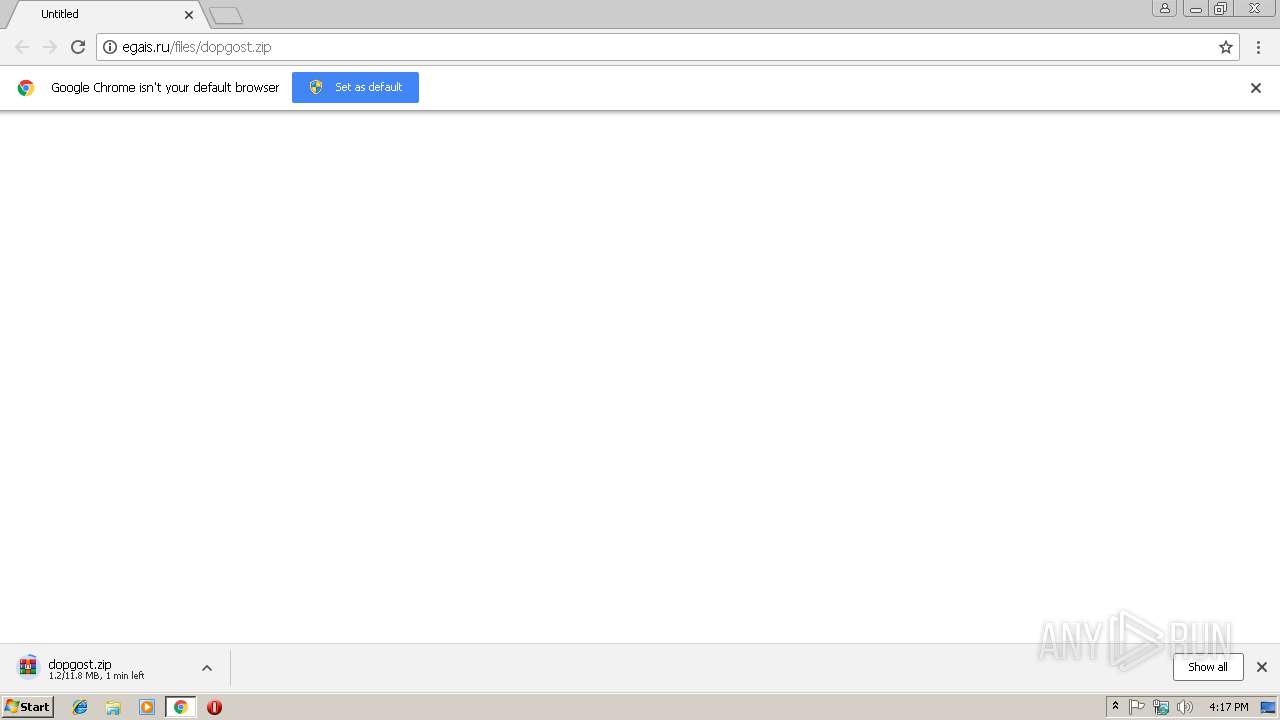
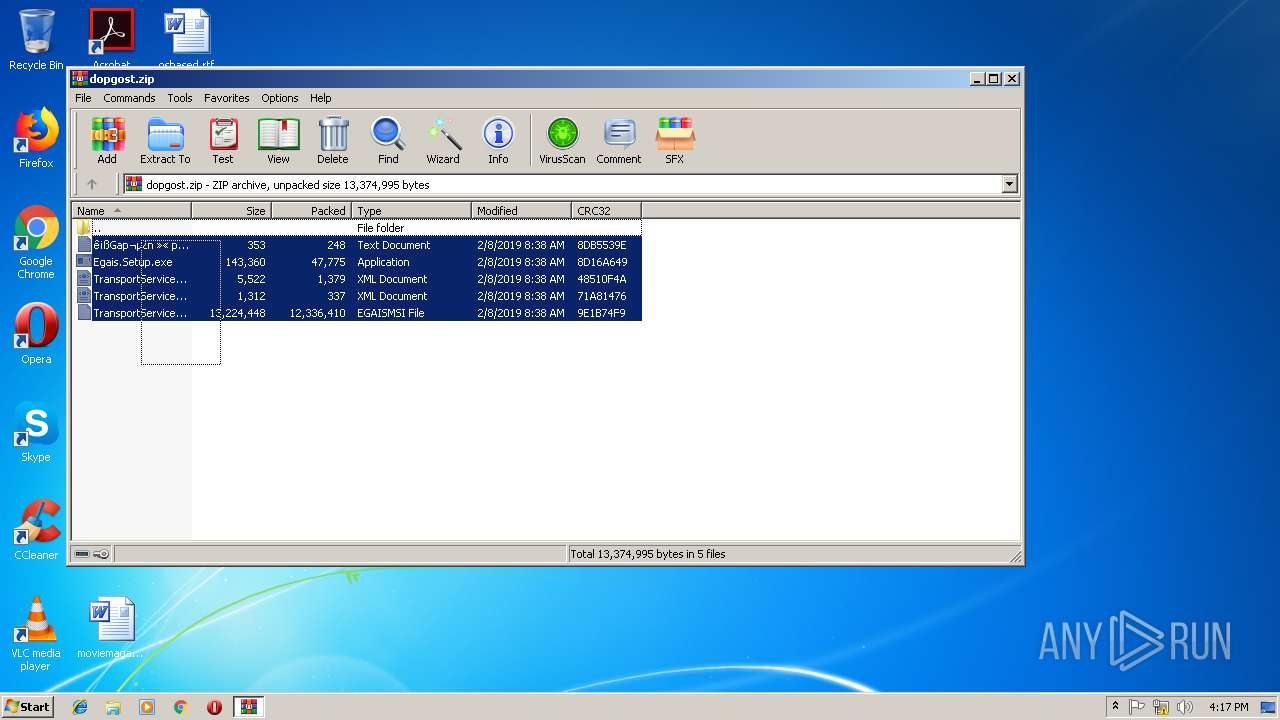
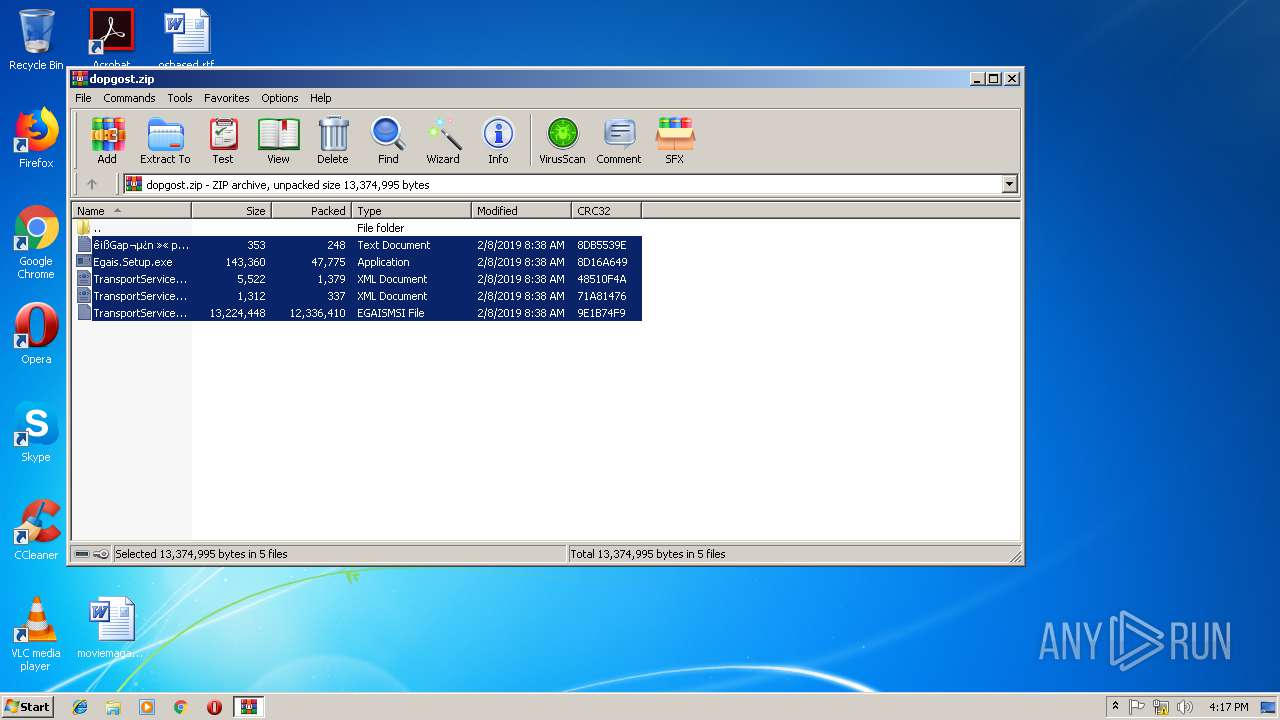
| URL: | http://egais.ru/files/dopgost.zip |
| Full analysis: | https://app.any.run/tasks/5beb97e0-4e86-4123-b43b-8c69015dcec7 |
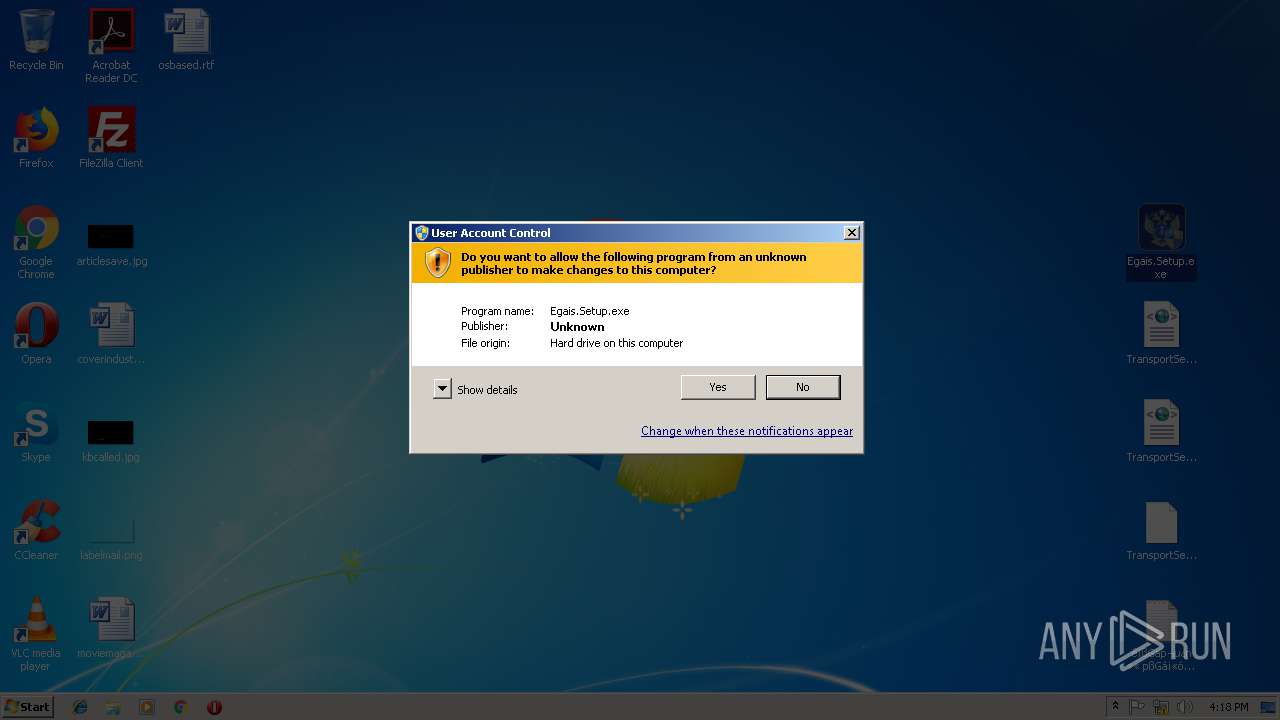
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 16:16:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 07E88FFA077869C1517BD5577AB5C4DD |
| SHA1: | 624E8E3F6E78F06048E01977060ED1893EE53B93 |
| SHA256: | 0EE2C59308318F97AC4192EF5EE2570C28DC78BAF8A8C85D69E4A96677DBFC2A |
| SSDEEP: | 3:N1KbH8fmJRLfUn:Cz8ELc |
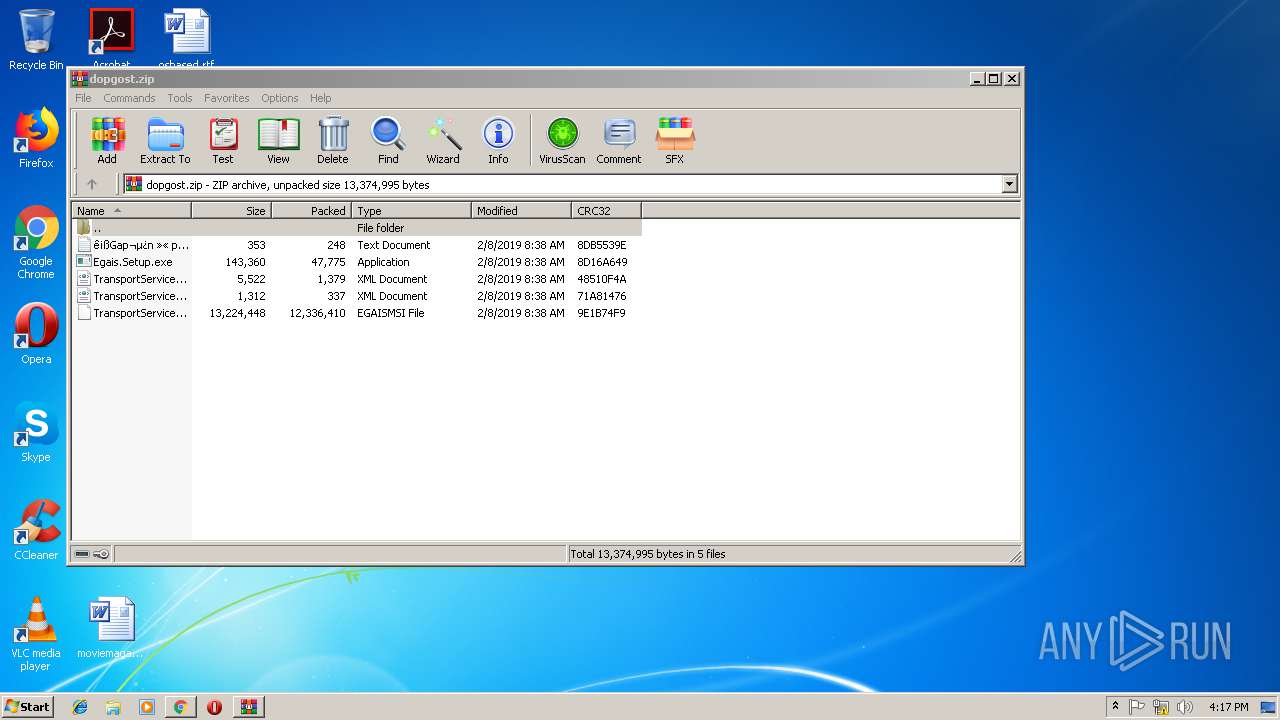
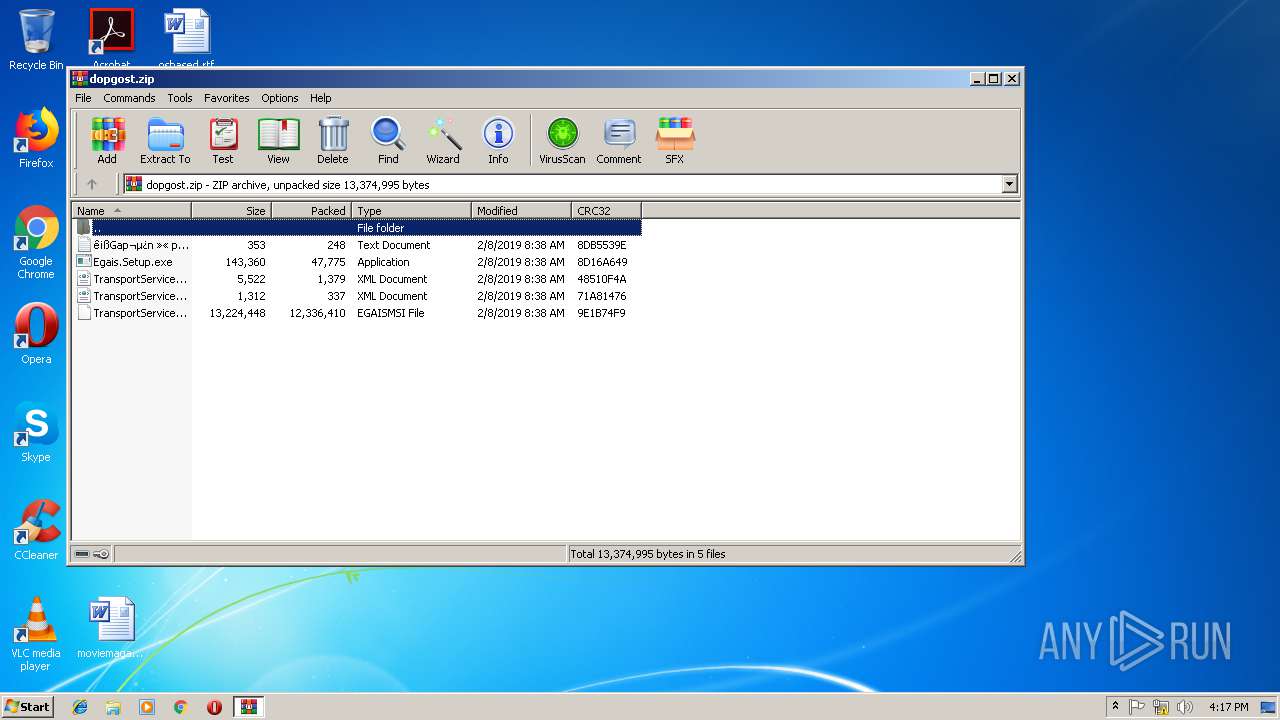
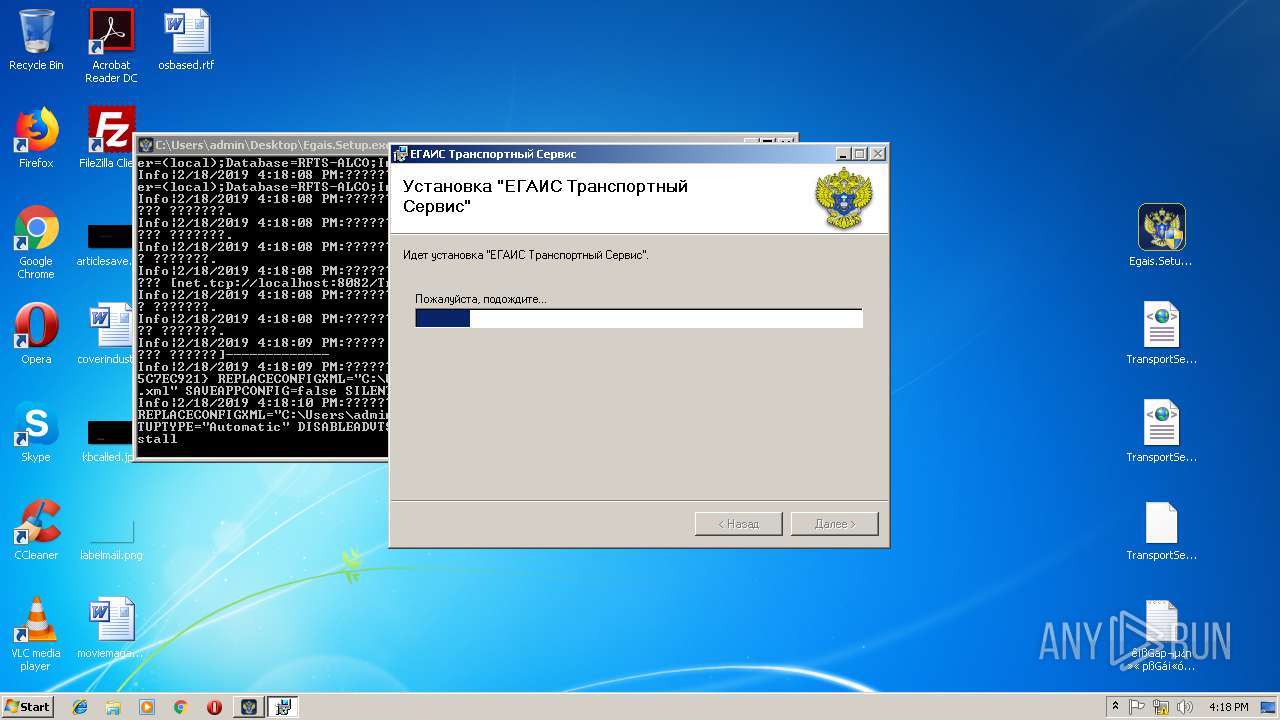
MALICIOUS
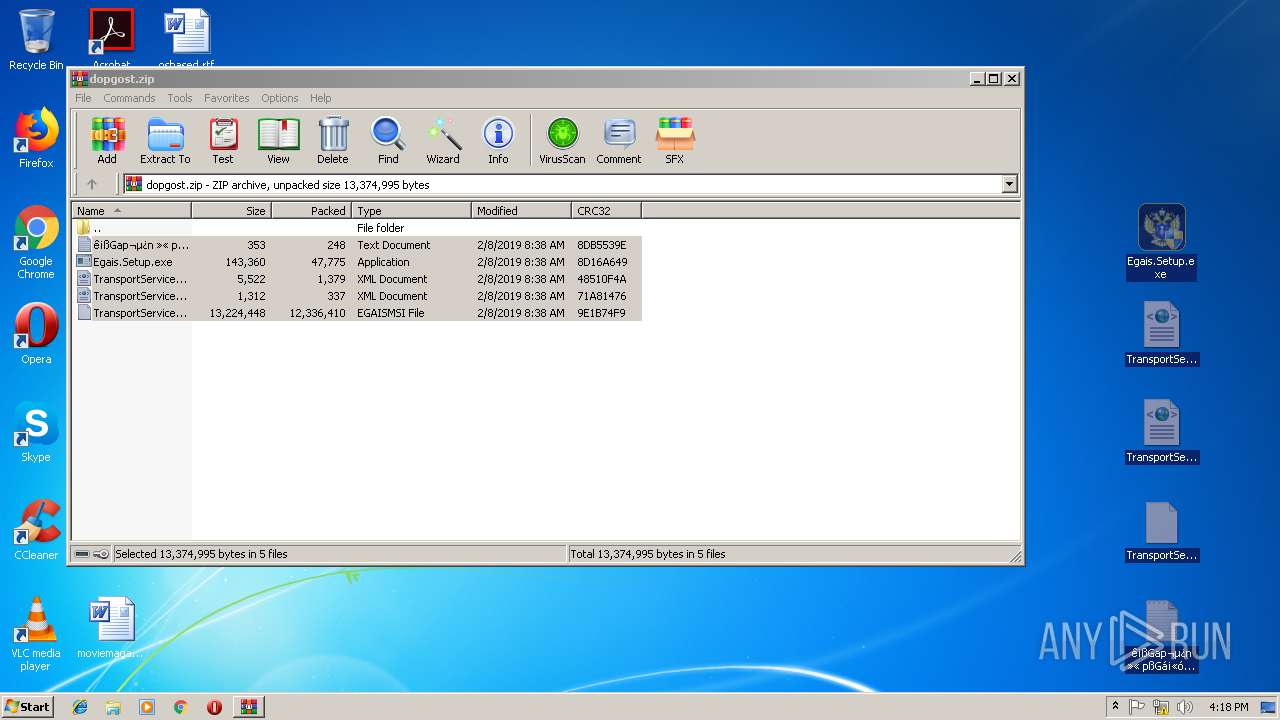
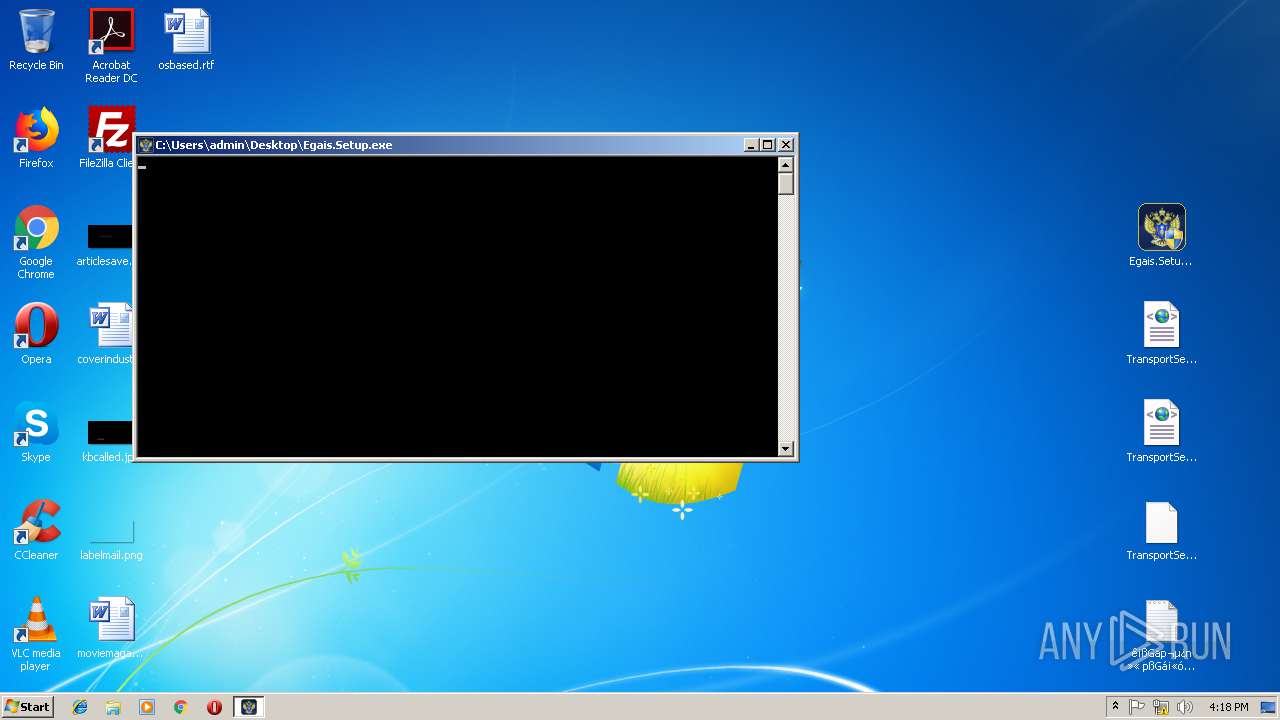
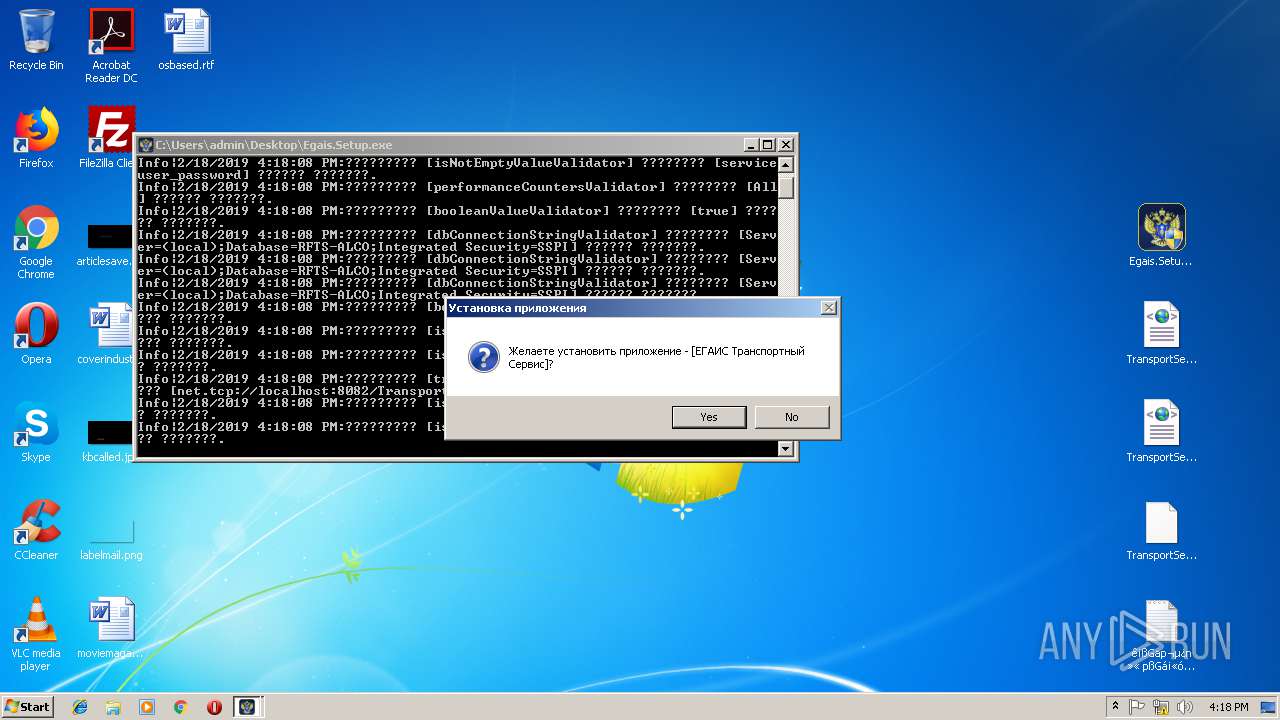
Application was dropped or rewritten from another process
- Egais.Setup.exe (PID: 3836)
- Egais.Setup.exe (PID: 2228)
- RemoteInstallService.exe (PID: 2436)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2720)
- msiexec.exe (PID: 3512)
Creates files in the Windows directory
- Installutil.exe (PID: 2508)
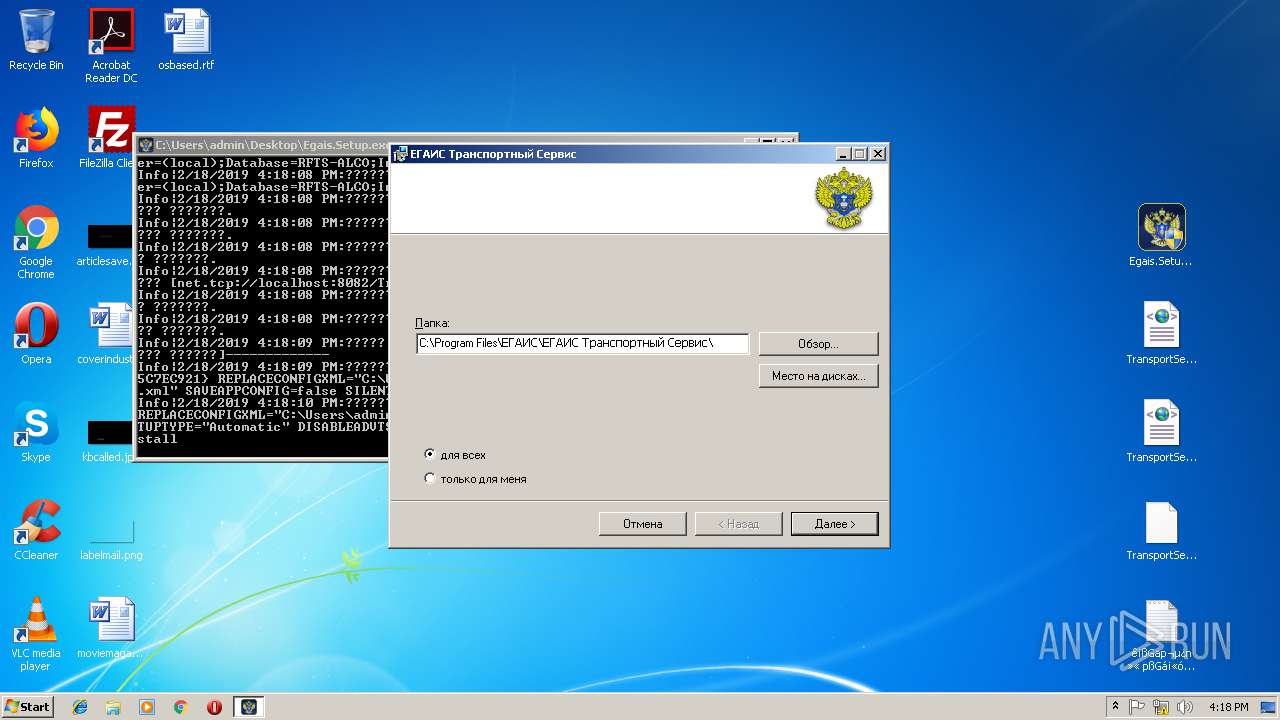
Creates files in the program directory
- Installutil.exe (PID: 2508)
INFO
Application launched itself
- chrome.exe (PID: 3428)
- msiexec.exe (PID: 3512)
Reads Internet Cache Settings
- chrome.exe (PID: 3428)
Creates files in the user directory
- chrome.exe (PID: 3428)
Searches for installed software
- msiexec.exe (PID: 3512)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2316)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3560)
- msiexec.exe (PID: 3512)
Creates files in the program directory
- MsiExec.exe (PID: 3560)
- msiexec.exe (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
29
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 992 | C:\Windows\system32\MsiExec.exe -Embedding 380300894EA4F396247142A13CDC4731 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1700 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES99A2.tmp" "c:\Users\admin\AppData\Local\Temp\CSC99A1.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1820 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\9x9vfwvj.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | Egais.Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
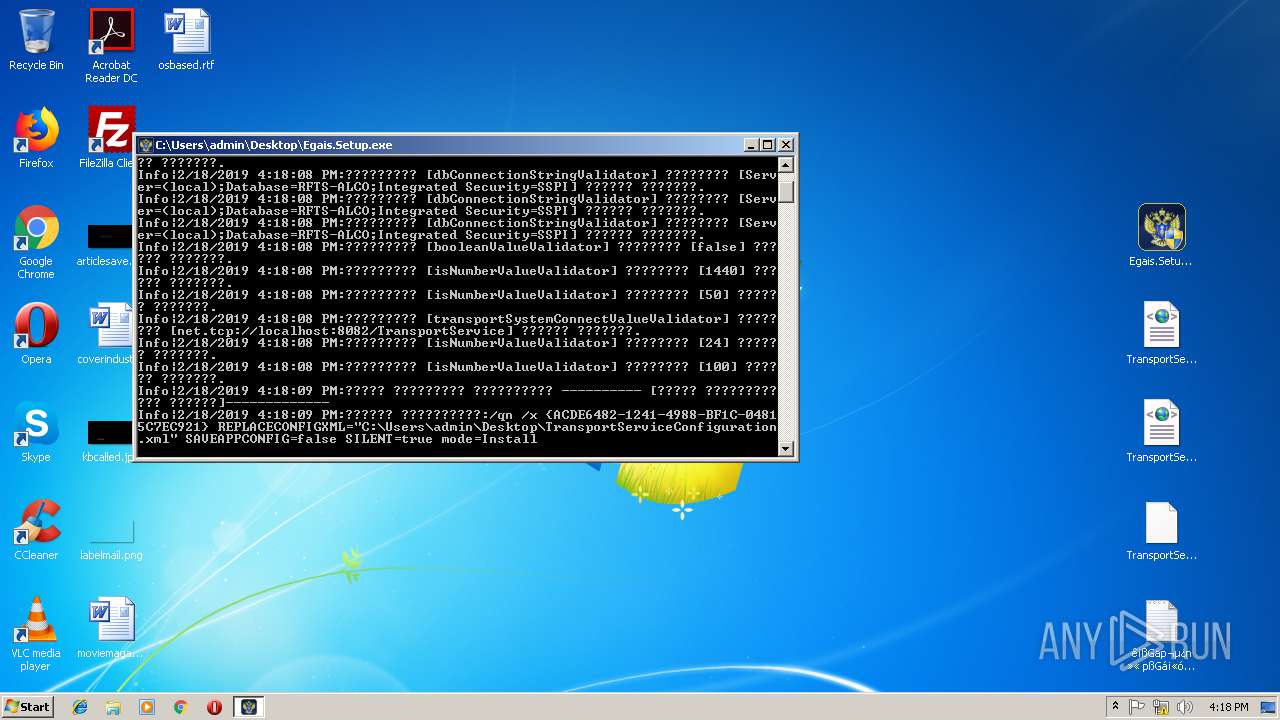
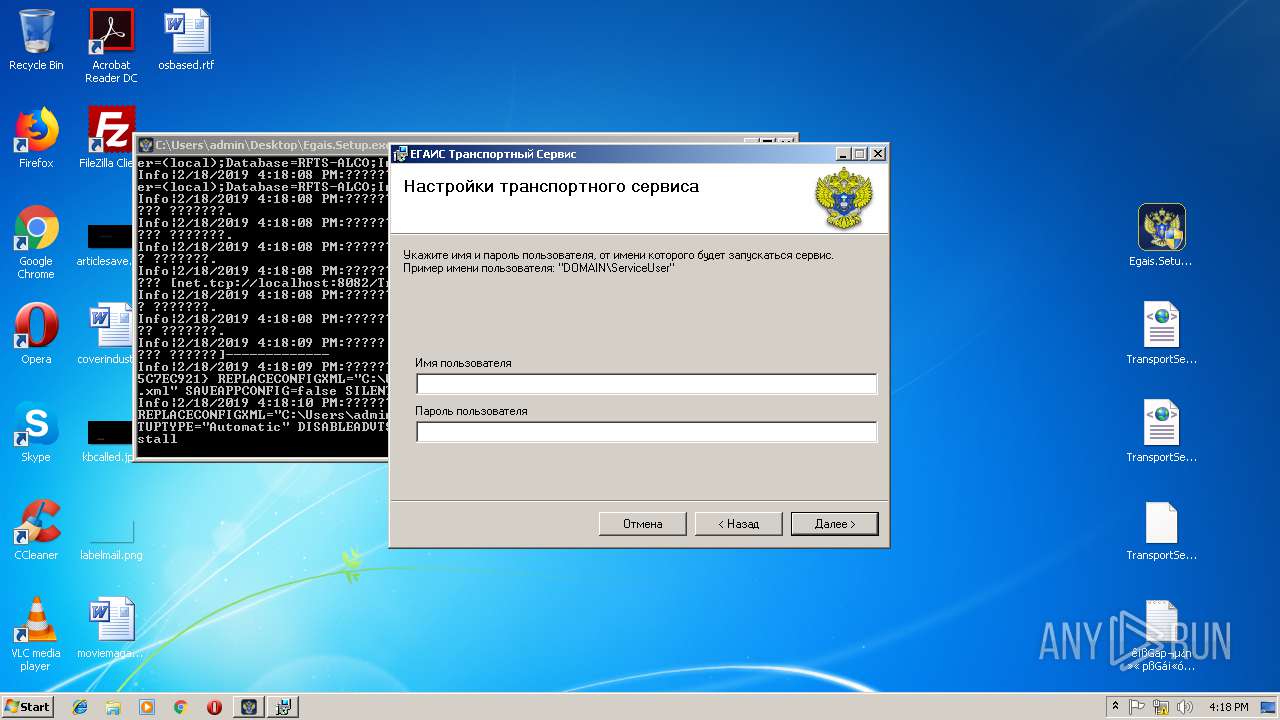
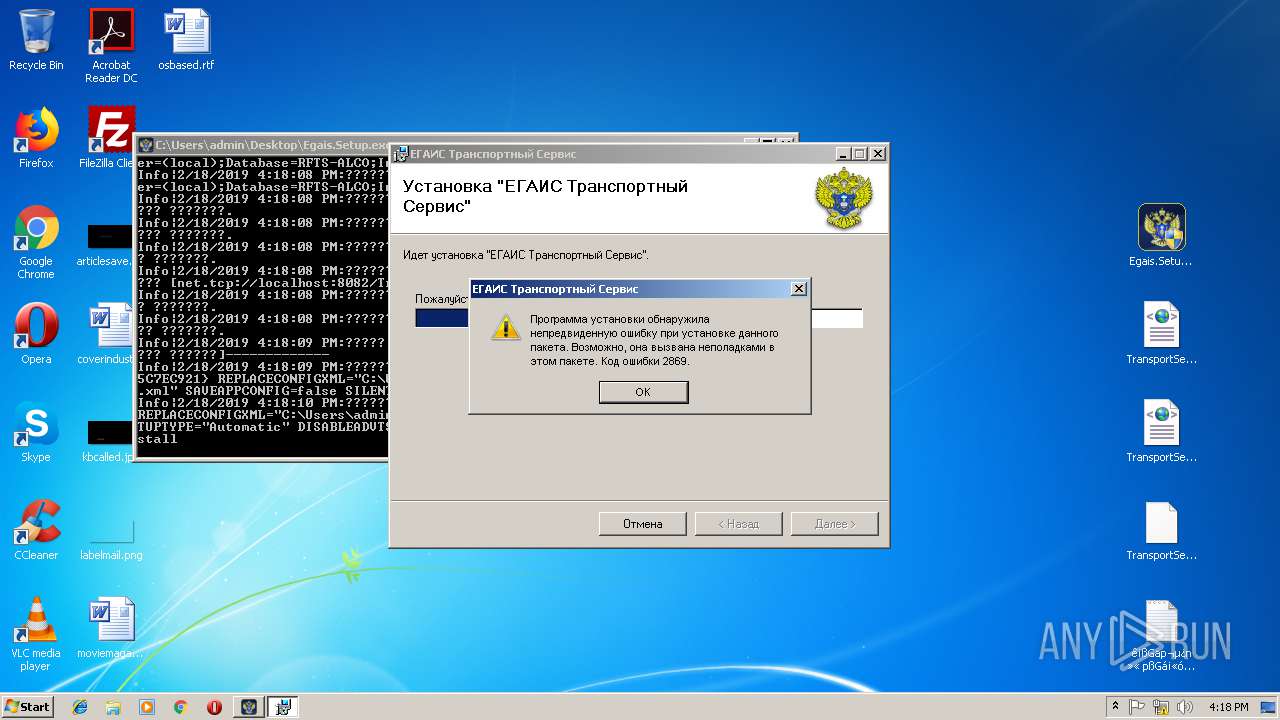
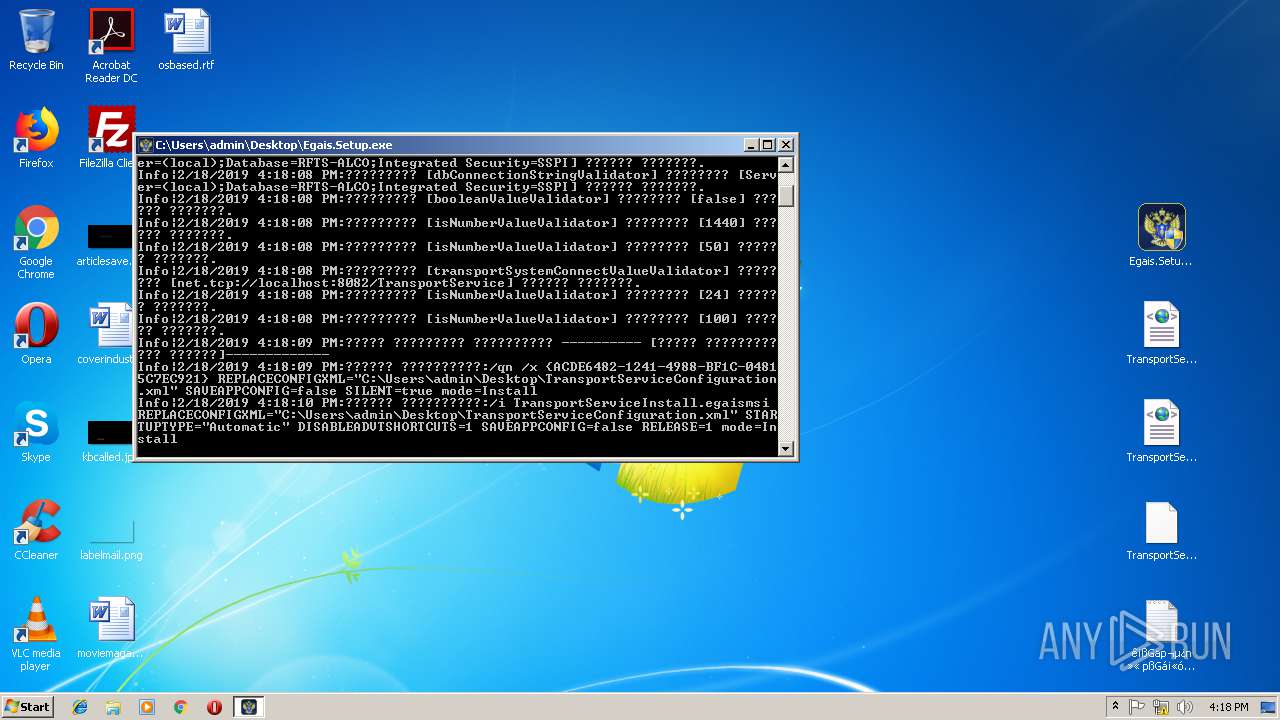
| 1832 | "C:\Windows\System32\msiexec.exe" /qn /x {ACDE6482-1241-4988-BF1C-04815C7EC921} REPLACECONFIGXML="C:\Users\admin\Desktop\TransportServiceConfiguration.xml" SAVEAPPCONFIG=false SILENT=true mode=Install | C:\Windows\System32\msiexec.exe | — | Egais.Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1605 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESD1D.tmp" "c:\Users\admin\AppData\Local\Temp\CSCD1C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2140 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000004D8" "000003A8" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
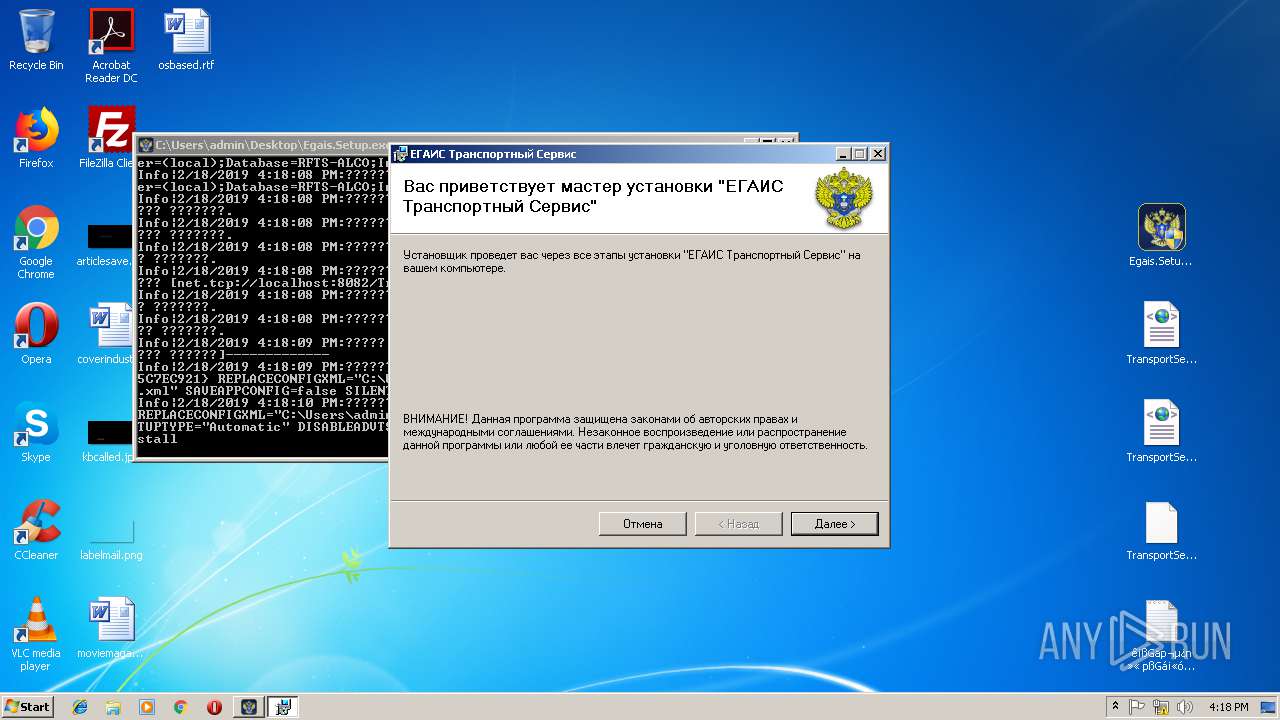
| 2228 | "C:\Users\admin\Desktop\Egais.Setup.exe" | C:\Users\admin\Desktop\Egais.Setup.exe | explorer.exe | ||||||||||||
User: admin Company: EGAIS Integrity Level: HIGH Description: Setup Exit code: 0 Version: 3.2.8.3 Modules
| |||||||||||||||
| 2316 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\d067b4tx.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | Egais.Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
2 344
Read events
1 768
Write events
415
Delete events
161
Modification events
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3428-13194980217396750 |
Value: 259 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3428-13194980217396750 |
Value: 259 | |||
Executable files
65
Suspicious files
34
Text files
212
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4cfba733-4308-44a7-8e63-db4e11cb7ad1.tmp | — | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9ea6bda8-70a9-43d0-a170-94a552891a4e.tmp | — | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0d9f158c-f580-496f-bfca-1855c197d6a8.tmp | — | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198bea.TMP | text | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF198bfa.TMP | text | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3428 | chrome.exe | GET | 200 | 146.120.90.19:80 | http://egais.ru/files/dopgost.zip | RU | compressed | 11.8 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3428 | chrome.exe | 146.120.90.19:80 | egais.ru | Russian Federal Service for Alcohol Market Regulation | RU | unknown |
3428 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3428 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3428 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3428 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
egais.ru |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |