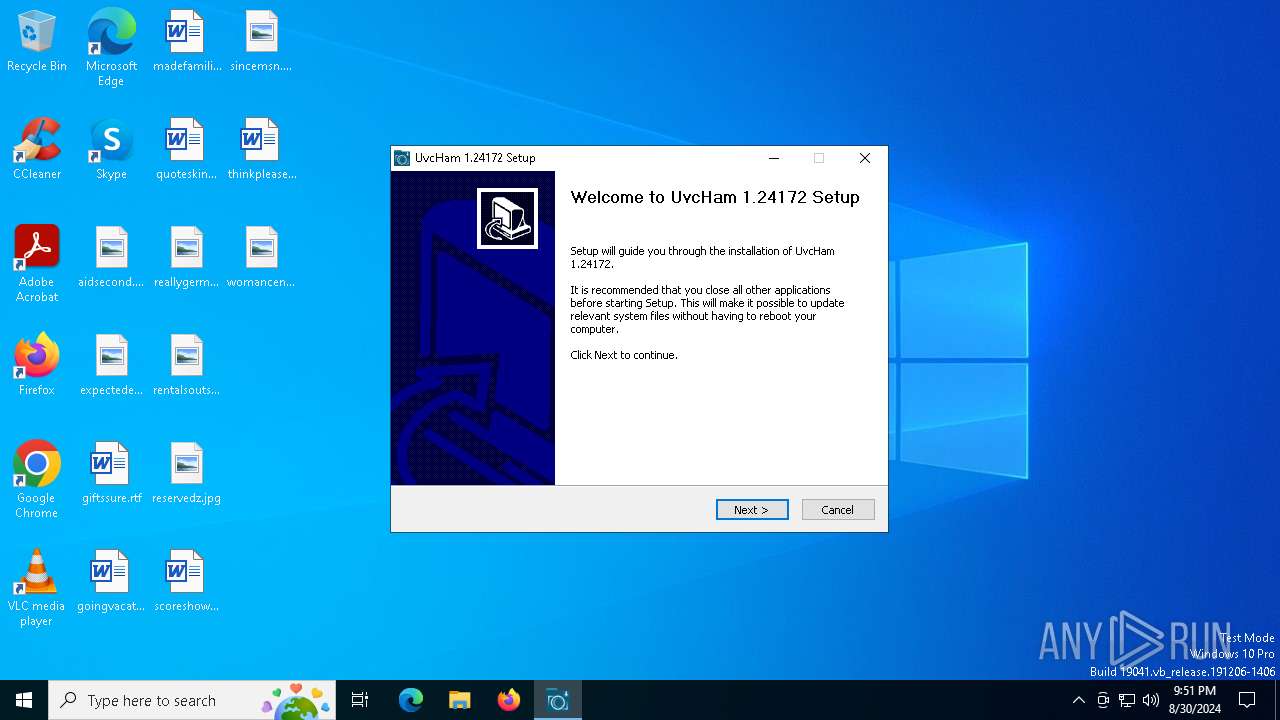
| File name: | UvcHamSetup.exe |
| Full analysis: | https://app.any.run/tasks/34978075-0466-44e5-9189-06cc2d4cb6ef |
| Verdict: | Malicious activity |
| Analysis date: | August 30, 2024, 21:50:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 697BB883AE72586679BD6F1D2BD74D67 |
| SHA1: | 14910844418759B480BDB70C1CB4728AAF175566 |
| SHA256: | 0F33406947EFA9E06CA57D9DEB4D541F093C1DC59BBC838A1B9021842033C771 |
| SSDEEP: | 98304:mvXj7cgjsyIFVJZ+SWN0nQHjM7IMPfiFx452Ce6FztwrMM9OpsDx20khz5sJrfEL:FqWjN |
MALICIOUS
Starts NET.EXE for service management
- UvcHamSetup.exe (PID: 7040)
- net.exe (PID: 6148)
- net.exe (PID: 1292)
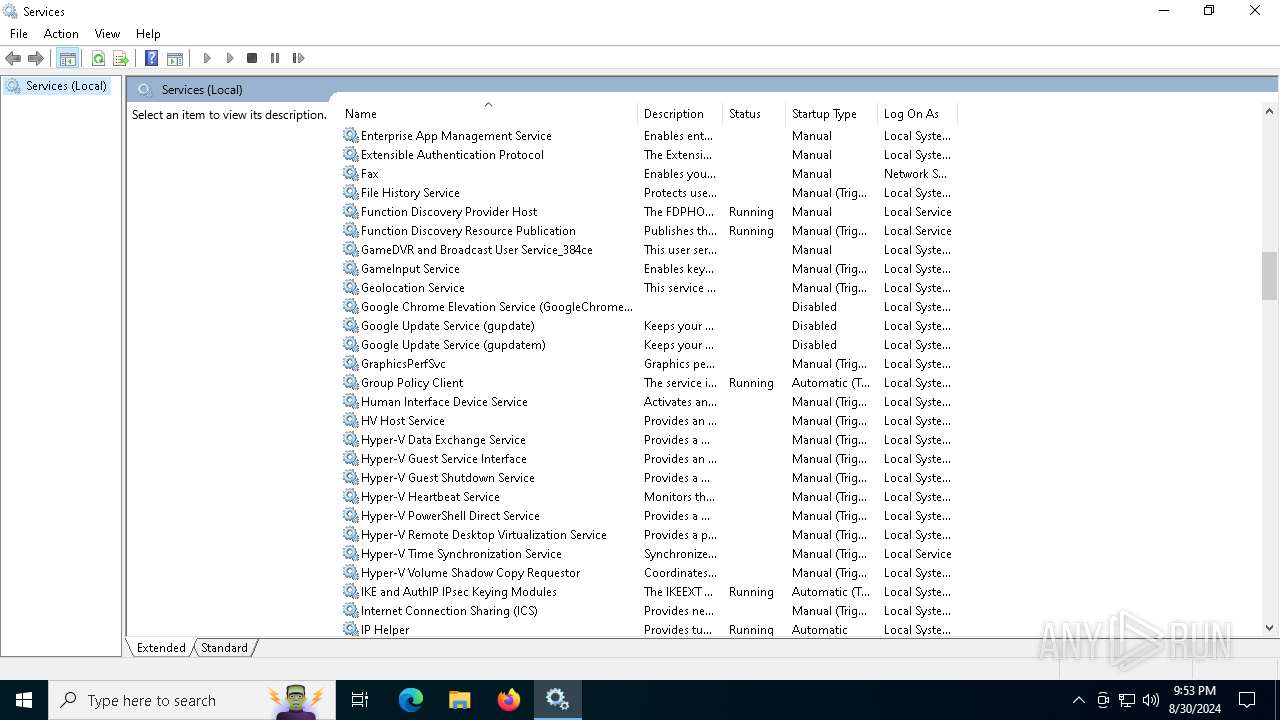
Registers / Runs the DLL via REGSVR32.EXE
- UvcHamSetup.exe (PID: 7040)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- UvcHamSetup.exe (PID: 7040)
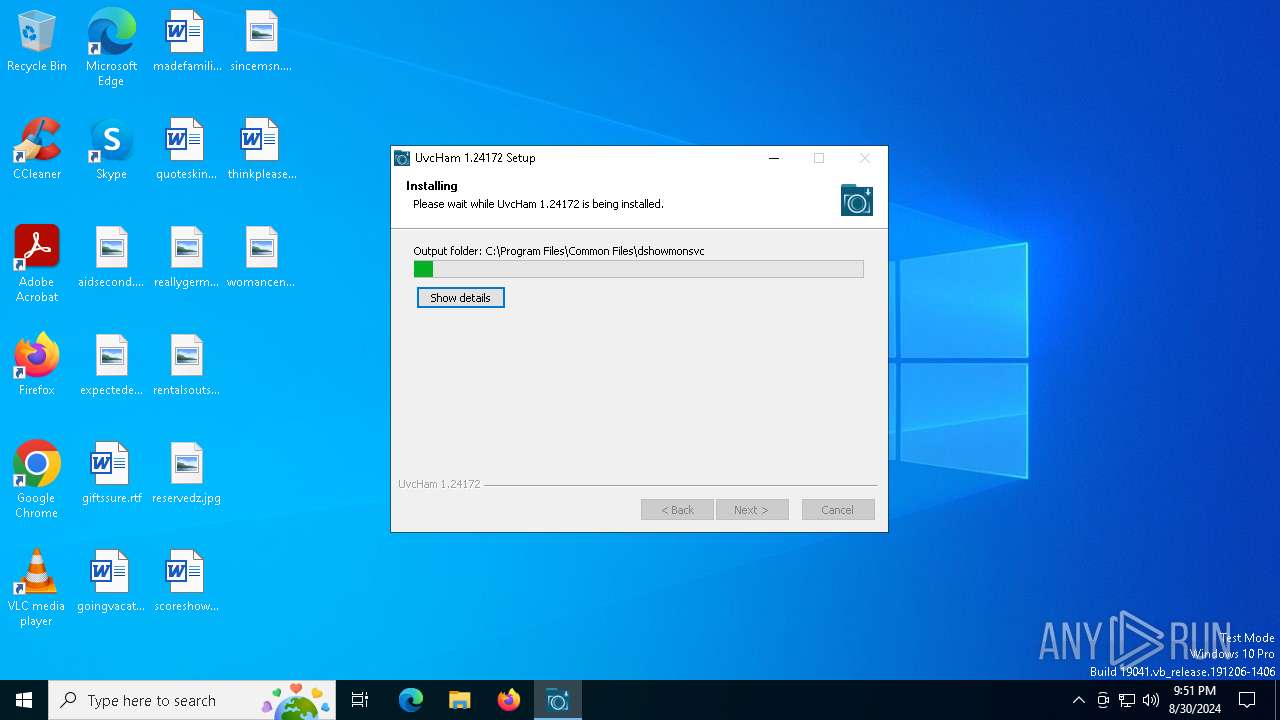
Drops the executable file immediately after the start
- UvcHamSetup.exe (PID: 7040)
The process creates files with name similar to system file names
- UvcHamSetup.exe (PID: 7040)
Executable content was dropped or overwritten
- UvcHamSetup.exe (PID: 7040)
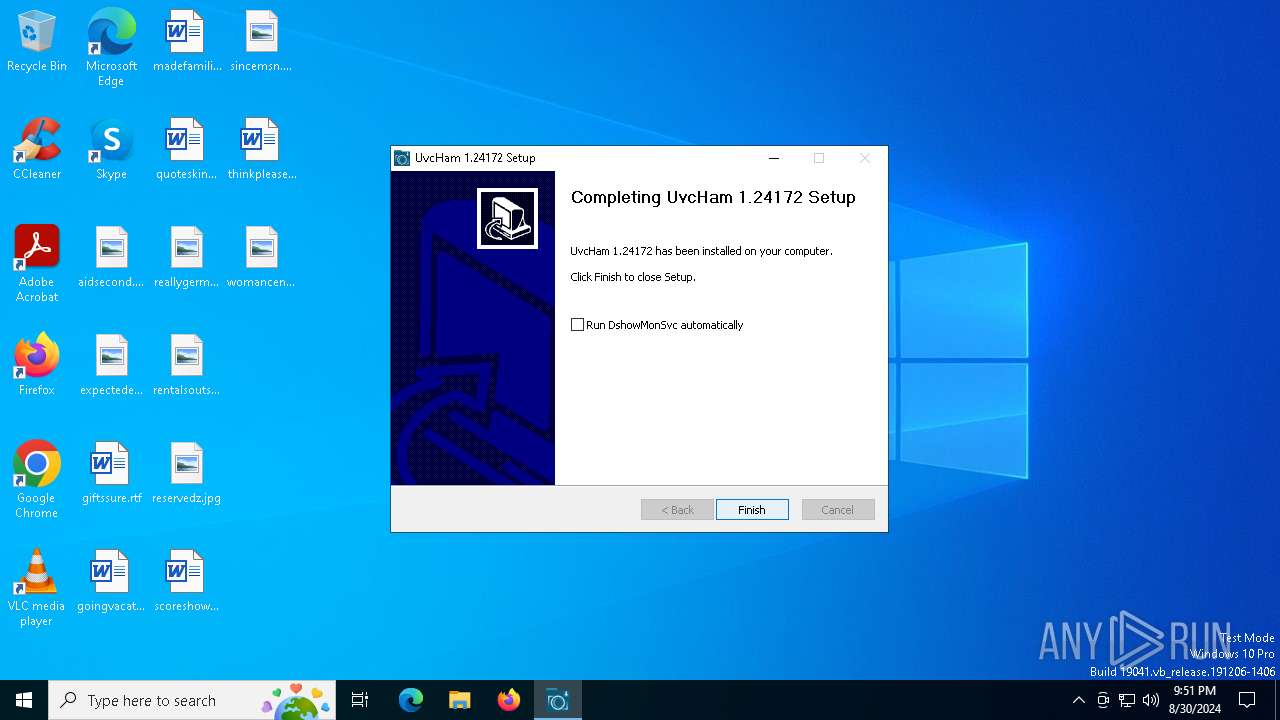
Creates a software uninstall entry
- UvcHamSetup.exe (PID: 7040)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2224)
- regsvr32.exe (PID: 6964)
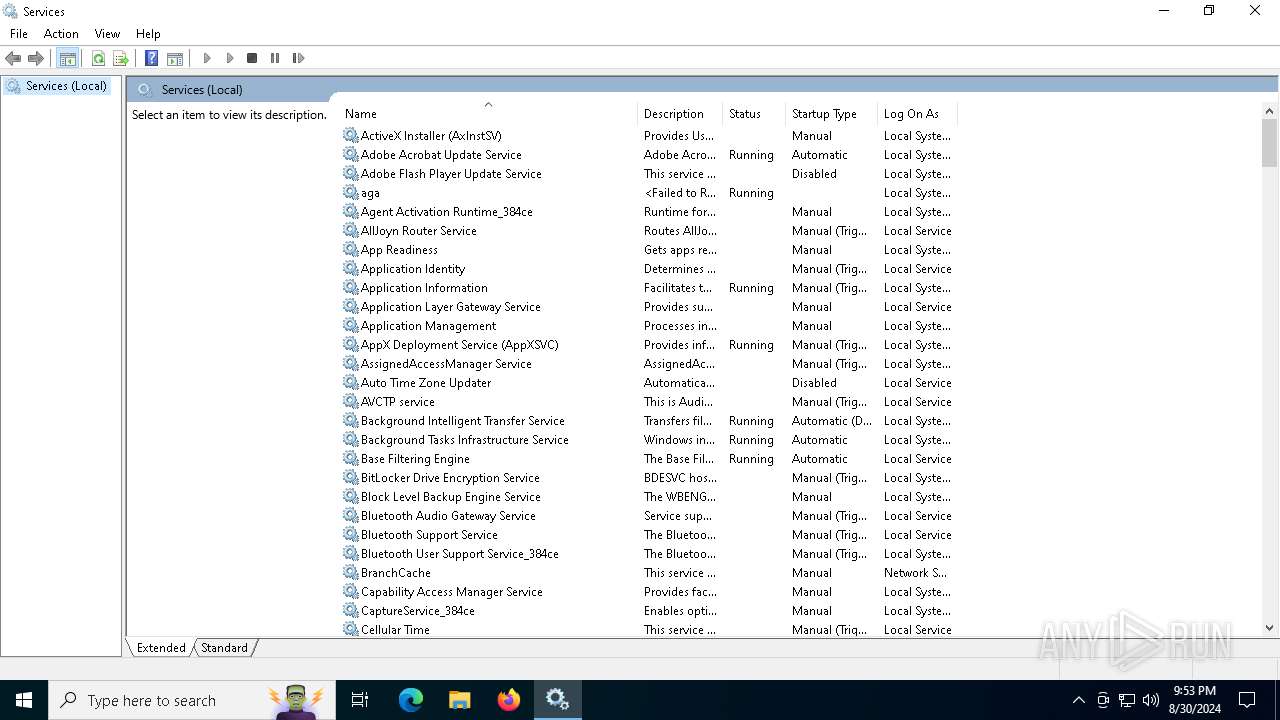
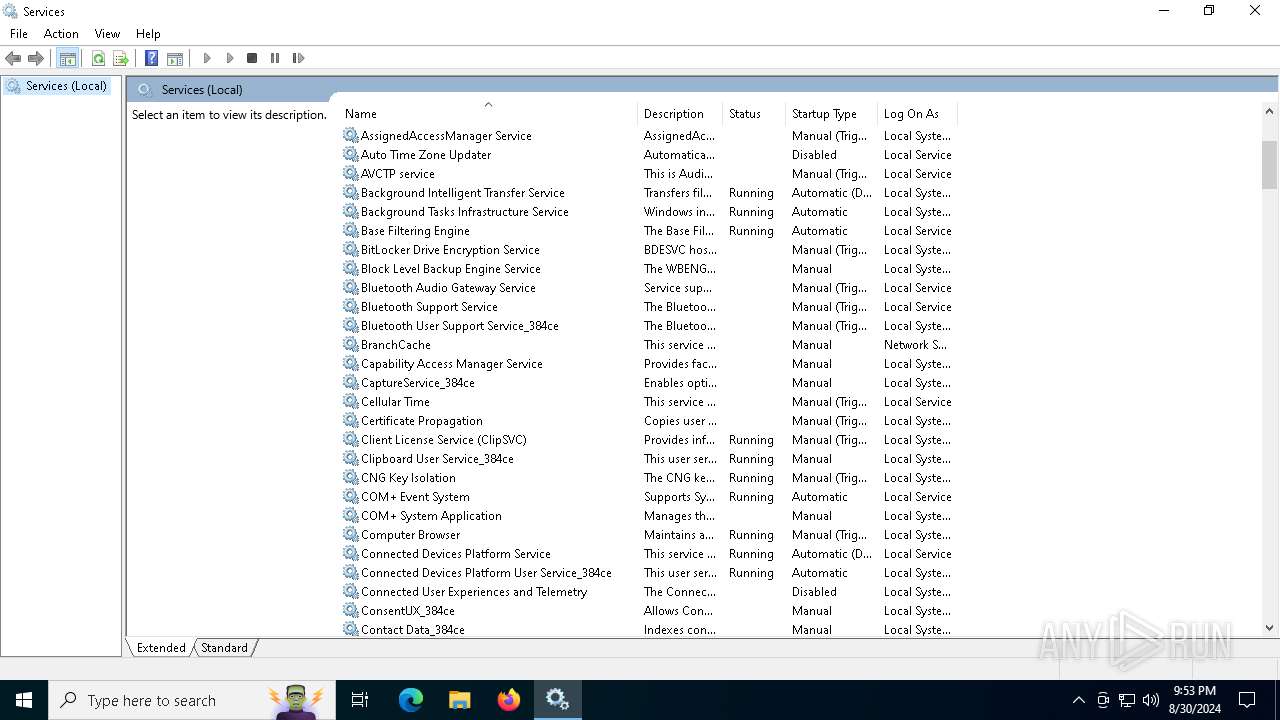
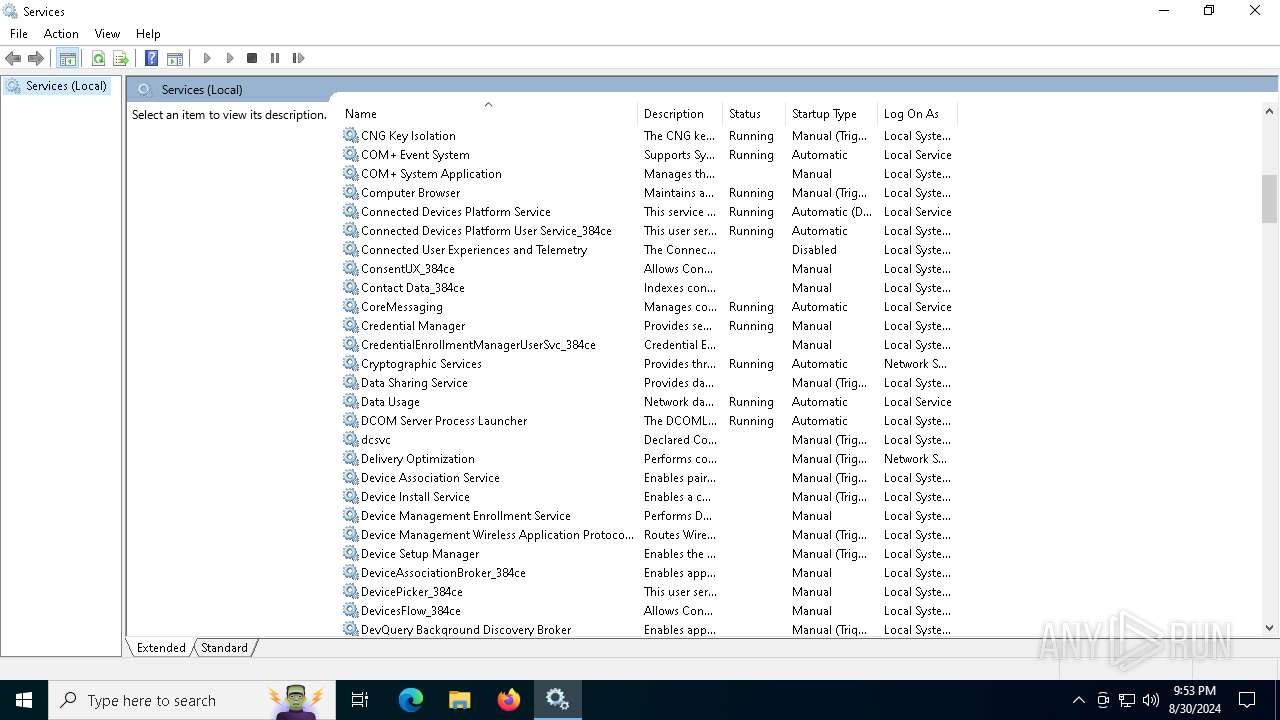
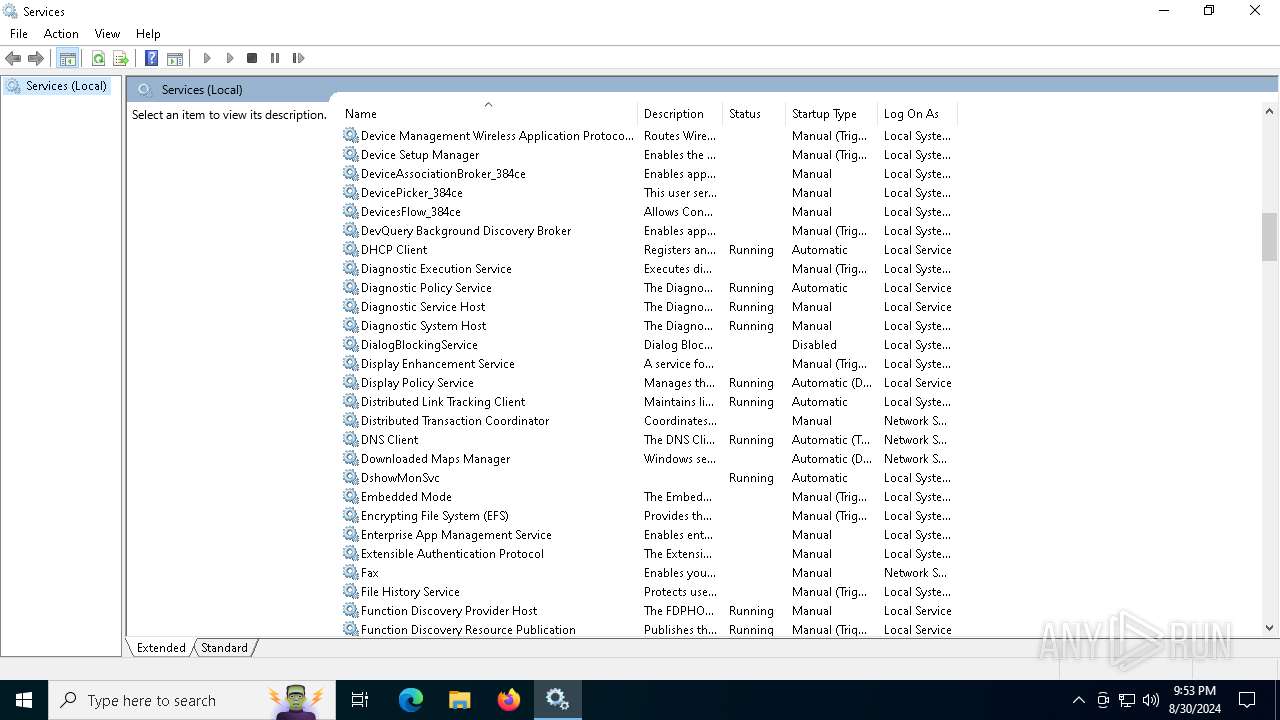
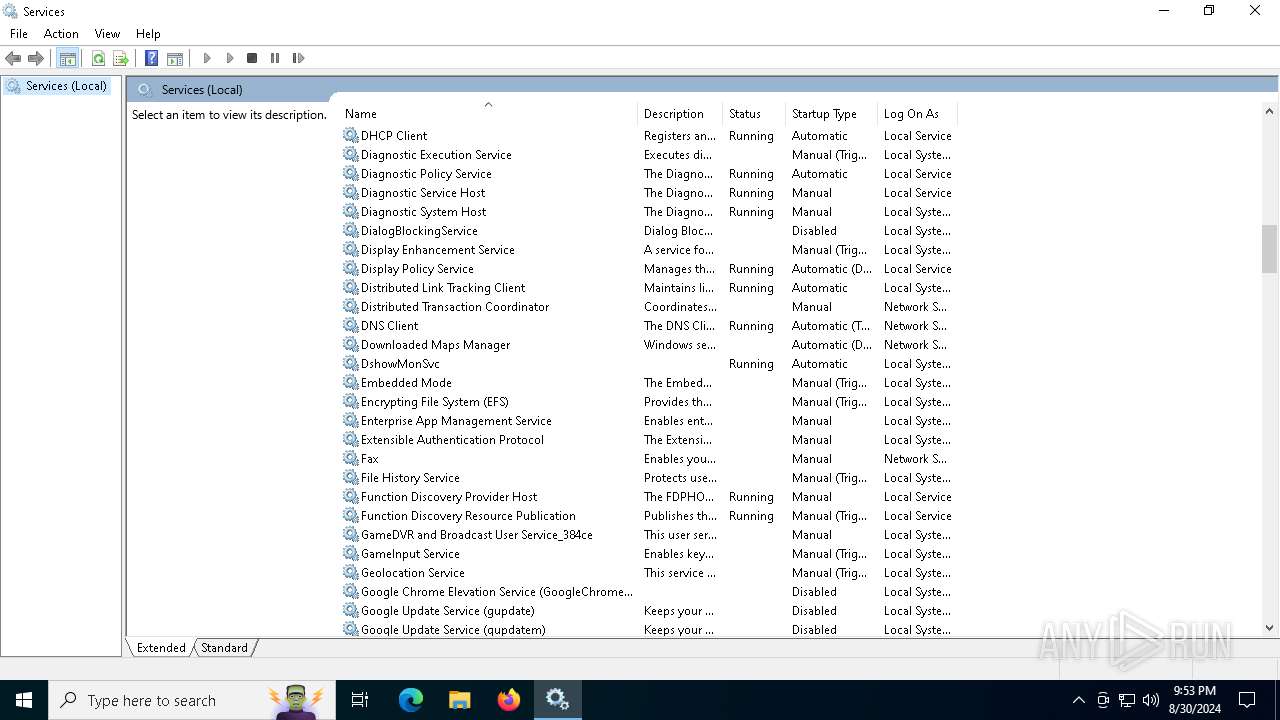
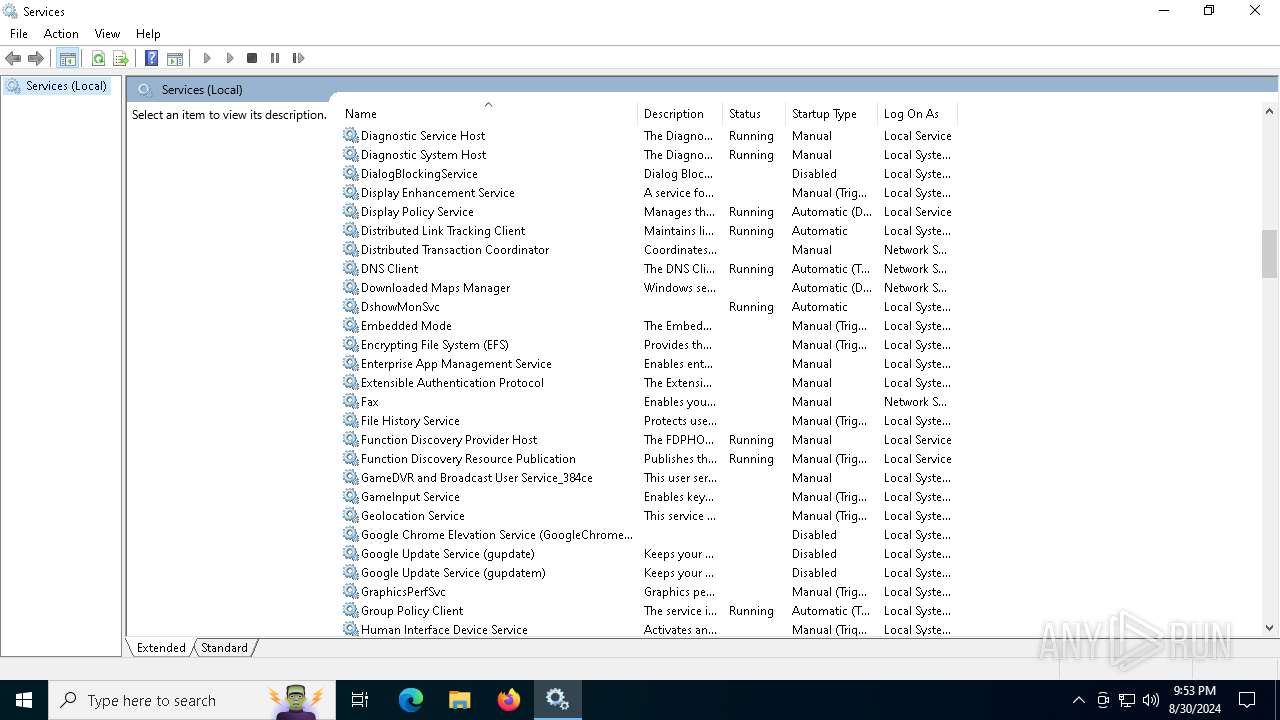
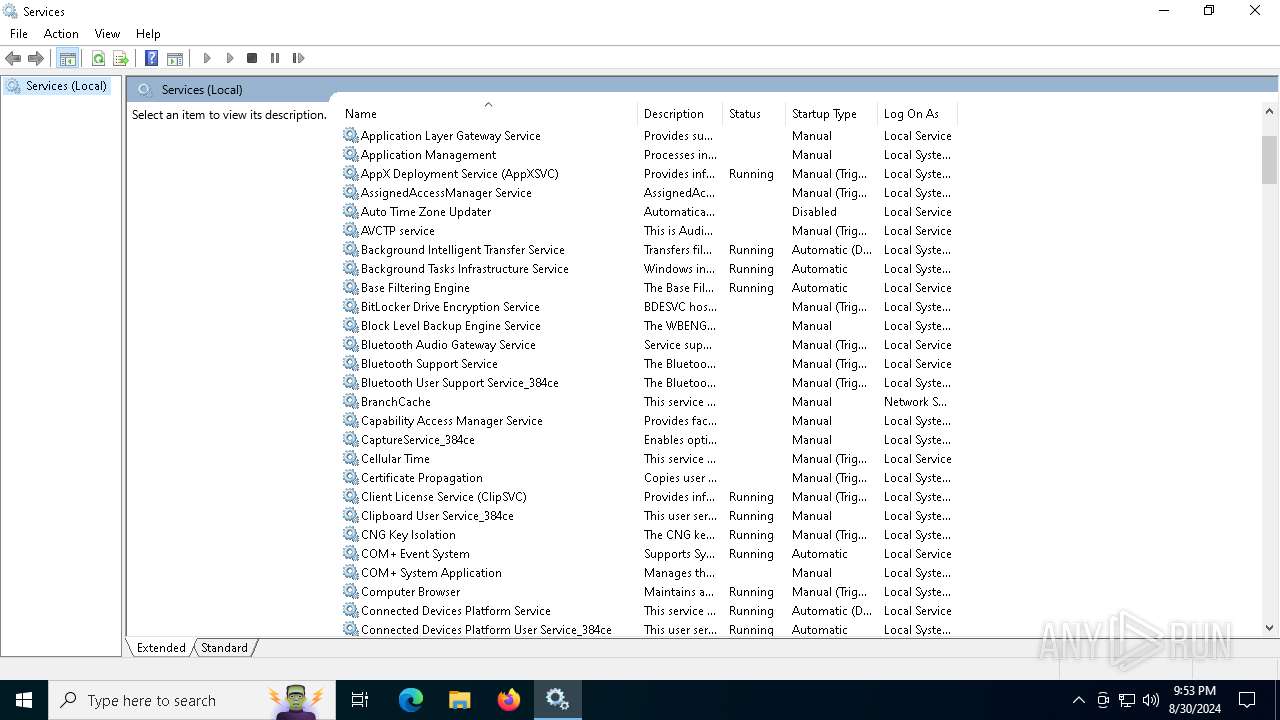
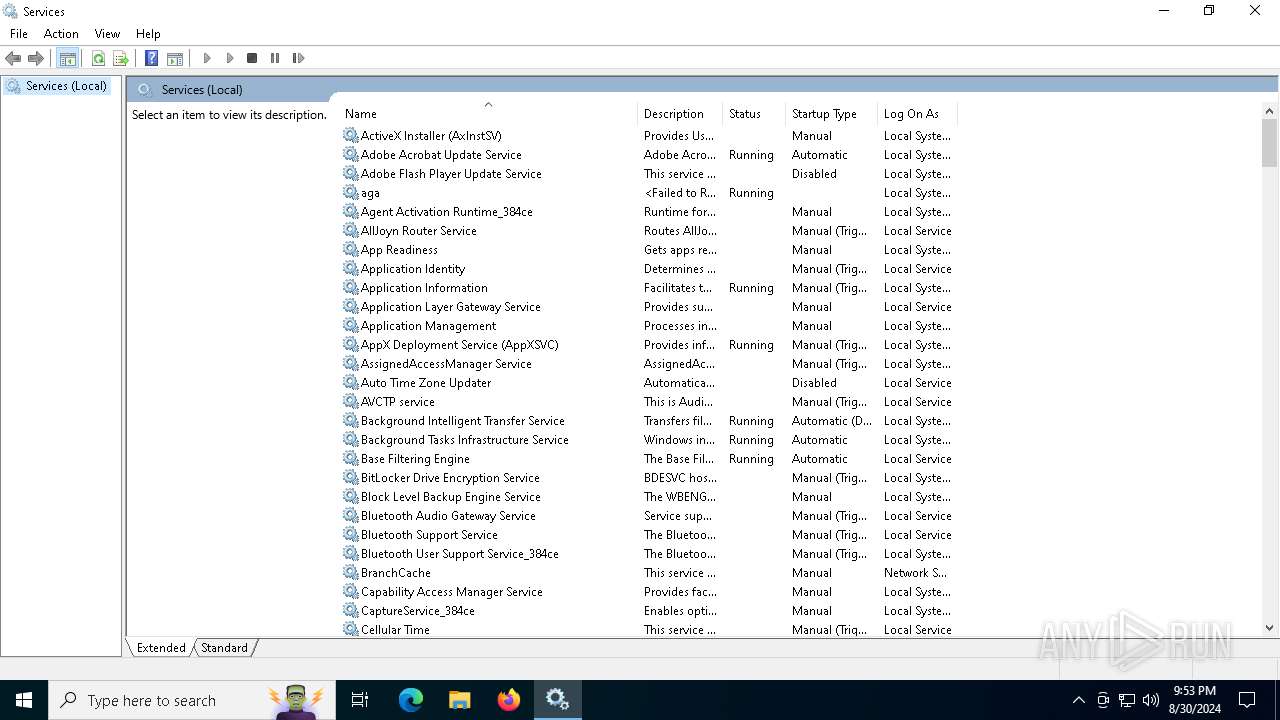
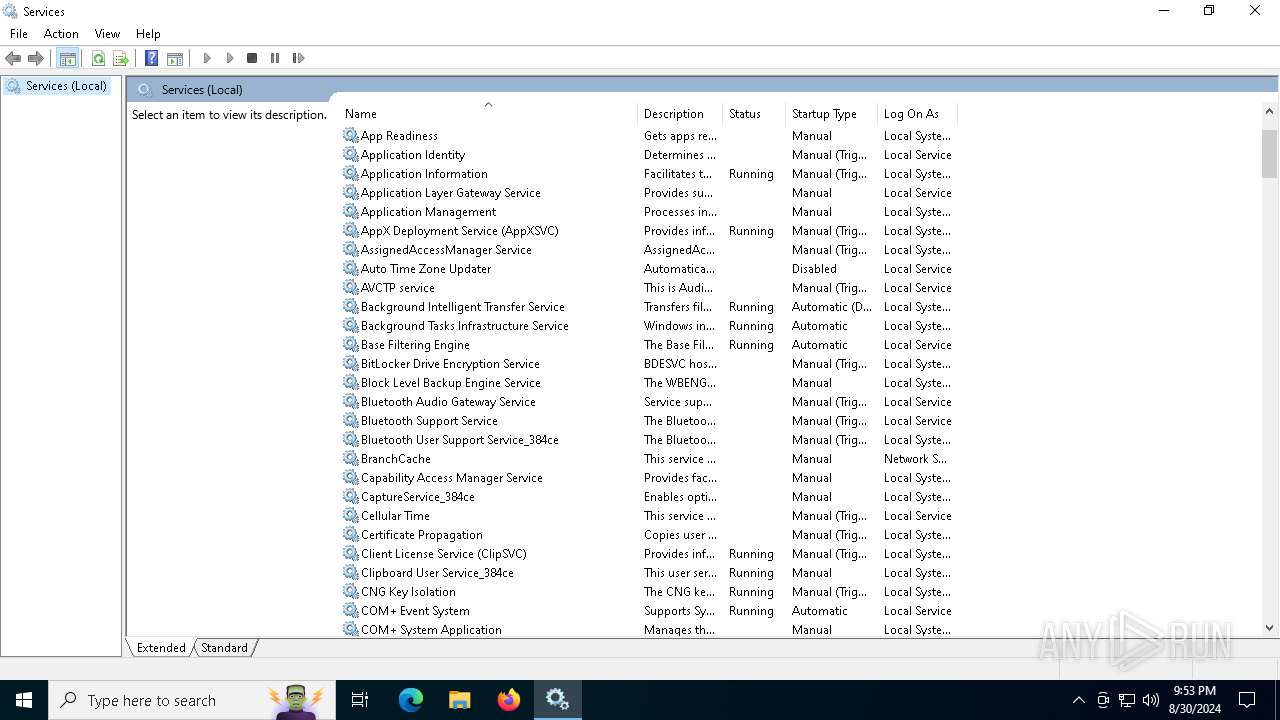
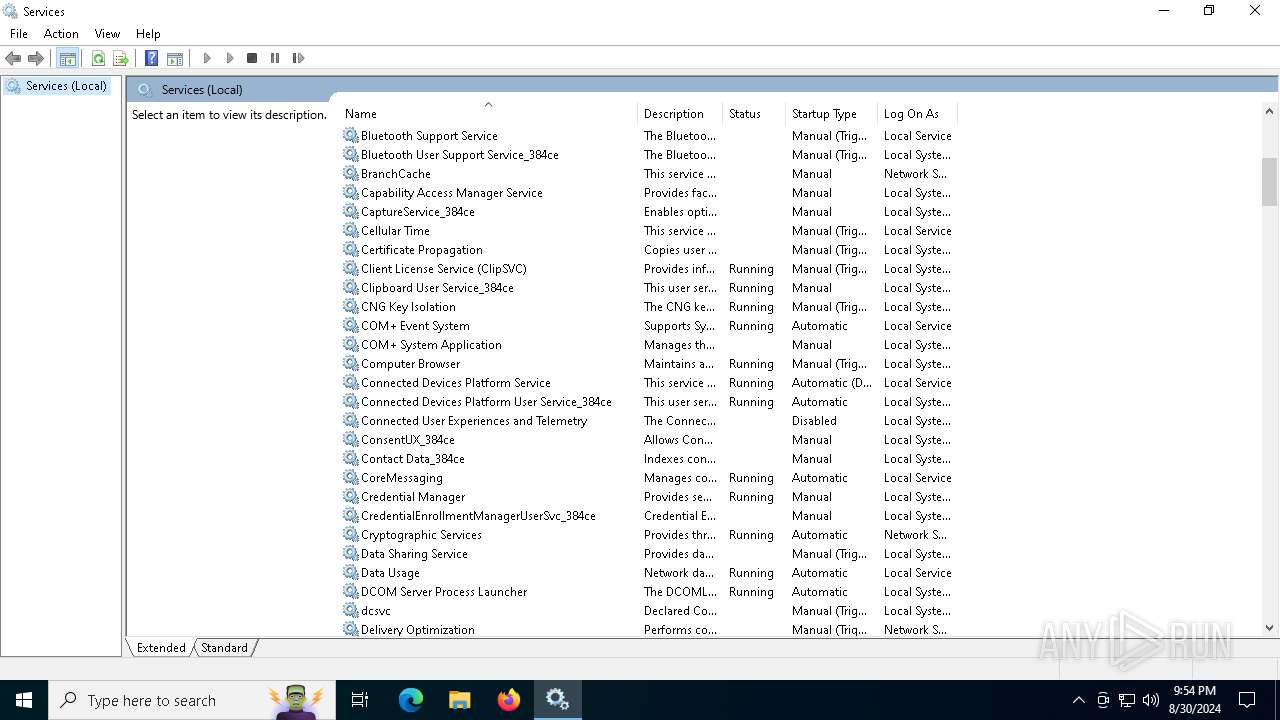
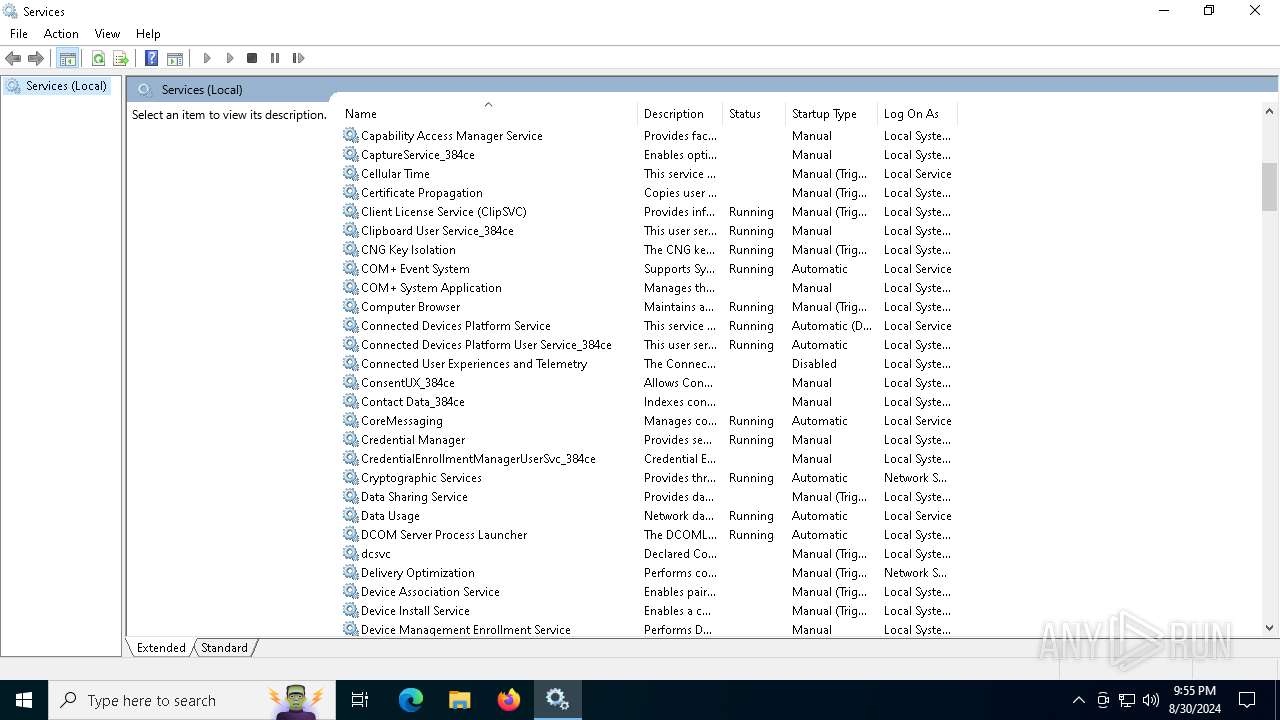
Executes as Windows Service
- dshowmonsvc.exe (PID: 5044)
Application launched itself
- dshowmonsvc.exe (PID: 5044)
Reads Microsoft Outlook installation path
- mmc.exe (PID: 232)
Reads Internet Explorer settings
- mmc.exe (PID: 232)
INFO
Checks supported languages
- UvcHamSetup.exe (PID: 7040)
- dshowmonsvc.exe (PID: 6844)
- dshowmonsvc.exe (PID: 5796)
- dshowmonsvc.exe (PID: 5044)
- dshowmonsvc.exe (PID: 6500)
Create files in a temporary directory
- UvcHamSetup.exe (PID: 7040)
Reads the computer name
- UvcHamSetup.exe (PID: 7040)
- dshowmonsvc.exe (PID: 6844)
- dshowmonsvc.exe (PID: 5796)
- dshowmonsvc.exe (PID: 5044)
Creates files in the program directory
- UvcHamSetup.exe (PID: 7040)
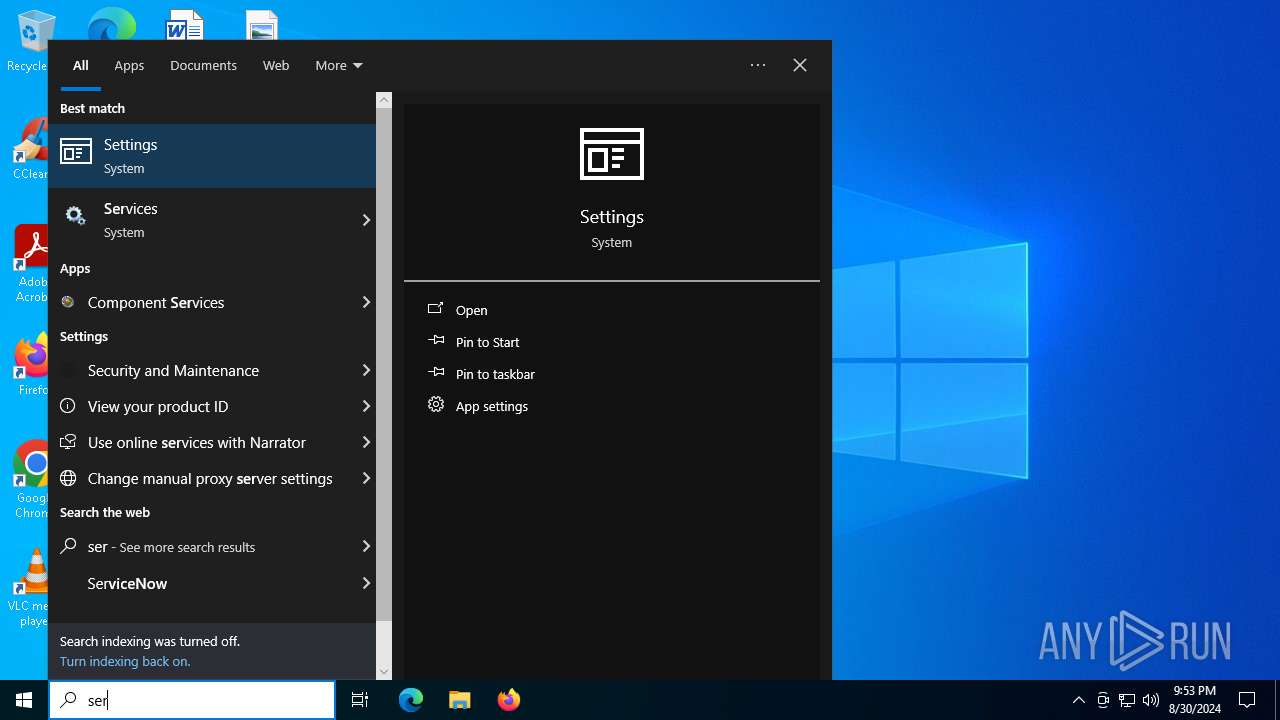
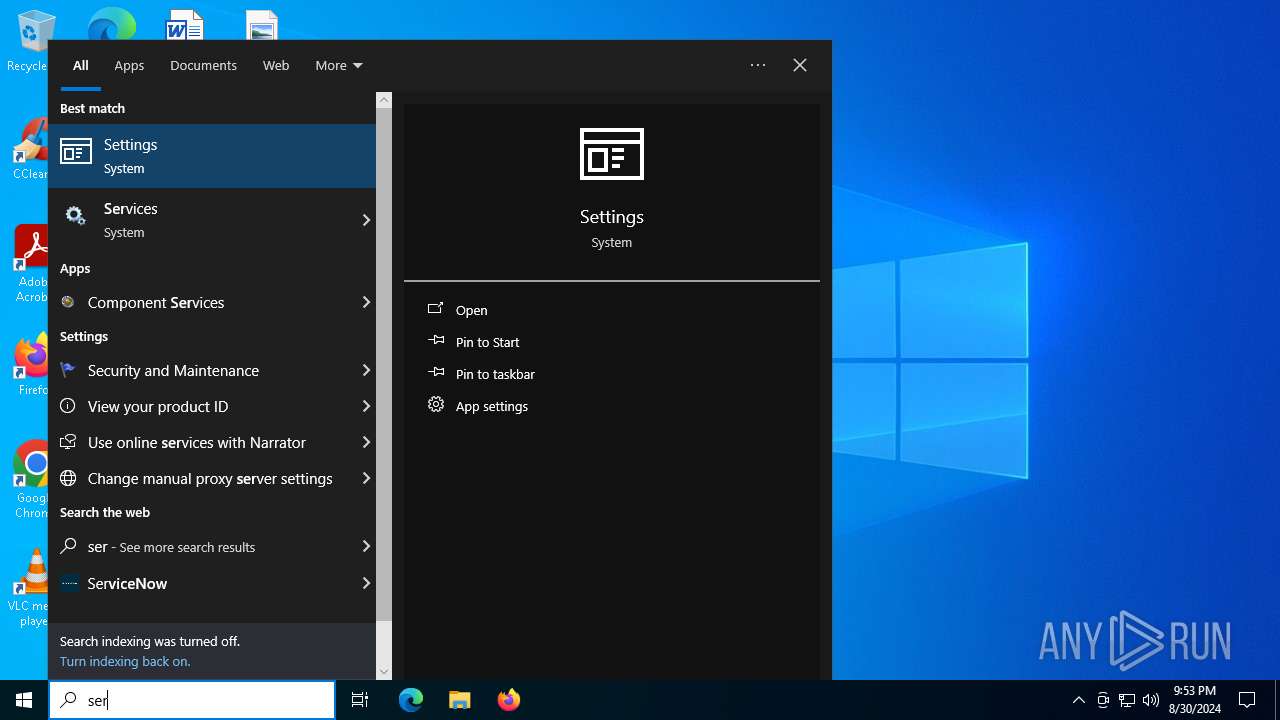
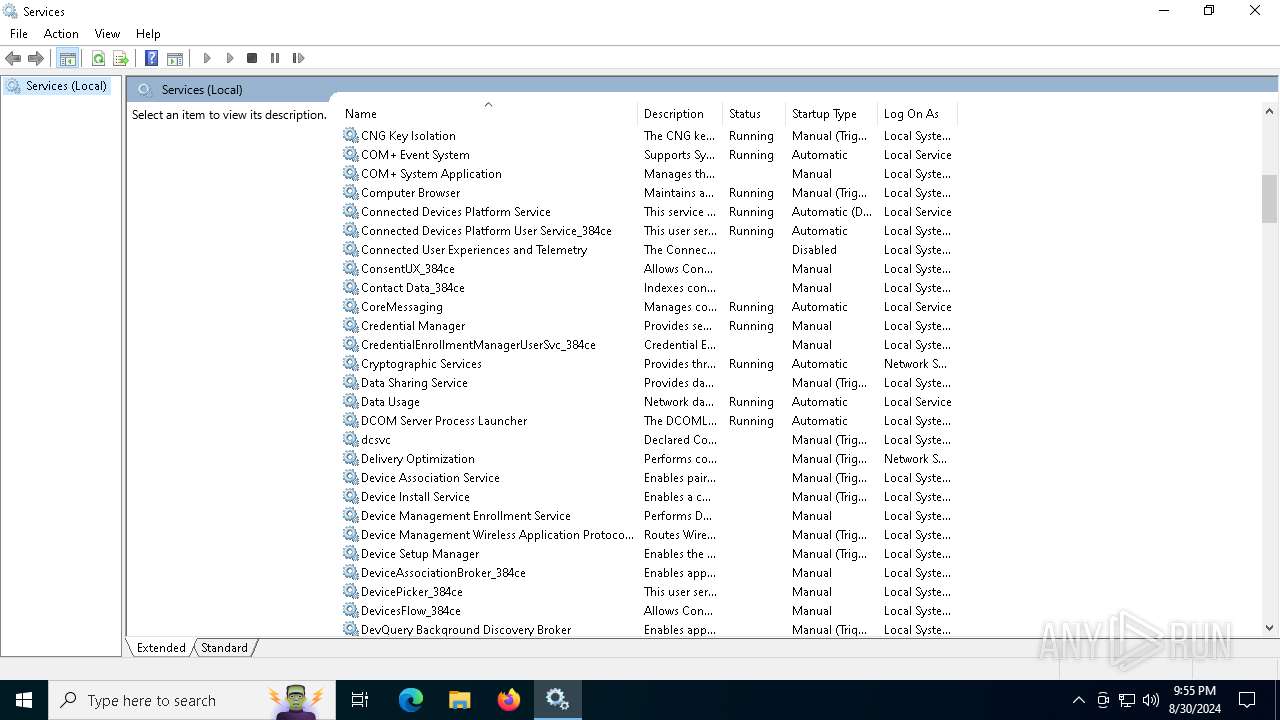
Manual execution by a user
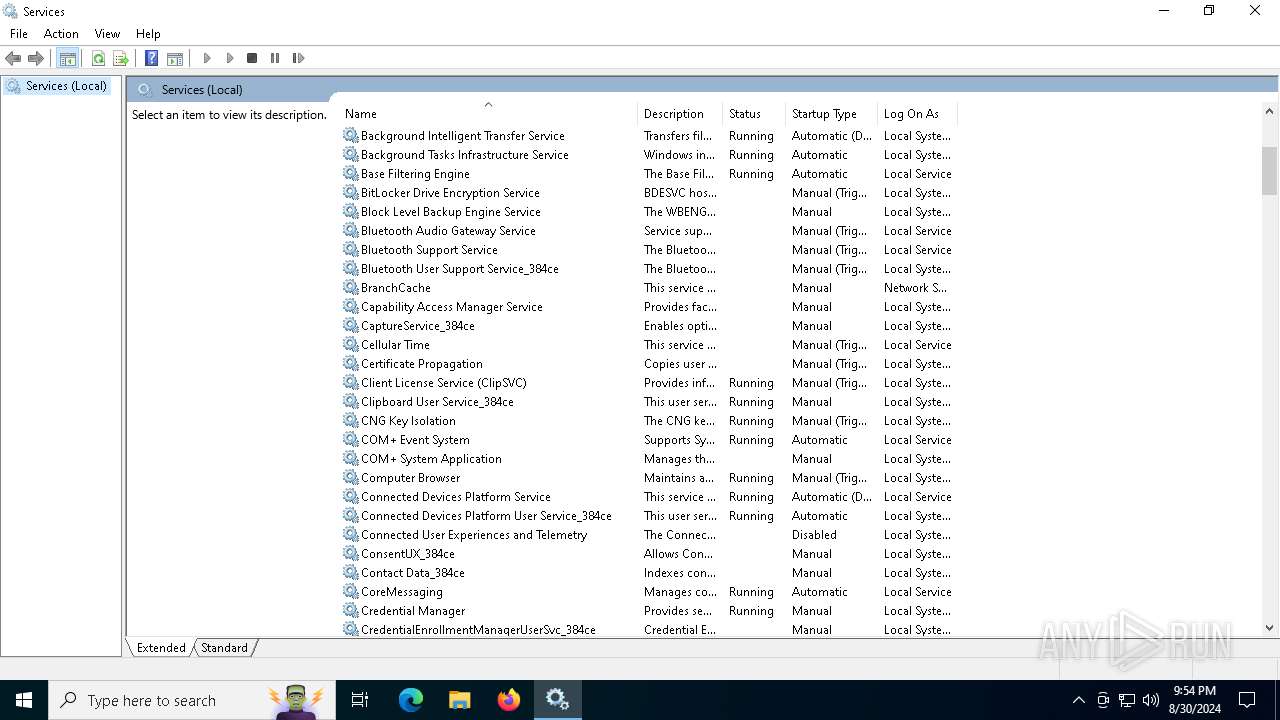
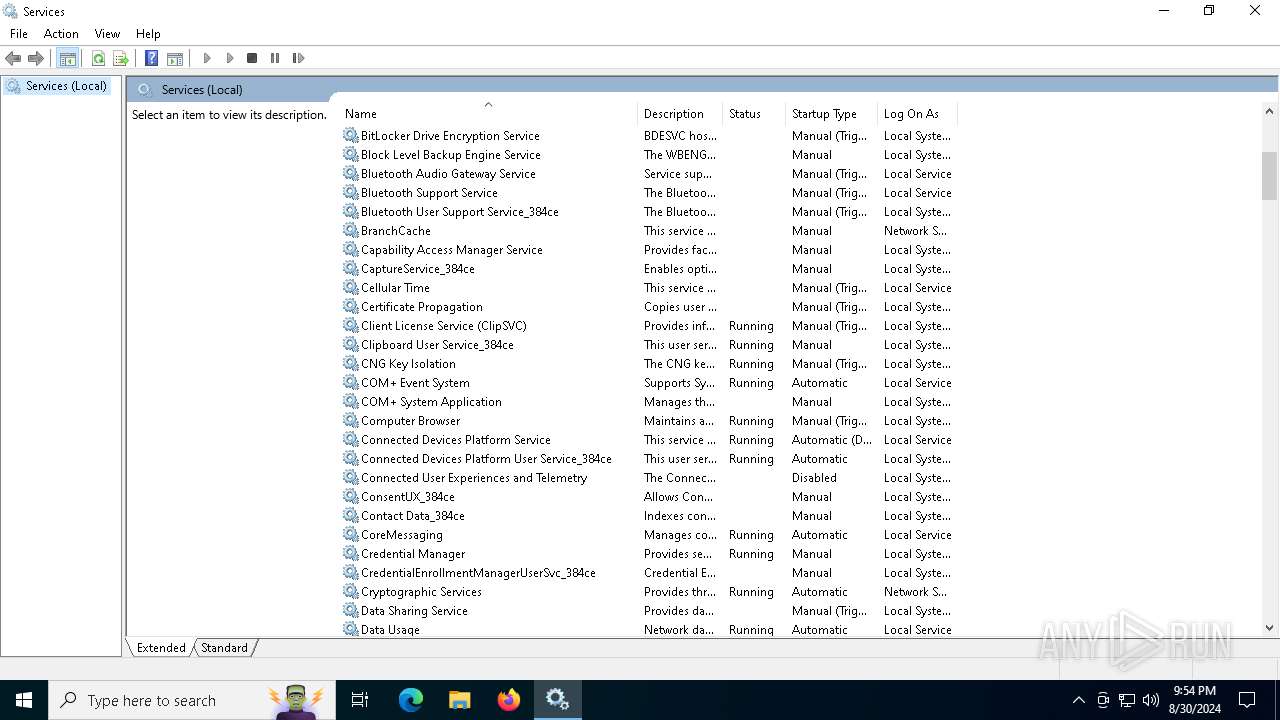
- mmc.exe (PID: 232)
- mmc.exe (PID: 508)
Creates files or folders in the user directory
- mmc.exe (PID: 232)
The process uses the downloaded file
- mmc.exe (PID: 232)
Reads the software policy settings
- slui.exe (PID: 4192)
- slui.exe (PID: 6344)
Checks proxy server information
- slui.exe (PID: 6344)
- mmc.exe (PID: 232)
Reads security settings of Internet Explorer
- mmc.exe (PID: 232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:24 22:19:26+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x35d8 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
159
Monitored processes
24
Malicious processes
3
Suspicious processes
2
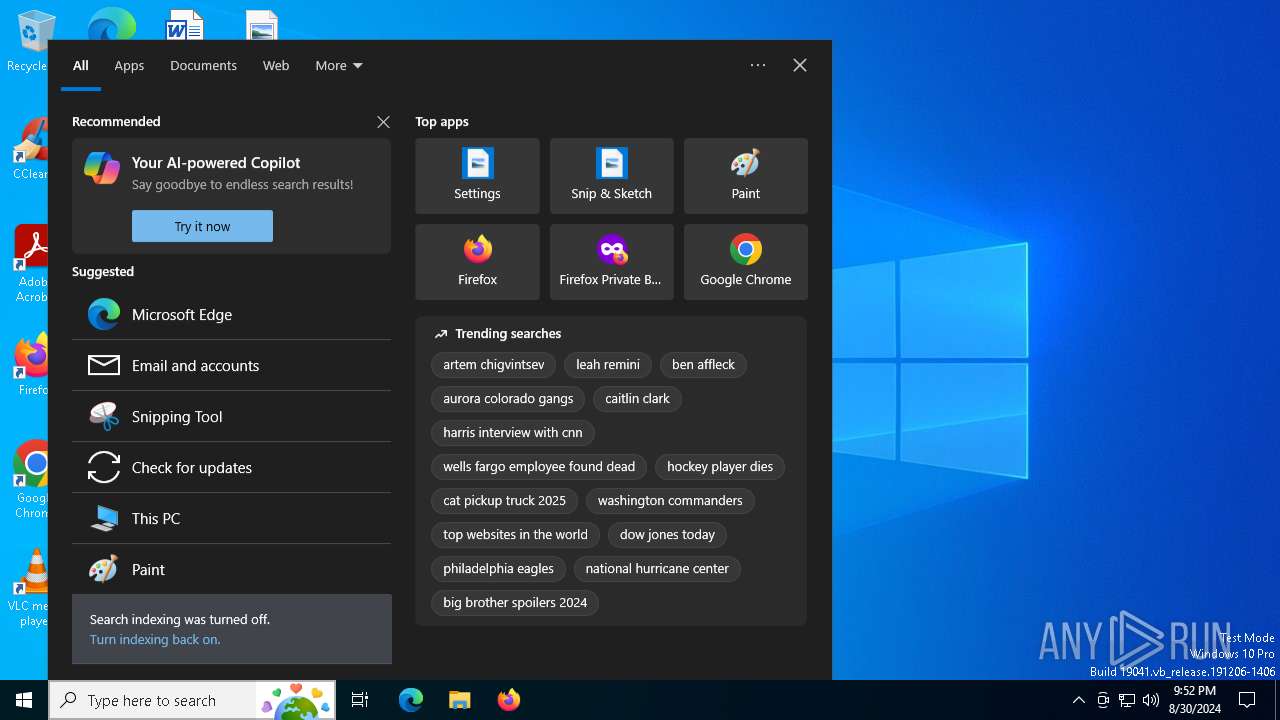
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
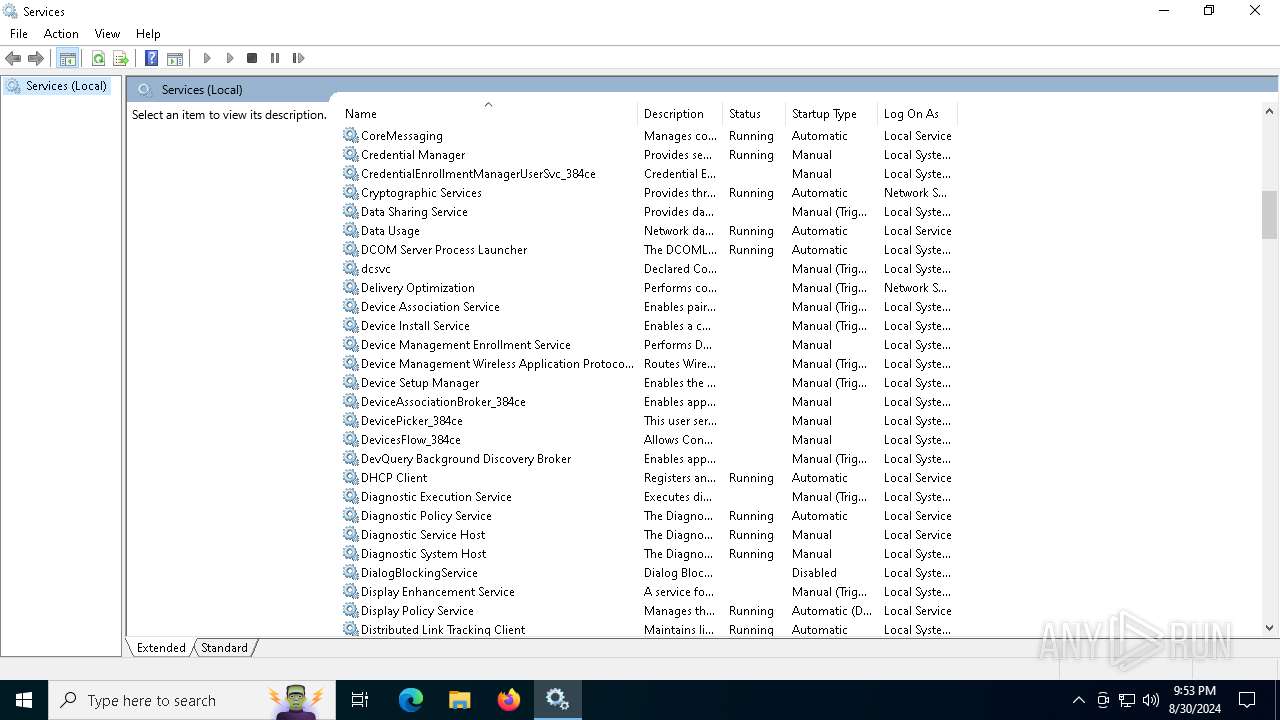
| 232 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\services.msc" | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\services.msc" | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | C:\WINDOWS\system32\net.exe start DshowMonSvc | C:\Windows\SysWOW64\net.exe | — | UvcHamSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1640 | C:\WINDOWS\System32\regsvr32.exe /s /u "C:\Program Files\UvcHam\x64\uvcham.ax" | C:\Windows\SysWOW64\regsvr32.exe | — | UvcHamSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2224 | C:\WINDOWS\SysWOW64\regsvr32.exe /s "C:\Program Files\UvcHam\x86\uvcham.ax" | C:\Windows\SysWOW64\regsvr32.exe | — | UvcHamSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | C:\WINDOWS\system32\net1 start DshowMonSvc | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4192 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | "C:\Users\admin\AppData\Local\Temp\UvcHamSetup.exe" | C:\Users\admin\AppData\Local\Temp\UvcHamSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5044 | "C:\Program Files\Common Files\dshowmonsvc\dshowmonsvc.exe" -service | C:\Program Files\Common Files\dshowmonsvc\dshowmonsvc.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Modules
| |||||||||||||||
Total events
7 180
Read events
7 038
Write events
121
Delete events
21
Modification events
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{36F02055-6EC6-4346-8648-8D08A2A7EE8A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{C2B17EFB-551B-498A-A4B2-D8D16718E56A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{C2B17EFB-551B-498A-A4B2-D8D26718E56A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{C2B17EFB-551B-498A-A4B2-D8D36718E56A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{C2B17EFB-551B-498A-A4B2-D8D46718E56A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{C2B17EFB-551B-498A-A4B2-D8D56718E56A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{C2B17EFB-551B-498A-A4B2-D8D66718E56A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{C2B17EFB-551B-498A-A4B2-D8D76718E56A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{C2B17EFB-551B-498A-A4B2-D8D86718E56A}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{83A605D5-7C29-43C3-8823-66B50532FD5F}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
Executable files
9
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7040 | UvcHamSetup.exe | C:\Users\admin\AppData\Local\Temp\nswA85F.tmp | — | |
MD5:— | SHA256:— | |||
| 7040 | UvcHamSetup.exe | C:\Users\admin\AppData\Local\Temp\nsqA88E.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 7040 | UvcHamSetup.exe | C:\Program Files\UvcHam\x86\uvcham.ax | executable | |
MD5:50BBD6174D41AC124DBF208981D2E9C0 | SHA256:910B5D2436B0A031868E2ADE0D6CF83DD3BAF36160BD4AACEFC53A1774128295 | |||
| 7040 | UvcHamSetup.exe | C:\Windows\twain_64\uvcham.ds | executable | |
MD5:A938B2722E946D785007794D0F38F91F | SHA256:2E919876EA8555F677BC64E75A6D42E47EB35071EFB5D87D0FDD9A86E3CCBB1A | |||
| 7040 | UvcHamSetup.exe | C:\Users\admin\AppData\Local\Temp\nsqA88E.tmp\nsExec.dll | executable | |
MD5:EC9C99216EF11CDD85965E78BC797D2C | SHA256:C1B7C3EF8B77A5BB335DC9EC9C3546B249014DDE43AA2A9ED719B4D5933741DF | |||
| 7040 | UvcHamSetup.exe | C:\Program Files\UvcHam\uninst.exe | executable | |
MD5:5409FDCA304345C488A76A1E0CE6771C | SHA256:F32CC15365949625CDED90C511A95A7A7E0A905F710F9D3D8AE69A51B1C1475B | |||
| 7040 | UvcHamSetup.exe | C:\Program Files\UvcHam\x64\uvcham.ax | executable | |
MD5:3E33464C8F12EBDD9FEF66BB8FC38A4B | SHA256:9C340A1E399FF48DF576E395DE47EBF3DB6A2A8D37A8004F5BED20097C448798 | |||
| 7040 | UvcHamSetup.exe | C:\Program Files\Common Files\dshowmonsvc\dshowmonsvc.exe | executable | |
MD5:EDE3D3E547D391DC2BACAD25F32AA15E | SHA256:480AB2FBEC891F6121F24E4BFB2E46BC8882B5E048E4C66A8B72C185AB9B5BF0 | |||
| 7040 | UvcHamSetup.exe | C:\Users\admin\AppData\Local\Temp\nsqA88E.tmp\System.dll | executable | |
MD5:6E55A6E7C3FDBD244042EB15CB1EC739 | SHA256:ACF90AB6F4EDC687E94AAF604D05E16E6CFB5E35873783B50C66F307A35C6506 | |||
| 7040 | UvcHamSetup.exe | C:\Users\admin\AppData\Local\Temp\nsqA88E.tmp\nsDialogs.dll | executable | |
MD5:CA5BB0EE2B698869C41C087C9854487C | SHA256:C719697D5CED17D97BBC48662327339CCEC7E03F6552AA1D5C248F6FA5F16324 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
47
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2476 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7104 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7104 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEASGp3XRNgzfylEWBFW6KKc%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 163.181.92.230:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEA%2FgMquETQMxBsUMjhPIsGg%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | 52.140.118.28:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IN | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6248 | svchost.exe | 52.140.118.28:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IN | whitelisted |
— | — | 52.140.118.28:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IN | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2476 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2476 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6248 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7104 | SIHClient.exe | 40.127.169.103:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |