| URL: | http://46.17.47.4/Redirection/index.php?referrer=other |
| Full analysis: | https://app.any.run/tasks/8854d6ba-bc6c-42d9-92cf-89b7b35fad27 |
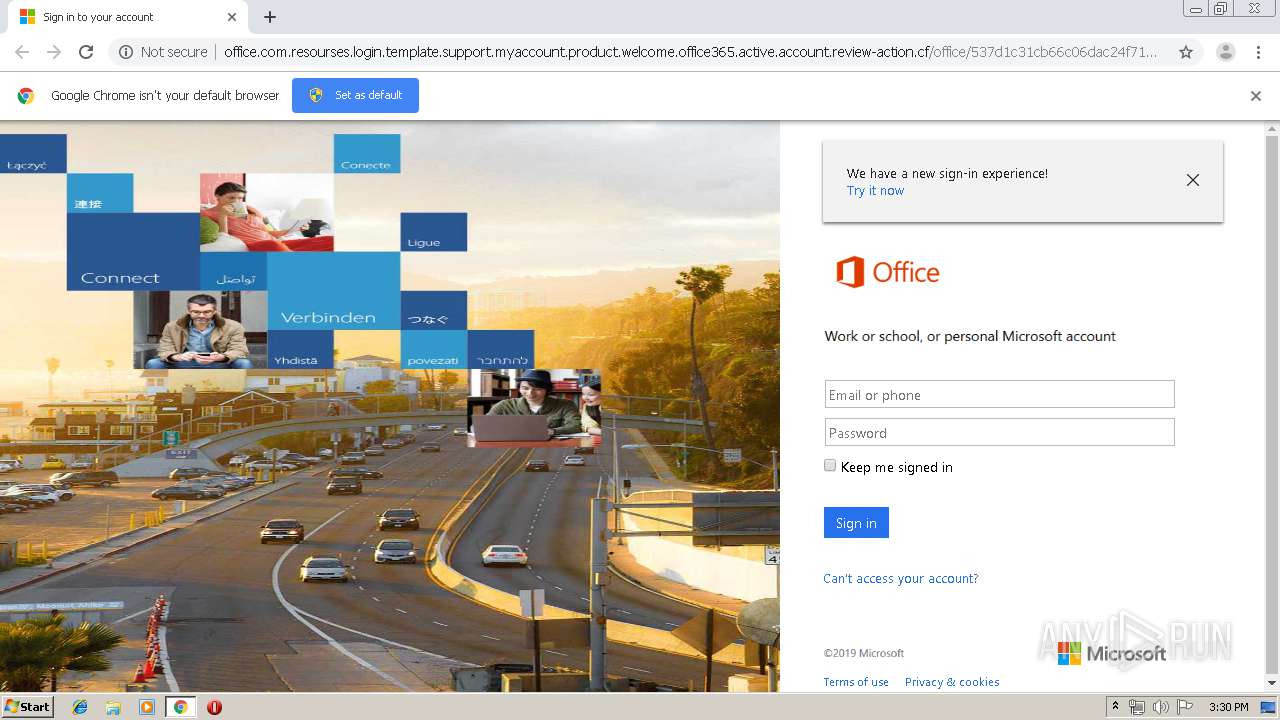
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 14:29:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D58FCEF0E39B04AB75C0D6D1FEC47902 |
| SHA1: | 835DED491EB8763CFF4D1A93F8D58E8FD7F48D7F |
| SHA256: | 0F5F563DB4EA07C13828FA38064E952403B67C8EBD00310EDB34C97606D89B8A |
| SSDEEP: | 3:N1K2sQw6QGcdhHcAcHyUX:C2LQDHcAcSO |
MALICIOUS
Loads Microsoft favicon from HTTP
- chrome.exe (PID: 1732)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
17
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15371088413337423395 --mojo-platform-channel-handle=3660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x70fea9d0,0x70fea9e0,0x70fea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5494645080817284628 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9097274751919909131 --mojo-platform-channel-handle=3952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15098022979927697729 --mojo-platform-channel-handle=3640 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12535053258640321122 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1102579751910682903 --mojo-platform-channel-handle=3628 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15030995160904450365 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3000 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10618810543064553895,12100539516448814660,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8341225358309713352 --mojo-platform-channel-handle=3736 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
175
Read events
132
Write events
40
Delete events
3
Modification events
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3440-13210180202955875 |
Value: 259 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
7
Text files
78
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\037c8d16-7cb4-4317-a6c0-03ce032b2dc0.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF378b2d.TMP | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF378b3d.TMP | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
23
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1732 | chrome.exe | GET | 302 | 85.117.235.165:80 | http://office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf/office/index.php | unknown | — | — | suspicious |
1732 | chrome.exe | GET | 200 | 85.117.235.165:80 | http://office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf/office/537d1c31cb66c06dac24f7185289bd/jquery.js | unknown | text | 107 Kb | suspicious |
1732 | chrome.exe | GET | 200 | 85.117.235.165:80 | http://office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf/office/537d1c31cb66c06dac24f7185289bd/css/login.min.css | unknown | text | 22.9 Kb | suspicious |
1732 | chrome.exe | GET | 200 | 85.117.235.165:80 | http://office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf/office/537d1c31cb66c06dac24f7185289bd/index.html | unknown | html | 15.1 Kb | suspicious |
1732 | chrome.exe | GET | 200 | 85.117.235.165:80 | http://office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf/office/537d1c31cb66c06dac24f7185289bd/img/logo.png | unknown | image | 16.3 Kb | suspicious |
1732 | chrome.exe | GET | 200 | 85.117.235.165:80 | http://office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf/office/537d1c31cb66c06dac24f7185289bd/img/bannerlogo.png | unknown | image | 16.3 Kb | suspicious |
1732 | chrome.exe | GET | 302 | 46.17.47.4:80 | http://46.17.47.4/Redirection/index.php?referrer=other | RU | text | 480 b | suspicious |
1732 | chrome.exe | GET | 200 | 85.117.235.165:80 | http://office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf/office/537d1c31cb66c06dac24f7185289bd/img/heading.PNG | unknown | image | 1.91 Kb | suspicious |
1732 | chrome.exe | GET | 200 | 85.117.235.165:80 | http://office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf/office/537d1c31cb66c06dac24f7185289bd/img/sub_heading.PNG | unknown | image | 822 b | suspicious |
1732 | chrome.exe | GET | 200 | 46.17.47.4:80 | http://46.17.47.4/Redirection/check.php?newtoken=MTU2NTcwNjYxMzQ0ZjdmNzJhZDY1MzcwMjJlMDY2NjczZjlkODMyZWExYTgzZTE0NGVmOGM5ZmUyN2Q4OWZlNzQ5ZGEzYzU0Njc5ODQ5ZjVjNg== | RU | html | 191 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1732 | chrome.exe | 216.58.207.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1732 | chrome.exe | 172.217.22.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1732 | chrome.exe | 46.17.47.4:80 | — | LLC Baxet | RU | unknown |
1732 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1732 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1732 | chrome.exe | 85.117.235.165:80 | office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf | — | — | suspicious |
1732 | chrome.exe | 172.217.21.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
1732 | chrome.exe | 173.194.150.251:80 | r5---sn-2gb7sn7z.gvt1.com | Google Inc. | US | whitelisted |
1732 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1732 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
office.com.resourses.login.template.support.myaccount.product.welcome.office365.active.account.review-action.cf |
| suspicious |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-2gb7sn7z.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |