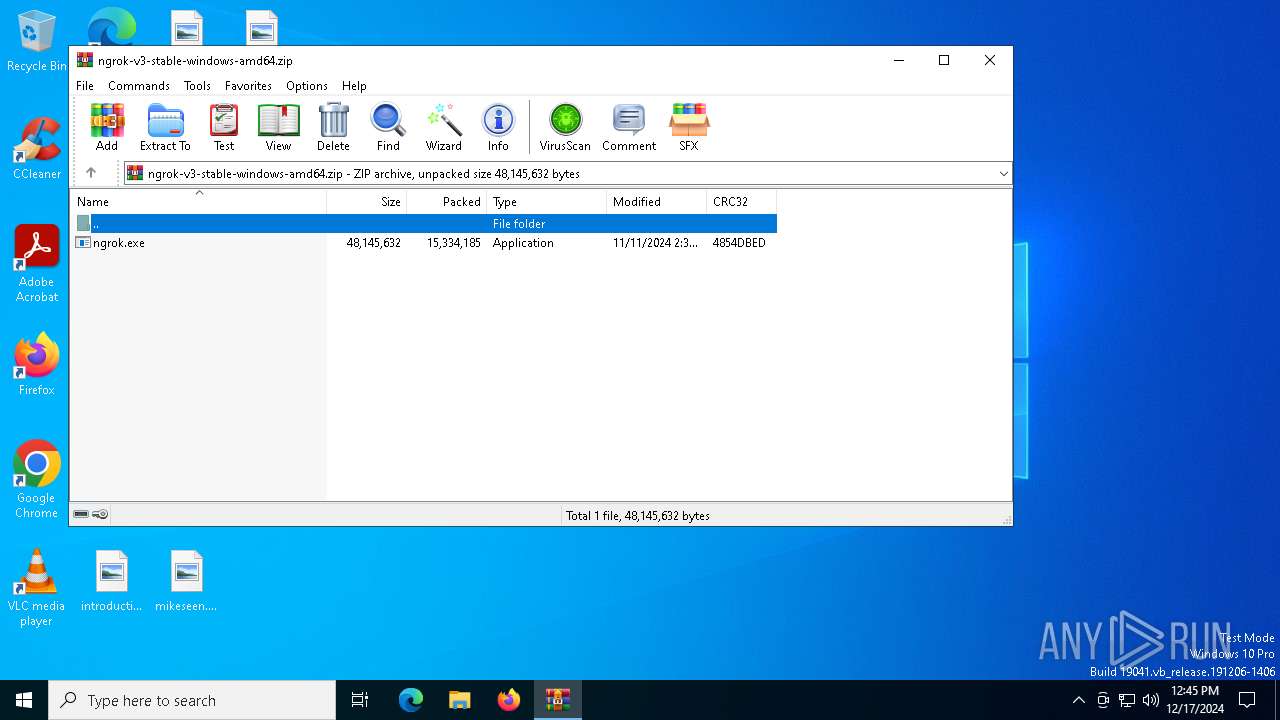
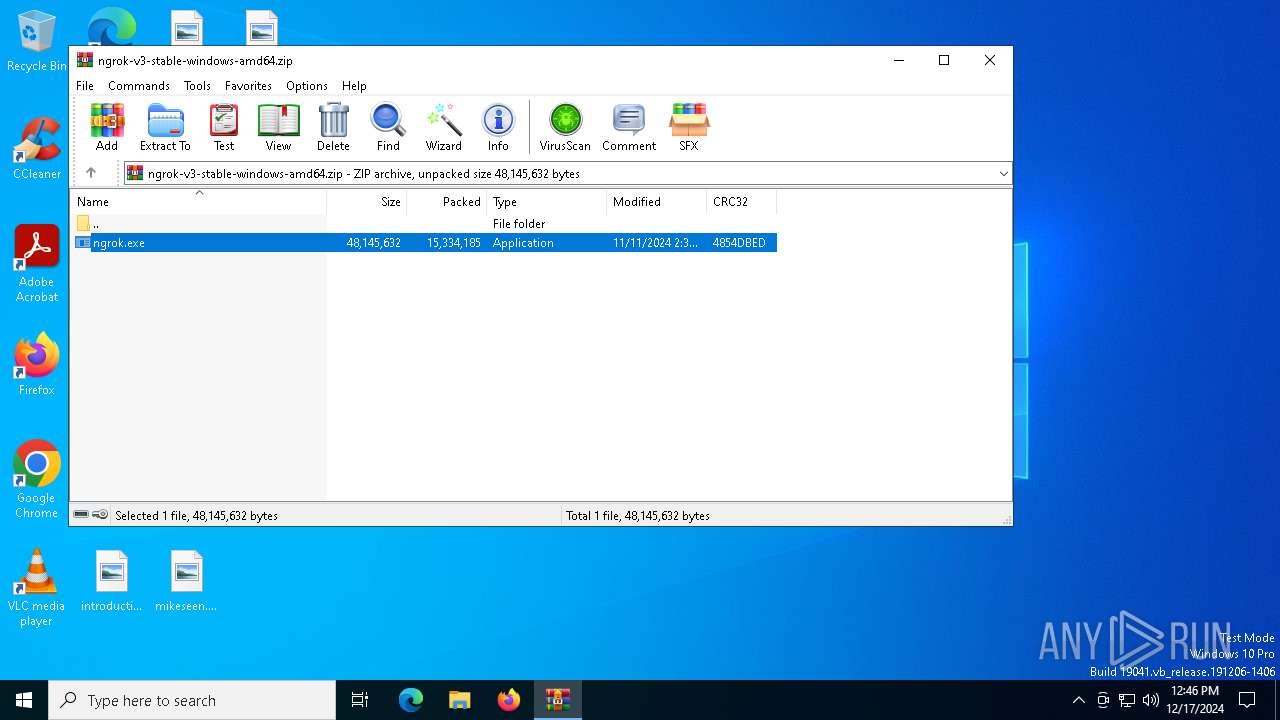
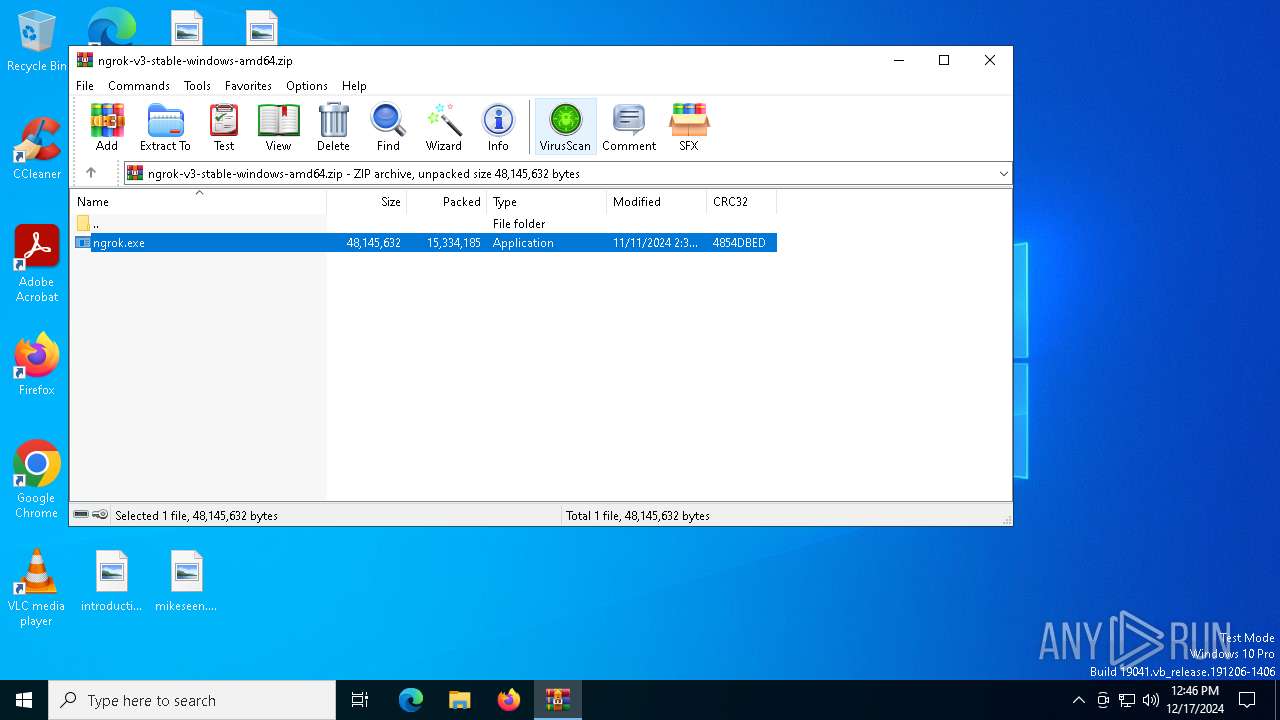
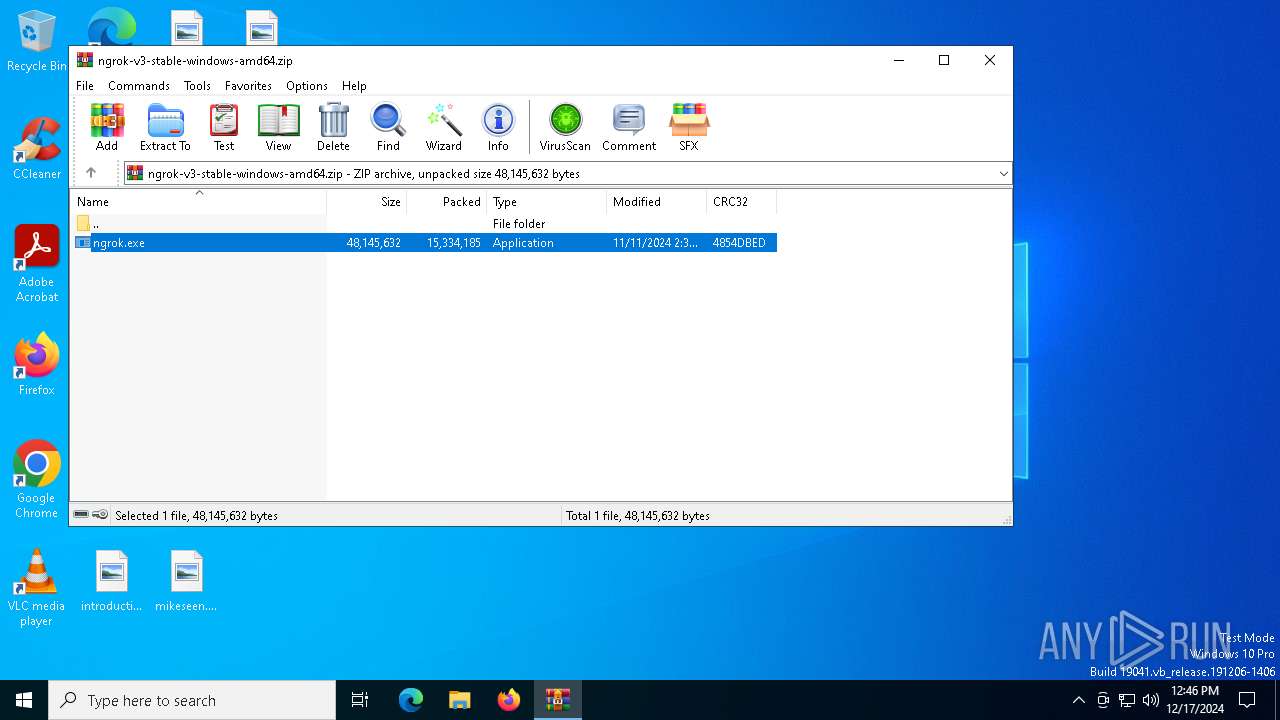
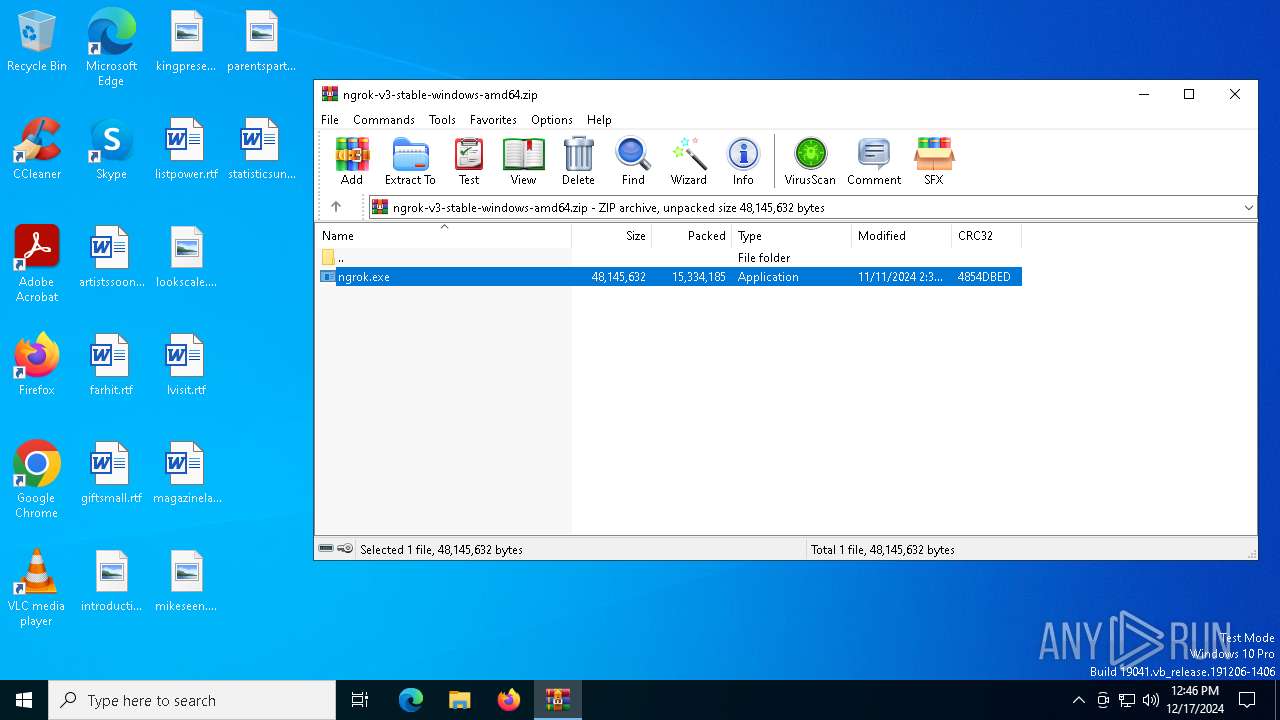
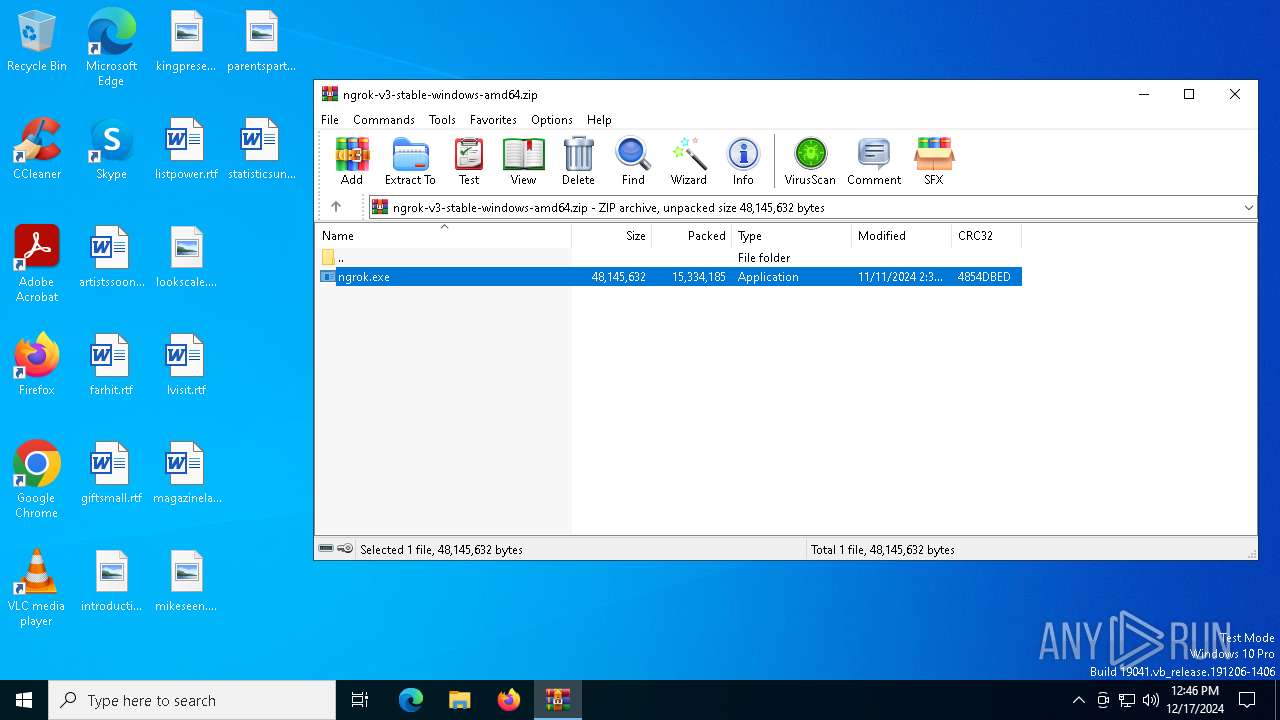
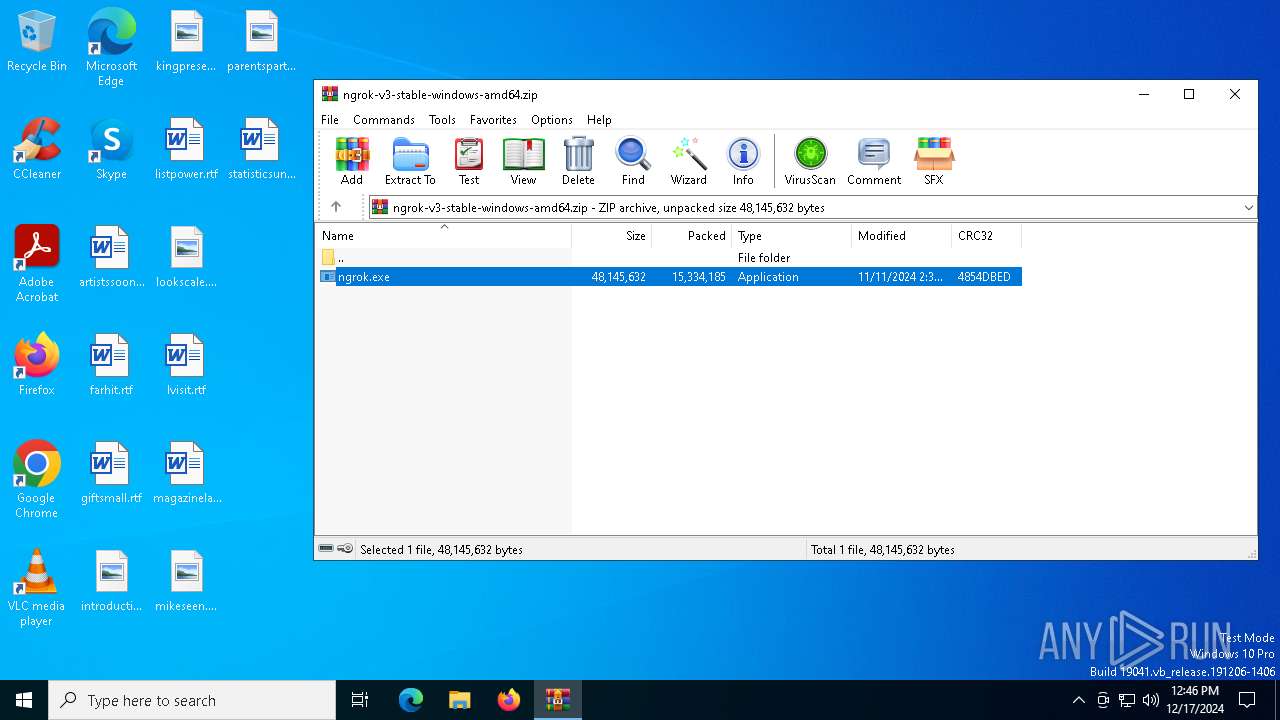
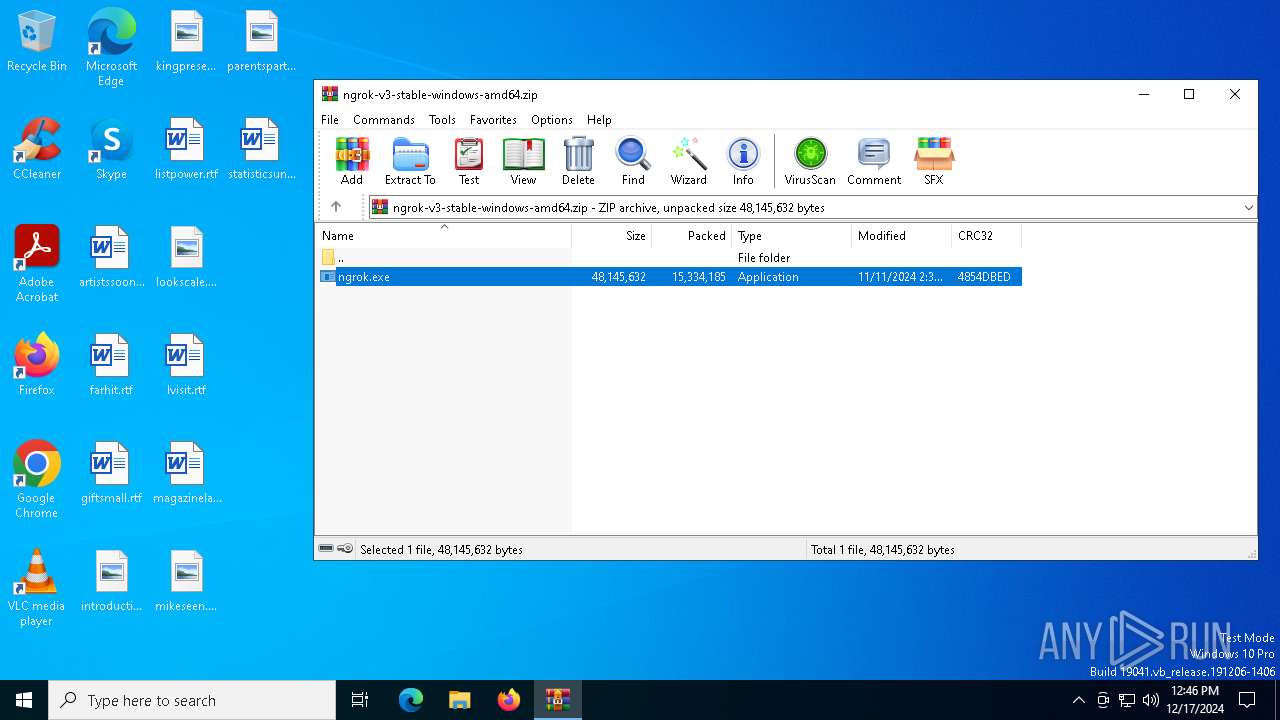
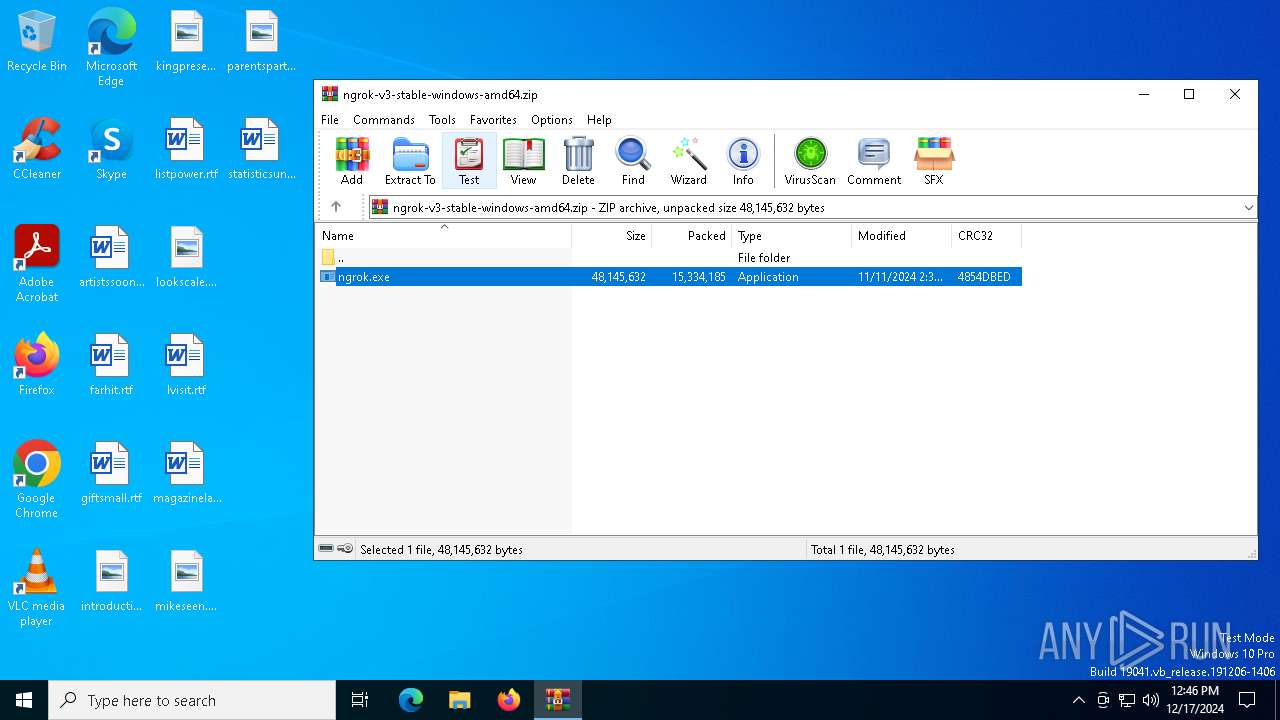
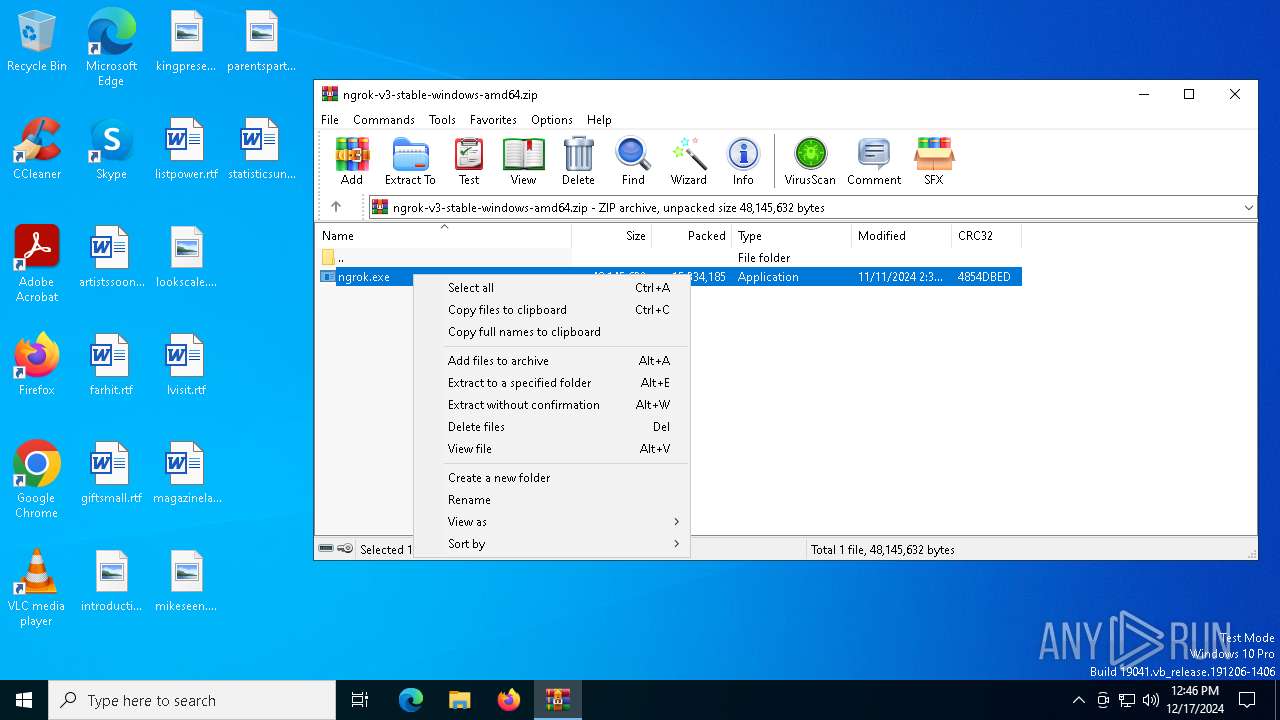
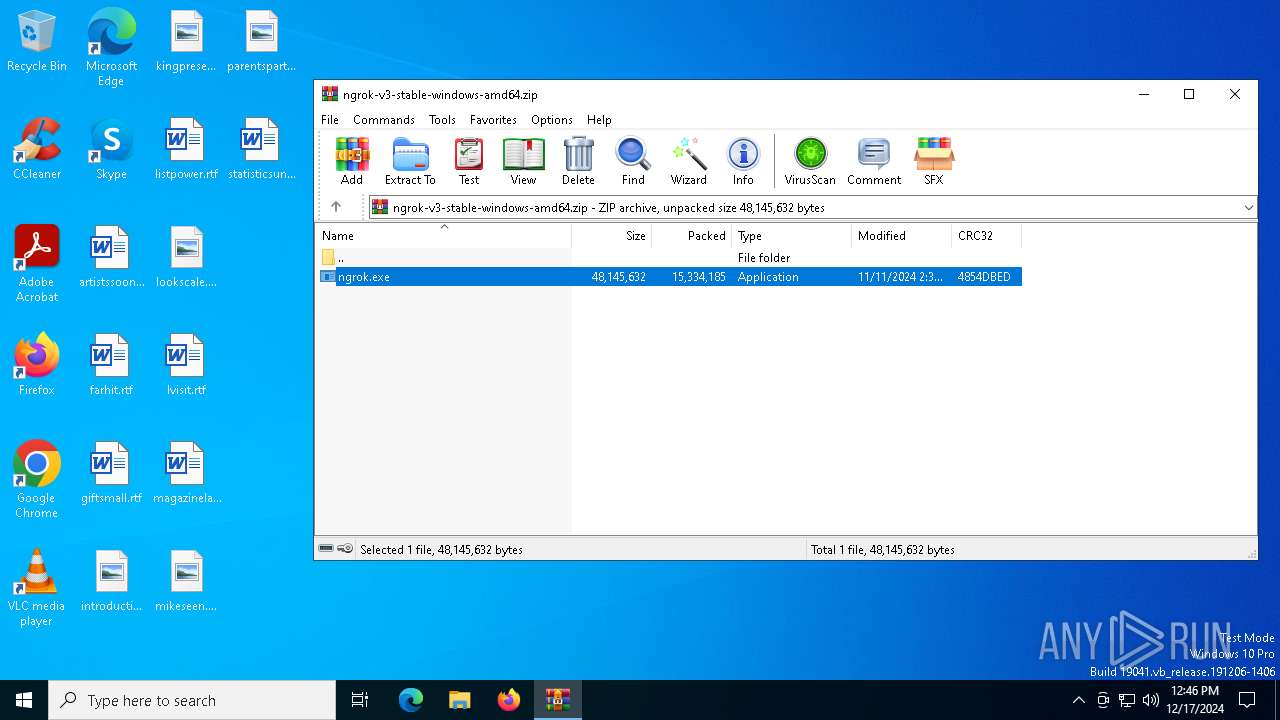
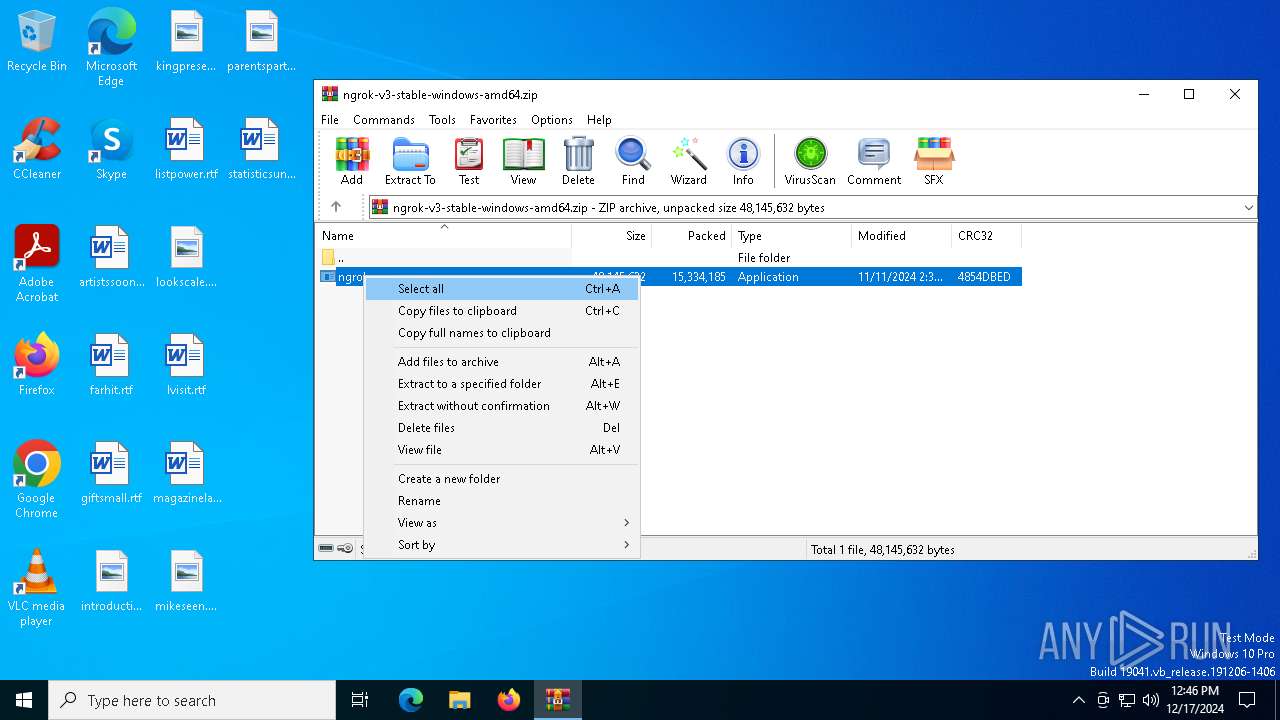
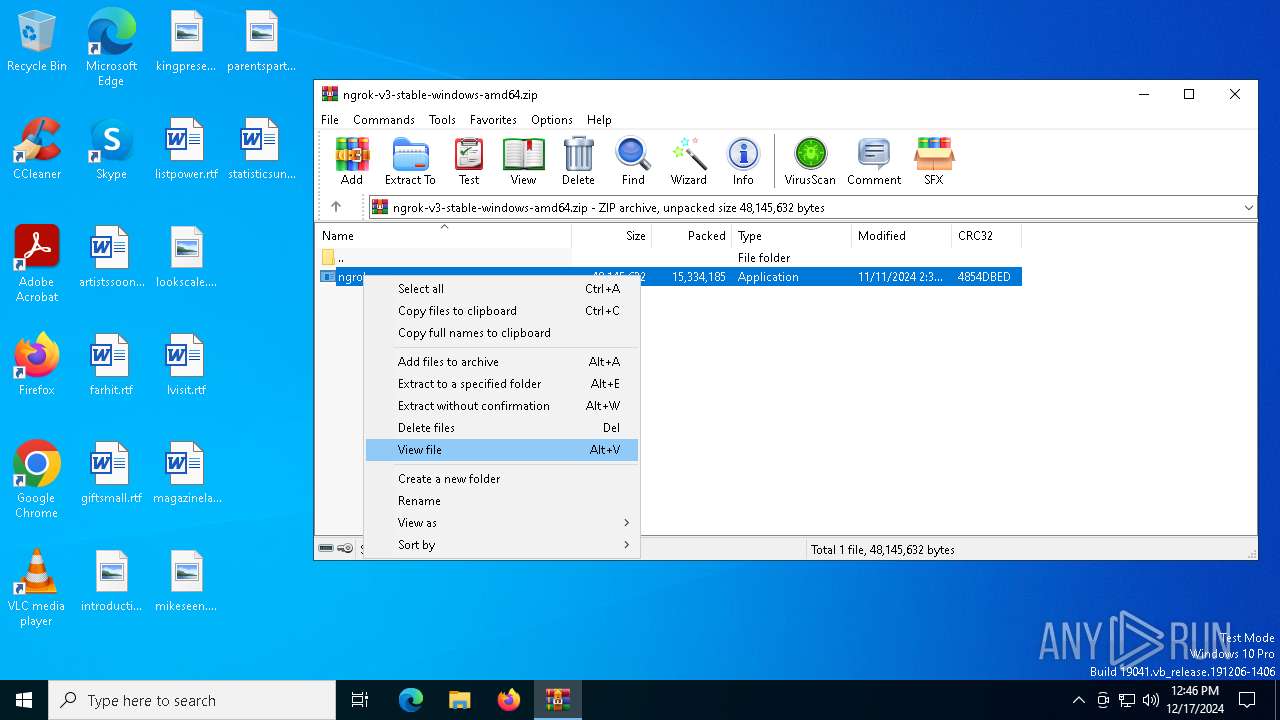
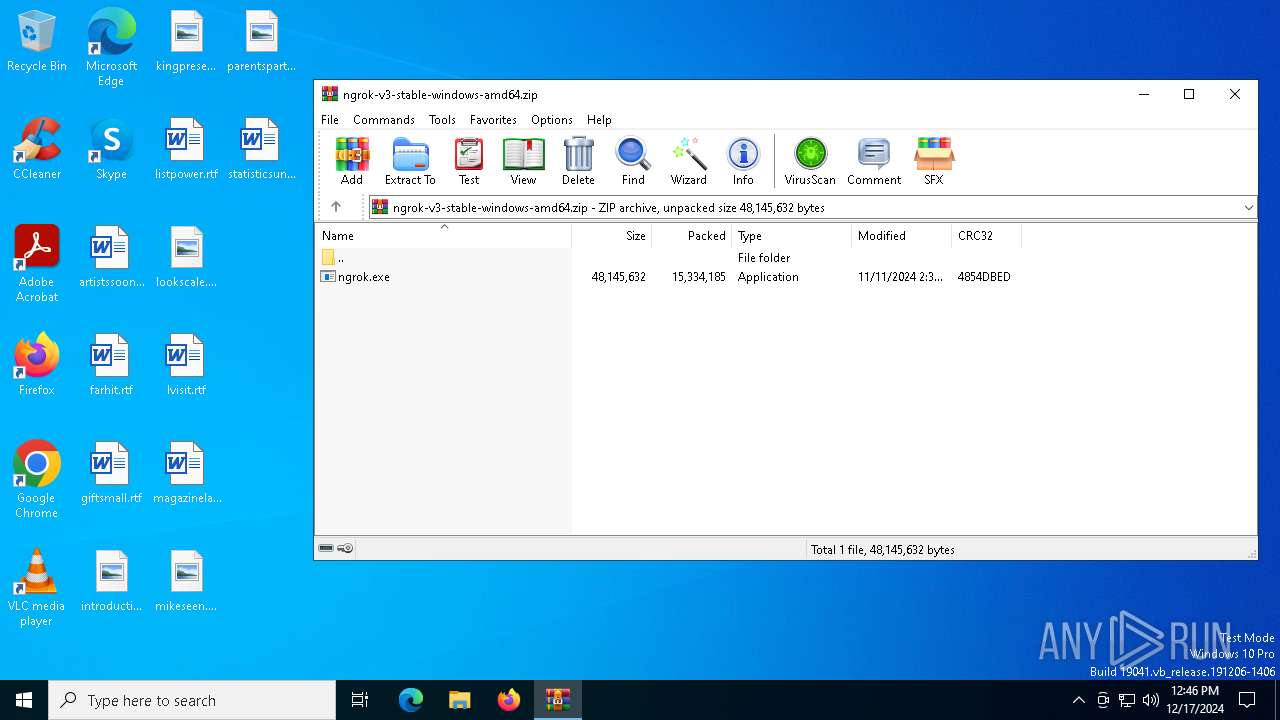
| File name: | ngrok-v3-stable-windows-amd64.zip |
| Full analysis: | https://app.any.run/tasks/245bbf3c-453a-4bdb-9476-a28d56b6233c |
| Verdict: | Malicious activity |
| Analysis date: | December 17, 2024, 12:45:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | AB5D10B3BAF4294877F11C22243EAB14 |
| SHA1: | 78397B9FA14A0BF2C8B0C5C1309331502B9A2637 |
| SHA256: | 0EC8CF167A77AE420D7F483E74AC6BAD6E653C36CCCB03DDD8C9FD9F8B49FF24 |
| SSDEEP: | 98304:iMrItipu5vD8z1tv5AXqQmj4jyITzQo99rrFv9HvTcBDeRLUkPJJGyxcgl0kHLB1:fz0tCVZgcDehGx8p8vco9GHMeb9cC |
MALICIOUS
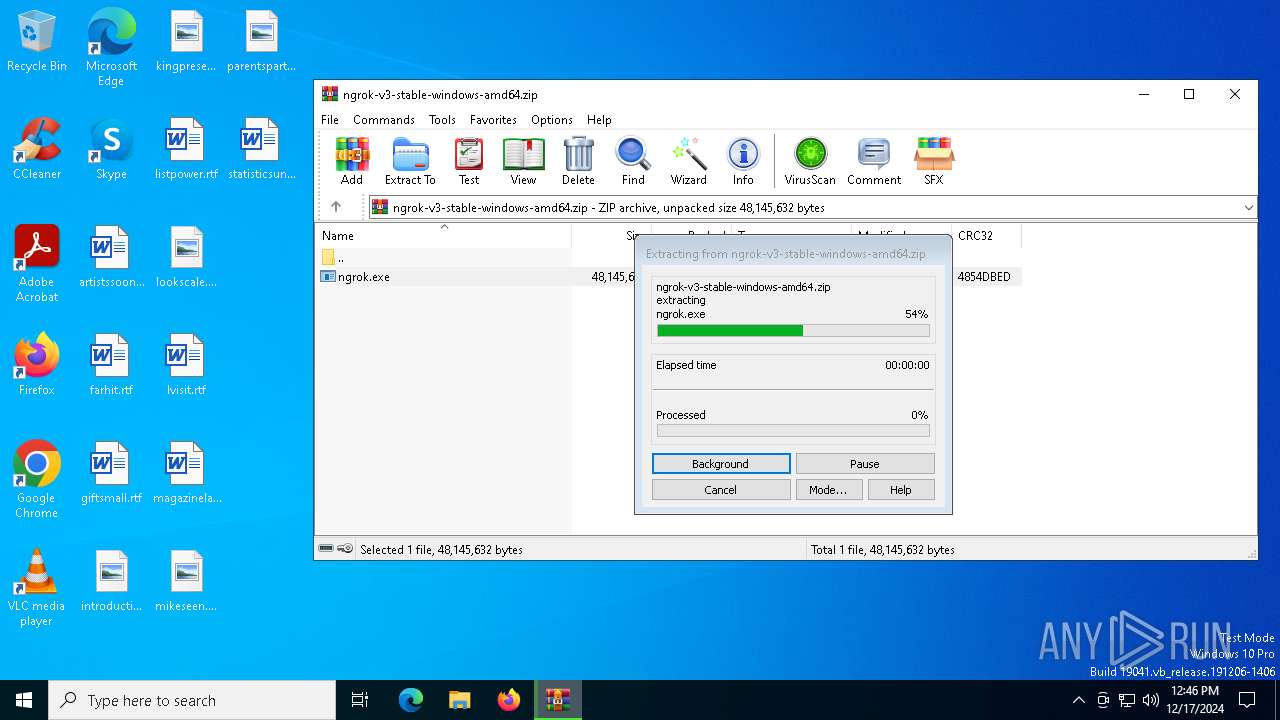
Generic archive extractor
- WinRAR.exe (PID: 6672)
SUSPICIOUS
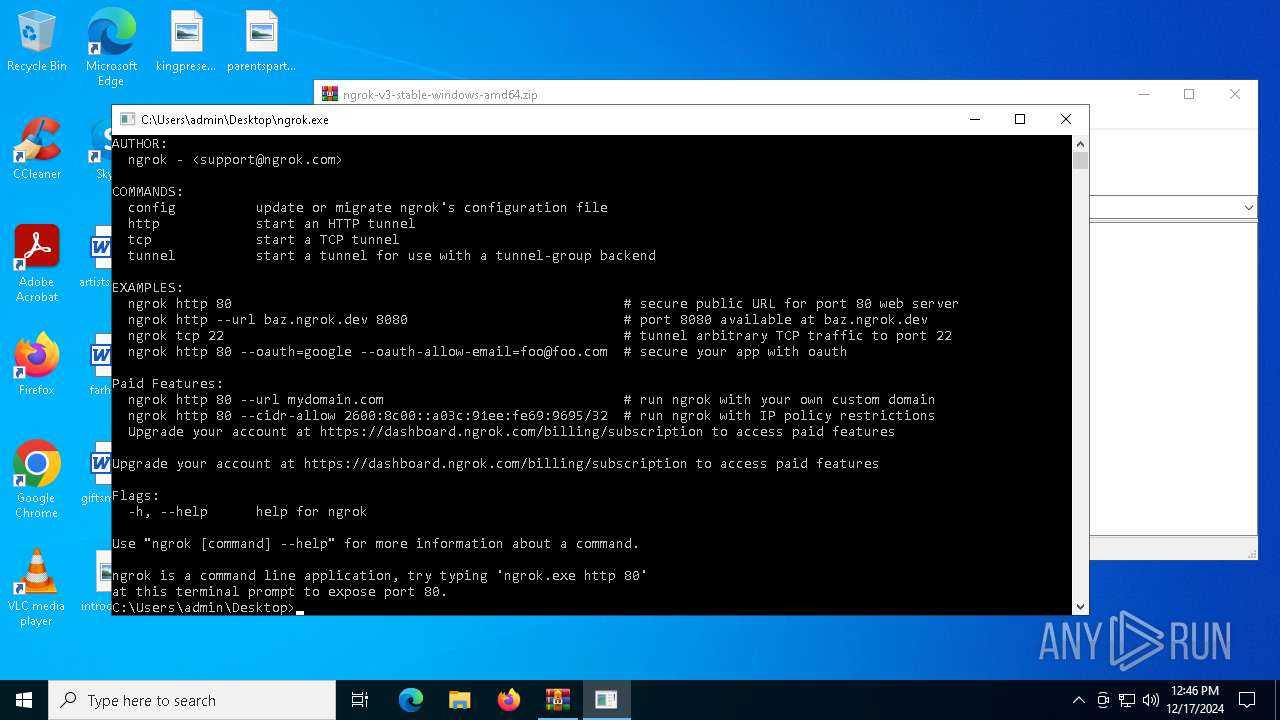
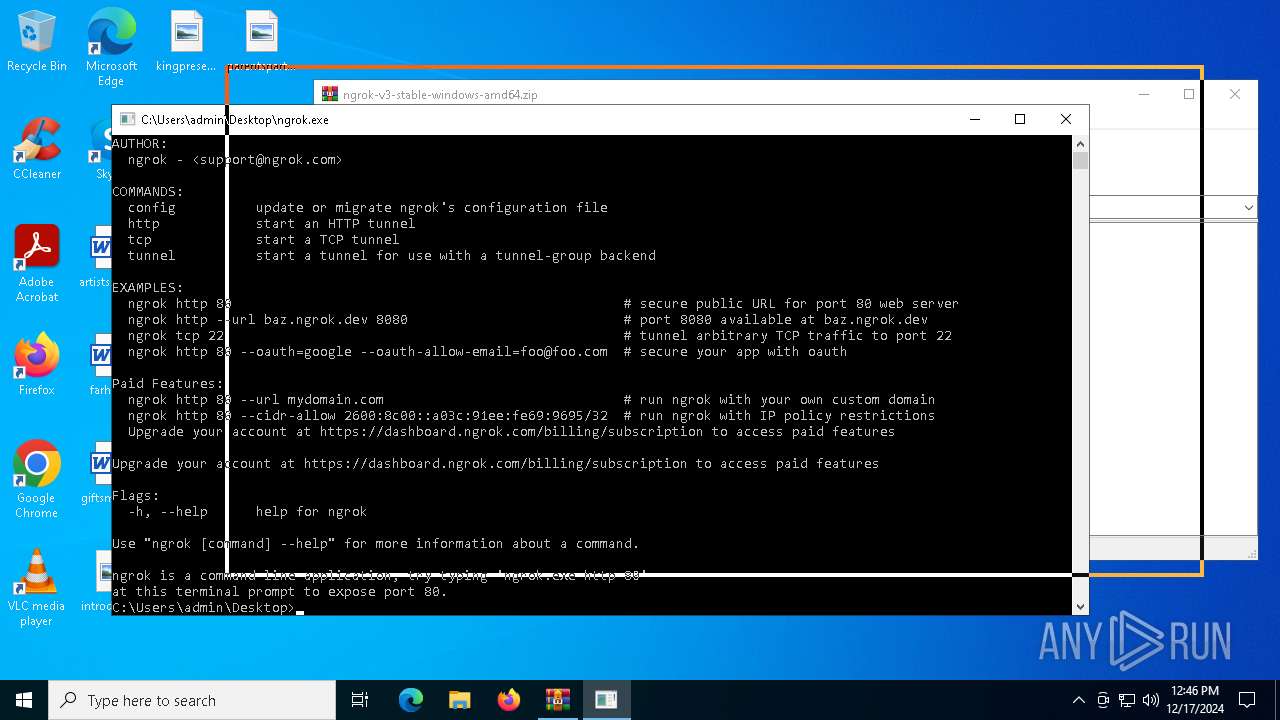
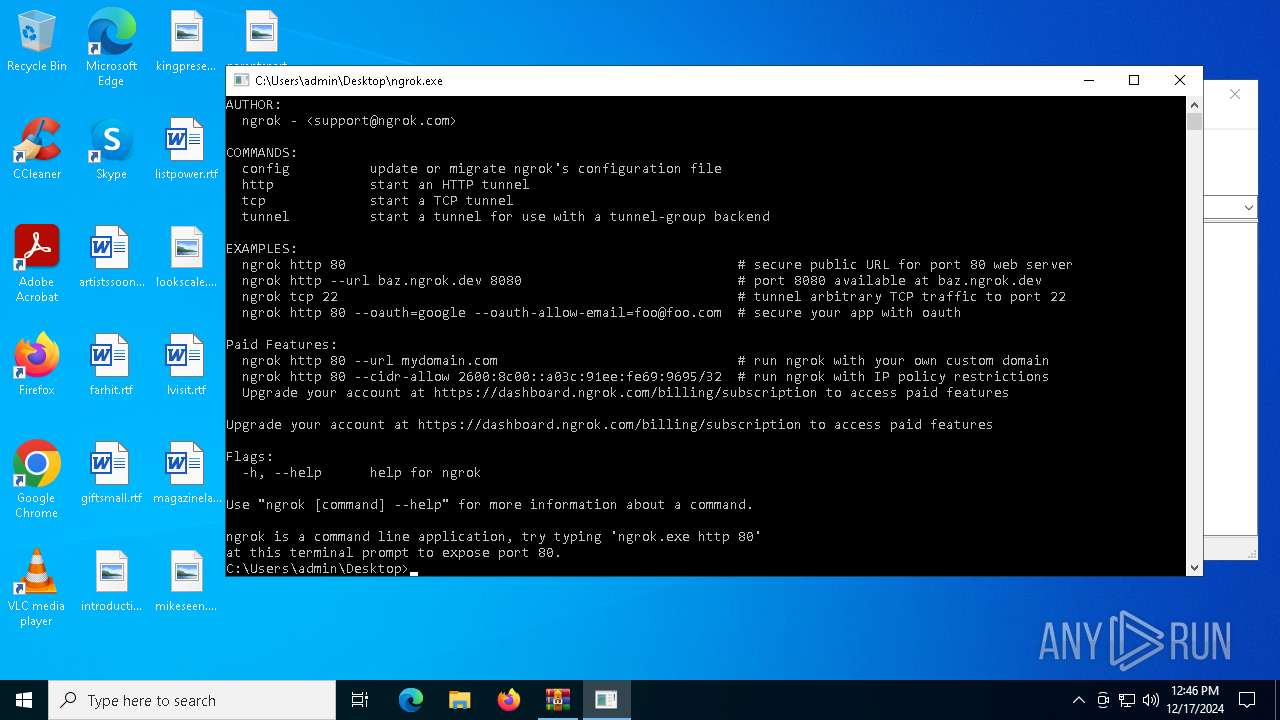
NGROK has been detected
- WinRAR.exe (PID: 6672)
- ngrok.exe (PID: 3988)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6672)
Application launched itself
- ngrok.exe (PID: 3988)
Starts CMD.EXE for commands execution
- ngrok.exe (PID: 3988)
INFO
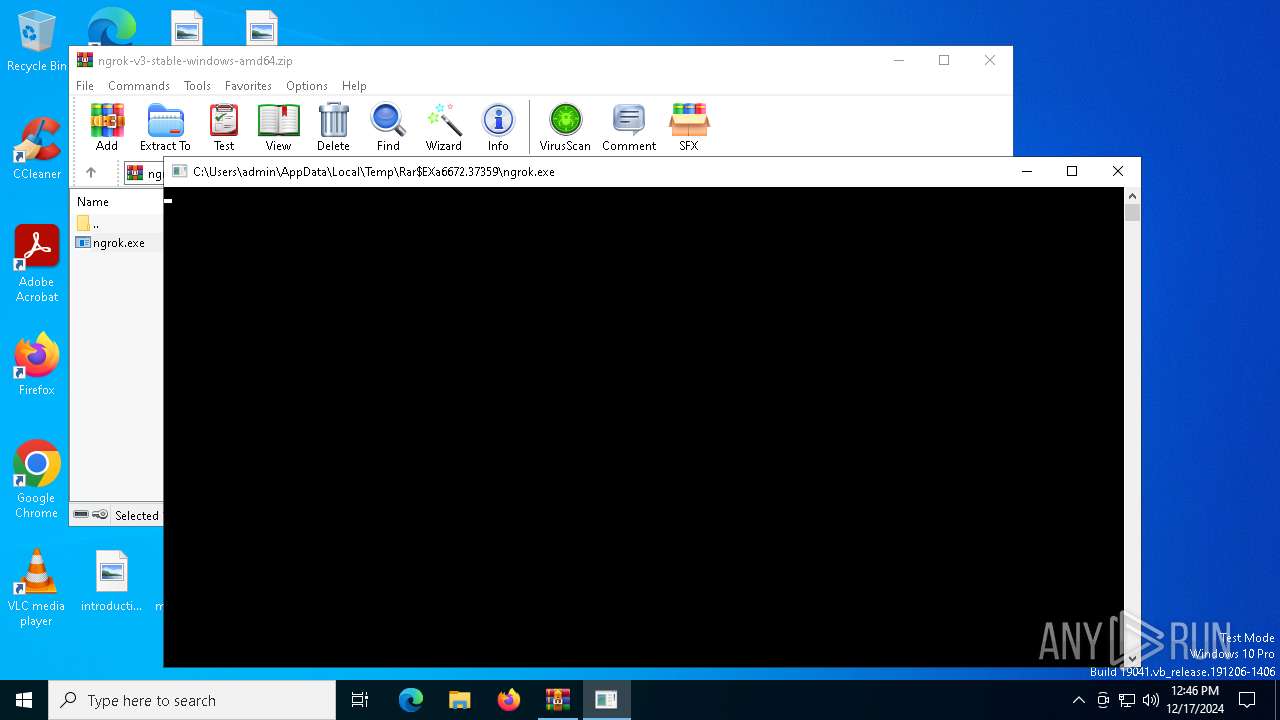
The process uses the downloaded file
- WinRAR.exe (PID: 6672)
Checks supported languages
- ngrok.exe (PID: 6844)
- ngrok.exe (PID: 7120)
- ngrok.exe (PID: 524)
- ngrok.exe (PID: 3988)
- ngrok.exe (PID: 4528)
Reads the computer name
- ngrok.exe (PID: 6844)
- ngrok.exe (PID: 7120)
- ngrok.exe (PID: 3988)
- ngrok.exe (PID: 4528)
Manual execution by a user
- ngrok.exe (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .kmz | | | Google Earth saved working session (60) |
|---|---|---|
| .zip | | | ZIP compressed archive (40) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:11:11 14:36:26 |
| ZipCRC: | 0x4854dbed |
| ZipCompressedSize: | 15334185 |
| ZipUncompressedSize: | 48145632 |
| ZipFileName: | ngrok.exe |
Total processes
125
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.39898\ngrok.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.39898\ngrok.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: The ngrok agent gets you online in one line. Exit code: 0 Modules
| |||||||||||||||
| 3876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ngrok.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\Desktop\ngrok.exe" | C:\Users\admin\Desktop\ngrok.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: The ngrok agent gets you online in one line. Modules
| |||||||||||||||
| 4520 | cmd.exe /K | C:\Windows\System32\cmd.exe | — | ngrok.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4528 | C:\Users\admin\Desktop\ngrok.exe | C:\Users\admin\Desktop\ngrok.exe | — | ngrok.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: The ngrok agent gets you online in one line. Exit code: 1 Modules
| |||||||||||||||
| 6292 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ngrok.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6672 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\ngrok-v3-stable-windows-amd64.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6844 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.37359\ngrok.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.37359\ngrok.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: The ngrok agent gets you online in one line. Exit code: 0 Modules
| |||||||||||||||
| 6856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ngrok.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7120 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.38754\ngrok.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.38754\ngrok.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: The ngrok agent gets you online in one line. Exit code: 0 Modules
| |||||||||||||||
Total events
3 050
Read events
3 042
Write events
8
Delete events
0
Modification events
| (PID) Process: | (6672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ngrok-v3-stable-windows-amd64.zip | |||
| (PID) Process: | (6672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
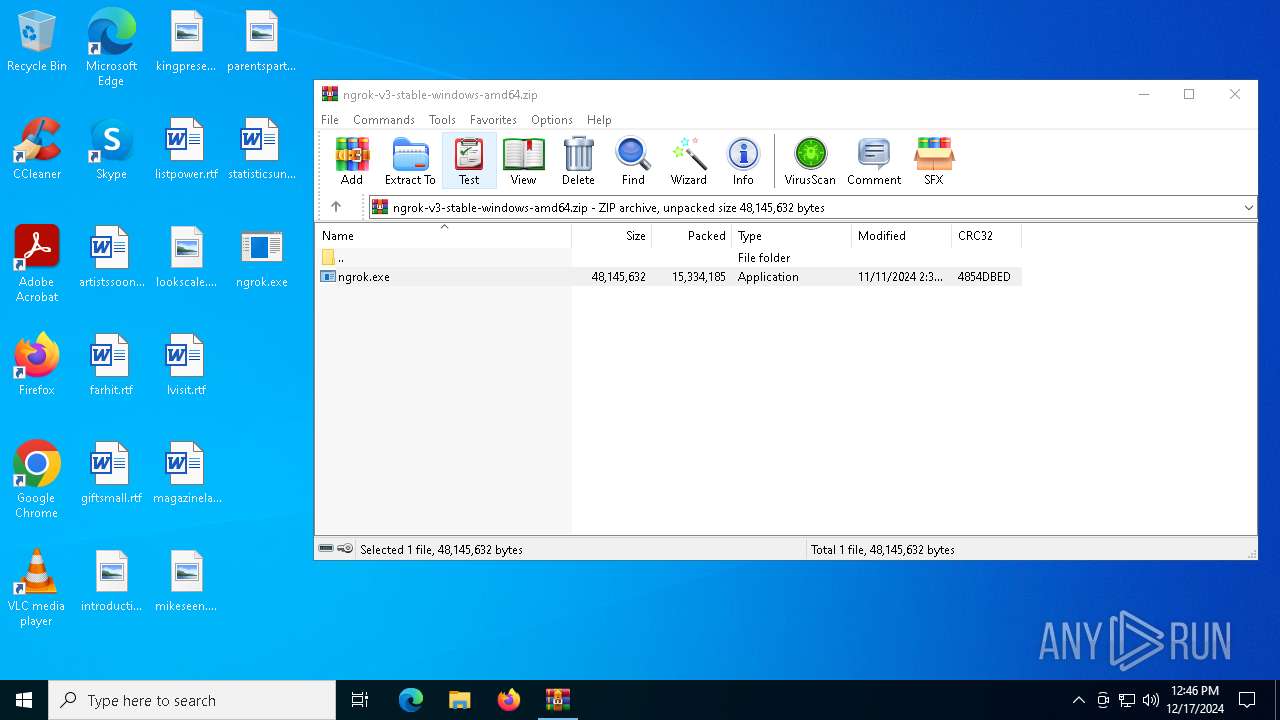
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.37359\ngrok.exe | — | |
MD5:— | SHA256:— | |||
| 6672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.38754\ngrok.exe | — | |
MD5:— | SHA256:— | |||
| 6672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6672.39898\ngrok.exe | — | |
MD5:— | SHA256:— | |||
| 6672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6672.41925\ngrok.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
31
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6184 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6988 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6988 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.29:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |