| File name: | TestProje.vmp.exe |
| Full analysis: | https://app.any.run/tasks/6427b532-621a-4707-9c39-8edc1c914517 |
| Verdict: | Malicious activity |
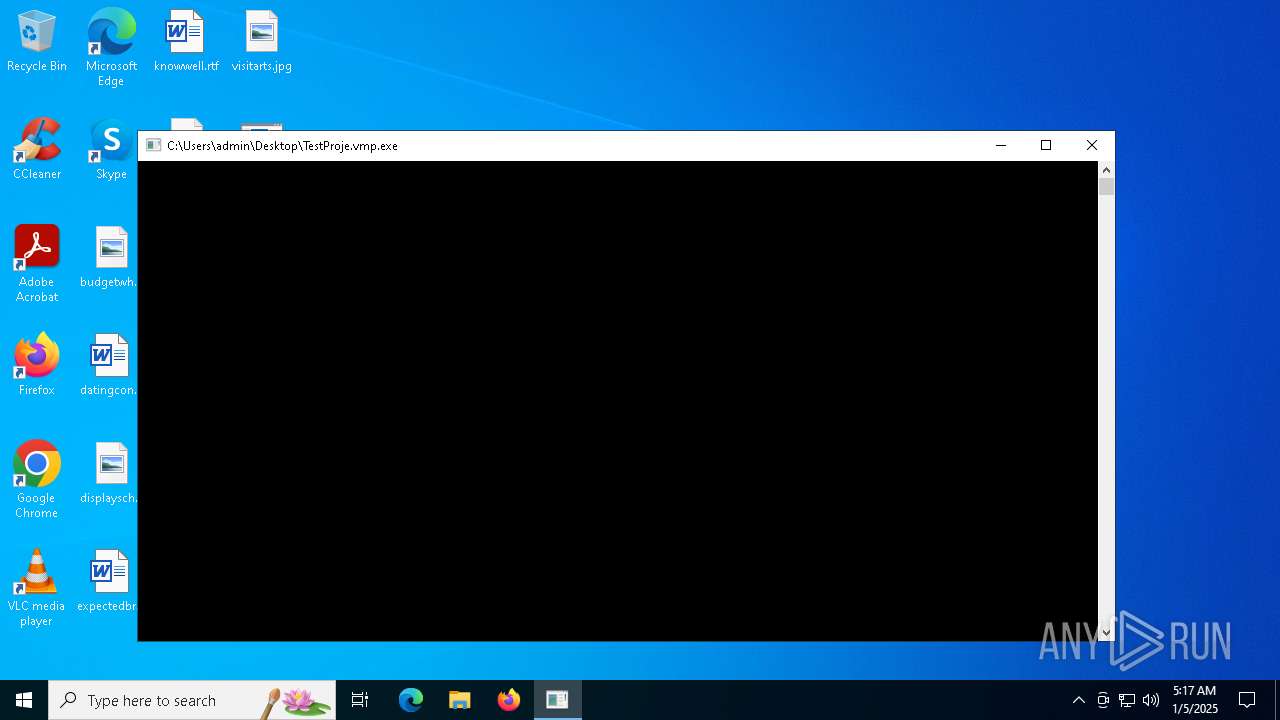
| Analysis date: | January 05, 2025, 05:17:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 1DA2EC7E1B5076CB997E50AAC57AD772 |
| SHA1: | CF5D54EE81D8387059A6384AFFF41252043A36F0 |
| SHA256: | 0E74423A870BA00F4C02E8D87CD39E23BAEF93A5A74FFAABB845D49224C15A68 |
| SSDEEP: | 49152:1M2AkEZnjDmnr6SYm1qx6/x1zi8AQsBj:1hAkEZnO6bm1q5 |
MALICIOUS
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6904)
- cmd.exe (PID: 6680)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 6336)
- cmd.exe (PID: 6616)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6764)
- cmd.exe (PID: 6560)
- cmd.exe (PID: 2956)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 5320)
- cmd.exe (PID: 3060)
- cmd.exe (PID: 436)
SUSPICIOUS
Hides command output
- cmd.exe (PID: 6564)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6904)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 6792)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 6264)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 5880)
- cmd.exe (PID: 628)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 5592)
- cmd.exe (PID: 3988)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 5568)
- cmd.exe (PID: 436)
- cmd.exe (PID: 6680)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6560)
- cmd.exe (PID: 6616)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 6764)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 7124)
- cmd.exe (PID: 2956)
- cmd.exe (PID: 6912)
- cmd.exe (PID: 5320)
- cmd.exe (PID: 3060)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 6280)
- cmd.exe (PID: 2548)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 6336)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 6200)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6456)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 6264)
- cmd.exe (PID: 5880)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 5592)
- cmd.exe (PID: 3988)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 5568)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 6912)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 7124)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 2548)
- cmd.exe (PID: 6200)
- cmd.exe (PID: 628)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 6652)
Starts CMD.EXE for commands execution
- TestProje.vmp.exe (PID: 6392)
- cmd.exe (PID: 3420)
Application launched itself
- cmd.exe (PID: 3420)
Reads security settings of Internet Explorer
- TestProje.vmp.exe (PID: 6392)
Starts SC.EXE for service management
- cmd.exe (PID: 4548)
- cmd.exe (PID: 6280)
Stops a currently running service
- sc.exe (PID: 6268)
- sc.exe (PID: 6244)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2600)
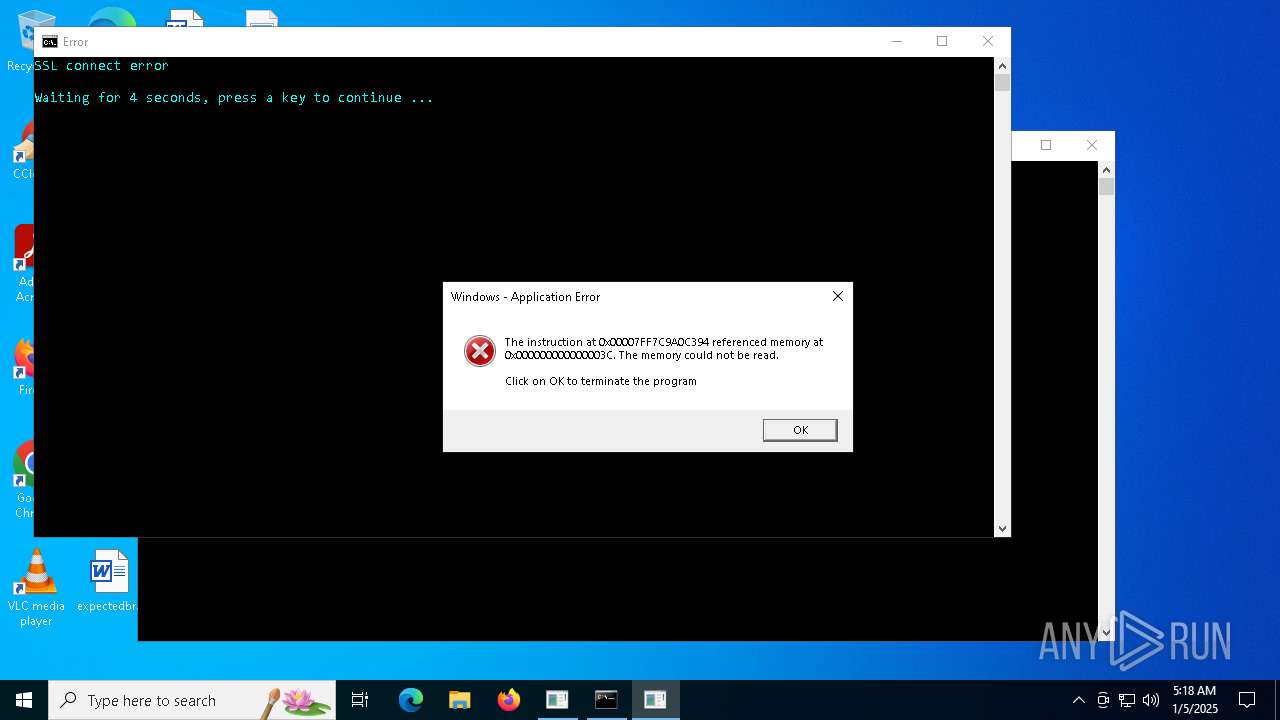
Executes application which crashes
- TestProje.vmp.exe (PID: 6392)
INFO
Checks supported languages
- TestProje.vmp.exe (PID: 6392)
Sends debugging messages
- TestProje.vmp.exe (PID: 6392)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 4136)
Reads the computer name
- TestProje.vmp.exe (PID: 6392)
Checks proxy server information
- TestProje.vmp.exe (PID: 6392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:12:10 17:39:50+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 805888 |
| InitializedDataSize: | 311808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc1ec4 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
227
Monitored processes
108
Malicious processes
1
Suspicious processes
19
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im OllyDbg.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | TestProje.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im cheatengine-x86_64.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | TestProje.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | find /i /v "md5" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im Xenos32.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | TestProje.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | taskkill /f /im de4dot.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | taskkill /FI "IMAGENAME eq httpdebugger*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2548 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq cheatengine*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | TestProje.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
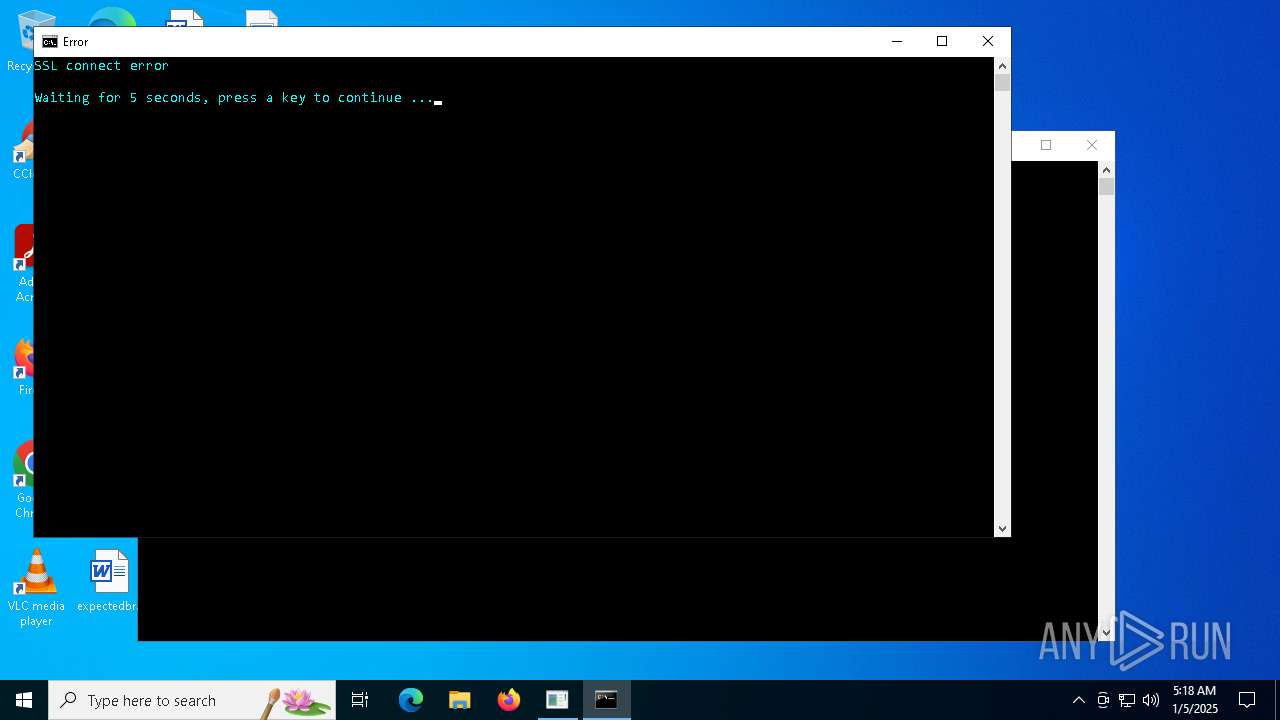
| 2600 | cmd /C "color b && title Error && echo SSL connect error && timeout /t 5" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2956 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im HTTPDebuggerUI.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | TestProje.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 621
Read events
5 618
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6392) TestProje.vmp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6392) TestProje.vmp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6392) TestProje.vmp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1688 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1688 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
1688 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1688 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1688 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
keyauth.win |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
6392 | TestProje.vmp.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
Process | Message |
|---|---|
TestProje.vmp.exe | leksa |
TestProje.vmp.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
TestProje.vmp.exe | RuzyCheats Security |
TestProje.vmp.exe | RuzyCheats Security |