| File name: | 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil |
| Full analysis: | https://app.any.run/tasks/780d9f2f-f63a-4f32-ae5a-a2fdbd3d5b00 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2025, 07:52:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | ACB4175A7C6B9F9FDF4D40286FBB53E9 |
| SHA1: | 6E8CA3533B500175E2D9A1D24A1BE5DD1E353E41 |
| SHA256: | 0ED71DCADD29D868354915427CAF6AB3DEA0B8283CBC9FF3E49D0DC39FF782D8 |
| SSDEEP: | 98304:rCUYs0h/lqUB9IrVVGzLYhER6D8XGAfAn8gr18Tlc2nbDC7swWun/TW1az1ke0r9:eiswYm0F |
MALICIOUS
Modifies exclusions in Windows Defender
- rvlkl_setup64.exe (PID: 6136)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe (PID: 3812)
- rvlkl_setup64.exe (PID: 6136)
Reads security settings of Internet Explorer
- 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe (PID: 3812)
- rvlkl_setup64.exe (PID: 6136)
- rvlkl.exe (PID: 1356)
Detected use of alternative data streams (AltDS)
- rvlkl_setup64.exe (PID: 6136)
Reads the date of Windows installation
- rvlkl_setup64.exe (PID: 6136)
INFO
Reads the computer name
- rvlkl_setup64.exe (PID: 6136)
- 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe (PID: 3812)
- rvlkl.exe (PID: 1356)
- identity_helper.exe (PID: 6332)
Create files in a temporary directory
- 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe (PID: 3812)
Checks supported languages
- 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe (PID: 3812)
- rvlkl_setup64.exe (PID: 6136)
- rvlkl.exe (PID: 1356)
- identity_helper.exe (PID: 6332)
Process checks computer location settings
- 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe (PID: 3812)
- rvlkl_setup64.exe (PID: 6136)
Creates files in the program directory
- rvlkl_setup64.exe (PID: 6136)
The process uses the downloaded file
- 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe (PID: 3812)
- rvlkl_setup64.exe (PID: 6136)
The sample compiled with english language support
- rvlkl_setup64.exe (PID: 6136)
- msedge.exe (PID: 5200)
Reads the machine GUID from the registry
- rvlkl_setup64.exe (PID: 6136)
- rvlkl.exe (PID: 1356)
Manual execution by a user
- msedge.exe (PID: 5028)
Executable content was dropped or overwritten
- msedge.exe (PID: 5200)
Application launched itself
- msedge.exe (PID: 5628)
- msedge.exe (PID: 5028)
Reads Environment values
- identity_helper.exe (PID: 6332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:10:27 09:40:48+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 105984 |
| InitializedDataSize: | 8021504 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf97c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
175
Monitored processes
53
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Users\admin\Desktop\2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe" | C:\Users\admin\Desktop\2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
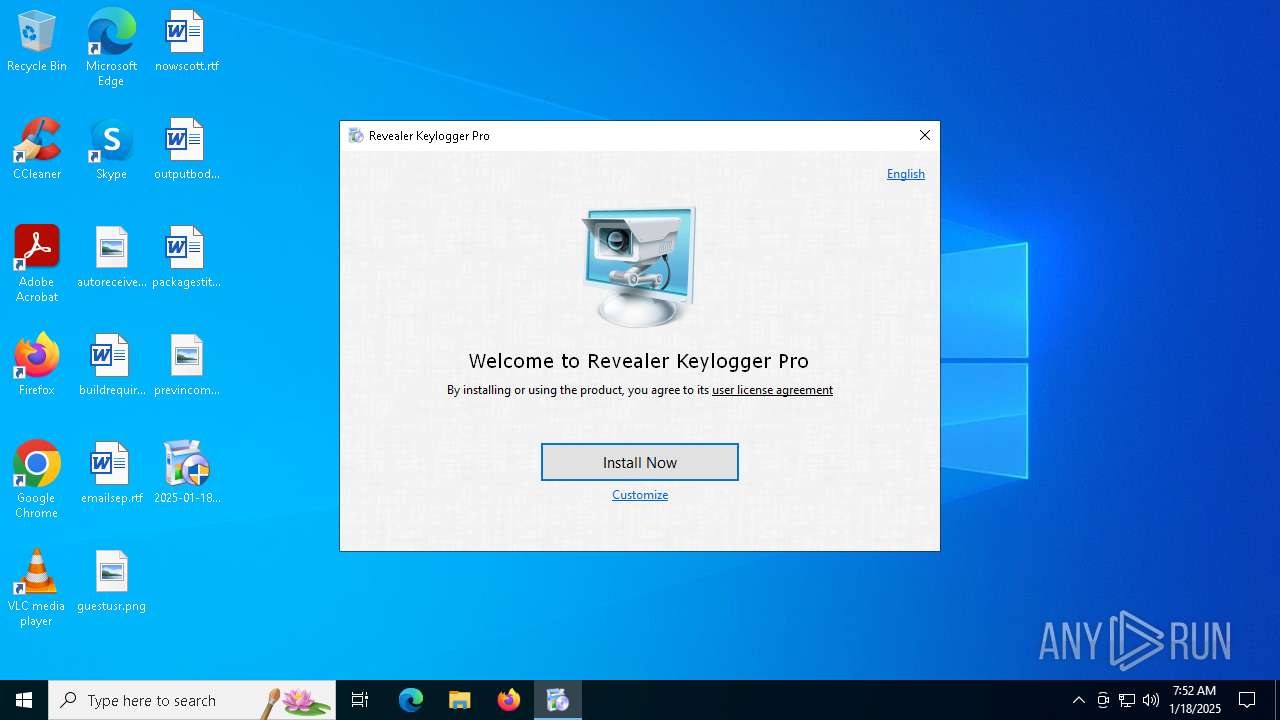
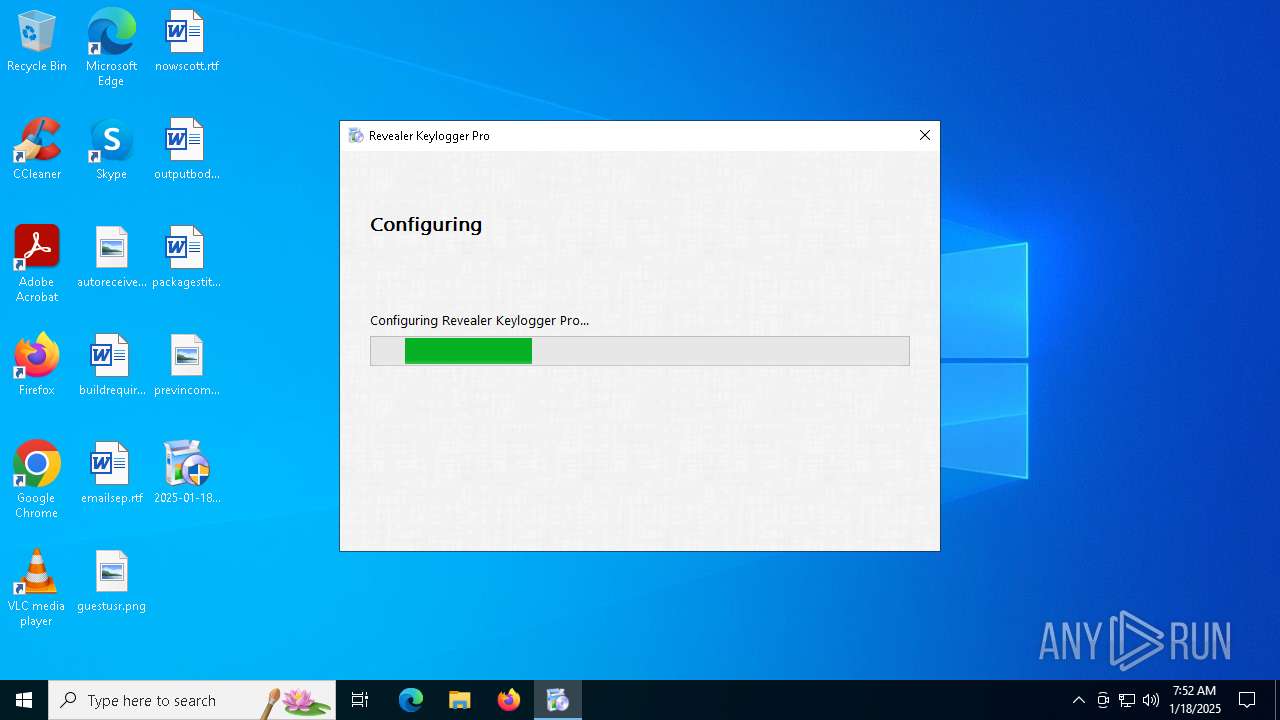
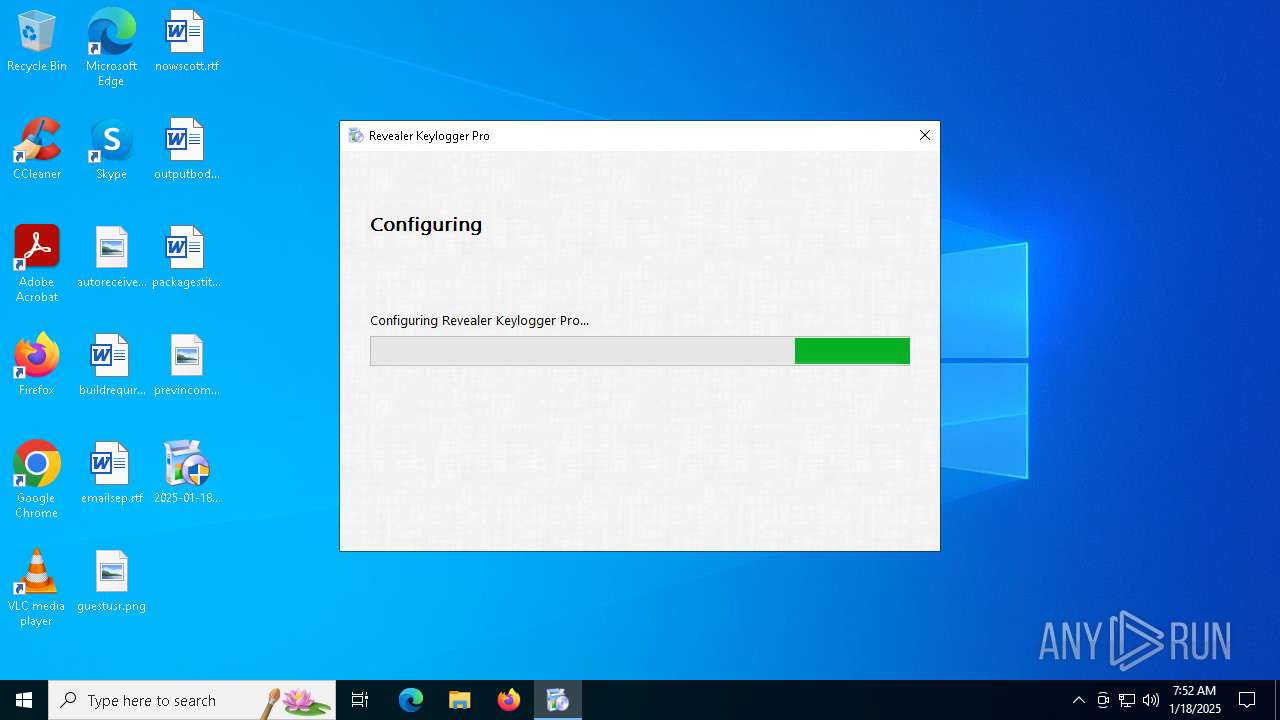
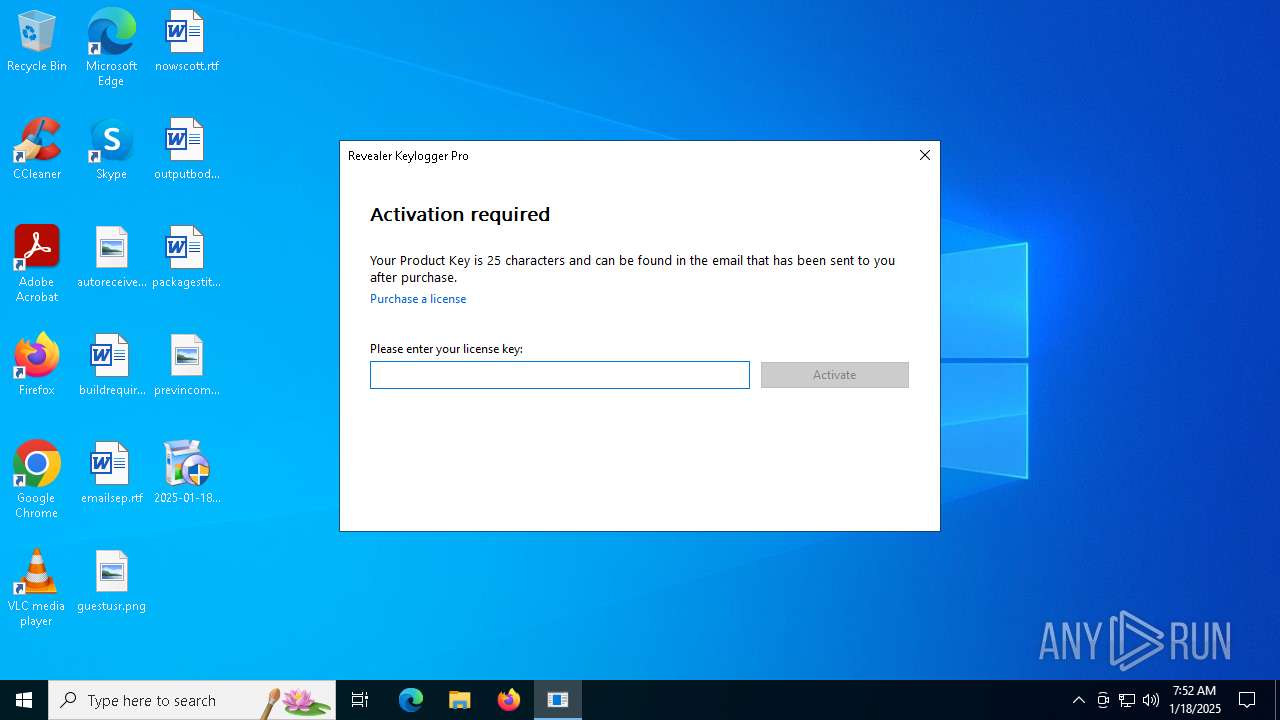
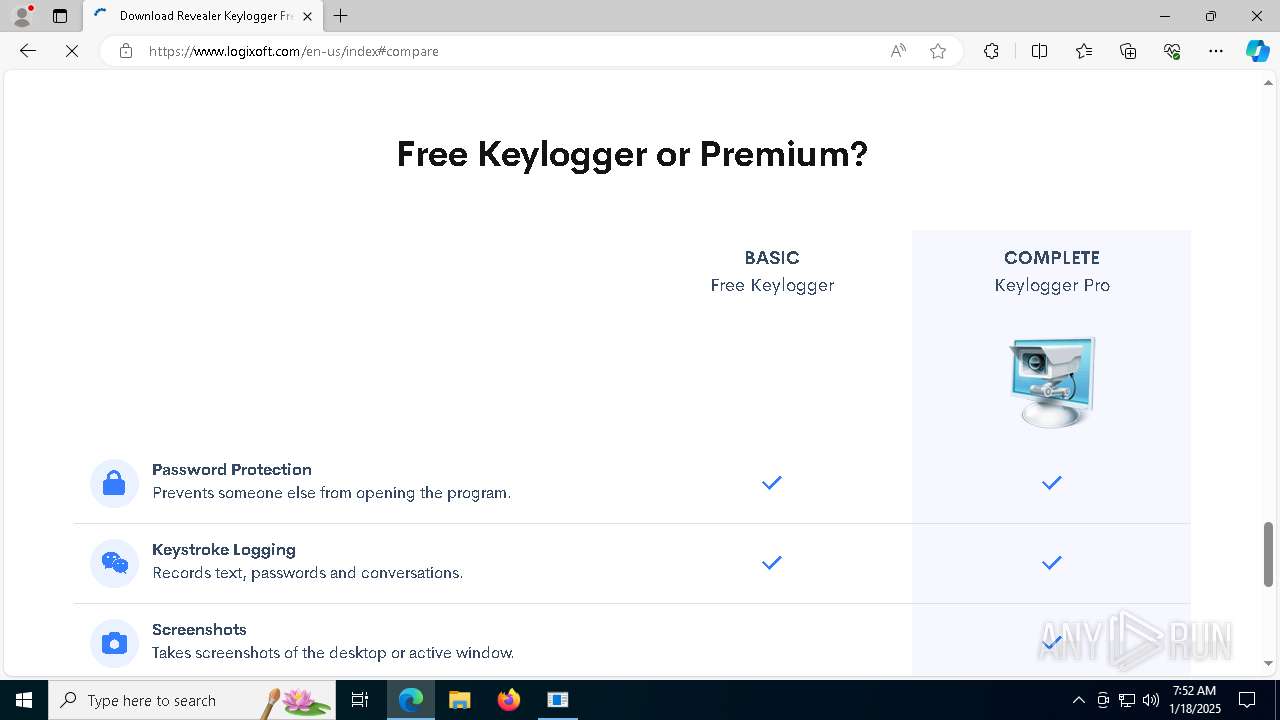
| 1356 | "C:\WINDOWS\system32\rvlkl.exe" -install -lang 9 | C:\Windows\System32\rvlkl.exe | — | rvlkl_setup64.exe | |||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Pro Version: 3.0.2.0 Modules
| |||||||||||||||
| 1544 | "C:\WINDOWS\system32\rvlkl.exe" -install -lang 9 | C:\Windows\System32\rvlkl.exe | — | rvlkl_setup64.exe | |||||||||||
User: admin Company: Logixoft Integrity Level: HIGH Description: Revealer Pro Exit code: 3221226540 Version: 3.0.2.0 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5676 --field-trial-handle=2352,i,17253656414649306909,5963544174233148142,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4444 --field-trial-handle=2352,i,17253656414649306909,5963544174233148142,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2412 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2348 --field-trial-handle=2352,i,17253656414649306909,5963544174233148142,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2996 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2f4,0x2f8,0x2fc,0x2ec,0x304,0x7ff821225fd8,0x7ff821225fe4,0x7ff821225ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3812 | "C:\Users\admin\Desktop\2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe" | C:\Users\admin\Desktop\2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x1f0,0x2b0,0x7ff821225fd8,0x7ff821225fe4,0x7ff821225ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2196 --field-trial-handle=2352,i,17253656414649306909,5963544174233148142,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
5 966
Read events
5 930
Write events
34
Delete events
2
Modification events
| (PID) Process: | (6136) rvlkl_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | rvlkl |
Value: | |||
| (PID) Process: | (6136) rvlkl_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | rkfree |
Value: | |||
| (PID) Process: | (6136) rvlkl_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths |
| Operation: | write | Name: | C:\WINDOWS\system32\rvlkl.dll |
Value: 0 | |||
| (PID) Process: | (6136) rvlkl_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths |
| Operation: | write | Name: | C:\WINDOWS\system32\rvlkl.exe |
Value: 0 | |||
| (PID) Process: | (6136) rvlkl_setup64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Processes |
| Operation: | write | Name: | C:\WINDOWS\system32\rvlkl.exe |
Value: 0 | |||
| (PID) Process: | (1356) rvlkl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1356) rvlkl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1356) rvlkl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
17
Suspicious files
373
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF138eb6.TMP | — | |
MD5:— | SHA256:— | |||
| 5028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF138eb6.TMP | — | |
MD5:— | SHA256:— | |||
| 5028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3812 | 2025-01-18_acb4175a7c6b9f9fdf4d40286fbb53e9_avoslocker_luca-stealer_revil.exe | C:\Users\admin\AppData\Local\Temp\rvlkl_setup\rvlkl_setup64.exe | executable | |
MD5:B5AB4500640AA522ADFD8AF49ABC8E7E | SHA256:CAC70BC51DED8DB36B1BFED97604E17339A9AF68824103A9B6A1E509413CE7D5 | |||
| 5628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:C7E2197BAE099B13BBB3ADEB1433487D | SHA256:3460EEAF45D581DD43A6E4E17AF8102DDAFF5AEAA88B10099527CF85211629E9 | |||
| 5628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:1E9E15EF6E531C4557100F20C9C76F01 | SHA256:46CB063CC268B69B172660F166C4394D5B4EDD802388B3EC16766DEBDB9F86C3 | |||
| 5028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF138ee5.TMP | — | |
MD5:— | SHA256:— | |||
| 5028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6136 | rvlkl_setup64.exe | C:\ProgramData\rvlkl\log.css | text | |
MD5:A35BD6E012B609D94A076699C5372657 | SHA256:6EF8CFC8307115A02E5B60AF549867DC79BDF3018EB95A9417E8E6C3632EABB5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
176
TCP/UDP connections
107
DNS requests
82
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4536 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4536 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
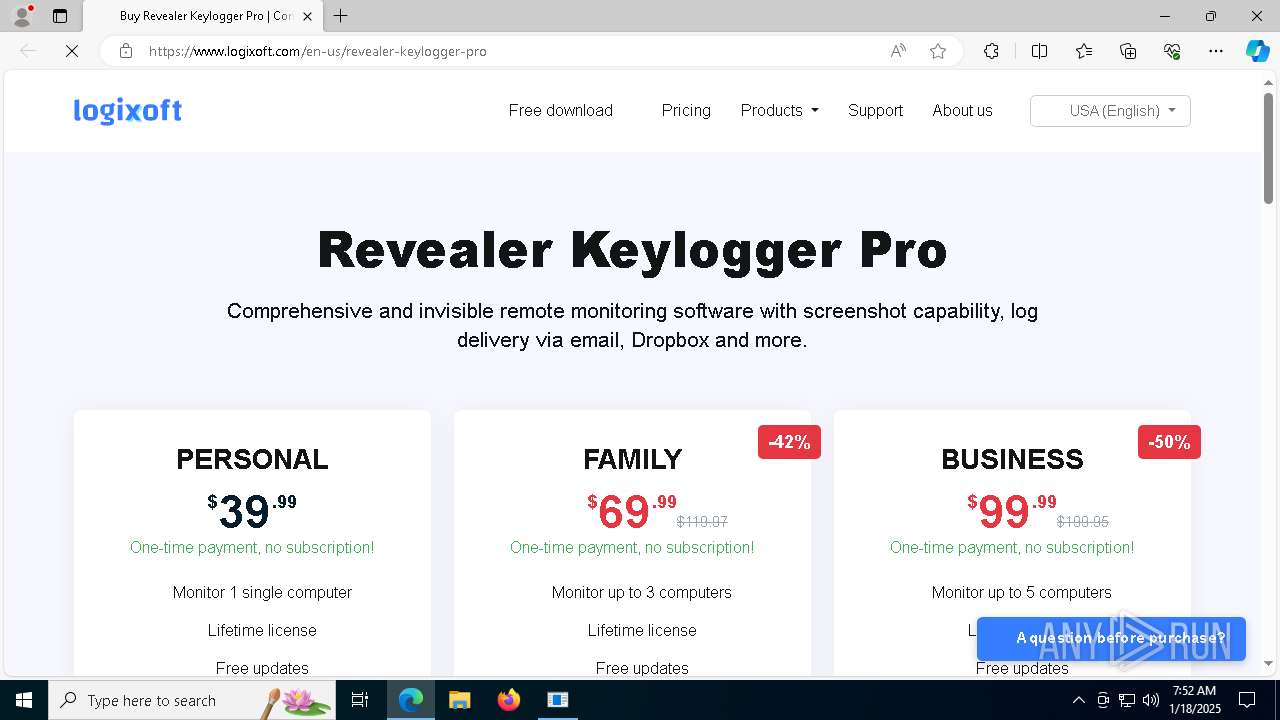
— | — | GET | 302 | 87.98.255.2:443 | https://www.logixoft.com/buyredirect.php?lang=en-us¤cy=USD | unknown | — | — | unknown |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
— | — | GET | 200 | 216.58.206.40:443 | https://www.googletagmanager.com/gtag/js?id=G-MNQH0H87JX | unknown | binary | 302 Kb | unknown |
— | — | GET | 200 | 87.98.255.2:443 | https://www.logixoft.com/css/defaultv5.min.css | unknown | text | 24.1 Kb | unknown |
— | — | GET | 200 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/Edge/122.0.2365.59?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=45&mngd=0&installdate=1661339457&edu=0&bphint=2&soobedate=1504771245&fg=1 | unknown | binary | 768 b | unknown |
— | — | GET | 200 | 13.107.21.239:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=122.0.2365.59&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | binary | 202 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4536 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4536 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4536 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4536 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.logixoft.com |
| malicious |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |