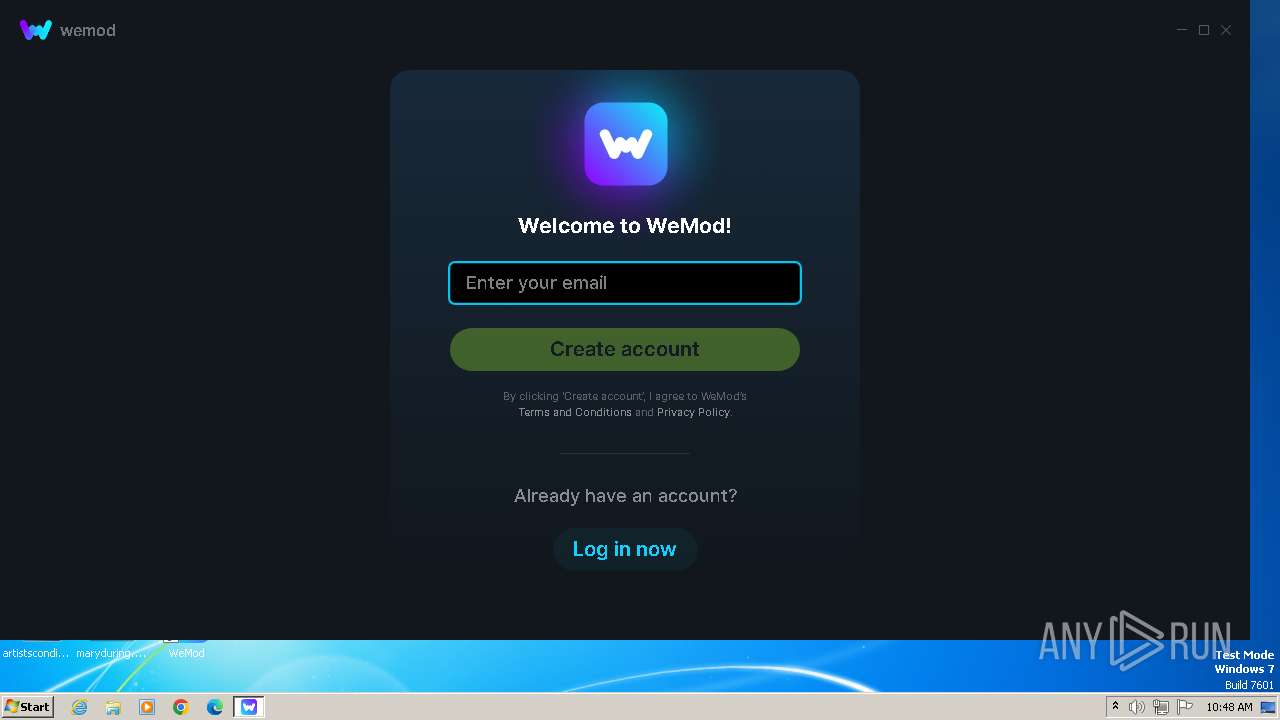
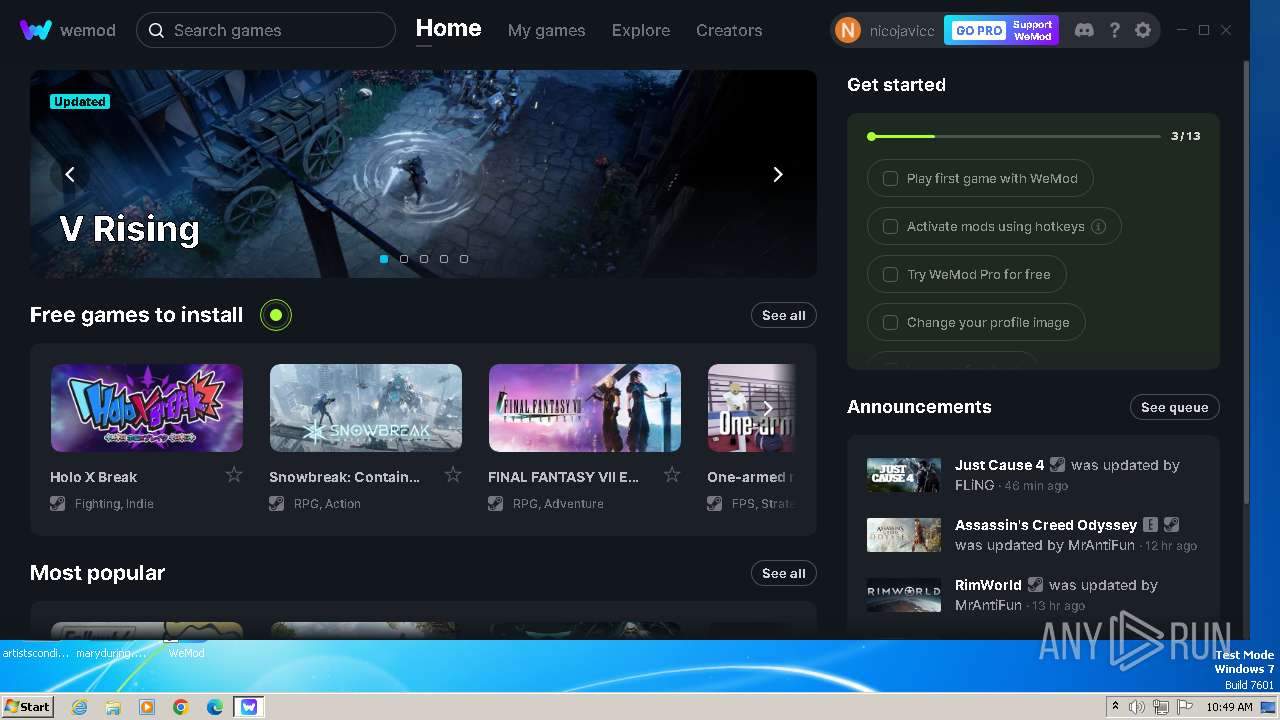
| File name: | WeMod-Setup.exe |
| Full analysis: | https://app.any.run/tasks/7da563bc-b4eb-4cf7-92c3-c518d533e884 |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2024, 09:46:27 |
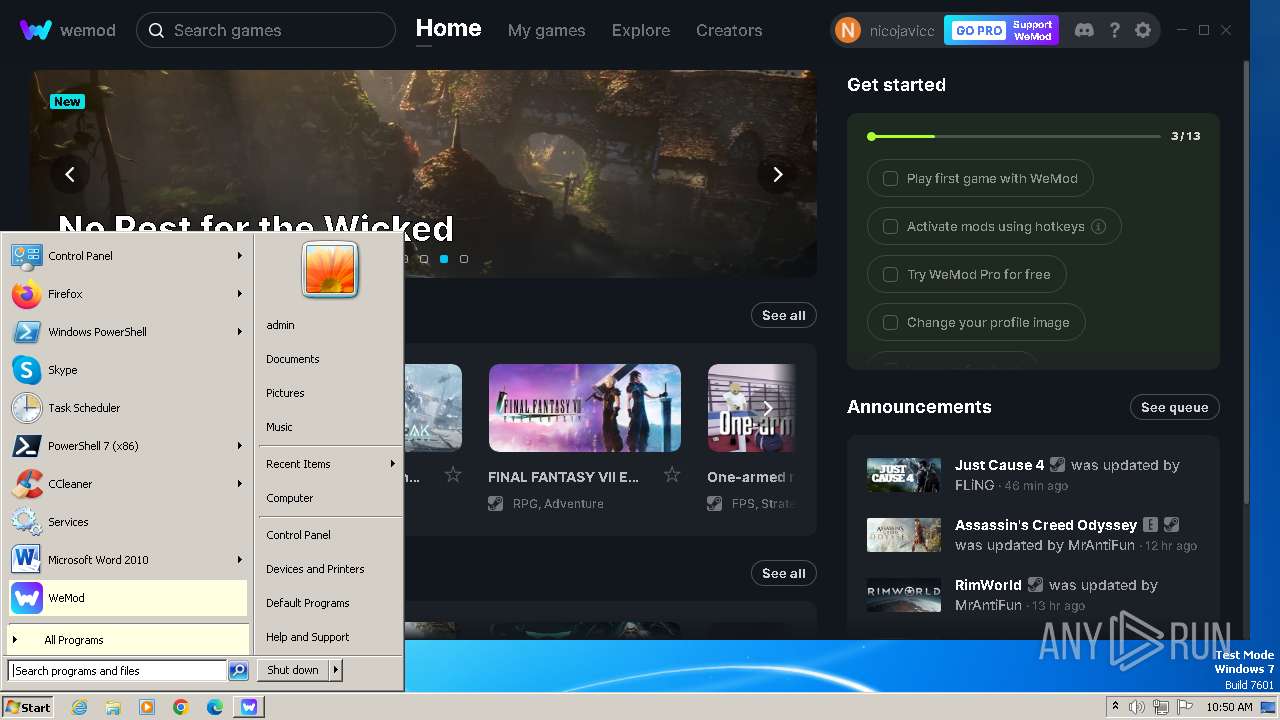
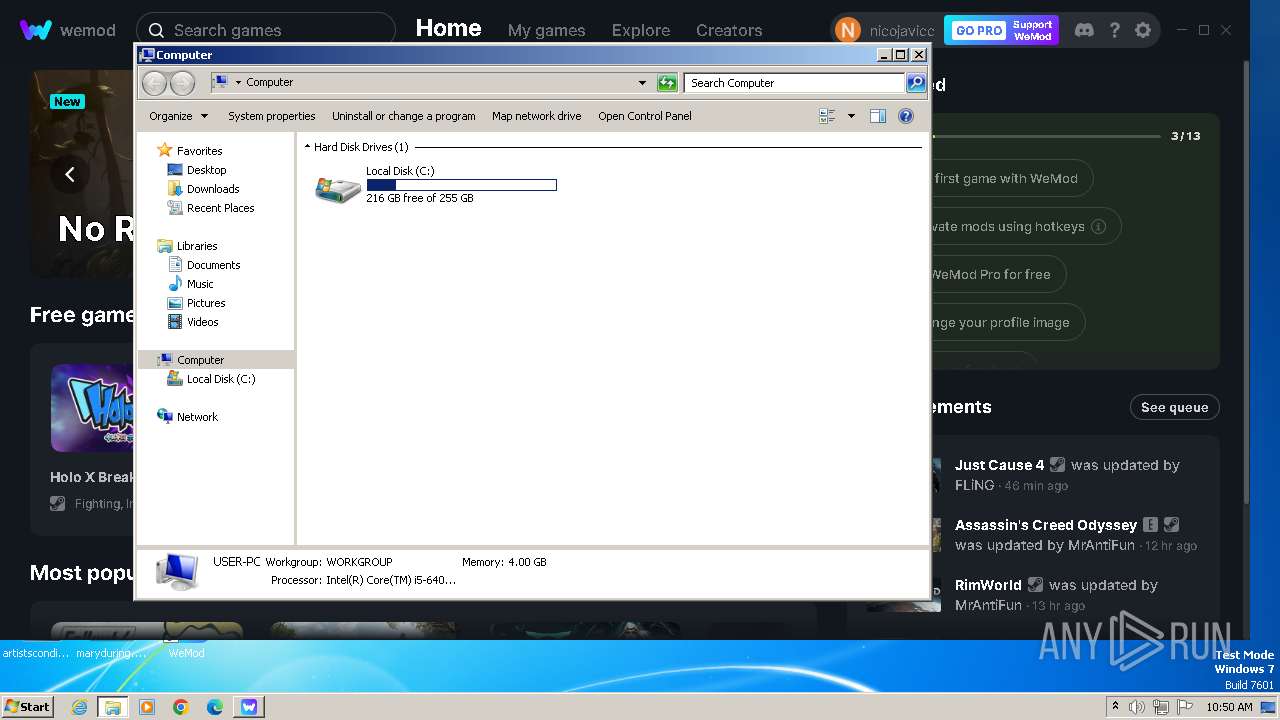
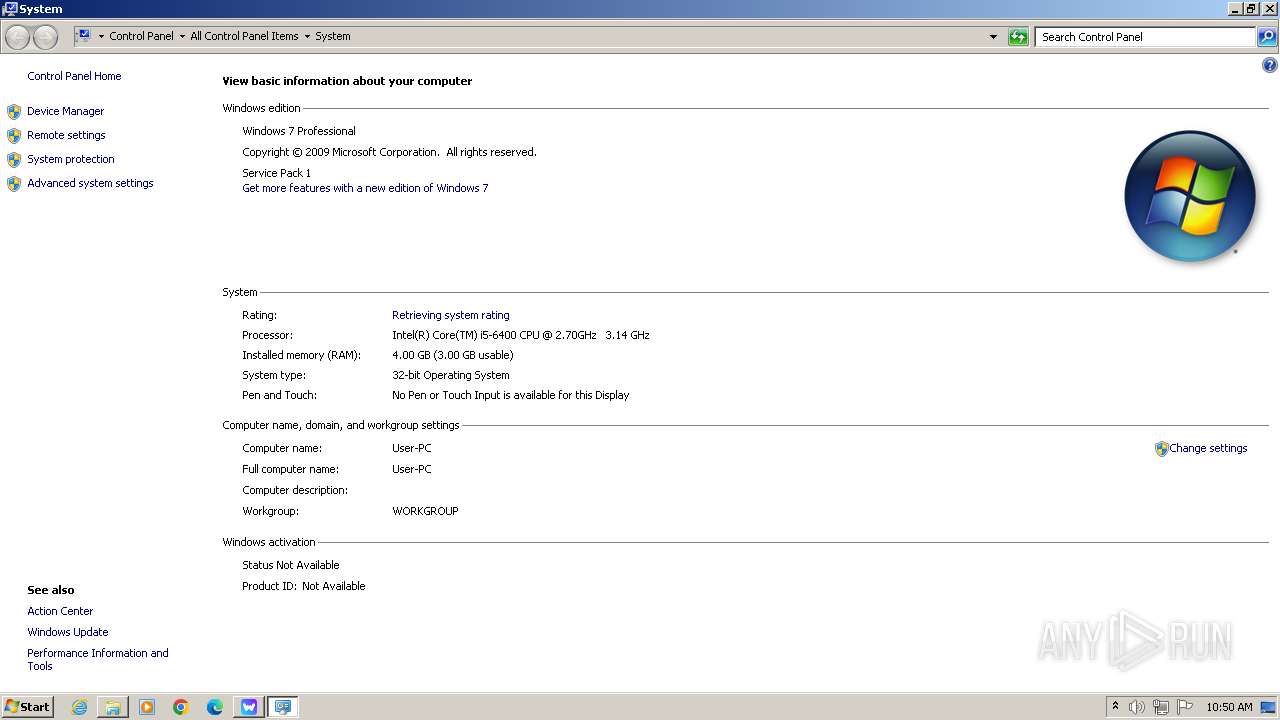
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0F92932E3D228414BCDB10E813221D1C |
| SHA1: | 52BF7531AF783E74E2450E85C21FF19F15280AC8 |
| SHA256: | 0ED8B1AE4816553389404BF9F7961B0A1CB3632B3403F8FCE8DE93F154C36575 |
| SSDEEP: | 1536:mBll12iut9nk7RBog5KG6JkOiVPL+09ME5LBtJD64uQgCANR9HEdOyJkNRBog5KZ:Q12ioE57miVj+J6pHdokdOp57N/ |
MALICIOUS
Drops the executable file immediately after the start
- WeMod-Setup.exe (PID: 3968)
- WeMod-Setup-638511040038411250.exe (PID: 1588)
- Update.exe (PID: 1704)
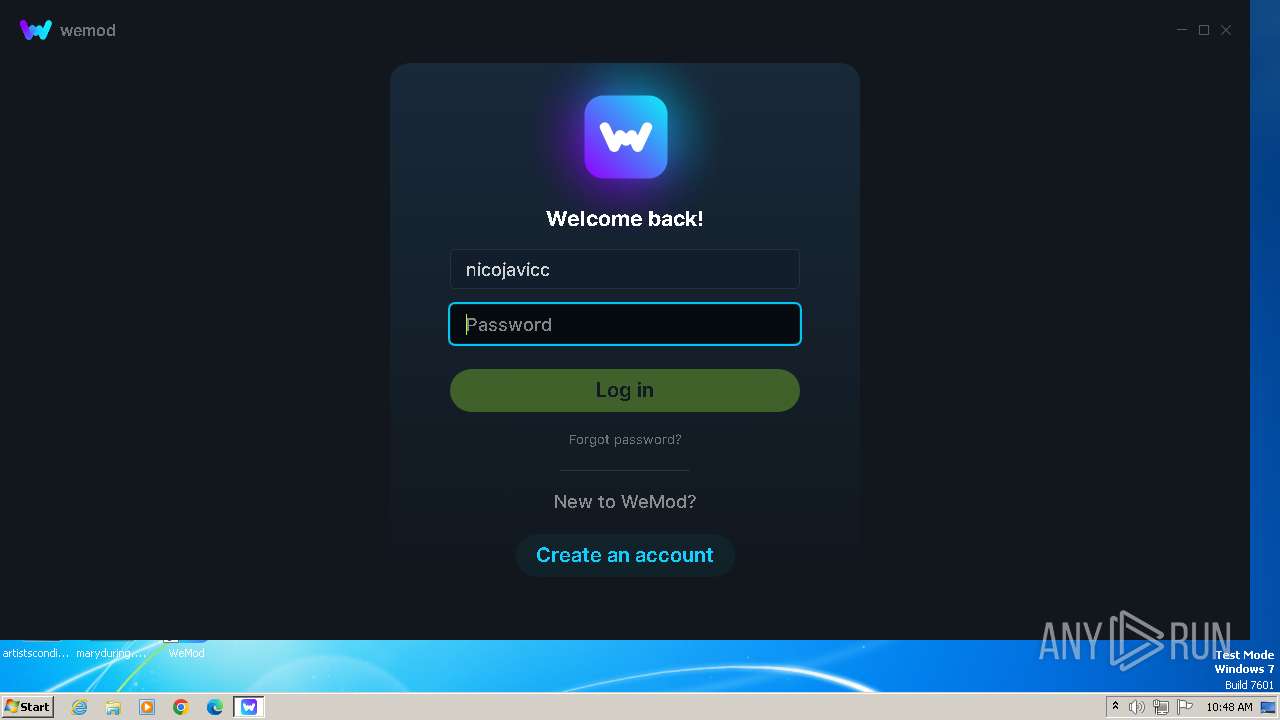
Actions looks like stealing of personal data
- WeMod.exe (PID: 2692)
SUSPICIOUS
Reads the Internet Settings
- WeMod-Setup.exe (PID: 3968)
- Update.exe (PID: 1704)
- Update.exe (PID: 2448)
- WeMod.exe (PID: 1612)
- Update.exe (PID: 2916)
Reads security settings of Internet Explorer
- WeMod-Setup.exe (PID: 3968)
- Update.exe (PID: 1704)
- Update.exe (PID: 2448)
Reads Microsoft Outlook installation path
- WeMod-Setup.exe (PID: 3968)
Reads settings of System Certificates
- WeMod-Setup.exe (PID: 3968)
- Update.exe (PID: 1704)
- WeMod.exe (PID: 1612)
- Update.exe (PID: 2916)
Checks Windows Trust Settings
- WeMod-Setup.exe (PID: 3968)
Reads Internet Explorer settings
- WeMod-Setup.exe (PID: 3968)
Executable content was dropped or overwritten
- WeMod-Setup-638511040038411250.exe (PID: 1588)
- Update.exe (PID: 1704)
Process drops legitimate windows executable
- Update.exe (PID: 1704)
Searches for installed software
- Update.exe (PID: 1704)
Creates a software uninstall entry
- Update.exe (PID: 1704)
Application launched itself
- WeMod.exe (PID: 1612)
INFO
Checks supported languages
- WeMod-Setup.exe (PID: 3968)
- wmpnscfg.exe (PID: 1184)
- WeMod-Setup-638511040038411250.exe (PID: 1588)
- Update.exe (PID: 1704)
- squirrel.exe (PID: 1836)
- Update.exe (PID: 2268)
- Update.exe (PID: 2448)
- WeMod.exe (PID: 1612)
- WeMod.exe (PID: 1548)
- WeMod.exe (PID: 1848)
- WeMod.exe (PID: 936)
- WeMod.exe (PID: 2692)
- WeMod.exe (PID: 916)
- Update.exe (PID: 2916)
- WeModAuxiliaryService.exe (PID: 2788)
Reads the computer name
- WeMod-Setup.exe (PID: 3968)
- wmpnscfg.exe (PID: 1184)
- Update.exe (PID: 1704)
- squirrel.exe (PID: 1836)
- Update.exe (PID: 2268)
- Update.exe (PID: 2448)
- WeMod.exe (PID: 1848)
- WeMod.exe (PID: 1612)
- WeMod.exe (PID: 936)
- Update.exe (PID: 2916)
- WeModAuxiliaryService.exe (PID: 2788)
- WeMod.exe (PID: 916)
Reads the machine GUID from the registry
- WeMod-Setup.exe (PID: 3968)
- Update.exe (PID: 1704)
- squirrel.exe (PID: 1836)
- Update.exe (PID: 2268)
- Update.exe (PID: 2448)
- WeMod.exe (PID: 1612)
- Update.exe (PID: 2916)
- WeModAuxiliaryService.exe (PID: 2788)
Checks proxy server information
- WeMod-Setup.exe (PID: 3968)
Reads the software policy settings
- WeMod-Setup.exe (PID: 3968)
- Update.exe (PID: 1704)
- WeMod.exe (PID: 1612)
- Update.exe (PID: 2916)
Creates files or folders in the user directory
- WeMod-Setup.exe (PID: 3968)
- WeMod-Setup-638511040038411250.exe (PID: 1588)
- Update.exe (PID: 1704)
- squirrel.exe (PID: 1836)
- Update.exe (PID: 2268)
- Update.exe (PID: 2448)
- WeMod.exe (PID: 1612)
- WeMod.exe (PID: 936)
- Update.exe (PID: 2916)
Manual execution by a user
- wmpnscfg.exe (PID: 1184)
- taskmgr.exe (PID: 660)
- control.exe (PID: 3280)
Reads Environment values
- WeMod-Setup.exe (PID: 3968)
- WeMod.exe (PID: 1548)
- Update.exe (PID: 1704)
- WeMod.exe (PID: 1612)
- Update.exe (PID: 2916)
Create files in a temporary directory
- WeMod-Setup.exe (PID: 3968)
- Update.exe (PID: 1704)
- WeMod.exe (PID: 1612)
- Update.exe (PID: 2916)
Reads product name
- WeMod.exe (PID: 1548)
- WeMod.exe (PID: 1612)
Process checks computer location settings
- WeMod.exe (PID: 2692)
- WeMod.exe (PID: 1612)
Reads CPU info
- WeMod.exe (PID: 1612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2059:09:10 14:56:13+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 105472 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ba0e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.0.0 |
| ProductVersionNumber: | 8.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | WeMod Setup |
| CompanyName: | WeMod LLC |
| FileDescription: | WeMod Setup |
| FileVersion: | 8.0.0.0 |
| InternalName: | WeMod-Setup.exe |
| LegalCopyright: | Copyright © WeMod LLC 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | WeMod-Setup.exe |
| ProductName: | WeMod |
| ProductVersion: | 8.0.0.0 |
| AssemblyVersion: | 8.0.0.0 |
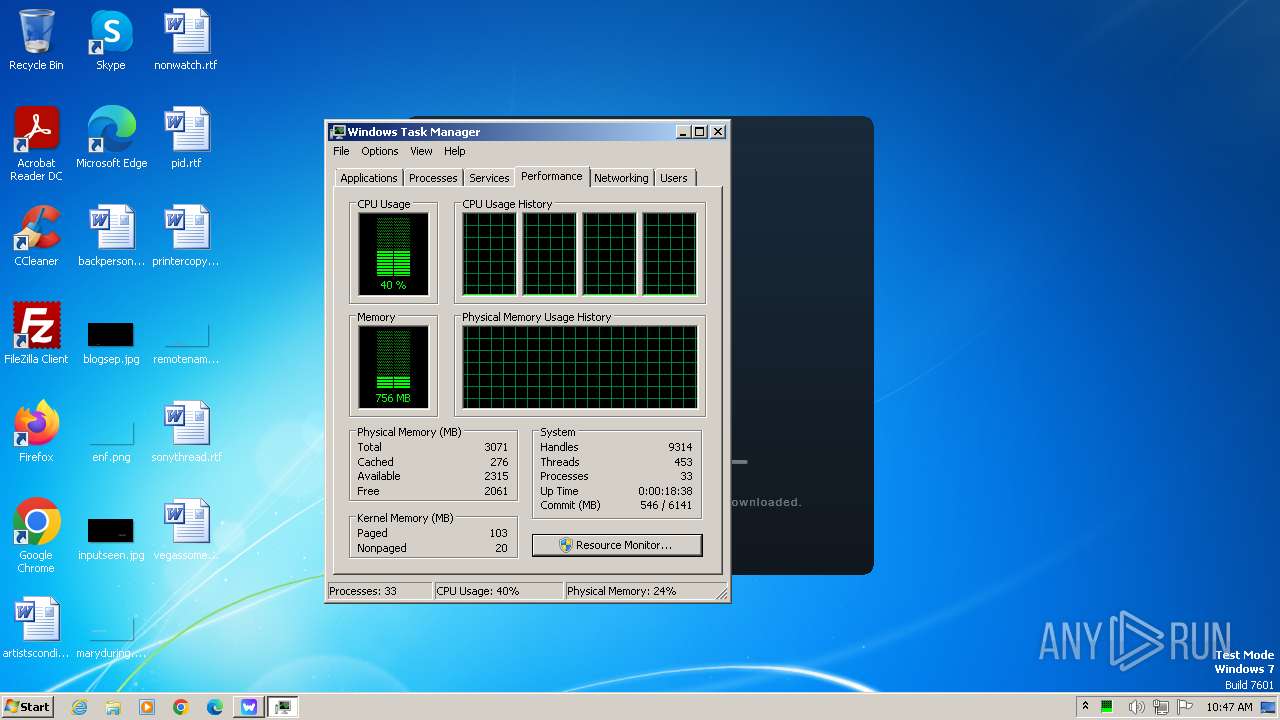
Total processes
55
Monitored processes
17
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
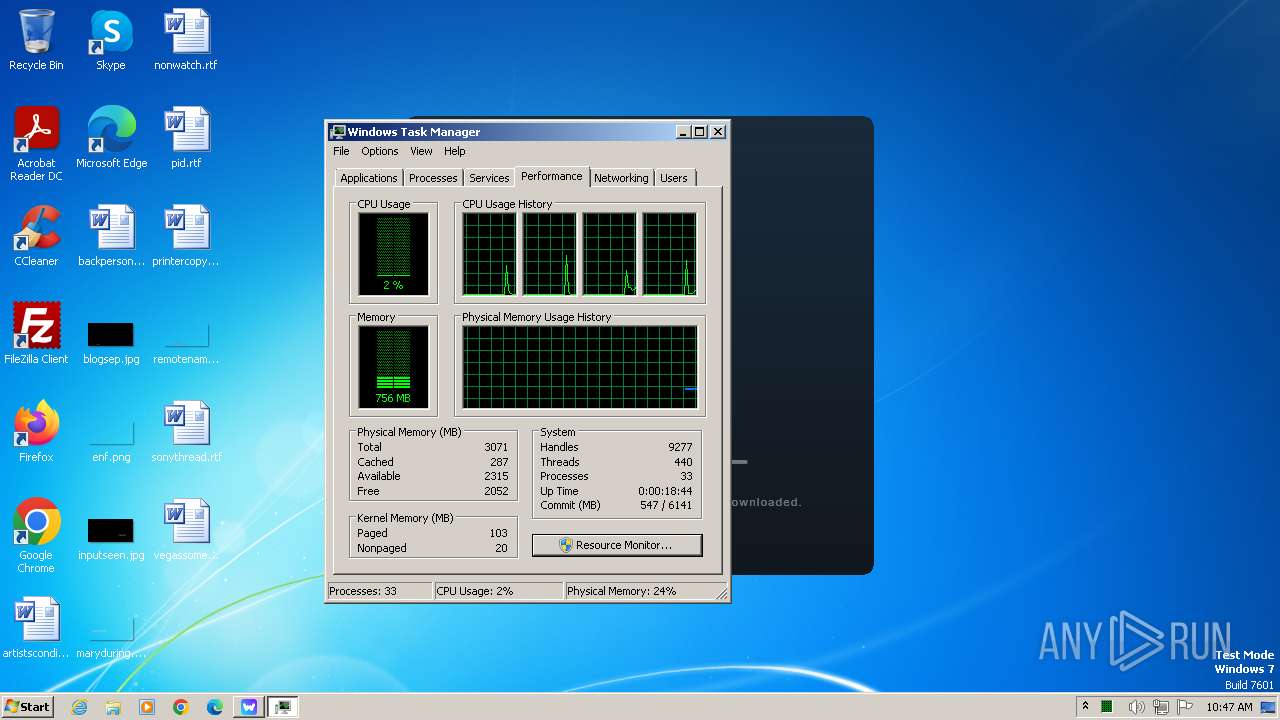
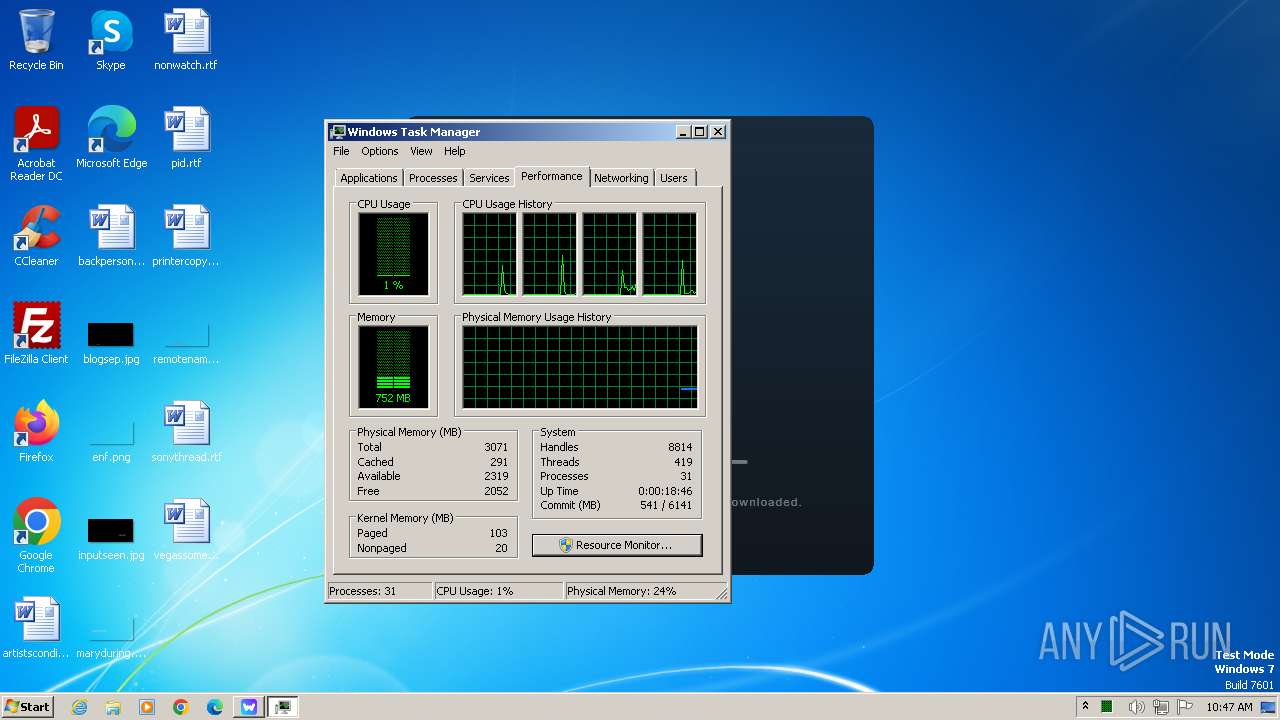
| 660 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\WeMod" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1272 --field-trial-handle=1036,i,3792157113076425664,11000871268014293886,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe | — | WeMod.exe | |||||||||||
User: admin Company: WeMod Integrity Level: LOW Description: WeMod - Cheats and Mods Version: 8.19.0 Modules
| |||||||||||||||
| 936 | "C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --force-ui-direction=ltr --user-data-dir="C:\Users\admin\AppData\Roaming\WeMod" --mojo-platform-channel-handle=1296 --field-trial-handle=1036,i,3792157113076425664,11000871268014293886,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe | WeMod.exe | ||||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Version: 8.19.0 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | "C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe" --squirrel-install 8.19.0 | C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe | — | Update.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Exit code: 0 Version: 8.19.0 Modules
| |||||||||||||||
| 1588 | "C:\Users\admin\AppData\Local\Temp\WeMod-Setup-638511040038411250.exe" --silent | C:\Users\admin\AppData\Local\Temp\WeMod-Setup-638511040038411250.exe | WeMod-Setup.exe | ||||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Ultimate Gaming Companion Exit code: 0 Version: 8.19.0 Modules
| |||||||||||||||
| 1612 | "C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe" wemod://?_inst=JaMhq9Tcejl5N1lk | C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe | — | Update.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Version: 8.19.0 Modules
| |||||||||||||||
| 1704 | "C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe" --install . --silent | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | WeMod-Setup-638511040038411250.exe | ||||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 2.0.1.23 Modules
| |||||||||||||||
| 1836 | "C:\Users\admin\AppData\Local\WeMod\app-8.19.0\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\WeMod\app-8.19.0\squirrel.exe | — | Update.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1848 | "C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\WeMod" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=992 --field-trial-handle=1036,i,3792157113076425664,11000871268014293886,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\WeMod\app-8.19.0\WeMod.exe | — | WeMod.exe | |||||||||||
User: admin Company: WeMod Integrity Level: LOW Description: WeMod - Cheats and Mods Exit code: 0 Version: 8.19.0 Modules
| |||||||||||||||
Total events
40 136
Read events
39 991
Write events
137
Delete events
8
Modification events
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3968) WeMod-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
22
Suspicious files
139
Text files
39
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3E0958535A59F099690DF7CB799DE040 | SHA256:85BE18D528D2D708DCB29DCA76E12ABF4D13ACA64661ADA1F1E09B4ED9BB228D | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\Inter-ExtraLight-7d759358c1[1].woff | binary | |
MD5:7D759358C1372FA6ACAE4CB22F93DEFA | SHA256:07F5B5F734793F48613D8DA246F4DB2B564BFA7149F62526326BE9CB8BB94841 | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:70732AF1880AAED47FD3BE29D9D084BD | SHA256:55B5327FFA4B60F59B03E1DCEB432E17703FEC0291D39A03D47A85D0F1357D4E | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Inter-Thin-0f080c40c6[1].woff | binary | |
MD5:0F080C40C639962E1CAD093AA58192DC | SHA256:E9DA5A64A6A8EB87A2C6D475327F072B5CA25731DF07119F576C10C50AA9554D | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\DOMStore\SBNY5O29\api.wemod[1].xml | text | |
MD5:C1DDEA3EF6BBEF3E7060A1A9AD89E4C5 | SHA256:B71E4D17274636B97179BA2D97C742735B6510EB54F22893D3A2DAFF2CEB28DB | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Inter-SemiBold-1d5bb5c64d[1].woff | binary | |
MD5:1D5BB5C64DC15405BDB04145DAB7B436 | SHA256:807D56B95FCC04CD1C26FCA043DDF19E300C8AE156747458BD025A2B21CF54B4 | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Inter-Regular-14d1275c67[1].woff | binary | |
MD5:14D1275C67676CC5D911232D0C890D97 | SHA256:3710E2CE073EC0EB39274DECC63768B52091A27E35F5C28D6ABB7A5FCEF0B7FC | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\Local\Temp\WeMod-Setup-638511040038411250.exe | — | |
MD5:— | SHA256:— | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Inter-Bold-45e58f4054[1].woff | binary | |
MD5:45E58F4054A3AD886E4582E1D43056FE | SHA256:57027B1C72507C75CF9FC21DCBBBD4366F01901B598764CB8703DFA4988A60CA | |||
| 3968 | WeMod-Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Inter-Medium-5ce3e4db96[1].woff | binary | |
MD5:5CE3E4DB9634913232403F166B2447DE | SHA256:68D52E74E8171DDB2C94CA60A2596DC8A46407320449881FD09369DBC317624C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
48
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | WeMod-Setup.exe | GET | 304 | 23.204.115.113:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cc1fd6eba5c377fe | unknown | — | — | unknown |
3968 | WeMod-Setup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | — | — | unknown |
3968 | WeMod-Setup.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
3968 | WeMod-Setup.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | — | — | unknown |
3968 | WeMod-Setup.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAFWoeiRoD5nEA9wbC%2FqWOc%3D | unknown | — | — | unknown |
3968 | WeMod-Setup.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | unknown | — | — | unknown |
3968 | WeMod-Setup.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | unknown | — | — | unknown |
3968 | WeMod-Setup.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEGO2IkqWfxOGk0NWE9vukyQ%3D | unknown | — | — | unknown |
1088 | svchost.exe | GET | 304 | 23.204.115.113:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?83bdd76cfa43776c | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3968 | WeMod-Setup.exe | 104.22.43.75:443 | api.wemod.com | CLOUDFLARENET | — | unknown |
3968 | WeMod-Setup.exe | 23.204.115.113:80 | ctldl.windowsupdate.com | AKAMAI-AS | US | unknown |
3968 | WeMod-Setup.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3968 | WeMod-Setup.exe | 52.26.41.155:443 | api2.amplitude.com | AMAZON-02 | US | unknown |
3968 | WeMod-Setup.exe | 142.250.185.174:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
3968 | WeMod-Setup.exe | 142.250.181.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3968 | WeMod-Setup.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.wemod.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
api2.amplitude.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
storage-cdn.wemod.com |
| unknown |
redirector.gvt1.com |
| whitelisted |
r5---sn-4g5lzned.gvt1.com |
| whitelisted |