| File name: | dhavi.exe |
| Full analysis: | https://app.any.run/tasks/2c846cec-5a0b-42a9-883a-d2a146616430 |
| Verdict: | Suspicious activity |
| Analysis date: | September 23, 2019, 14:25:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DABAE7B121575AA2ABDBF5D555820FE6 |
| SHA1: | 16E0666DED1F90745D3FAE092A79BE32ECCA481A |
| SHA256: | 0EF1AF62838DF9DB4ABF73CF9FCF55AABE7FA8F8315B06B8DE52CCCABB32DC2F |
| SSDEEP: | 12288:MJTxCHRkaR4mLYdbsGpkspCyRoowhtIKxVGNAnmuk6Nuf59:MHqRfRDGpbTQRKN9uk6NGX |
MALICIOUS
Application was dropped or rewritten from another process
- dhavi_.exe (PID: 1756)
Loads dropped or rewritten executable
- dhavi_.exe (PID: 1756)
Changes the autorun value in the registry
- dhavi.exe (PID: 3320)
SUSPICIOUS
Executable content was dropped or overwritten
- dhavi.exe (PID: 3320)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:04:13 20:32:45+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 39424 |
| InitializedDataSize: | 623104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x645c |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.31.0.4444 |
| ProductVersionNumber: | 3.31.0.4444 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
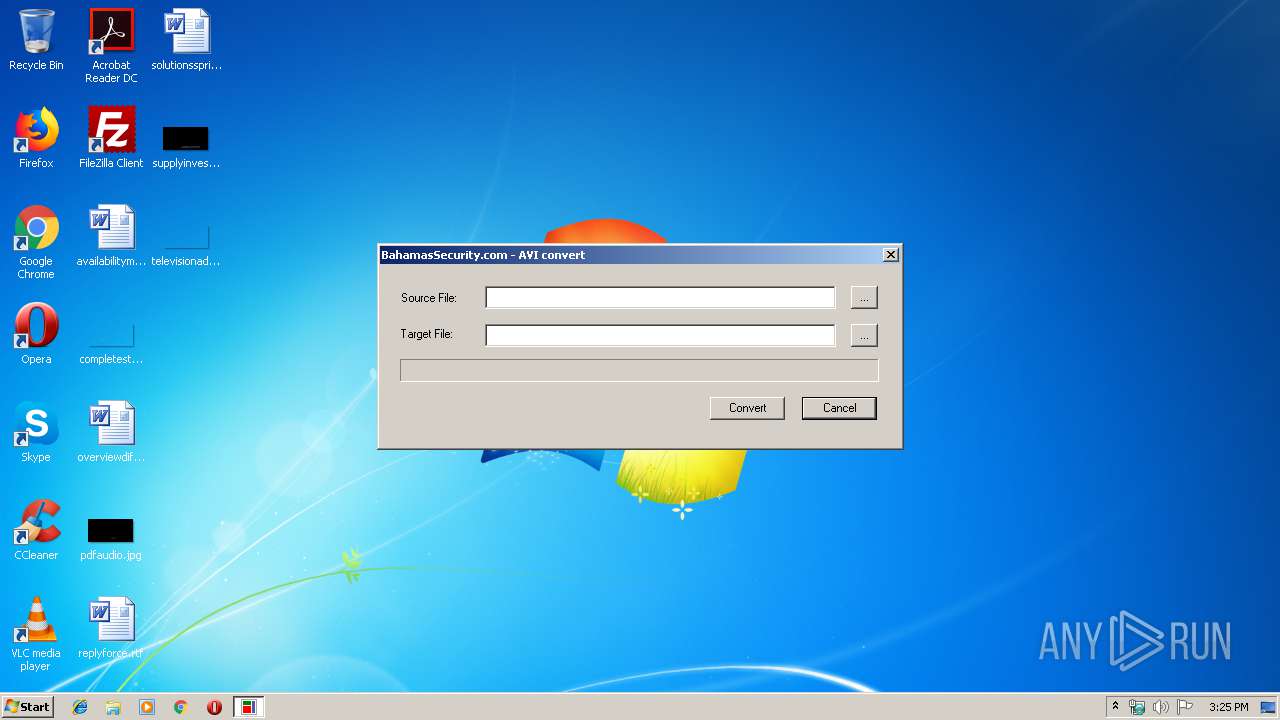
| CompanyName: | BahamasSecurity.com |
| FileDescription: | Dahua AVI Convert |
| FileVersion: | 3, 31, 0, 4444 |
| InternalName: | dhavi |
| LegalCopyright: | Copyright (C) 2012 |
| LegalTrademarks: | - |
| OriginalFileName: | dhplayer |
| PrivateBuild: | - |
| ProductName: | Dahua AVI Convert |
| ProductVersion: | 3, 31, 0, 4444 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Apr-2008 18:32:45 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | BahamasSecurity.com |
| FileDescription: | Dahua AVI Convert |
| FileVersion: | 3, 31, 0, 4444 |
| InternalName: | dhavi |
| LegalCopyright: | Copyright (C) 2012 |
| LegalTrademarks: | - |
| OriginalFilename: | dhplayer |
| PrivateBuild: | - |
| ProductName: | Dahua AVI Convert |
| ProductVersion: | 3, 31, 0, 4444 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Apr-2008 18:32:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000099C8 | 0x00009A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57773 |
.data | 0x0000B000 | 0x00001BE4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.248 |
.rsrc | 0x0000D000 | 0x00097D2C | 0x00097E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98755 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40277 | 892 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 6.14112 | 2216 | UNKNOWN | English - United States | RT_ICON |
63 | 2.48958 | 140 | Latin 1 / Western European | English - United States | RT_STRING |
76 | 3.2674 | 1312 | Latin 1 / Western European | English - United States | RT_STRING |
77 | 3.29977 | 1484 | Latin 1 / Western European | English - United States | RT_STRING |
80 | 3.27174 | 1200 | Latin 1 / Western European | English - United States | RT_STRING |
83 | 3.2912 | 1098 | Latin 1 / Western European | English - United States | RT_STRING |
85 | 3.13591 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
3000 | 2.32824 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
ADMQCMD | 2.80735 | 7 | Latin 1 / Western European | English - United States | RT_RCDATA |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1756 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dhavi_.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dhavi_.exe | — | dhavi.exe | |||||||||||
User: admin Company: BahamasSecurity.com Integrity Level: MEDIUM Description: Dahua AVI Convert Exit code: 0 Version: 3, 31, 0, 4444 Modules
| |||||||||||||||
| 3320 | "C:\Users\admin\AppData\Local\Temp\dhavi.exe" | C:\Users\admin\AppData\Local\Temp\dhavi.exe | explorer.exe | ||||||||||||
User: admin Company: BahamasSecurity.com Integrity Level: MEDIUM Description: Dahua AVI Convert Exit code: 0 Version: 3, 31, 0, 4444 Modules
| |||||||||||||||
Total events
1
Read events
0
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3320) dhavi.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
Executable files
9
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\MP3Decoder.dll | executable | |
MD5:CEF5B19A69D8F9212CEEF5E87525BA9F | SHA256:A0FE0F56BD34627C20F94966E62F668E4EF01C02636E2A031D8F4FDEE0542D6F | |||
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\jpegdec.dll | executable | |
MD5:39C0F19E0522080D07FA7959370BDE88 | SHA256:21C04BE26FDEB54458D54F98336578DF838555C1F409B3114A86A4B4B00B8DBD | |||
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dllmpeg4.dll | executable | |
MD5:FC7A2841FB81544E75706FA1B1D5DF43 | SHA256:EBC950EF380D2A06A1570A8C9773639205D06D1ACBB70BCBA7F3957308620FE3 | |||
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dllh264.dll | executable | |
MD5:9EAAECC5EC8272CB03770DC1B011C483 | SHA256:E4A53FE452930DBA7B19F3E553B84BCD55B84522BECC6EE00C13E49FEB977D3D | |||
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dhplay.dll | executable | |
MD5:F2E23B6AA2894420D0486BB3AB042502 | SHA256:F795B68849D311249FD0AD9B606A47C52E1FCCB66C3FF9E4DB239312857454E0 | |||
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AACDecoder.dll | executable | |
MD5:CBE124335264E8B89C36FAC3627F7F92 | SHA256:68076B56B36FDD5670507B008469EAC704D1758F76935C61EBA3AF98B404E210 | |||
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dhavi_.exe | executable | |
MD5:9778C976B2CA2F016285B227D9587A9B | SHA256:0DC739A3DB96C823E720048C6B36638759D840B5CB6084672CE937935398EE4D | |||
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\DllDeinterlace.dll | executable | |
MD5:8D3B62A4C04F5D00D3EB4DBC6445F7C3 | SHA256:ECF16A6ABDB777DE4F45CBBF7EB491698C7947F2786F22C7590EA08B5AD869CE | |||
| 3320 | dhavi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AmrDll.dll | executable | |
MD5:A2CC8A53E8CF1E426AFE6EC1043163F0 | SHA256:F04B4B508F38C02AE19949ABEE62684510A0B1FEA6B400C2B0A7D6C83270CE34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report