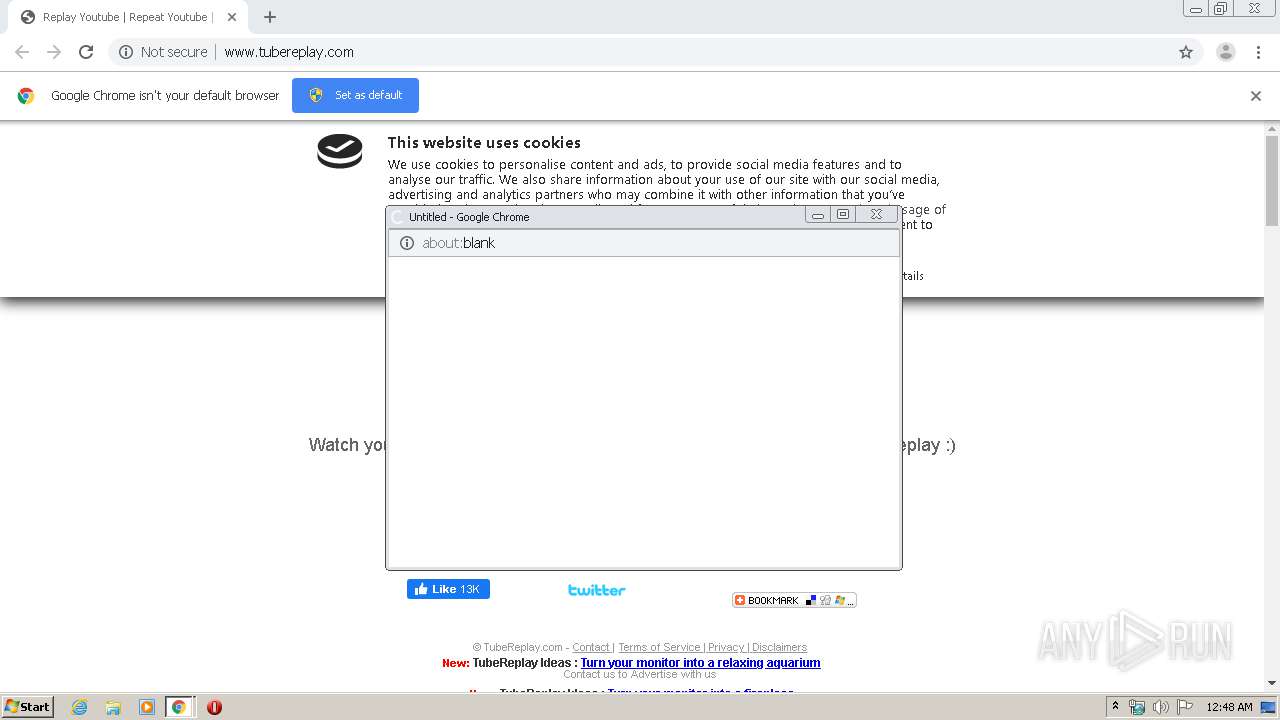
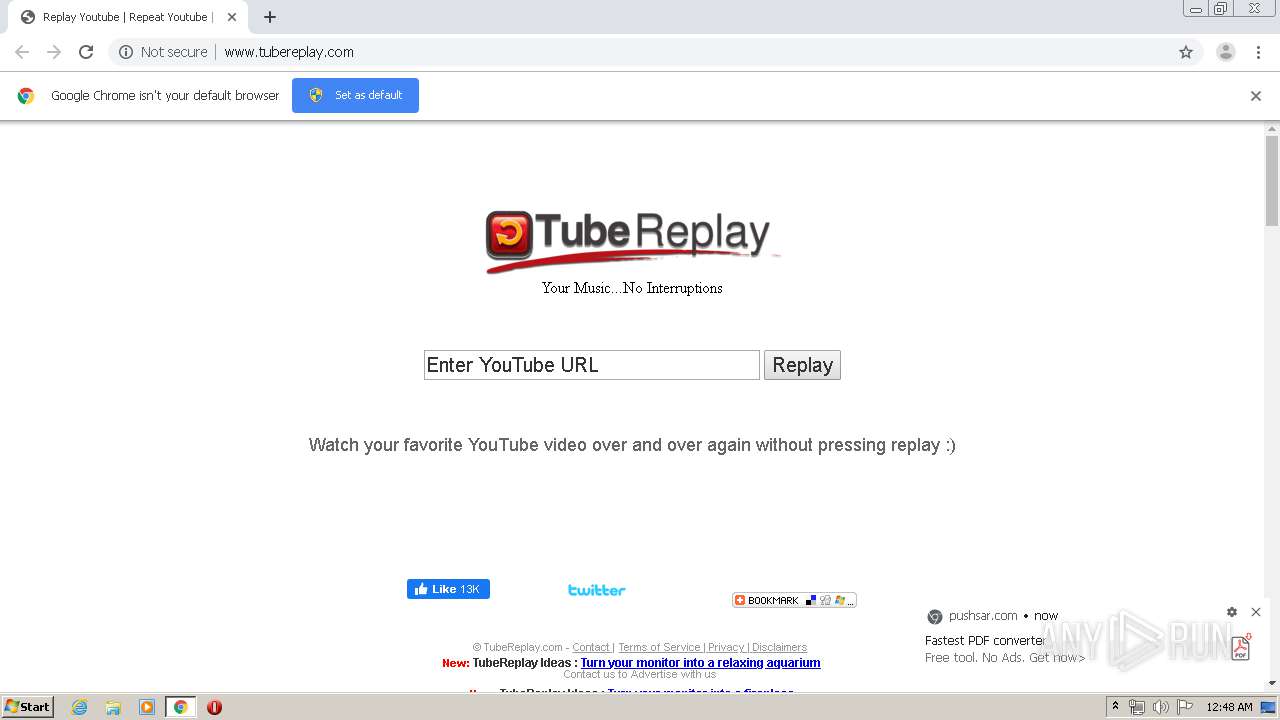
| URL: | http://www.tubereplay.com/ |
| Full analysis: | https://app.any.run/tasks/d537fdde-1d66-4400-b095-a0a788701e00 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 00:47:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 34D1ECA083457C1FD0D1F48AC916D2B8 |
| SHA1: | B255F4BDFB847AA5F128E28AE13BD455C3FB3393 |
| SHA256: | 0EE4C3909EDAF83D1AD0E2D1498BBEDF4A4983A276A17633D2DE196DC1178720 |
| SSDEEP: | 3:N1KJS4twSK3n:Cc4G53 |
MALICIOUS
No malicious indicators.SUSPICIOUS
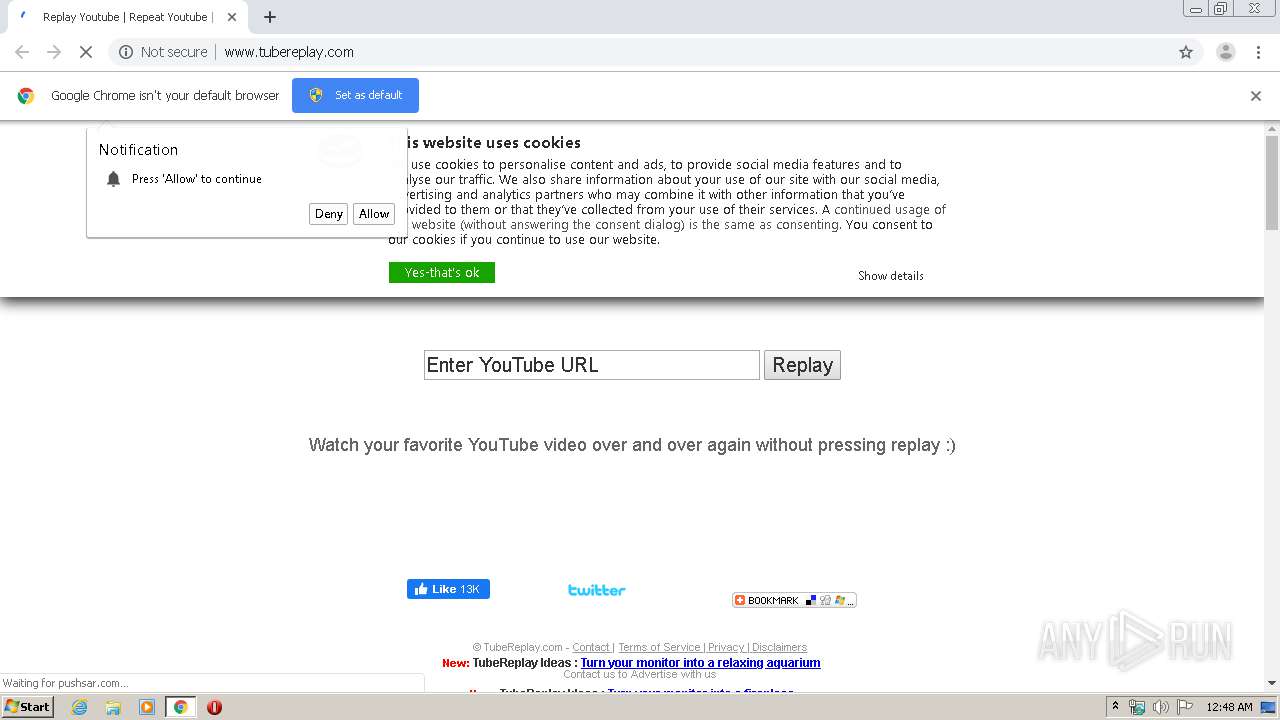
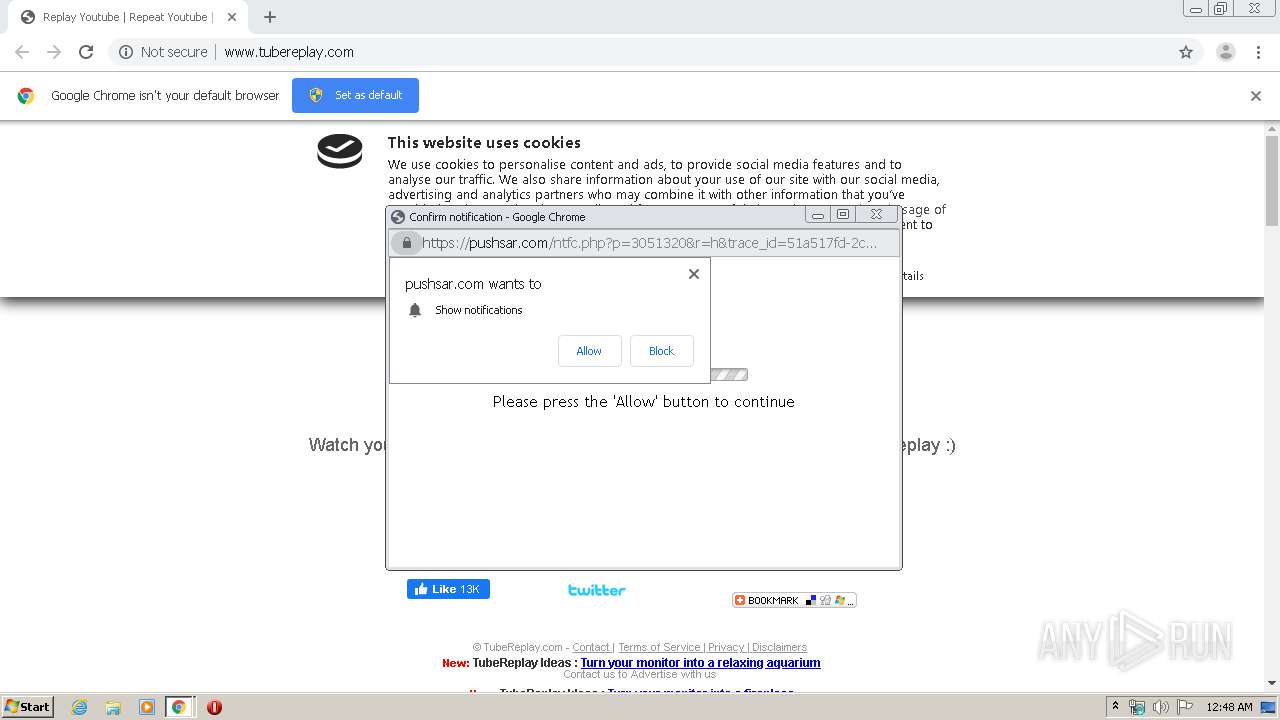
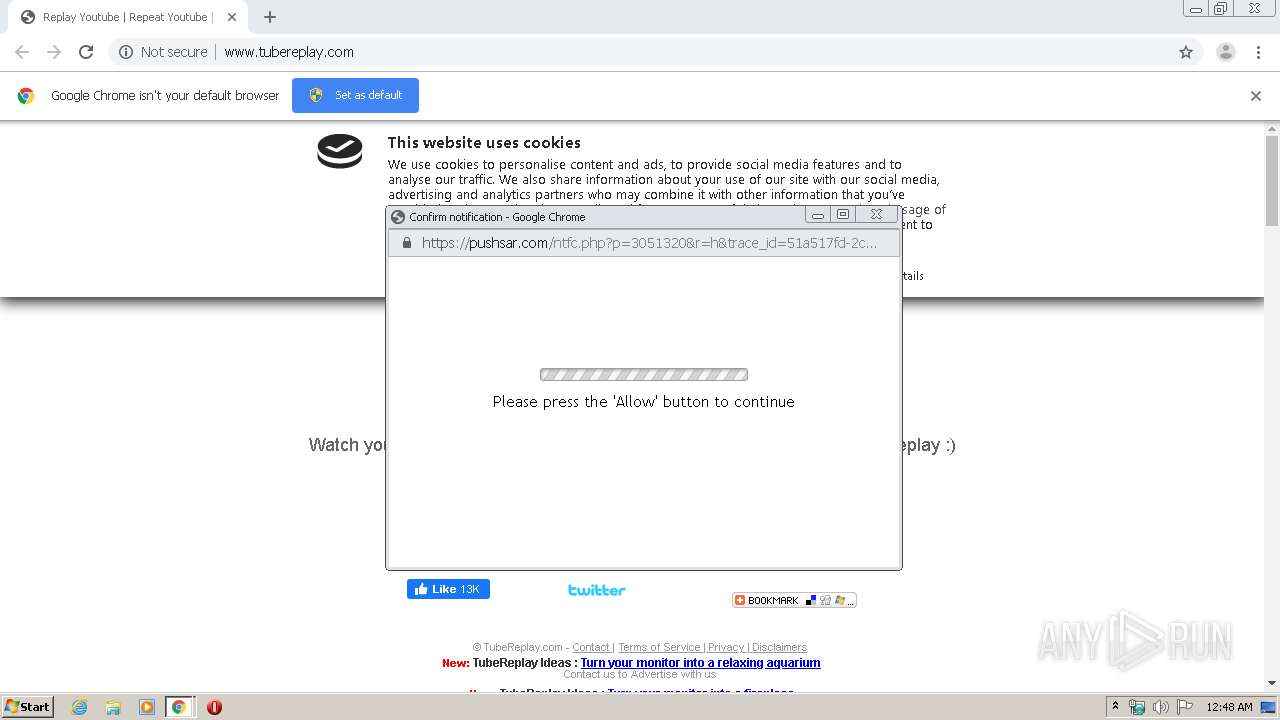
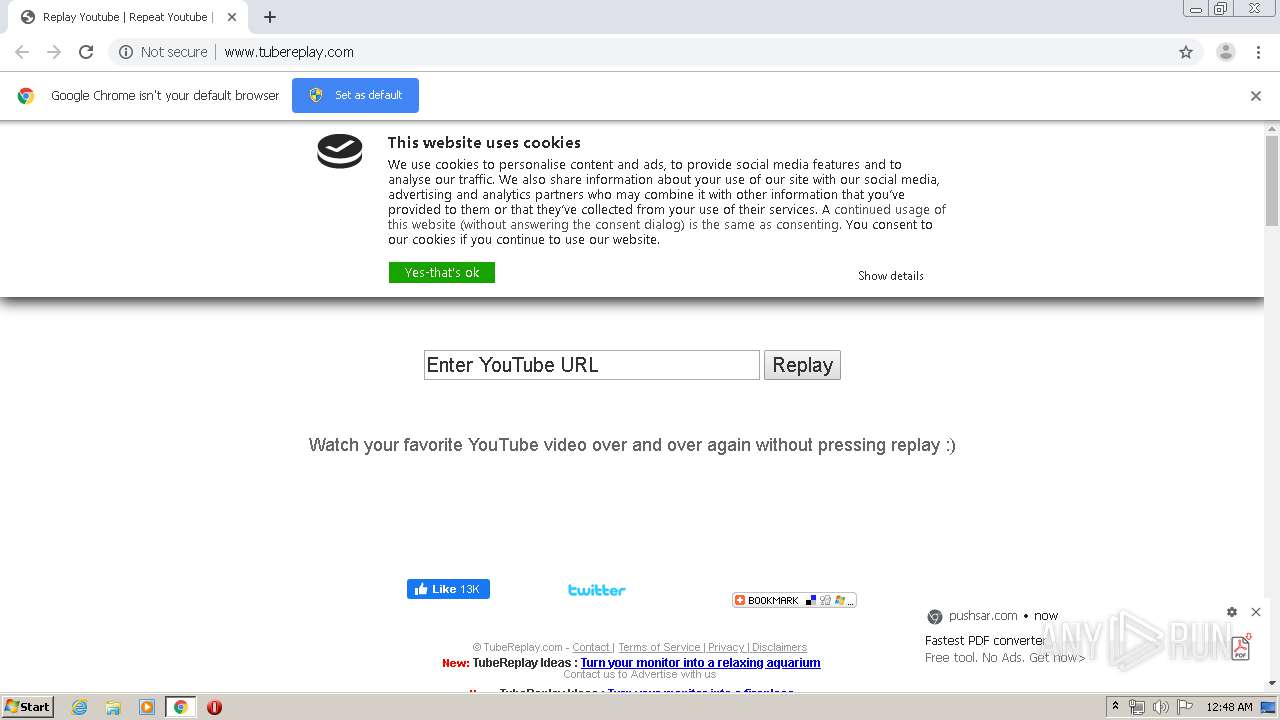
Modifies files in Chrome extension folder
- chrome.exe (PID: 3924)
INFO
Application launched itself
- chrome.exe (PID: 3924)
Reads the hosts file
- chrome.exe (PID: 3960)
- chrome.exe (PID: 3924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2419832560827717672 --mojo-platform-channel-handle=5588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8043602117763616005 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1048910834173773453 --mojo-platform-channel-handle=4404 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8931831851442175851 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5812344403057136831 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3052 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11100349398089787472 --mojo-platform-channel-handle=5728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14035261799510245926 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13854119272678163842 --mojo-platform-channel-handle=4556 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3348642055562109217,10350340324290237480,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12628791299966653329 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
644
Read events
559
Write events
80
Delete events
5
Modification events
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3924-13226806077720500 |
Value: 259 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
53
Text files
281
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E507A3E-F54.pma | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2ef7e1c2-fd61-45c3-9364-8e6454e839ee.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66d0a.TMP | text | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66f3d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
68
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3960 | chrome.exe | GET | — | 104.28.20.190:80 | http://www.tubereplay.com/ | US | — | — | suspicious |
3960 | chrome.exe | GET | 204 | 2.16.186.80:80 | http://b.scorecardresearch.com/b2?c1=7&c2=2000001&c3=1&rn=dkv0kj&c7=http%3A%2F%2Fwww.tubereplay.com%2F&c8=Replay%20Youtube%20%7C%20Repeat%20Youtube%20%7C%20TubeReplay&cv=1.7&cs_ak_ss=1 | unknown | — | — | whitelisted |
3960 | chrome.exe | GET | 302 | 2.16.186.80:80 | http://b.scorecardresearch.com/b?c1=7&c2=2000001&c3=1&rn=dkv0kj&c7=http%3A%2F%2Fwww.tubereplay.com%2F&c8=Replay%20Youtube%20%7C%20Repeat%20Youtube%20%7C%20TubeReplay&cv=1.7 | unknown | — | — | whitelisted |
3960 | chrome.exe | GET | 302 | 23.210.248.44:80 | http://m.addthis.com/live/red_lojson/100lo.json?1837mwn&colc=1582332484145&si=5e507a410ff147e1&uid=5e507a443d166175&pub=tubereplay&rev=18.4-edge&jsl=32&ln=en&pc=men&vpc=&dp=www.tubereplay.com&aa=0&of=0&uf=1&nt=cs;8,ce;36,dc;146,dclee;146,dcles;146,di;146,dl;116,dle;8,dls;8,fs;0,lee;u,les;146,ns;1,rs;36,rspe;124,rsps;111,scs;u&pd=0&irt=0&ct=0&tct=0&abt=0<=176&cdn=0&lnlc=US&whcs=1&tl=c%3D744%2Cm%3D3421%2Ci%3D3430%2Cxm%3D3598%2Cxp%3D3603&pi=1&&rb=0&gen=1000&gen=100&callback=_ate.track.hsr&mk=replay%20youtube%20video%2Crepeat%20video%2Cyoutube%20replay%2Cautoreplay%2Ctubereplay&uvs=5e507a4174103752000&chr=UTF-8&md=0&vcl=0 | NL | — | — | shared |
3960 | chrome.exe | GET | 200 | 104.28.20.190:80 | http://www.tubereplay.com/twitter.png | US | image | 1.67 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 104.28.20.190:80 | http://www.tubereplay.com/uo.png | US | image | 1.67 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 104.28.20.190:80 | http://www.tubereplay.com/images/logo/logo.png | US | image | 6.25 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 104.28.20.190:80 | http://www.tubereplay.com/images/christmas-songs.jpg | US | image | 17.2 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 104.28.20.190:80 | http://www.tubereplay.com/replaybt.png | US | image | 3.98 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 104.28.20.190:80 | http://www.tubereplay.com/favicon.ico | US | image | 1.67 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3960 | chrome.exe | 88.85.82.156:80 | pushsar.com | Webzilla B.V. | NL | suspicious |
3960 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
3960 | chrome.exe | 172.217.22.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 13.35.253.90:443 | cdn.eventfinda.co.nz | — | US | malicious |
3960 | chrome.exe | 152.195.39.166:80 | townsquare.media | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
3960 | chrome.exe | 104.28.20.190:80 | www.tubereplay.com | Cloudflare Inc | US | shared |
3960 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 160.153.71.6:80 | thinkdeeplyspeaksimply.com | GoDaddy.com, LLC | US | unknown |
3960 | chrome.exe | 172.217.16.129:443 | 4.bp.blogspot.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 31.13.92.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.tubereplay.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
pushsar.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
townsquare.media |
| unknown |
cdn.eventfinda.co.nz |
| whitelisted |
4.bp.blogspot.com |
| whitelisted |
thinkdeeplyspeaksimply.com |
| unknown |