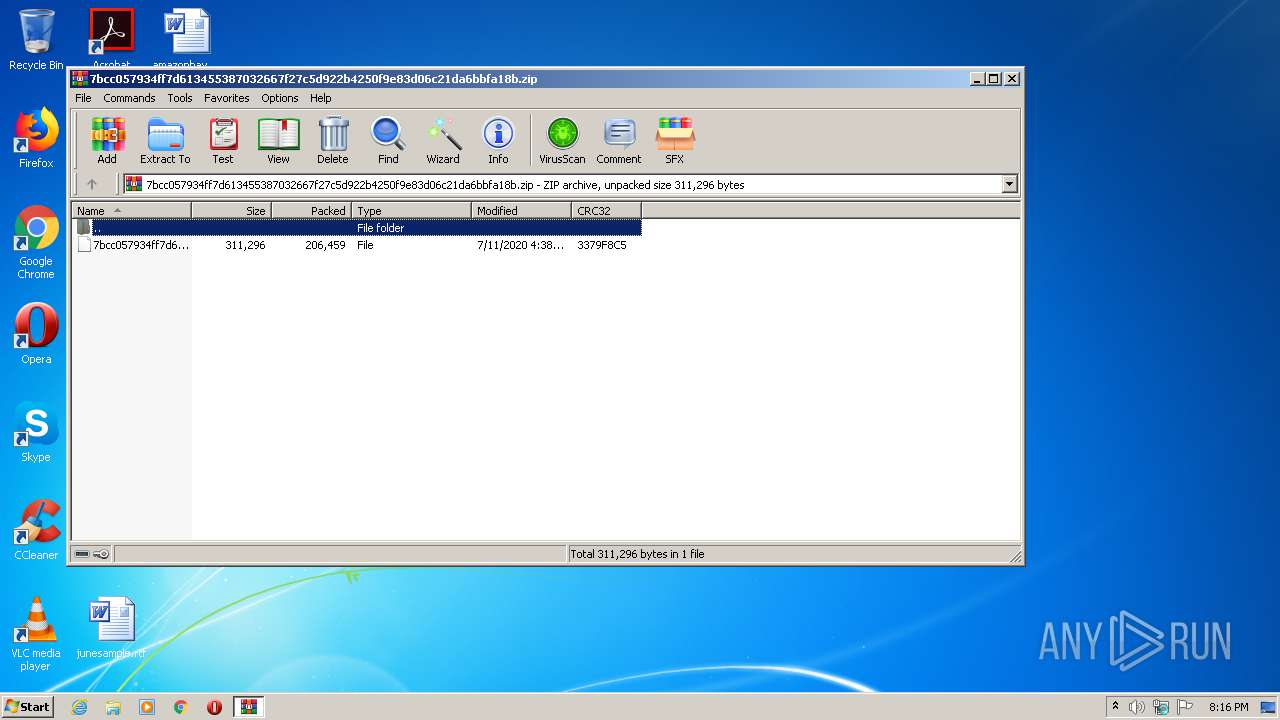
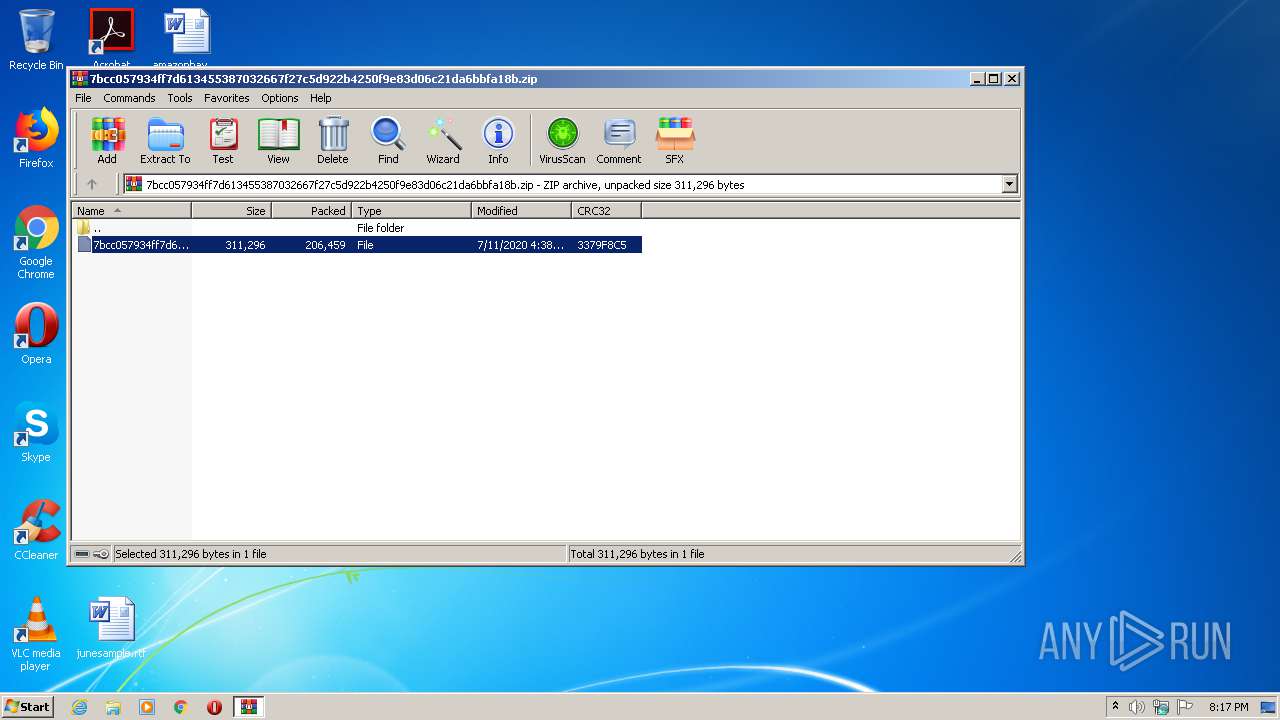
| File name: | 7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.zip |
| Full analysis: | https://app.any.run/tasks/a7bff10d-29af-45c2-8c27-174f731409da |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 19:16:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4A5FF31A30A310DCA55758F699E05064 |
| SHA1: | 2247A707770F15F14BA23E7A366DC7E0401CF776 |
| SHA256: | 0F11D7A0FA4E5082943BEBD54892F7B4CA5EE66747130391C08E72CC0B978626 |
| SSDEEP: | 3072:yMfRBk8660RCo/Ylfhbm1zzFgWbcXPRDkl3SHX8JCHIhHCtnK96lVFxkIrNgoELF:y/B28zeWbcFmC3ostzBgLSxfUv |
MALICIOUS
Renames files like Ransomware
- explorer.exe (PID: 328)
Application was dropped or rewritten from another process
- 7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.exe (PID: 2776)
Runs injected code in another process
- explorer.exe (PID: 328)
- 7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.exe (PID: 2776)
Changes the autorun value in the registry
- explorer.exe (PID: 328)
Changes internet zones settings
- explorer.exe (PID: 328)
Application was injected by another process
- taskeng.exe (PID: 1988)
- ctfmon.exe (PID: 540)
- explorer.exe (PID: 328)
- dwm.exe (PID: 120)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 328)
- WinRAR.exe (PID: 2184)
Creates files in the program directory
- explorer.exe (PID: 328)
INFO
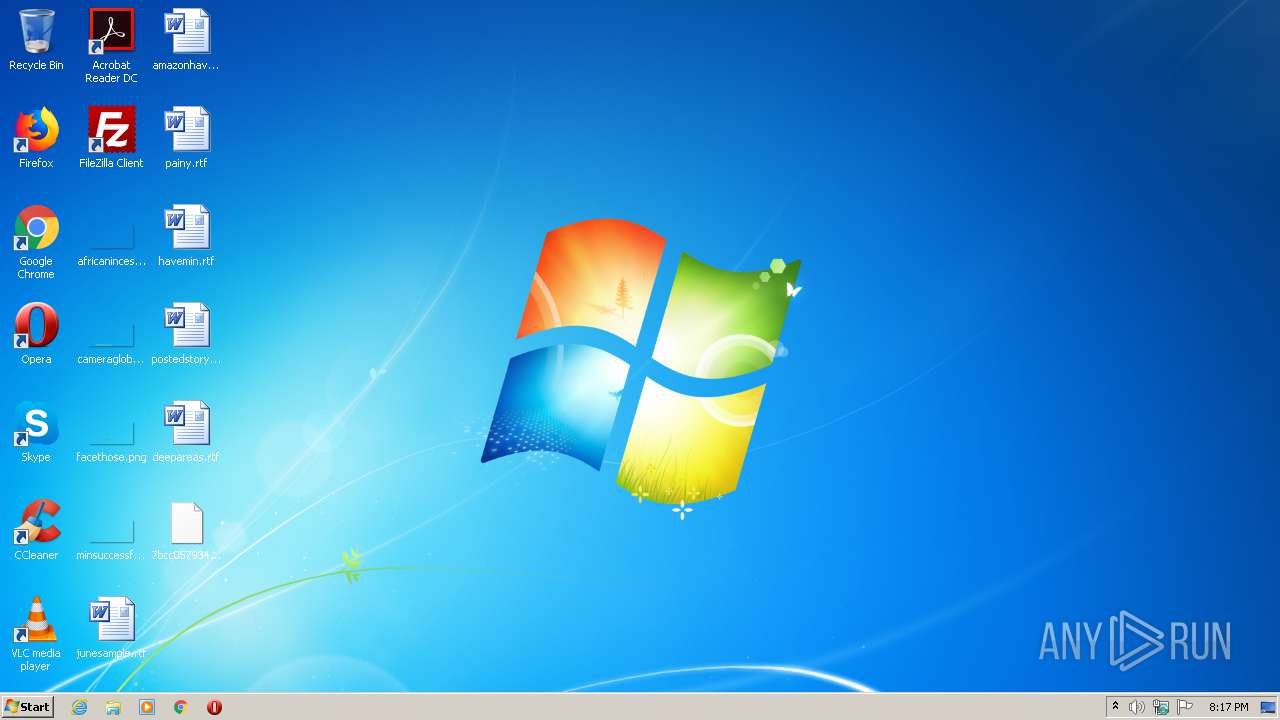
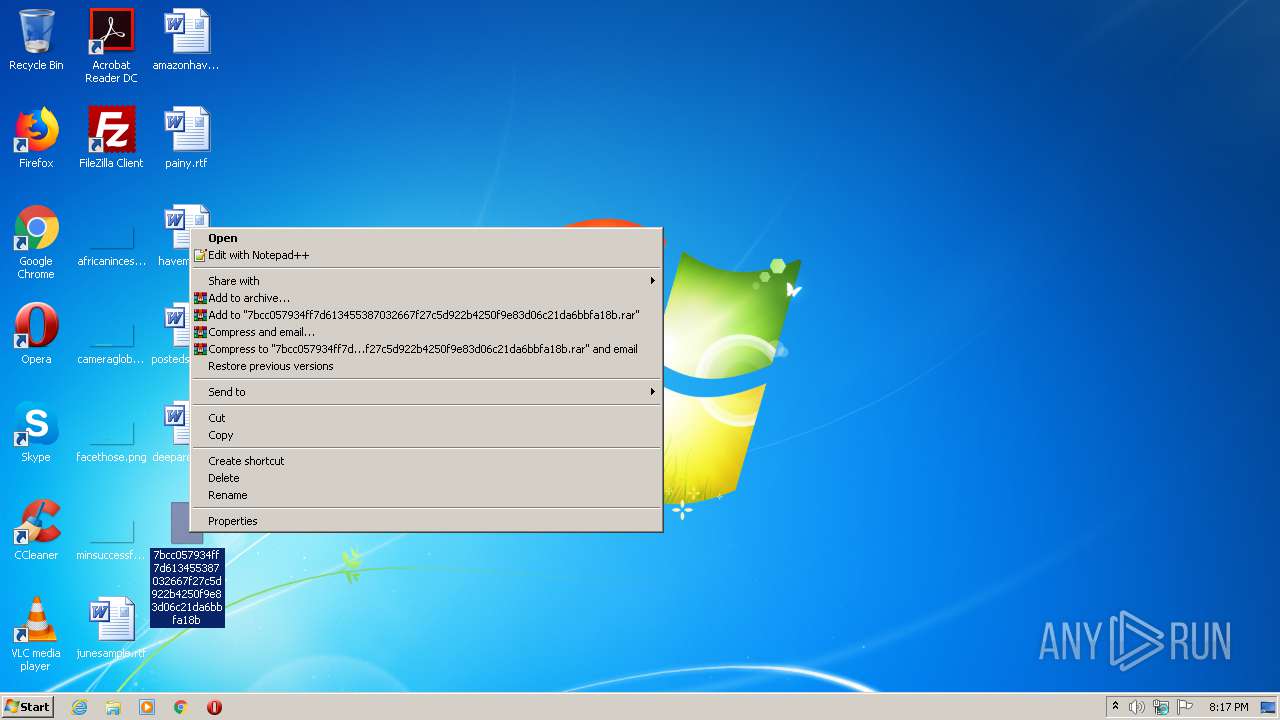
Manual execution by user
- 7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.exe (PID: 2776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
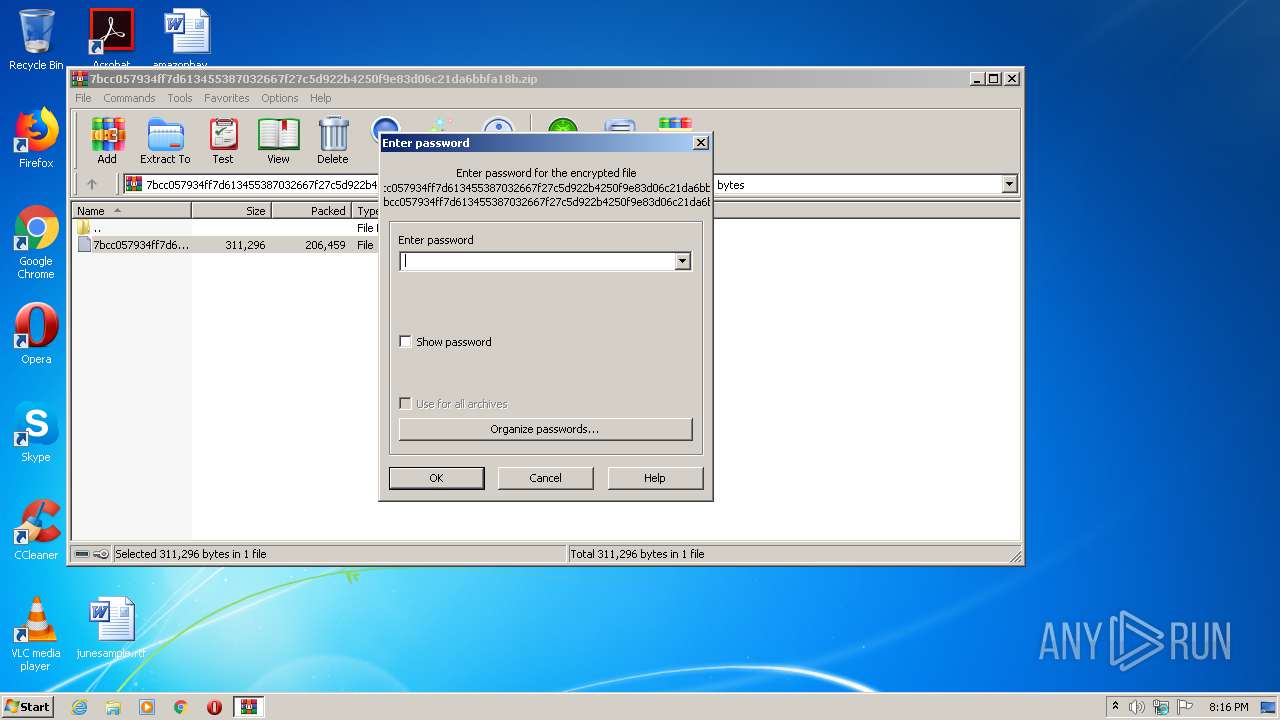
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:07:11 15:38:17 |
| ZipCRC: | 0x3379f8c5 |
| ZipCompressedSize: | 206459 |
| ZipUncompressedSize: | 311296 |
| ZipFileName: | 7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b |
Total processes
36
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1988 | taskeng.exe {B14E2254-30F5-4DE4-9F11-F28DDD7DC91D} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
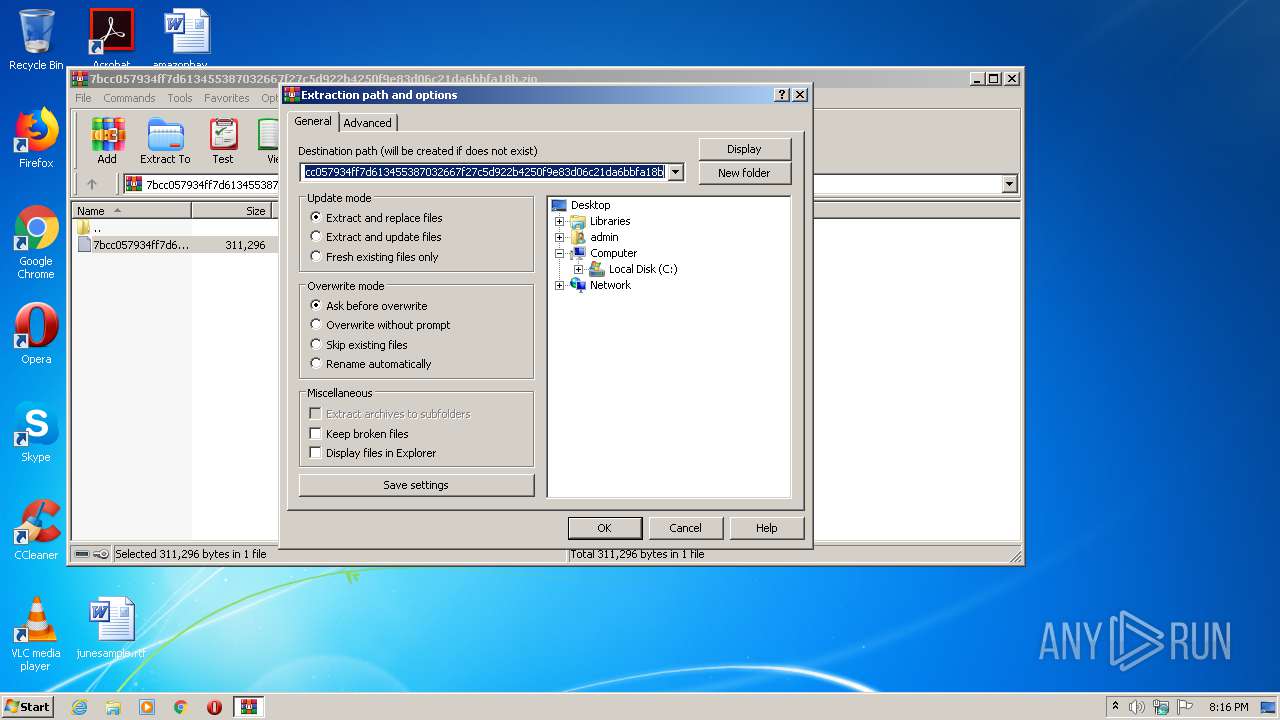
| 2184 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
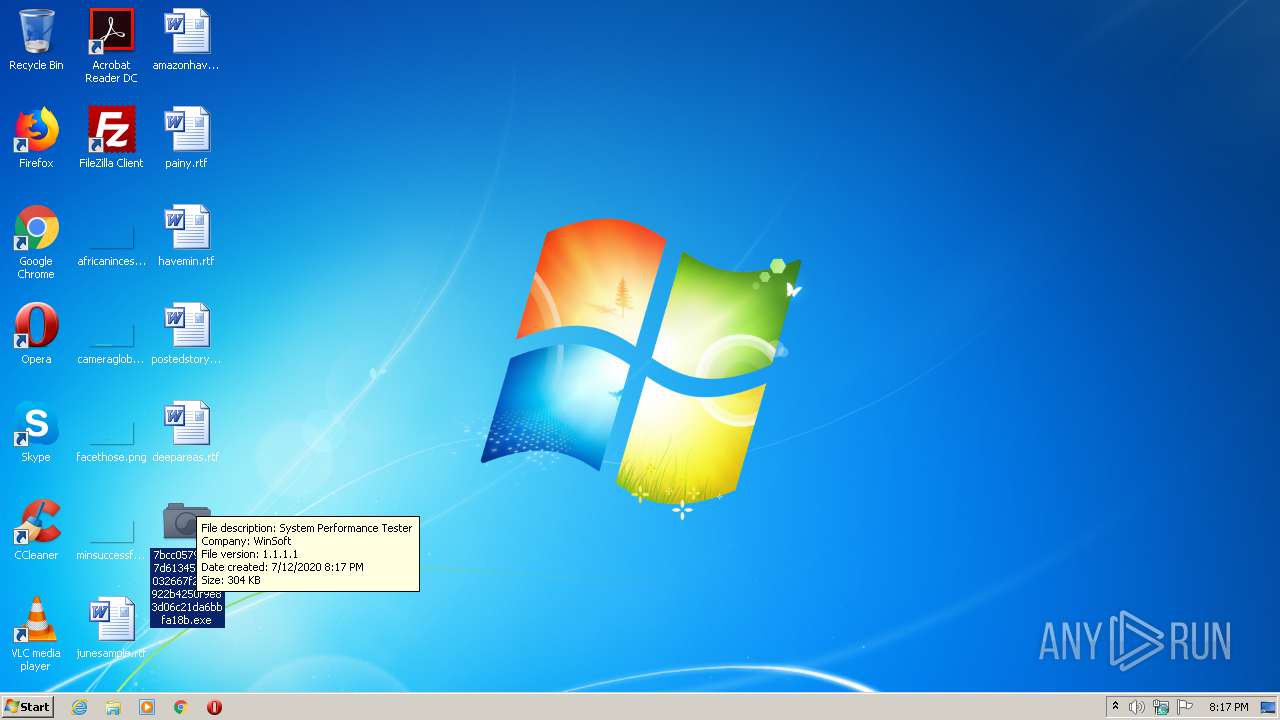
| 2776 | "C:\Users\admin\Desktop\7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.exe" | C:\Users\admin\Desktop\7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.exe | — | explorer.exe | |||||||||||
User: admin Company: WinSoft Integrity Level: MEDIUM Description: System Performance Tester Exit code: 0 Version: 1.1.1.1 Modules
| |||||||||||||||
Total events
3 128
Read events
3 072
Write events
56
Delete events
0
Modification events
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.zip | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2184) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (328) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 328 | explorer.exe | C:\ProgramData\RotqEwko\PizbUlfu.exe | executable | |
MD5:63744F970915477D6200184D673CEC98 | SHA256:7BCC057934FF7D613455387032667F27C5D922B4250F9E83D06C21DA6BBFA18B | |||
| 2184 | WinRAR.exe | C:\Users\admin\Desktop\7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b | executable | |
MD5:63744F970915477D6200184D673CEC98 | SHA256:7BCC057934FF7D613455387032667F27C5D922B4250F9E83D06C21DA6BBFA18B | |||
| 328 | explorer.exe | C:\Users\admin\Desktop\7bcc057934ff7d613455387032667f27c5d922b4250f9e83d06c21da6bbfa18b.exe | executable | |
MD5:63744F970915477D6200184D673CEC98 | SHA256:7BCC057934FF7D613455387032667F27C5D922B4250F9E83D06C21DA6BBFA18B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report