| download: | /FMRS.exe |
| Full analysis: | https://app.any.run/tasks/58c5f6ec-0193-4853-98f0-6b4e940157e3 |
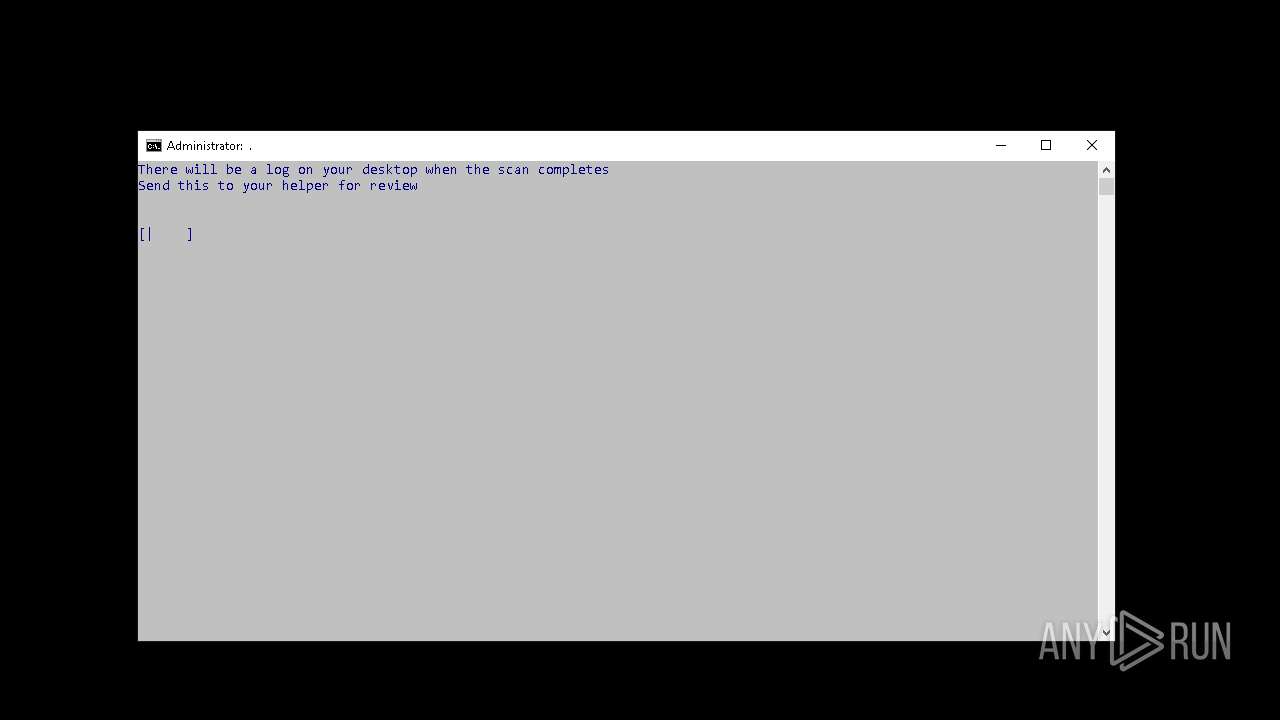
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | December 19, 2024, 08:13:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 04F9C2B48B4369A3CCBC4D36DEA4745A |
| SHA1: | 24AE9FDC2A75EDFBB46ED2AE290FFCBA737D0063 |
| SHA256: | 0E704F2E222F7E18972D41D29802CE3EAA26B27CC0882309F11D0538FB7D7911 |
| SSDEEP: | 49152:2fiEC71DD7npYnsQWQOTjw+nqHMzPQyRfLPrPFPml+9uD0Hz4mJ0zr4n1m7GtKiy:2fiEG1DD7qnspQOTjw+naMzpRfLBPmYk |
MALICIOUS
Opens a text file (SCRIPT)
- cscript.exe (PID: 3140)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 6800)
- net.exe (PID: 308)
Starts CertUtil for downloading files
- cmd.exe (PID: 6800)
SUSPICIOUS
Executable content was dropped or overwritten
- FMRS.exe (PID: 6696)
- cmd.exe (PID: 6800)
Starts CMD.EXE for commands execution
- FMRS.exe (PID: 6696)
- cmd.exe (PID: 6800)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6800)
Application launched itself
- cmd.exe (PID: 6800)
Reads security settings of Internet Explorer
- FMRS.exe (PID: 6696)
Hides command output
- cmd.exe (PID: 4932)
Executing commands from a ".bat" file
- FMRS.exe (PID: 6696)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6800)
Identifying current user with WHOAMI command
- cmd.exe (PID: 6800)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 6800)
- net.exe (PID: 4264)
Searches for installed software
- dllhost.exe (PID: 372)
Executes as Windows Service
- VSSVC.exe (PID: 4520)
The process executes VB scripts
- cmd.exe (PID: 6800)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 3140)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 3140)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 3140)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 3140)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6800)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 3140)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 3140)
Get information on the list of running processes
- cmd.exe (PID: 6800)
Uses WEVTUTIL.EXE to get a list of log names
- cmd.exe (PID: 6800)
Uses WEVTUTIL.EXE to cleanup log
- cmd.exe (PID: 6800)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 6800)
Lists all scheduled tasks
- schtasks.exe (PID: 2524)
- schtasks.exe (PID: 6696)
- schtasks.exe (PID: 6700)
- schtasks.exe (PID: 5508)
- schtasks.exe (PID: 1144)
- schtasks.exe (PID: 3100)
- schtasks.exe (PID: 4872)
- schtasks.exe (PID: 3096)
- schtasks.exe (PID: 4108)
- schtasks.exe (PID: 5792)
- schtasks.exe (PID: 5108)
- schtasks.exe (PID: 5144)
- schtasks.exe (PID: 1152)
- schtasks.exe (PID: 2728)
- schtasks.exe (PID: 1752)
- schtasks.exe (PID: 4992)
- schtasks.exe (PID: 6160)
- schtasks.exe (PID: 5892)
- schtasks.exe (PID: 5604)
- schtasks.exe (PID: 5056)
- schtasks.exe (PID: 5132)
- schtasks.exe (PID: 2880)
- schtasks.exe (PID: 4968)
- schtasks.exe (PID: 4564)
- schtasks.exe (PID: 6300)
- schtasks.exe (PID: 792)
- schtasks.exe (PID: 5248)
- schtasks.exe (PID: 4852)
- schtasks.exe (PID: 6048)
- schtasks.exe (PID: 4860)
- schtasks.exe (PID: 7080)
- schtasks.exe (PID: 4900)
- schtasks.exe (PID: 2992)
- schtasks.exe (PID: 3912)
- schtasks.exe (PID: 4504)
- schtasks.exe (PID: 6676)
- schtasks.exe (PID: 4224)
- schtasks.exe (PID: 6952)
- schtasks.exe (PID: 5952)
- schtasks.exe (PID: 768)
- schtasks.exe (PID: 5164)
- schtasks.exe (PID: 6904)
- schtasks.exe (PID: 6712)
- schtasks.exe (PID: 6760)
- schtasks.exe (PID: 5888)
- schtasks.exe (PID: 6168)
- schtasks.exe (PID: 6308)
- schtasks.exe (PID: 4408)
- schtasks.exe (PID: 4804)
- schtasks.exe (PID: 2884)
- schtasks.exe (PID: 5364)
- schtasks.exe (PID: 5584)
- schtasks.exe (PID: 1140)
- schtasks.exe (PID: 3284)
- schtasks.exe (PID: 5160)
- schtasks.exe (PID: 5808)
- schtasks.exe (PID: 4120)
- schtasks.exe (PID: 900)
- schtasks.exe (PID: 4944)
- schtasks.exe (PID: 2744)
- schtasks.exe (PID: 6656)
- schtasks.exe (PID: 5040)
- schtasks.exe (PID: 5060)
- schtasks.exe (PID: 5368)
- schtasks.exe (PID: 2976)
- schtasks.exe (PID: 4548)
- schtasks.exe (PID: 4748)
- schtasks.exe (PID: 1112)
- schtasks.exe (PID: 940)
- schtasks.exe (PID: 4808)
- schtasks.exe (PID: 4856)
- schtasks.exe (PID: 5216)
- schtasks.exe (PID: 5912)
- schtasks.exe (PID: 2996)
- schtasks.exe (PID: 4924)
- schtasks.exe (PID: 7096)
- schtasks.exe (PID: 5236)
- schtasks.exe (PID: 6156)
- schtasks.exe (PID: 6868)
- schtasks.exe (PID: 5404)
- schtasks.exe (PID: 6936)
- schtasks.exe (PID: 6368)
- schtasks.exe (PID: 5192)
- schtasks.exe (PID: 5164)
- schtasks.exe (PID: 6628)
- schtasks.exe (PID: 6712)
- schtasks.exe (PID: 6644)
- schtasks.exe (PID: 5952)
- schtasks.exe (PID: 6760)
- schtasks.exe (PID: 6168)
- schtasks.exe (PID: 4408)
- schtasks.exe (PID: 6776)
- schtasks.exe (PID: 6308)
- schtasks.exe (PID: 4804)
- schtasks.exe (PID: 6324)
- schtasks.exe (PID: 5152)
- schtasks.exe (PID: 1140)
- schtasks.exe (PID: 3284)
- schtasks.exe (PID: 5068)
- schtasks.exe (PID: 1296)
- schtasks.exe (PID: 1512)
- schtasks.exe (PID: 5108)
- schtasks.exe (PID: 5408)
- schtasks.exe (PID: 1828)
- schtasks.exe (PID: 3224)
- schtasks.exe (PID: 1052)
- schtasks.exe (PID: 5052)
- schtasks.exe (PID: 5132)
- schtasks.exe (PID: 1876)
- schtasks.exe (PID: 4692)
- schtasks.exe (PID: 5696)
- schtasks.exe (PID: 5328)
- schtasks.exe (PID: 4812)
- schtasks.exe (PID: 4756)
- schtasks.exe (PID: 5276)
- schtasks.exe (PID: 2908)
- schtasks.exe (PID: 520)
- schtasks.exe (PID: 6196)
- schtasks.exe (PID: 4648)
- schtasks.exe (PID: 6096)
- schtasks.exe (PID: 4820)
- schtasks.exe (PID: 2548)
- schtasks.exe (PID: 4116)
- schtasks.exe (PID: 6260)
- schtasks.exe (PID: 6716)
- schtasks.exe (PID: 5360)
- schtasks.exe (PID: 2224)
- schtasks.exe (PID: 6864)
- schtasks.exe (PID: 3732)
- schtasks.exe (PID: 6612)
- schtasks.exe (PID: 6728)
- schtasks.exe (PID: 6312)
- schtasks.exe (PID: 3444)
- schtasks.exe (PID: 536)
- schtasks.exe (PID: 2888)
- schtasks.exe (PID: 6904)
- schtasks.exe (PID: 3900)
- schtasks.exe (PID: 4800)
- schtasks.exe (PID: 5280)
- schtasks.exe (PID: 5652)
- schtasks.exe (PID: 5116)
- schtasks.exe (PID: 5440)
- schtasks.exe (PID: 3236)
- schtasks.exe (PID: 5268)
- schtasks.exe (PID: 5828)
- schtasks.exe (PID: 3144)
- schtasks.exe (PID: 3140)
- schtasks.exe (PID: 5632)
- schtasks.exe (PID: 6744)
- schtasks.exe (PID: 2148)
- schtasks.exe (PID: 3620)
- schtasks.exe (PID: 6748)
- schtasks.exe (PID: 5700)
- schtasks.exe (PID: 4776)
- schtasks.exe (PID: 3820)
- schtasks.exe (PID: 4764)
- schtasks.exe (PID: 5016)
- schtasks.exe (PID: 940)
- schtasks.exe (PID: 4732)
- schtasks.exe (PID: 4788)
- schtasks.exe (PID: 2260)
- schtasks.exe (PID: 3632)
- schtasks.exe (PID: 4468)
- schtasks.exe (PID: 5388)
- schtasks.exe (PID: 6888)
- schtasks.exe (PID: 5332)
- schtasks.exe (PID: 4848)
- schtasks.exe (PID: 4892)
- schtasks.exe (PID: 5404)
- schtasks.exe (PID: 5296)
- schtasks.exe (PID: 1380)
- schtasks.exe (PID: 6408)
- schtasks.exe (PID: 4224)
- schtasks.exe (PID: 6948)
- schtasks.exe (PID: 6752)
- schtasks.exe (PID: 536)
- schtasks.exe (PID: 4428)
- schtasks.exe (PID: 5268)
- schtasks.exe (PID: 5760)
- schtasks.exe (PID: 3236)
- schtasks.exe (PID: 6296)
- schtasks.exe (PID: 1016)
- schtasks.exe (PID: 6916)
- schtasks.exe (PID: 6704)
- schtasks.exe (PID: 436)
- schtasks.exe (PID: 5280)
- schtasks.exe (PID: 5116)
- schtasks.exe (PID: 5440)
- schtasks.exe (PID: 5632)
- schtasks.exe (PID: 6744)
- schtasks.exe (PID: 2148)
- schtasks.exe (PID: 4144)
- schtasks.exe (PID: 5340)
- schtasks.exe (PID: 2800)
- schtasks.exe (PID: 5652)
- schtasks.exe (PID: 5680)
- schtasks.exe (PID: 716)
- schtasks.exe (PID: 2668)
- schtasks.exe (PID: 5064)
- schtasks.exe (PID: 5060)
- schtasks.exe (PID: 5368)
- schtasks.exe (PID: 6184)
- schtasks.exe (PID: 6012)
- schtasks.exe (PID: 1516)
- schtasks.exe (PID: 4708)
- schtasks.exe (PID: 6368)
- schtasks.exe (PID: 4940)
- schtasks.exe (PID: 3912)
- schtasks.exe (PID: 4808)
- schtasks.exe (PID: 6200)
- schtasks.exe (PID: 5228)
- schtasks.exe (PID: 6172)
- schtasks.exe (PID: 6816)
- schtasks.exe (PID: 6404)
- schtasks.exe (PID: 3080)
- schtasks.exe (PID: 6872)
- schtasks.exe (PID: 2200)
- schtasks.exe (PID: 4800)
- schtasks.exe (PID: 6312)
- schtasks.exe (PID: 6728)
- schtasks.exe (PID: 6940)
- schtasks.exe (PID: 3564)
- schtasks.exe (PID: 6952)
- schtasks.exe (PID: 5952)
- schtasks.exe (PID: 1760)
- schtasks.exe (PID: 5768)
- schtasks.exe (PID: 1612)
- schtasks.exe (PID: 1140)
- schtasks.exe (PID: 3096)
- schtasks.exe (PID: 5068)
- schtasks.exe (PID: 5928)
- schtasks.exe (PID: 5152)
- schtasks.exe (PID: 736)
- schtasks.exe (PID: 5108)
- schtasks.exe (PID: 5408)
- schtasks.exe (PID: 2212)
Lists all scheduled tasks in specific format
- schtasks.exe (PID: 2940)
The process executes via Task Scheduler
- explorer.exe (PID: 3284)
INFO
The process uses the downloaded file
- powershell.exe (PID: 6864)
Checks supported languages
- FMRS.exe (PID: 6696)
- grep.exe (PID: 5300)
- sed.exe (PID: 4128)
- grep.exe (PID: 2148)
- grep.exe (PID: 3188)
- nircmd.exe (PID: 1804)
- grep.exe (PID: 1904)
- grep.exe (PID: 4604)
- sort_.exe (PID: 3560)
- sed.exe (PID: 6892)
- grep.exe (PID: 6868)
- grep.exe (PID: 2612)
- grep.exe (PID: 4860)
- grep.exe (PID: 5084)
- grep.exe (PID: 6956)
- grep.exe (PID: 4400)
- grep.exe (PID: 3560)
- grep.exe (PID: 6208)
- OfficeClickToRun.exe (PID: 2216)
- grep.exe (PID: 6648)
- grep.exe (PID: 6108)
- grep.exe (PID: 6948)
- grep.exe (PID: 5400)
- grep.exe (PID: 7052)
- grep.exe (PID: 6600)
- grep.exe (PID: 3864)
- grep.exe (PID: 1356)
- grep.exe (PID: 6736)
- grep.exe (PID: 7136)
- grep.exe (PID: 5512)
- grep.exe (PID: 736)
- grep.exe (PID: 2888)
- grep.exe (PID: 3456)
- grep.exe (PID: 2792)
- grep.exe (PID: 5284)
- grep.exe (PID: 4848)
- grep.exe (PID: 2996)
- grep.exe (PID: 7080)
- grep.exe (PID: 4556)
- sed.exe (PID: 4888)
- grep.exe (PID: 5564)
- grep.exe (PID: 6648)
- grep.exe (PID: 5888)
- grep.exe (PID: 6712)
- sed.exe (PID: 1016)
- sort_.exe (PID: 3864)
- grep.exe (PID: 5988)
- grep.exe (PID: 436)
- grep.exe (PID: 3116)
- grep.exe (PID: 5116)
- grep.exe (PID: 3060)
- grep.exe (PID: 5088)
- grep.exe (PID: 5632)
- grep.exe (PID: 3176)
- grep.exe (PID: 3532)
- grep.exe (PID: 2796)
- grep.exe (PID: 440)
- grep.exe (PID: 5440)
- grep.exe (PID: 3540)
- grep.exe (PID: 808)
- grep.exe (PID: 5032)
- grep.exe (PID: 5540)
- grep.exe (PID: 6164)
- grep.exe (PID: 4832)
- grep.exe (PID: 4916)
- grep.exe (PID: 4492)
- grep.exe (PID: 4628)
- grep.exe (PID: 6892)
- grep.exe (PID: 3688)
- grep.exe (PID: 6404)
- grep.exe (PID: 5196)
- grep.exe (PID: 7048)
- grep.exe (PID: 640)
- grep.exe (PID: 2200)
- grep.exe (PID: 2220)
- grep.exe (PID: 6796)
- grep.exe (PID: 3100)
- grep.exe (PID: 3456)
- grep.exe (PID: 4132)
- grep.exe (PID: 5280)
- grep.exe (PID: 5812)
- grep.exe (PID: 3180)
- grep.exe (PID: 6148)
- grep.exe (PID: 5316)
- grep.exe (PID: 1596)
- grep.exe (PID: 5336)
- grep.exe (PID: 3944)
- grep.exe (PID: 4640)
- grep.exe (PID: 2980)
- grep.exe (PID: 6200)
- grep.exe (PID: 4784)
- grep.exe (PID: 4780)
- grep.exe (PID: 4892)
- grep.exe (PID: 4468)
- grep.exe (PID: 6888)
- grep.exe (PID: 5388)
- grep.exe (PID: 6816)
- grep.exe (PID: 1344)
- grep.exe (PID: 3688)
- grep.exe (PID: 6872)
- grep.exe (PID: 6568)
- grep.exe (PID: 1380)
- grep.exe (PID: 6304)
- grep.exe (PID: 6700)
- grep.exe (PID: 188)
- grep.exe (PID: 3128)
- grep.exe (PID: 1540)
- grep.exe (PID: 5944)
- grep.exe (PID: 5364)
- grep.exe (PID: 2124)
- grep.exe (PID: 3448)
- grep.exe (PID: 2884)
- grep.exe (PID: 6668)
- grep.exe (PID: 4128)
- grep.exe (PID: 5808)
- grep.exe (PID: 4500)
- grep.exe (PID: 2600)
- grep.exe (PID: 2384)
- grep.exe (PID: 5472)
- grep.exe (PID: 4996)
- grep.exe (PID: 716)
- grep.exe (PID: 3288)
- grep.exe (PID: 2076)
- grep.exe (PID: 4632)
- grep.exe (PID: 5224)
- grep.exe (PID: 6036)
- grep.exe (PID: 4264)
- grep.exe (PID: 2324)
- grep.exe (PID: 308)
- grep.exe (PID: 7068)
- grep.exe (PID: 6648)
- grep.exe (PID: 5908)
- grep.exe (PID: 2776)
- grep.exe (PID: 6672)
- grep.exe (PID: 6712)
- grep.exe (PID: 6760)
- grep.exe (PID: 4336)
- grep.exe (PID: 5004)
- grep.exe (PID: 3096)
- grep.exe (PID: 5596)
- grep.exe (PID: 4120)
- grep.exe (PID: 7028)
- grep.exe (PID: 1488)
- grep.exe (PID: 5552)
- grep.exe (PID: 908)
- grep.exe (PID: 4088)
- grep.exe (PID: 6204)
- grep.exe (PID: 4040)
- grep.exe (PID: 7072)
- grep.exe (PID: 4836)
- grep.exe (PID: 6652)
- grep.exe (PID: 5196)
- grep.exe (PID: 6764)
- grep.exe (PID: 3808)
- grep.exe (PID: 4408)
- grep.exe (PID: 2524)
- grep.exe (PID: 5516)
- grep.exe (PID: 5648)
- grep.exe (PID: 6356)
- grep.exe (PID: 5004)
- grep.exe (PID: 4132)
- grep.exe (PID: 3052)
- grep.exe (PID: 6748)
- grep.exe (PID: 3820)
- grep.exe (PID: 4848)
- grep.exe (PID: 4788)
- grep.exe (PID: 5332)
- grep.exe (PID: 6308)
- grep.exe (PID: 3696)
- grep.exe (PID: 716)
- grep.exe (PID: 1052)
- grep.exe (PID: 5132)
- grep.exe (PID: 4264)
- grep.exe (PID: 1868)
- grep.exe (PID: 4220)
- grep.exe (PID: 4880)
- grep.exe (PID: 6068)
- grep.exe (PID: 6292)
- grep.exe (PID: 2776)
- grep.exe (PID: 5284)
- grep.exe (PID: 5224)
- grep.exe (PID: 6740)
- grep.exe (PID: 6608)
- grep.exe (PID: 3220)
- grep.exe (PID: 5888)
- grep.exe (PID: 1684)
- grep.exe (PID: 3732)
- grep.exe (PID: 5956)
- grep.exe (PID: 5232)
- sort_.exe (PID: 6284)
- sort_.exe (PID: 5632)
- sort_.exe (PID: 6656)
- grep.exe (PID: 4604)
- grep.exe (PID: 536)
- sort_.exe (PID: 2792)
- grep.exe (PID: 3548)
- grep.exe (PID: 6012)
- grep.exe (PID: 4764)
- grep.exe (PID: 4608)
- sort_.exe (PID: 4388)
- grep.exe (PID: 808)
- sort_.exe (PID: 4088)
- grep.exe (PID: 4732)
- grep.exe (PID: 424)
- sort_.exe (PID: 4940)
- grep.exe (PID: 4648)
- grep.exe (PID: 5720)
- grep.exe (PID: 6652)
- sort_.exe (PID: 6688)
- grep.exe (PID: 6612)
- grep.exe (PID: 6376)
- sort_.exe (PID: 4916)
- grep.exe (PID: 6156)
- grep.exe (PID: 6740)
- sort_.exe (PID: 6168)
- sort_.exe (PID: 1144)
- TextInputHost.exe (PID: 908)
- StartMenuExperienceHost.exe (PID: 5796)
- SearchApp.exe (PID: 4040)
- grep.exe (PID: 6628)
The sample compiled with english language support
- cmd.exe (PID: 6800)
- FMRS.exe (PID: 6696)
Process checks computer location settings
- FMRS.exe (PID: 6696)
- StartMenuExperienceHost.exe (PID: 5796)
- SearchApp.exe (PID: 4040)
Reads the computer name
- FMRS.exe (PID: 6696)
- nircmd.exe (PID: 1804)
- OfficeClickToRun.exe (PID: 2216)
Sends debugging messages
- grep.exe (PID: 5300)
- grep.exe (PID: 2148)
- grep.exe (PID: 1904)
- grep.exe (PID: 4604)
- grep.exe (PID: 3912)
- grep.exe (PID: 6868)
- grep.exe (PID: 2612)
- grep.exe (PID: 6956)
- grep.exe (PID: 4752)
- grep.exe (PID: 4860)
- grep.exe (PID: 5084)
- grep.exe (PID: 1556)
- grep.exe (PID: 4400)
- grep.exe (PID: 3912)
- grep.exe (PID: 3560)
- grep.exe (PID: 6108)
- grep.exe (PID: 6648)
- grep.exe (PID: 6600)
- grep.exe (PID: 6948)
- grep.exe (PID: 7052)
- grep.exe (PID: 5400)
- grep.exe (PID: 3864)
- grep.exe (PID: 6736)
- grep.exe (PID: 1356)
- grep.exe (PID: 6208)
- grep.exe (PID: 5512)
- grep.exe (PID: 736)
- grep.exe (PID: 2888)
- grep.exe (PID: 7136)
- grep.exe (PID: 3456)
- grep.exe (PID: 2792)
- grep.exe (PID: 5284)
- grep.exe (PID: 4848)
- grep.exe (PID: 2996)
- grep.exe (PID: 4556)
- grep.exe (PID: 7080)
- grep.exe (PID: 5564)
- grep.exe (PID: 6648)
- grep.exe (PID: 6712)
- grep.exe (PID: 5888)
- grep.exe (PID: 6732)
- grep.exe (PID: 3896)
- grep.exe (PID: 5988)
- grep.exe (PID: 5944)
- grep.exe (PID: 436)
- grep.exe (PID: 3116)
- grep.exe (PID: 5652)
- grep.exe (PID: 5116)
- grep.exe (PID: 3060)
- grep.exe (PID: 5440)
- grep.exe (PID: 5088)
- grep.exe (PID: 5632)
- grep.exe (PID: 3176)
- grep.exe (PID: 2928)
- grep.exe (PID: 3532)
- grep.exe (PID: 440)
- grep.exe (PID: 2796)
- grep.exe (PID: 3540)
- grep.exe (PID: 808)
- grep.exe (PID: 5032)
- grep.exe (PID: 5064)
- grep.exe (PID: 5624)
- grep.exe (PID: 5540)
- grep.exe (PID: 4560)
- grep.exe (PID: 2612)
- grep.exe (PID: 6164)
- grep.exe (PID: 4832)
- grep.exe (PID: 4492)
- grep.exe (PID: 4388)
- grep.exe (PID: 4628)
- grep.exe (PID: 3992)
- grep.exe (PID: 4916)
- grep.exe (PID: 6864)
- grep.exe (PID: 6892)
- grep.exe (PID: 6708)
- grep.exe (PID: 3688)
- grep.exe (PID: 6404)
- grep.exe (PID: 3832)
- grep.exe (PID: 5196)
- grep.exe (PID: 7048)
- grep.exe (PID: 640)
- grep.exe (PID: 1400)
- grep.exe (PID: 6568)
- grep.exe (PID: 2200)
- grep.exe (PID: 6812)
- grep.exe (PID: 2220)
- grep.exe (PID: 6796)
- grep.exe (PID: 5812)
- grep.exe (PID: 5928)
- grep.exe (PID: 3100)
- grep.exe (PID: 3456)
- grep.exe (PID: 4132)
- grep.exe (PID: 5280)
- grep.exe (PID: 3180)
- grep.exe (PID: 5104)
- grep.exe (PID: 5748)
- grep.exe (PID: 5960)
- grep.exe (PID: 6996)
- grep.exe (PID: 1512)
- grep.exe (PID: 6148)
- grep.exe (PID: 5680)
- grep.exe (PID: 5316)
- grep.exe (PID: 1048)
- grep.exe (PID: 2100)
- grep.exe (PID: 4640)
- grep.exe (PID: 2980)
- grep.exe (PID: 1596)
- grep.exe (PID: 3944)
- grep.exe (PID: 3932)
- grep.exe (PID: 4784)
- grep.exe (PID: 4780)
- grep.exe (PID: 3632)
- grep.exe (PID: 4892)
- grep.exe (PID: 6200)
- grep.exe (PID: 5388)
- grep.exe (PID: 6816)
- grep.exe (PID: 1344)
- grep.exe (PID: 6708)
- grep.exe (PID: 4468)
- grep.exe (PID: 6888)
- grep.exe (PID: 1380)
- grep.exe (PID: 5196)
- grep.exe (PID: 6568)
- grep.exe (PID: 6872)
- grep.exe (PID: 3688)
- grep.exe (PID: 5932)
- grep.exe (PID: 1540)
- grep.exe (PID: 3128)
- grep.exe (PID: 6304)
- grep.exe (PID: 6700)
- grep.exe (PID: 1888)
- grep.exe (PID: 2124)
- grep.exe (PID: 2884)
- grep.exe (PID: 4500)
- grep.exe (PID: 396)
- grep.exe (PID: 2600)
- grep.exe (PID: 5808)
- grep.exe (PID: 2384)
- grep.exe (PID: 3288)
- grep.exe (PID: 4996)
- grep.exe (PID: 5224)
- grep.exe (PID: 6036)
- grep.exe (PID: 7068)
- grep.exe (PID: 2324)
- grep.exe (PID: 4504)
- grep.exe (PID: 4900)
- grep.exe (PID: 6212)
- grep.exe (PID: 5908)
- grep.exe (PID: 2776)
- grep.exe (PID: 6672)
- grep.exe (PID: 5336)
- grep.exe (PID: 5508)
- grep.exe (PID: 4336)
- grep.exe (PID: 2440)
- grep.exe (PID: 6776)
- grep.exe (PID: 5004)
- grep.exe (PID: 5420)
- grep.exe (PID: 908)
- grep.exe (PID: 3108)
- grep.exe (PID: 3096)
- grep.exe (PID: 7144)
- grep.exe (PID: 5740)
- grep.exe (PID: 776)
- grep.exe (PID: 4120)
- grep.exe (PID: 5544)
- grep.exe (PID: 6204)
- grep.exe (PID: 1112)
- grep.exe (PID: 4040)
- grep.exe (PID: 4444)
- grep.exe (PID: 5220)
- grep.exe (PID: 4896)
- grep.exe (PID: 4836)
- grep.exe (PID: 4780)
- grep.exe (PID: 3688)
- grep.exe (PID: 5932)
- grep.exe (PID: 5360)
- grep.exe (PID: 5196)
- grep.exe (PID: 5712)
- grep.exe (PID: 6108)
- grep.exe (PID: 2524)
- grep.exe (PID: 848)
- grep.exe (PID: 3060)
- grep.exe (PID: 3052)
- grep.exe (PID: 4132)
- grep.exe (PID: 2928)
- grep.exe (PID: 2744)
- grep.exe (PID: 6748)
- grep.exe (PID: 5700)
- grep.exe (PID: 3820)
- grep.exe (PID: 4776)
- grep.exe (PID: 2260)
- grep.exe (PID: 7096)
- grep.exe (PID: 4848)
- grep.exe (PID: 7148)
- grep.exe (PID: 5164)
- grep.exe (PID: 6904)
- grep.exe (PID: 640)
- grep.exe (PID: 6640)
- grep.exe (PID: 5956)
- grep.exe (PID: 3440)
- grep.exe (PID: 2888)
- grep.exe (PID: 6988)
- grep.exe (PID: 4124)
- grep.exe (PID: 5572)
- grep.exe (PID: 3552)
- grep.exe (PID: 4944)
- grep.exe (PID: 5052)
- grep.exe (PID: 5132)
- grep.exe (PID: 2756)
- grep.exe (PID: 1152)
- grep.exe (PID: 3176)
- grep.exe (PID: 1052)
- grep.exe (PID: 6068)
- grep.exe (PID: 6292)
- grep.exe (PID: 2776)
- grep.exe (PID: 4224)
- grep.exe (PID: 4264)
- grep.exe (PID: 5284)
- grep.exe (PID: 4788)
- grep.exe (PID: 5224)
- grep.exe (PID: 6576)
- grep.exe (PID: 6740)
- grep.exe (PID: 6608)
- grep.exe (PID: 5888)
- grep.exe (PID: 1684)
- grep.exe (PID: 536)
- grep.exe (PID: 5956)
- grep.exe (PID: 6960)
- grep.exe (PID: 488)
- grep.exe (PID: 5484)
- grep.exe (PID: 5152)
- grep.exe (PID: 5572)
- grep.exe (PID: 5892)
- grep.exe (PID: 5748)
- grep.exe (PID: 4604)
- grep.exe (PID: 5768)
- grep.exe (PID: 1708)
- grep.exe (PID: 5308)
- grep.exe (PID: 424)
- grep.exe (PID: 4732)
- grep.exe (PID: 4856)
- grep.exe (PID: 4320)
- grep.exe (PID: 5060)
- grep.exe (PID: 2904)
- grep.exe (PID: 6012)
- grep.exe (PID: 6260)
- grep.exe (PID: 6156)
- grep.exe (PID: 6652)
- grep.exe (PID: 6644)
- grep.exe (PID: 6612)
- grep.exe (PID: 6376)
- grep.exe (PID: 4888)
- grep.exe (PID: 4116)
- grep.exe (PID: 4648)
- grep.exe (PID: 6940)
- StartMenuExperienceHost.exe (PID: 5796)
- grep.exe (PID: 6740)
NirSoft software is detected
- nircmd.exe (PID: 1804)
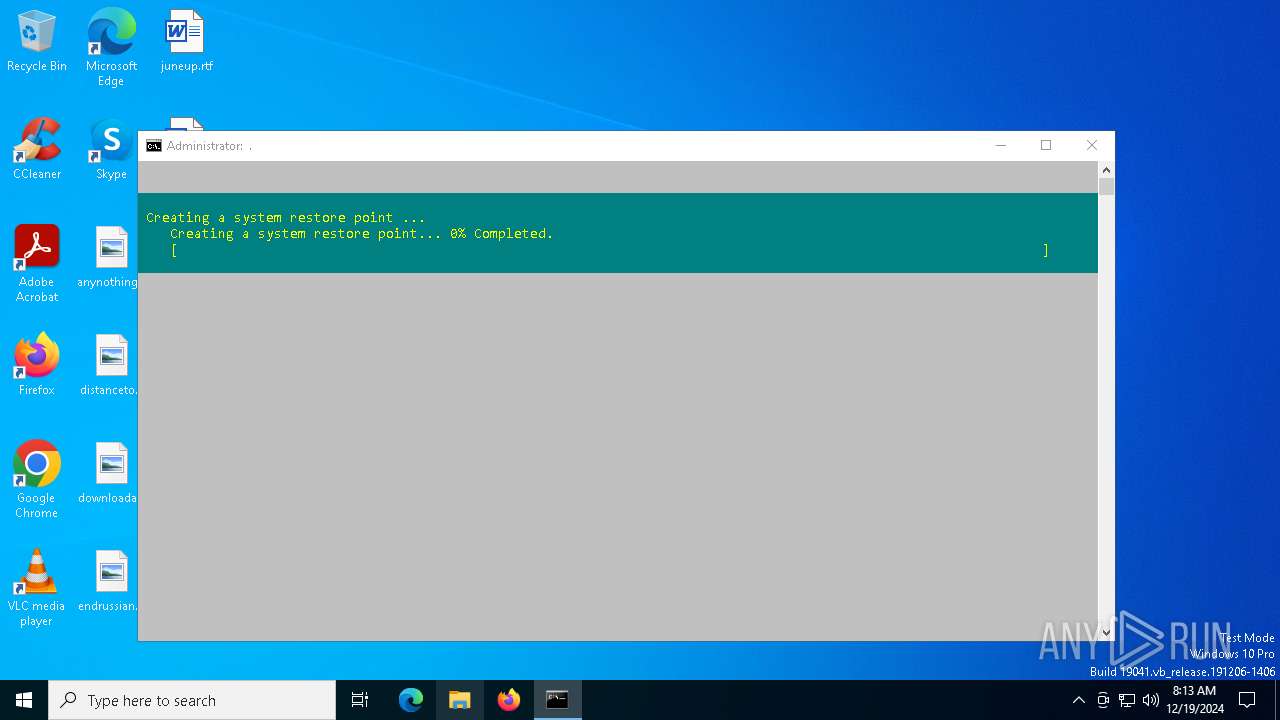
Manages system restore points
- SrTasks.exe (PID: 2744)
Executes as Windows Service
- OfficeClickToRun.exe (PID: 2216)
Reads the machine GUID from the registry
- OfficeClickToRun.exe (PID: 2216)
- SearchApp.exe (PID: 4040)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 2216)
Checks proxy server information
- OfficeClickToRun.exe (PID: 2216)
- explorer.exe (PID: 3284)
Reads security settings of Internet Explorer
- certutil.exe (PID: 5236)
- explorer.exe (PID: 3284)
Reads the software policy settings
- SearchApp.exe (PID: 4040)
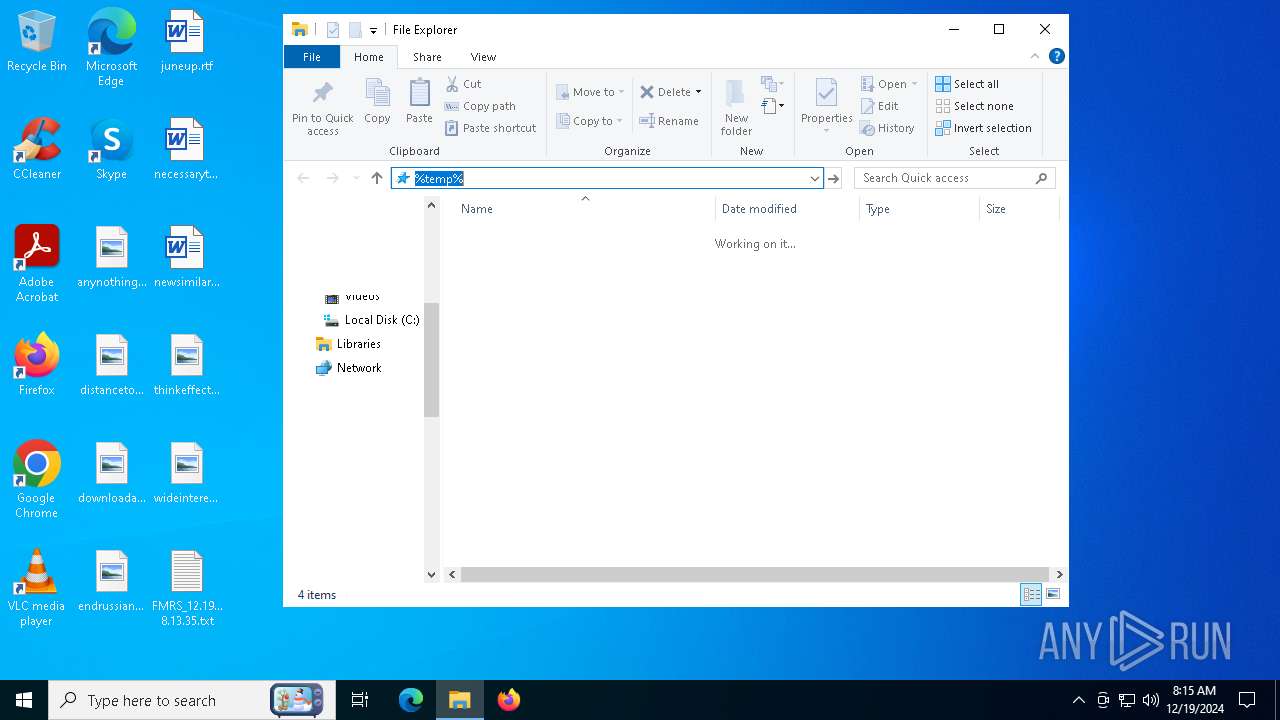
Drops encrypted VBS script (Microsoft Script Encoder)
- explorer.exe (PID: 3284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:06:27 07:06:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 70656 |
| InitializedDataSize: | 235520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11def |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.4.0 |
| ProductVersionNumber: | 3.5.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
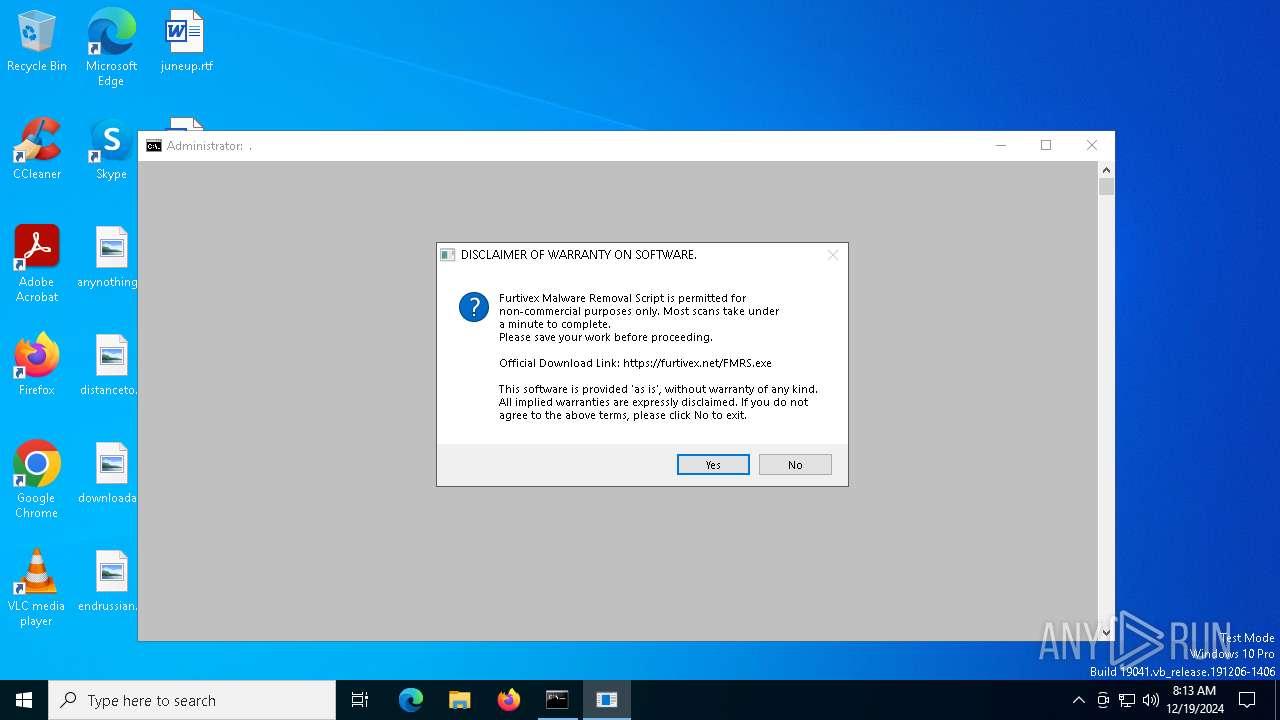
| CompanyName: | Furtivex |
| FileVersion: | 3.5.4 |
| InternalName: | FMRS.exe |
| OriginalFileName: | FMRS.exe |
| ProductName: | Furtivex Malware Removal Script |
| ProductVersion: | 3.5.4 |
Total processes
958
Monitored processes
813
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | TASKKILL /F /IM "dasHost.exe" | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | GREP -Pis "\<Command\>(auditpol|[w|c]script|certutil|mshta|netsh|powershell).*\\(System32|Roaming|Local(Low)?|AppData|WINDOWS|SysWOW64|Public|Program Files( \(x86\))?|Windows NT)\\[A-Z0-9_.-]{1,}\.(bat|com|cmd|jar|jse?|ps1|url|vb[e|s]).*\<\/Command\>f7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Windows\grep.exe | cmd.exe | ||||||||||||
User: admin Company: GnuWin32 <http://gnuwin32.sourceforge.net> Integrity Level: HIGH Description: Grep: print lines matching a pattern Exit code: 1 Version: 2.5.4.3331 Modules
| |||||||||||||||
| 308 | net user John | C:\Windows\SysWOW64\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 308 | GREP -Pis "\<Command\>(auditpol|[w|c]script|certutil|mshta|netsh|powershell).*\\(System32|Roaming|Local(Low)?|AppData|WINDOWS|SysWOW64|Public|Program Files( \(x86\))?|Windows NT)\\[A-Z0-9_.-]{1,}\.(bat|com|cmd|jar|jse?|ps1|url|vb[e|s]).*\<\/Command\>f7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Windows\grep.exe | cmd.exe | ||||||||||||
User: admin Company: GnuWin32 <http://gnuwin32.sourceforge.net> Integrity Level: HIGH Description: Grep: print lines matching a pattern Exit code: 1 Version: 2.5.4.3331 Modules
| |||||||||||||||
| 372 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | GREP -Pis "\<Command\>(auditpol|[w|c]script|certutil|mshta|netsh|powershell).*\\(System32|Roaming|Local(Low)?|AppData|WINDOWS|SysWOW64|Public|Program Files( \(x86\))?|Windows NT)\\[A-Z0-9_.-]{1,}\.(bat|com|cmd|jar|jse?|ps1|url|vb[e|s]).*\<\/Command\>f7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Windows\grep.exe | cmd.exe | ||||||||||||
User: admin Company: GnuWin32 <http://gnuwin32.sourceforge.net> Integrity Level: HIGH Description: Grep: print lines matching a pattern Exit code: 1 Version: 2.5.4.3331 Modules
| |||||||||||||||
| 420 | POWERSHELL -command "Get-BitsTransfer -AllUsers | Where-Object { $_.JobState -CContains 'Error' } | Remove-BitsTransfer" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | GREP -Esi ".*\.(bat|cmd|dll|exe|jar|jse?|pif|ps1|scr|tmp|vb[e|s])f7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Windows\grep.exe | cmd.exe | ||||||||||||
User: admin Company: GnuWin32 <http://gnuwin32.sourceforge.net> Integrity Level: HIGH Description: Grep: print lines matching a pattern Exit code: 1 Version: 2.5.4.3331 Modules
| |||||||||||||||
| 436 | GREP -Pis "\<Command\>(auditpol|[w|c]script|certutil|mshta|netsh|powershell).*\\(System32|Roaming|Local(Low)?|AppData|WINDOWS|SysWOW64|Public|Program Files( \(x86\))?|Windows NT)\\[A-Z0-9_.-]{1,}\.(bat|com|cmd|jar|jse?|ps1|url|vb[e|s]).*\<\/Command\>f7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Windows\grep.exe | cmd.exe | ||||||||||||
User: admin Company: GnuWin32 <http://gnuwin32.sourceforge.net> Integrity Level: HIGH Description: Grep: print lines matching a pattern Exit code: 1 Version: 2.5.4.3331 Modules
| |||||||||||||||
| 436 | SCHTASKS /QUERY /TN "Microsoft\Windows\Task Manager\Interactive" /XML | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
74 407
Read events
73 890
Write events
479
Delete events
38
Modification events
| (PID) Process: | (372) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000000D9D82E7ED51DB017401000008180000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000007FFDC2E7ED51DB017401000008180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000007FFDC2E7ED51DB017401000008180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000A561C5E7ED51DB017401000008180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000C6BAD3E7ED51DB0174010000DC180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000C6BAD3E7ED51DB0174010000DC180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000C6BAD3E7ED51DB0174010000DC180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (4520) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000DC534DE8ED51DB01A81100009C180000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4520) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000DC534DE8ED51DB01A8110000A8010000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
18
Suspicious files
12
Text files
164
Unknown types
0
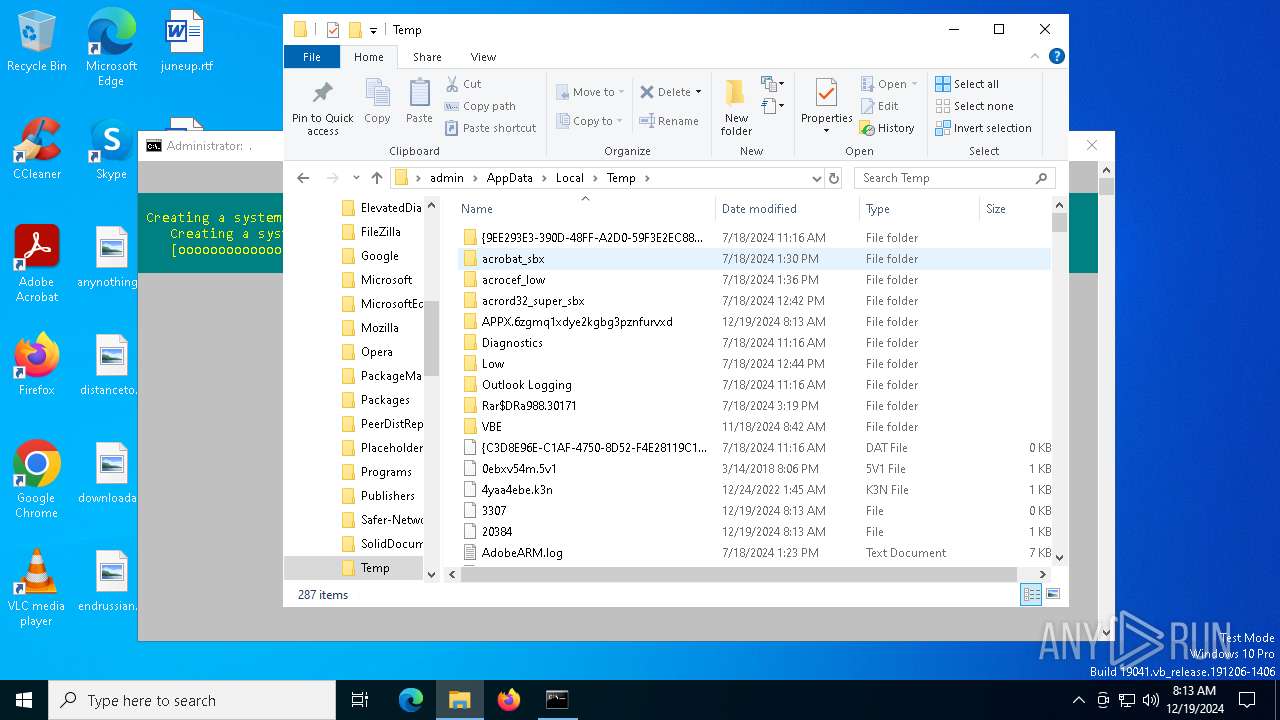
Dropped files
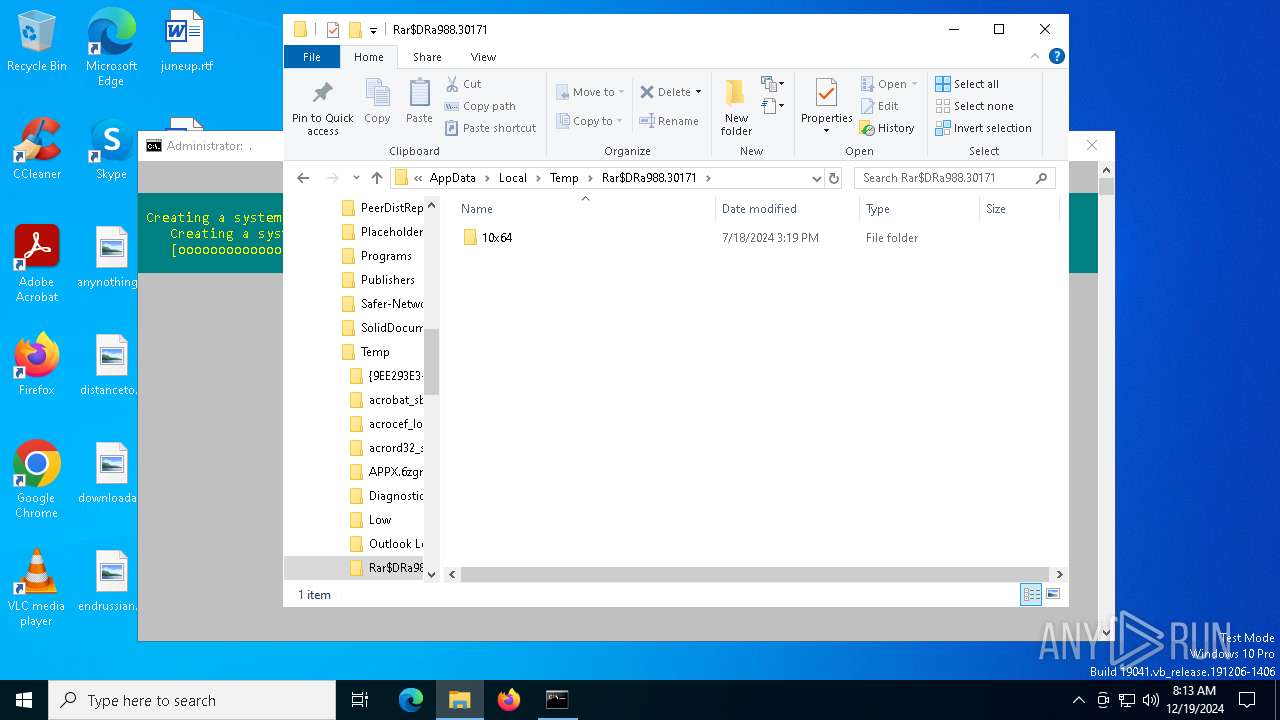
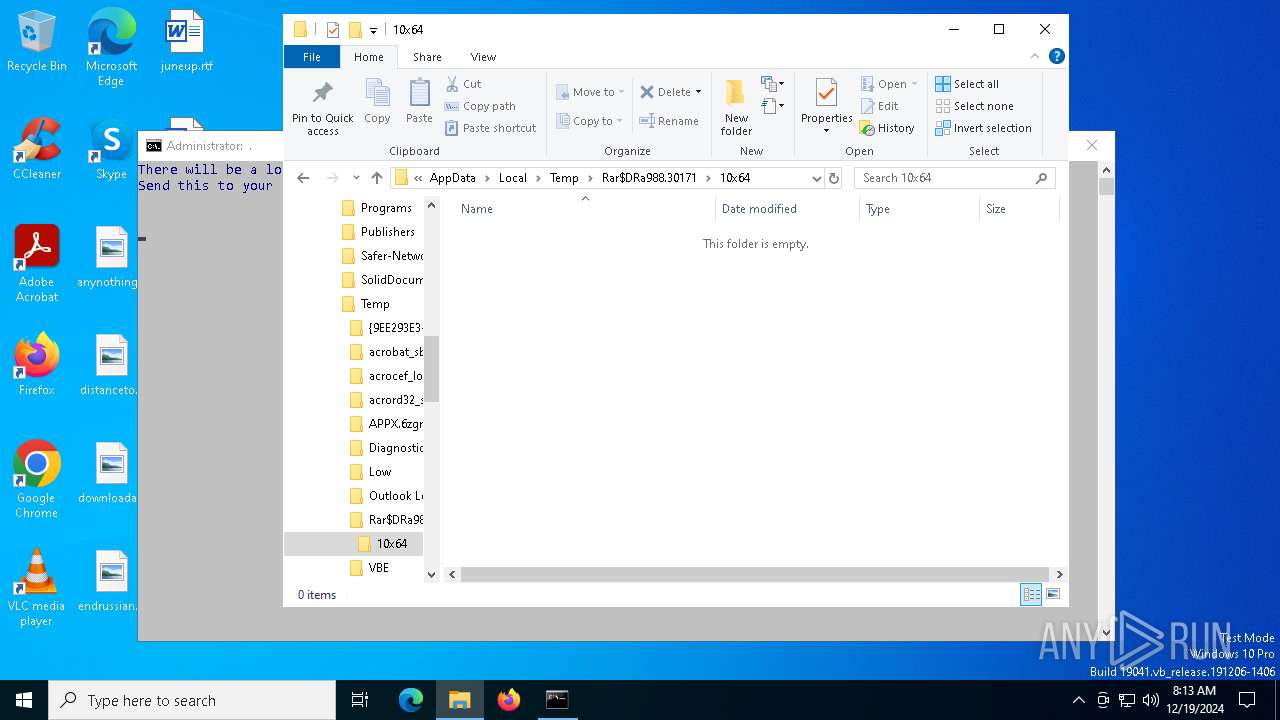
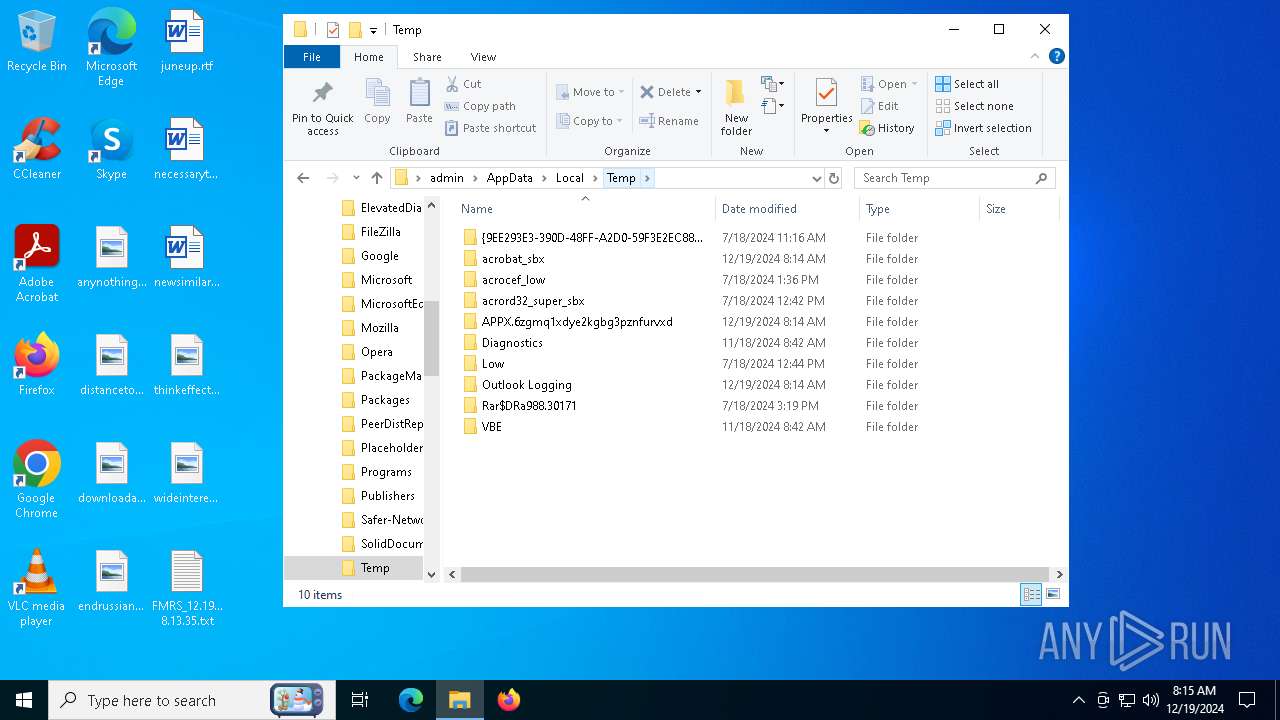
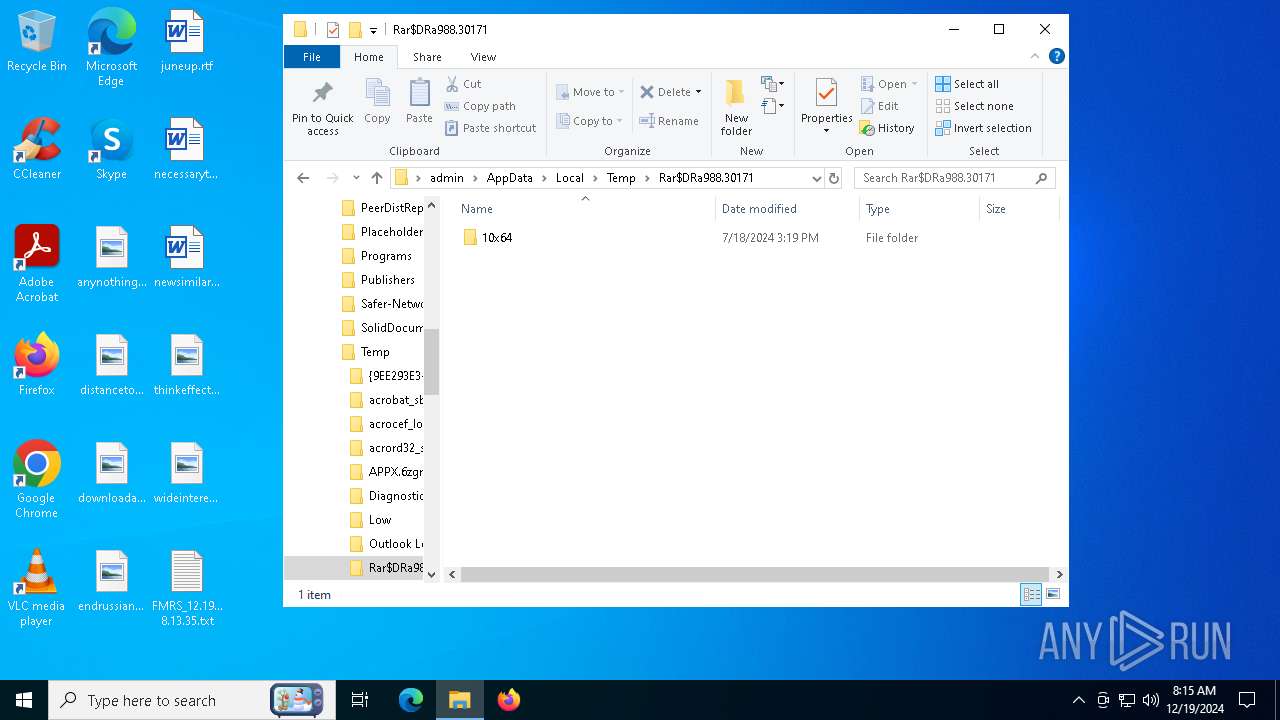
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\GNU License.url | binary | |
MD5:691BE400143F3097A6F20CD00897CCF9 | SHA256:2208A2417BFB72AF4395500C622BB1866B569B5394F0B59683A3EB10FD807F0A | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\R3570R3.bat | text | |
MD5:EB8670897FFD320C2C84389FE3A3316C | SHA256:468548E25CC89CC9A4B4D958FCD6F6734C383E9320E58AC6CA44A70E4C4FFB77 | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\FMRS.bat | text | |
MD5:AD88DEB343E505CD031E0643A3BA4285 | SHA256:7C9D6BC05D684198AC31087B28E8A3C6F5E1F020AACA458E5DEC2F75A8231548 | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\pol.bat | text | |
MD5:06202C5A32B2530AEEE7E0695AF37D3C | SHA256:4D0BC7C07A2AC8F6B9FD94764CE5A08079CDFC7137A0D69C1C58594B398D35DE | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\I4ng.bat | text | |
MD5:E27BBC6ED3148F67B3BEC7ED31D2A1DB | SHA256:86E0D911BAFE97D55BA0C80C0258ED974AB9B508281FE891AEF4CF741FA2B5CF | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\dependencies\libintl3.dll | executable | |
MD5:D202BAA425176287017FFE1FB5D1B77C | SHA256:F48CE1866602B114E653C876334B771107559ACF1C685373D2305034613958F0 | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\jm.bat | text | |
MD5:FD221780EB829789CD69A46F0A718251 | SHA256:3BB8EADF66983F0AE828C930340AE18736A5B2696421FD0ED1FE6375D361AFD6 | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\regbad.cfg | text | |
MD5:7CC11E0E36E74A5CBD4925D219C36306 | SHA256:A078E9E393D919ED5A0226E7909195AEC9C4C6408EB23C3894ABC9B54421F87B | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\NirCmd.chm | binary | |
MD5:DE1D4E1CAF466F6FA52F1EE518551C3E | SHA256:573AA5B8DB5F7B73CD0CB166514A197553E73659E881707C781691CBF2034516 | |||
| 6696 | FMRS.exe | C:\Users\admin\AppData\Local\Temp\APPX.6zgmq1xdye2kgbg3pznfurvxd\svc_stop_disable.cfg | text | |
MD5:ED82FD2B2B7BB0E2E277C4FB6EF92545 | SHA256:118F78FE35486F5F160590BD48E7113017CB8F005F2B5C5FAB003727679BCFD5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
50
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6636 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3564 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3564 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4040 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5620 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
732 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.146:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|
grep.exe | Invalid parameter passed to C runtime function.
|