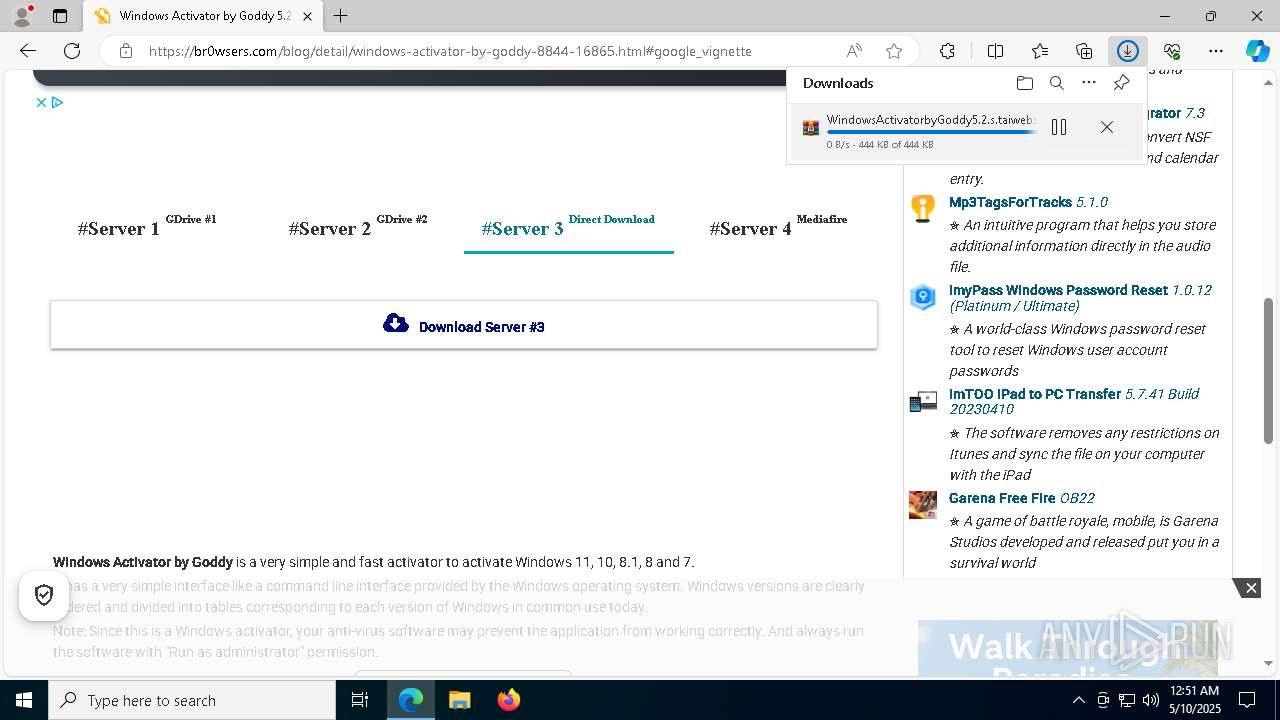
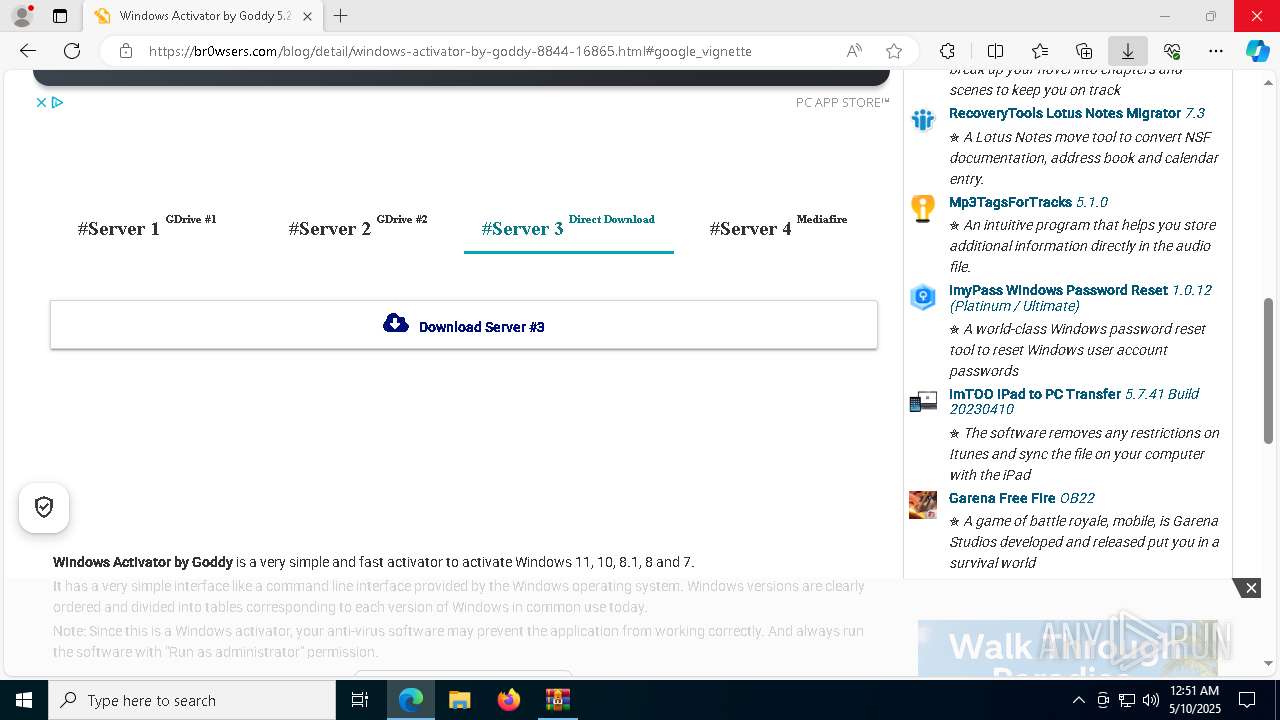
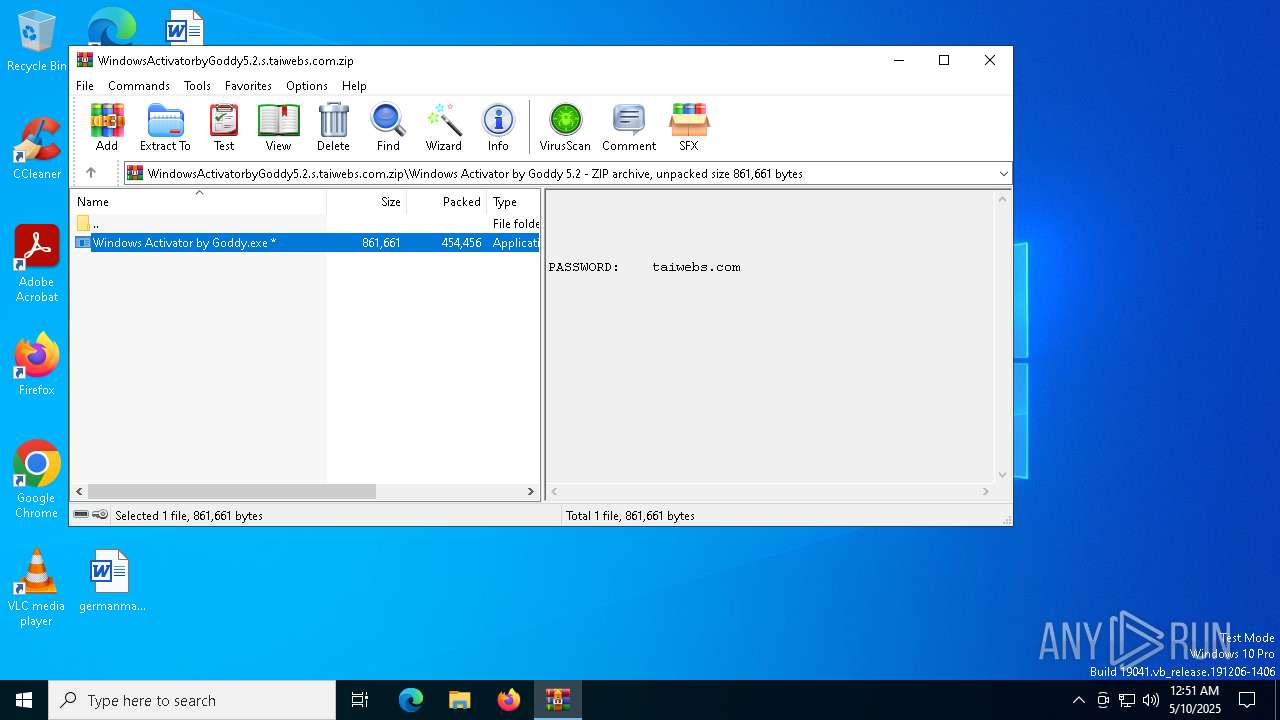
| URL: | https://en.taiwebs.com/windows/download-windows-activator-by-goddy-8844.html |
| Full analysis: | https://app.any.run/tasks/42ccfc19-d9d8-40b2-a1a7-e24c5a4f9b95 |
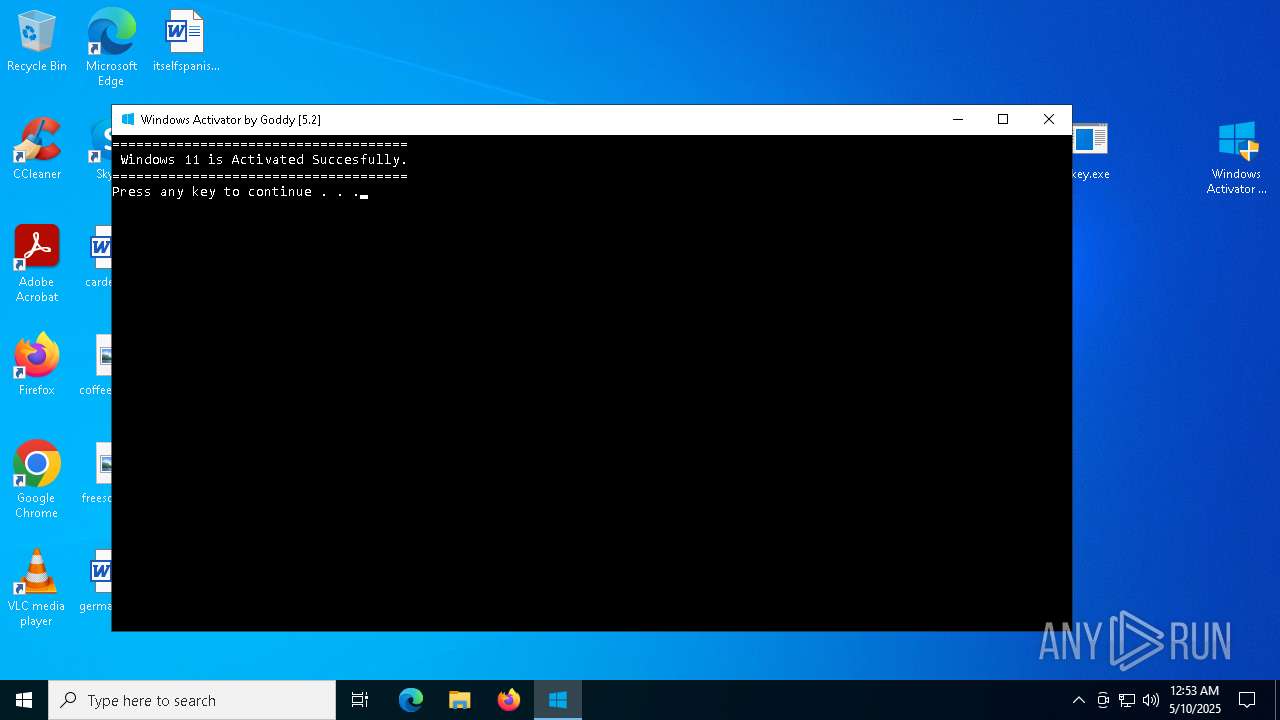
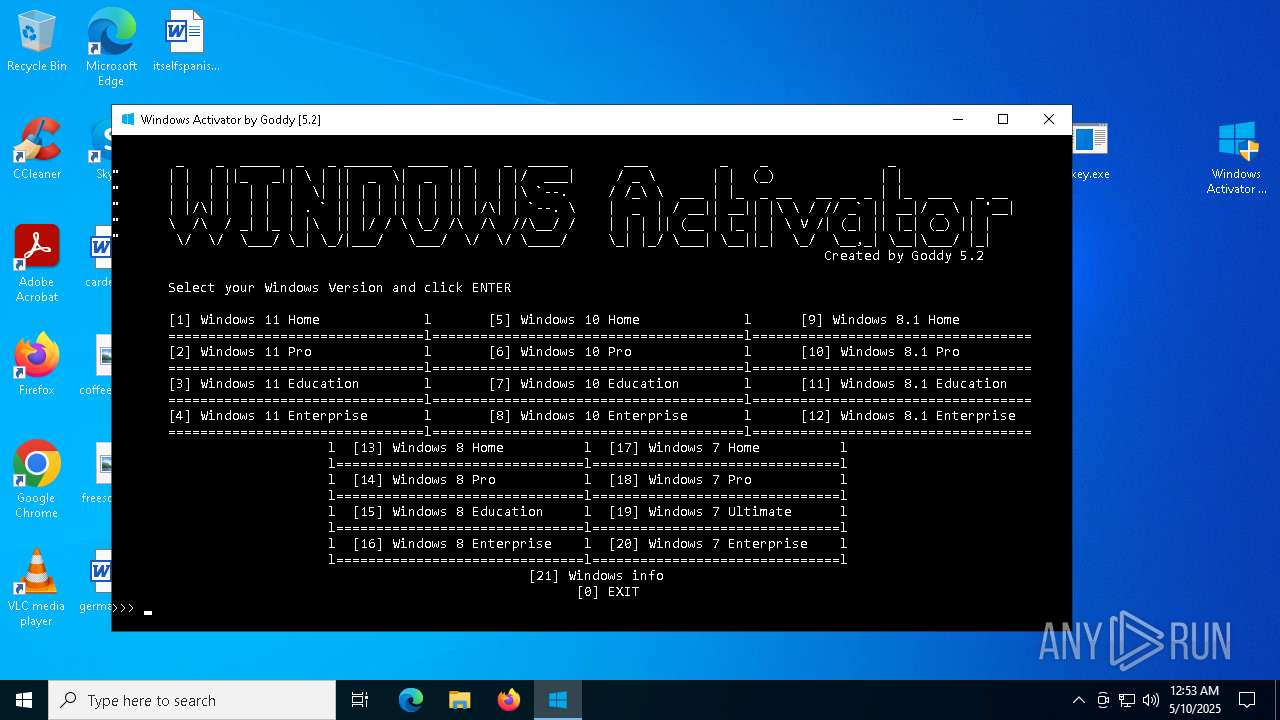
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 00:50:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BA2A45614BC3CF76AE4ECDFC252A7CF9 |
| SHA1: | 0AD6A35D697FC5EB0B38C931F4EE55592C098D57 |
| SHA256: | 0F3B675FCE7D3FDFFD40B681FEB833EFBACF56AA42D98A915E91340BDE514A4A |
| SSDEEP: | 3:N8cSAsGFMjKJSM1KSB0K35fRRP0n:2czs0pcM1KSB9fRR8n |
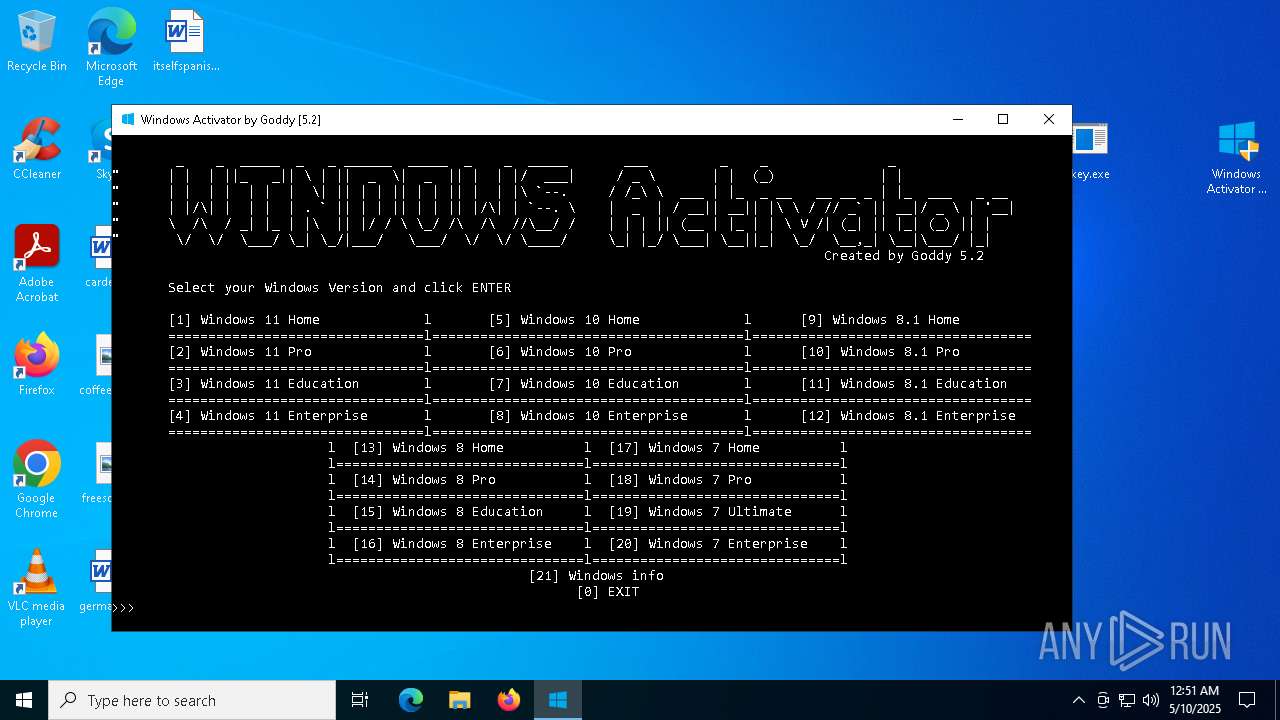
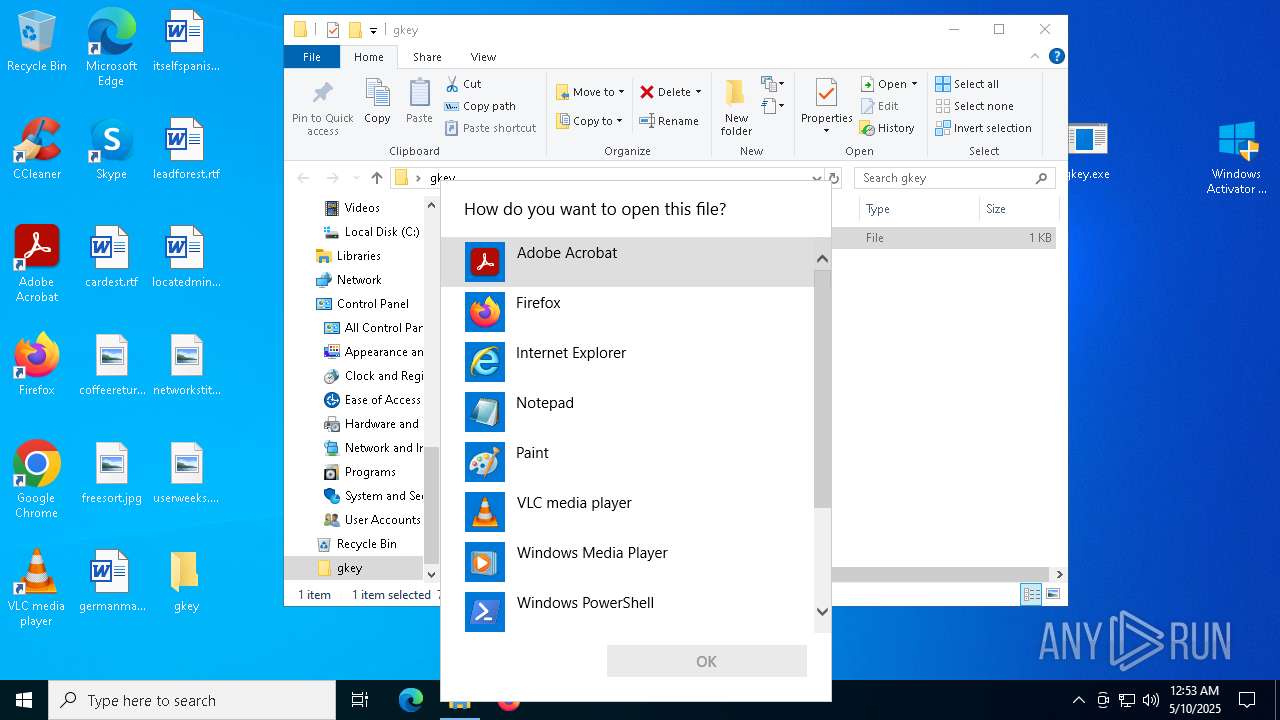
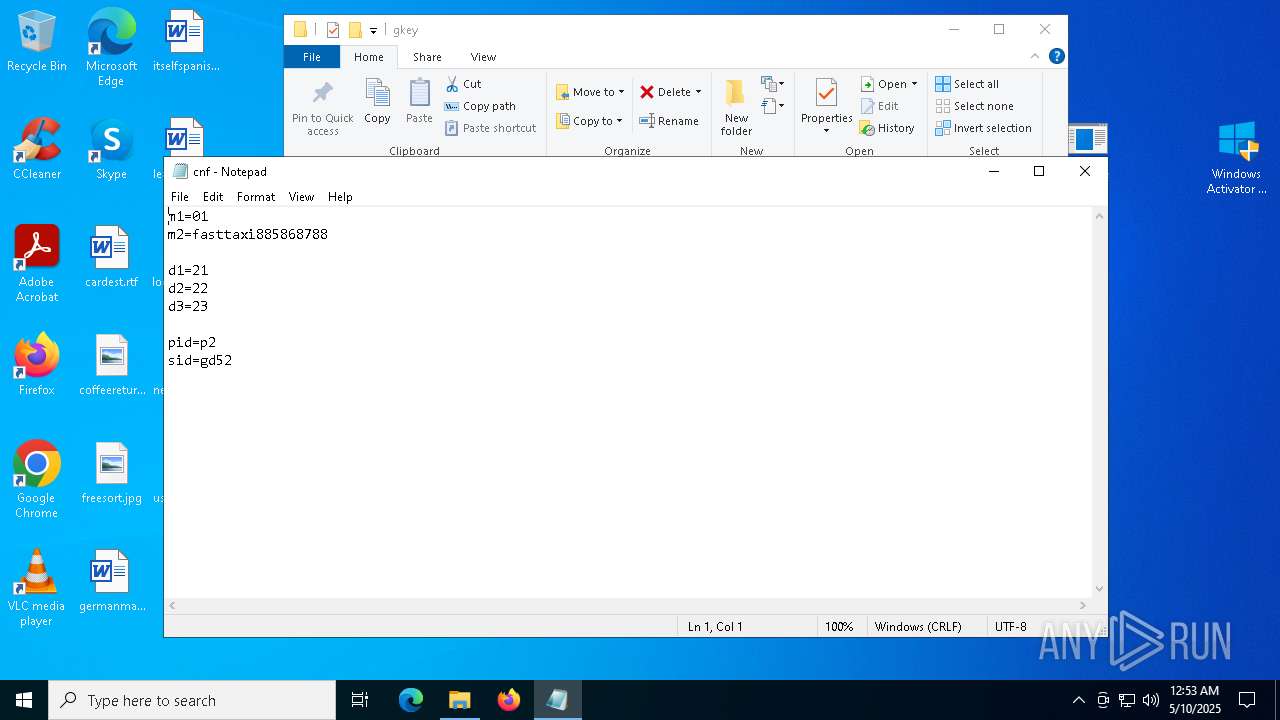
MALICIOUS
No malicious indicators.SUSPICIOUS
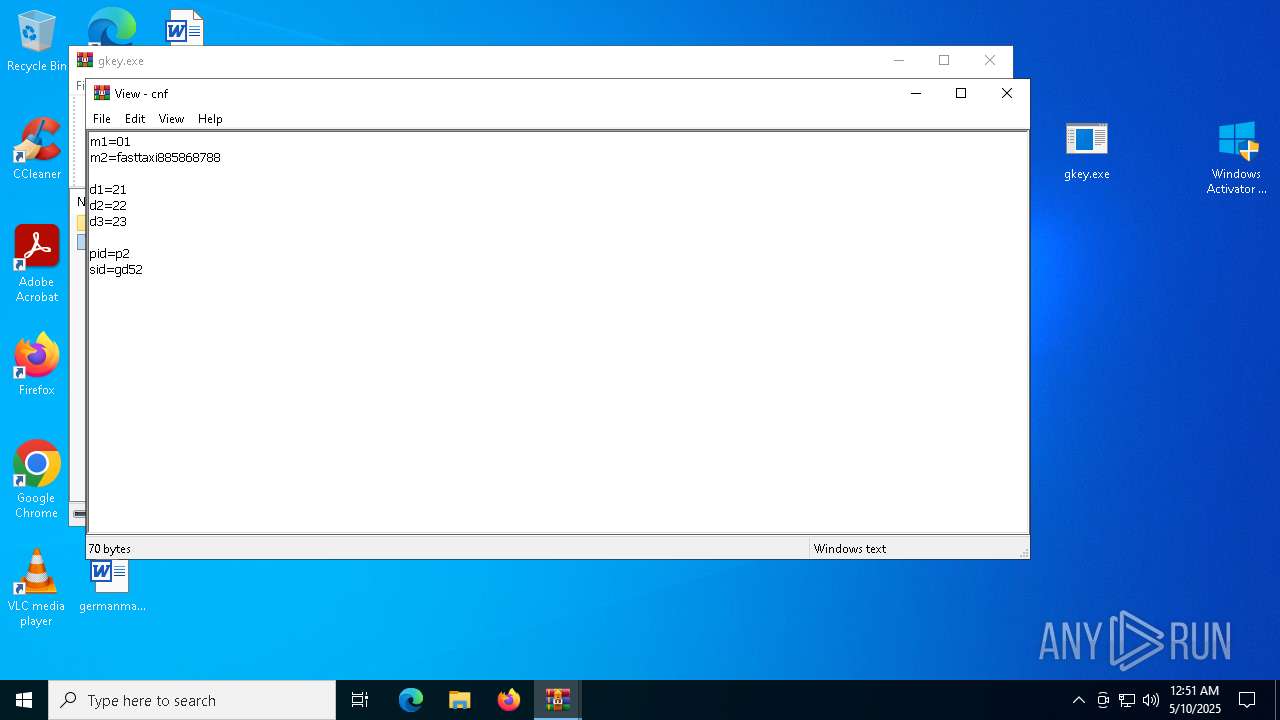
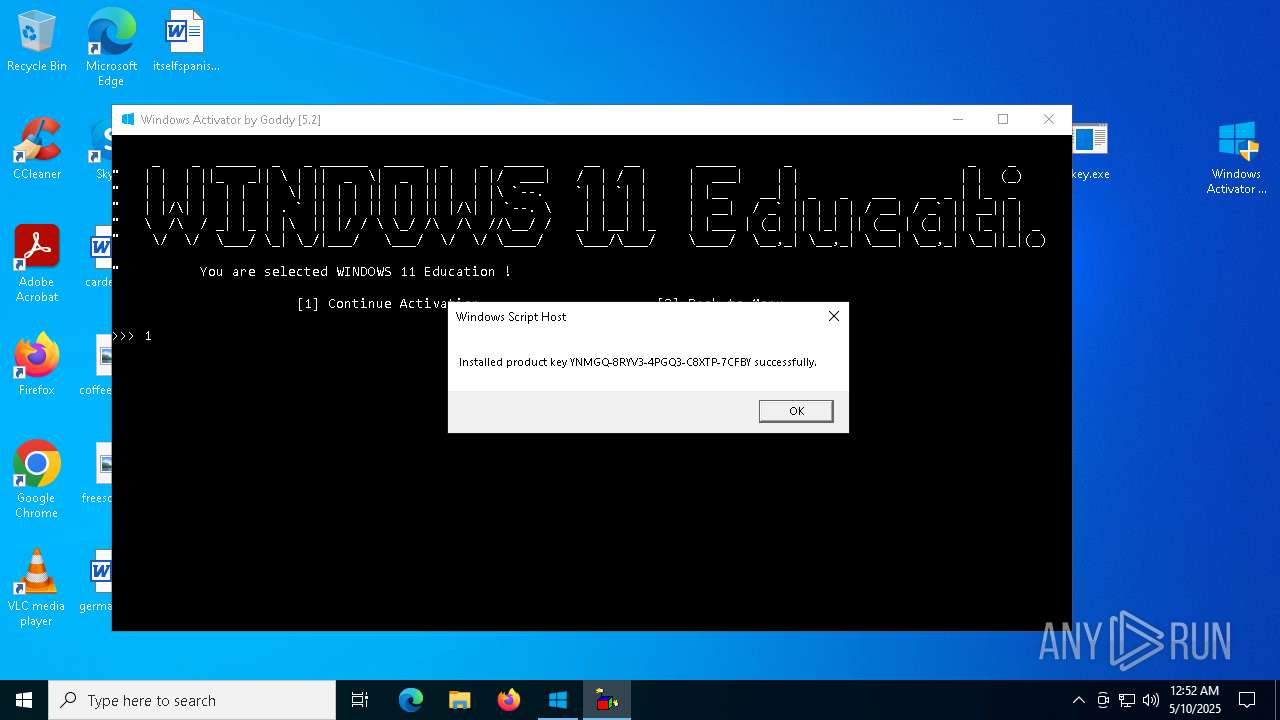
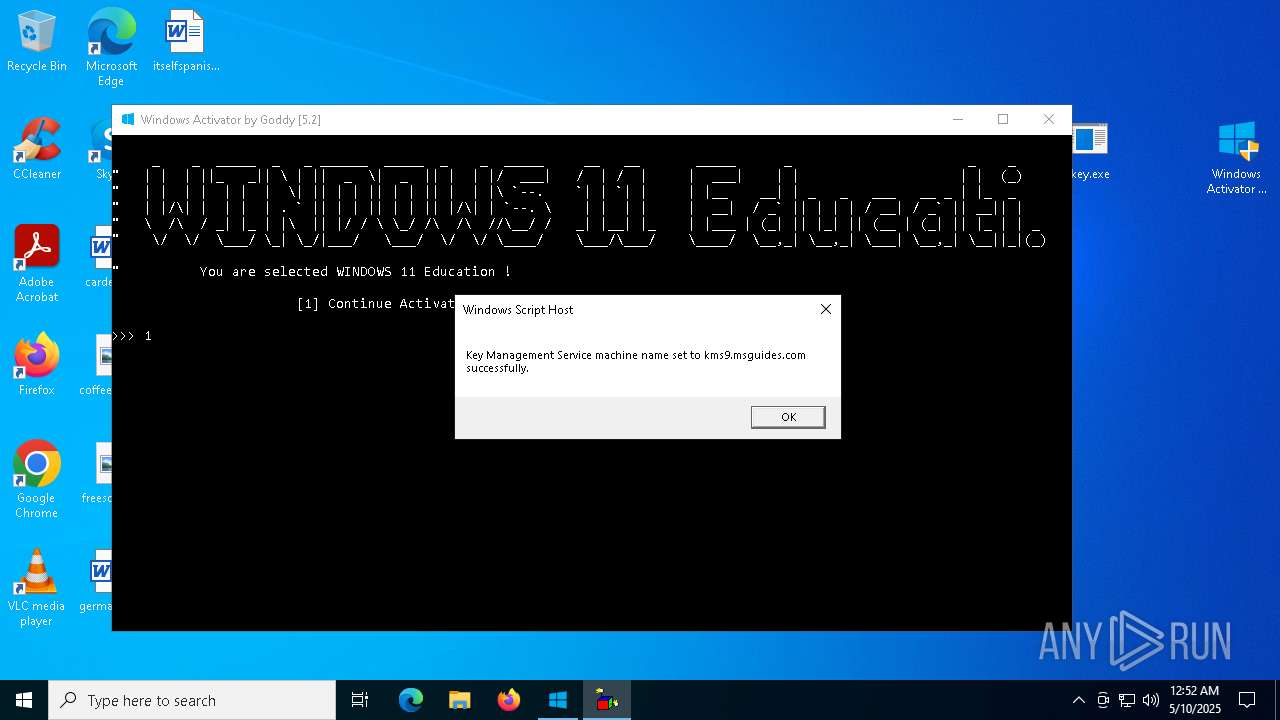
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7224)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7940)
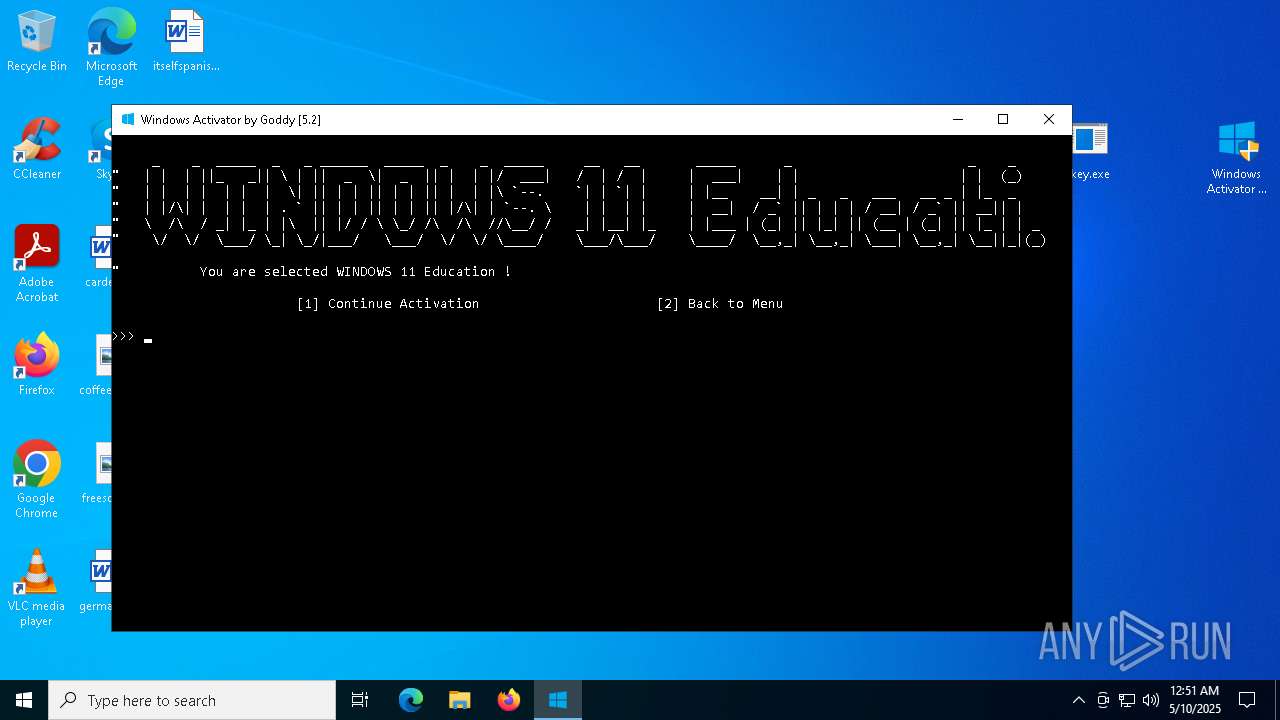
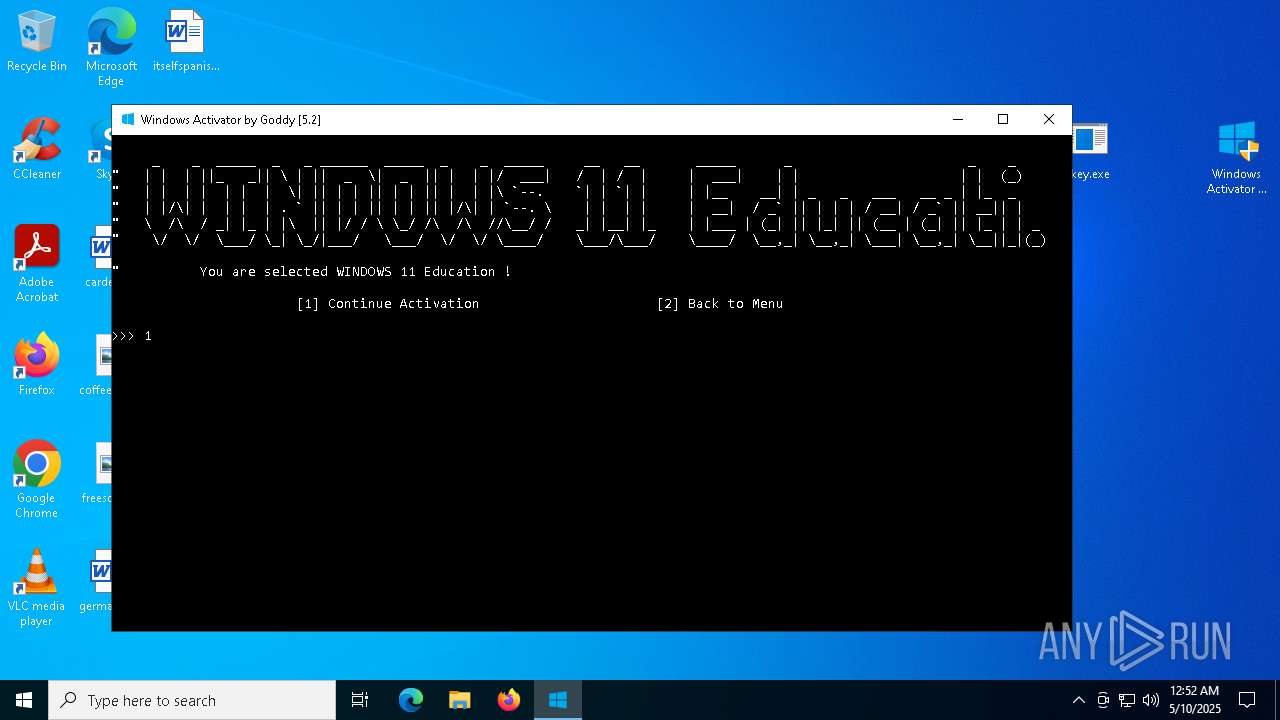
Starts CMD.EXE for commands execution
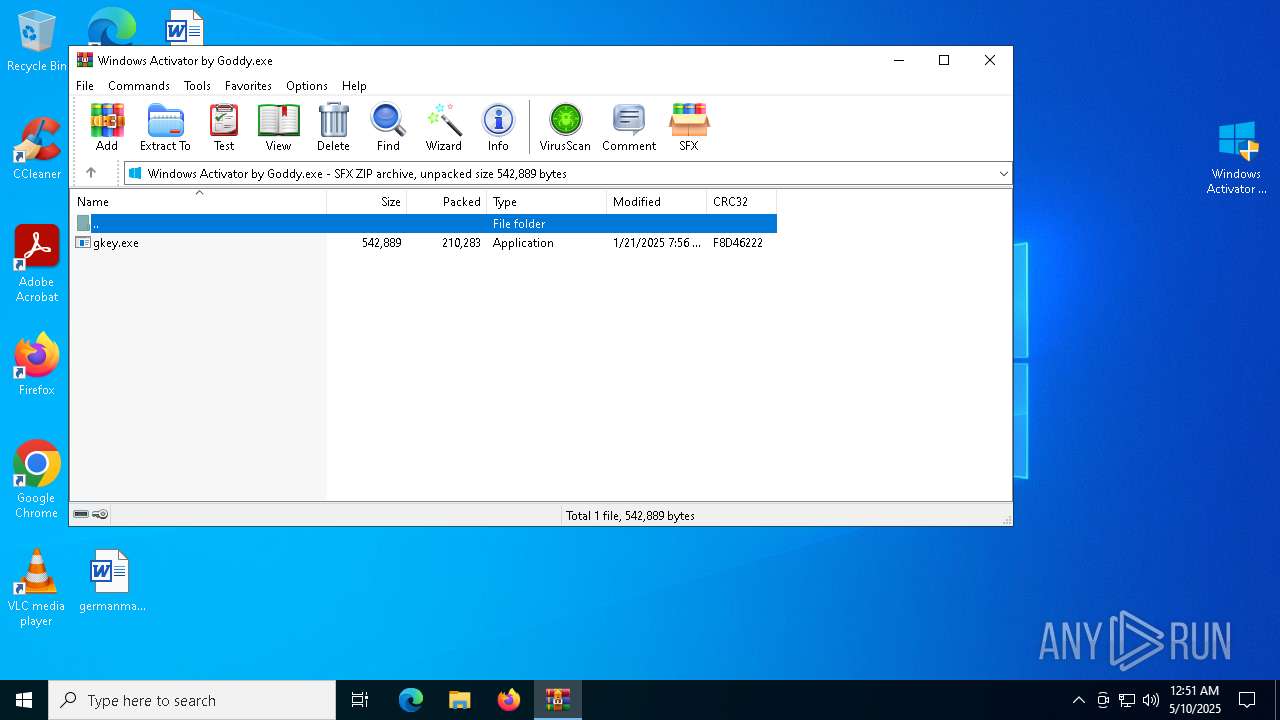
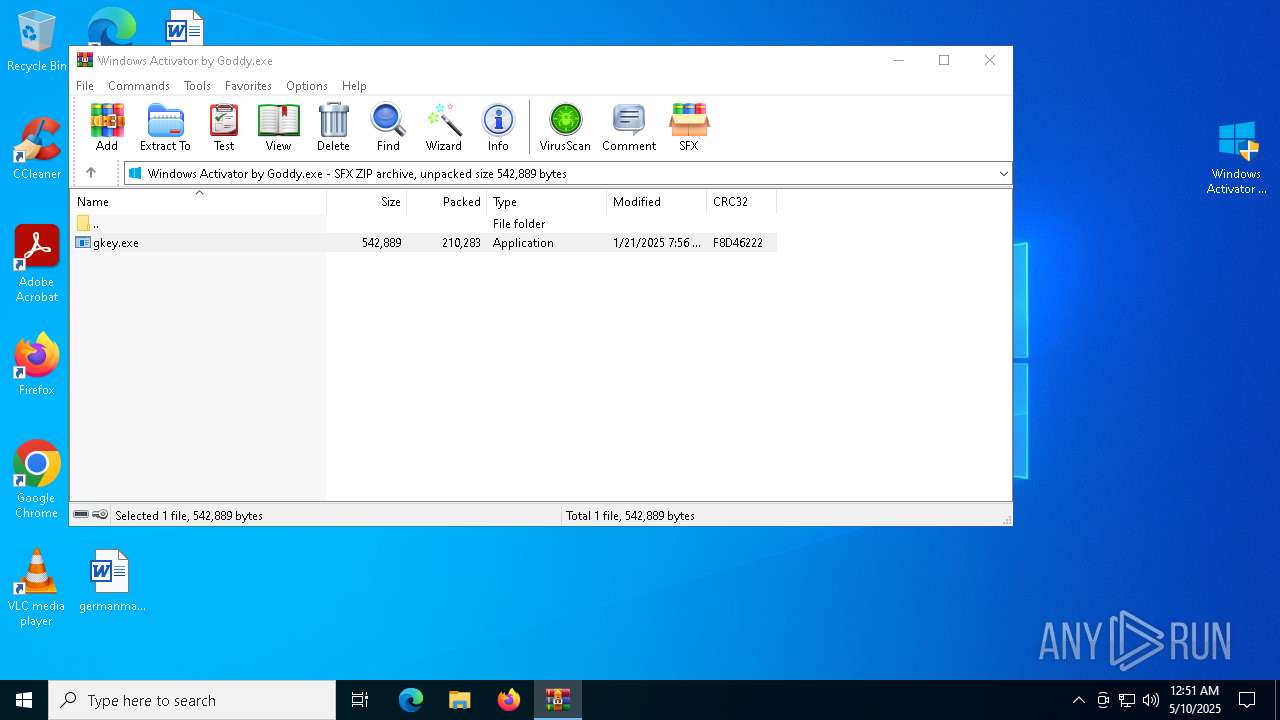
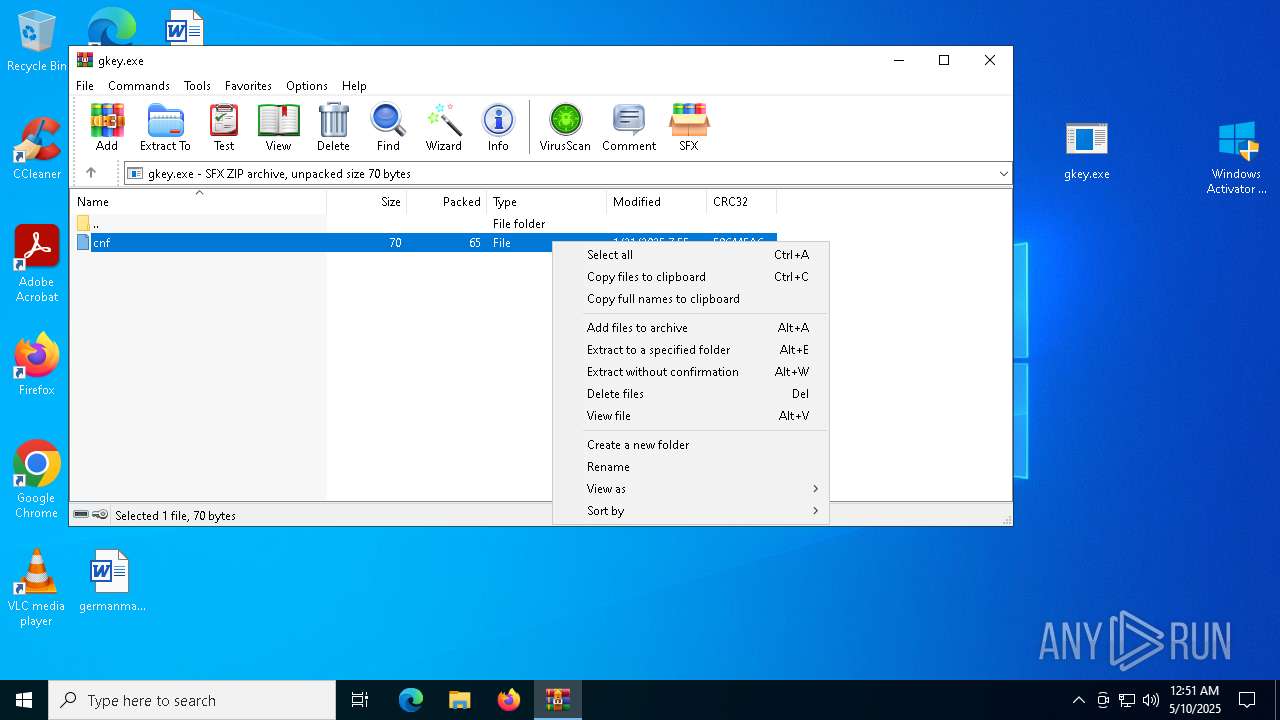
- Windows Activator by Goddy.exe (PID: 1672)
- gkey.exe (PID: 7176)
- cmd.exe (PID: 7224)
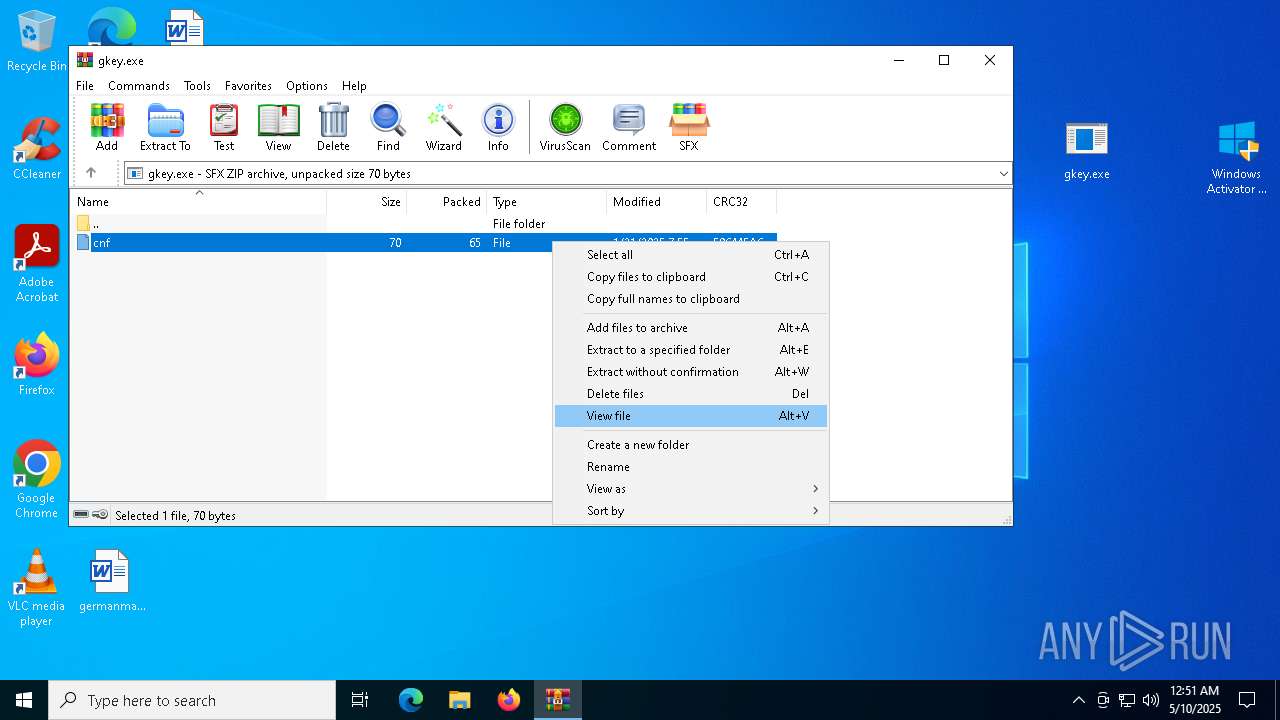
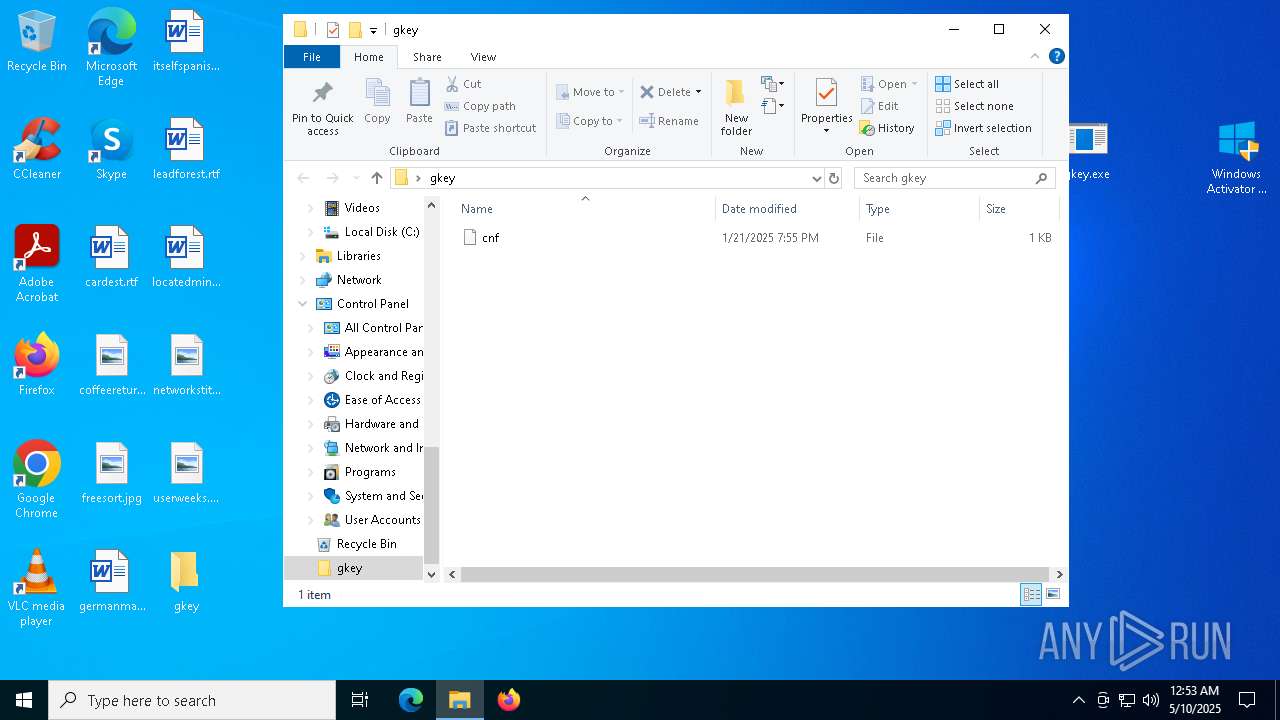
The executable file from the user directory is run by the CMD process
- gkey.exe (PID: 7176)
- 7z2201.exe (PID: 7608)
Executing commands from a ".bat" file
- gkey.exe (PID: 7176)
Starts NET.EXE to display or manage information about active sessions
- Windows Activator by Goddy.exe (PID: 1672)
- net.exe (PID: 7488)
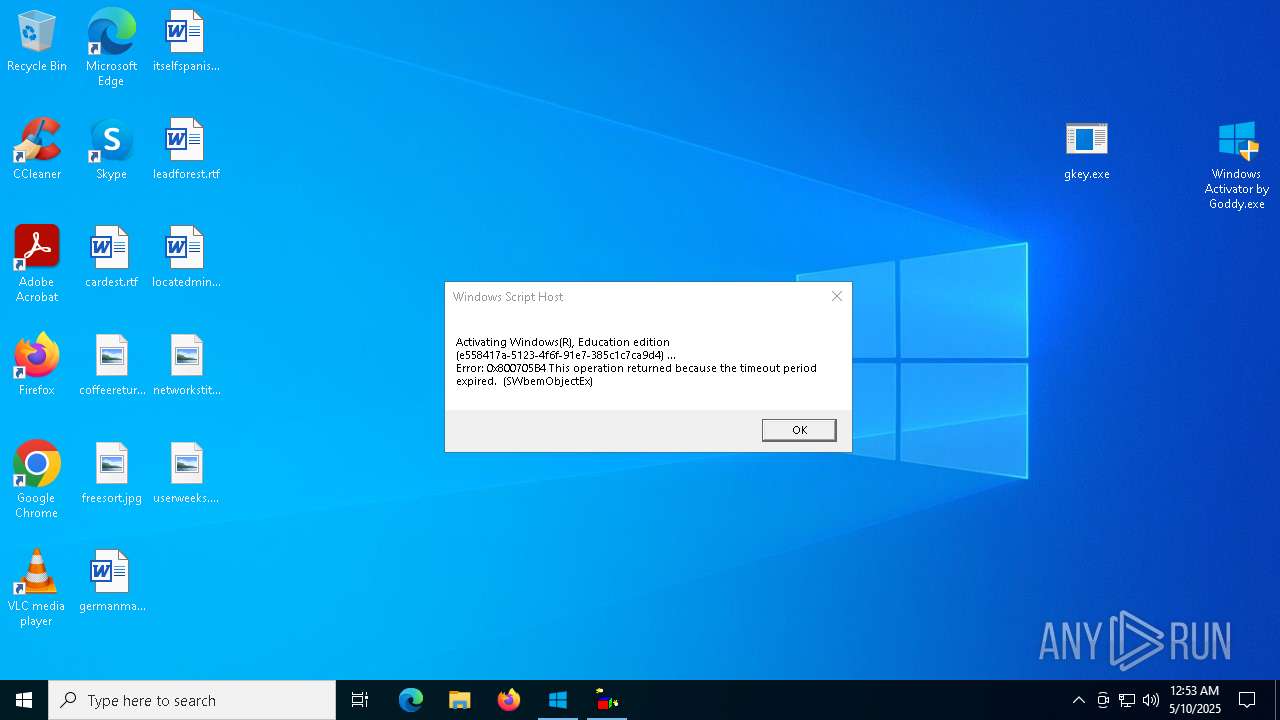
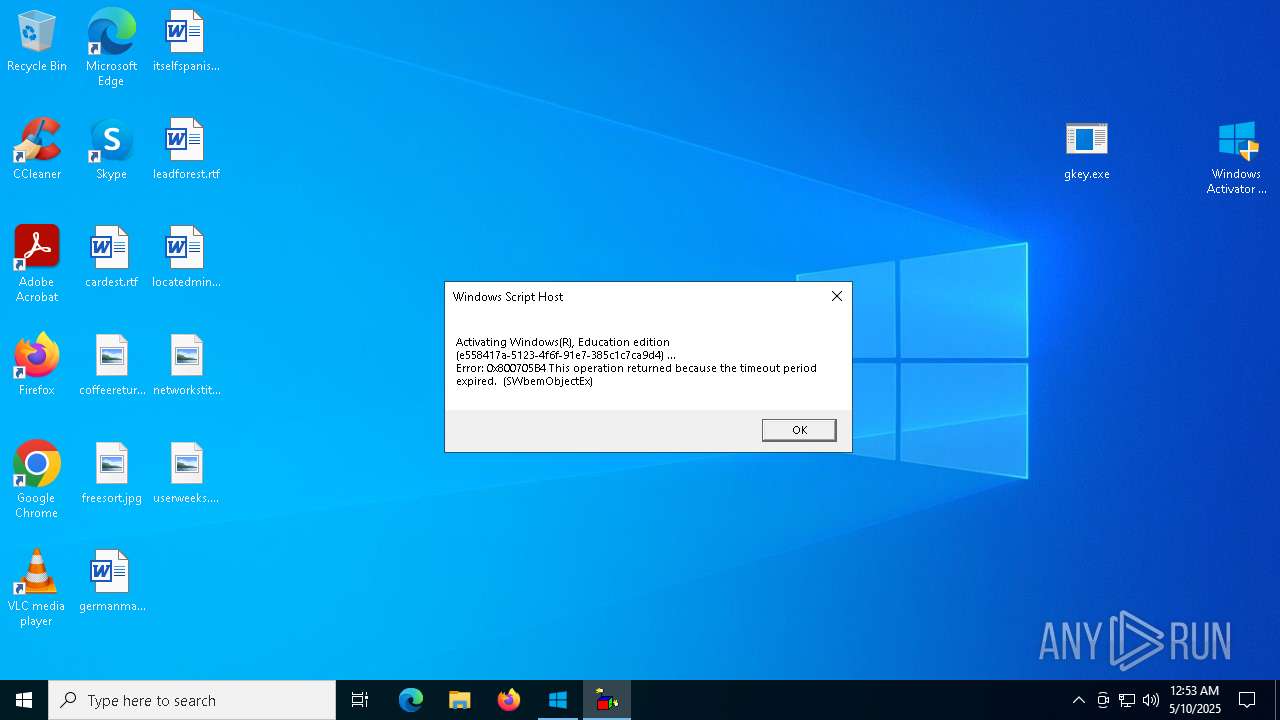
Uses WMIC.EXE
- cmd.exe (PID: 7960)
Get information on the list of running processes
- cmd.exe (PID: 7344)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 8128)
Checks for external IP
- curl.exe (PID: 7348)
- curl.exe (PID: 5132)
- svchost.exe (PID: 2196)
Execution of CURL command
- cmd.exe (PID: 7224)
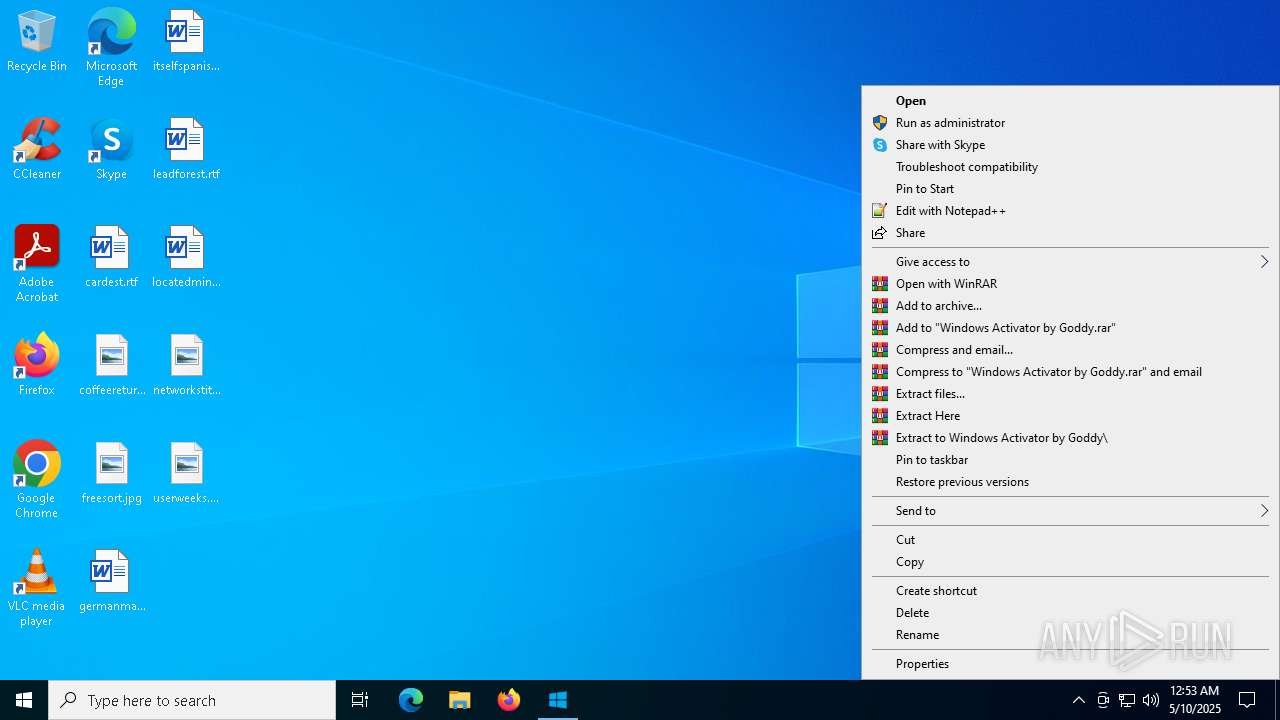
Executable content was dropped or overwritten
- curl.exe (PID: 2616)
- 7z2201.exe (PID: 7608)
Drops 7-zip archiver for unpacking
- curl.exe (PID: 2616)
- 7z2201.exe (PID: 7608)
The process executes VB scripts
- Windows Activator by Goddy.exe (PID: 1672)
Runs PING.EXE to delay simulation
- Windows Activator by Goddy.exe (PID: 1672)
Application launched itself
- cmd.exe (PID: 7224)
INFO
Reads Environment values
- identity_helper.exe (PID: 6248)
- identity_helper.exe (PID: 6576)
Application launched itself
- msedge.exe (PID: 7020)
- msedge.exe (PID: 8164)
Reads the computer name
- identity_helper.exe (PID: 6248)
- identity_helper.exe (PID: 6576)
Checks supported languages
- identity_helper.exe (PID: 6248)
- identity_helper.exe (PID: 6576)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7020)
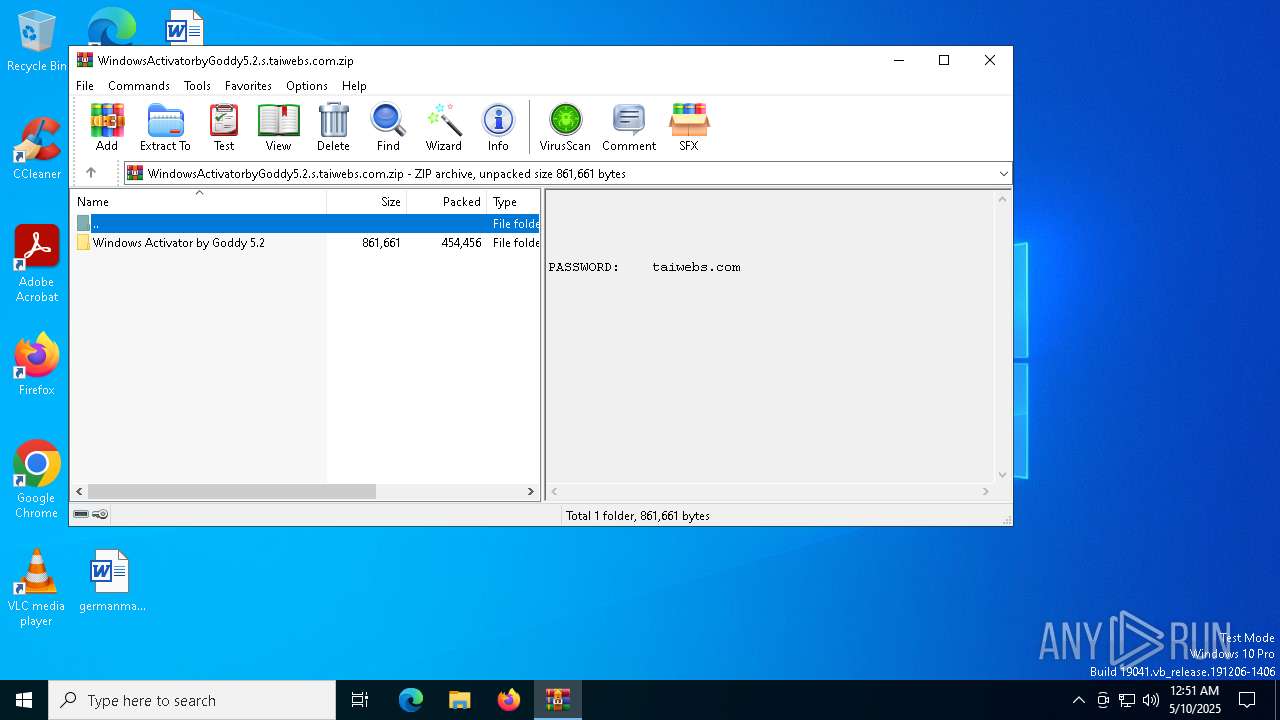
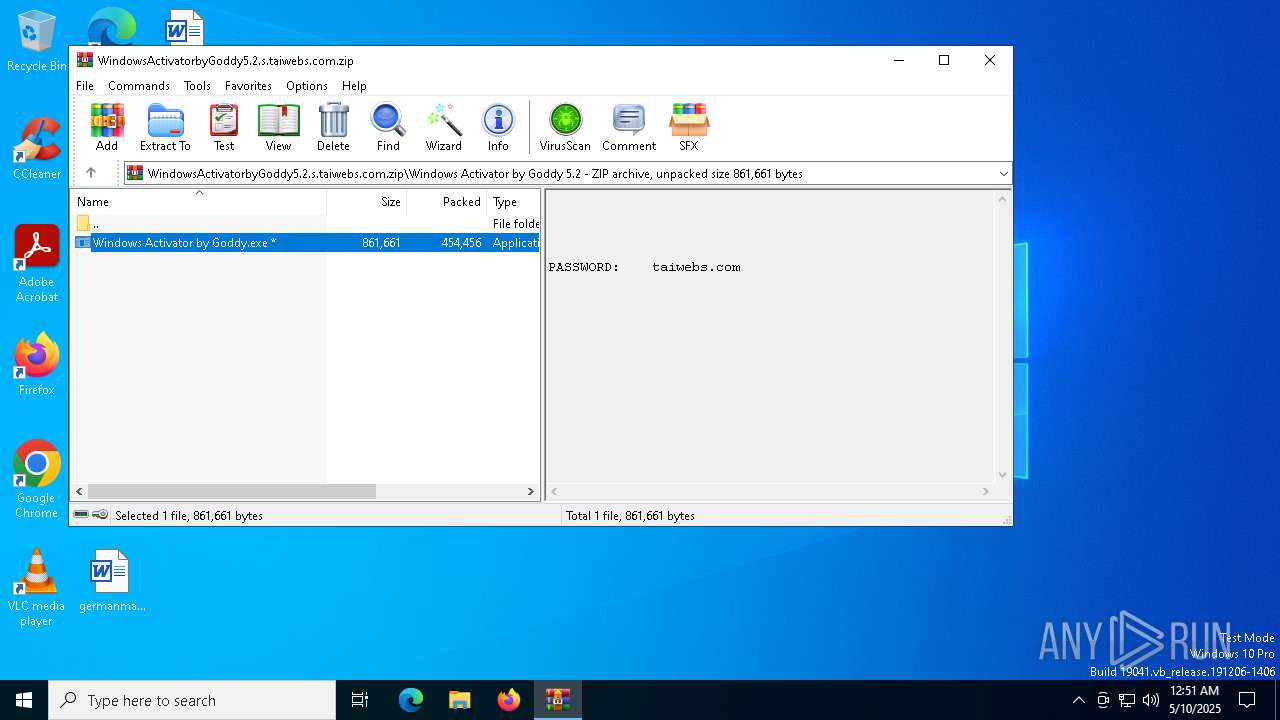
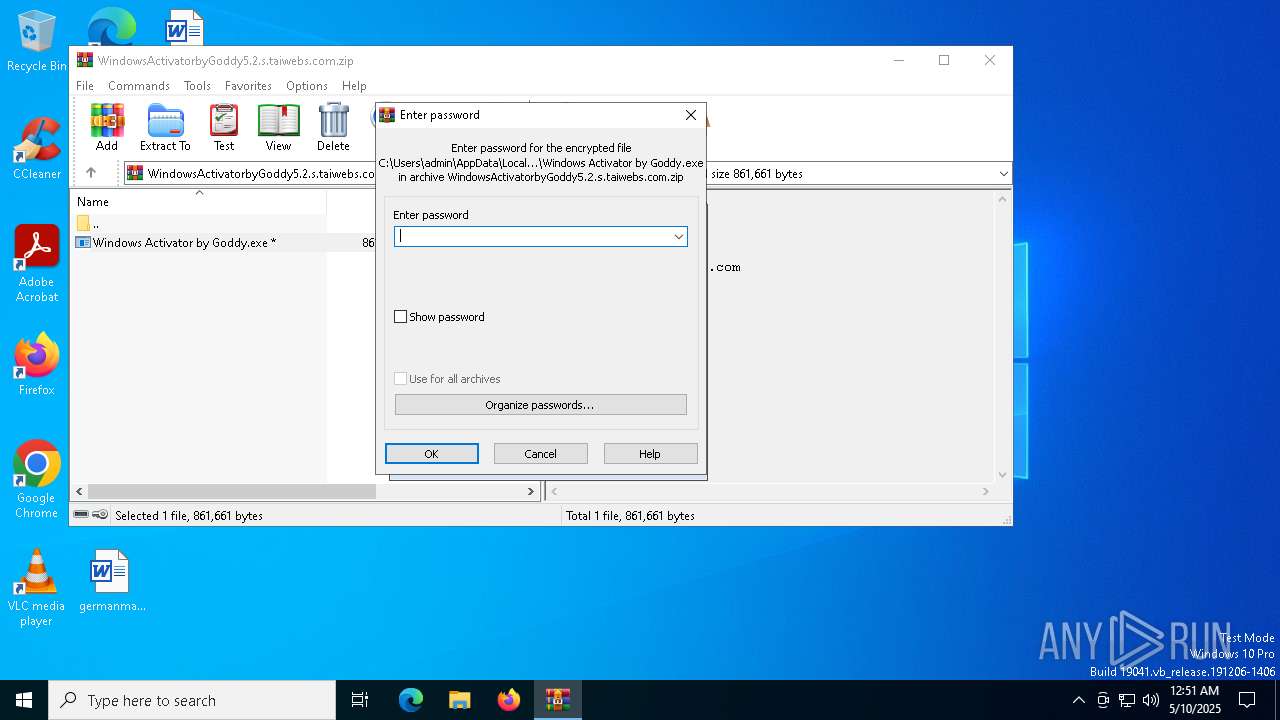
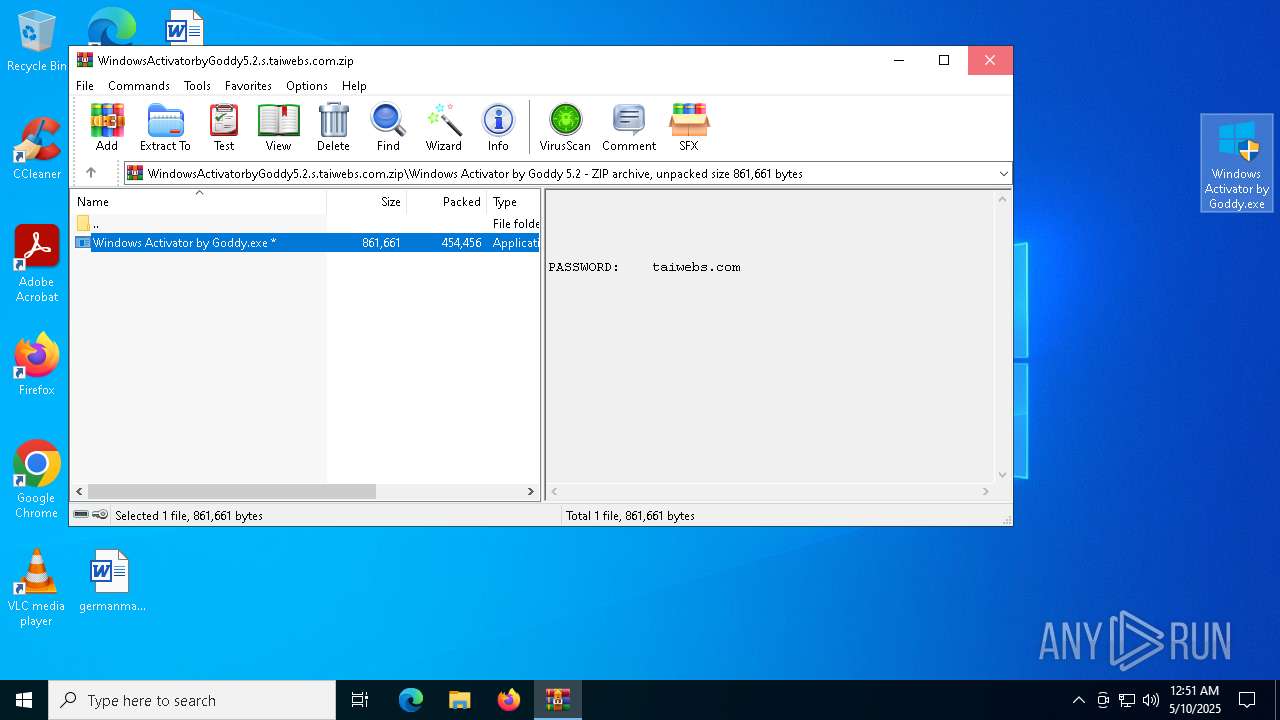
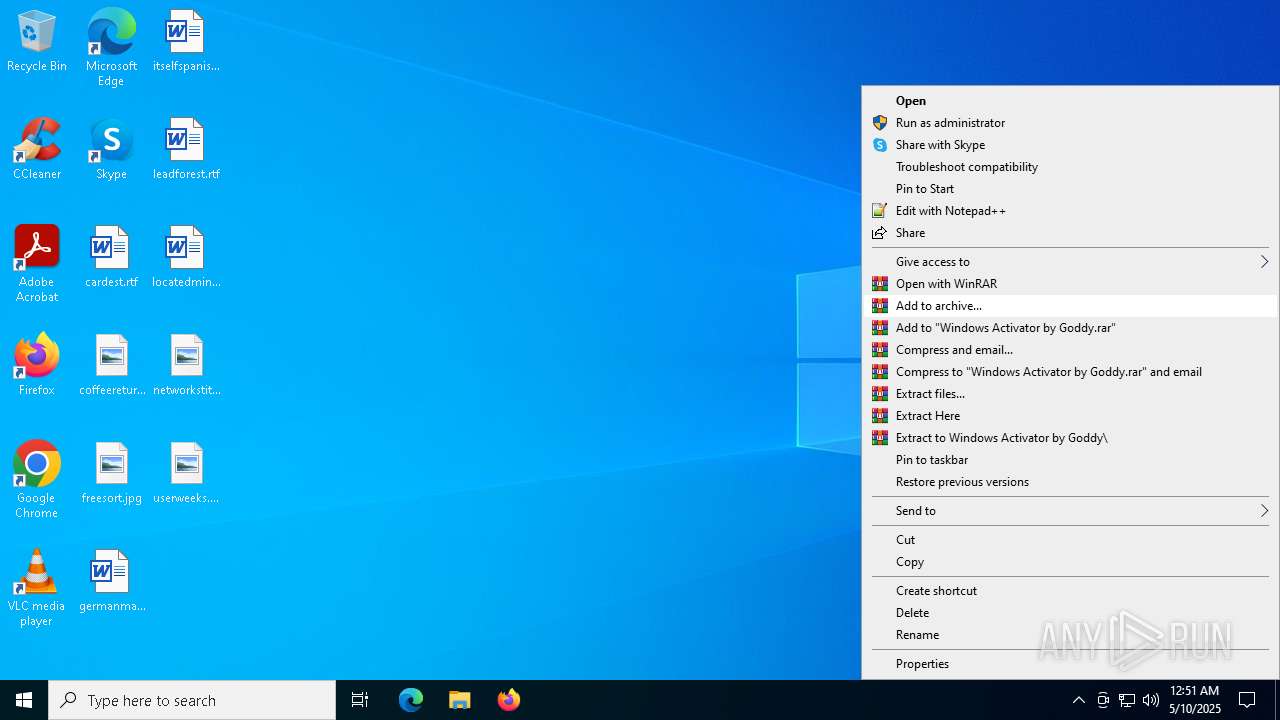
Manual execution by a user
- WinRAR.exe (PID: 7324)
- WinRAR.exe (PID: 7940)
- Windows Activator by Goddy.exe (PID: 5384)
- Windows Activator by Goddy.exe (PID: 1672)
- WinRAR.exe (PID: 4112)
Starts MODE.COM to configure console settings
- mode.com (PID: 5548)
Execution of CURL command
- cmd.exe (PID: 744)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7224)
Checks operating system version
- cmd.exe (PID: 7224)
The sample compiled with english language support
- curl.exe (PID: 2616)
- 7z2201.exe (PID: 7608)
The sample compiled with russian language support
- 7z2201.exe (PID: 7608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
264
Monitored processes
126
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6408 --field-trial-handle=2372,i,11440536832275381178,17892937549476164399,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /S /D /c" ver " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7756 --field-trial-handle=2372,i,11440536832275381178,17892937549476164399,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=7672 --field-trial-handle=2372,i,11440536832275381178,17892937549476164399,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2748 --field-trial-handle=2364,i,8271860486141099978,10123276855737834142,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | C:\WINDOWS\system32\cmd.exe /c curl https://ipinfo.io/country -k | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7360 --field-trial-handle=2372,i,11440536832275381178,17892937549476164399,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=7704 --field-trial-handle=2372,i,11440536832275381178,17892937549476164399,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x30c,0x310,0x314,0x308,0x254,0x7ffc87fc5fd8,0x7ffc87fc5fe4,0x7ffc87fc5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6292 --field-trial-handle=2372,i,11440536832275381178,17892937549476164399,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
19 383
Read events
19 253
Write events
130
Delete events
0
Modification events
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A77043C153932F00 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 17AD58C153932F00 | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A81DF53F-F0D9-4ED1-B2D6-3362E46FD05A} | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {966D648E-6D9E-4728-AB11-6FF5C099DF30} | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {962D36CD-840D-4CB8-B7A2-2CEB6148035E} | |||
| (PID) Process: | (7020) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CE31D80E-927B-4074-A99F-94BC1E131712} | |||
Executable files
37
Suspicious files
656
Text files
216
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10cbae.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10cbae.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10cbae.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10cbae.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10cbed.TMP | — | |
MD5:— | SHA256:— | |||
| 7020 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
230
DNS requests
266
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2416 | svchost.exe | HEAD | 200 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
2416 | svchost.exe | GET | 206 | 23.44.215.49:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/171c624f-5058-42bd-933b-dc1bbb19e661?P1=1747407517&P2=404&P3=2&P4=jRCgWPfqNfO2Kqk6Cy6nao17%2fjDUi%2bxJhdnZilX%2bTcUdObnzplDx%2fqap4tL7%2fB%2bseY8qCm5sI9BWRQv2r7NaYg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7020 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7212 | msedge.exe | 188.114.96.3:443 | en.taiwebs.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
en.taiwebs.com |
| unknown |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |