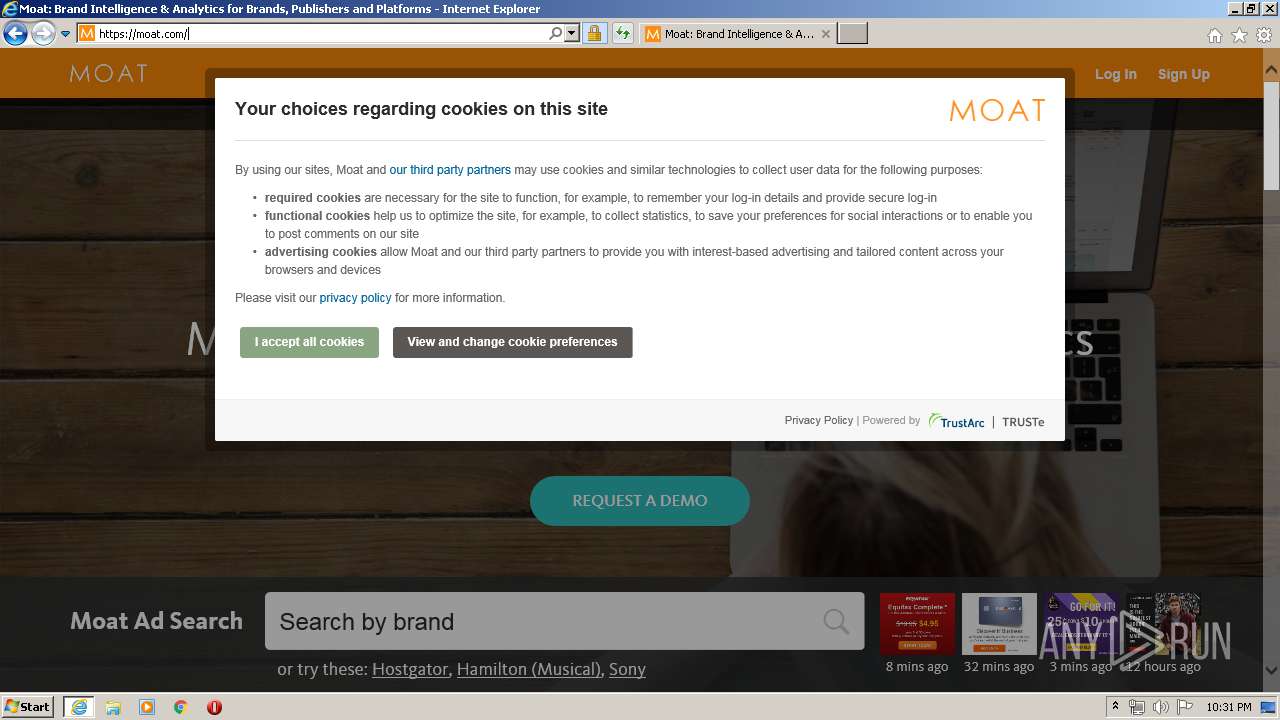
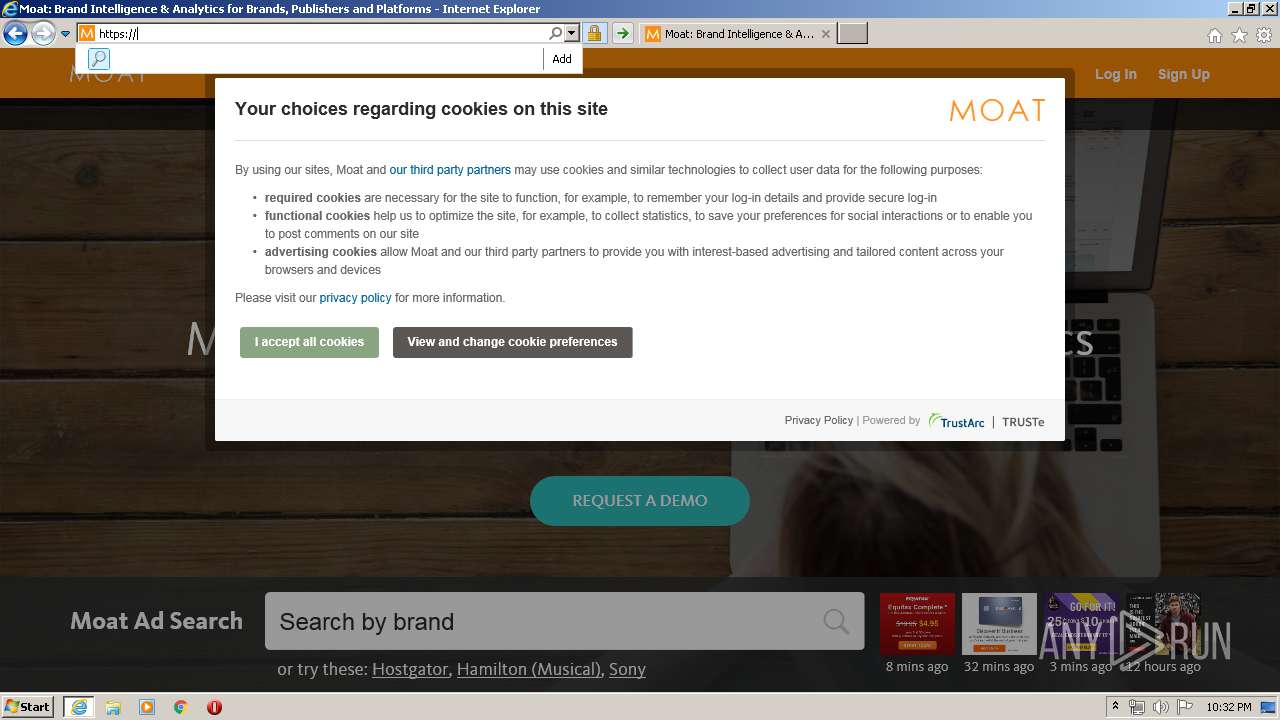
| URL: | http://z.moatads.com |
| Full analysis: | https://app.any.run/tasks/e0f5c2d6-93e4-454d-a7f1-284a2525bd8c |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2020, 22:31:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DEBE88D4F11297F9C5492CD7F8B376CD |
| SHA1: | DB97307E1A36EE5DE2C2C3006995AF27FB99E03E |
| SHA256: | 0EB4E65991D9AE5ABFA5BCF7DDC1DFEE9B2889311FFB4763D6E5DFFADD853E66 |
| SSDEEP: | 3:N1KELIfREBWLKn:CEL0iMK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2220)
INFO
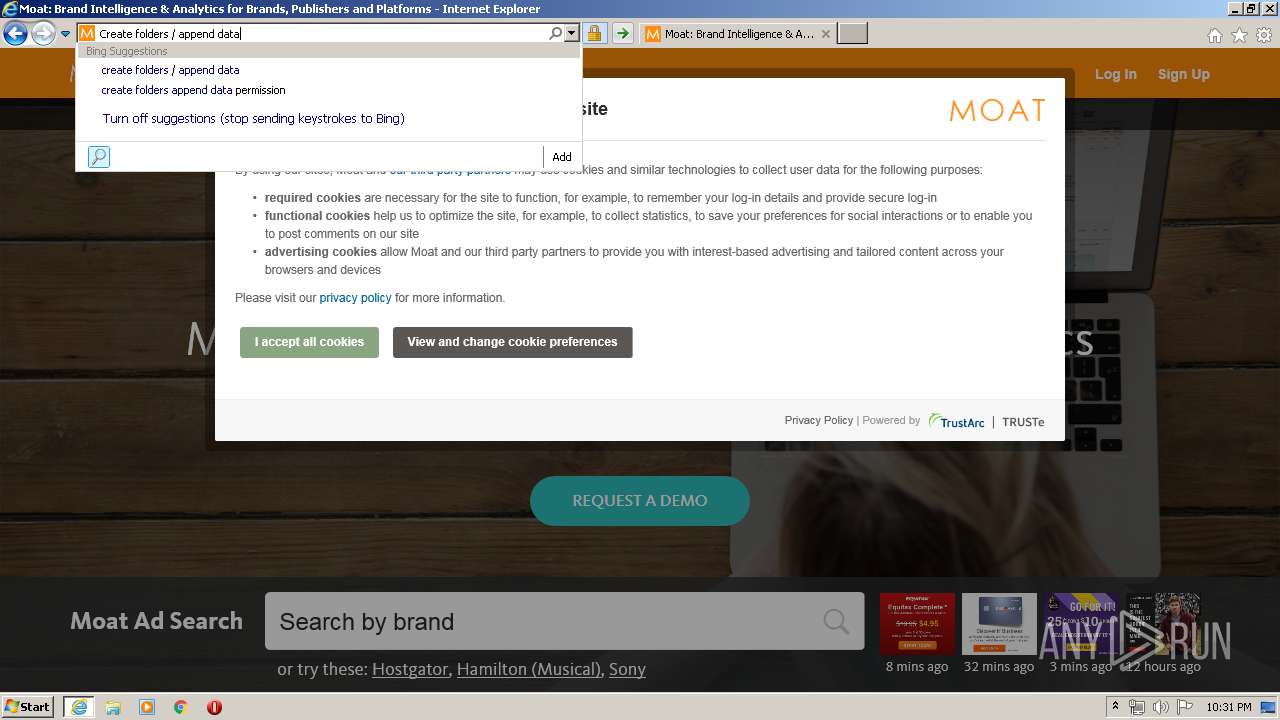
Reads Internet Cache Settings
- iexplore.exe (PID: 2488)
- iexplore.exe (PID: 3996)
Changes internet zones settings
- iexplore.exe (PID: 2488)
Reads internet explorer settings
- iexplore.exe (PID: 3996)
Creates files in the user directory
- iexplore.exe (PID: 2488)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2220)
- iexplore.exe (PID: 3996)
Connects to unusual port
- iexplore.exe (PID: 3996)
Reads settings of System Certificates
- iexplore.exe (PID: 3996)
- iexplore.exe (PID: 2488)
Changes settings of System certificates
- iexplore.exe (PID: 2488)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
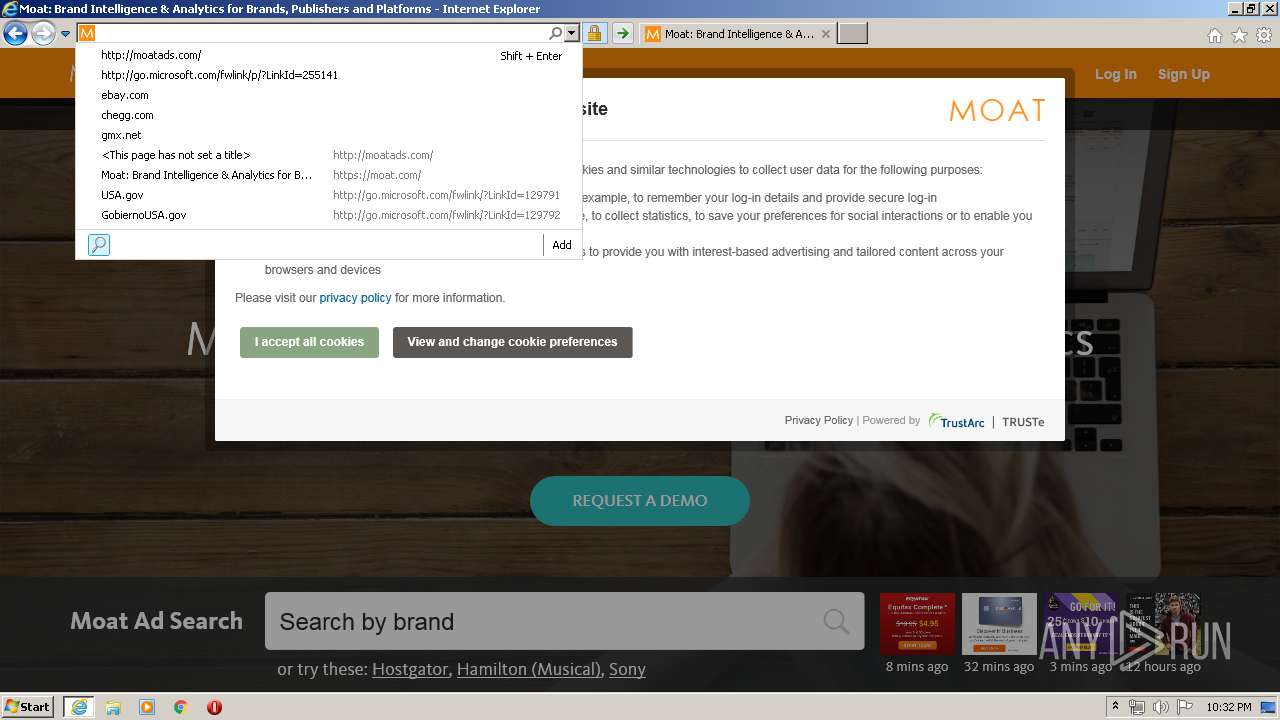
| 2488 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://z.moatads.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3996 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2488 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 893
Read events
1 526
Write events
3 650
Delete events
1 717
Modification events
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1715804788 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30793222 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
83
Text files
177
Unknown types
70
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8QU1CQCK.txt | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1UAOJV3W.txt | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 2488 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\errorPageStrings[1] | text | |
MD5:E3E4A98353F119B80B323302F26B78FA | SHA256:9466D620DC57835A2475F8F71E304F54AEE7160E134BA160BAAE0F19E5E71E66 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8AA4.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8AA5.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:FD5E62147E0751B246B08C70C827B516 | SHA256:35740FB3CCE2E3BFAD379FC239FFF9CC96013960E682683C1F7ABD34313D757E | |||
| 2488 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:54319322A2530191C85DF1C29E75D43F | SHA256:B0DBDF7A5E75A8ED5F4A4515EA07384111910E7E26688EBA74D5A2A399831243 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:9C79052CD4702AB47E3269B42E873AC7 | SHA256:27174FF21A72F50A2731A7454133B29C2397AA53ABD8848C6FED36A36F0E25EE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
164
DNS requests
43
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | iexplore.exe | GET | 403 | 2.18.235.40:80 | http://z.moatads.com/ | unknown | xml | 243 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fmoatads.com%2F&maxwidth=532&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 211 b | whitelisted |
2488 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2F.moatads.com%2F&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 212 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAdfvIAL5%2BNs%2F%2BbWdX4WCY8%3D | US | der | 471 b | whitelisted |
3996 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3996 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
3996 | iexplore.exe | GET | 200 | 52.23.179.69:80 | http://moatads.com/ | US | html | 152 b | unknown |
3996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3996 | iexplore.exe | 2.18.235.40:80 | z.moatads.com | Akamai International B.V. | — | whitelisted |
3996 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
2488 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3996 | iexplore.exe | 52.23.179.69:80 | moatads.com | Amazon.com, Inc. | US | unknown |
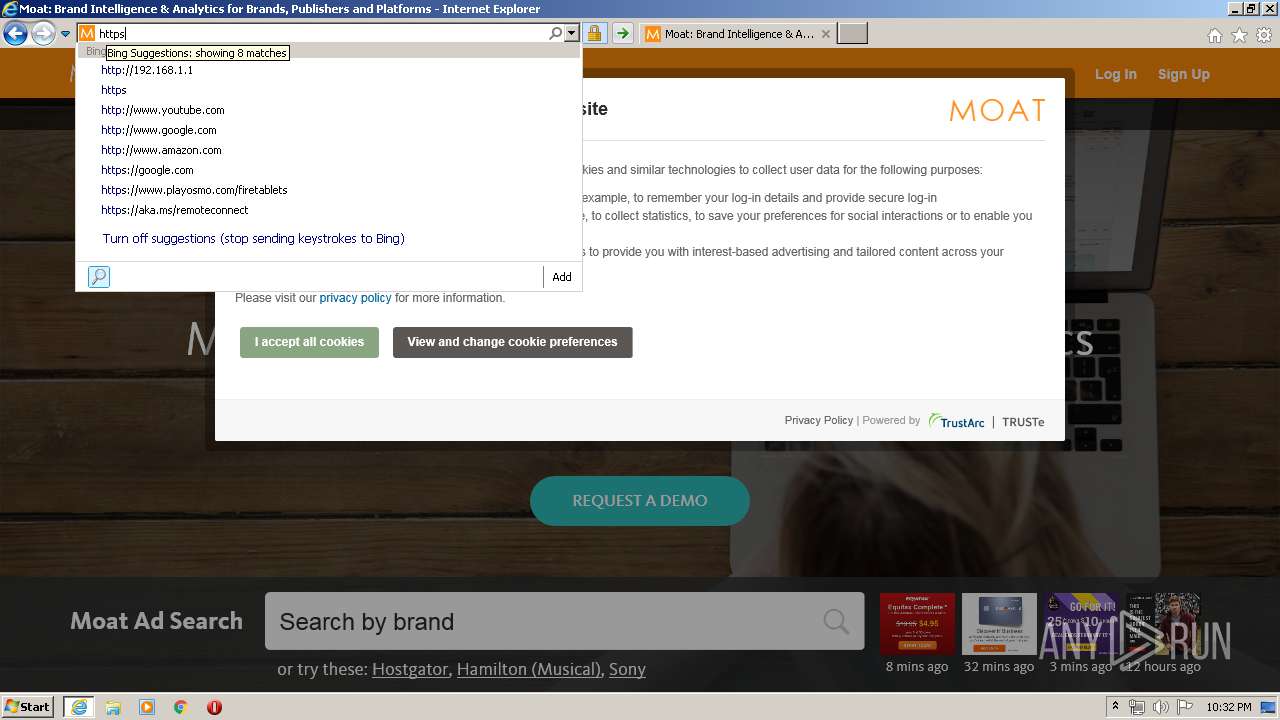
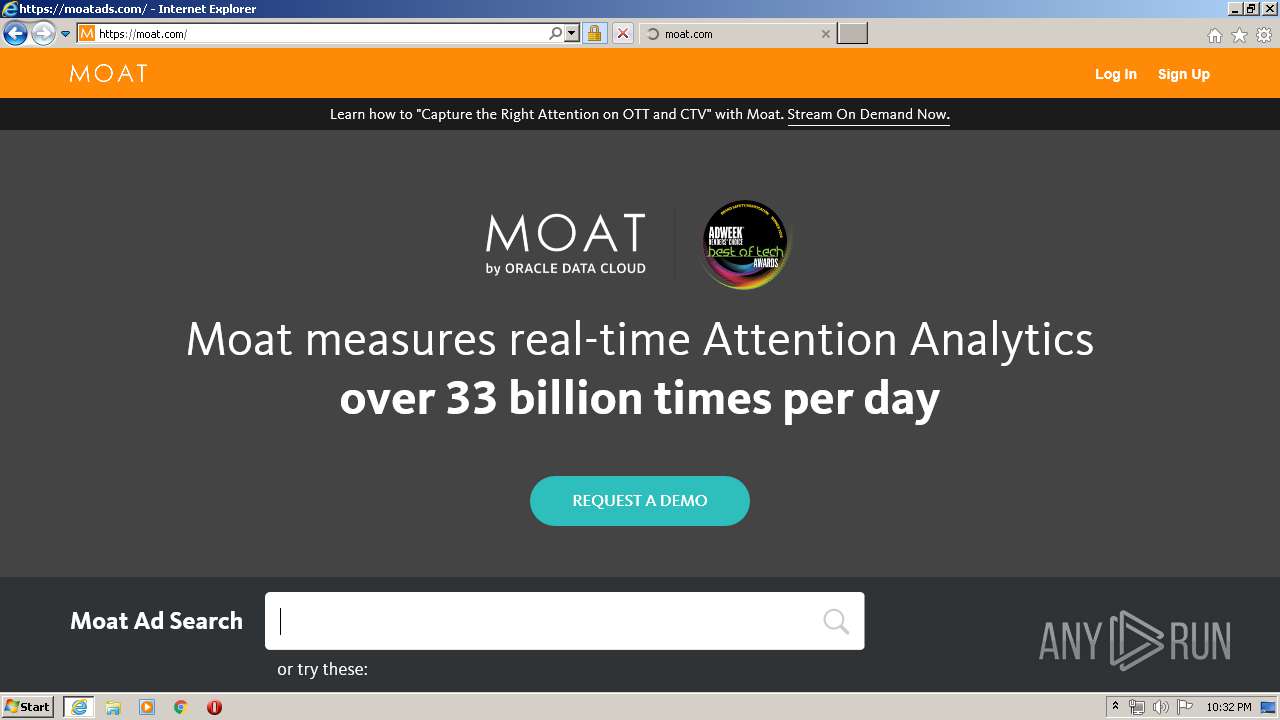
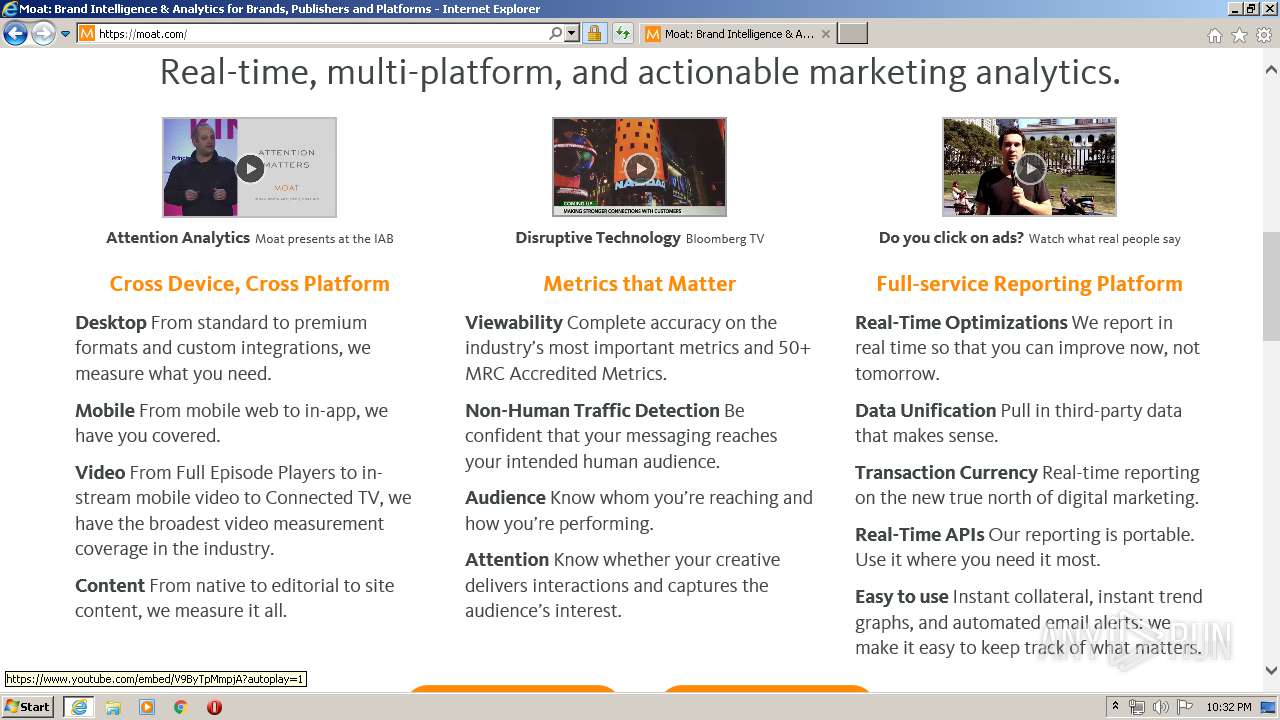
3996 | iexplore.exe | 54.236.65.72:443 | www.moat.com | Amazon.com, Inc. | US | unknown |
2488 | iexplore.exe | 52.23.179.69:80 | moatads.com | Amazon.com, Inc. | US | unknown |
3996 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3996 | iexplore.exe | 34.206.55.131:443 | www.moat.com | Amazon.com, Inc. | US | unknown |
3996 | iexplore.exe | 104.17.64.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3996 | iexplore.exe | 104.16.94.80:443 | app-sj16.marketo.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
z.moatads.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
moatads.com |
| unknown |
www.moat.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
moat.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
assets.moat.com |
| shared |
www.oracle.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3996 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
3996 | iexplore.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3996 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |