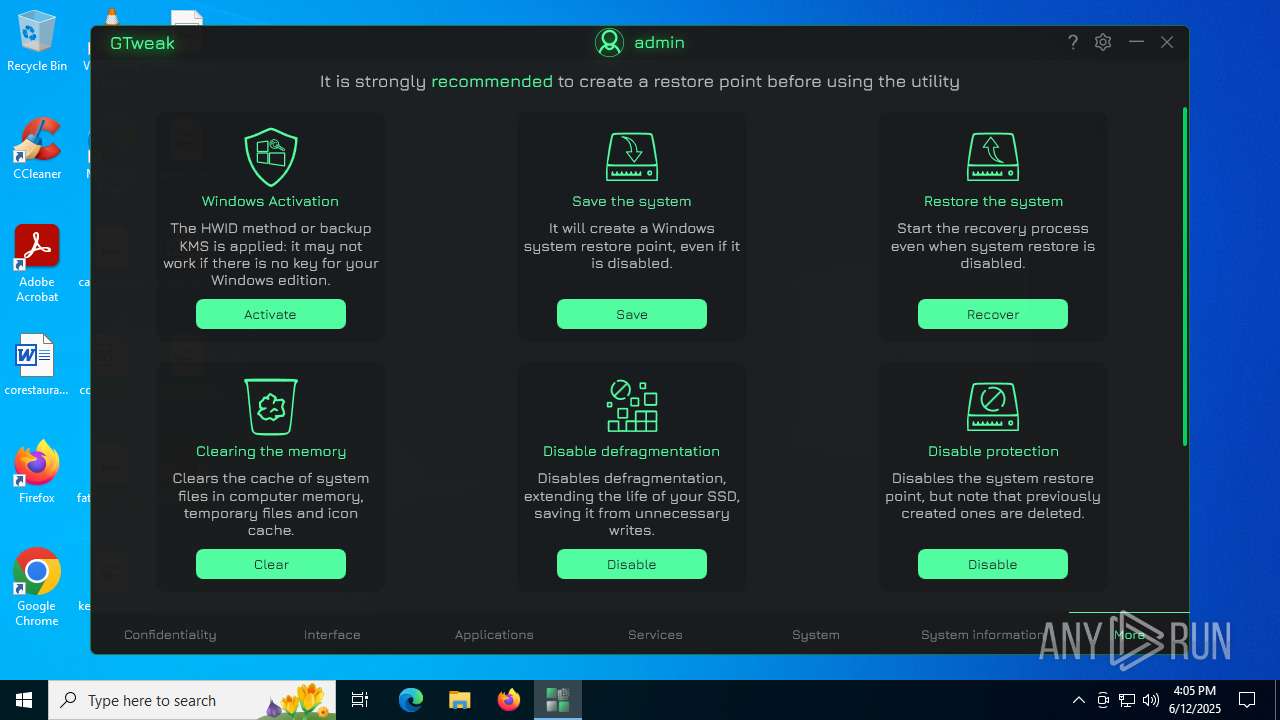
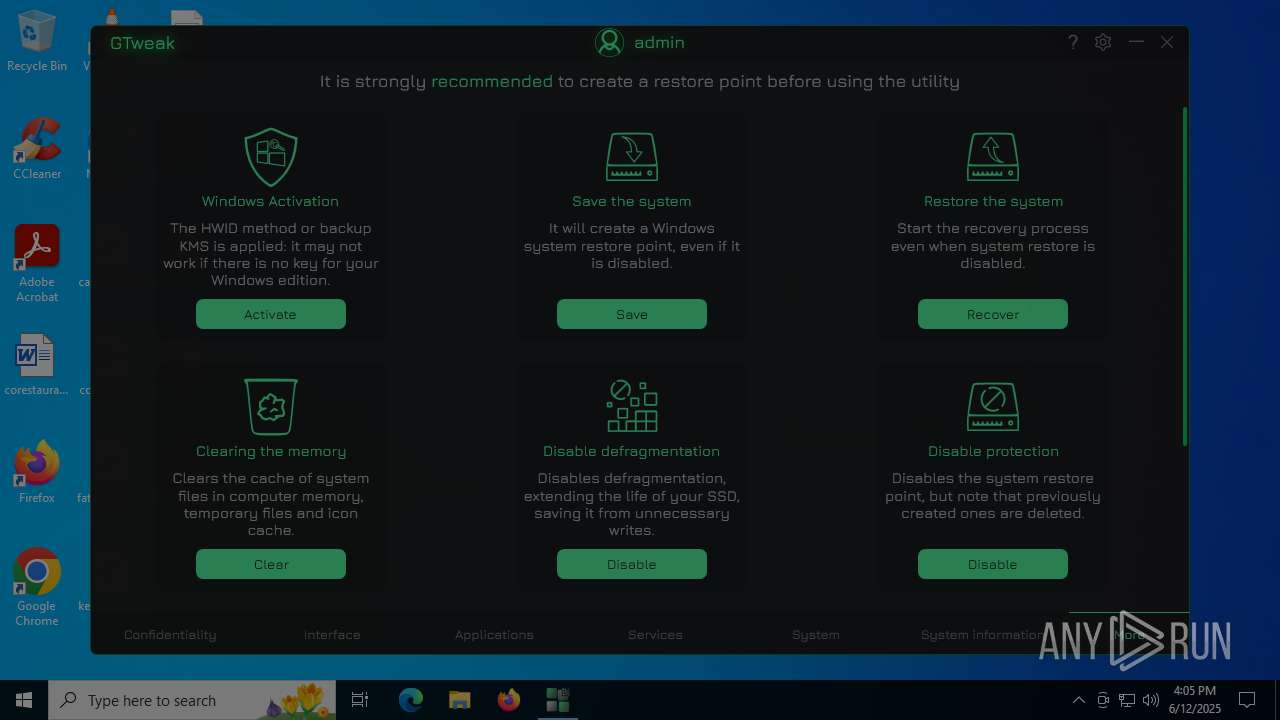
| File name: | GTweak.exe |
| Full analysis: | https://app.any.run/tasks/427417b5-7ee1-4aeb-899b-079756841193 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2025, 16:04:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 58FDBEEDD845DFC5B330D33635EB1B35 |
| SHA1: | 2E9B6220B931412671B4C9DD2795A1935429F9B4 |
| SHA256: | 0ED3031CE41FB95CC13050E8A53DD58E7A4901511ECBA134242B07C085AFCC6D |
| SSDEEP: | 98304:t9axC5aXJXIdSorCngK5AdzUqbXIdSorCngK5JQrDczVS9UVDg4q8Nt4769D6fle:Cr |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2188)
- powershell.exe (PID: 5708)
Changes powershell execution policy (Bypass)
- GTweak.exe (PID: 2076)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- GTweak.exe (PID: 2076)
Reads security settings of Internet Explorer
- GTweak.exe (PID: 2076)
Starts POWERSHELL.EXE for commands execution
- GTweak.exe (PID: 2076)
The process hide an interactive prompt from the user
- GTweak.exe (PID: 2076)
Starts application with an unusual extension
- cmd.exe (PID: 3388)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 3388)
Starts CMD.EXE for commands execution
- GTweak.exe (PID: 2076)
Windows service management via SC.EXE
- sc.exe (PID: 592)
- sc.exe (PID: 6492)
- sc.exe (PID: 4888)
- sc.exe (PID: 7076)
- sc.exe (PID: 4216)
- sc.exe (PID: 4156)
- sc.exe (PID: 2160)
- sc.exe (PID: 2140)
- sc.exe (PID: 1180)
- sc.exe (PID: 6748)
- sc.exe (PID: 4888)
- sc.exe (PID: 4920)
- sc.exe (PID: 4828)
- sc.exe (PID: 1508)
- sc.exe (PID: 1056)
- sc.exe (PID: 6260)
- sc.exe (PID: 6012)
- sc.exe (PID: 7124)
- sc.exe (PID: 4920)
- sc.exe (PID: 4380)
- sc.exe (PID: 1480)
- sc.exe (PID: 3864)
- sc.exe (PID: 6380)
- sc.exe (PID: 6756)
- sc.exe (PID: 1356)
- sc.exe (PID: 4236)
- sc.exe (PID: 1056)
- sc.exe (PID: 1488)
- sc.exe (PID: 4796)
- sc.exe (PID: 2096)
- sc.exe (PID: 5928)
- sc.exe (PID: 5352)
- sc.exe (PID: 6392)
- sc.exe (PID: 3048)
- sc.exe (PID: 7140)
- sc.exe (PID: 4052)
- sc.exe (PID: 5084)
- sc.exe (PID: 7040)
Starts SC.EXE for service management
- cmd.exe (PID: 4864)
- cmd.exe (PID: 3844)
- cmd.exe (PID: 6016)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 6292)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 5564)
- cmd.exe (PID: 6520)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 4060)
Checks for external IP
- svchost.exe (PID: 2200)
- GTweak.exe (PID: 2076)
Executes as Windows Service
- VSSVC.exe (PID: 6896)
Searches for installed software
- dllhost.exe (PID: 2380)
The process hides Powershell's copyright startup banner
- GTweak.exe (PID: 2076)
INFO
Reads the computer name
- GTweak.exe (PID: 2076)
Checks supported languages
- GTweak.exe (PID: 2076)
- chcp.com (PID: 1356)
Disables trace logs
- GTweak.exe (PID: 2076)
- netsh.exe (PID: 3964)
- netsh.exe (PID: 5896)
- netsh.exe (PID: 3924)
- netsh.exe (PID: 728)
Checks proxy server information
- GTweak.exe (PID: 2076)
Reads Environment values
- GTweak.exe (PID: 2076)
Reads the machine GUID from the registry
- GTweak.exe (PID: 2076)
Changes the display of characters in the console
- cmd.exe (PID: 3388)
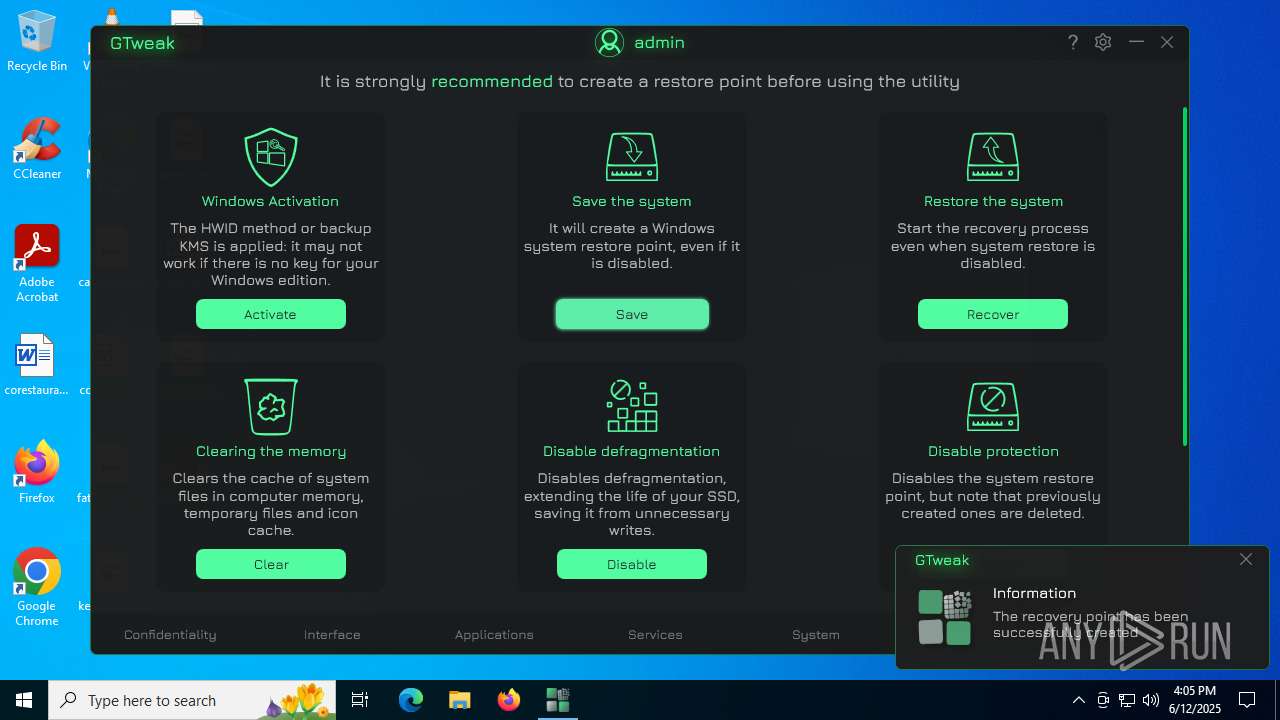
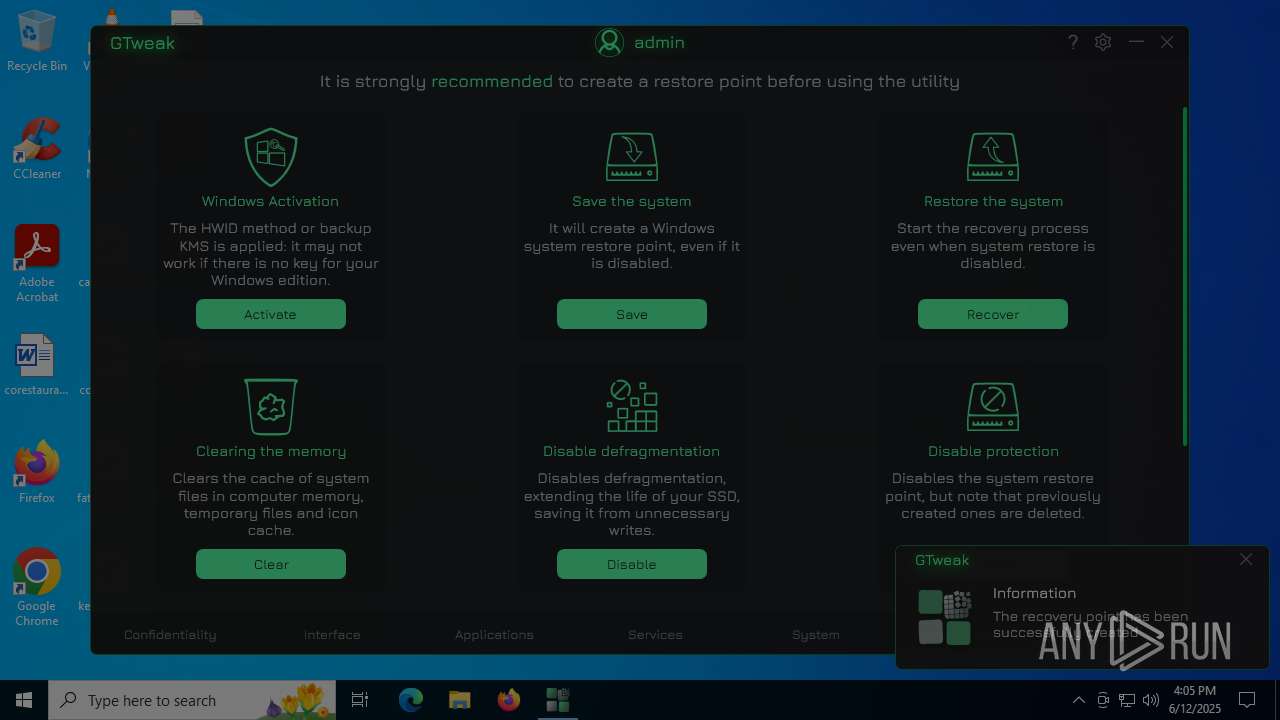
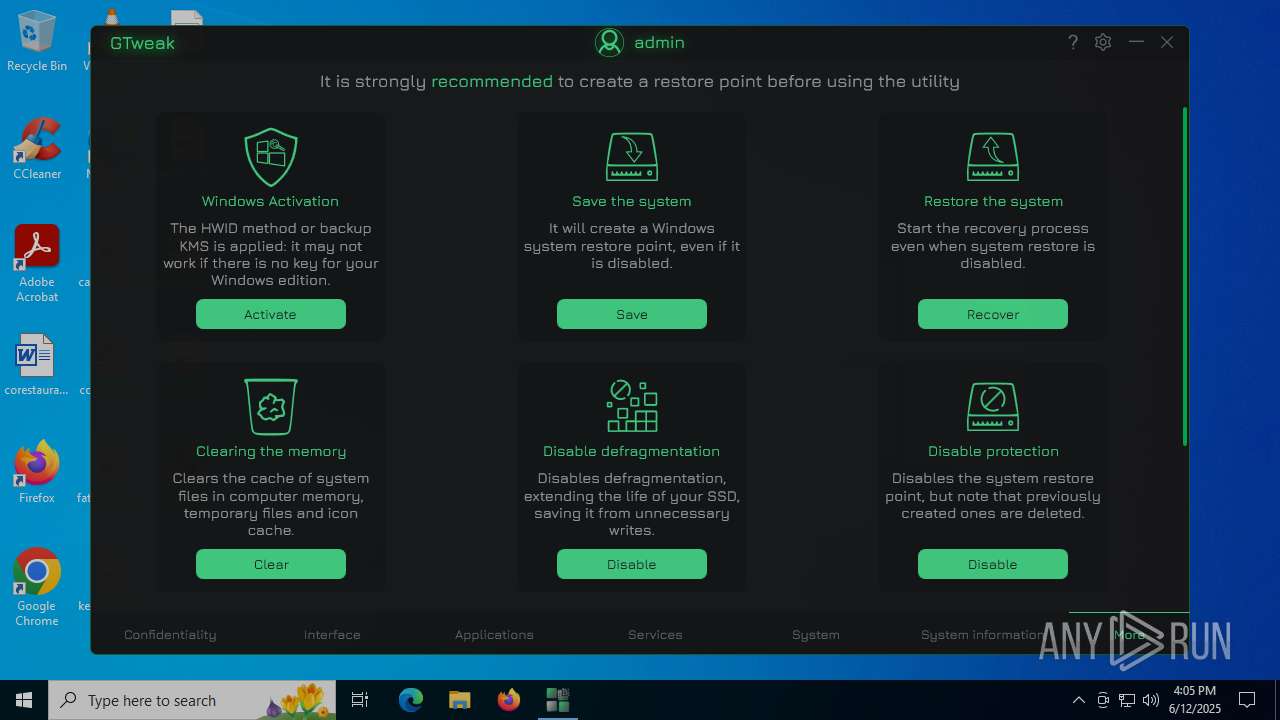
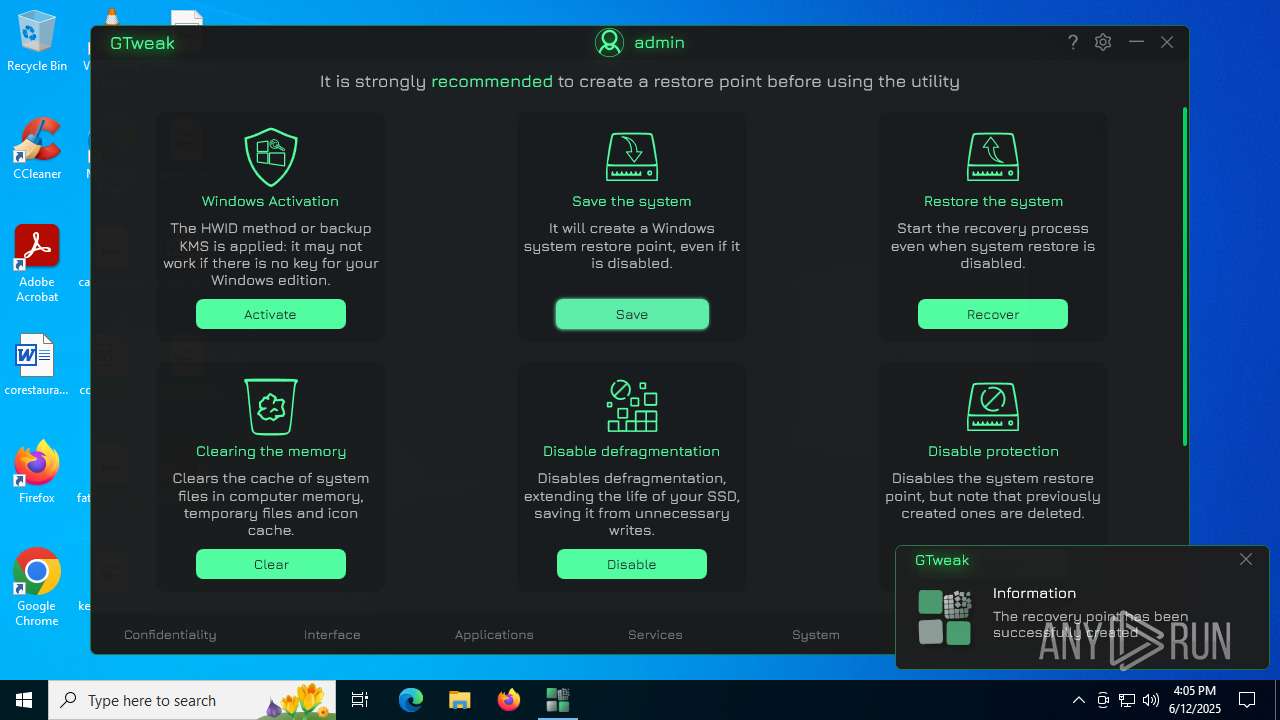
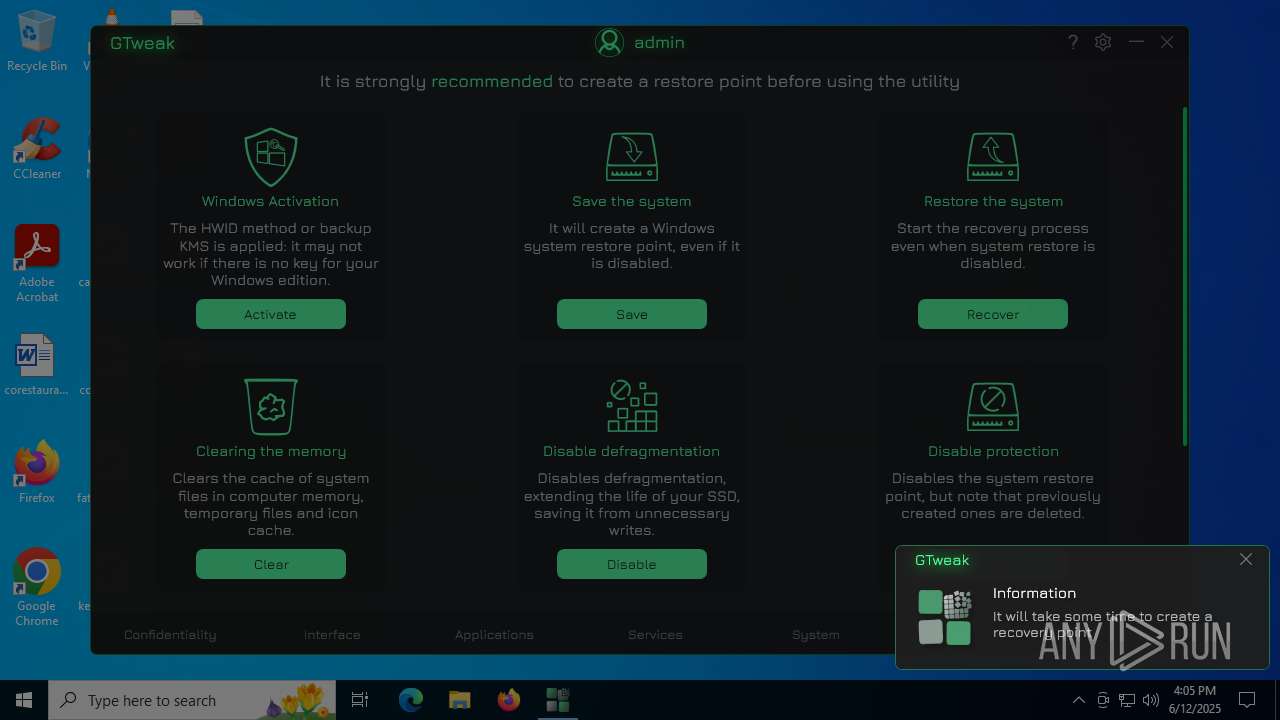
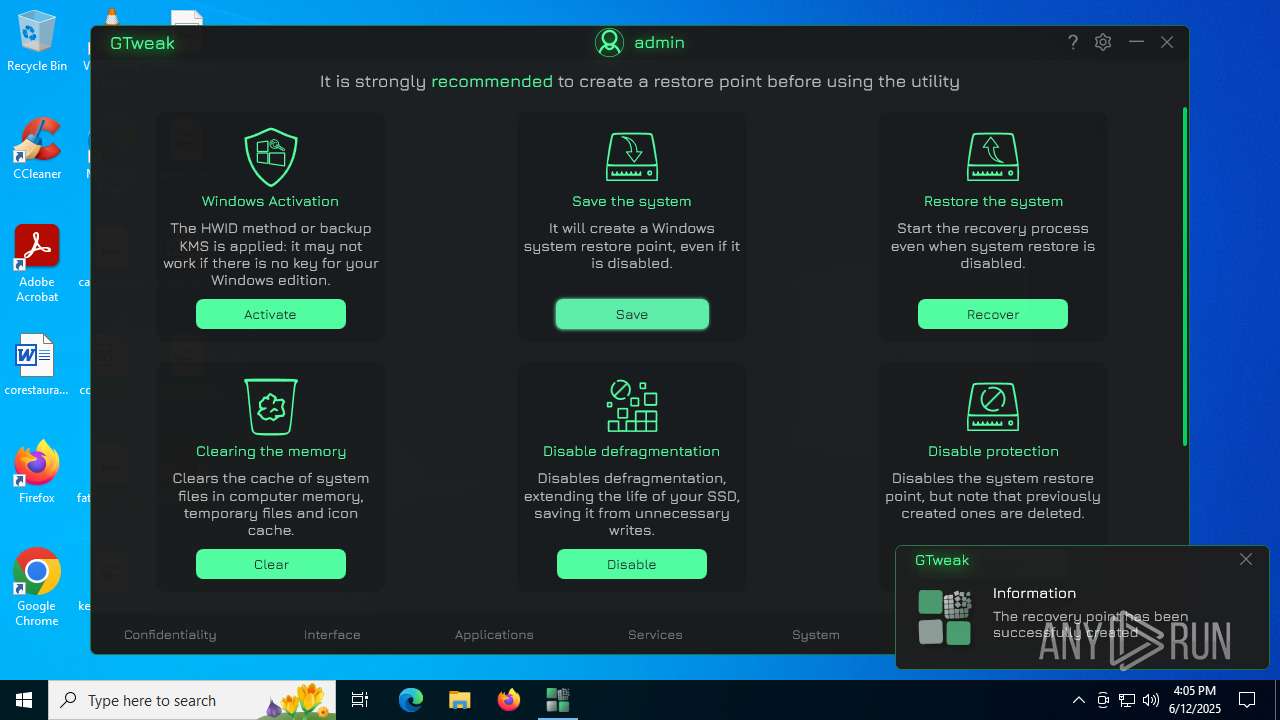
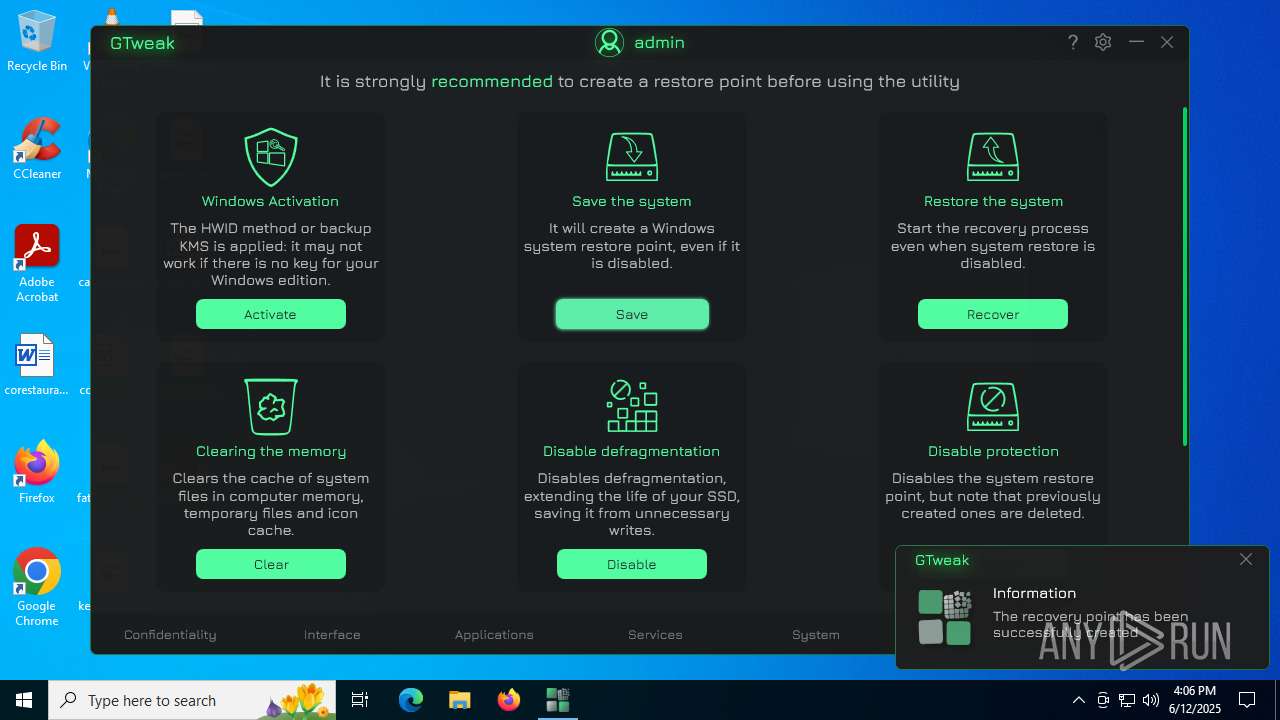
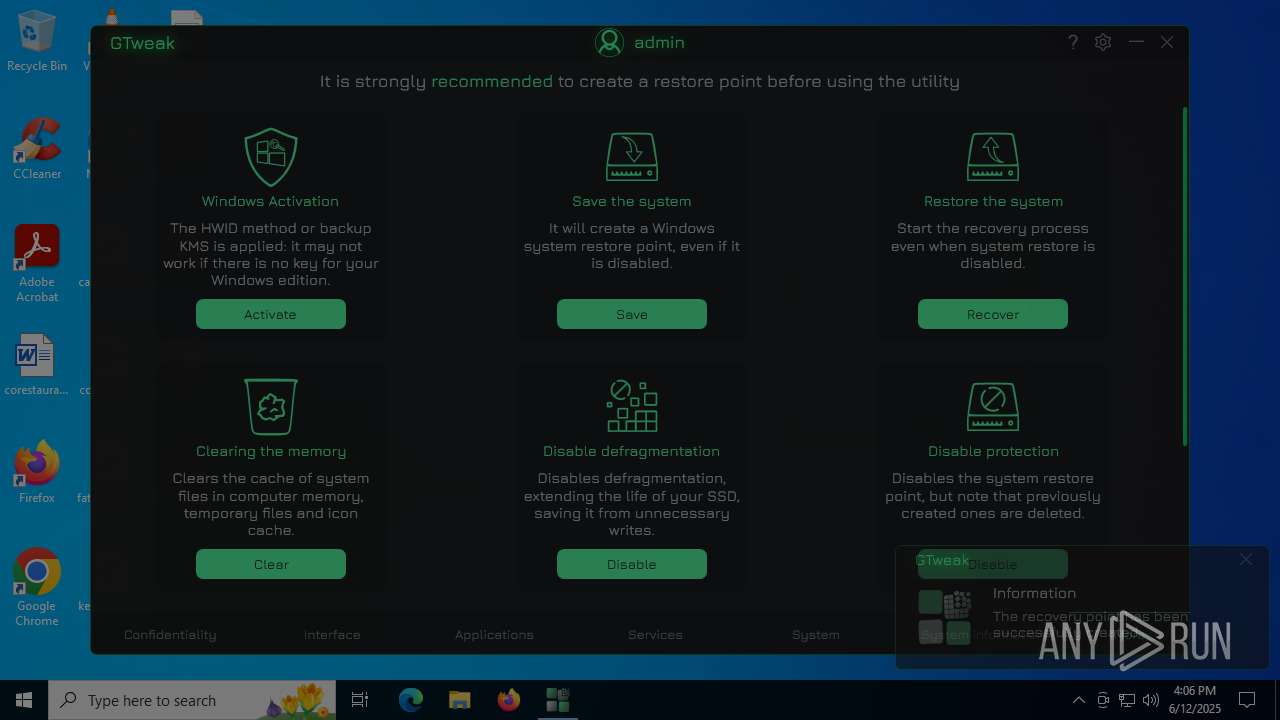
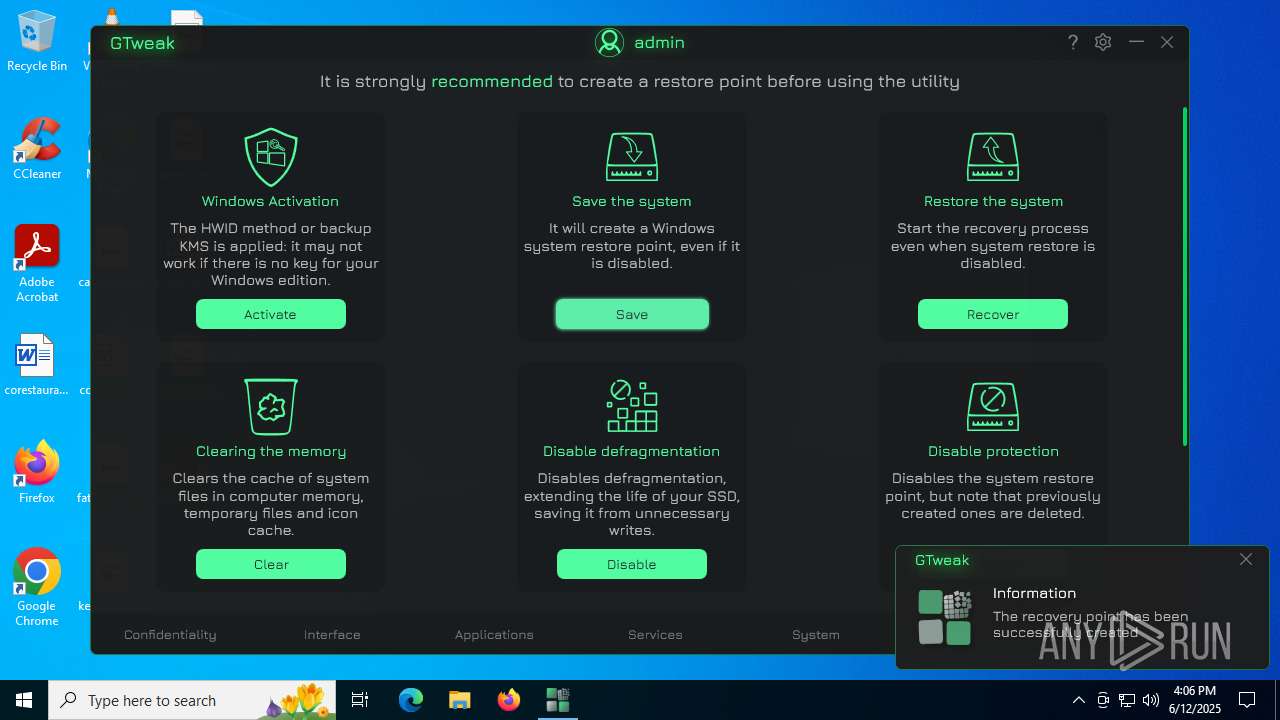
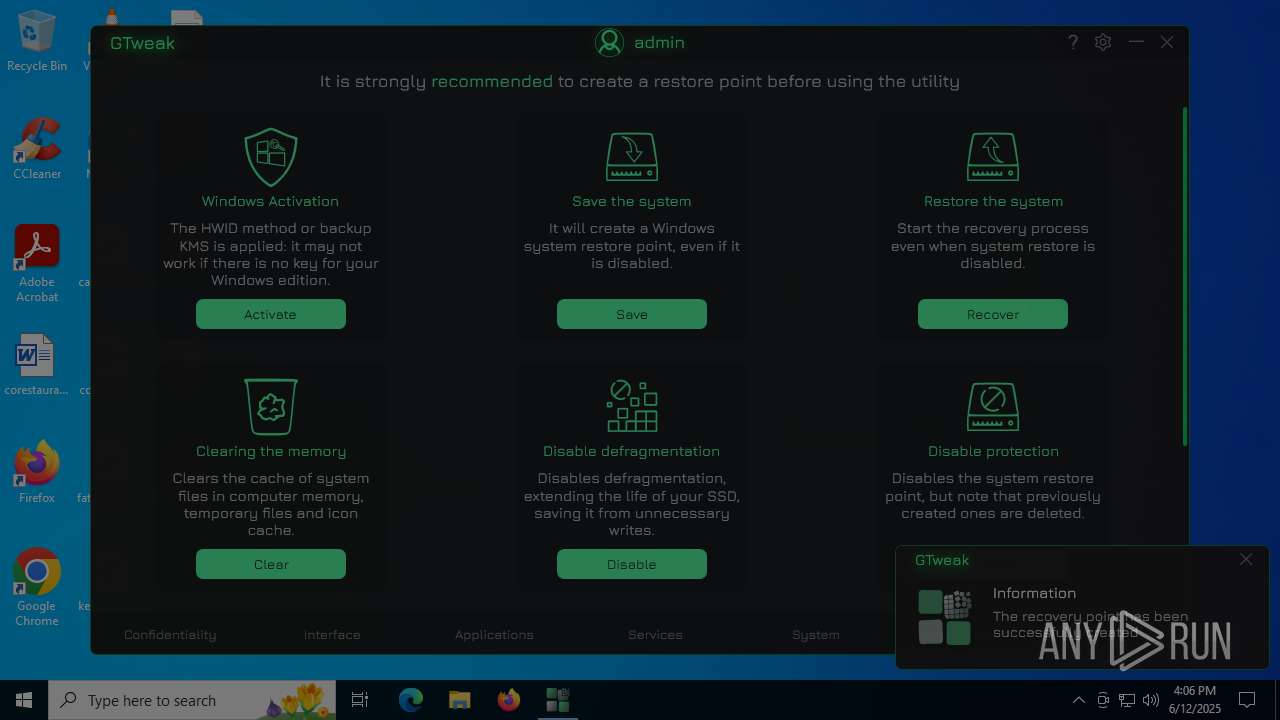
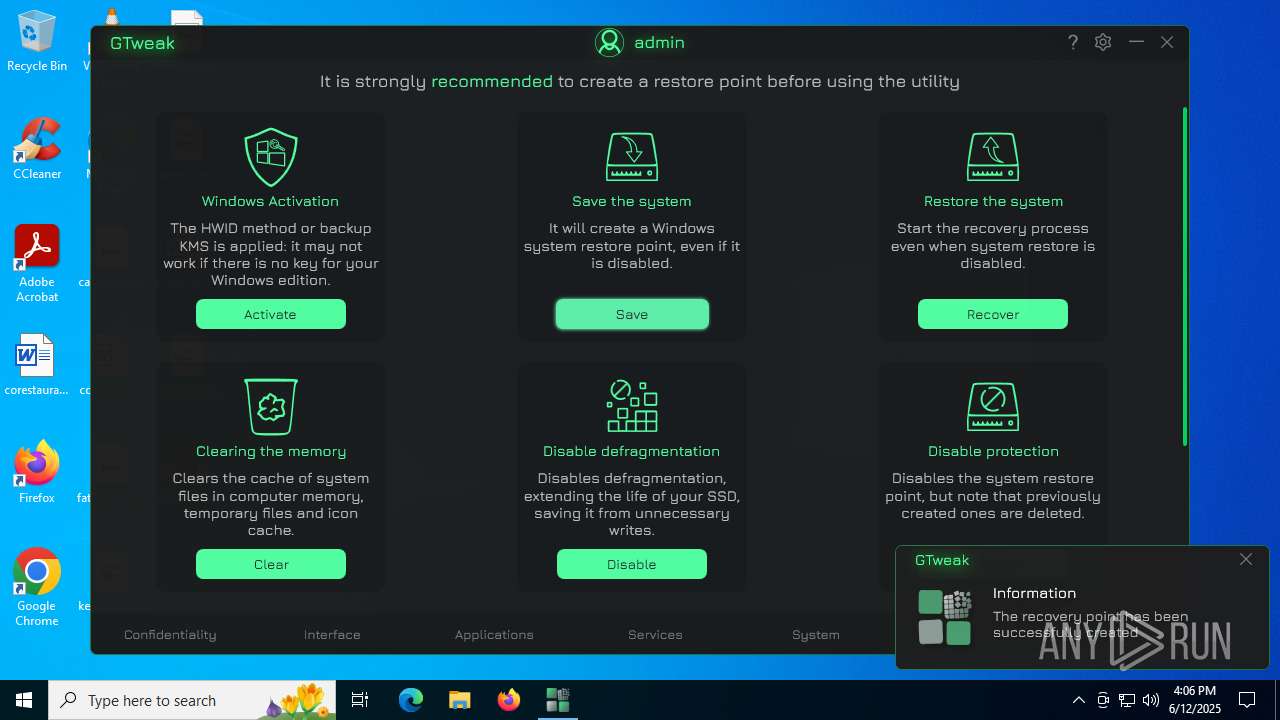
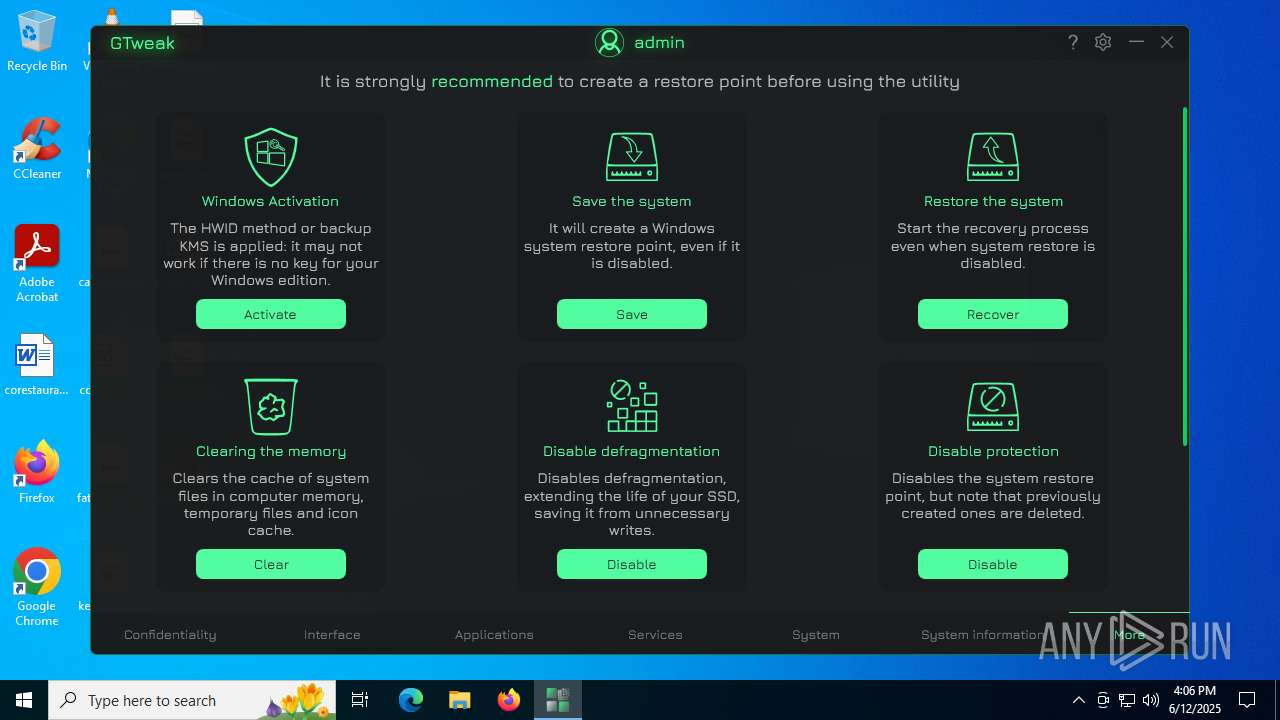
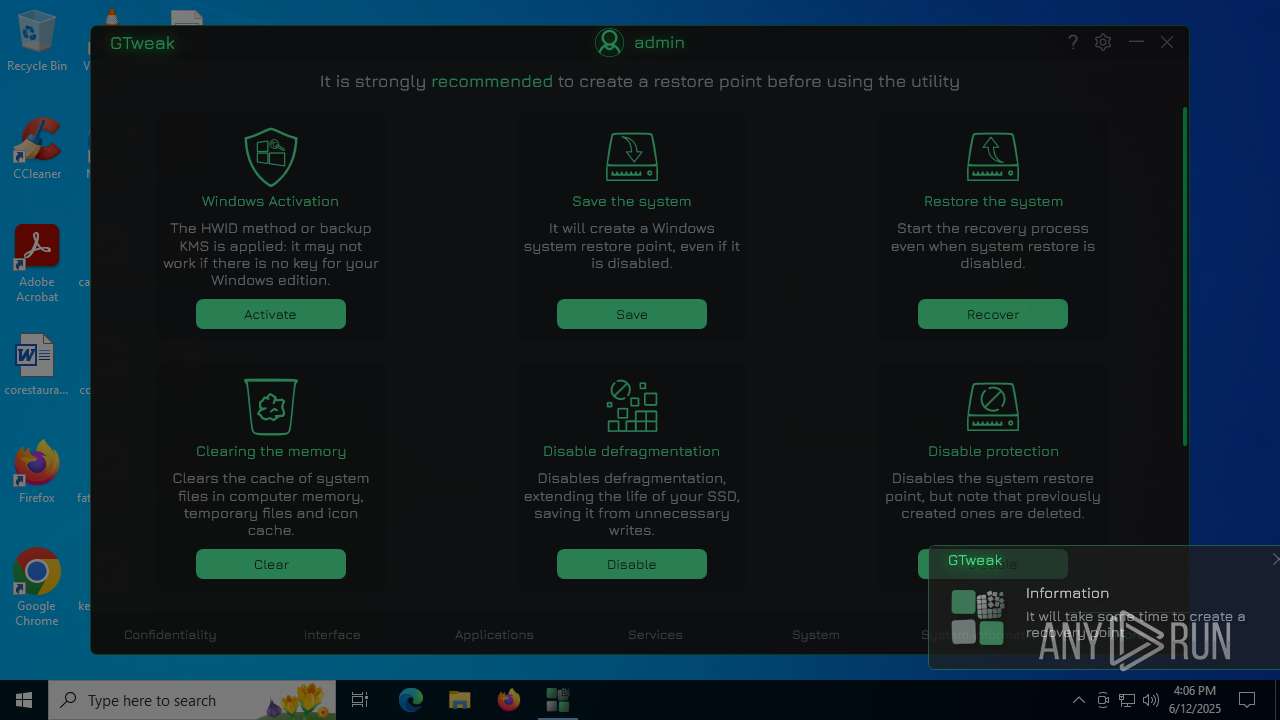
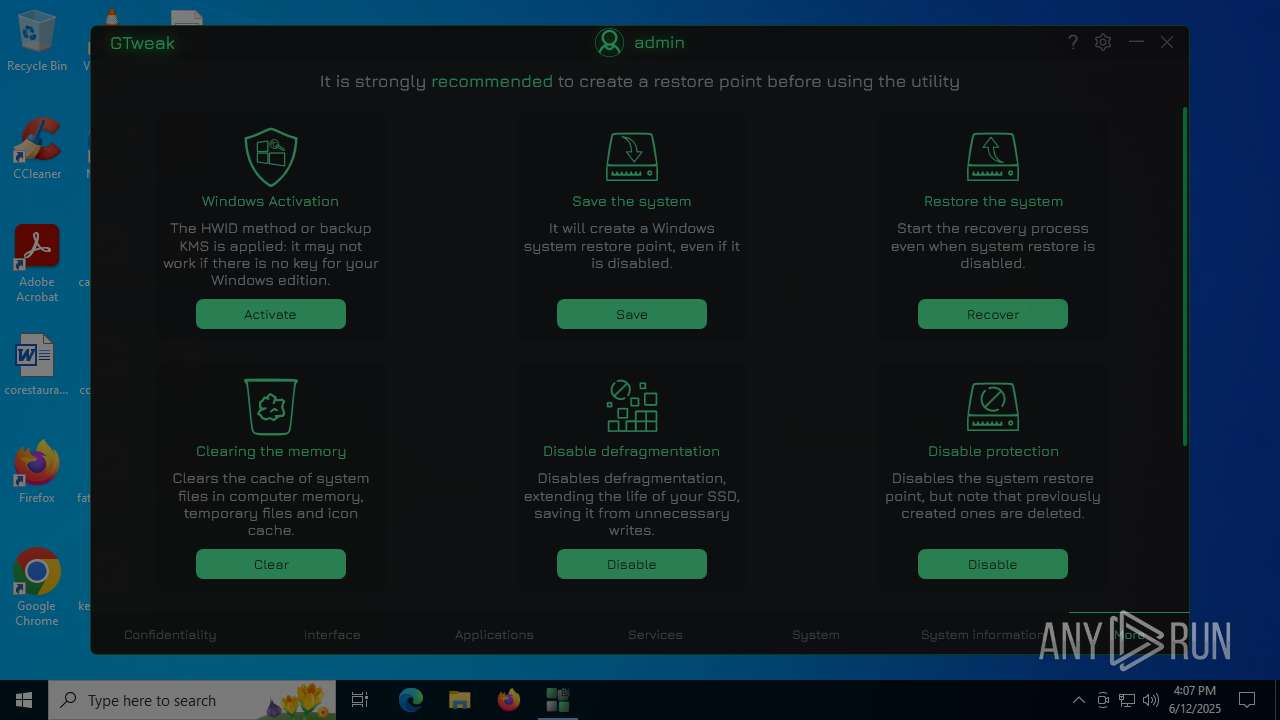
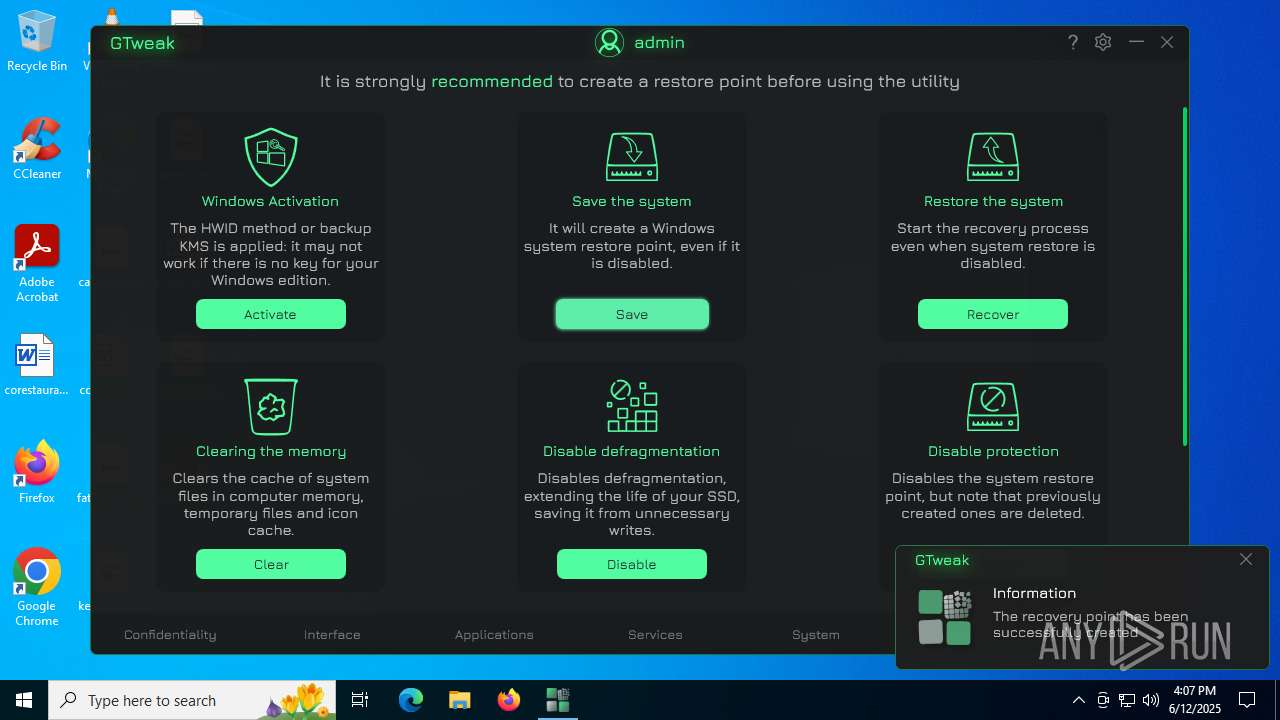
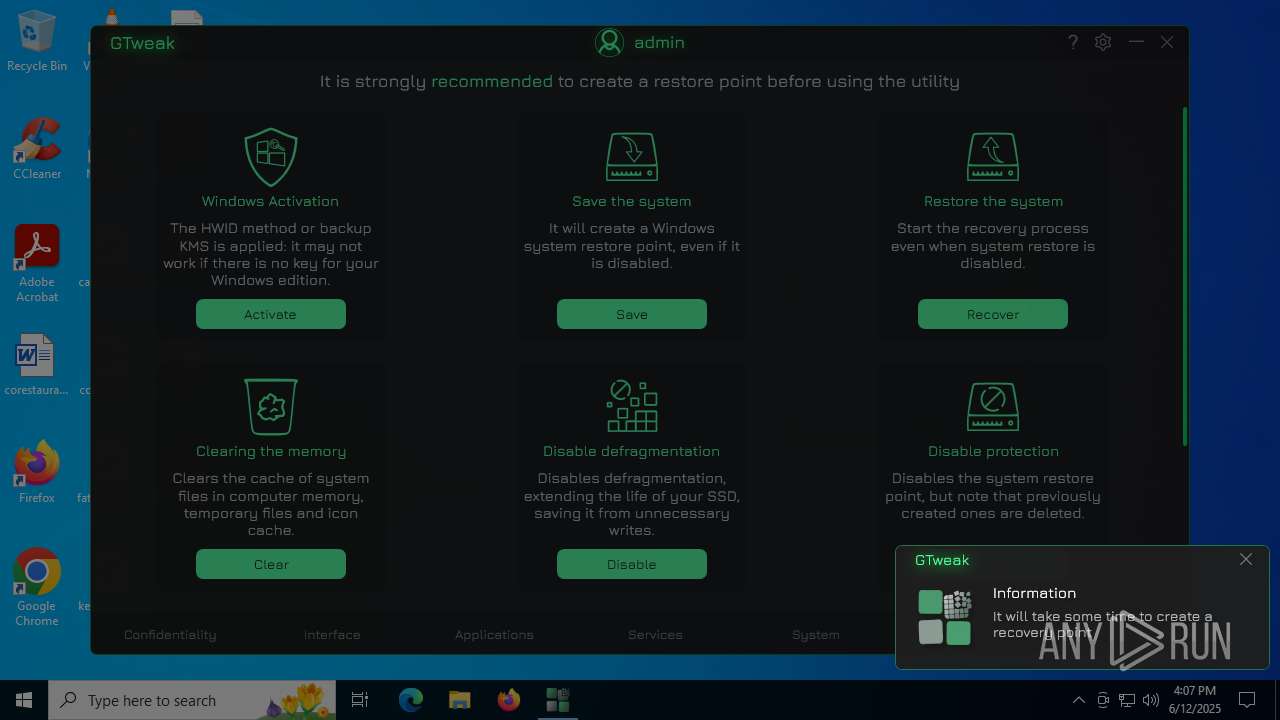
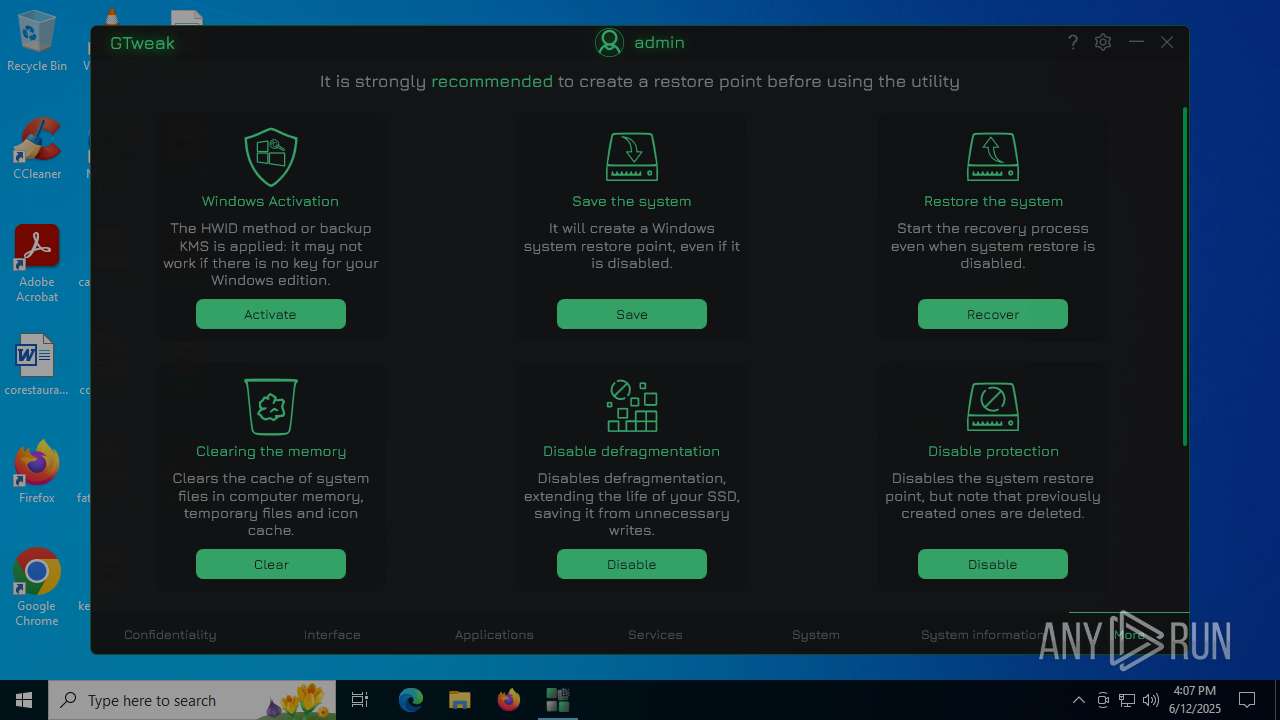
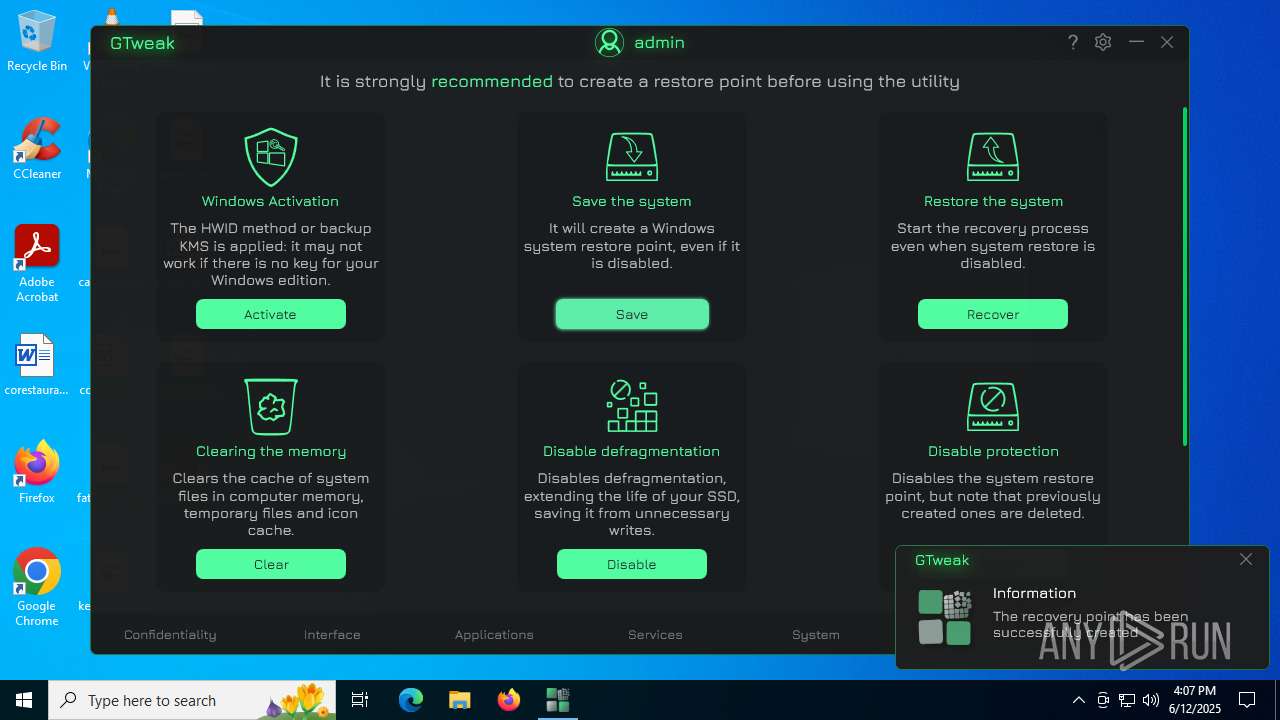
Manages system restore points
- SrTasks.exe (PID: 2520)
- SrTasks.exe (PID: 3100)
- SrTasks.exe (PID: 4760)
- SrTasks.exe (PID: 1132)
- SrTasks.exe (PID: 2512)
- SrTasks.exe (PID: 6836)
- SrTasks.exe (PID: 360)
- SrTasks.exe (PID: 6036)
Reads product name
- GTweak.exe (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:29 05:16:23+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 2952192 |
| InitializedDataSize: | 218624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.2.46.2 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Perfect Windows 10 & 11 setup with essential settings for maximum convenience |
| FileDescription: | GTweak |
| FileVersion: | 5.2.46.2 |
| InternalName: | GTweak.exe |
| LegalCopyright: | © 2024-2025 Greedeks |
| LegalTrademarks: | Greedeks |
| OriginalFileName: | GTweak.exe |
| ProductName: | GTweak |
| ProductVersion: | Build: 5.2.5 |
| AssemblyVersion: | 5.2.46.2 |
Total processes
234
Monitored processes
96
Malicious processes
10
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:18 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | sc config wbengine start= demand | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | netsh int ipv6 6to4 show state | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | sc config vds start= demand | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | sc config VSS start= demand | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "cmd.exe" /c sc config wbengine start= demand && sc config swprv start= demand && sc config vds start= demand && sc config VSS start= demand | C:\Windows\System32\cmd.exe | — | GTweak.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:14 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 643
Read events
24 979
Write events
1 548
Delete events
116
Modification events
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | EnableNotifications |
Value: 1 | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | EnableAutoUpdate |
Value: 1 | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | EnableTopMost |
Value: 0 | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | EnableIpBlur |
Value: 1 | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | EnableSound |
Value: 1 | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | VolumeLevel |
Value: 50 | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Language |
Value: en | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Theme |
Value: Dark | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\GTweak_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2076) GTweak.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\GTweak_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
17
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1052 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4688 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4324 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2188 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nyr0nthk.hdi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1052 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{0c39746f-fdf0-499a-9281-c7241e710c44}_OnDiskSnapshotProp | binary | |
MD5:F511875D8B385FE5663C7907BF22E772 | SHA256:68F2372791432080ED4B61749CC602396FB7EF5BC4D66732EFA85C33B34E9B57 | |||
| 4324 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{6a9370df-f765-4143-ad3f-ded23223acf7}_OnDiskSnapshotProp | binary | |
MD5:CFC89079E492E79A6F857A28F5B0397E | SHA256:0334D8F527E59F2B4A62860471763B742D955DAC45CE91E328B55C4AF742576C | |||
| 5708 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ulk4w43f.nrm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2188 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:14AFF53BA85AB338E3FF3081A1E70FCB | SHA256:5EFB2A9CAFF570A870D6A556E9E2433CF36DA601AEAB3B59C2DC64622680C6D4 | |||
| 2188 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4mxz1kq5.j3u.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
52
DNS requests
26
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
4708 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
2076 | GTweak.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=61439 | US | binary | 292 b | whitelisted |
— | — | POST | 200 | 40.126.32.134:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
— | — | GET | 304 | 4.245.163.56:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
— | — | POST | 403 | 23.35.229.160:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | US | html | 386 b | whitelisted |
4708 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
2620 | SIHClient.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | RU | binary | 510 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4708 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4708 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4708 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
api.github.com |
| whitelisted |
ipapi.co |
| shared |
nexusrules.officeapps.live.com |
| whitelisted |
api.db-ip.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ipapi .co in DNS lookup) |
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (api.db-ip.com) |
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2076 | GTweak.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |