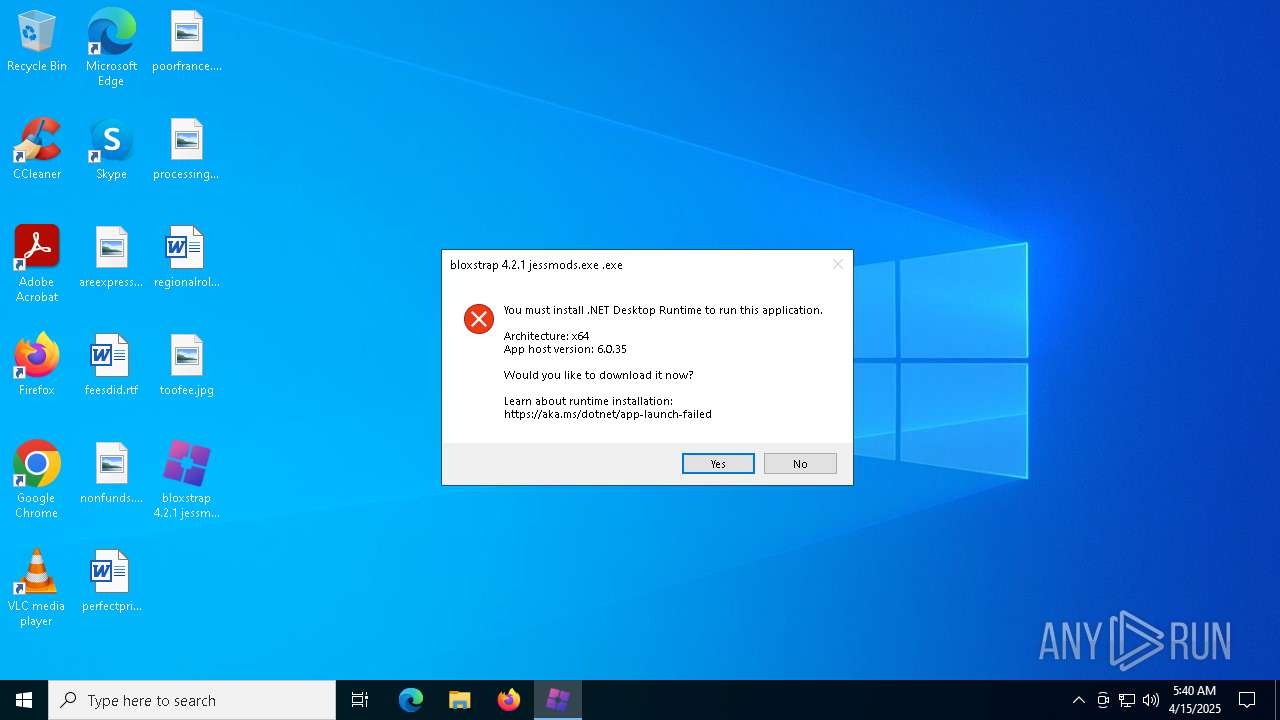
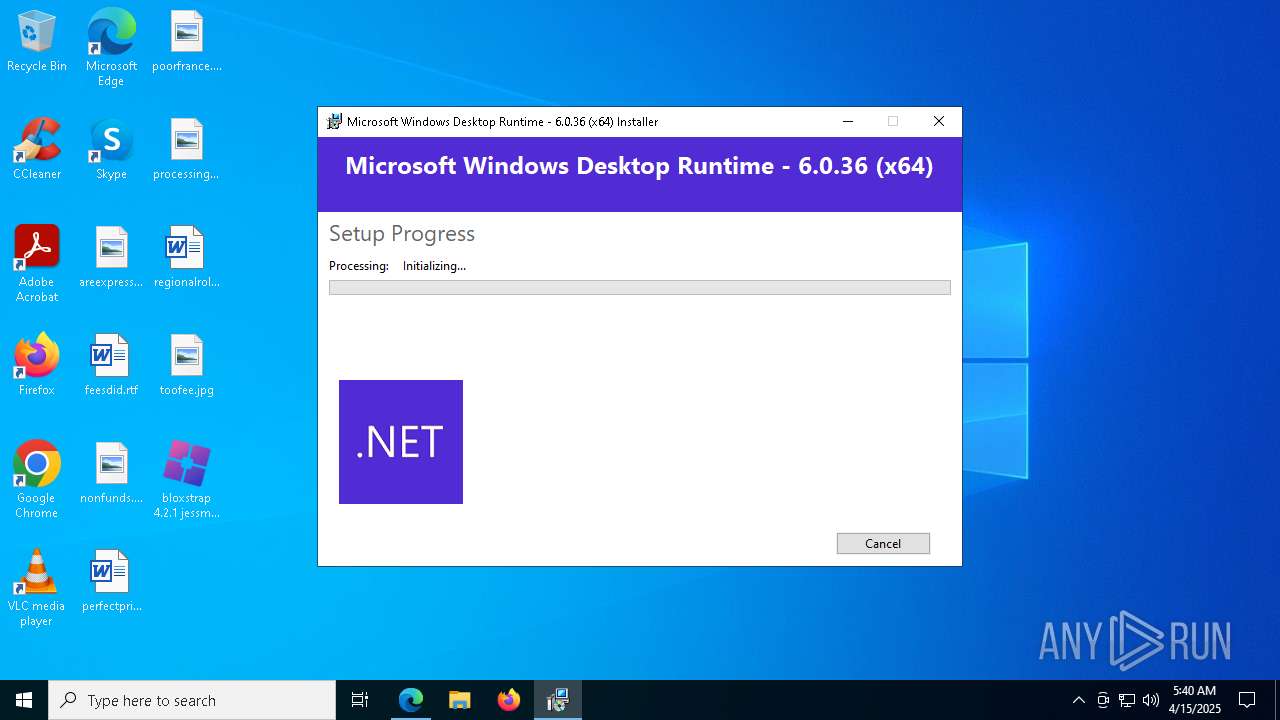
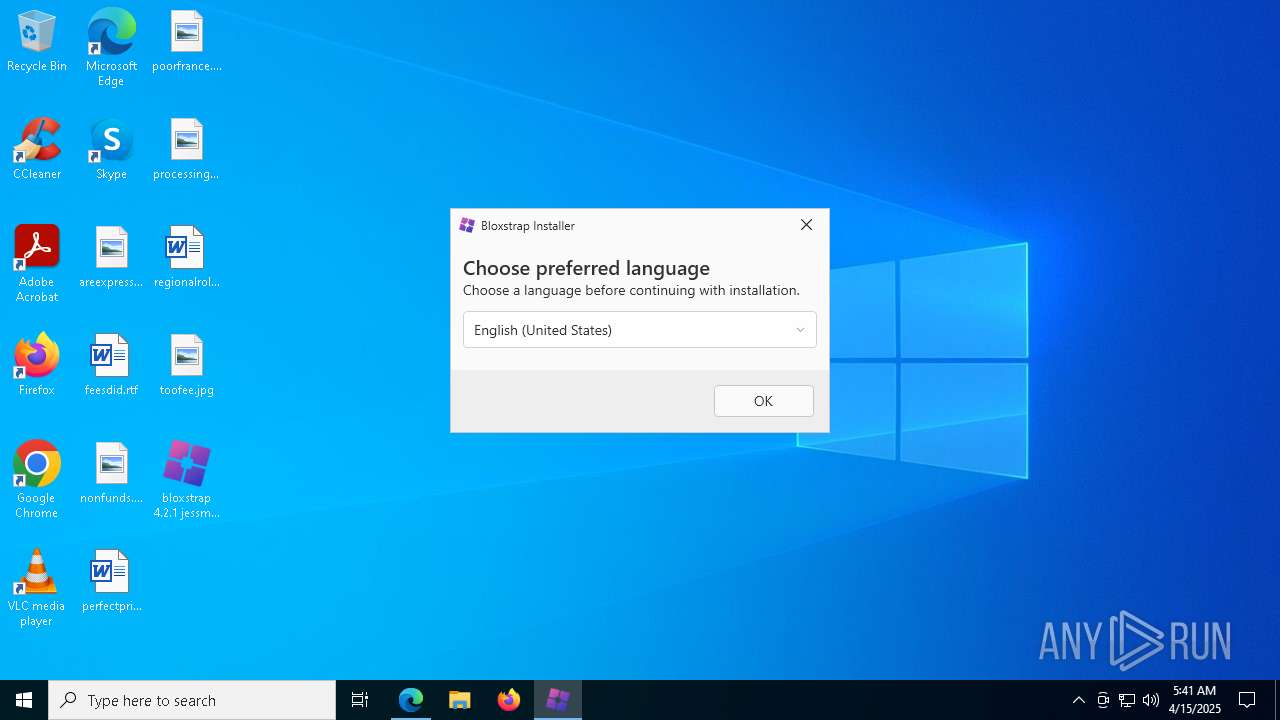
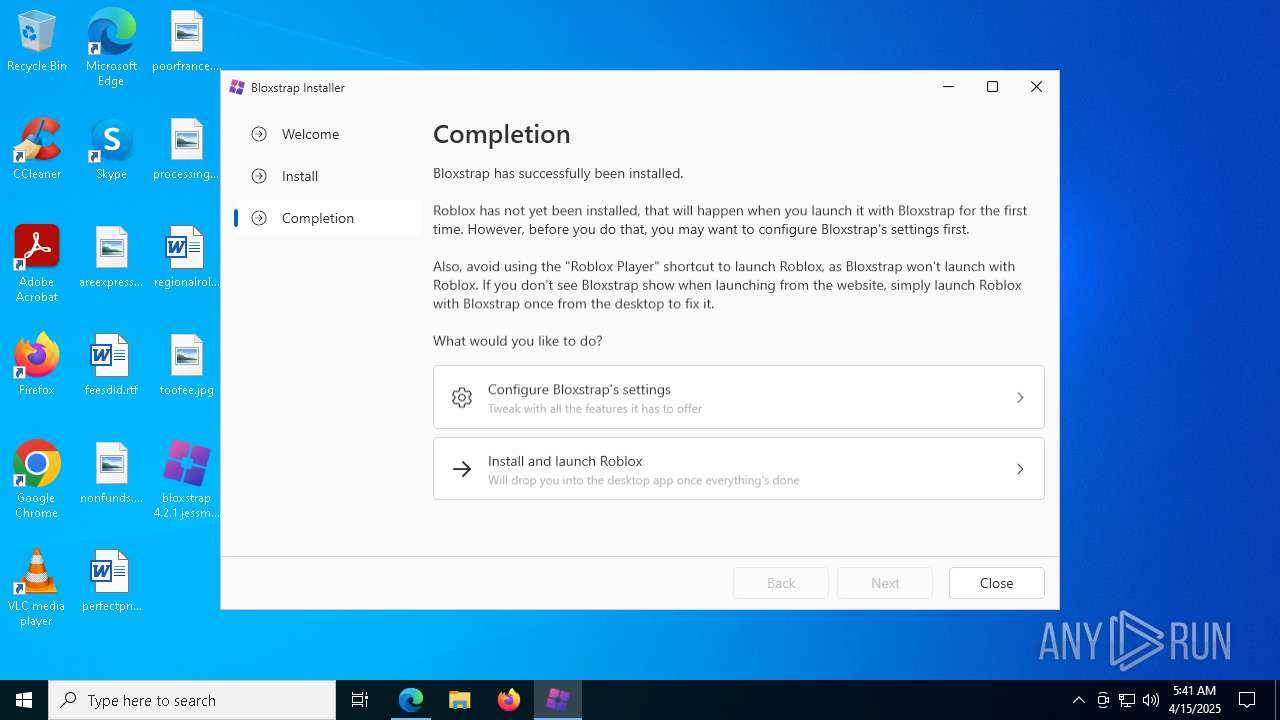
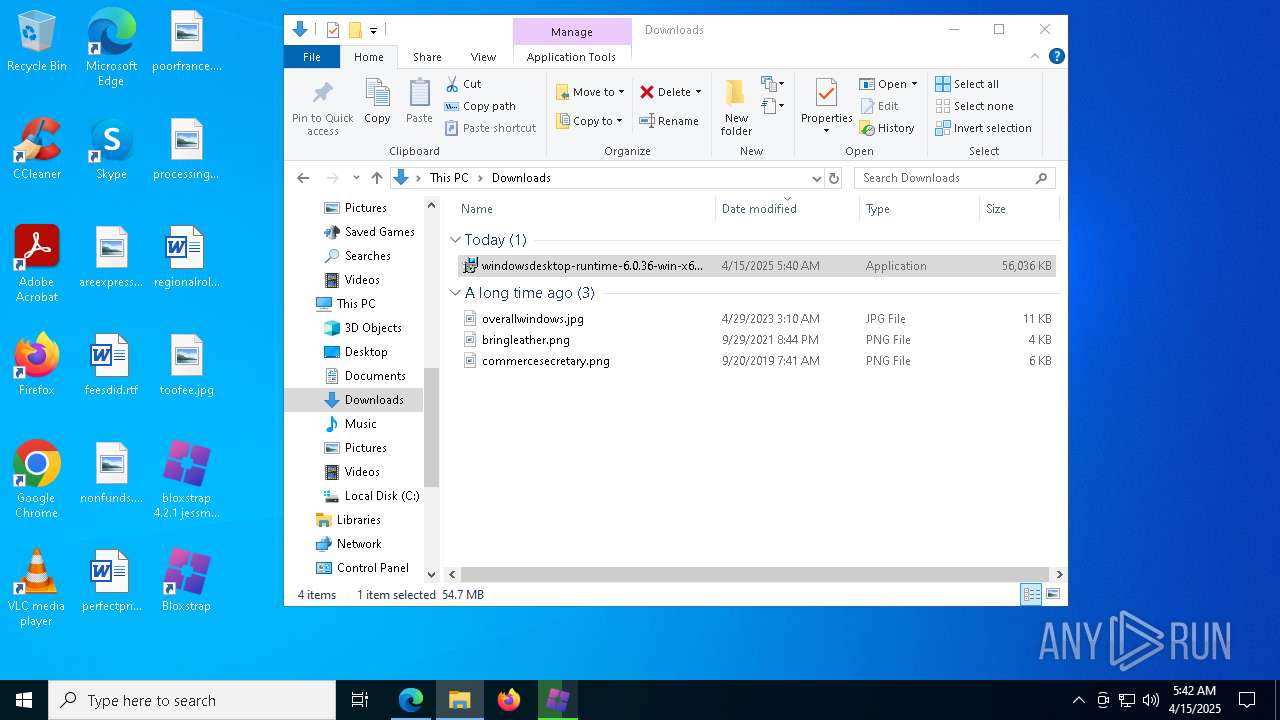
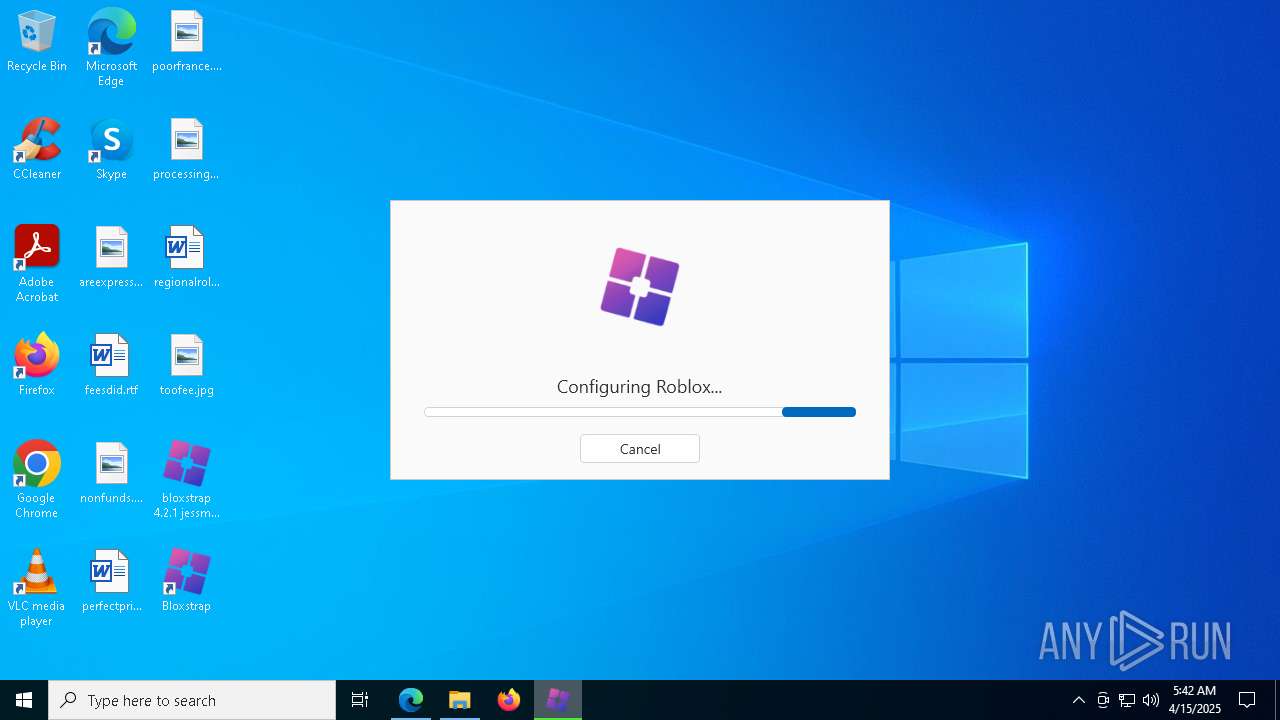
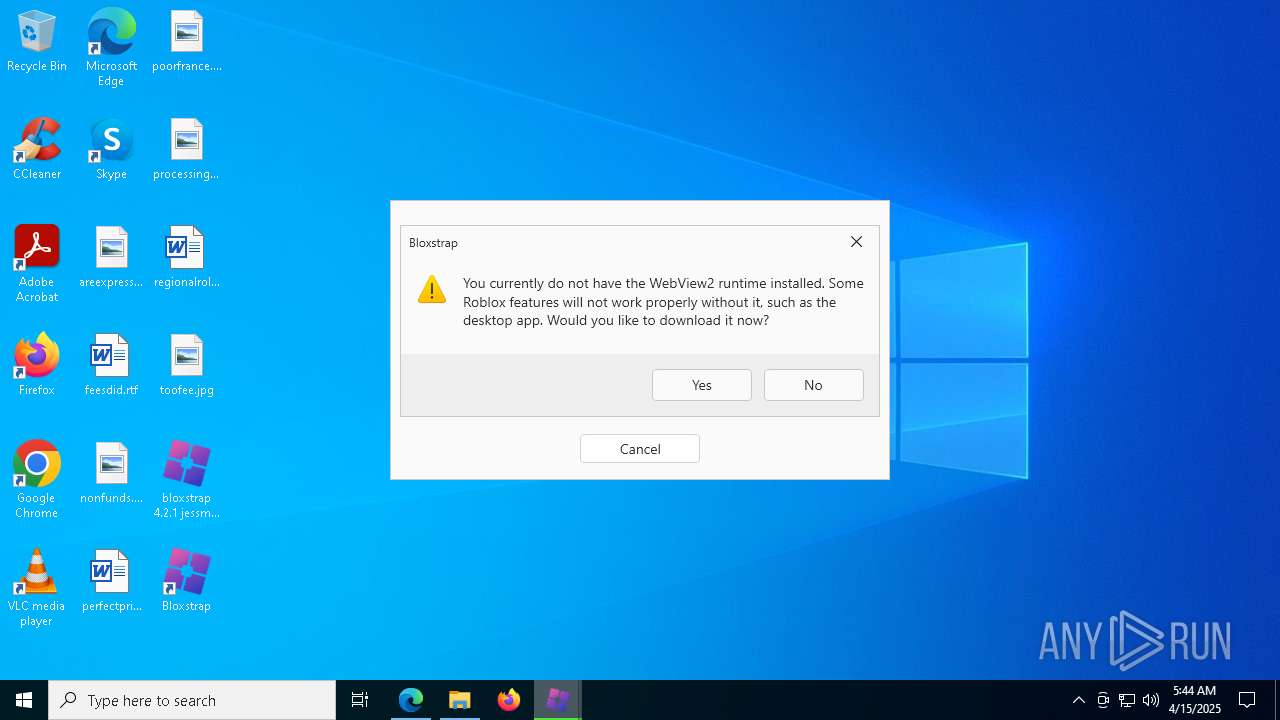
| File name: | bloxstrap 4.2.1 jessmods.exe |
| Full analysis: | https://app.any.run/tasks/f4662040-a225-4617-9722-3247a5030e86 |
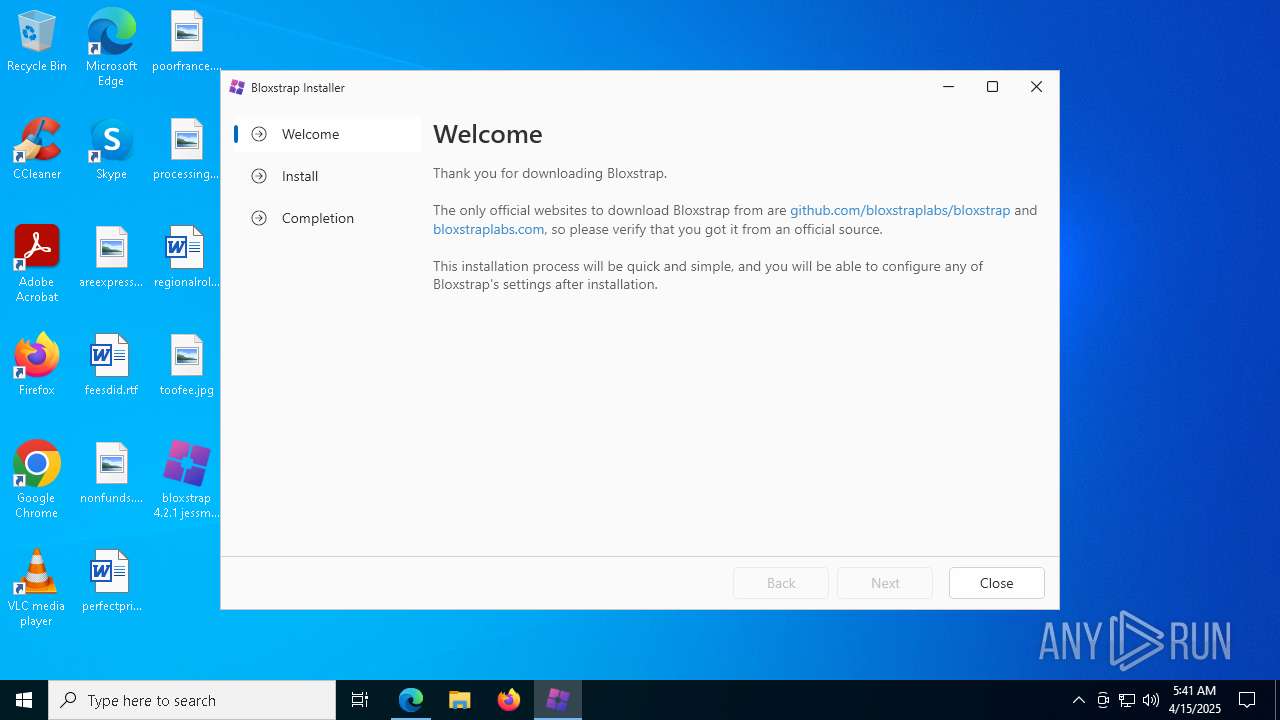
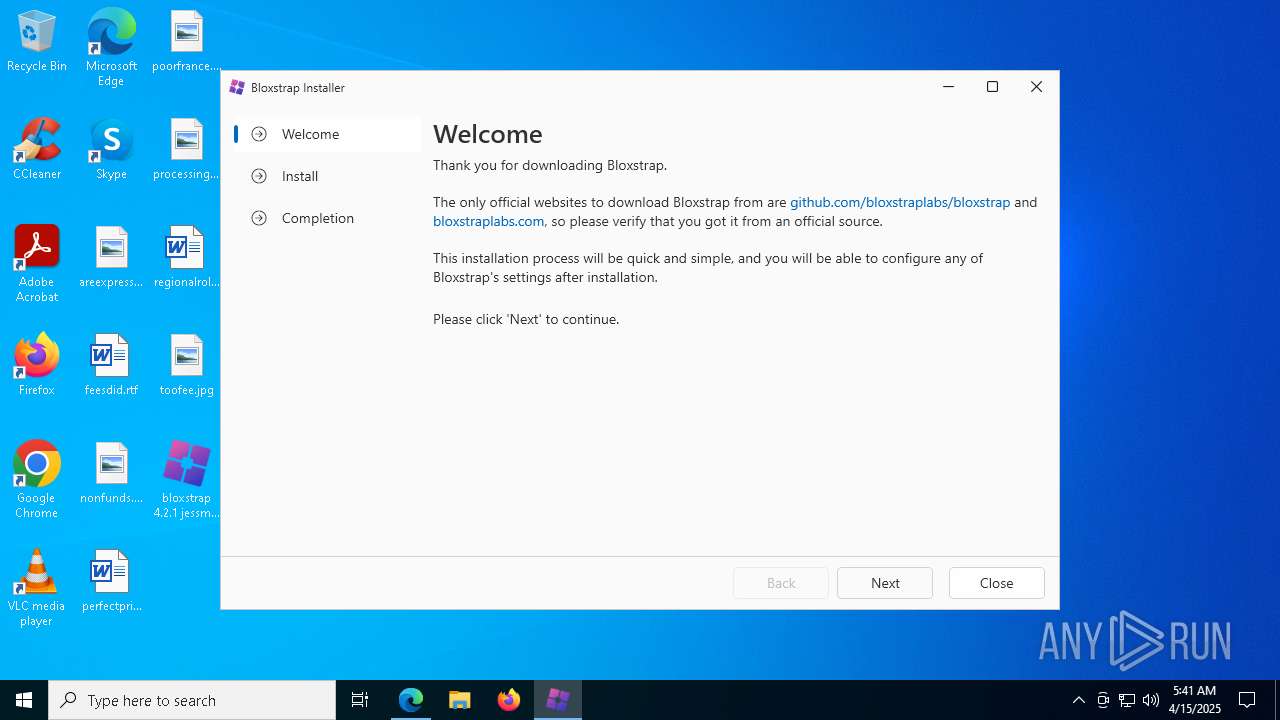
| Verdict: | Malicious activity |
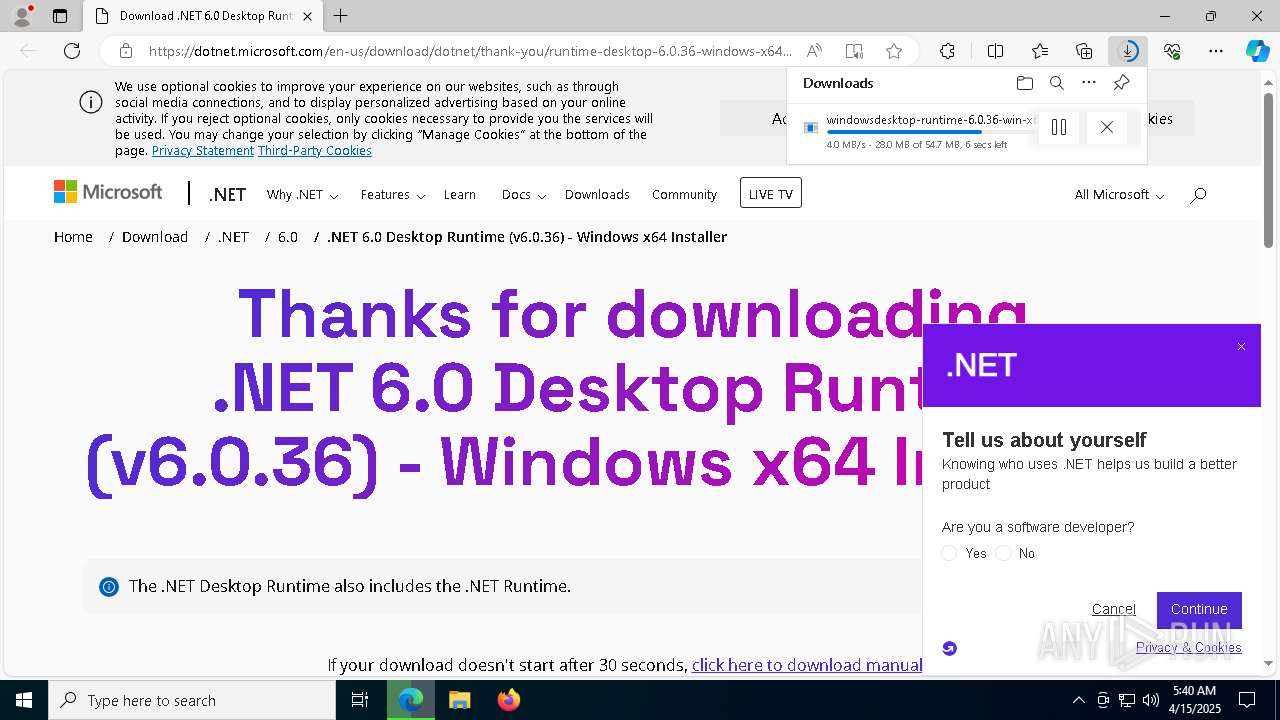
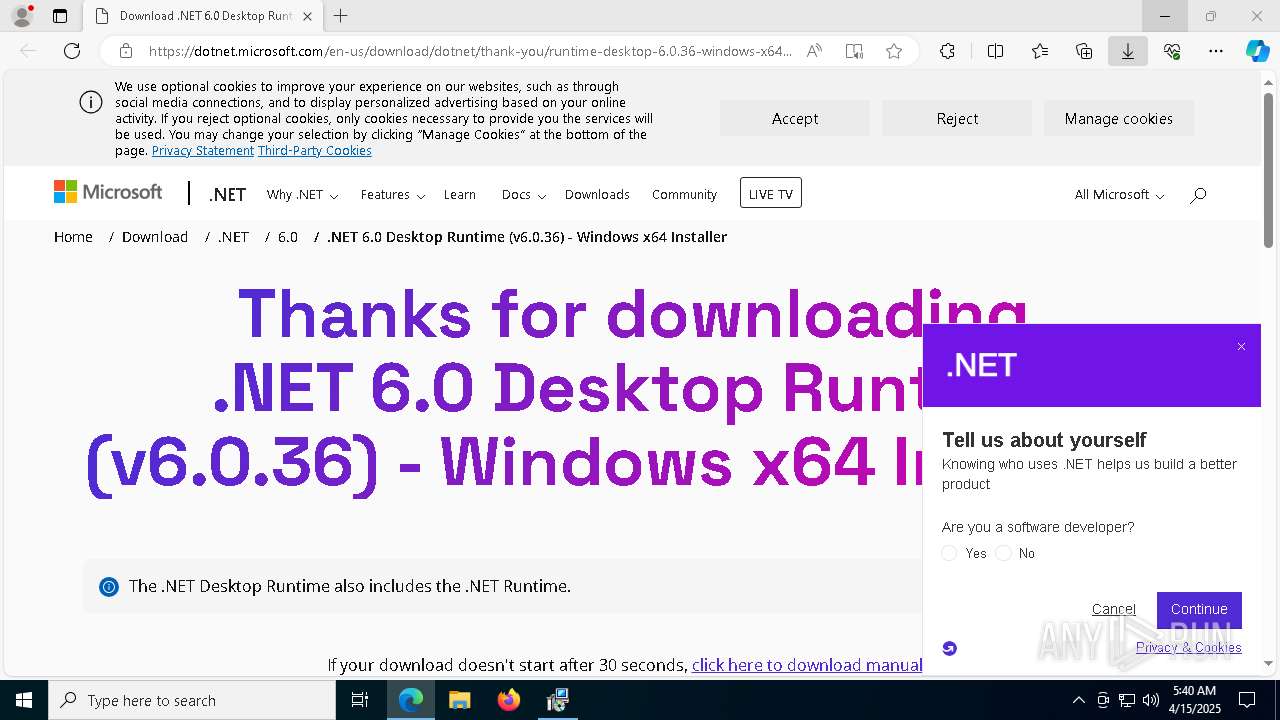
| Analysis date: | April 15, 2025, 05:40:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 104981CB101BD19E37763CEBD753928D |
| SHA1: | DF7F64CB7EA7045F5D19060AF8686F8C66432B37 |
| SHA256: | 0EE218FDE47582841E22FB4F2C866EC8BDCBEB00F8D636876677B2ECFDE50792 |
| SSDEEP: | 98304:3PwTIWIOIKJknj40Pm0000x+p6Ke0RWX1ImKaItwJY/4q1aJX1RKnnnnnnnnnnnJ:/4tvNA |
MALICIOUS
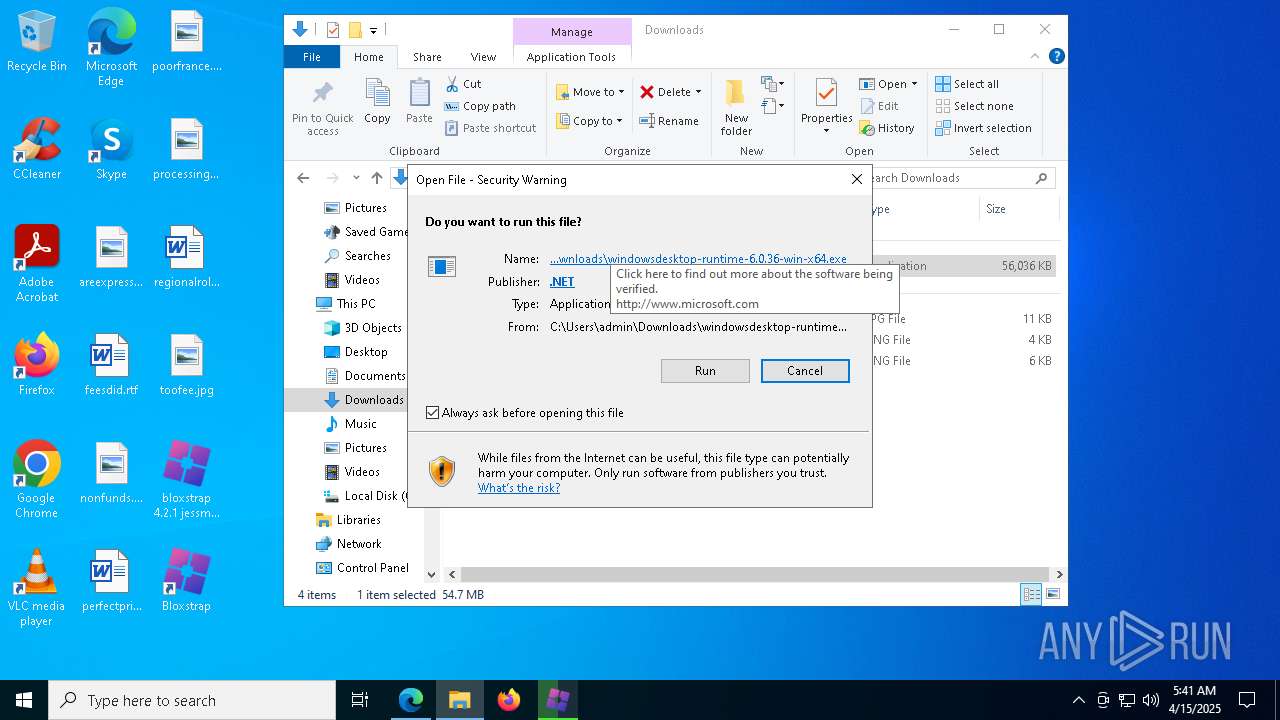
Changes the autorun value in the registry
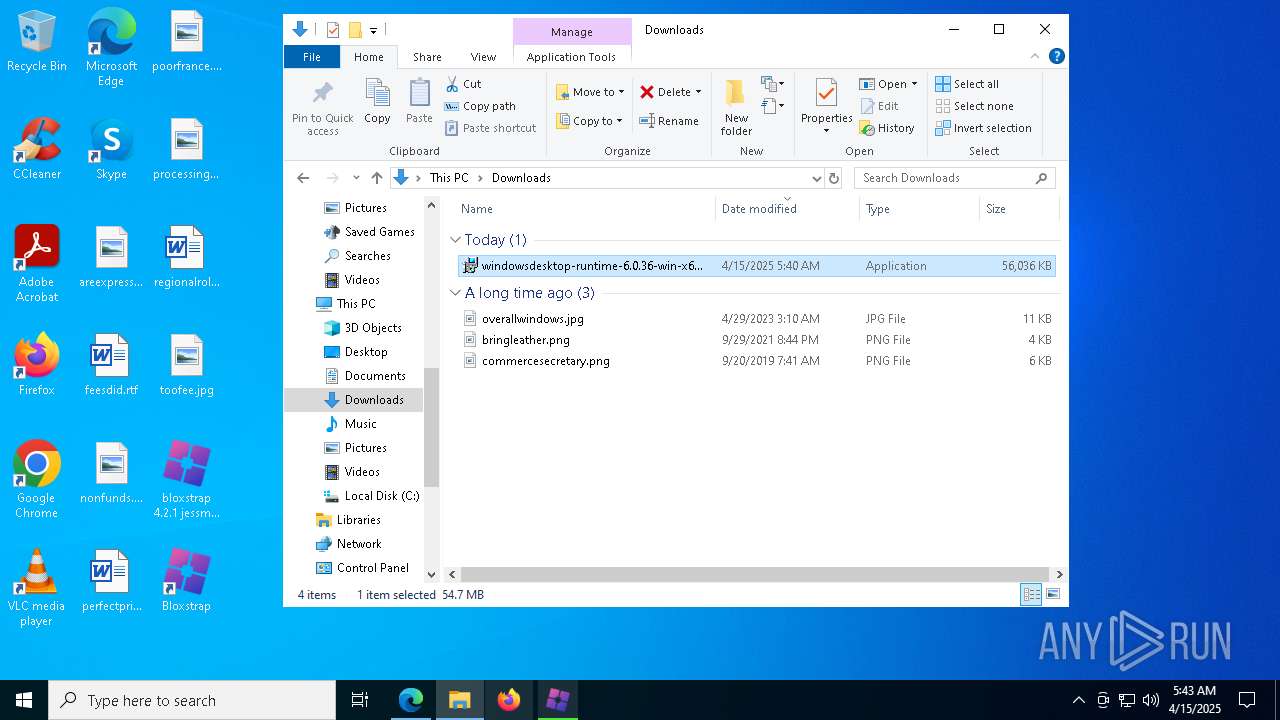
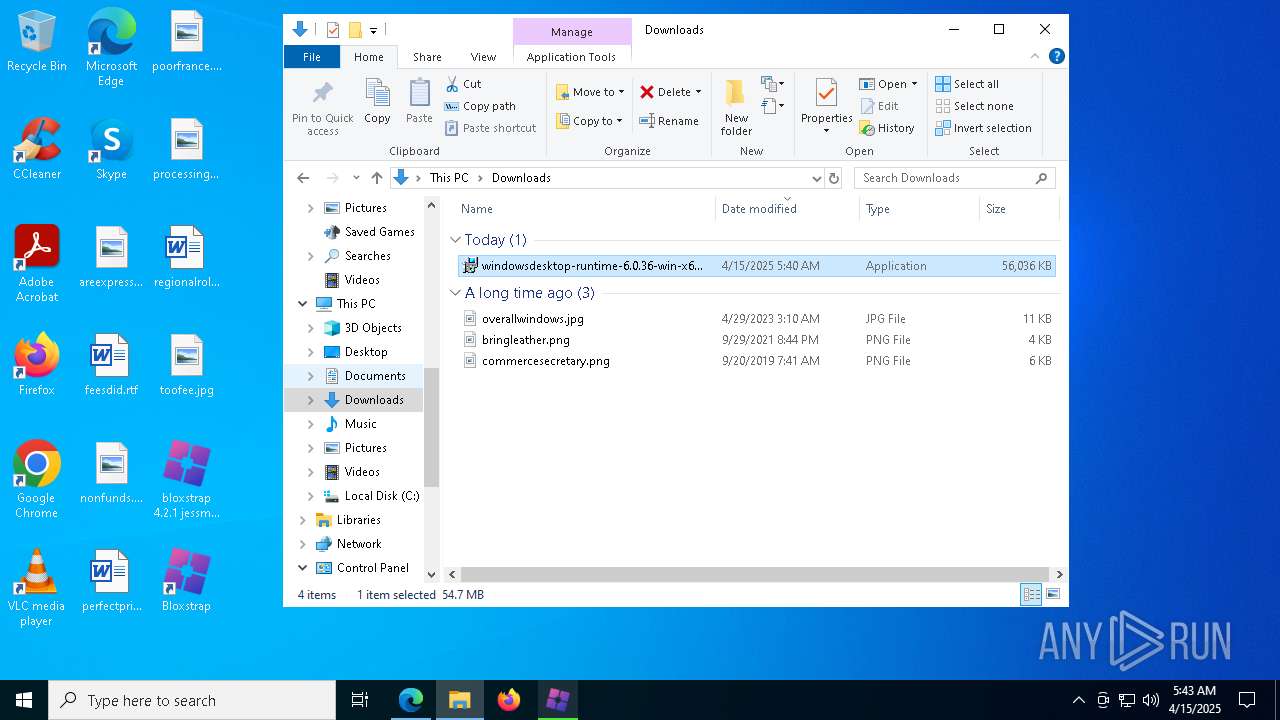
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- MicrosoftEdgeUpdate.exe (PID: 7084)
SUSPICIOUS
Reads security settings of Internet Explorer
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 6808)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- MicrosoftEdgeUpdate.exe (PID: 7084)
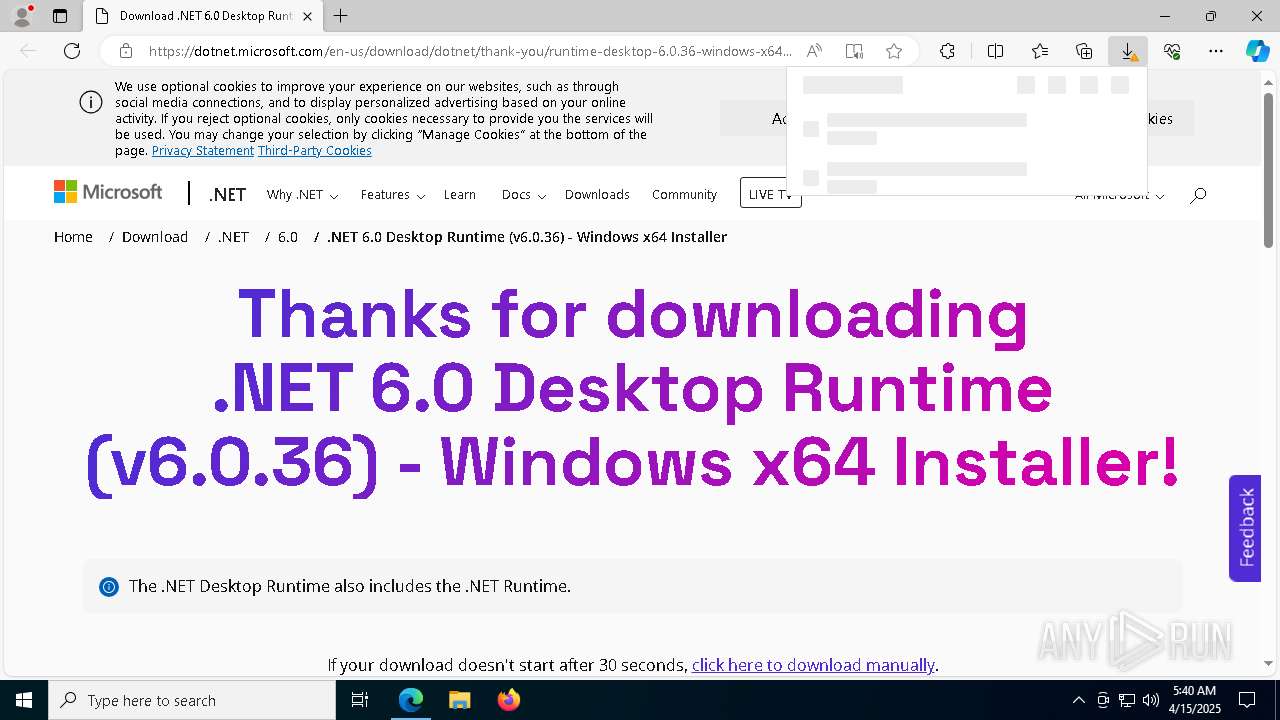
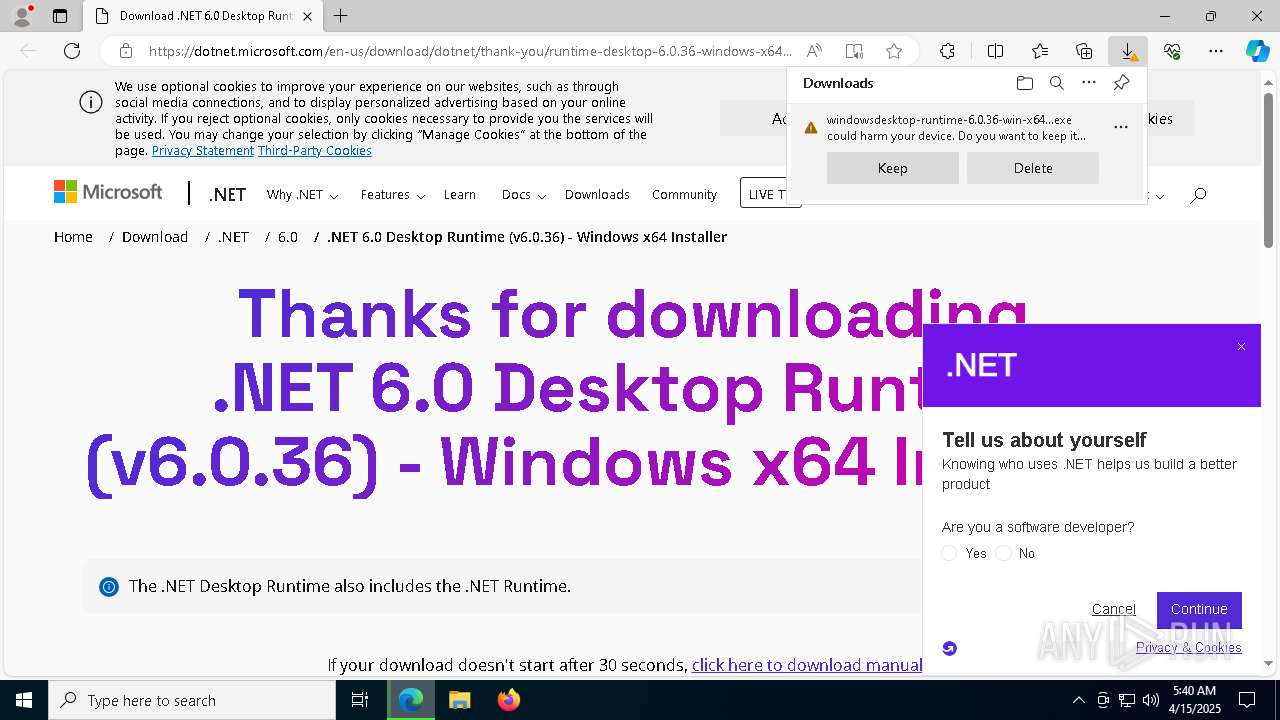
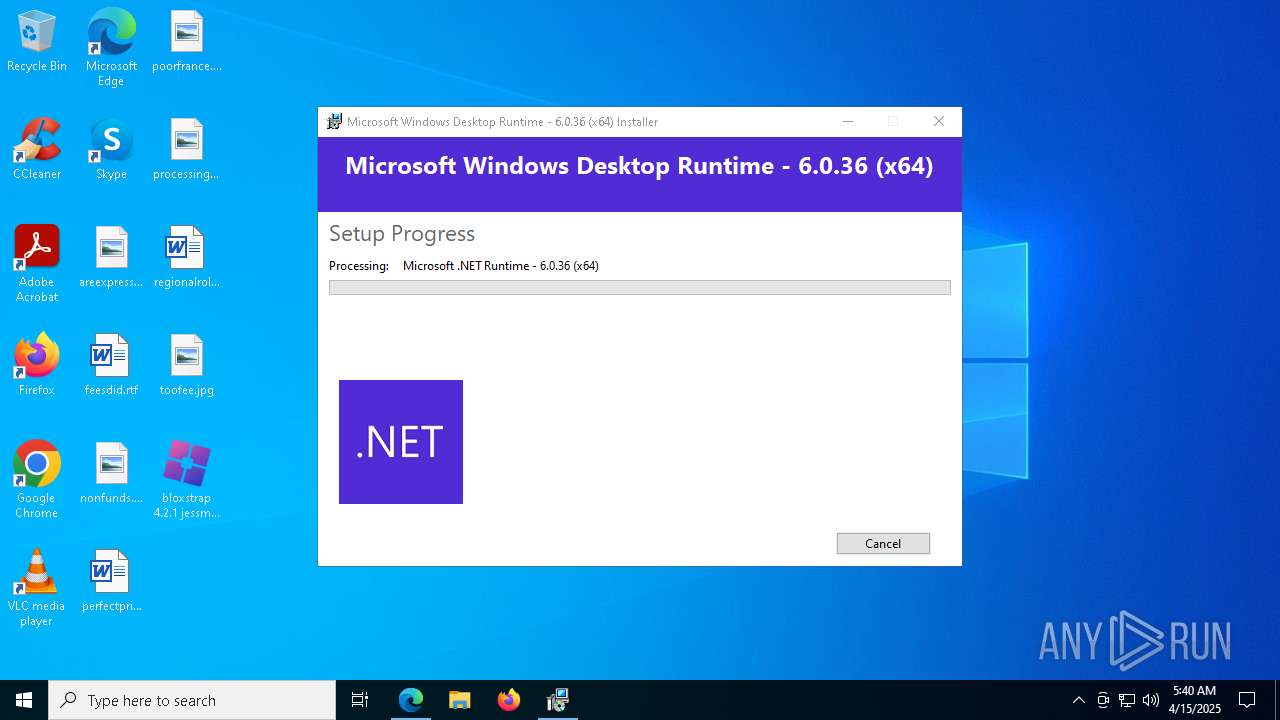
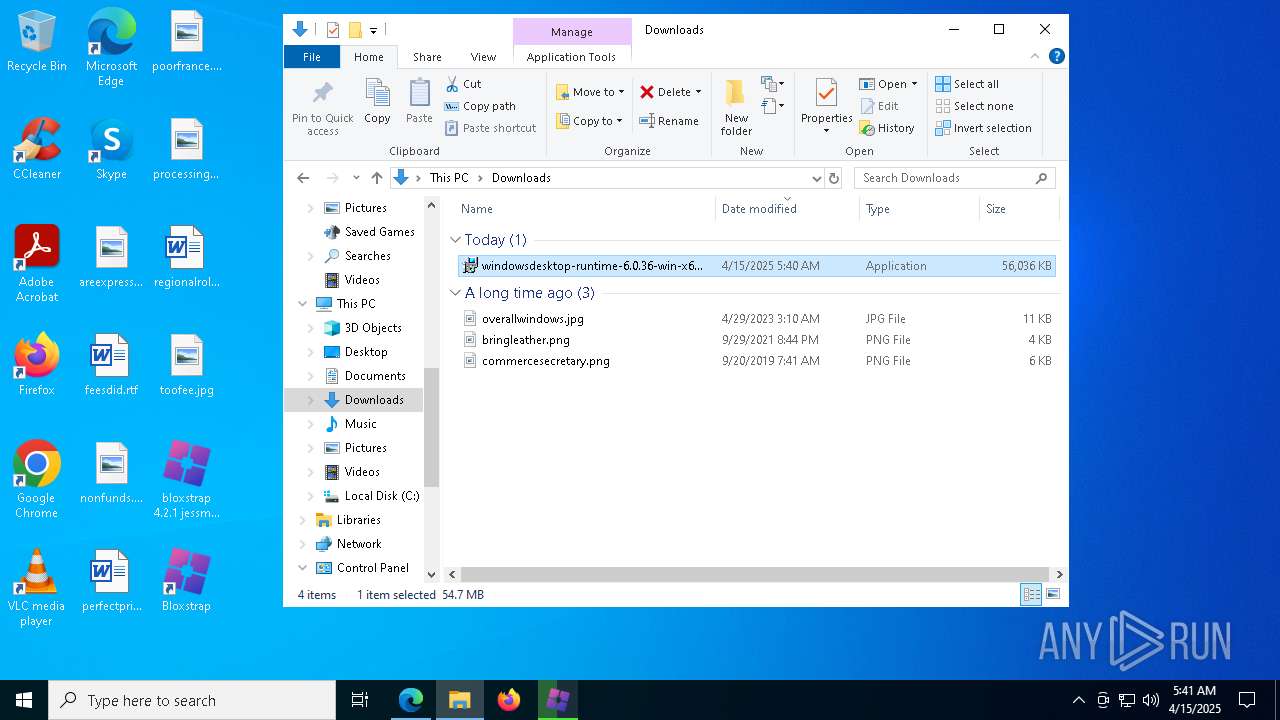
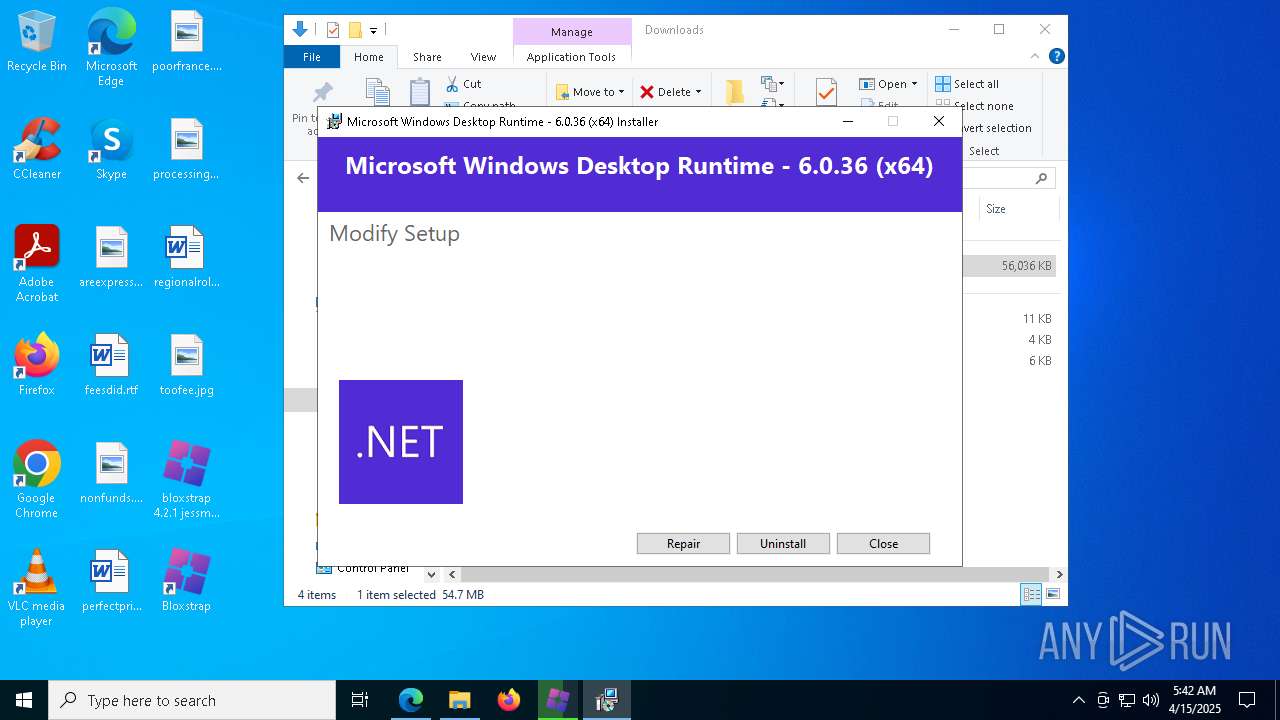
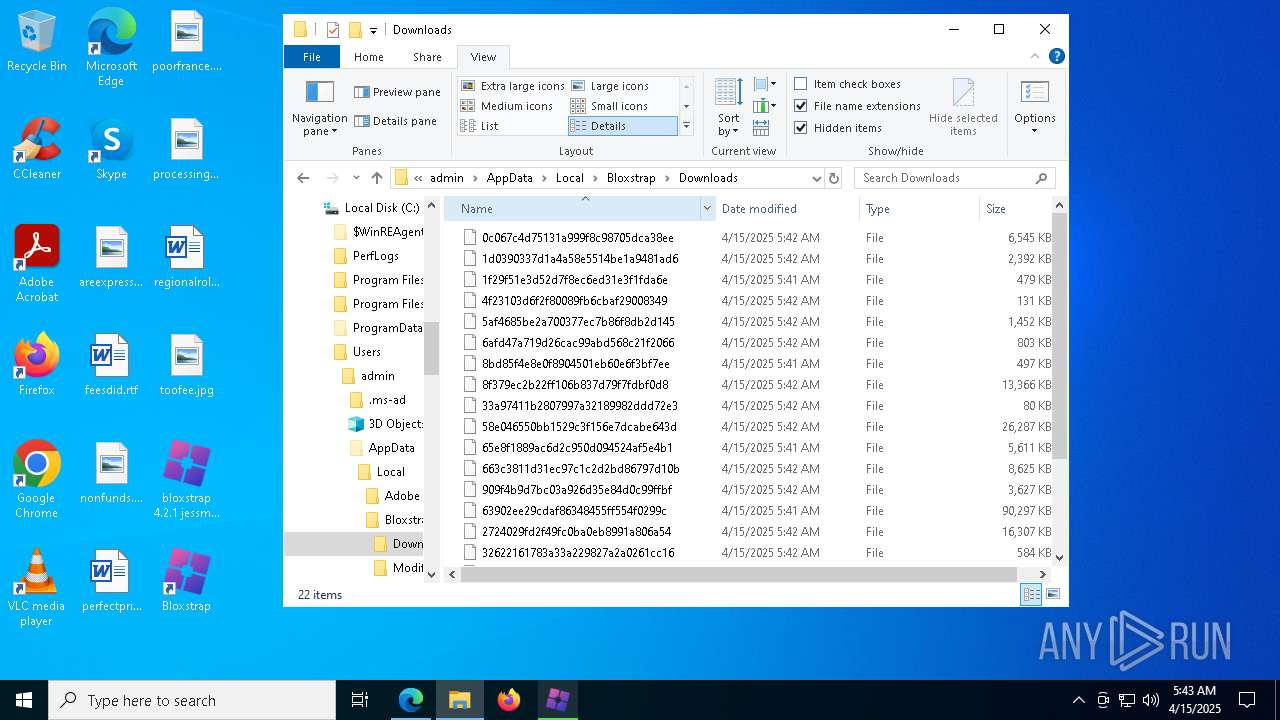
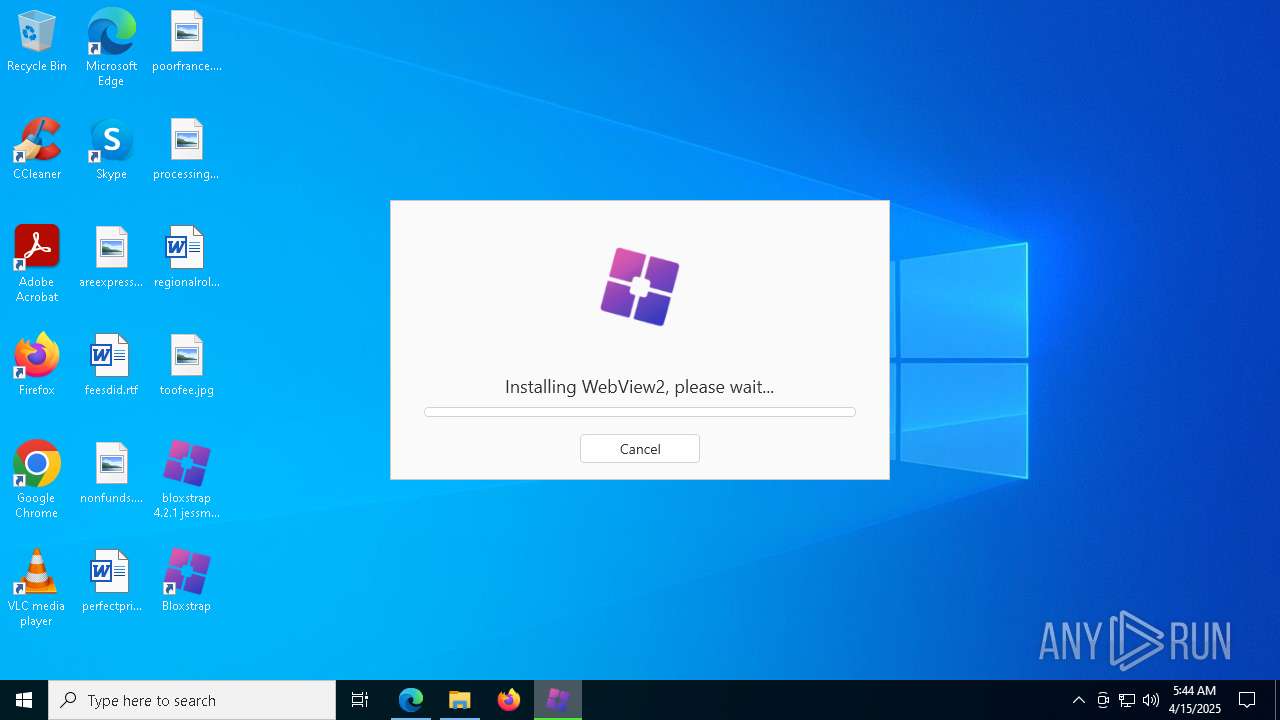
Executable content was dropped or overwritten
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 8084)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 3268)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 4200)
- MicrosoftEdgeWebview2Setup.exe (PID: 5552)
- MicrosoftEdgeUpdate.exe (PID: 7084)
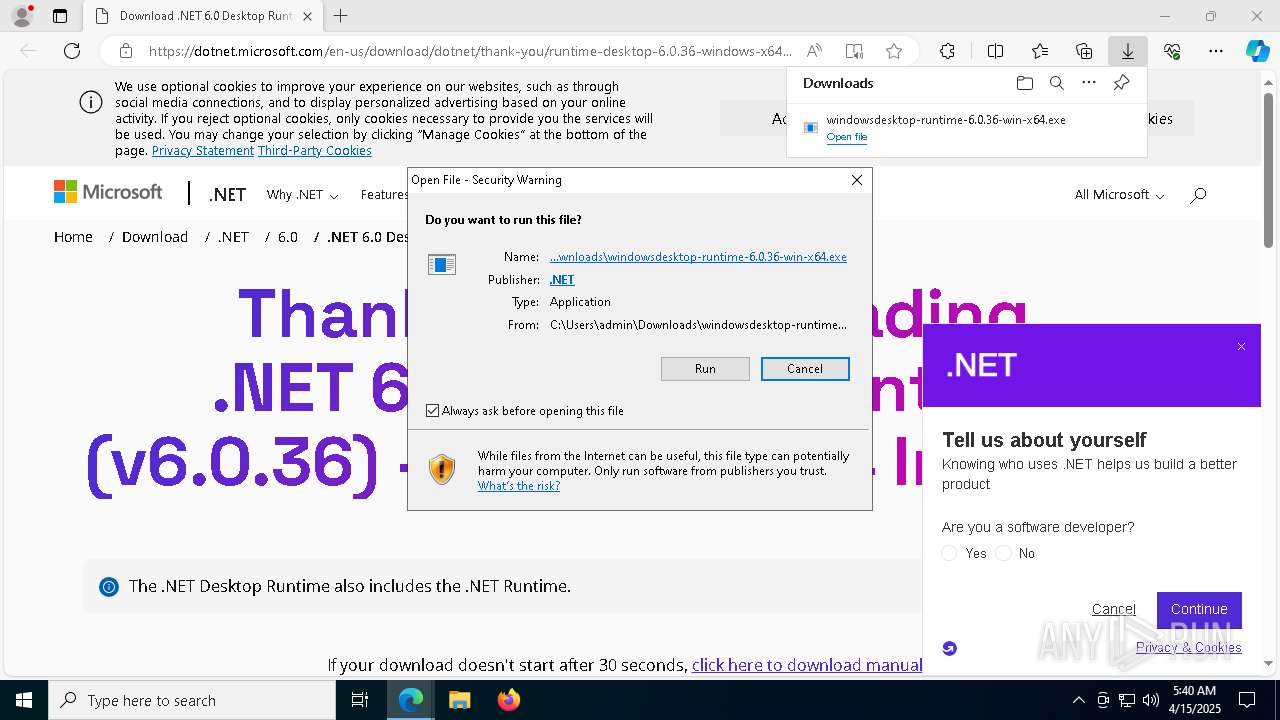
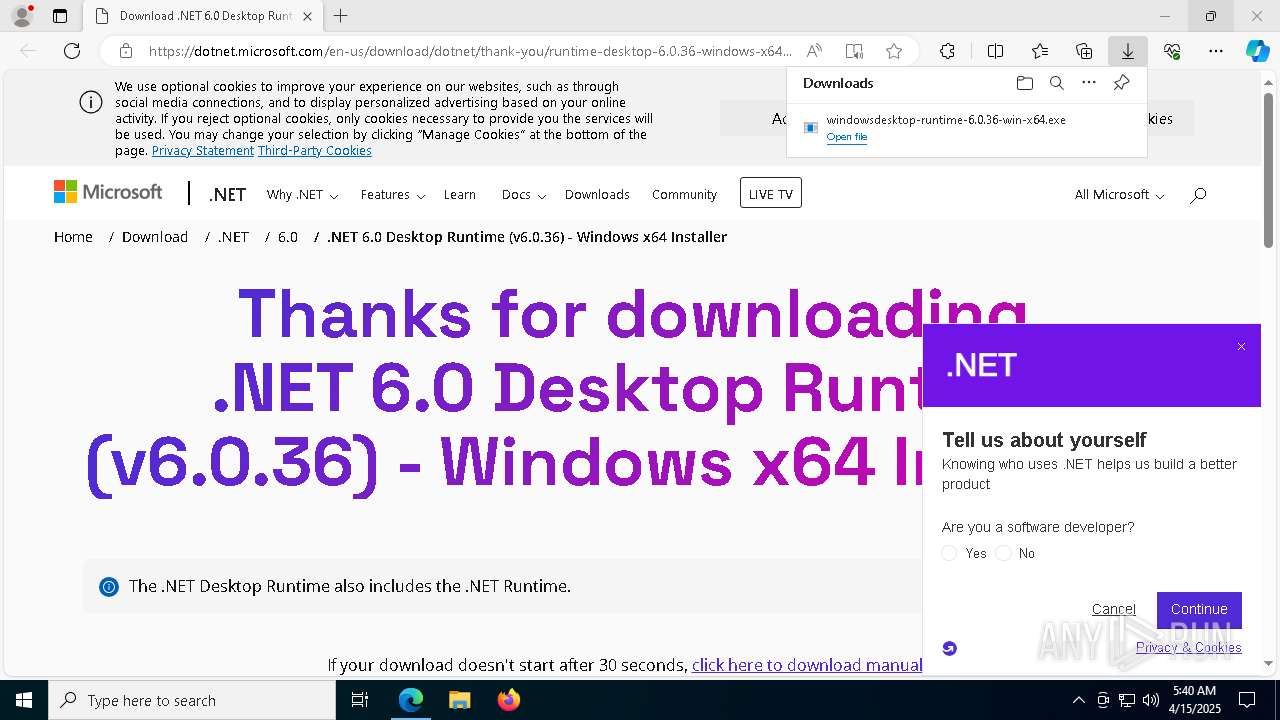
Process drops legitimate windows executable
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 8084)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- msiexec.exe (PID: 4464)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 3268)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- MicrosoftEdgeWebview2Setup.exe (PID: 5552)
- MicrosoftEdgeUpdate.exe (PID: 7084)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 4200)
- MicrosoftEdgeUpdate.exe (PID: 7084)
Searches for installed software
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 4200)
Starts itself from another location
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- MicrosoftEdgeUpdate.exe (PID: 7084)
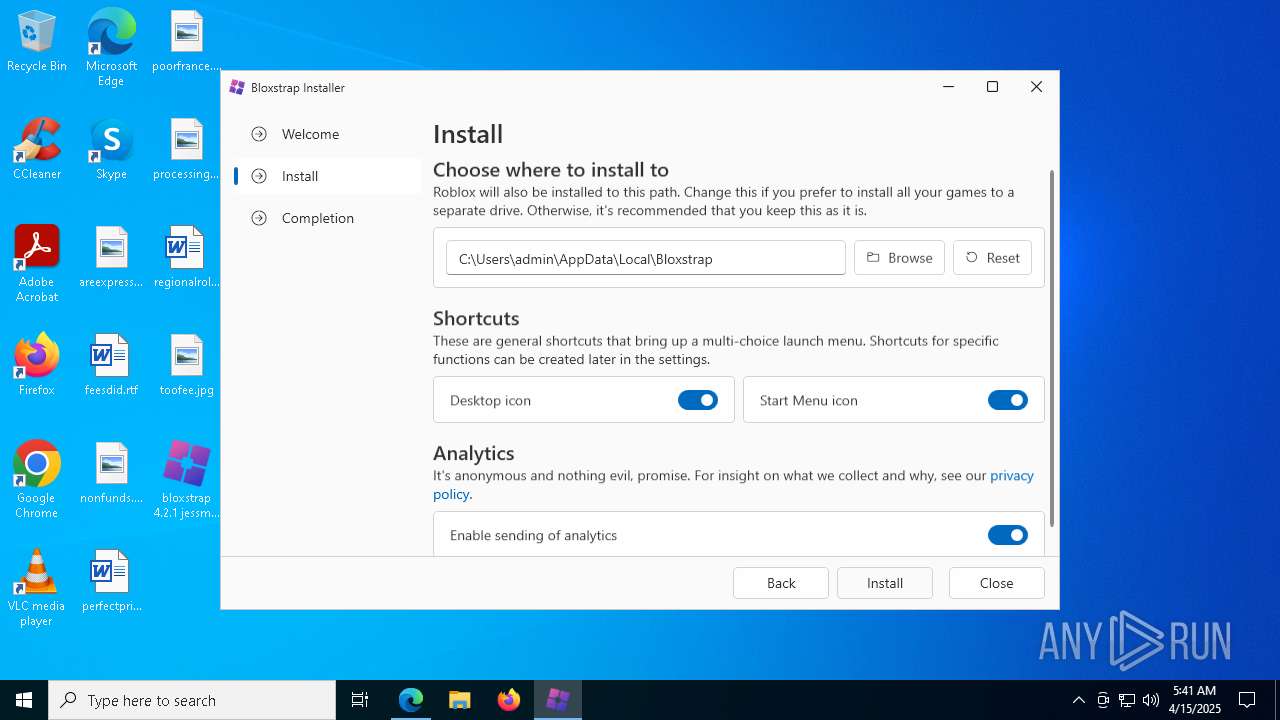
Creates a software uninstall entry
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4464)
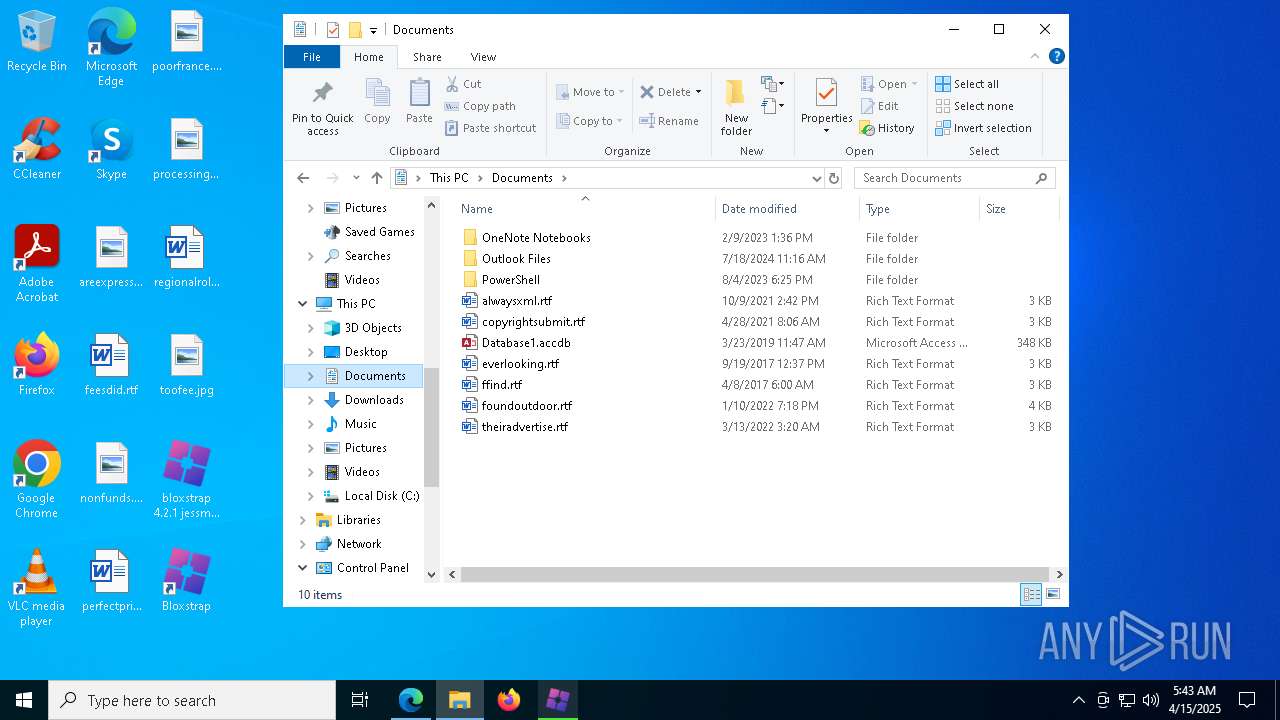
The process creates files with name similar to system file names
- msiexec.exe (PID: 4464)
The process drops C-runtime libraries
- msiexec.exe (PID: 4464)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3804)
- MicrosoftEdgeUpdate.exe (PID: 3192)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6652)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3012)
INFO
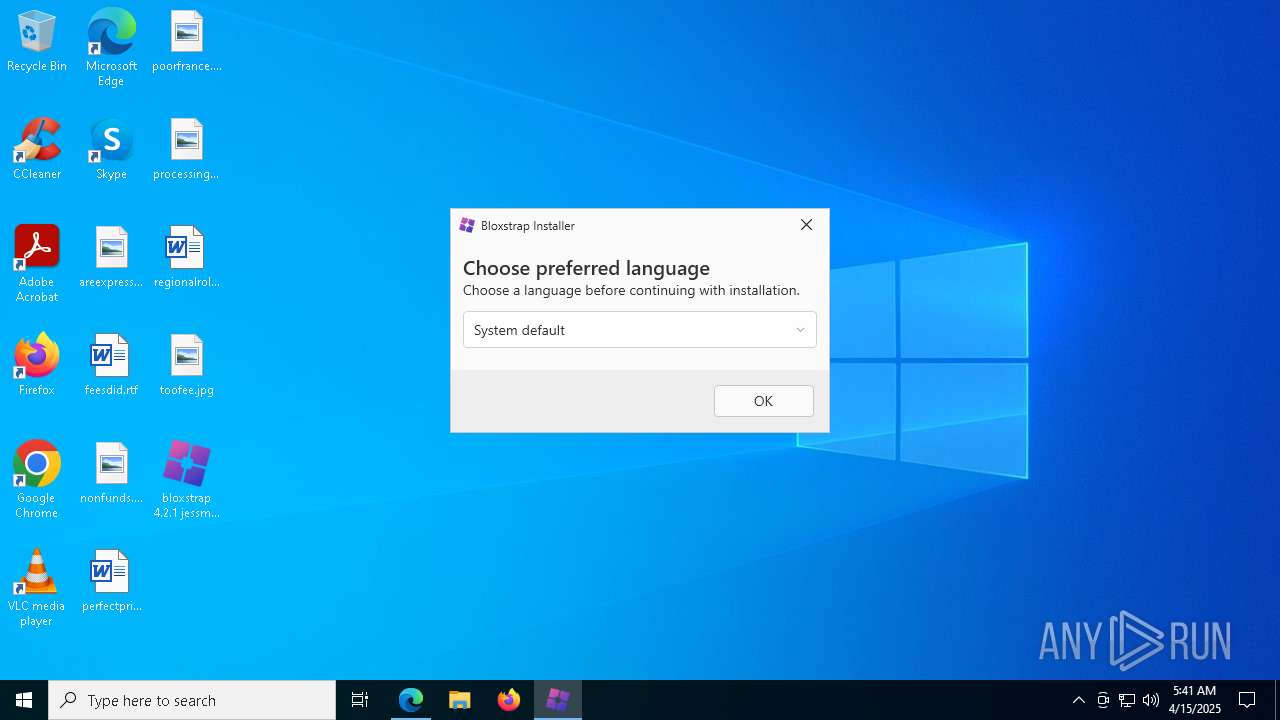
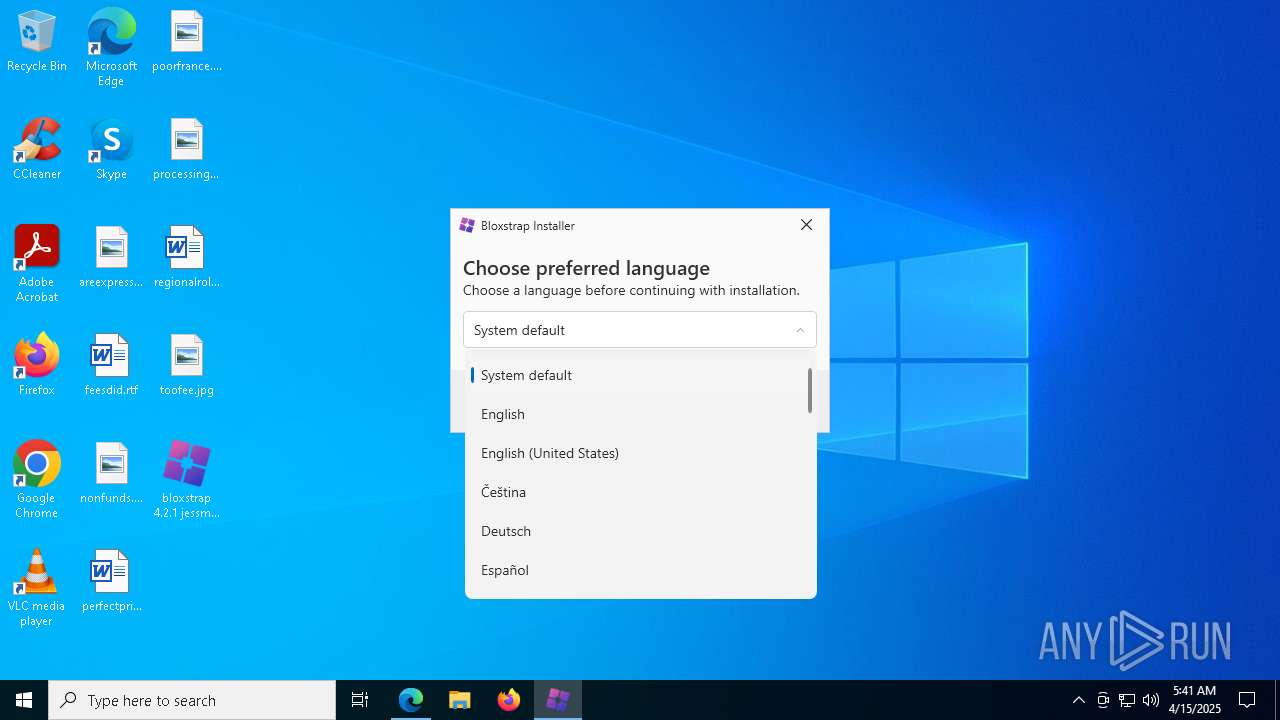
Checks supported languages
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 6808)
- identity_helper.exe (PID: 1912)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 8084)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- msiexec.exe (PID: 4464)
- msiexec.exe (PID: 7812)
- msiexec.exe (PID: 7904)
- msiexec.exe (PID: 8016)
- msiexec.exe (PID: 1040)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 3268)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 4200)
- MicrosoftEdgeWebview2Setup.exe (PID: 5552)
- MicrosoftEdgeUpdate.exe (PID: 7084)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3804)
- MicrosoftEdgeUpdate.exe (PID: 3192)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6652)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3012)
- MicrosoftEdgeUpdate.exe (PID: 8112)
- MicrosoftEdgeUpdate.exe (PID: 5984)
- MicrosoftEdgeUpdate.exe (PID: 3032)
Reads the computer name
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 6808)
- identity_helper.exe (PID: 1912)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- msiexec.exe (PID: 4464)
- msiexec.exe (PID: 7812)
- msiexec.exe (PID: 7904)
- msiexec.exe (PID: 8016)
- msiexec.exe (PID: 1040)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 4200)
- MicrosoftEdgeUpdate.exe (PID: 7084)
- MicrosoftEdgeUpdate.exe (PID: 3192)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3804)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6652)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 3012)
- MicrosoftEdgeUpdate.exe (PID: 5984)
- MicrosoftEdgeUpdate.exe (PID: 3032)
- MicrosoftEdgeUpdate.exe (PID: 8112)
Application launched itself
- msedge.exe (PID: 2088)
Executable content was dropped or overwritten
- msedge.exe (PID: 2088)
- msiexec.exe (PID: 4464)
- msedge.exe (PID: 6032)
Reads Environment values
- identity_helper.exe (PID: 1912)
- MicrosoftEdgeUpdate.exe (PID: 8112)
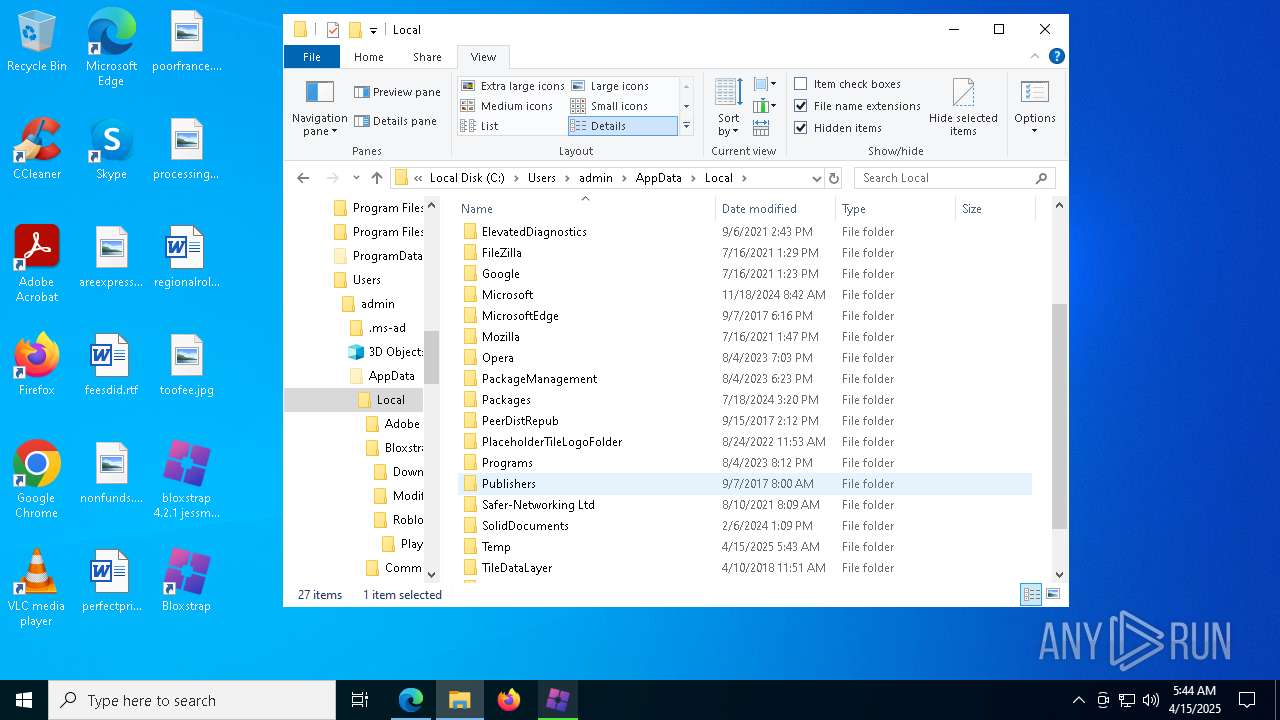
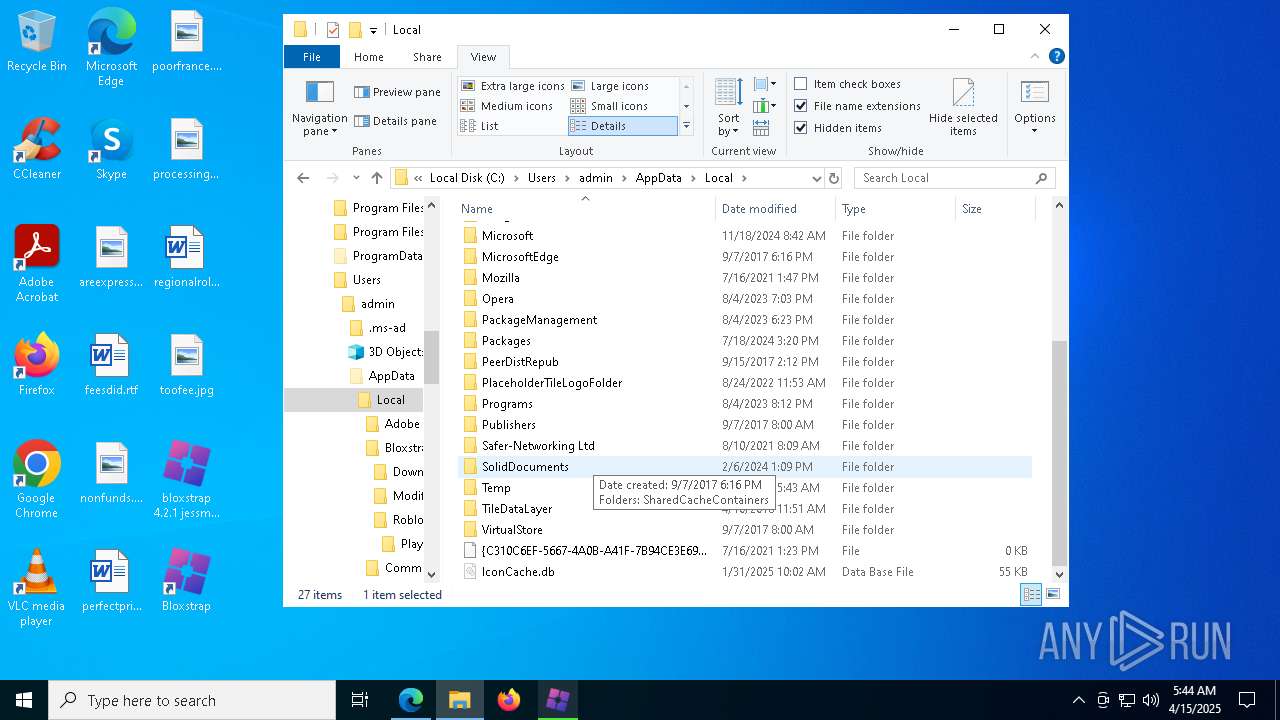
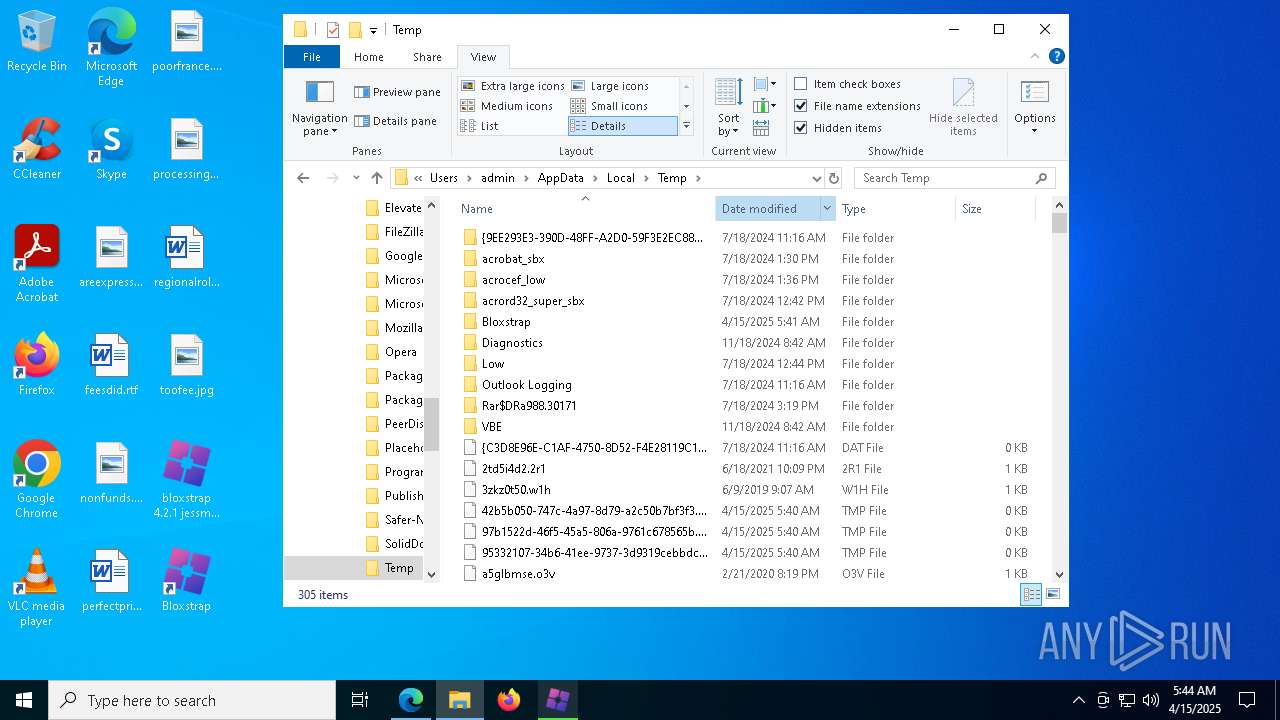
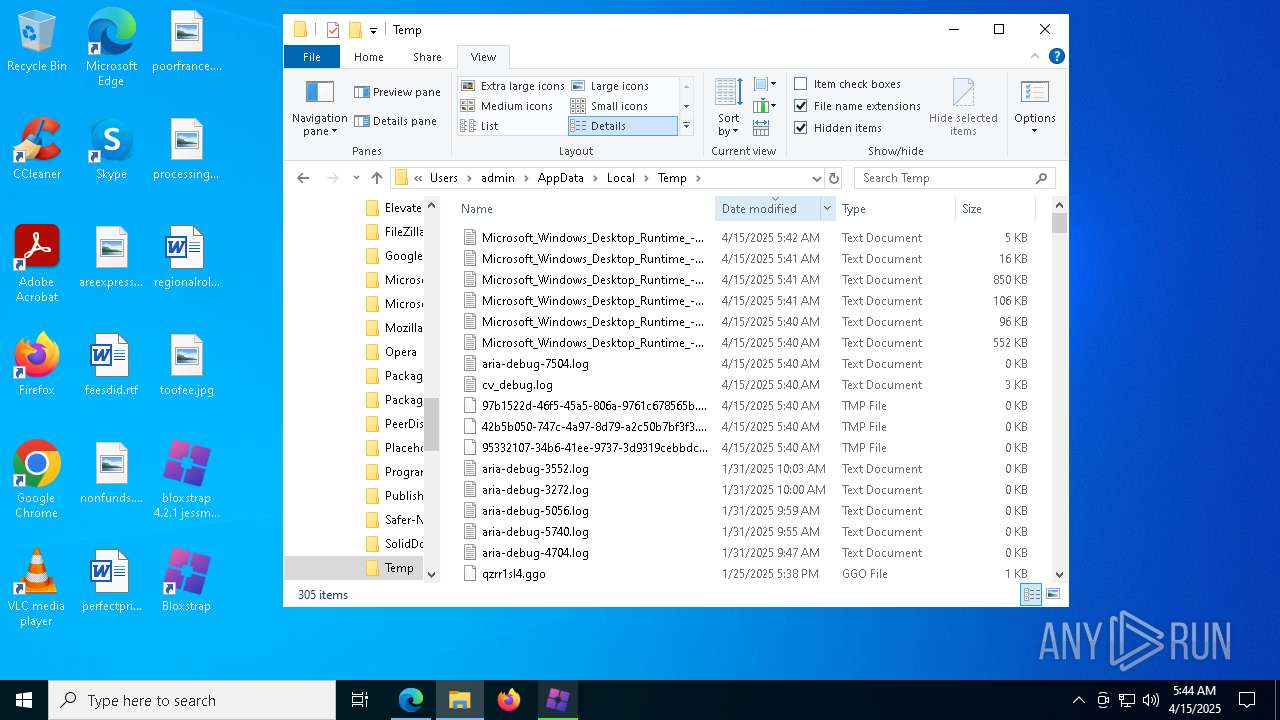
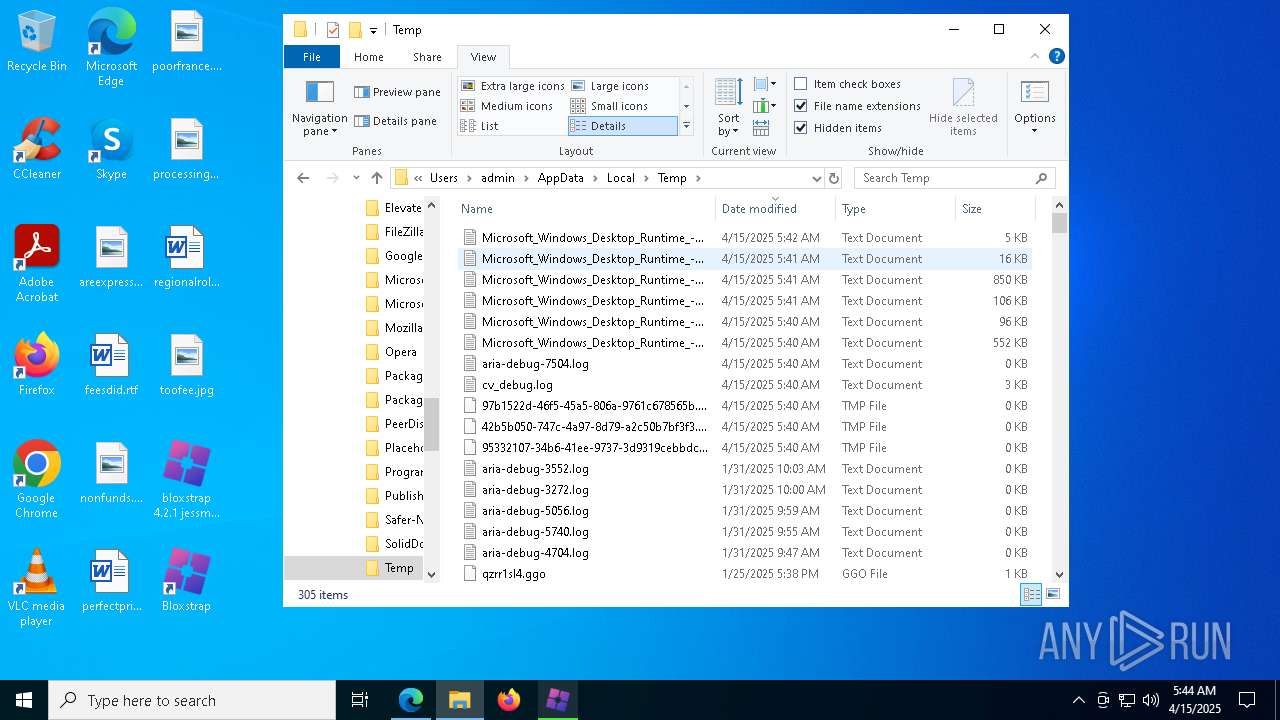
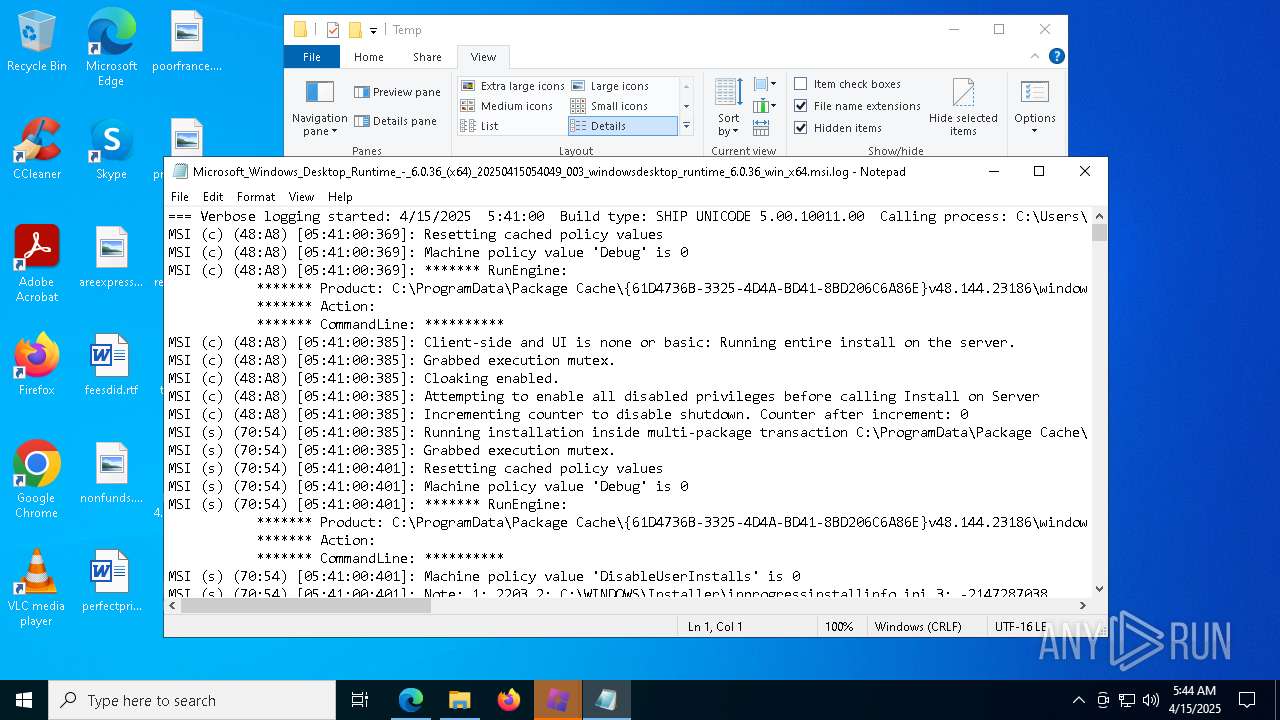
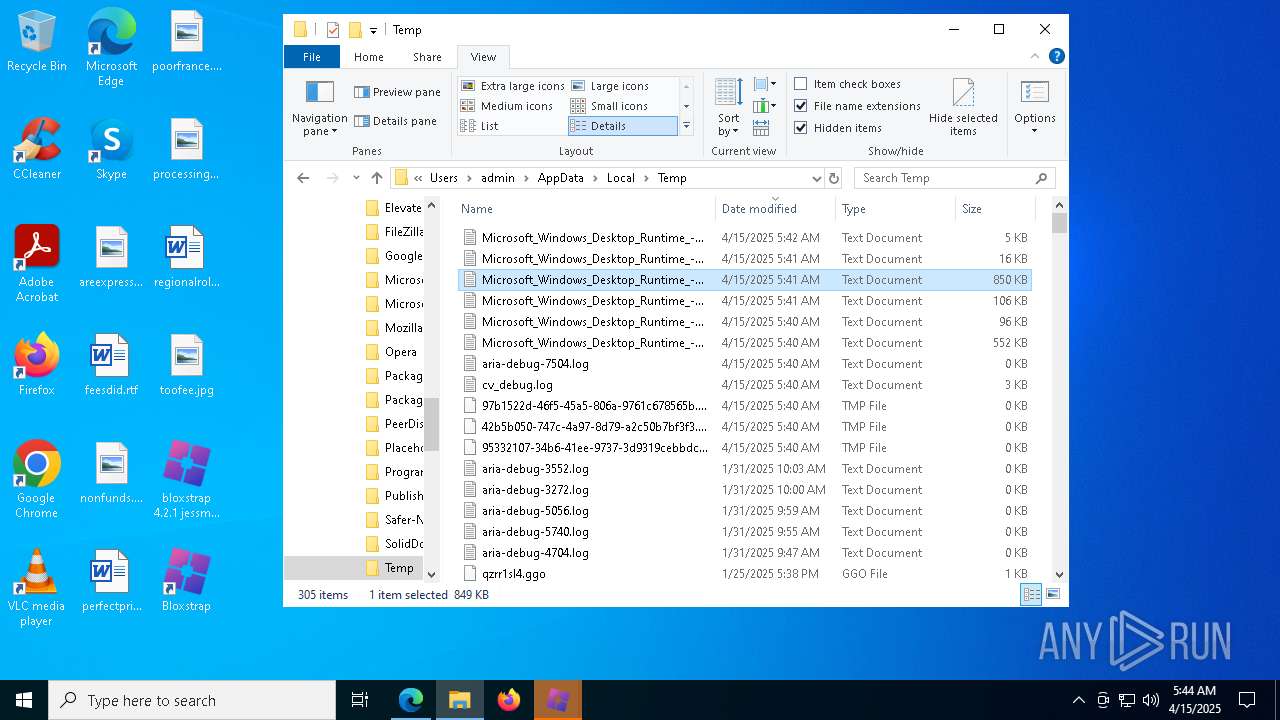
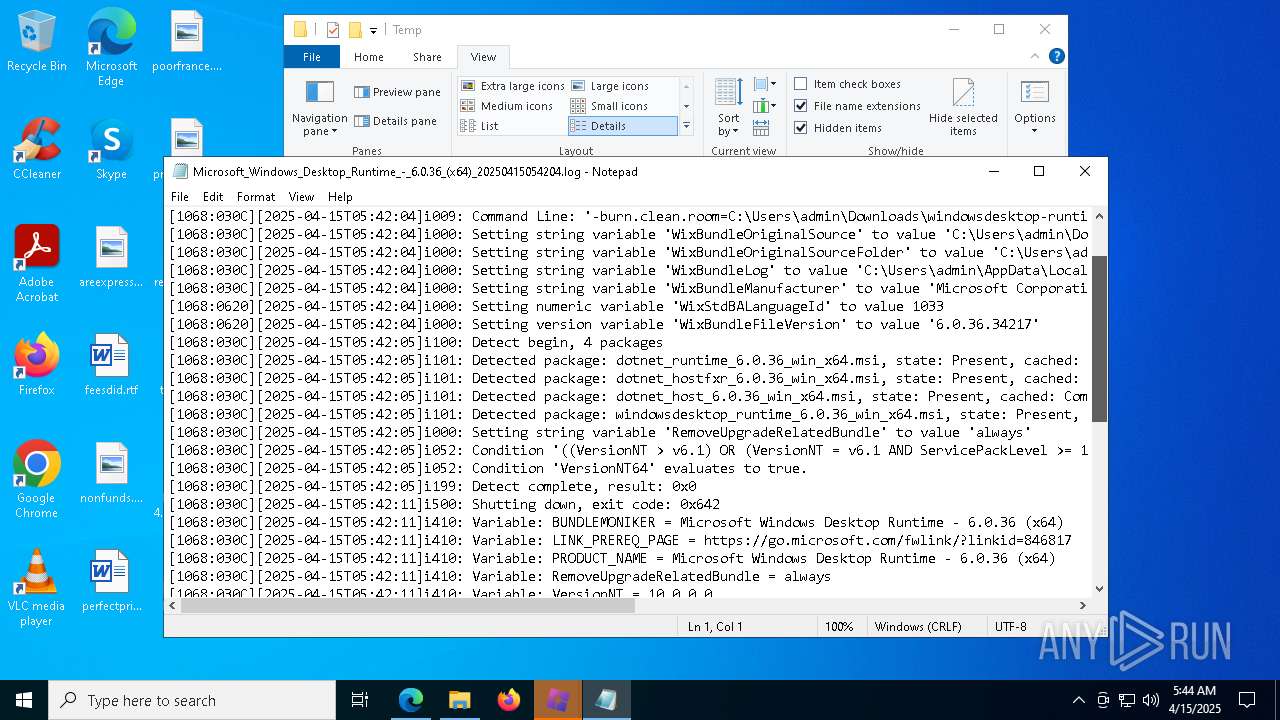
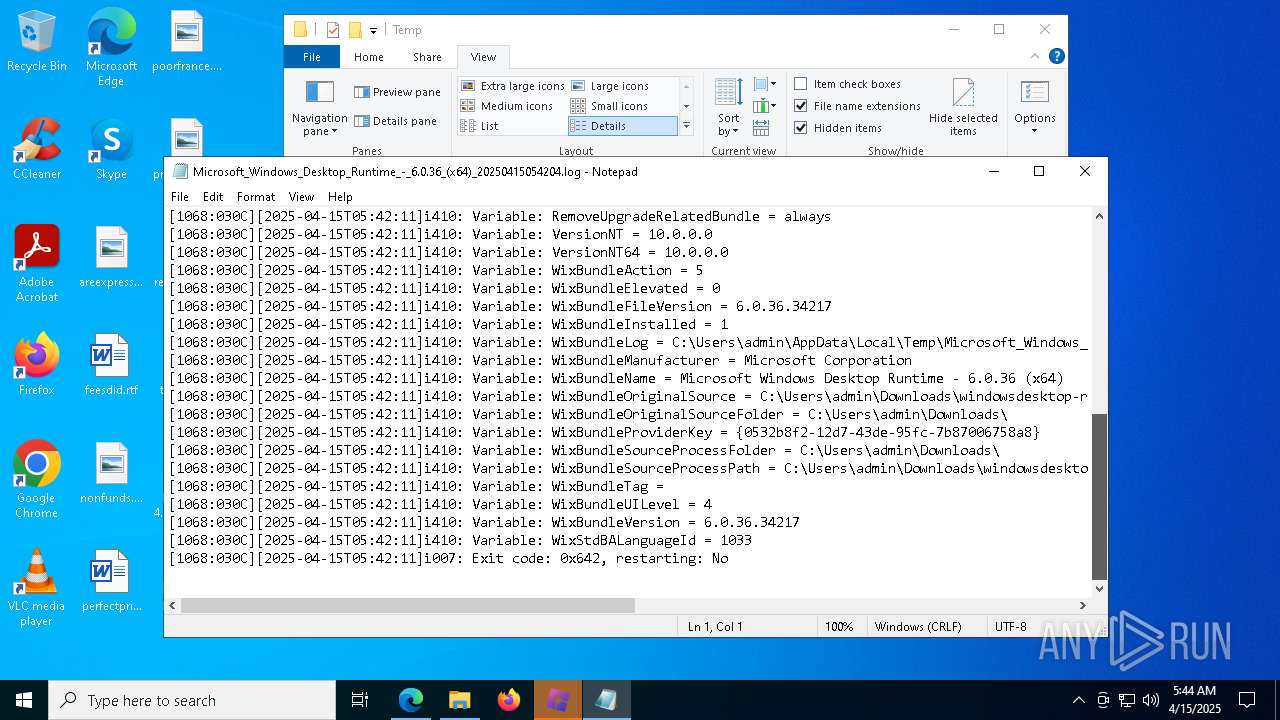
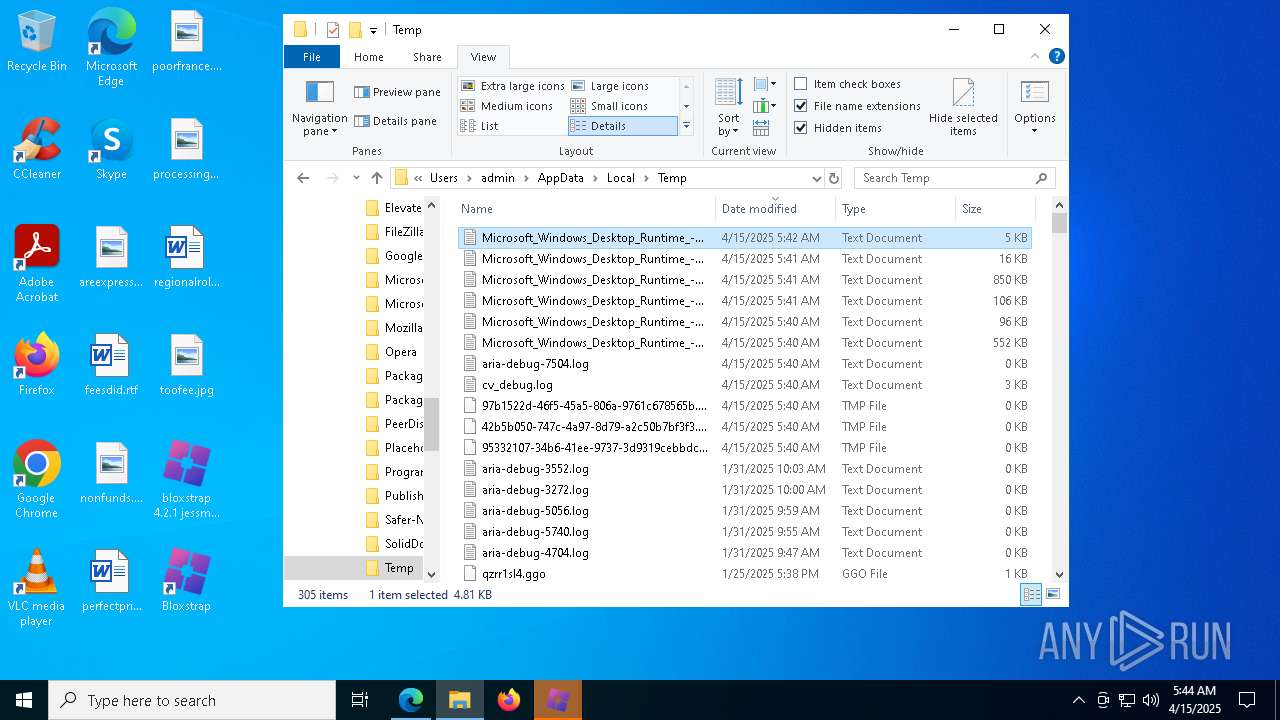
Create files in a temporary directory
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 8084)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 3268)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 4200)
- MicrosoftEdgeWebview2Setup.exe (PID: 5552)
- MicrosoftEdgeUpdate.exe (PID: 7084)
The sample compiled with english language support
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 8084)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- msiexec.exe (PID: 4464)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 3268)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 4200)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- MicrosoftEdgeWebview2Setup.exe (PID: 5552)
- MicrosoftEdgeUpdate.exe (PID: 7084)
- msedge.exe (PID: 6032)
Process checks computer location settings
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7200)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- MicrosoftEdgeUpdate.exe (PID: 7084)
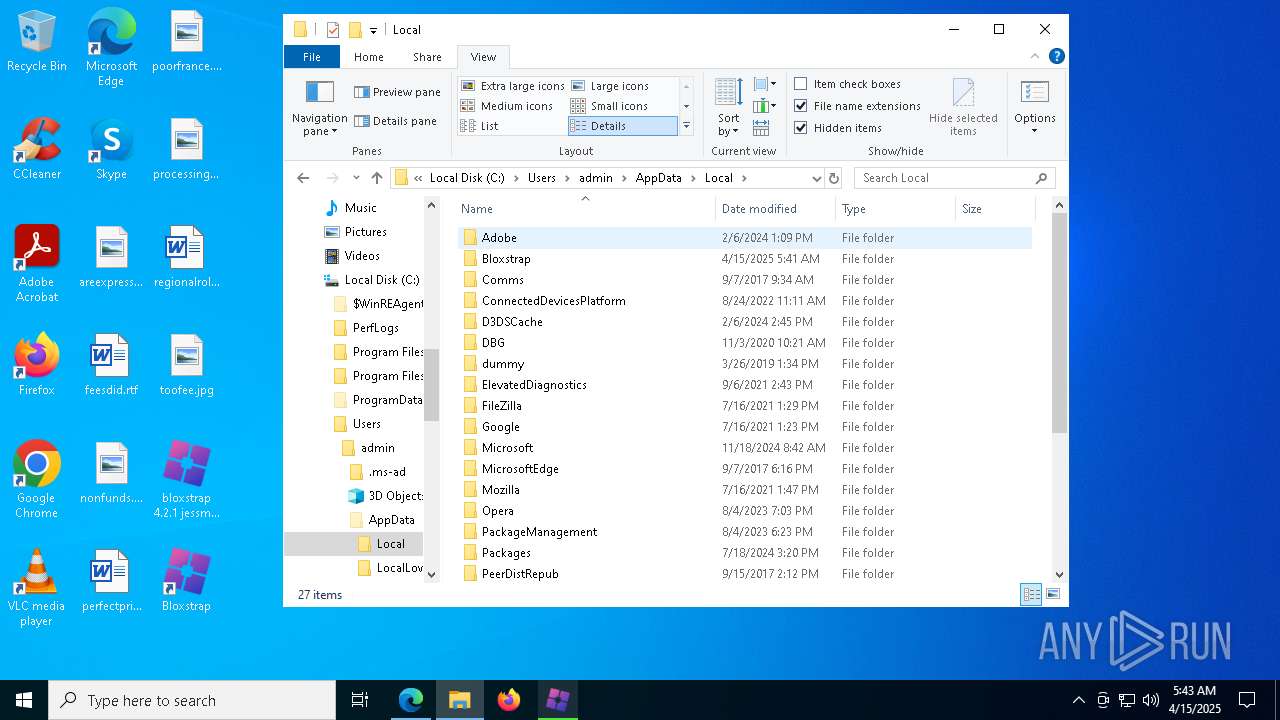
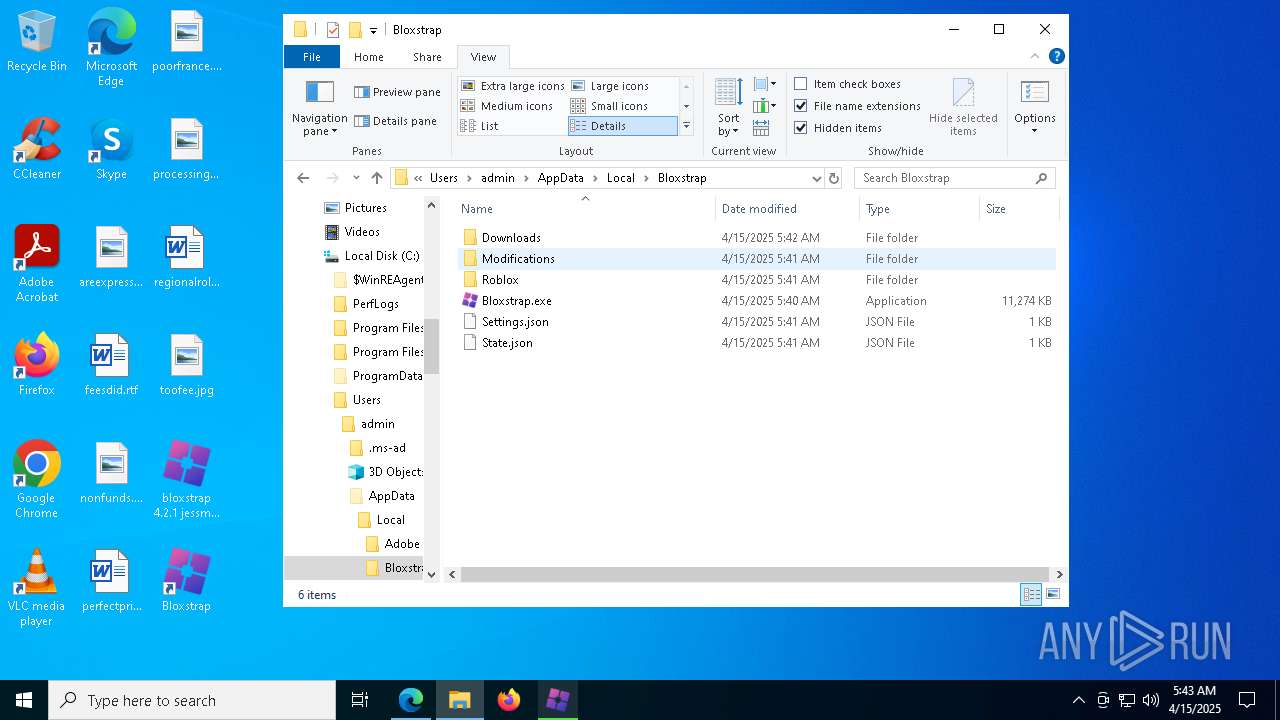
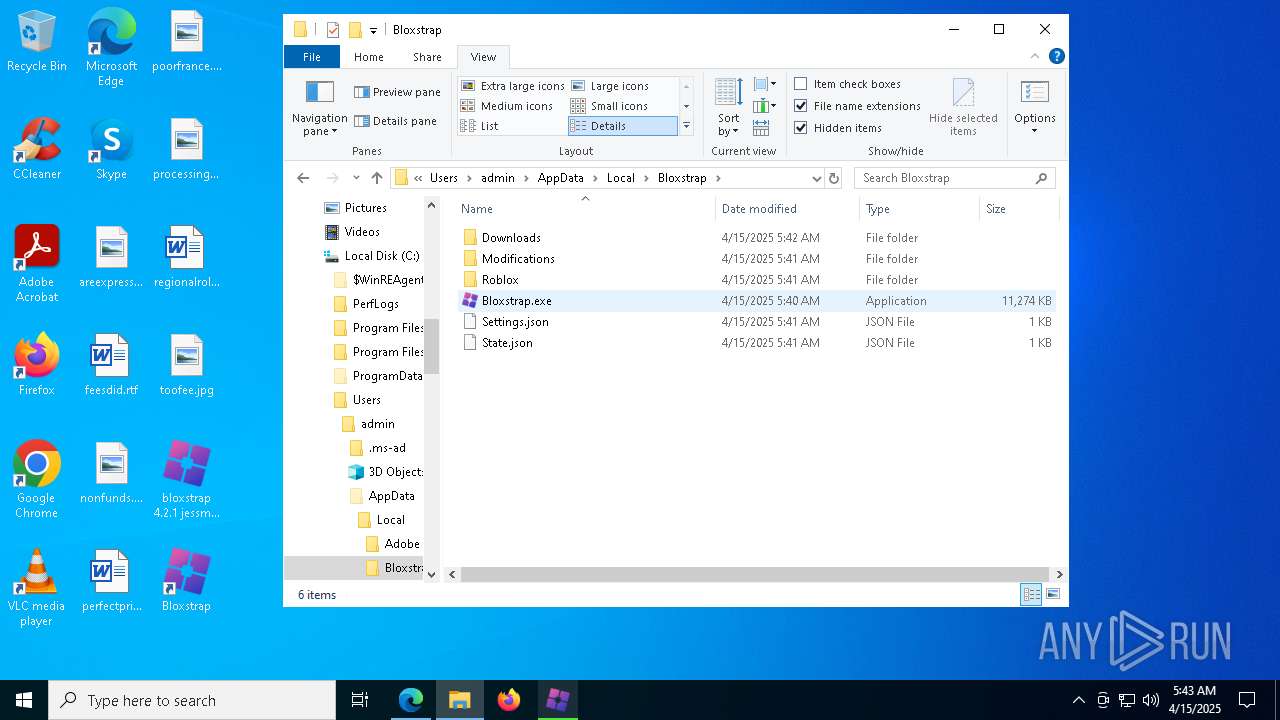
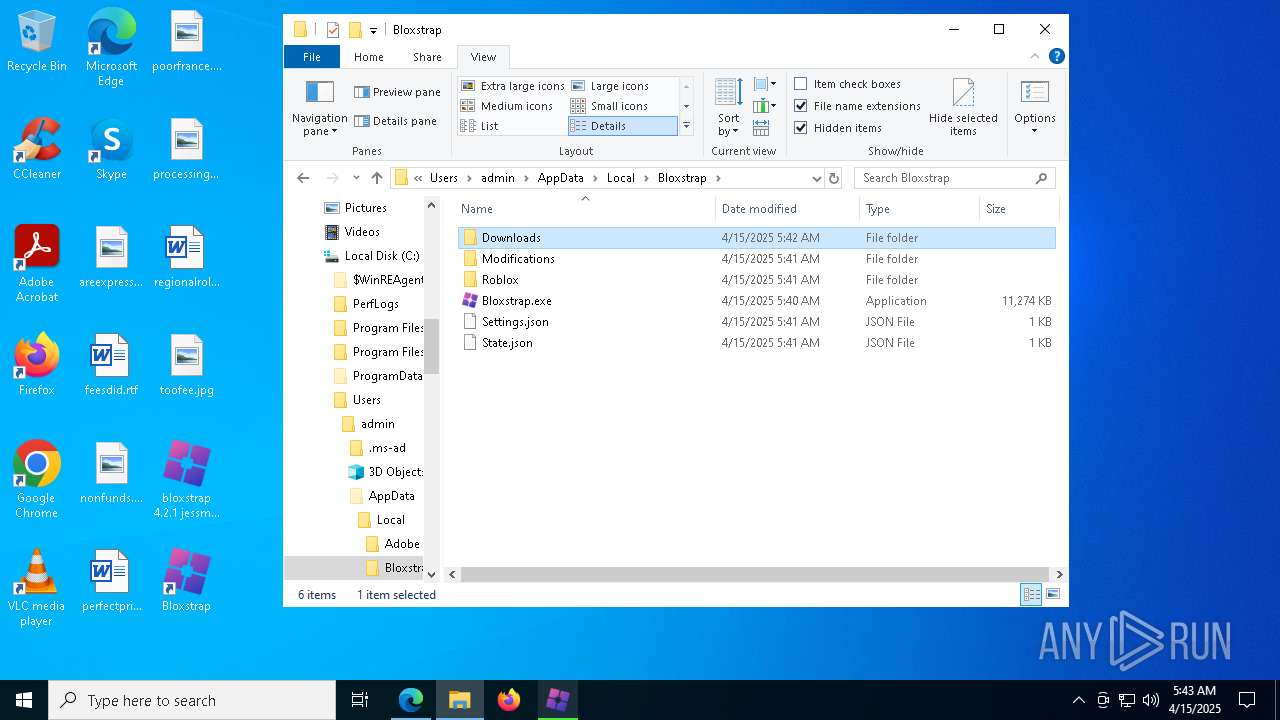
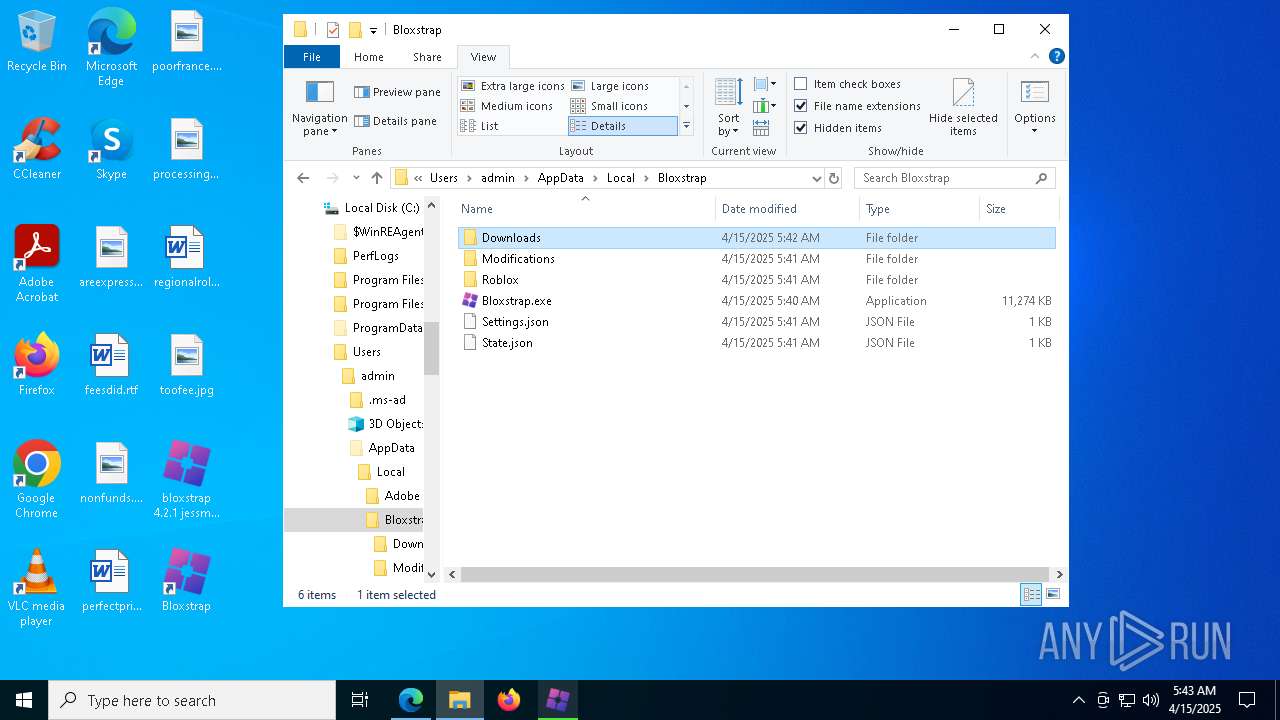
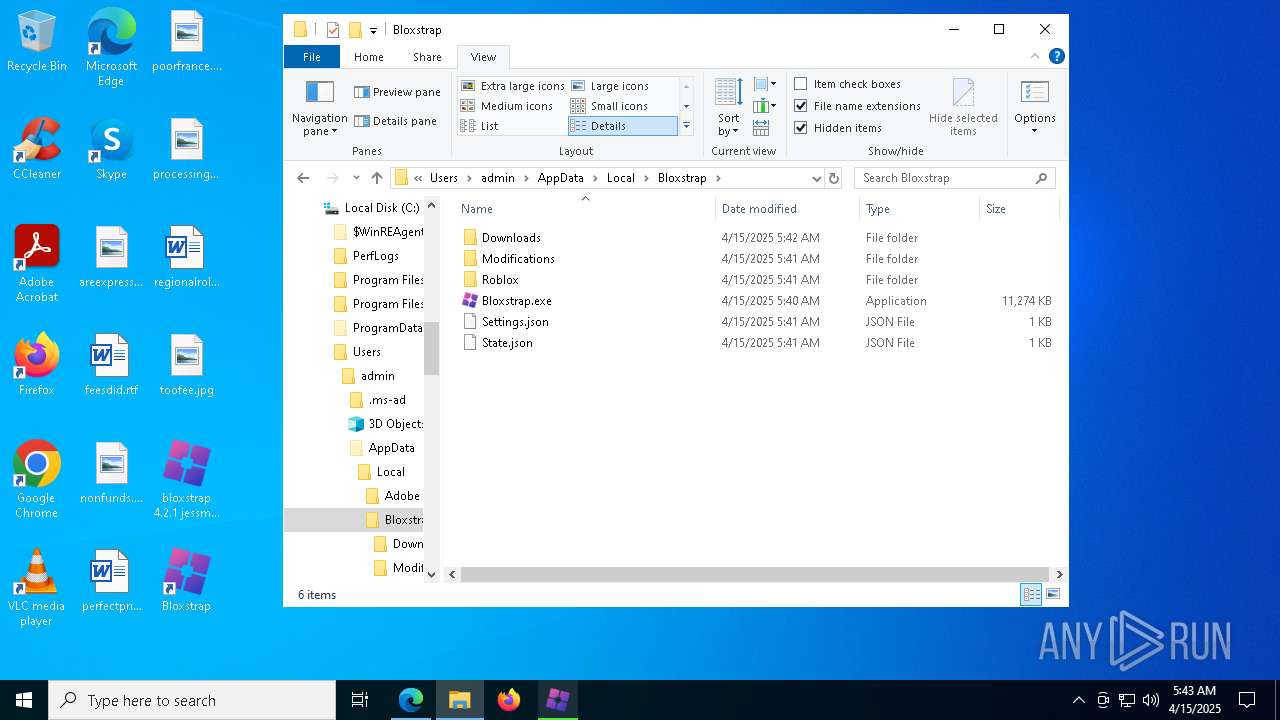
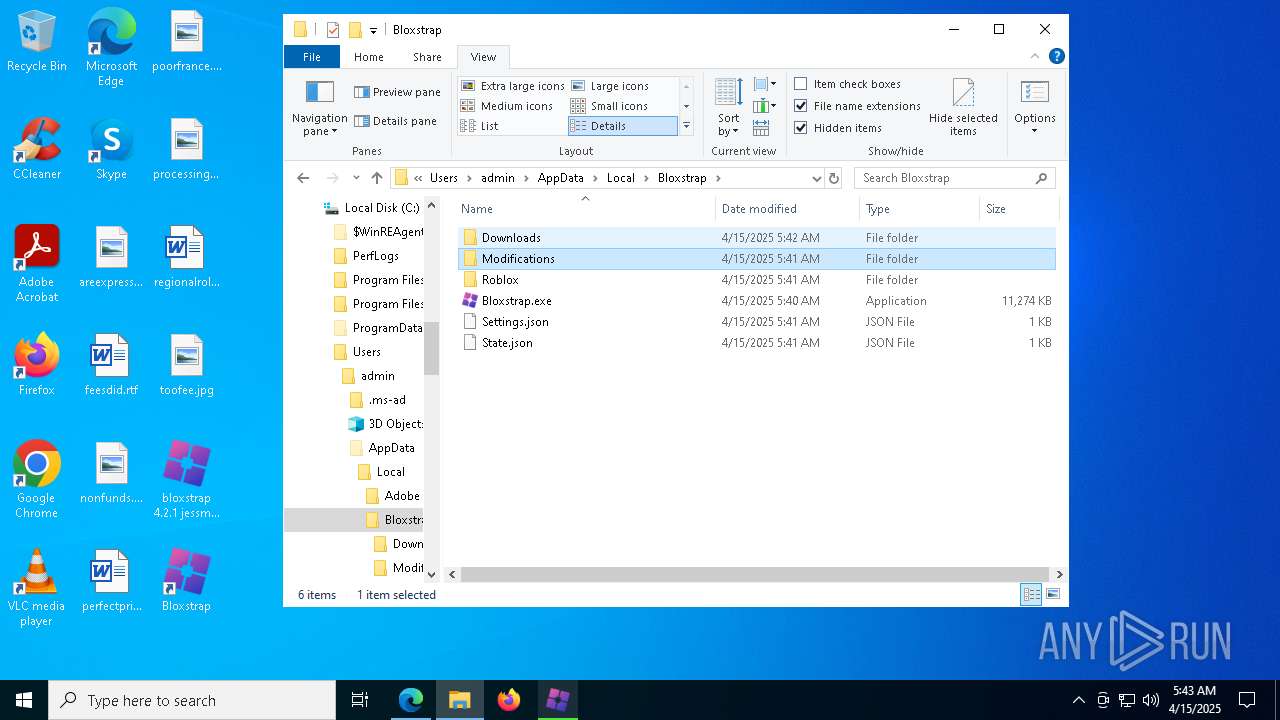
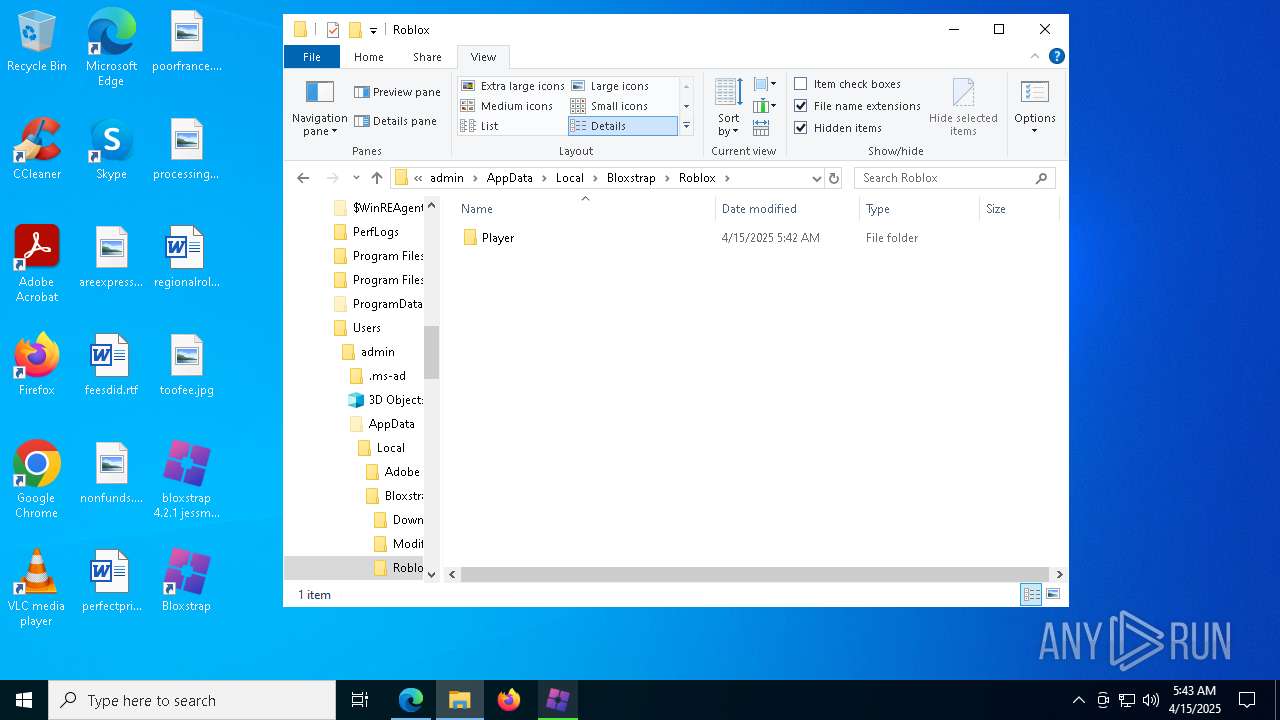
Creates files in the program directory
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
Reads the machine GUID from the registry
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 7752)
- msiexec.exe (PID: 4464)
Reads the software policy settings
- msiexec.exe (PID: 4464)
- slui.exe (PID: 6372)
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- slui.exe (PID: 8076)
- MicrosoftEdgeUpdate.exe (PID: 3032)
- MicrosoftEdgeUpdate.exe (PID: 8112)
Creates a software uninstall entry
- msiexec.exe (PID: 4464)
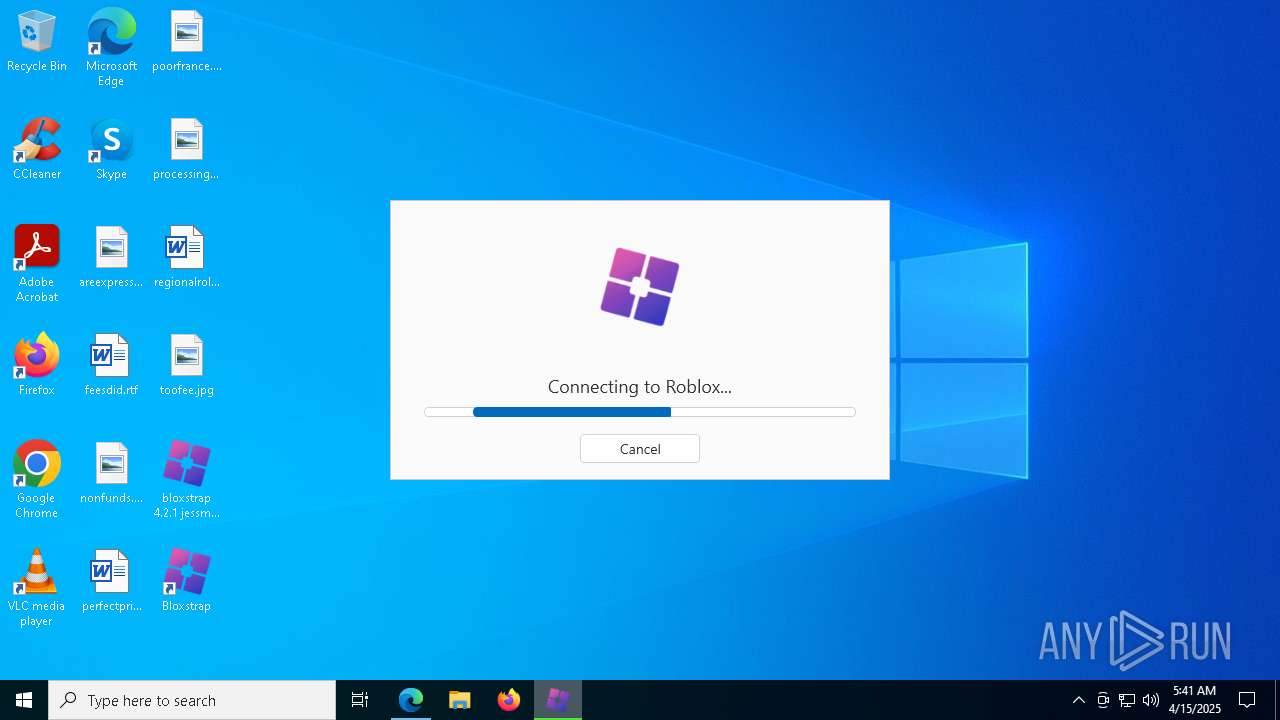
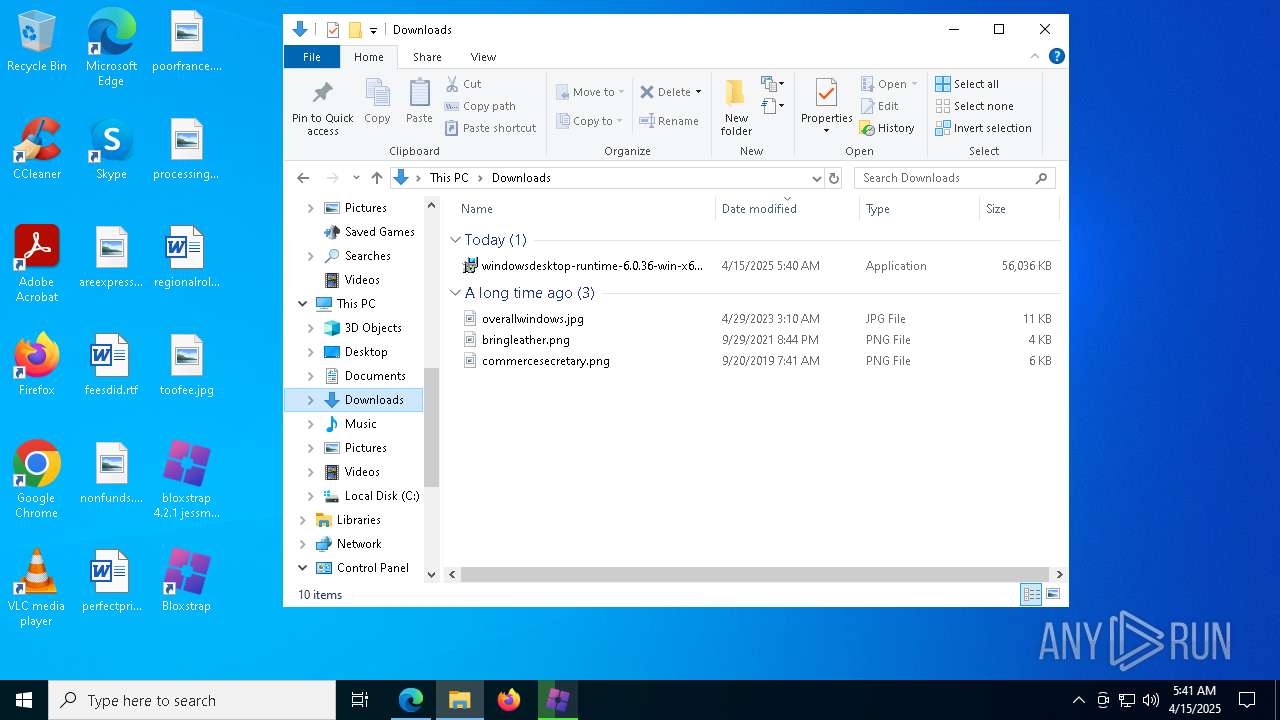
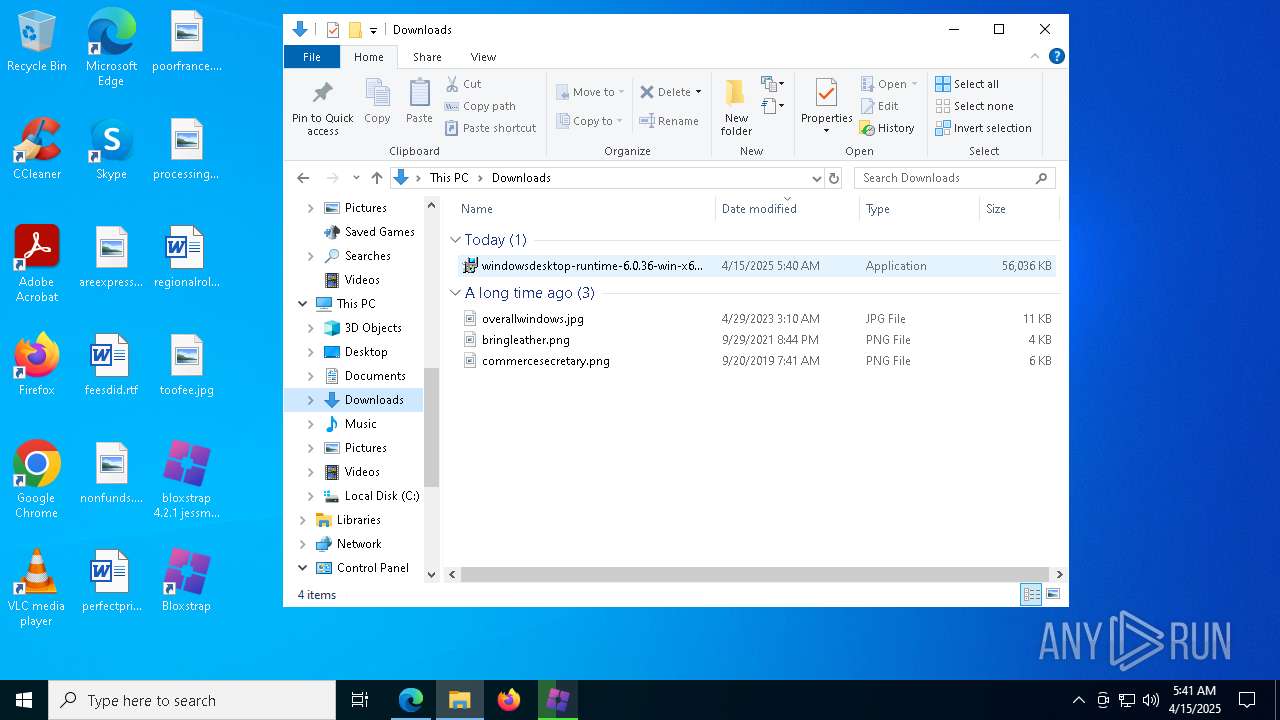
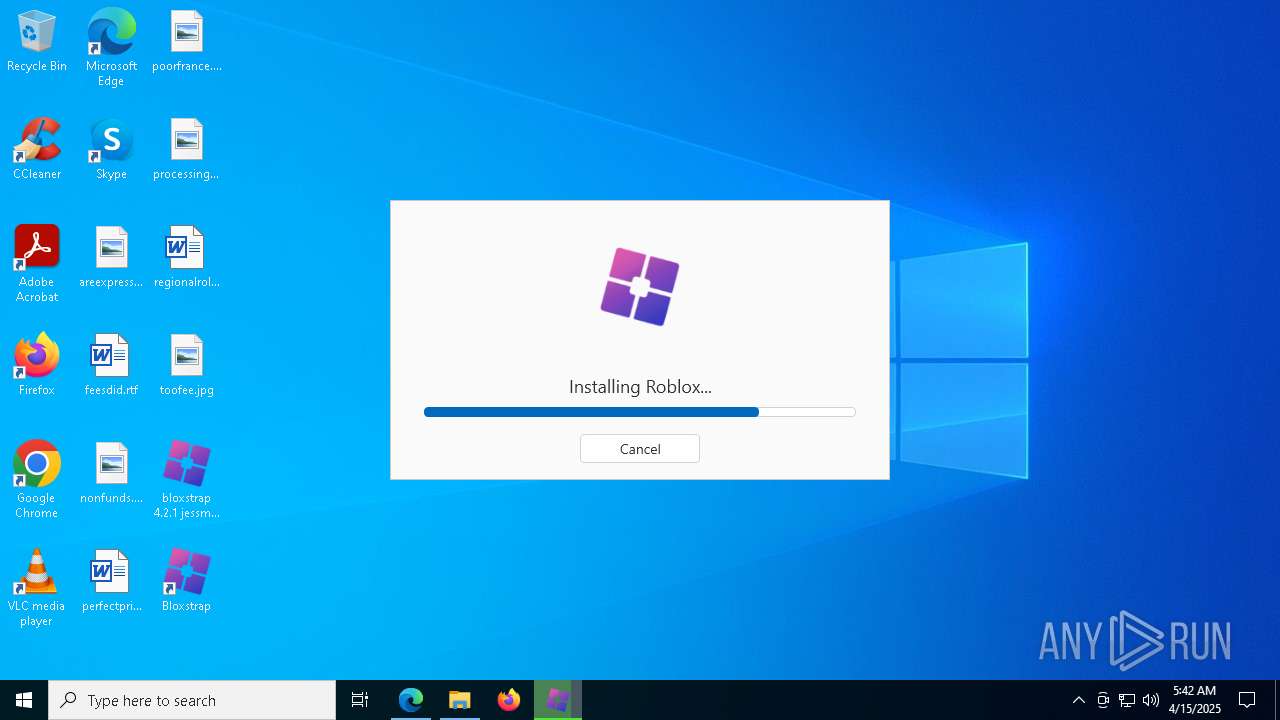
Manual execution by a user
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- windowsdesktop-runtime-6.0.36-win-x64.exe (PID: 3268)
- notepad.exe (PID: 2644)
- notepad.exe (PID: 8004)
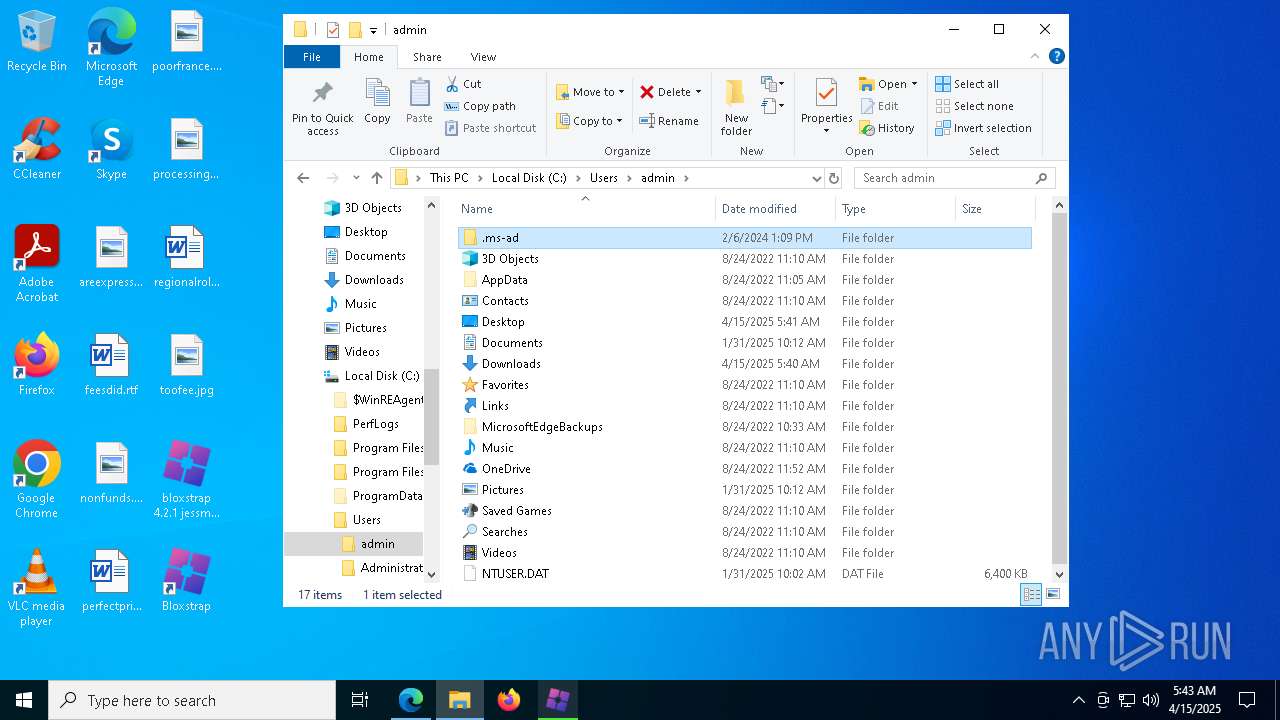
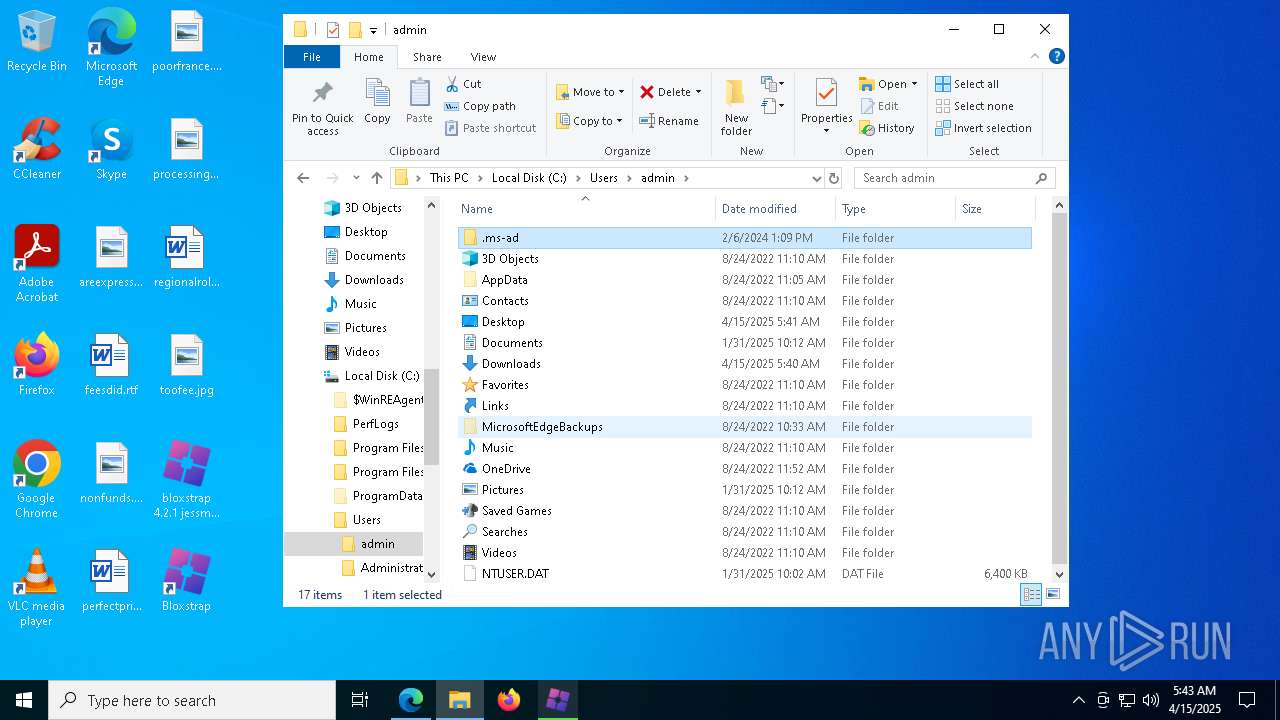
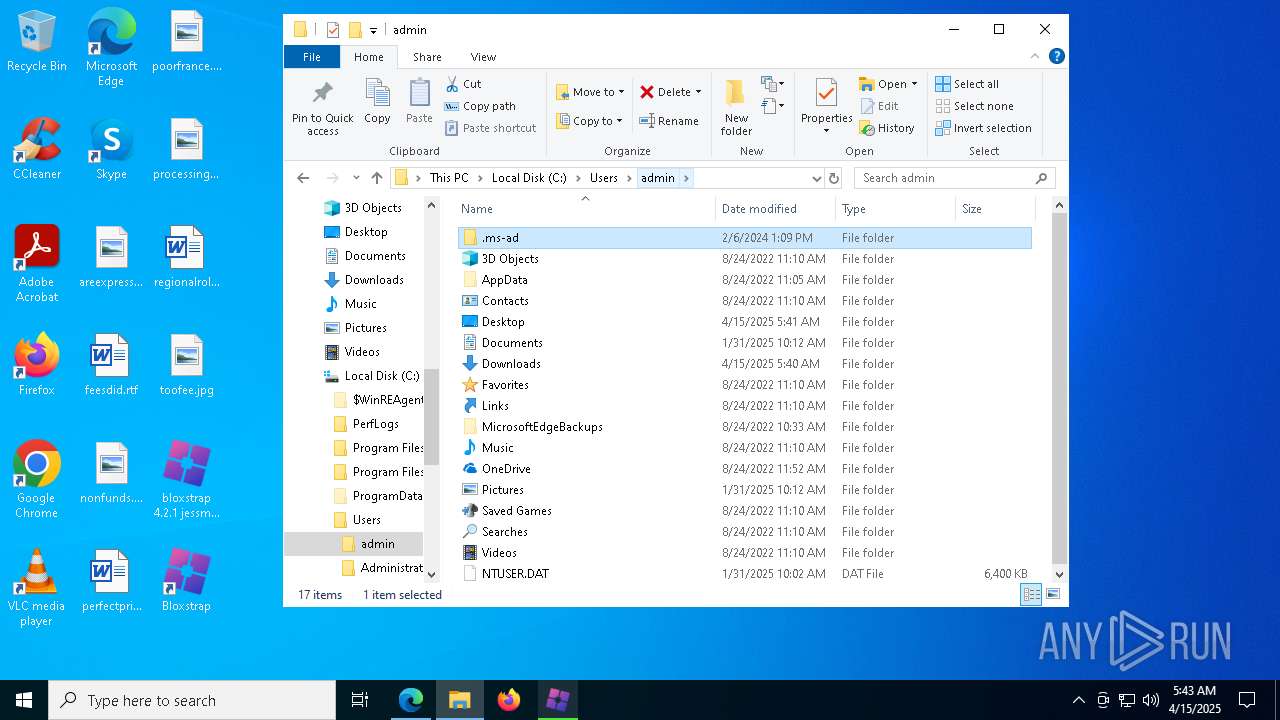
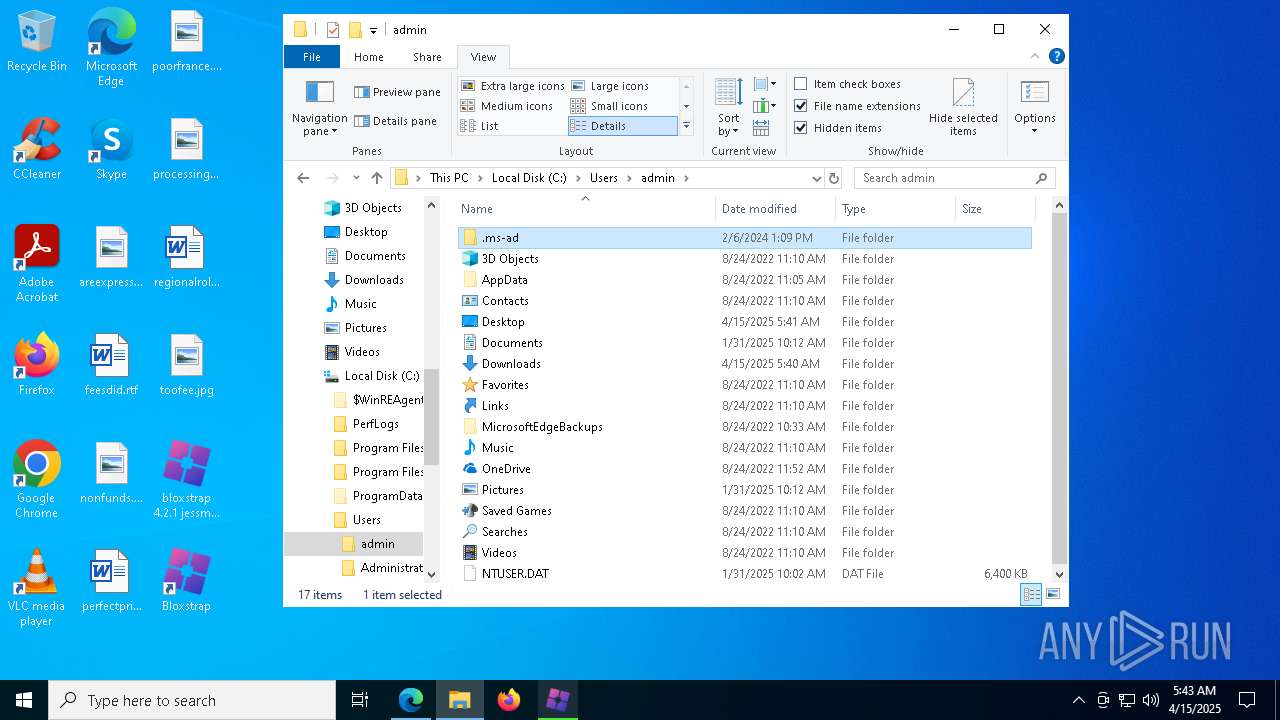
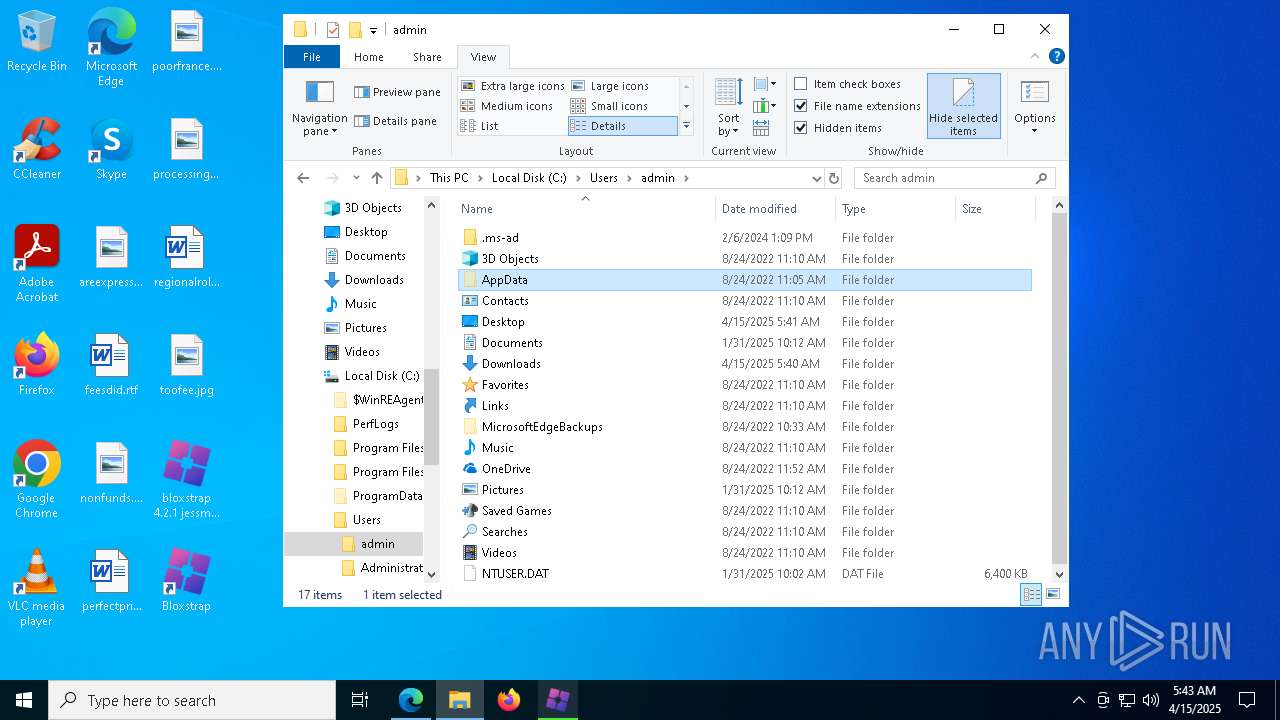
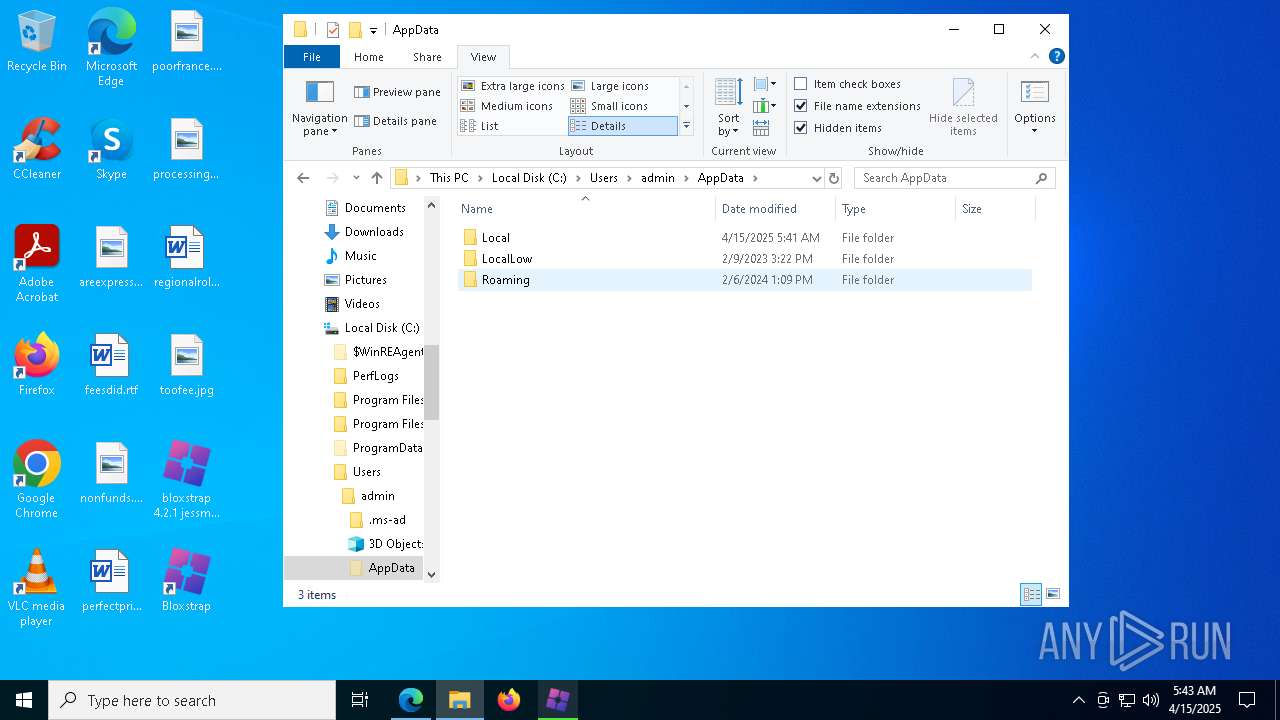
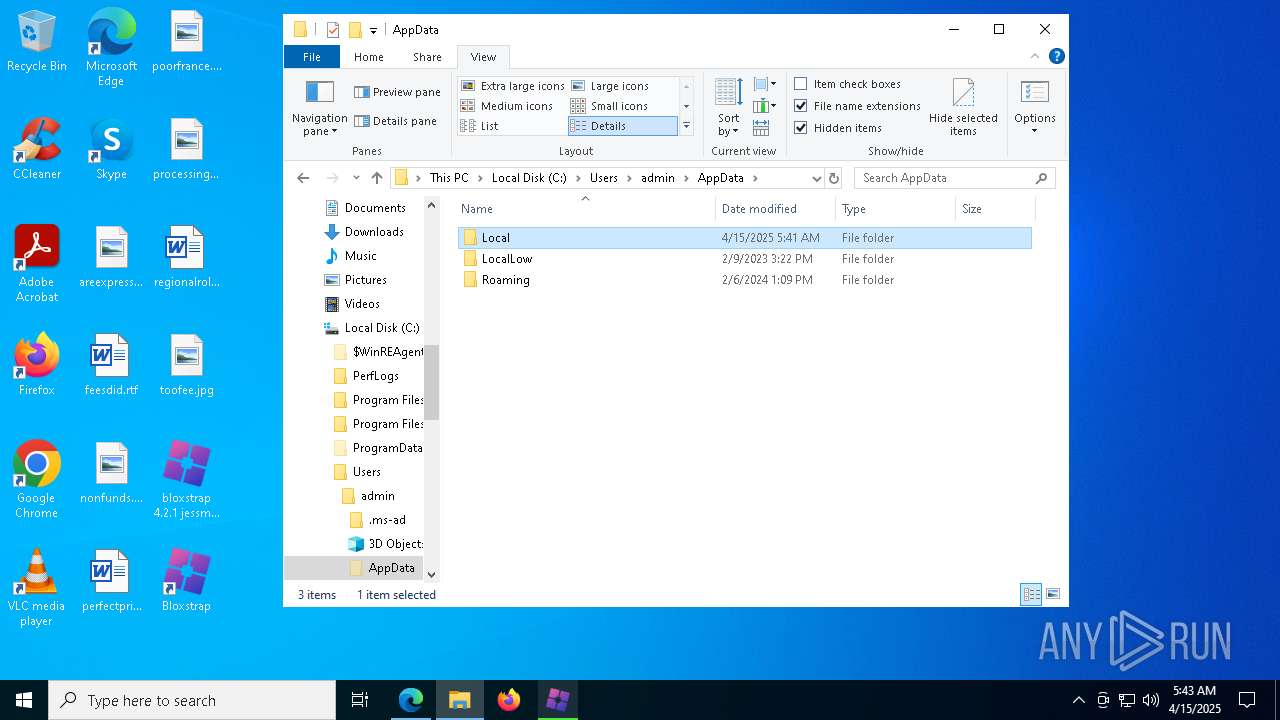
Creates files or folders in the user directory
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- MicrosoftEdgeUpdate.exe (PID: 7084)
Checks proxy server information
- bloxstrap 4.2.1 jessmods.exe .exe (PID: 7872)
- slui.exe (PID: 8076)
- MicrosoftEdgeUpdate.exe (PID: 3032)
- MicrosoftEdgeUpdate.exe (PID: 8112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (46.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (41) |
| .exe | | | Win32 Executable (generic) (6.6) |
| .exe | | | Generic Win/DOS Executable (2.9) |
| .exe | | | DOS Executable Generic (2.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:09 14:02:40+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.29 |
| CodeSize: | 99840 |
| InitializedDataSize: | 190464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14050 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.2.1.0 |
| ProductVersionNumber: | 4.2.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Bloxstrap |
| FileDescription: | Bloxstrap |
| FileVersion: | 4.2.1 |
| InternalName: | Bloxstrap.dll |
| LegalCopyright: | |
| OriginalFileName: | Bloxstrap.dll |
| ProductName: | Bloxstrap |
| ProductVersion: | 4.2.1 |
| AssemblyVersion: | 4.2.1.0 |
Total processes
218
Monitored processes
81
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5604 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5284 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5812 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | C:\Windows\syswow64\MsiExec.exe -Embedding 6F5262CACF8FA7B0FC4B920928879EEB | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5612 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7044 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7876 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2784 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2280 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1912 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7044 --field-trial-handle=2300,i,15705778602456690153,3810222696190397632,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
24 873
Read events
22 749
Write events
2 045
Delete events
79
Modification events
| (PID) Process: | (6808) bloxstrap 4.2.1 jessmods.exe .exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6808) bloxstrap 4.2.1 jessmods.exe .exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6808) bloxstrap 4.2.1 jessmods.exe .exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6808) bloxstrap 4.2.1 jessmods.exe .exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2088) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2088) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2088) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2088) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2088) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1FC9A0E360912F00 | |||
| (PID) Process: | (2088) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5399AEE360912F00 | |||
Executable files
795
Suspicious files
687
Text files
3 282
Unknown types
0
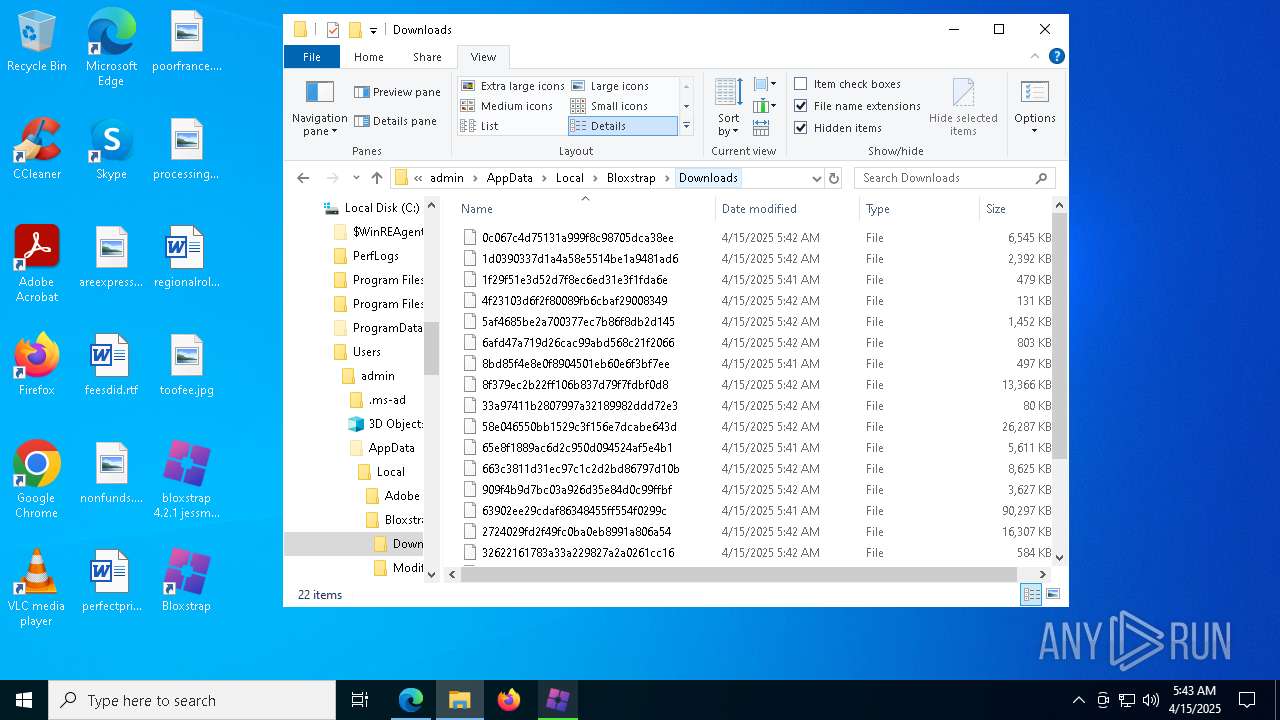
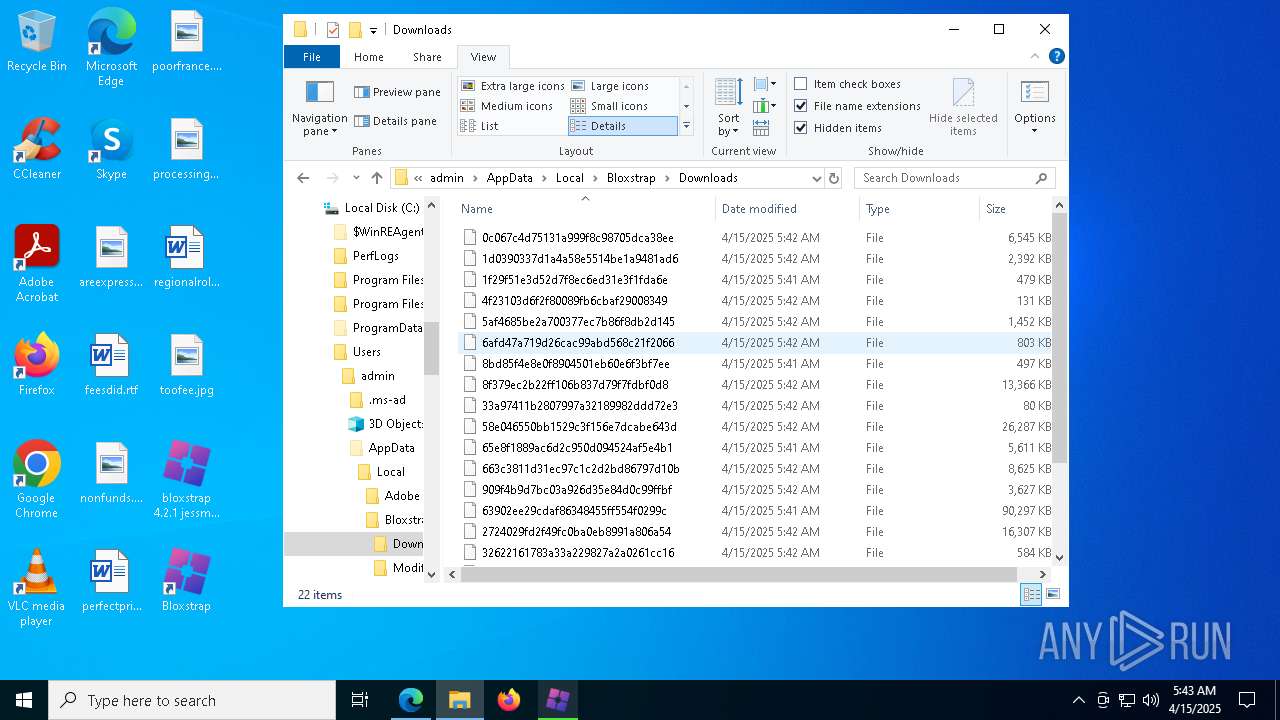
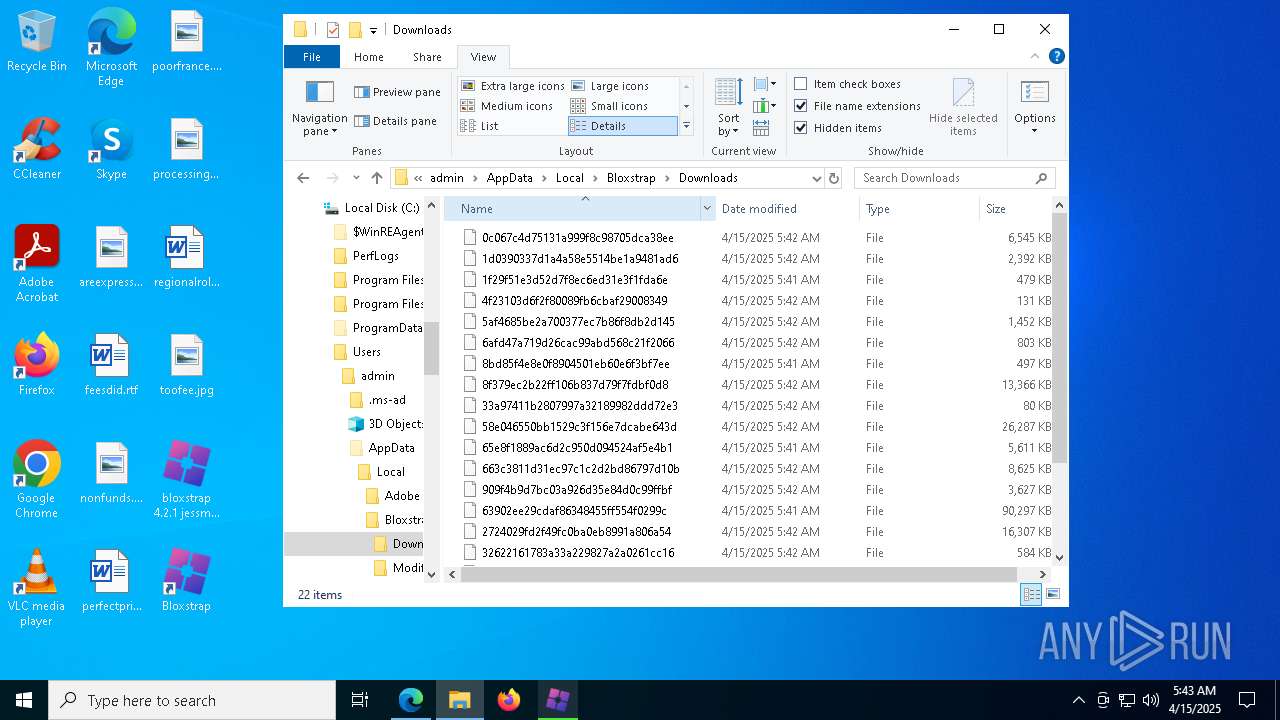
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10d7f3.TMP | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10d803.TMP | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10d803.TMP | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10d803.TMP | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10d812.TMP | — | |
MD5:— | SHA256:— | |||
| 2088 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
84
DNS requests
102
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7744 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7744 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2088 | msedge.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2088 | msedge.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
1912 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744953270&P2=404&P3=2&P4=i1%2fgoAMpRKhNL%2fcIBj%2f%2fSh6tBKn%2bJu6UAyjWHKzcQYZim52tVcpXDULM3x4UScVevLguwblXwK%2ba4UxZYI8xIA%3d%3d | unknown | — | — | whitelisted |
1912 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744953270&P2=404&P3=2&P4=i1%2fgoAMpRKhNL%2fcIBj%2f%2fSh6tBKn%2bJu6UAyjWHKzcQYZim52tVcpXDULM3x4UScVevLguwblXwK%2ba4UxZYI8xIA%3d%3d | unknown | — | — | whitelisted |
1912 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744953270&P2=404&P3=2&P4=i1%2fgoAMpRKhNL%2fcIBj%2f%2fSh6tBKn%2bJu6UAyjWHKzcQYZim52tVcpXDULM3x4UScVevLguwblXwK%2ba4UxZYI8xIA%3d%3d | unknown | — | — | whitelisted |
1912 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744953270&P2=404&P3=2&P4=i1%2fgoAMpRKhNL%2fcIBj%2f%2fSh6tBKn%2bJu6UAyjWHKzcQYZim52tVcpXDULM3x4UScVevLguwblXwK%2ba4UxZYI8xIA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2088 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
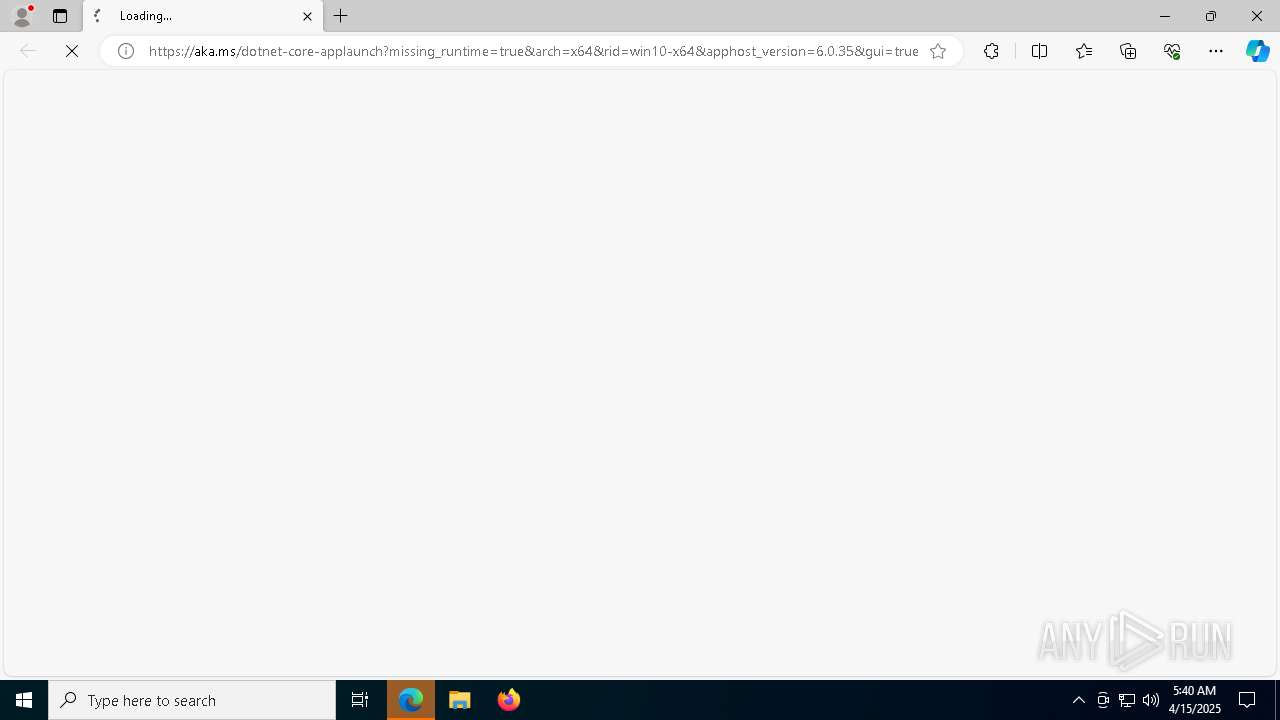
aka.ms |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1912 | svchost.exe | Misc activity | ET INFO Packed Executable Download |