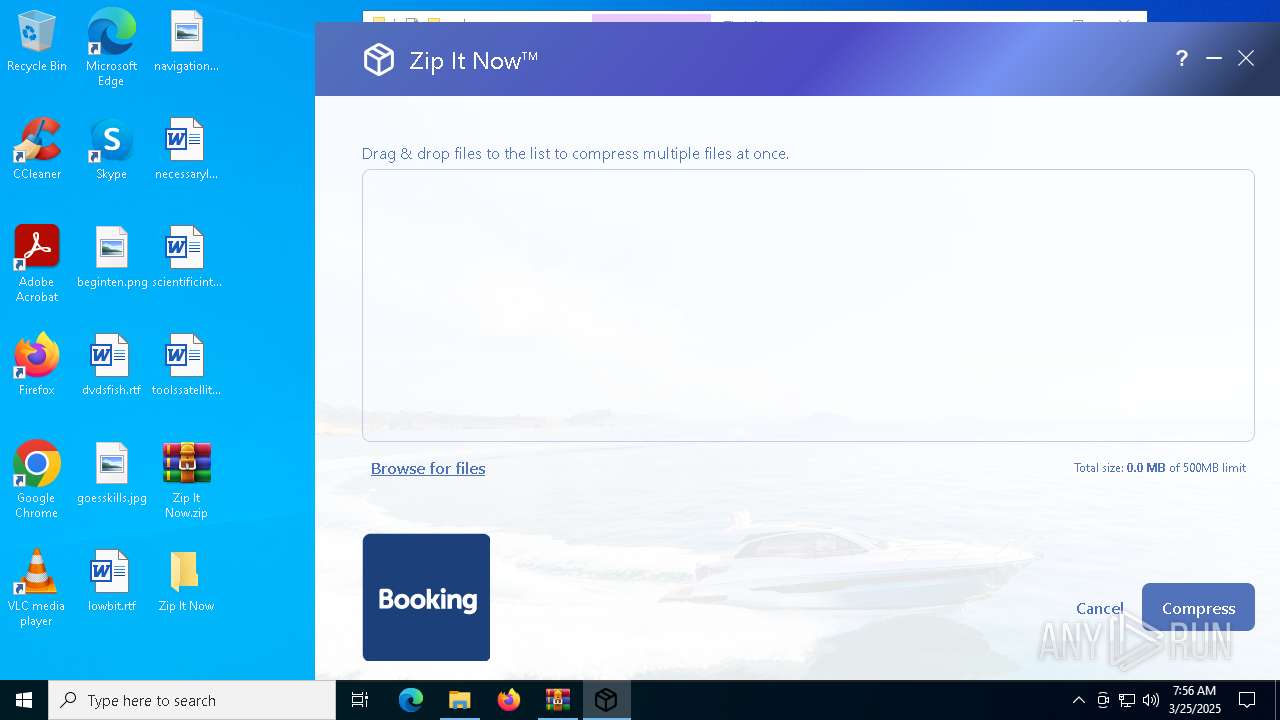
Total processes
153
Monitored processes
13
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
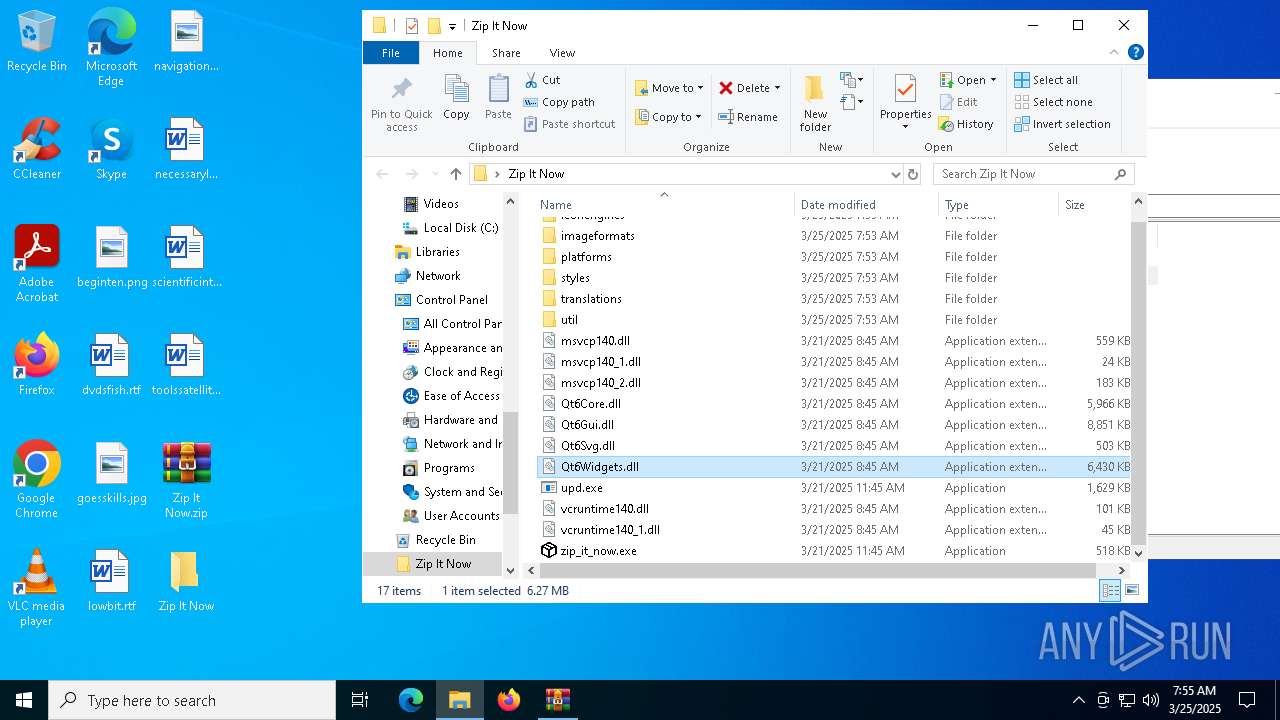
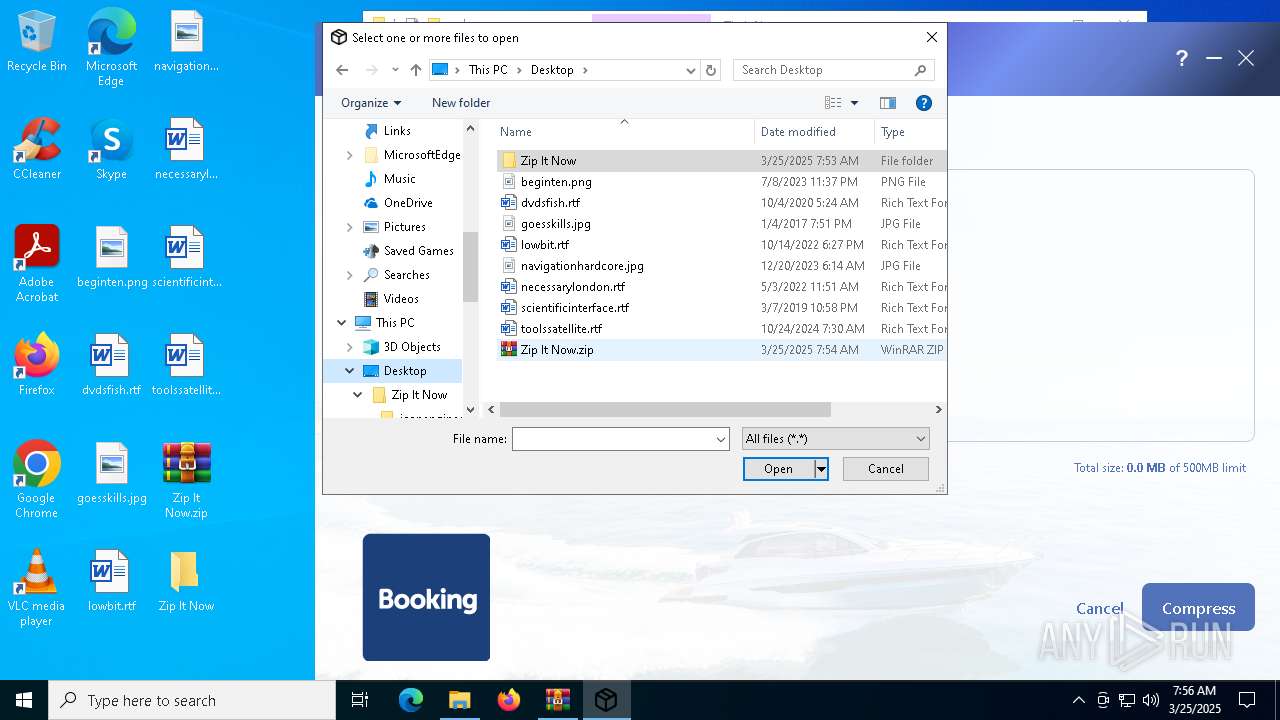
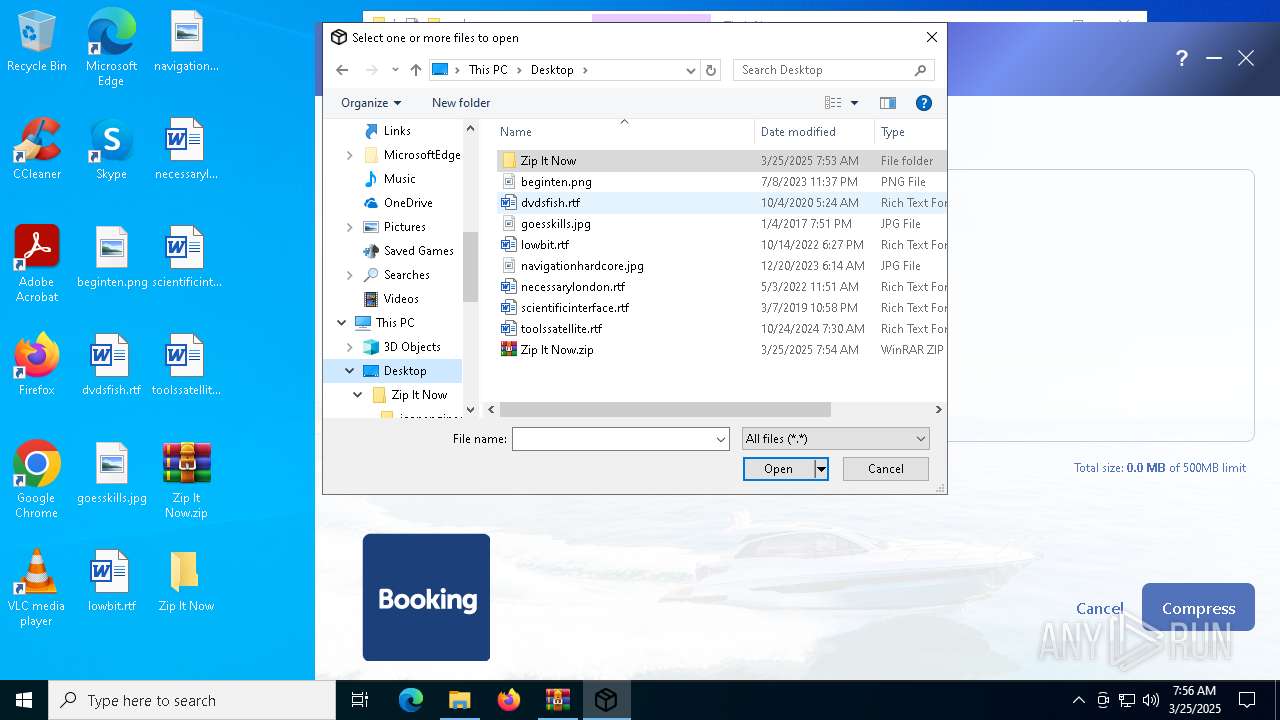
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
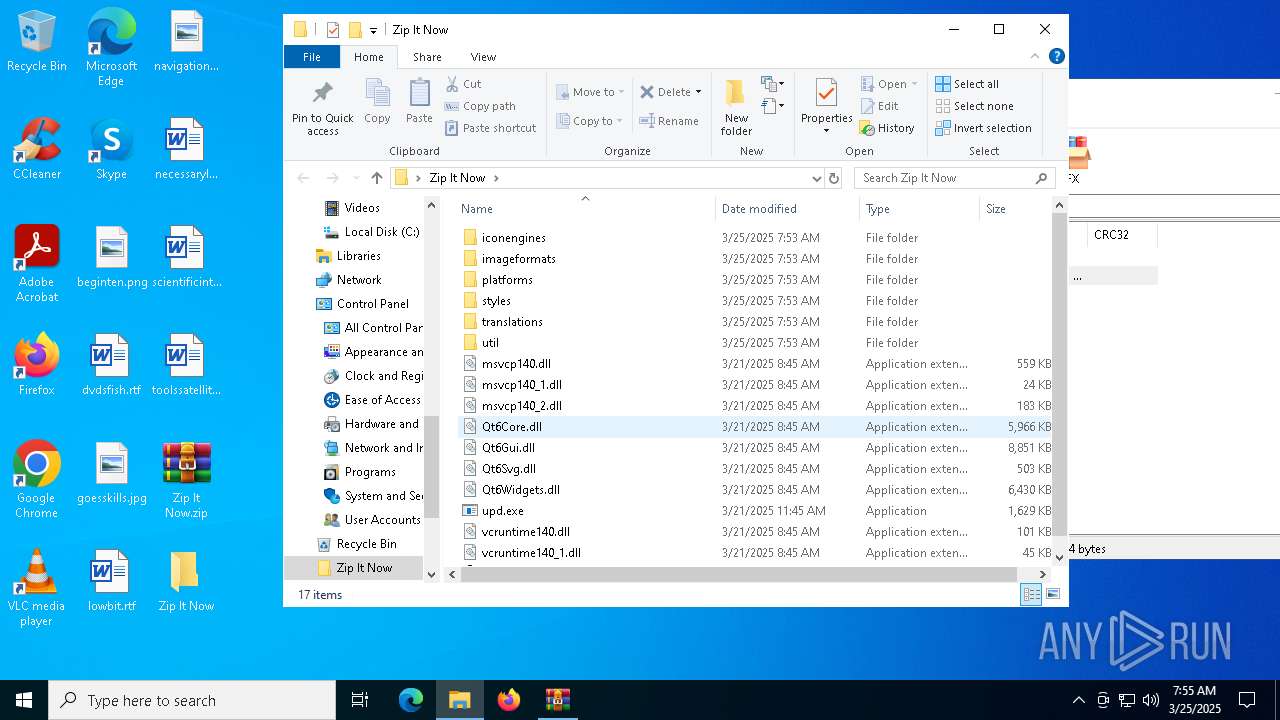
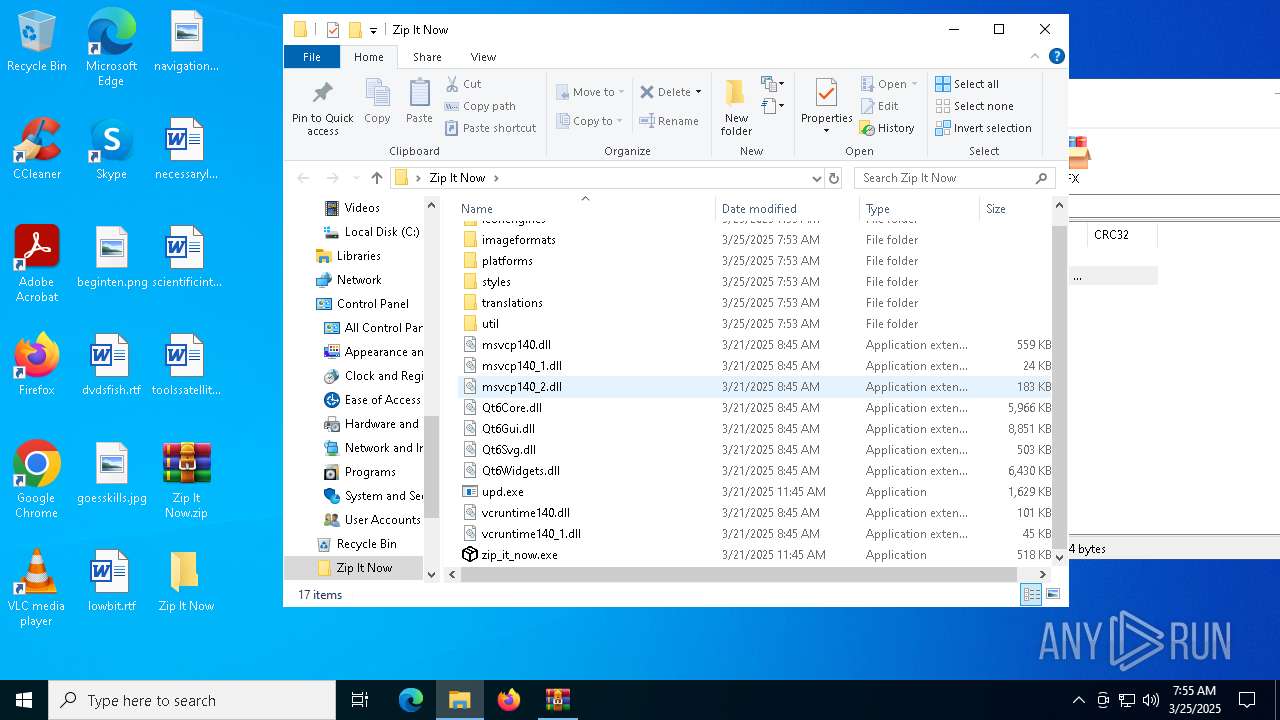
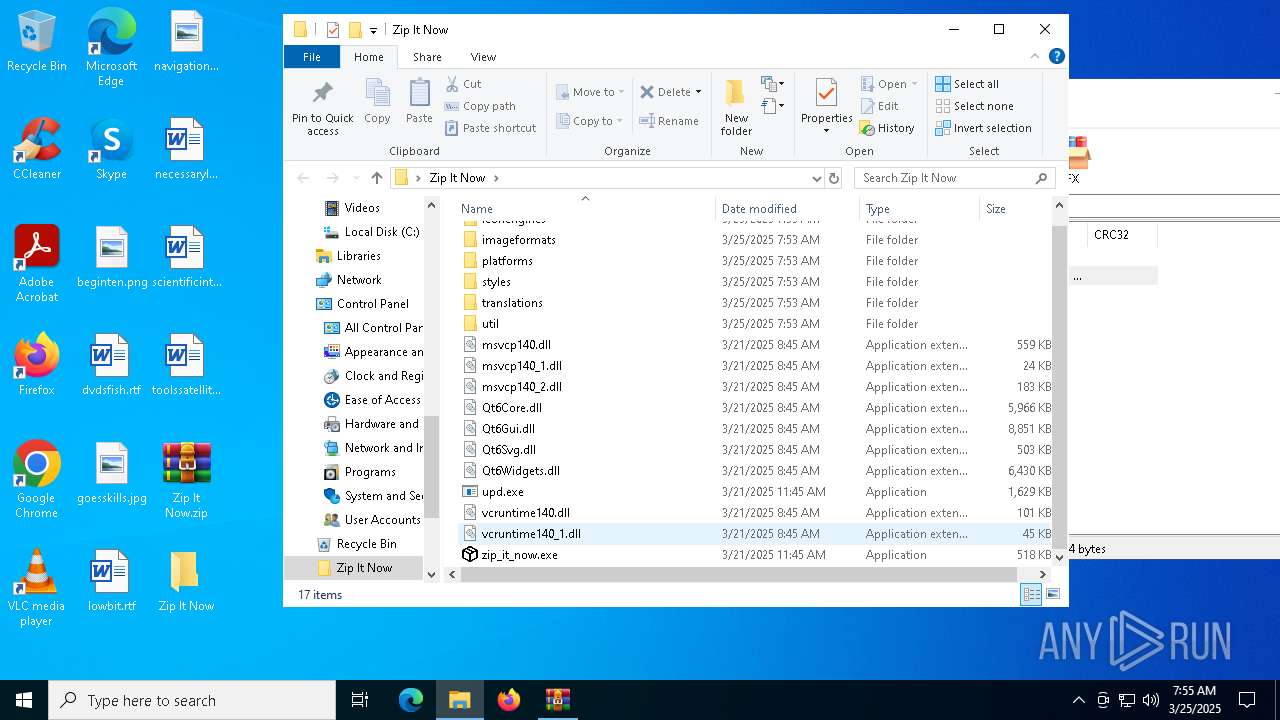
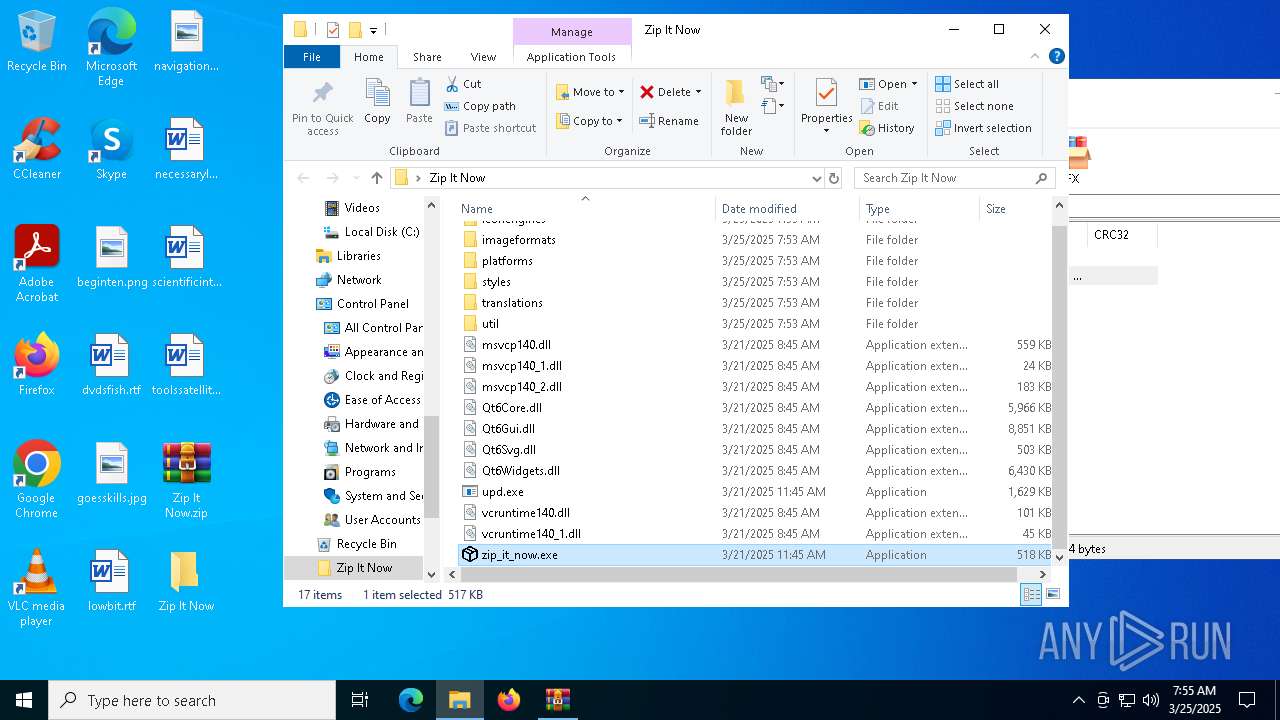
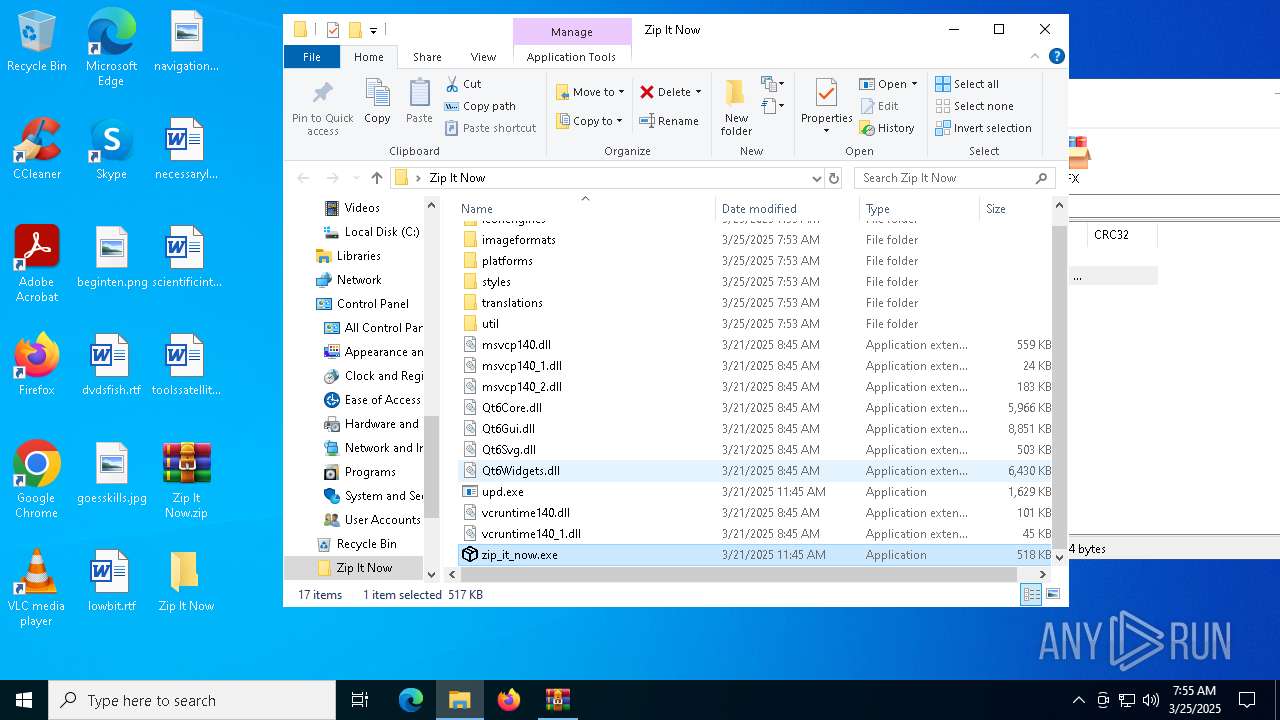
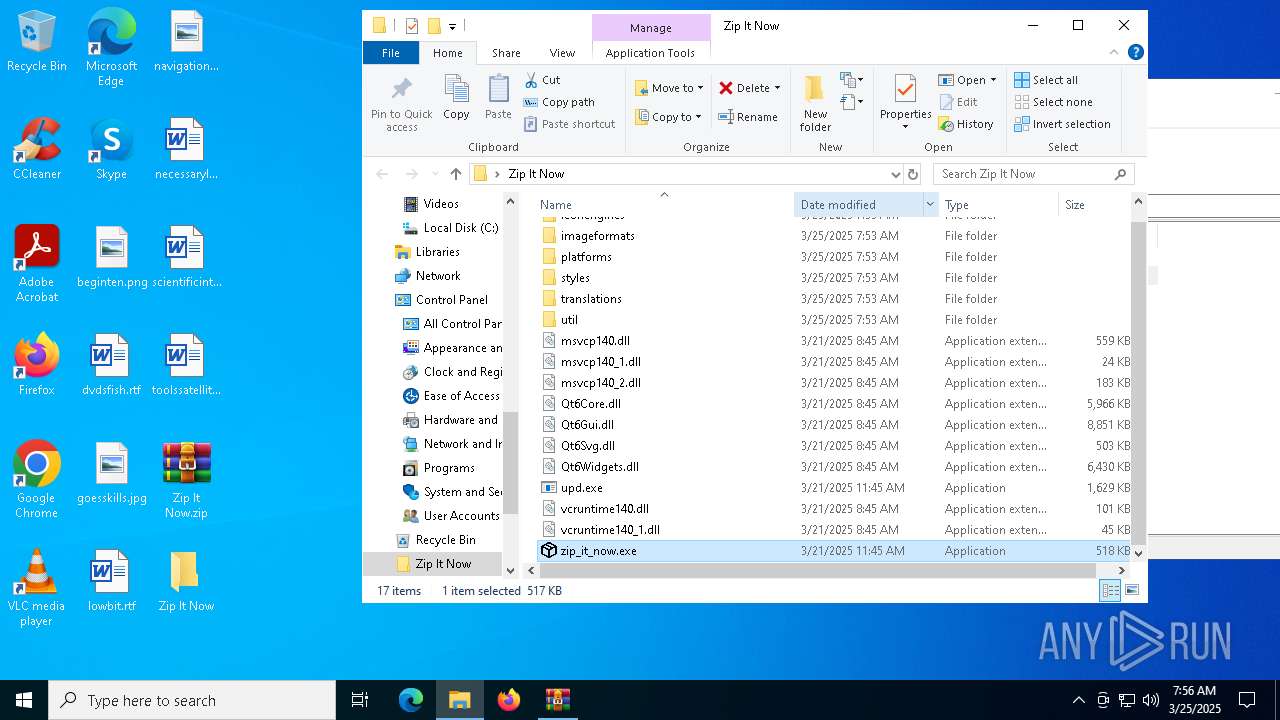
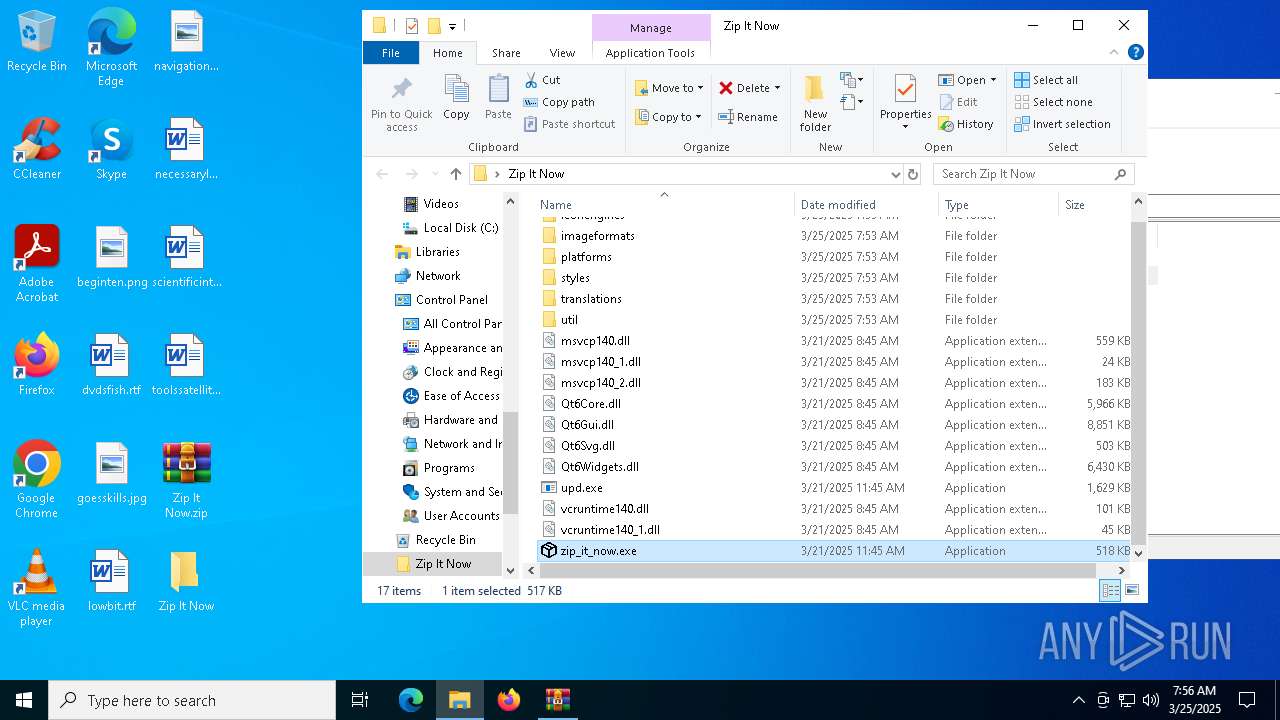
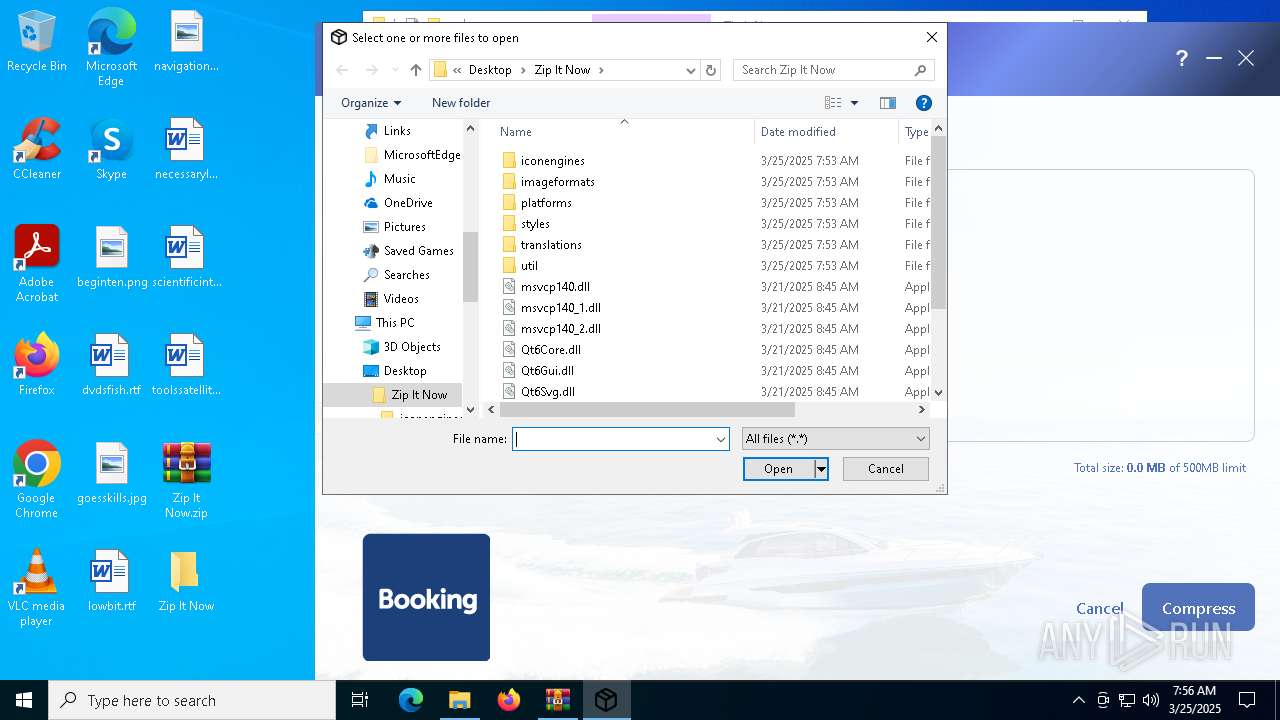
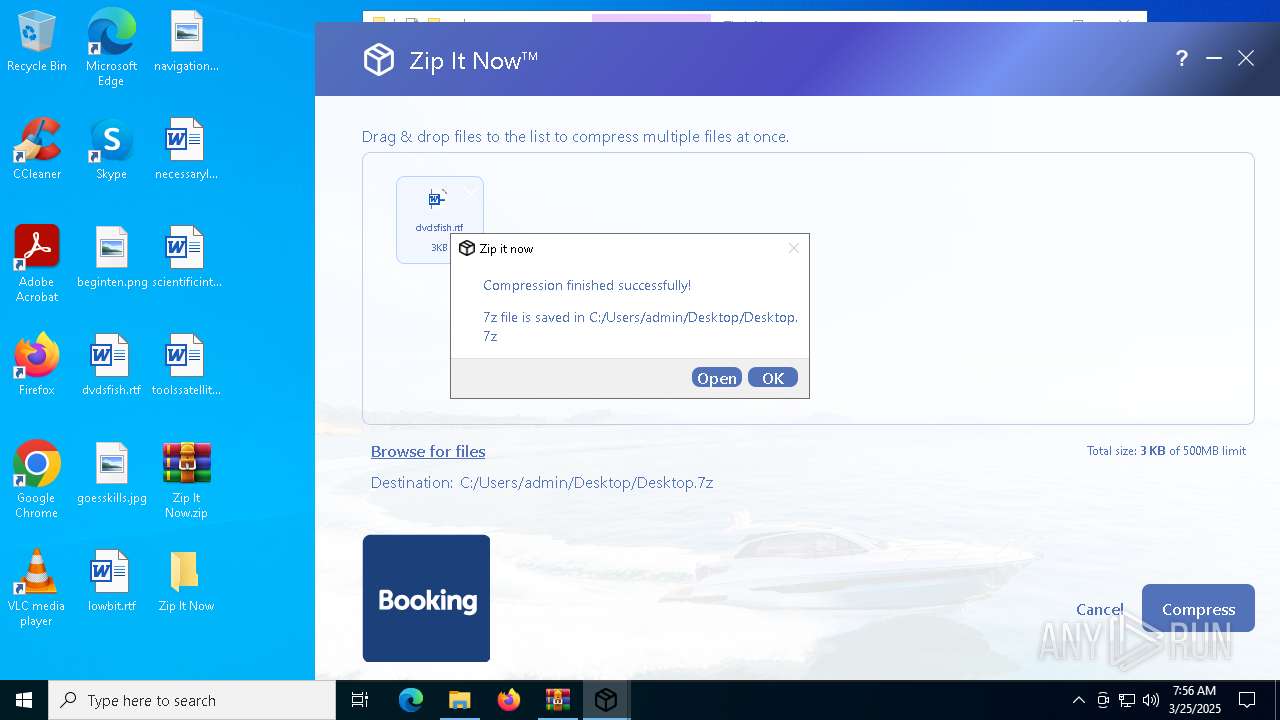
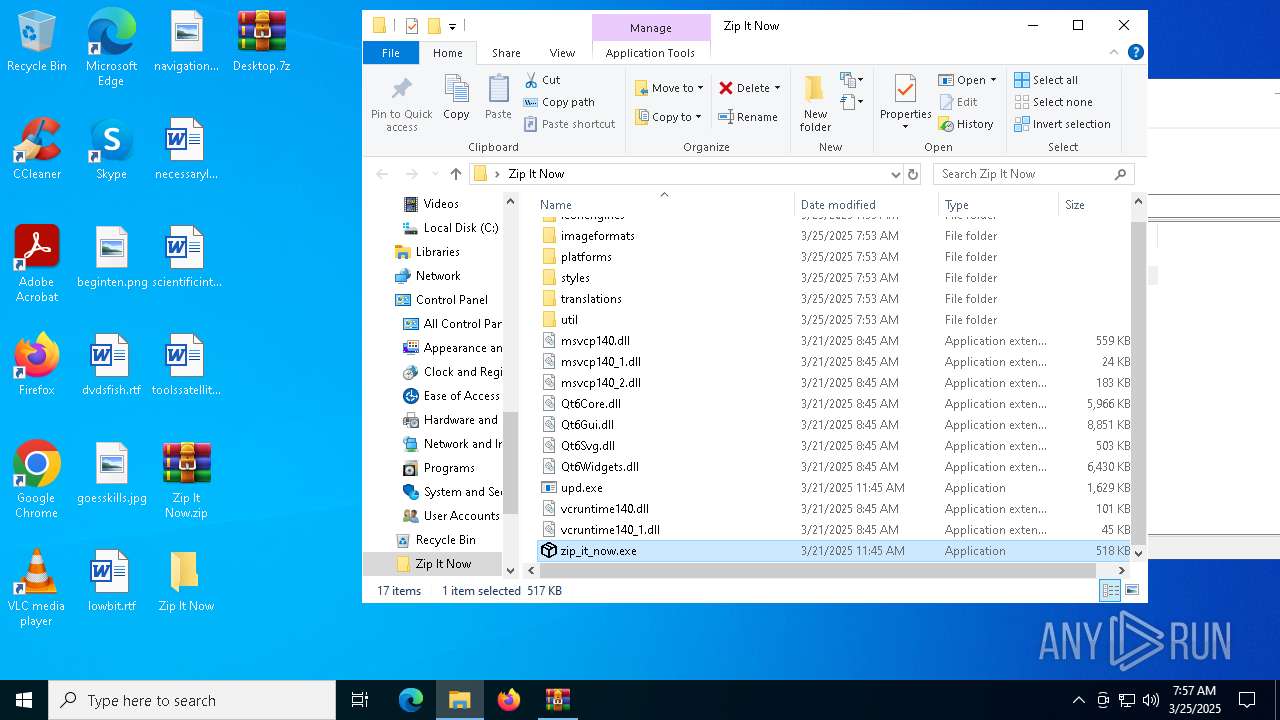
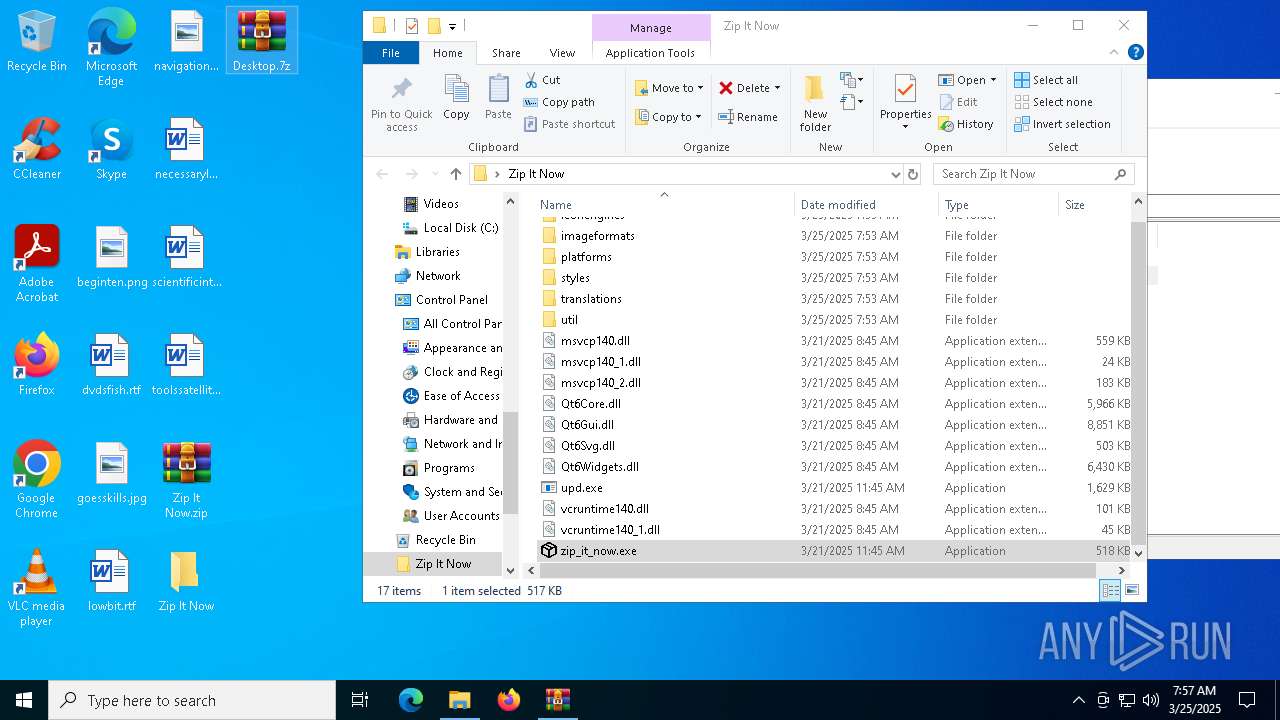
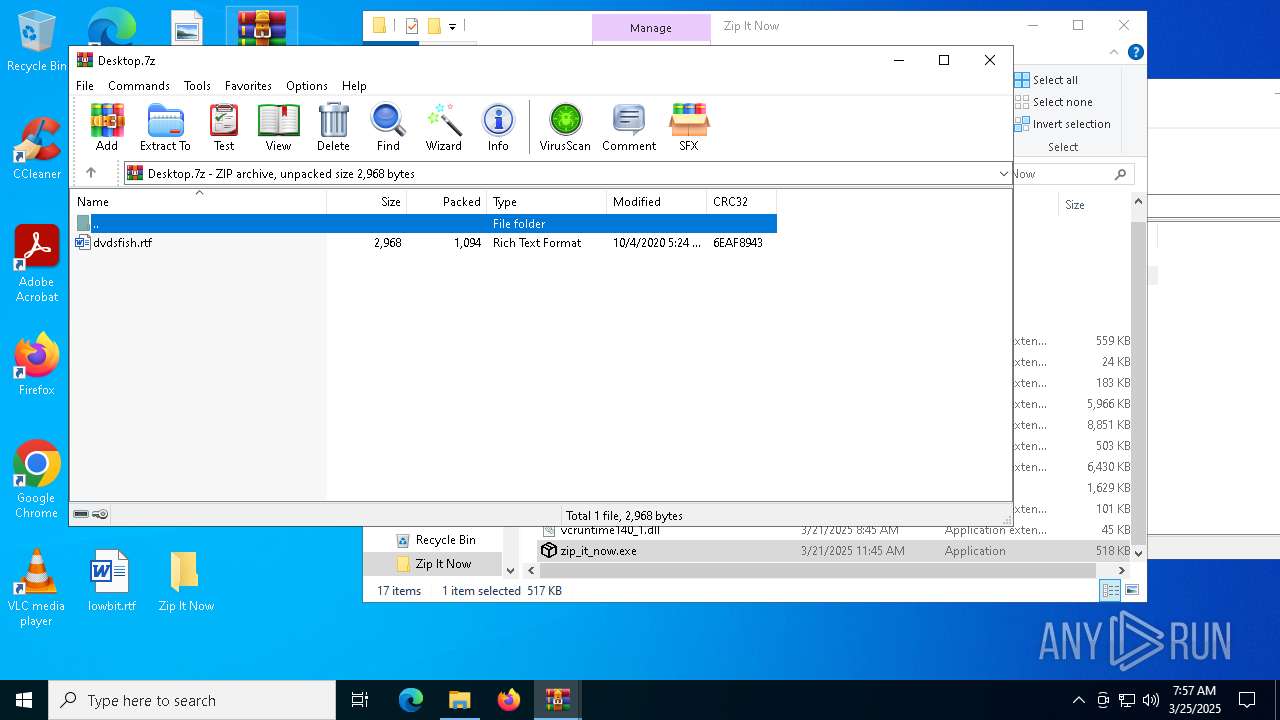
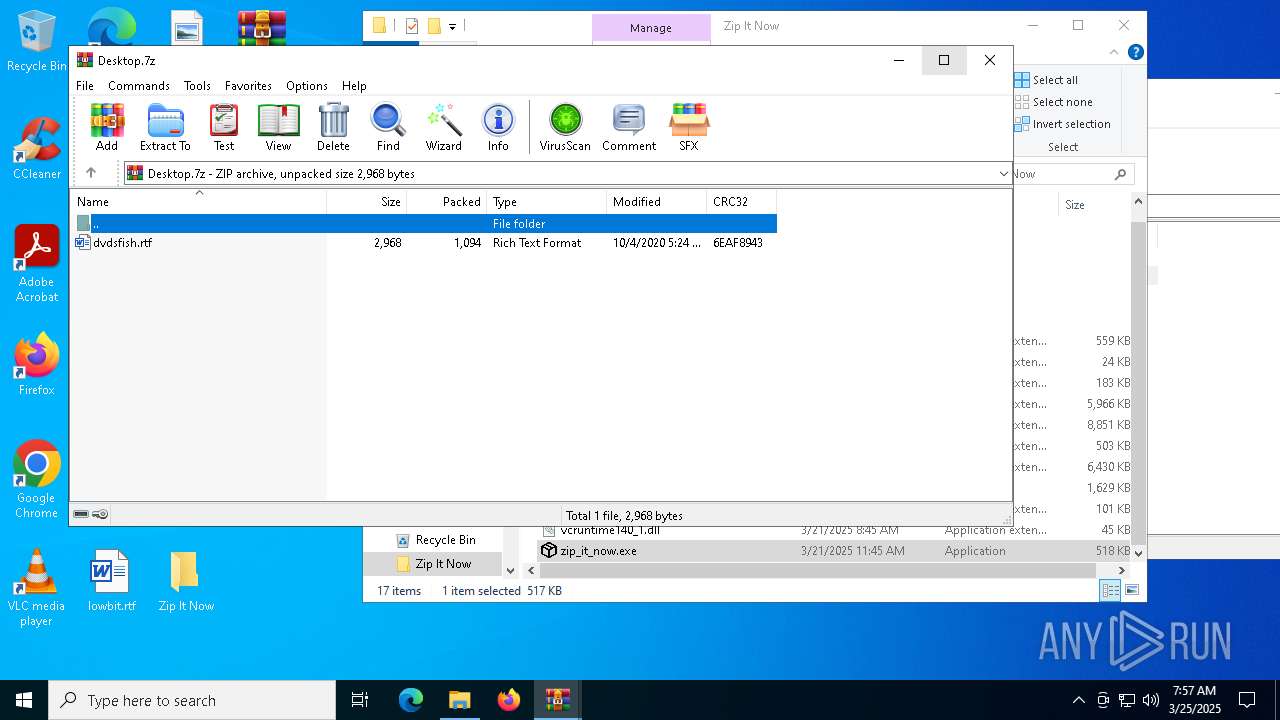
| 536 | util\7z.exe a -tzip C:/Users/admin/Desktop/Desktop.7z C:/Users/admin/Desktop/dvdsfish.rtf -r | C:\Users\admin\Desktop\Zip It Now\util\7z.exe | — | zip_it_now.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 0 Version: 22.01 Modules
| |||||||||||||||
| 1568 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
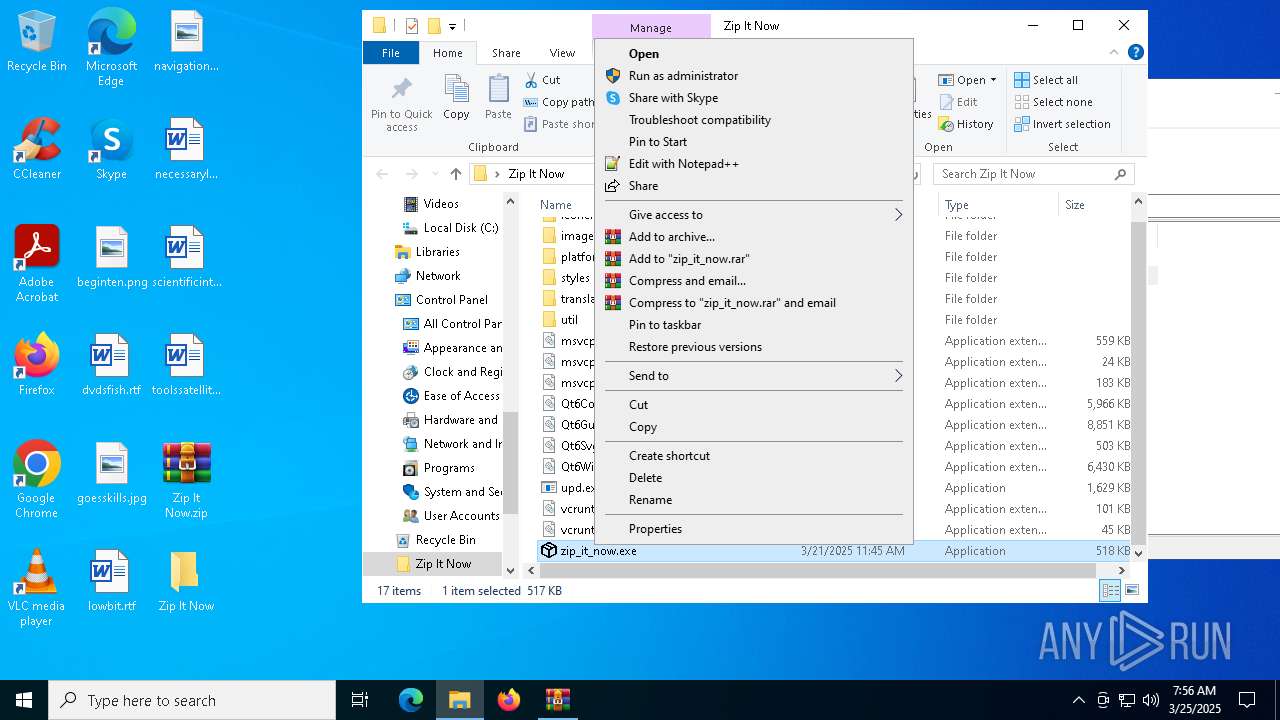
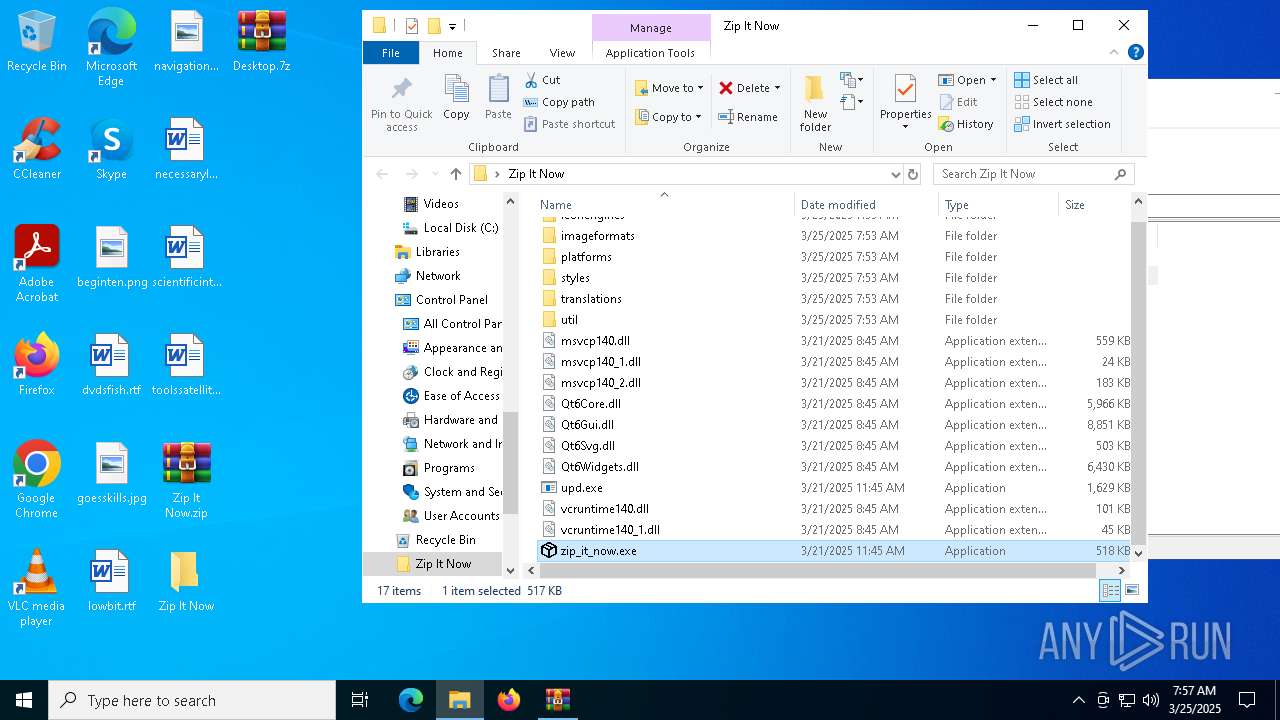
| 2040 | "C:\Users\admin\Desktop\Zip It Now\zip_it_now.exe" | C:\Users\admin\Desktop\Zip It Now\zip_it_now.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2560 | "C:\Users\admin\Desktop\Zip It Now\upd.exe" | C:\Users\admin\Desktop\Zip It Now\upd.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 2904 | "C:\Users\admin\Desktop\Zip It Now\zip_it_now.exe" | C:\Users\admin\Desktop\Zip It Now\zip_it_now.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
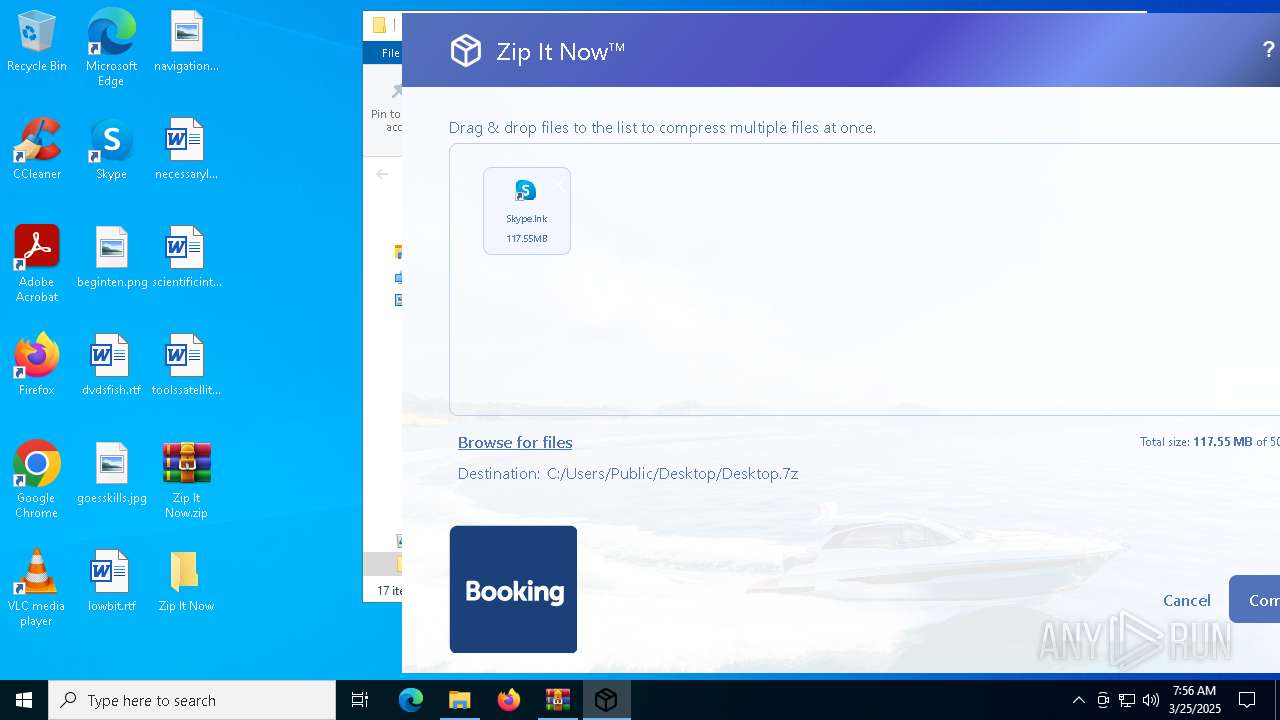
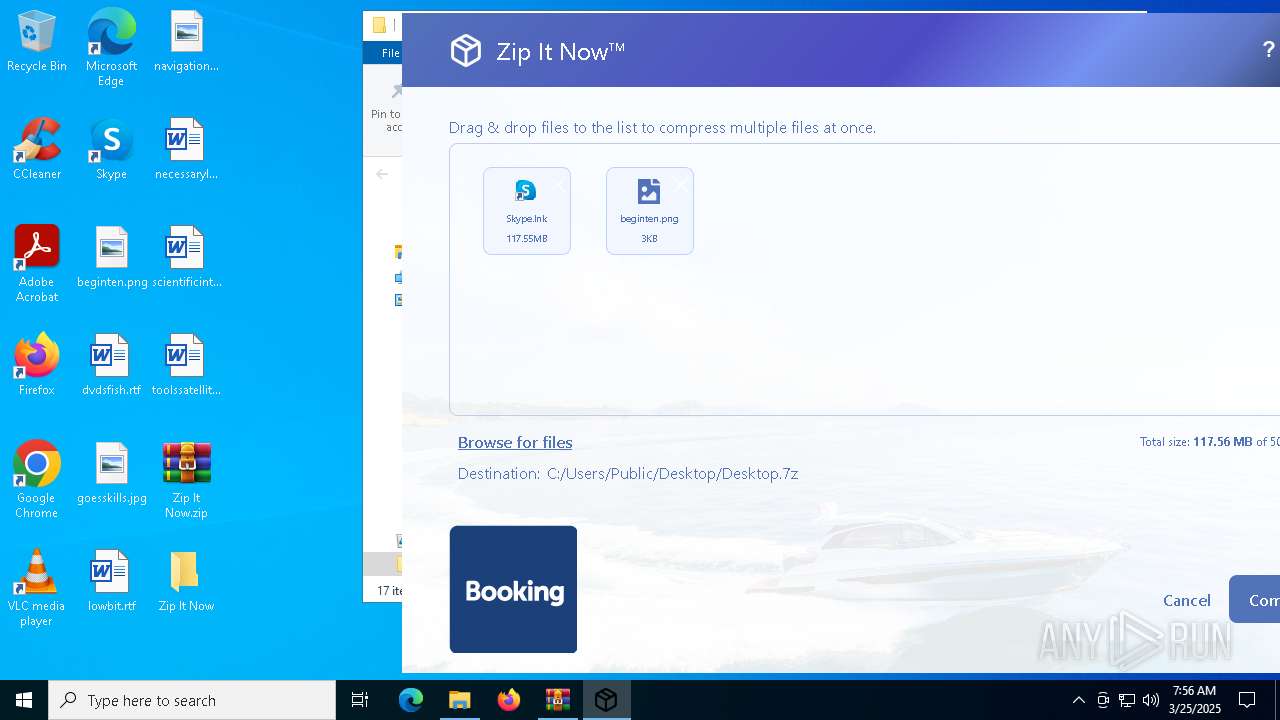
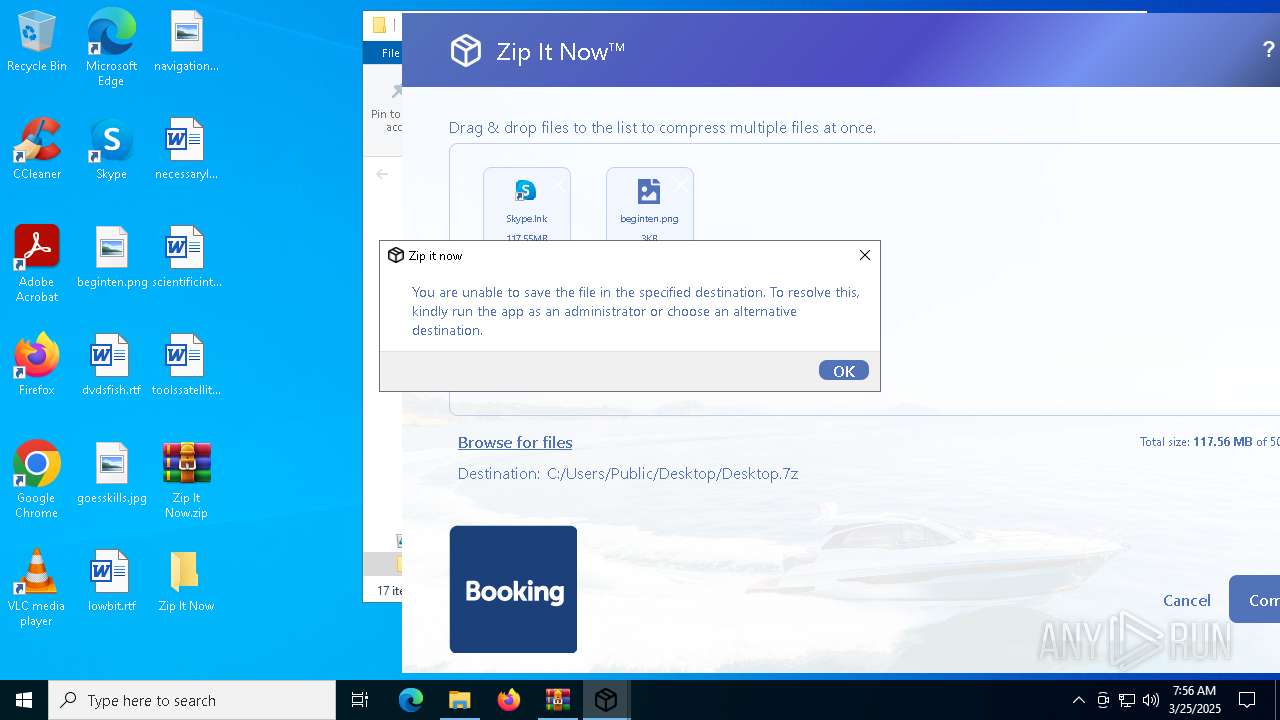
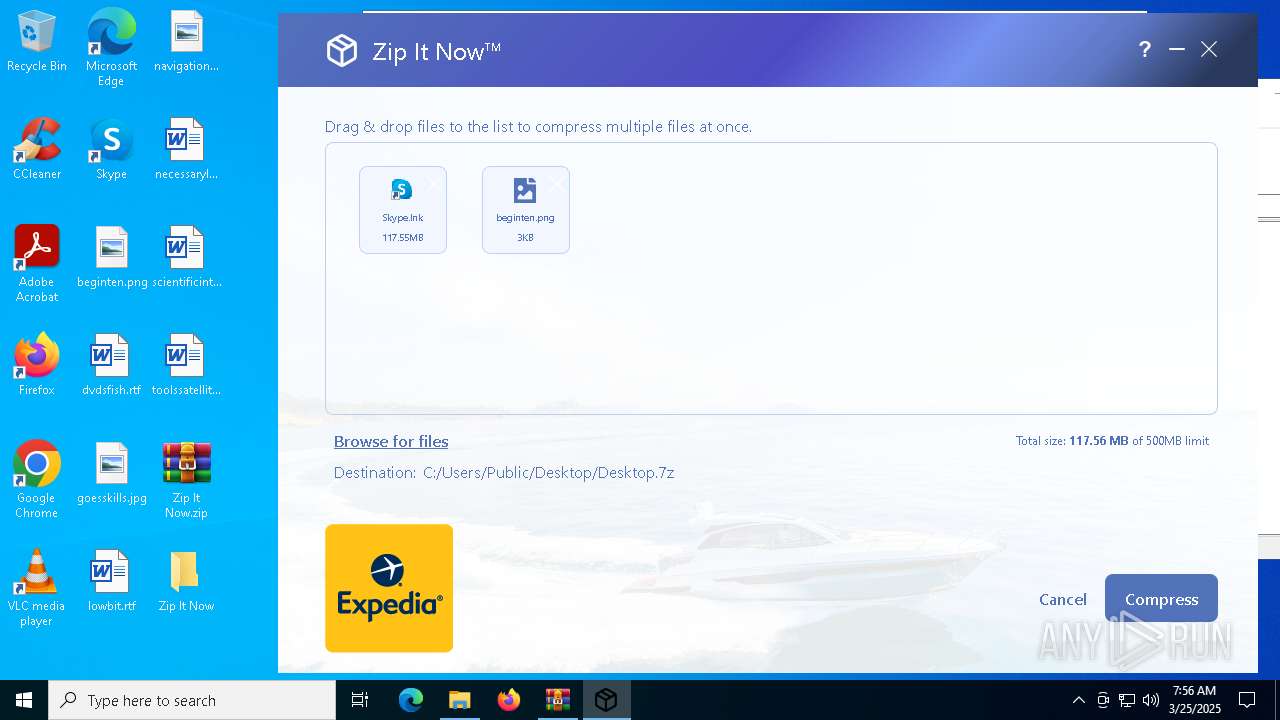
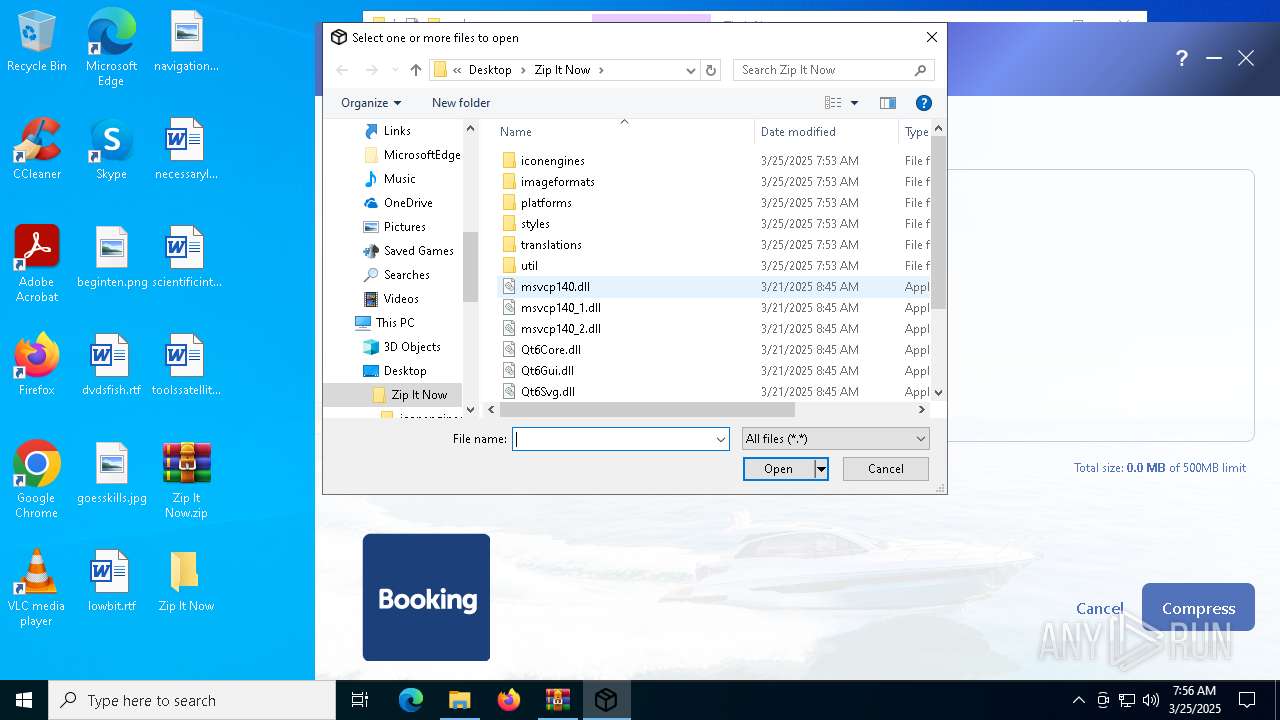
| 3008 | util\7z.exe a -tzip C:/Users/Public/Desktop/Desktop.7z C:/Users/Public/Desktop/Skype.lnk C:/Users/admin/Desktop/beginten.png -r | C:\Users\admin\Desktop\Zip It Now\util\7z.exe | — | zip_it_now.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 2 Version: 22.01 Modules
| |||||||||||||||
| 4452 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Desktop.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5020 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | "C:\Users\admin\Desktop\Zip It Now\zip_it_now.exe" | C:\Users\admin\Desktop\Zip It Now\zip_it_now.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5384 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 425
Read events
9 317
Write events
104
Delete events
4
Modification events
| (PID) Process: | (5556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Zip It Now.zip | |||
| (PID) Process: | (5556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5256) zip_it_now.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
| (PID) Process: | (2040) zip_it_now.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
Executable files
26
Suspicious files
34
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\imageformats\qgif.dll | executable | |
MD5:0C29D05DA47954CAD9B66C519187E2BA | SHA256:B1AF633A000FD8E2CDAC988248EC984AB39B633E678B4700163F2A2761A08323 | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\iconengines\qsvgicon.dll | executable | |
MD5:86ACD7B222196BCC95DD20A7038C5C12 | SHA256:0194BC1679CDBFF3EEEC85E56D6D97D7B8A1A5DDD0BF026BA90356BAE1D4E8FF | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\imageformats\qicns.dll | executable | |
MD5:65682BA0E5E6931BDB9EDD3179B08A1E | SHA256:A741826ED2E3FA95F1B2C0D31931C00B3BA9488664A92357A8F3CB09A94D4C3E | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\imageformats\qpdf.dll | executable | |
MD5:2E3D72B227D7767B8D702F072EF454E9 | SHA256:3C963727BF40C49AB9DC7E18F32F9EB5ADE89FF0500983145AEBA978DC49C20B | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\imageformats\qtga.dll | executable | |
MD5:9BBA83D7CA82616B59A0593A63449EBA | SHA256:EEA58AE3E461697F7B67777660797F49465AF65332A8801B6AFE826BCA6EE7D8 | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\imageformats\qjpeg.dll | executable | |
MD5:9D88F76F6DE80FF457CFE2419A4334AA | SHA256:66DD26E1CDF681EE28D363CA3E8162DF42D68392AFB845C9A870AE6F27889F8E | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\imageformats\qico.dll | executable | |
MD5:793DBF7BA9C51B24F7D6EC4950B5BB63 | SHA256:81AA6C240523C4ED1FEC1A7B49CCA595EE70BA5AE635D9310EA089CD7B802E26 | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\msvcp140.dll | executable | |
MD5:BF78C15068D6671693DFCDFA5770D705 | SHA256:A88B8C1C8F27BF90FE960E0E8BD56984AD48167071AF92D96EC1051F89F827FB | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\imageformats\qwebp.dll | executable | |
MD5:2C5E1A897DB38619E62088A603F86427 | SHA256:B0E46794751211020E9CD26386D55B957515B745A731DE8DB337EAFA3F3FED32 | |||
| 5556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5556.13193\Zip It Now\imageformats\qwbmp.dll | executable | |
MD5:211F7809EAE378A0E4F56E0A3B1201C3 | SHA256:5E293B50E667BCDFF606F62486E3F13C081DDFDB1A03A92E482D56A18F5B3CDF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2108 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4920 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4920 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2108 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |