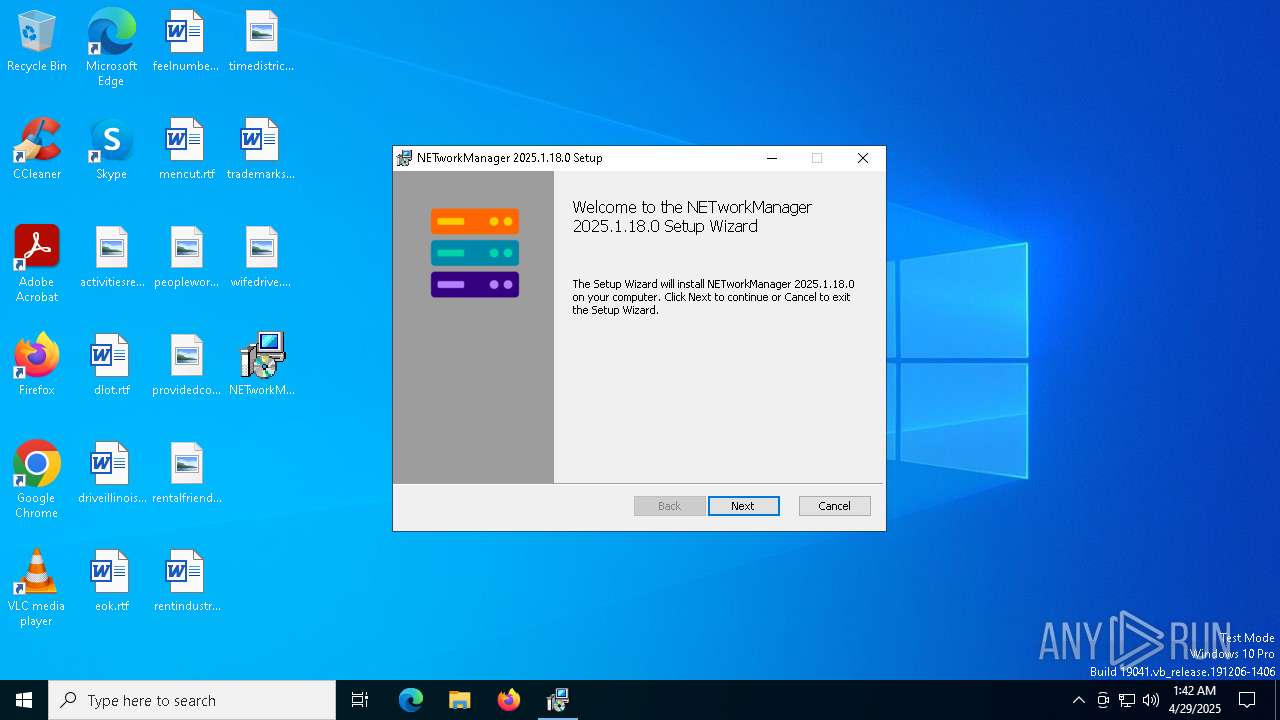
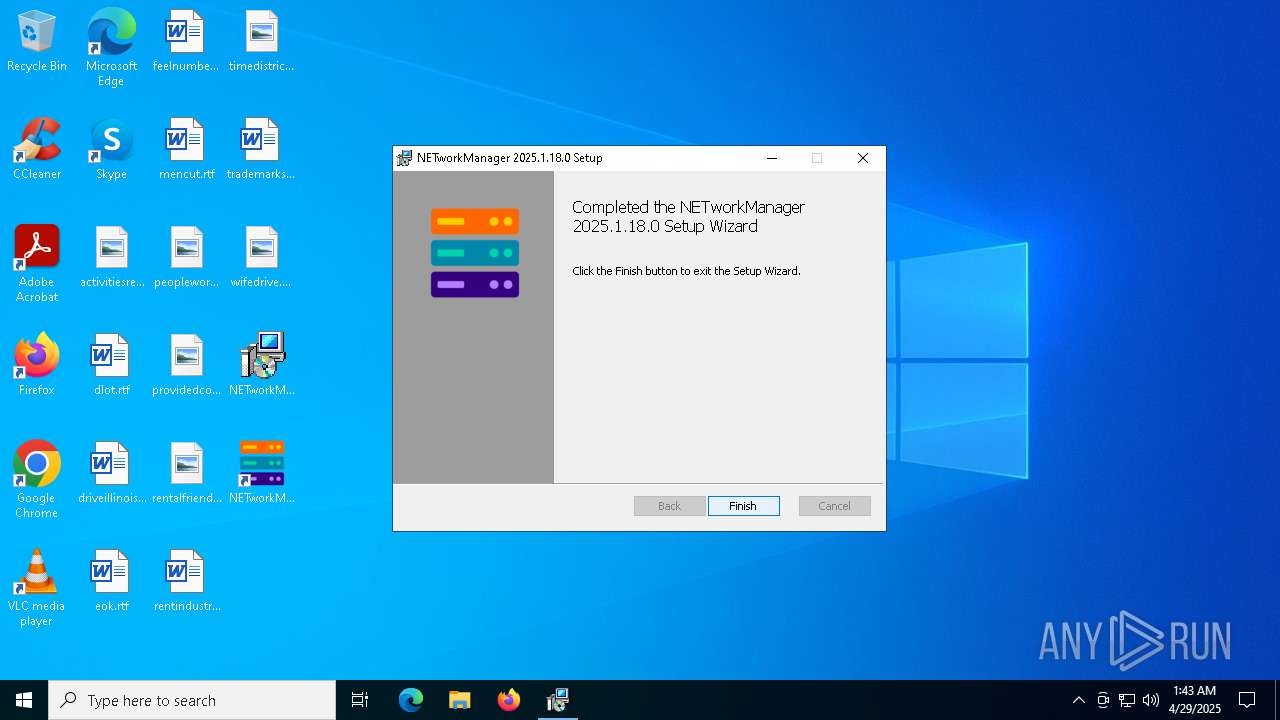
| File name: | NETworkManager_2025.1.18.0_Setup.msi |
| Full analysis: | https://app.any.run/tasks/a13151d7-6d43-4093-901f-0187ae4c145b |
| Verdict: | Malicious activity |
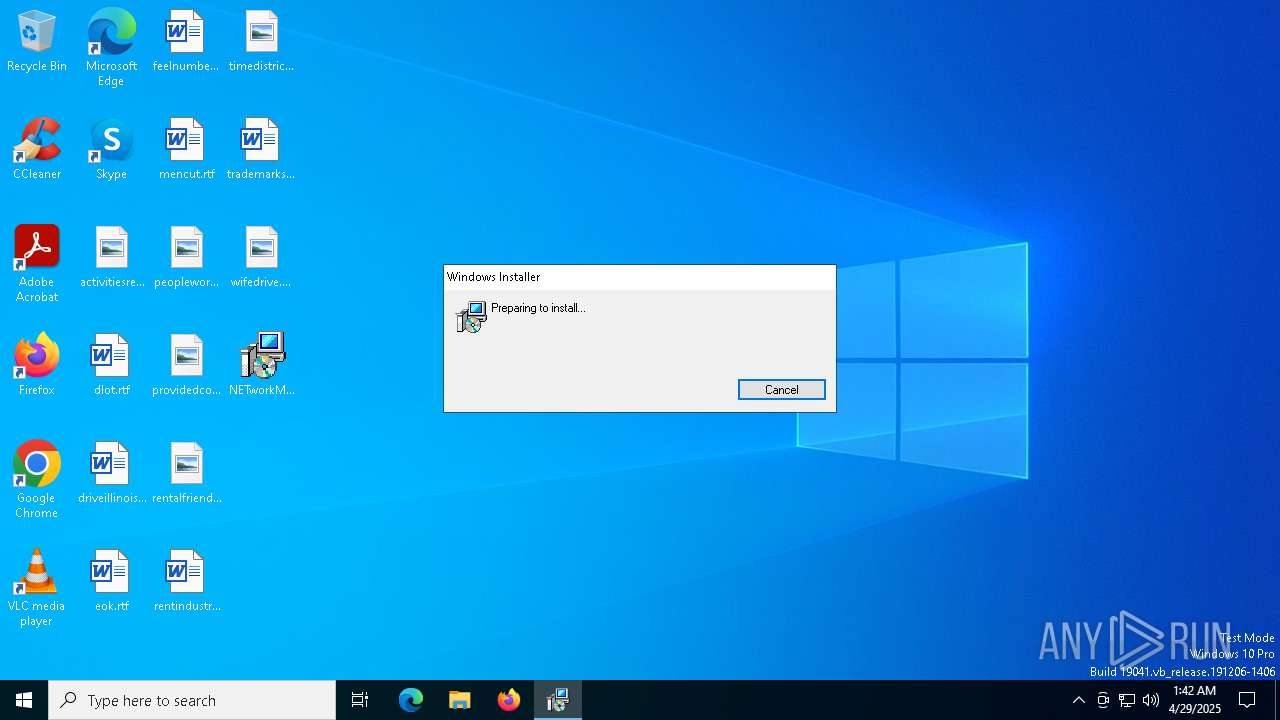
| Analysis date: | April 29, 2025, 01:42:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: NETworkManager 2025.1.18.0, Author: BornToBeRoot, Keywords: Installer, Comments: This installer database contains the logic and data required to install NETworkManager 2025.1.18.0., Template: x64;1033, Revision Number: {D7026757-7B61-4C0F-A6F3-B13C64BA3C1A}, Create Time/Date: Sat Jan 18 00:31:30 2025, Last Saved Time/Date: Sat Jan 18 00:31:30 2025, Number of Pages: 500, Number of Words: 2, Name of Creating Application: WiX Toolset (5.0.0.0), Security: 2 |
| MD5: | E63B42D493F1BBF07BE848E31652DDE0 |
| SHA1: | 042CE4092643E5AC351EE328169F544573D9C640 |
| SHA256: | 0E8722AB821FDFC5079C8E914CDBC293F373F551924EFBA14CA4AF6E68B678F9 |
| SSDEEP: | 196608:31dxkxH+zS5i1sQh1w4K0pY1sdHa6dD8naF5QWP:31LM4ScuYBK0pbdHa6ZsY5Qk |
MALICIOUS
No malicious indicators.SUSPICIOUS
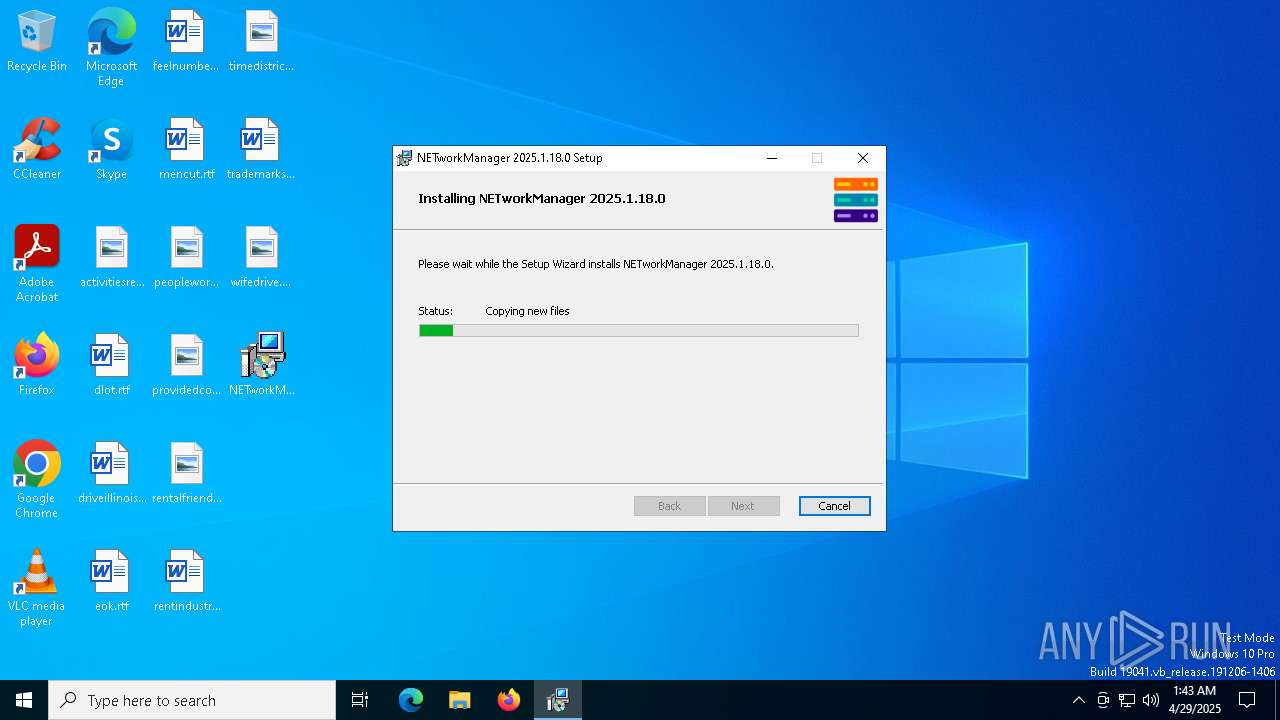
Application launched itself
- msiexec.exe (PID: 7472)
Executes as Windows Service
- VSSVC.exe (PID: 7628)
Process drops legitimate windows executable
- msiexec.exe (PID: 7472)
INFO
An automatically generated document
- msiexec.exe (PID: 7324)
Creates files or folders in the user directory
- msiexec.exe (PID: 7324)
Reads the computer name
- msiexec.exe (PID: 7472)
- msiexec.exe (PID: 7544)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7324)
Reads the software policy settings
- msiexec.exe (PID: 7324)
Checks supported languages
- msiexec.exe (PID: 7472)
- msiexec.exe (PID: 7544)
Checks proxy server information
- msiexec.exe (PID: 7324)
The sample compiled with english language support
- msiexec.exe (PID: 7324)
- msiexec.exe (PID: 7472)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7324)
- msiexec.exe (PID: 7472)
Manages system restore points
- SrTasks.exe (PID: 8036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | NETworkManager 2025.1.18.0 |
| Author: | BornToBeRoot |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install NETworkManager 2025.1.18.0. |
| Template: | x64;1033 |
| RevisionNumber: | {D7026757-7B61-4C0F-A6F3-B13C64BA3C1A} |
| CreateDate: | 2025:01:18 00:31:30 |
| ModifyDate: | 2025:01:18 00:31:30 |
| Pages: | 500 |
| Words: | 2 |
| Software: | WiX Toolset (5.0.0.0) |
| Security: | Read-only recommended |
Total processes
131
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4776 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7324 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\NETworkManager_2025.1.18.0_Setup.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7472 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7544 | C:\Windows\System32\MsiExec.exe -Embedding 0DCCB8576513C0DCC305A5B6D1B87E01 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7628 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8036 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 047
Read events
13 389
Write events
641
Delete events
17
Modification events
| (PID) Process: | (7472) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000784F9A04A8B8DB01301D0000B81D0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7472) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000784F9A04A8B8DB01301D0000B81D0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7472) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000009BA6F904A8B8DB01301D0000B81D0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7472) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000DB3EF704A8B8DB01301D0000B81D0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7472) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000DB3EF704A8B8DB01301D0000B81D0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7472) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000002D72FE04A8B8DB01301D0000B81D0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7472) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000025337F05A8B8DB01301D00005C1E0000E80300000100000000000000000000009771E714A638BB4FB22B96F21D3A6F2B00000000000000000000000000000000 | |||
| (PID) Process: | (7628) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7628) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (7628) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
287
Suspicious files
26
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7472 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7472 | msiexec.exe | C:\Windows\Installer\11655e.msi | — | |
MD5:— | SHA256:— | |||
| 7324 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8E6.tmp | executable | |
MD5:58007EABCA988956B74C5D5E2F5F7F4A | SHA256:A3ED7FF3E2A7281672708D9A56579EC5F3D6A341920524C390AA1F4DB0A54B7B | |||
| 7324 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_A784AE3E993E9BBF7162E8F9F9758D3D | binary | |
MD5:C03591273F71CB5BD6039108A32F21F4 | SHA256:46C0380A6E3A026EB0FB3E7A413AA06EABD01DF7220EDF74A4080238C659EE26 | |||
| 7324 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_A784AE3E993E9BBF7162E8F9F9758D3D | binary | |
MD5:CE7D0C14DB092479048E67447E309DE3 | SHA256:922154AE2BC08D9464A36549B6606820D2E270DBFBF8C6FE74266F42881DBD85 | |||
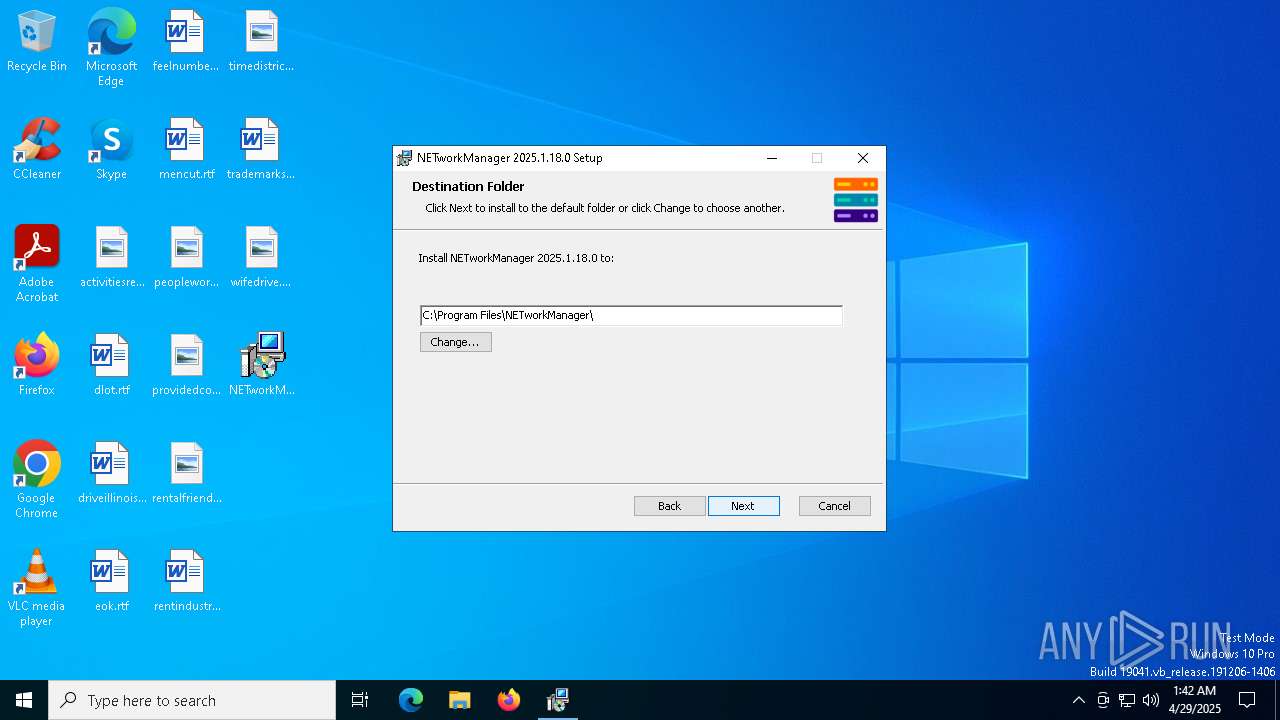
| 7472 | msiexec.exe | C:\Program Files\NETworkManager\NETworkManager.exe | executable | |
MD5:927B948091329B88CFA275A46651B61F | SHA256:CDCAD3BAE0DD4D6F6F3E6705215593D83853BDE9D1E5C402AB9A064A9EBC1F1A | |||
| 7472 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{14e77197-38a6-4fbb-b22b-96f21d3a6f2b}_OnDiskSnapshotProp | binary | |
MD5:D09240CA9A7C473F742E3E13E4F4AE9C | SHA256:B357C4BD10093C6485FF2C9FB1B0E9A2A8C9E42E0BC1A785541CD4BAA62AC1D6 | |||
| 7472 | msiexec.exe | C:\Program Files\NETworkManager\log4net.config | text | |
MD5:6F232A1CA42CDAE339D15AFACB4A2CEA | SHA256:05563622568DDAE5A53AC7B00C56BC06C59F77390C2D582403B821D556425523 | |||
| 7472 | msiexec.exe | C:\Program Files\NETworkManager\NETworkManager.runtimeconfig.json | binary | |
MD5:FD035897B90F9438D7E0E173EFA65DE3 | SHA256:734420B89F54729C6658374B3ECF8729C744A02E4A1D6BCE1B0CA6C5B9E8FC33 | |||
| 7472 | msiexec.exe | C:\Program Files\NETworkManager\NETworkManager.dll | executable | |
MD5:F83B6C397FE1679F36CDA55AAF717BCD | SHA256:01490537ECBC49921FF084EDF00301888ACB15655A3979F7F738EA067BC54267 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
24
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7324 | msiexec.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEQCBTkIXoSl%2F7VrM1Bf4ka11 | unknown | — | — | whitelisted |
7324 | msiexec.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/gsgccr45codesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLuA3ygnKW%2F7xuSx%2F09F%2BhHVuEUQQU2rONwCSQo2t30wygWd0hZ2R2C3gCDBiDgM%2Fh%2BD6nB8ZbKA%3D%3D | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7324 | msiexec.exe | 151.101.130.133:80 | ocsp.globalsign.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4776 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |