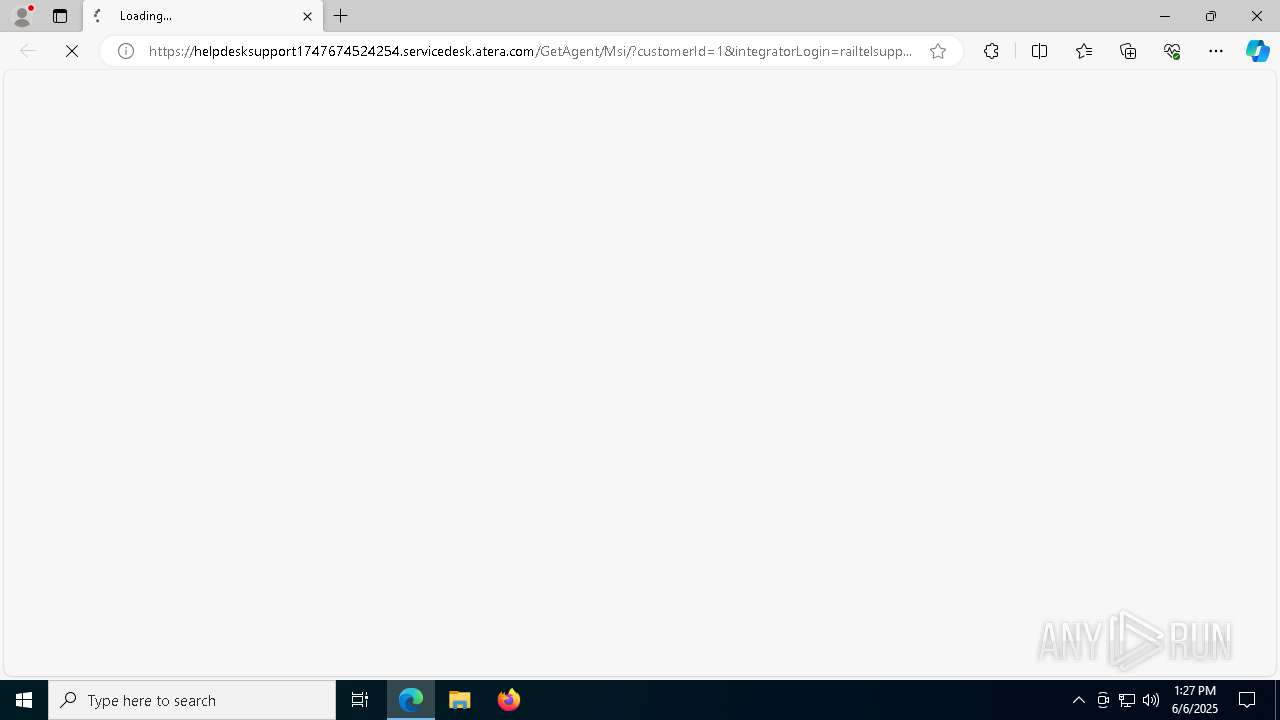
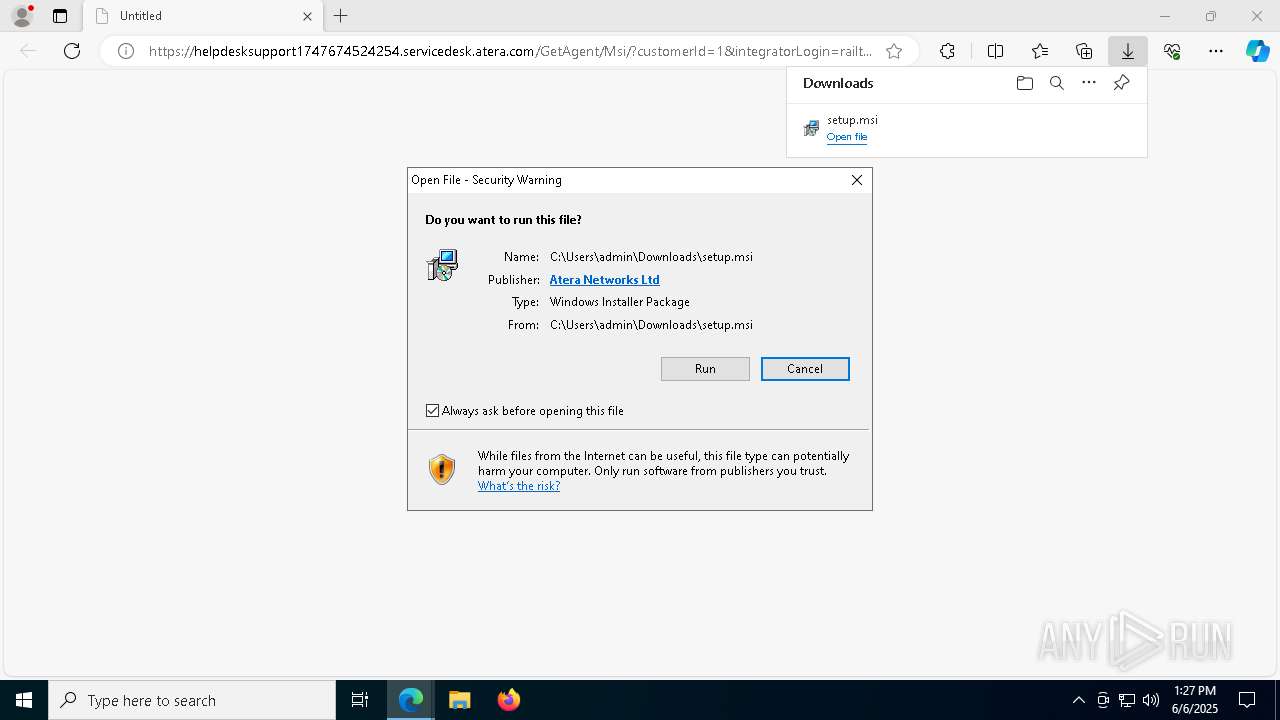
| URL: | https://HelpdeskSupport1747674524254.servicedesk.atera.com/GetAgent/Msi/?customerId=1&integratorLogin=railtelsupport0awcsoftware.com&accountId=001Q300000TNUrDIAX |
| Full analysis: | https://app.any.run/tasks/0d796ef5-3c3b-4a70-8138-e4f2be315ab5 |
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2025, 13:27:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C7671872A99733ABA92C9908E7F2F37E |
| SHA1: | CBDEED3AF19BA983119C3CC4EB8671BEF2EA742A |
| SHA256: | 0F0BF52433574D9EAA25BEB8F3683C9C75C63593CCFA2DA251CE4B3B04322152 |
| SSDEEP: | 3:N8D46VVKiVSeELjMmJJUyG6lK1s9HACUl0UIp/XRV7xE0F/a42VV2:2D3VglD6yblKu9HALEjV7xEY/QM |
MALICIOUS
Starts NET.EXE for service management
- msiexec.exe (PID: 6824)
- net.exe (PID: 5096)
- net.exe (PID: 8532)
- msiexec.exe (PID: 8596)
- net.exe (PID: 8496)
Bypass execution policy to execute commands
- powershell.exe (PID: 7348)
- powershell.exe (PID: 2340)
- powershell.exe (PID: 2596)
- powershell.exe (PID: 9200)
Changes powershell execution policy (Bypass)
- AgentPackageAgentInformation.exe (PID: 7612)
- AgentPackageAgentInformation.exe (PID: 8844)
Executing a file with an untrusted certificate
- SRSelfSignCertUtil.exe (PID: 8420)
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 7692)
- rundll32.exe (PID: 4996)
- rundll32.exe (PID: 1164)
- AteraAgent.exe (PID: 7792)
- rundll32.exe (PID: 2064)
- csc.exe (PID: 6512)
- SplashtopStreamer.exe (PID: 8456)
- PreVerCheck.exe (PID: 8560)
- SetupUtil.exe (PID: 8476)
- AteraAgent.exe (PID: 6148)
- AgentPackageTicketing.exe (PID: 9160)
- AgentPackageUpgradeAgent.exe (PID: 9032)
- csc.exe (PID: 7928)
- rundll32.exe (PID: 6668)
- rundll32.exe (PID: 8328)
- AgentPackageRuntimeInstaller.exe (PID: 5072)
- rundll32.exe (PID: 9192)
- 8-0-11.exe (PID: 4996)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 5304)
- SplashtopStreamer.exe (PID: 924)
- 8-0-11.exe (PID: 9108)
- PreVerCheck.exe (PID: 2108)
Process drops legitimate windows executable
- msedge.exe (PID: 5568)
- msedge.exe (PID: 2040)
- msiexec.exe (PID: 7716)
- AteraAgent.exe (PID: 7792)
- AteraAgent.exe (PID: 6148)
- AgentPackageUpgradeAgent.exe (PID: 9032)
- 8-0-11.exe (PID: 9108)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 5304)
- 8-0-11.exe (PID: 4996)
Potential Corporate Privacy Violation
- rundll32.exe (PID: 4996)
- rundll32.exe (PID: 2064)
- AteraAgent.exe (PID: 7792)
- AgentPackageAgentInformation.exe (PID: 1548)
- AgentPackageAgentInformation.exe (PID: 496)
- AteraAgent.exe (PID: 6148)
- AgentPackageMonitoring.exe (PID: 3208)
- AgentPackageInternalPoller.exe (PID: 5304)
- AgentPackageAgentInformation.exe (PID: 7612)
- AgentPackageMarketplace.exe (PID: 8860)
- AgentPackageTicketing.exe (PID: 9160)
- AgentPackageMonitoring.exe (PID: 8852)
- rundll32.exe (PID: 8328)
- AgentPackageSTRemote.exe (PID: 1548)
- AgentPackageAgentInformation.exe (PID: 8844)
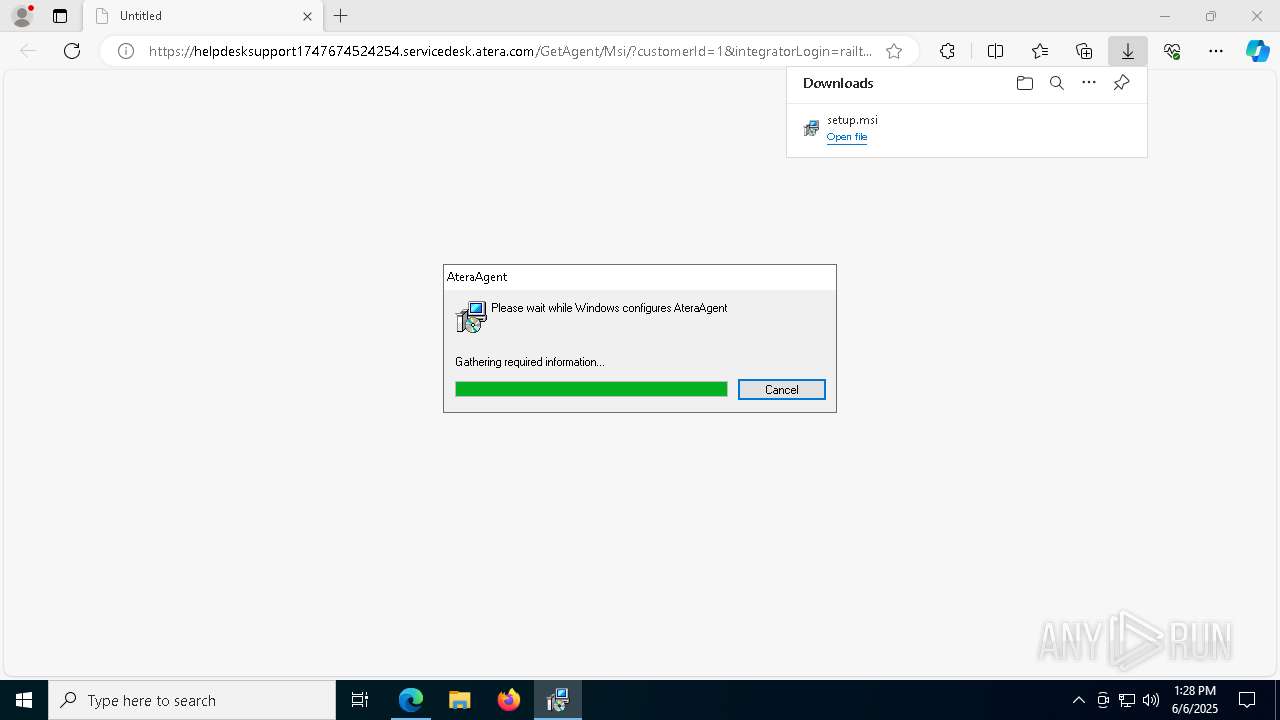
ATERAAGENT has been detected
- AteraAgent.exe (PID: 7792)
- AteraAgent.exe (PID: 7740)
- AteraAgent.exe (PID: 6148)
- AteraAgent.exe (PID: 8556)
- AteraAgent.exe (PID: 3208)
Starts SC.EXE for service management
- AteraAgent.exe (PID: 7792)
- AteraAgent.exe (PID: 6148)
Executes as Windows Service
- AteraAgent.exe (PID: 7792)
- AteraAgent.exe (PID: 6148)
- VSSVC.exe (PID: 7524)
- SRService.exe (PID: 6656)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 6824)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 4276)
- cmd.exe (PID: 8928)
- cmd.exe (PID: 9060)
- cmd.exe (PID: 9172)
- cmd.exe (PID: 8472)
- msiexec.exe (PID: 8596)
Restarts service on failure
- sc.exe (PID: 924)
- sc.exe (PID: 7900)
Starts POWERSHELL.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 7612)
- cmd.exe (PID: 8328)
- AgentPackageAgentInformation.exe (PID: 8844)
- cmd.exe (PID: 9128)
The process hides Powershell's copyright startup banner
- AgentPackageAgentInformation.exe (PID: 7612)
- AgentPackageAgentInformation.exe (PID: 8844)
The process executes Powershell scripts
- AgentPackageAgentInformation.exe (PID: 7612)
- cmd.exe (PID: 8328)
- AgentPackageAgentInformation.exe (PID: 8844)
- cmd.exe (PID: 9128)
The process bypasses the loading of PowerShell profile settings
- AgentPackageAgentInformation.exe (PID: 7612)
- AgentPackageAgentInformation.exe (PID: 8844)
Executes application which crashes
- cscript.exe (PID: 536)
- cscript.exe (PID: 8664)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6512)
- csc.exe (PID: 7928)
Starts CMD.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 7612)
- AgentPackageRuntimeInstaller.exe (PID: 5072)
- msiexec.exe (PID: 8632)
- SetupUtil.exe (PID: 8476)
- AgentPackageAgentInformation.exe (PID: 8844)
The process executes VB scripts
- cmd.exe (PID: 7900)
- cmd.exe (PID: 8556)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 7716)
Starts a Microsoft application from unusual location
- 8-0-11.exe (PID: 4996)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 5304)
Starts itself from another location
- 8-0-11.exe (PID: 4996)
INFO
Application launched itself
- msedge.exe (PID: 2040)
Manages system restore points
- SrTasks.exe (PID: 4728)
The sample compiled with english language support
- rundll32.exe (PID: 7692)
- rundll32.exe (PID: 4996)
- rundll32.exe (PID: 1164)
- rundll32.exe (PID: 2064)
- AteraAgent.exe (PID: 7792)
- PreVerCheck.exe (PID: 8560)
- SplashtopStreamer.exe (PID: 8456)
- msiexec.exe (PID: 7716)
- SetupUtil.exe (PID: 8476)
- msiexec.exe (PID: 8632)
- AteraAgent.exe (PID: 6148)
- rundll32.exe (PID: 8328)
- rundll32.exe (PID: 6668)
- rundll32.exe (PID: 9192)
- 8-0-11.exe (PID: 4996)
- dotnet-runtime-8.0.11-win-x64.exe (PID: 5304)
- SplashtopStreamer.exe (PID: 924)
- 8-0-11.exe (PID: 9108)
- PreVerCheck.exe (PID: 2108)
Executable content was dropped or overwritten
- msedge.exe (PID: 5568)
- msedge.exe (PID: 2040)
- msiexec.exe (PID: 7716)
- msiexec.exe (PID: 8632)
Checks supported languages
- identity_helper.exe (PID: 6824)
- msiexec.exe (PID: 7716)
Reads Environment values
- identity_helper.exe (PID: 6824)
Reads the computer name
- identity_helper.exe (PID: 6824)
- msiexec.exe (PID: 7716)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2040)
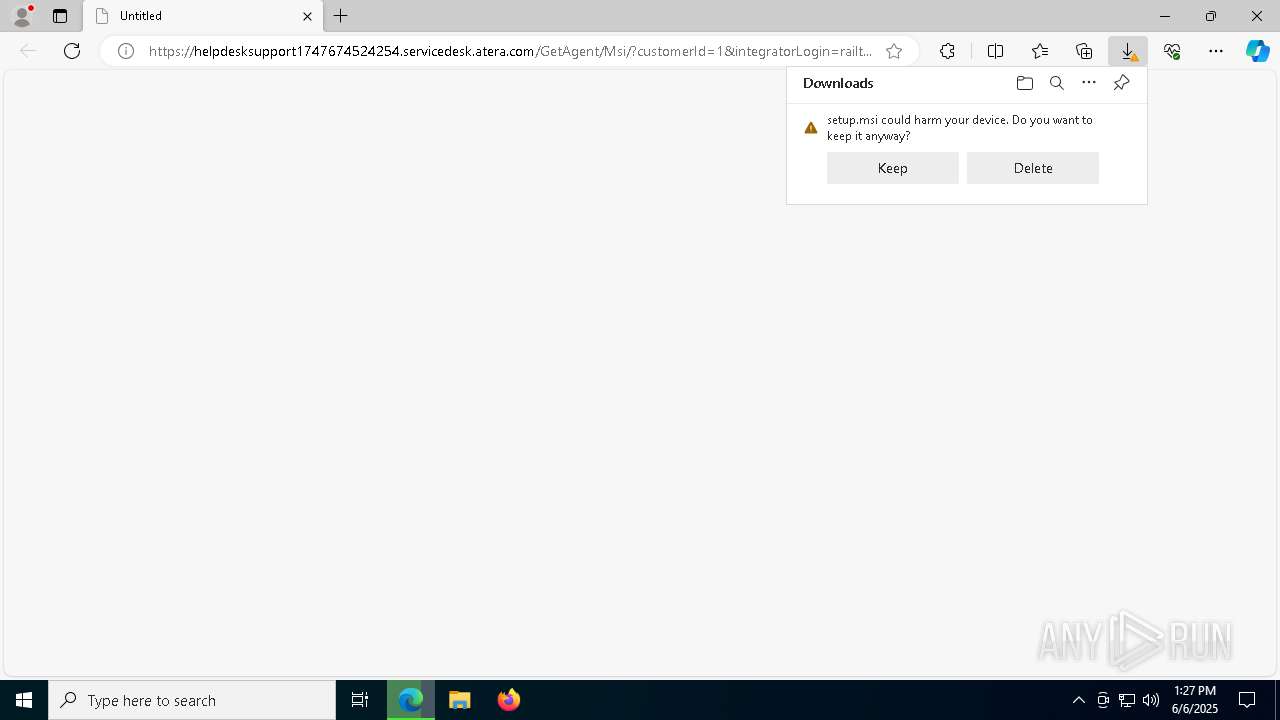
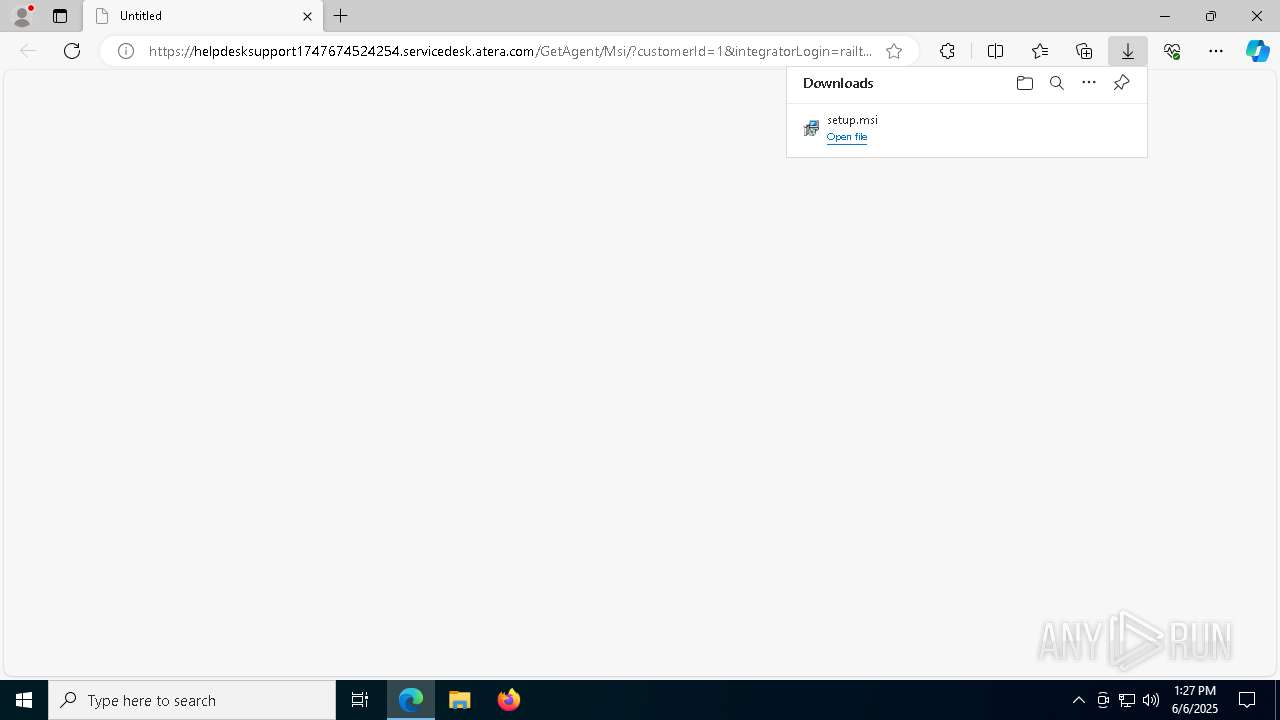
Launching a file from the Downloads directory
- msedge.exe (PID: 2040)
Reads the software policy settings
- msiexec.exe (PID: 7860)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
402
Monitored processes
267
Malicious processes
7
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5404 --field-trial-handle=2252,i,13859903311195230973,1571504055643007689,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 240 | "C:\Program Files (x86)\Splashtop\Splashtop Remote\Server\BdEpSDK.exe" -v | C:\Program Files (x86)\Splashtop\Splashtop Remote\Server\BdEpSDK.exe | — | SRAgent.exe | |||||||||||
User: SYSTEM Company: Splashtop Inc. Integrity Level: SYSTEM Description: SplashtopR Streamer BdEpSDK Exit code: 4294967294 Version: 1.0.0.8 Modules
| |||||||||||||||
| 404 | C:\WINDOWS\TEMP\{7BECBC4F-2D1E-4581-913B-85A174C60B5B}\_is7A39.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{75695142-5BB5-4CEB-B702-FE5179C7CA59} | C:\Windows\Temp\{7BECBC4F-2D1E-4581-913B-85A174C60B5B}\_is7A39.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Flexera Integrity Level: SYSTEM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 27.0.122 Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe" 898b25bf-aa43-48f3-844b-dc922a10d5ef "b50bc889-889d-483a-a3fe-a2552868804a" agent-api.atera.com/Production 443 or8ixLi90Mf "minimalIdentification" 001Q300000TNUrDIAX | C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe | AteraAgent.exe | ||||||||||||
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageAgentInformation Exit code: 0 Version: 40.4.0.0 Modules
| |||||||||||||||
| 536 | cscript "C:\Program Files\Microsoft Office\Office16\ospp.vbs" /dstatus | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft ® Console Based Script Host Exit code: 255 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 772 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 840 | "TaskKill.exe" /f /im AteraAgent.exe | C:\Windows\SysWOW64\taskkill.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5668 --field-trial-handle=2252,i,13859903311195230973,1571504055643007689,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Windows\System32\sc.exe" failure AteraAgent reset= 600 actions= restart/25000 | C:\Windows\System32\sc.exe | — | AteraAgent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "C:\WINDOWS\TEMP\SplashtopStreamer.exe" prevercheck /s /i sec_opt=0,confirm_d=0,hidewindow=1 | C:\Windows\Temp\SplashtopStreamer.exe | AgentPackageSTRemote.exe | ||||||||||||
User: SYSTEM Company: Splashtop Inc. Integrity Level: SYSTEM Description: Splashtop® Streamer Exit code: 0 Version: 3.74.2.21 Modules
| |||||||||||||||
Total events
118 997
Read events
117 500
Write events
1 326
Delete events
171
Modification events
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 721ECD797D952F00 | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1AE8D4797D952F00 | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {21806F93-748A-45EB-A3E4-DEEDCDE21F6C} | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6E0CCD1E-A9BA-4108-B00B-C99B8A7F2C55} | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (2040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
733
Suspicious files
538
Text files
282
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF120b04.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF120b24.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF120b24.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF120b33.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF120b33.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF120b52.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
106
DNS requests
73
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4616 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2040 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2040 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
2040 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAnTy%2FhDMohv9omwS69%2Fdow%3D | unknown | — | — | whitelisted |
2148 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2148 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7740 | AteraAgent.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4616 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
7924 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2040 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5568 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | msedge.exe | 20.101.44.219:443 | helpdesksupport1747674524254.servicedesk.atera.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
helpdesksupport1747674524254.servicedesk.atera.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4996 | rundll32.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7792 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
2064 | rundll32.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7792 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7792 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7792 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
1548 | AgentPackageAgentInformation.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
496 | AgentPackageAgentInformation.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7792 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7792 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
Process | Message |
|---|---|
AgentPackageMonitoring.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageMonitoring\x64\SQLite.Interop.dll"...
|
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUtility::OSInfo] OS 10.0(19045) x64:1 (Last=0) |
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUnPack::FindHeader] Name:C:\WINDOWS\TEMP\SplashtopStreamer.exe (Last=0) |
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUnPack::UnPackFiles] FreeSpace:231753728000 FileSize:60981760 (Last=0) |
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUnPack::FindHeader] Sign Size:10376 (Last=0) |
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUnPack::FindHeader] Header offset:434176 (Last=183) |
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUnPack::UnPackFiles] (1/5)UnPack file name:C:\WINDOWS\TEMP\unpack\setup.msi (60981760) (Last=0) |
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUnPack::UnPackFiles] (2/5)UnPack file name:C:\WINDOWS\TEMP\unpack\run.bat (15) (Last=122) |
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUnPack::UnPackFiles] UnPack count:2 len:15 File:(null) (Last=0) |
SplashtopStreamer.exe | [8456]2025-06-06 13:28:38 [CUnPack::UnPackFiles] FreeSpace:231692722176 FileSize:1528 (Last=183) |