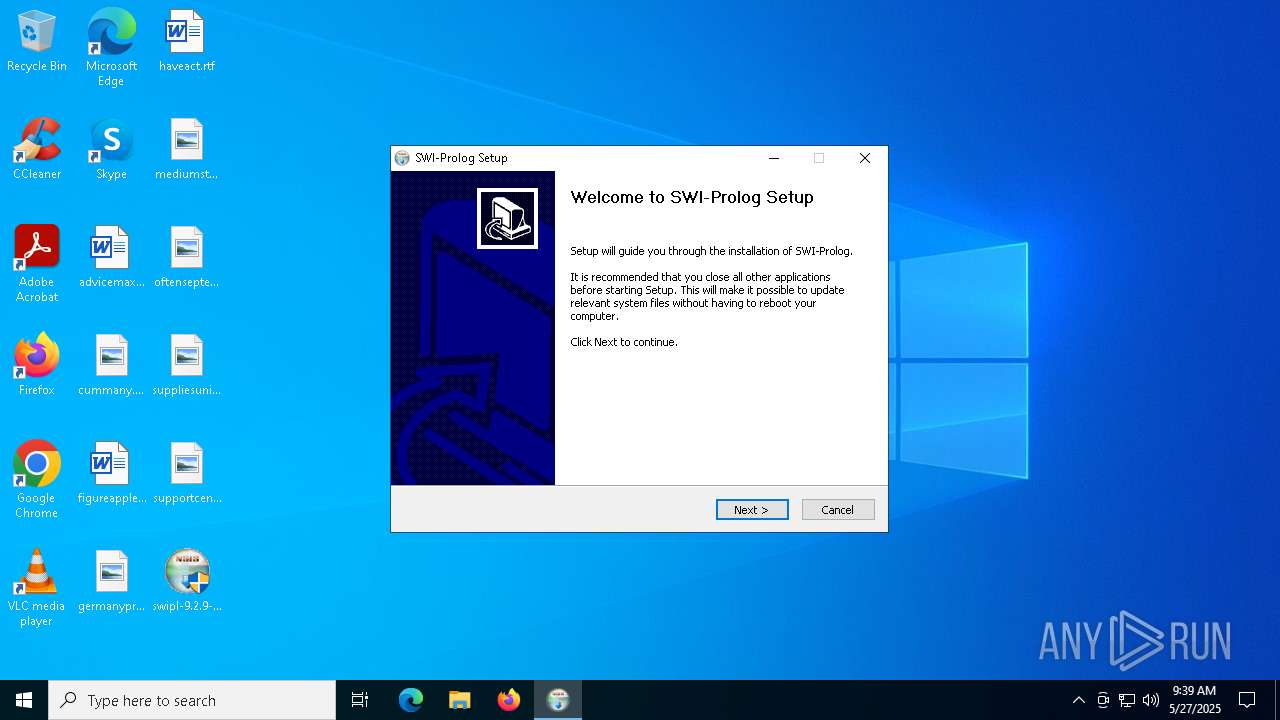
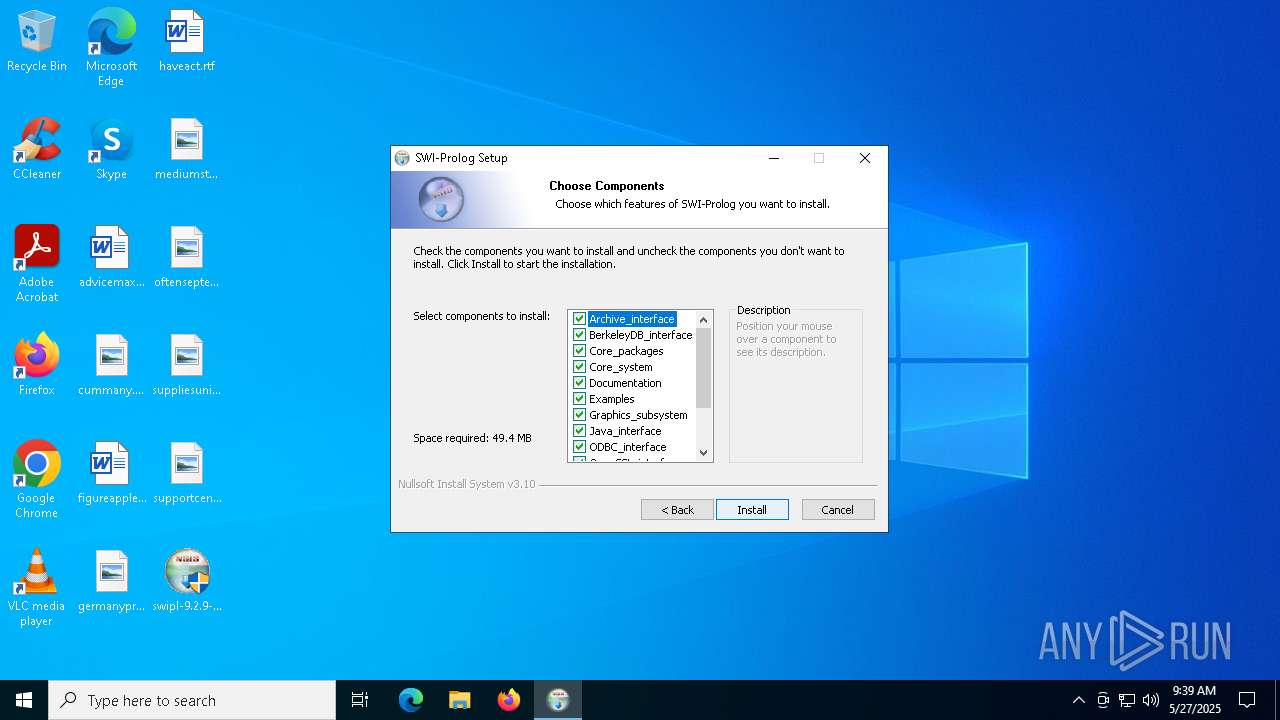
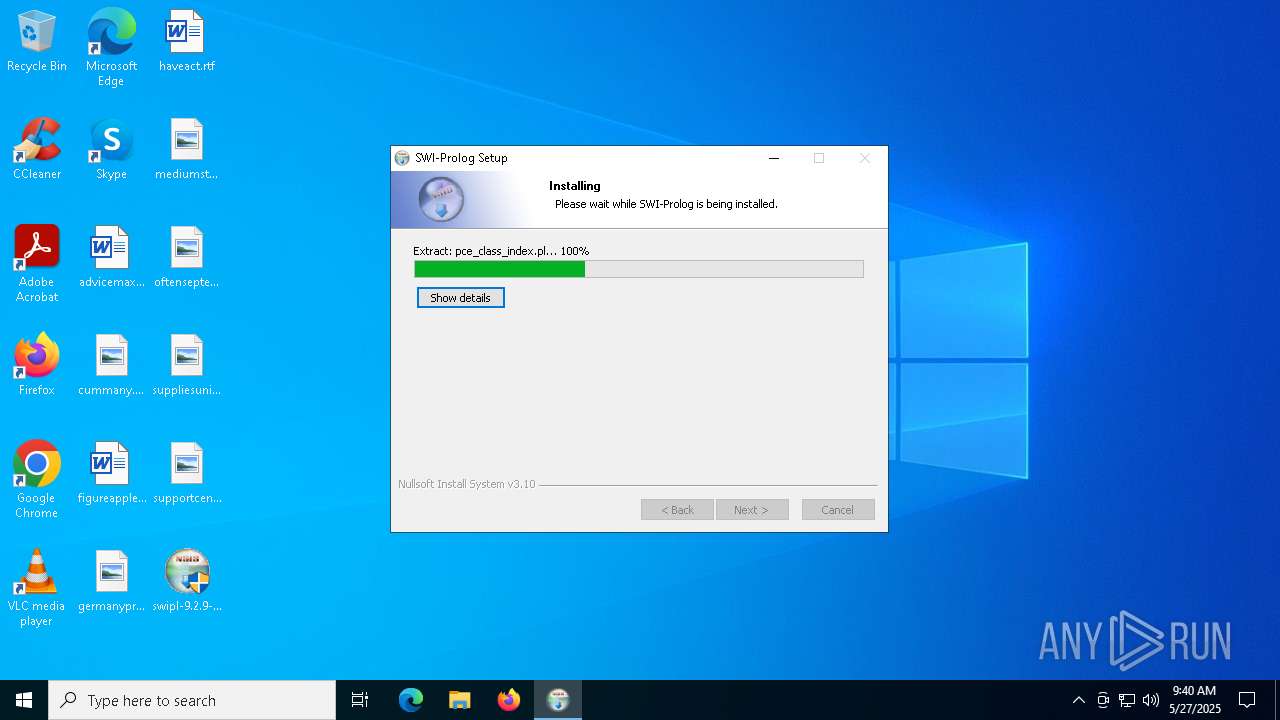
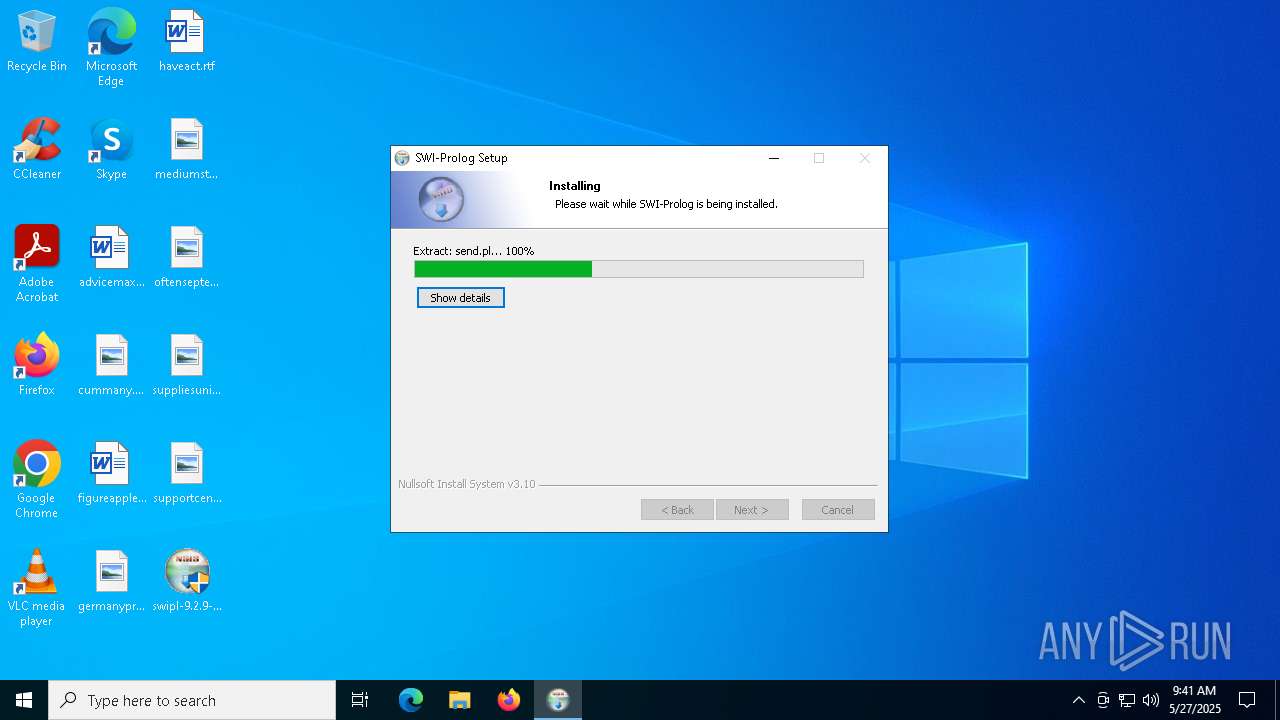
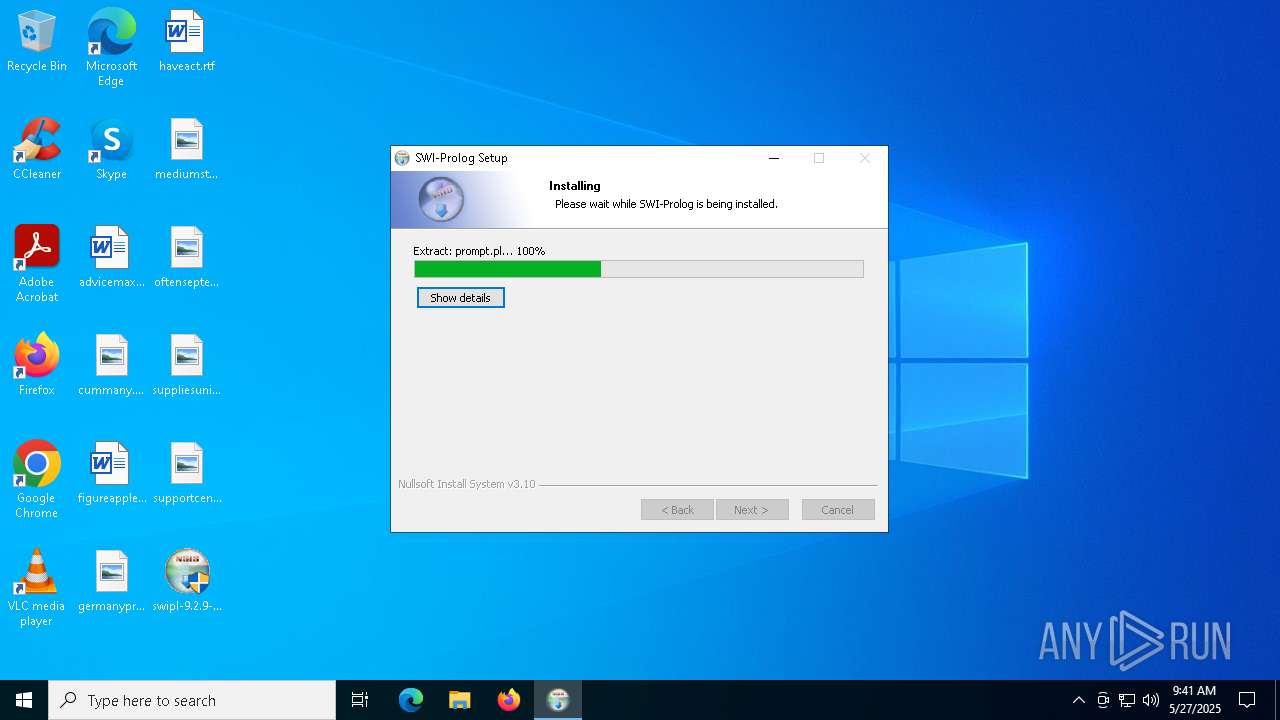
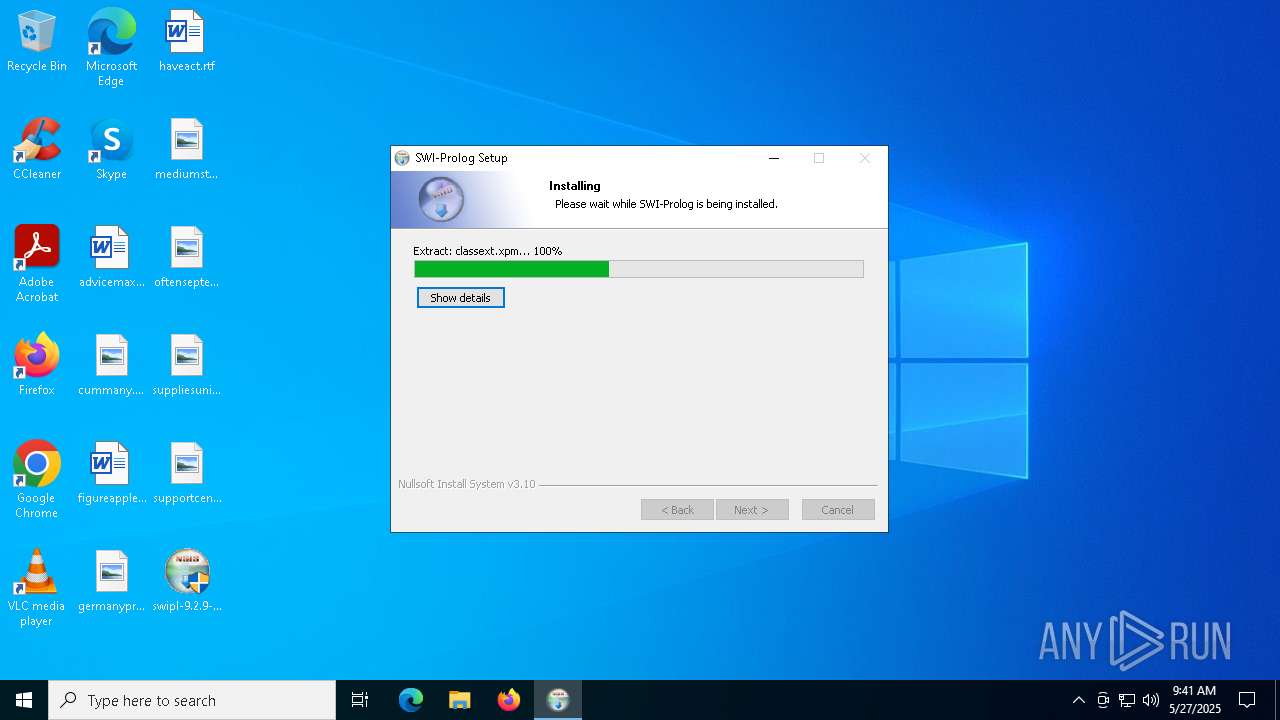
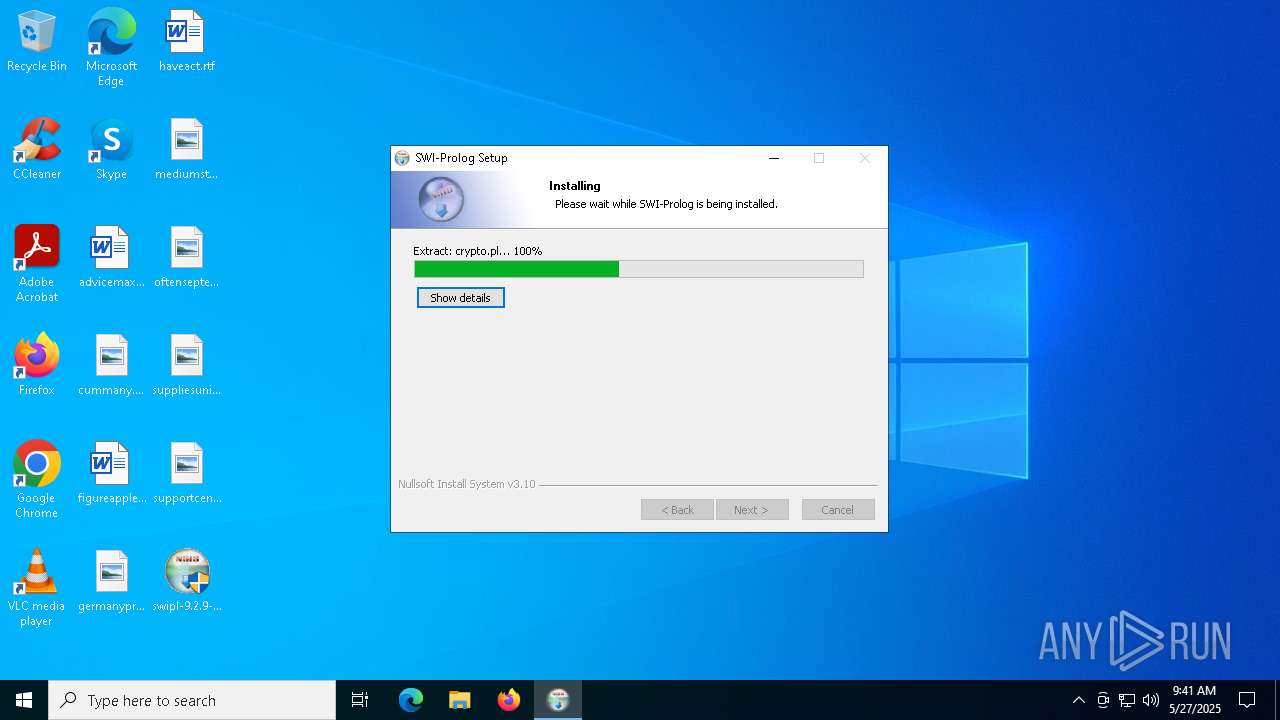
| File name: | swipl-9.2.9-1.x64.exe |
| Full analysis: | https://app.any.run/tasks/24386564-6c2f-4fd6-83dc-0f1ba29d79d0 |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2025, 09:38:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
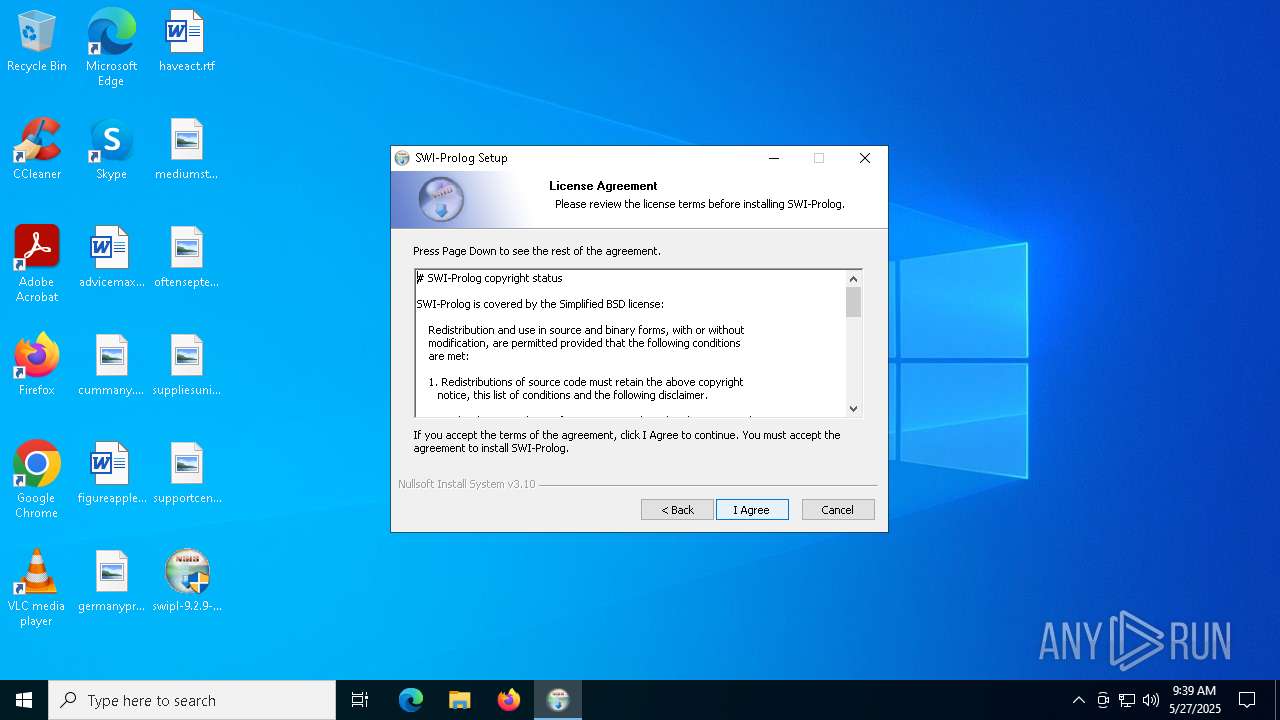
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive, 7 sections |
| MD5: | 4C6F256CCEBA54D21E548E3762E5AC10 |
| SHA1: | A1A3DC0C122C4645DB3E286D8547A0BCBA2BC899 |
| SHA256: | 0E6DBF5F4BB245344A257F2715F5D793D17870DEE9EEA1735CCB67B35F1E037C |
| SSDEEP: | 98304:DpvKwFEpJ0r4X8ofXjGwE2Ti88h0vPhlus4h98QAYnmtHgkiur+3LRYvOGG4c46e:Lape0J7roa95CnPHdl9XK |
MALICIOUS
No malicious indicators.SUSPICIOUS
There is functionality for taking screenshot (YARA)
- swipl-9.2.9-1.x64.exe (PID: 7616)
Malware-specific behavior (creating "System.dll" in Temp)
- swipl-9.2.9-1.x64.exe (PID: 7616)
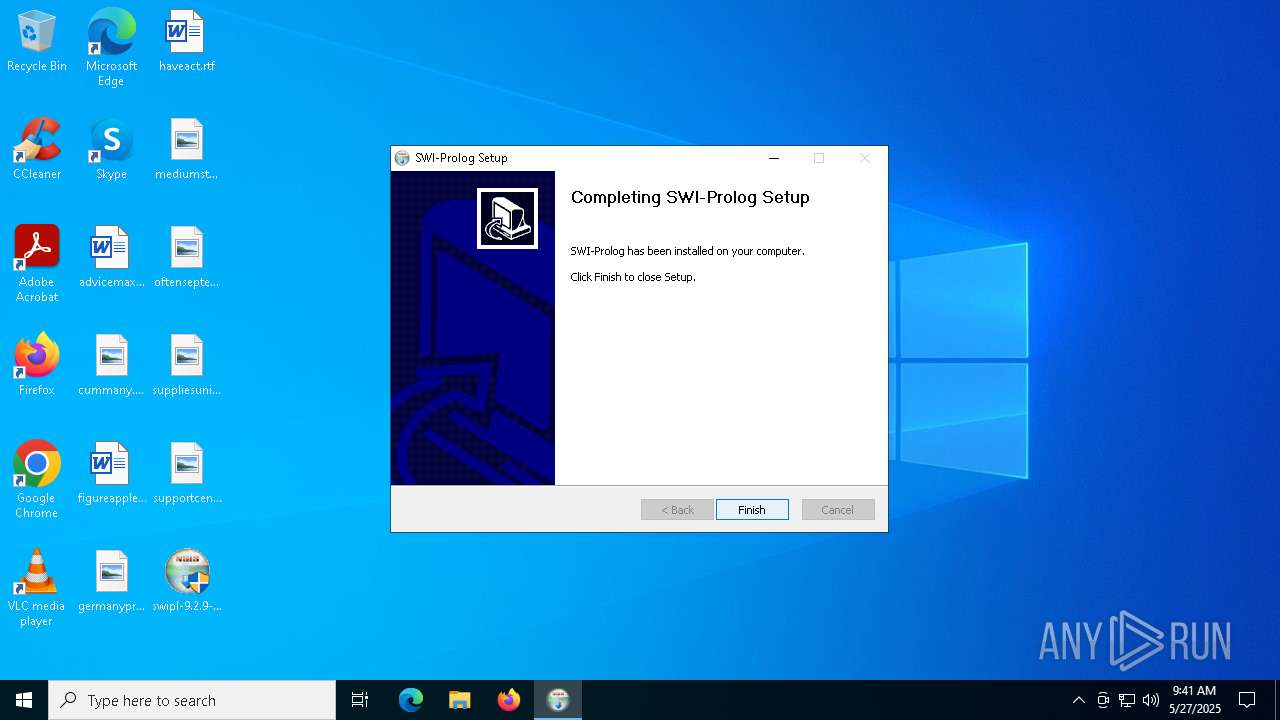
Creates a software uninstall entry
- swipl-9.2.9-1.x64.exe (PID: 7616)
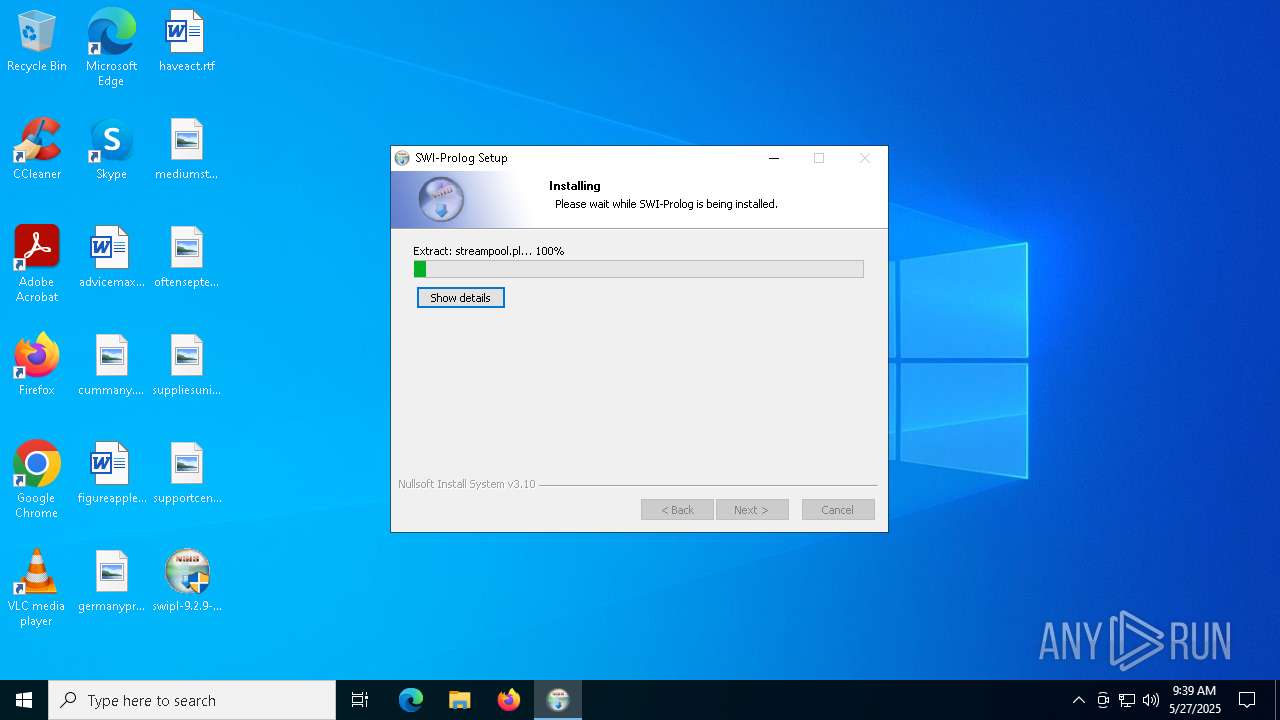
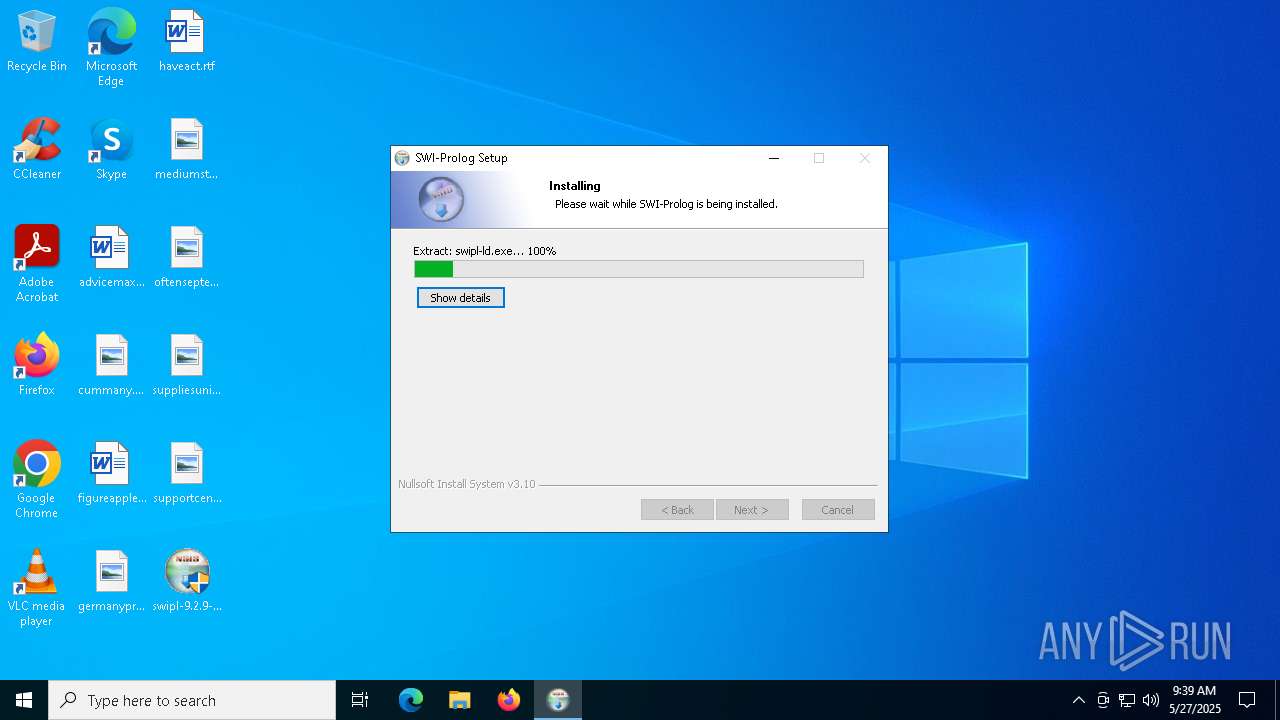
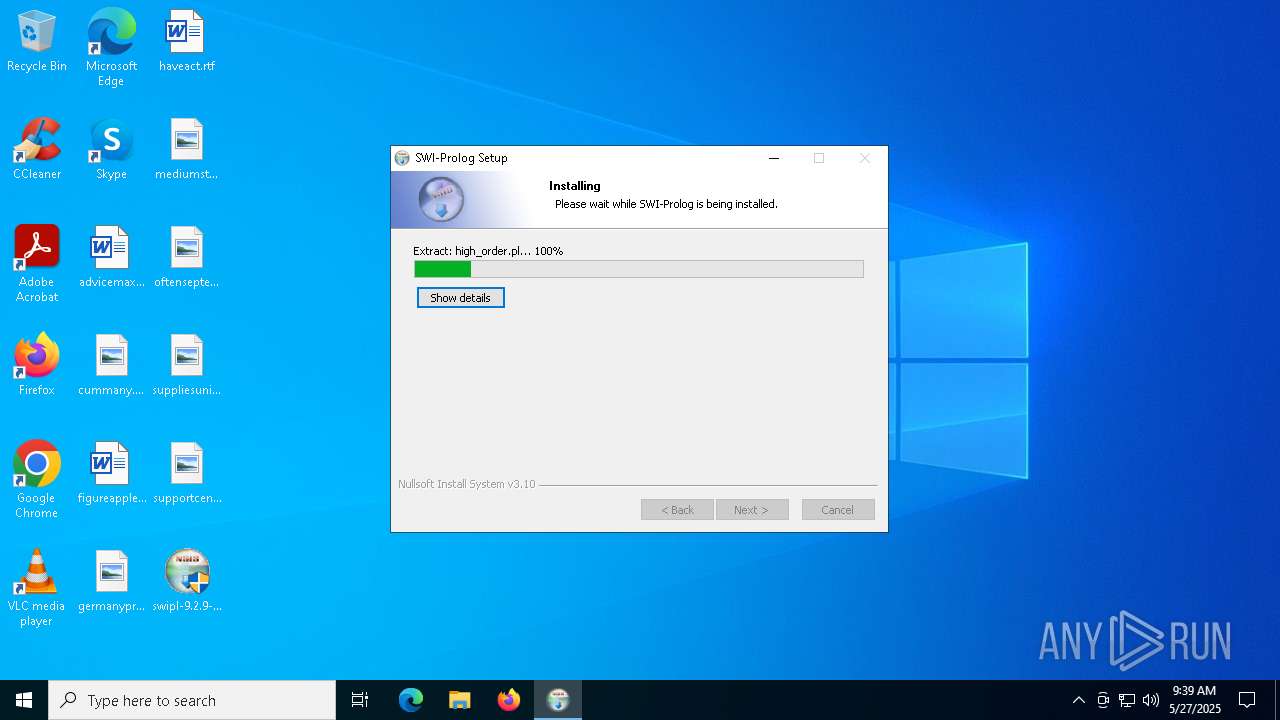
Executable content was dropped or overwritten
- swipl-9.2.9-1.x64.exe (PID: 7616)
The process creates files with name similar to system file names
- swipl-9.2.9-1.x64.exe (PID: 7616)
INFO
Reads the computer name
- swipl-9.2.9-1.x64.exe (PID: 7616)
Create files in a temporary directory
- swipl-9.2.9-1.x64.exe (PID: 7616)
The sample compiled with english language support
- swipl-9.2.9-1.x64.exe (PID: 7616)
Reads the software policy settings
- slui.exe (PID: 7208)
Checks proxy server information
- slui.exe (PID: 7208)
Checks supported languages
- swipl-9.2.9-1.x64.exe (PID: 7616)
Creates files in the program directory
- swipl-9.2.9-1.x64.exe (PID: 7616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:18 00:00:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.42 |
| CodeSize: | 40448 |
| InitializedDataSize: | 68608 |
| UninitializedDataSize: | 407552 |
| EntryPoint: | 0x4a8e |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
134
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7208 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7492 | "C:\Users\admin\Desktop\swipl-9.2.9-1.x64.exe" | C:\Users\admin\Desktop\swipl-9.2.9-1.x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7616 | "C:\Users\admin\Desktop\swipl-9.2.9-1.x64.exe" | C:\Users\admin\Desktop\swipl-9.2.9-1.x64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
3 596
Read events
3 567
Write events
29
Delete events
0
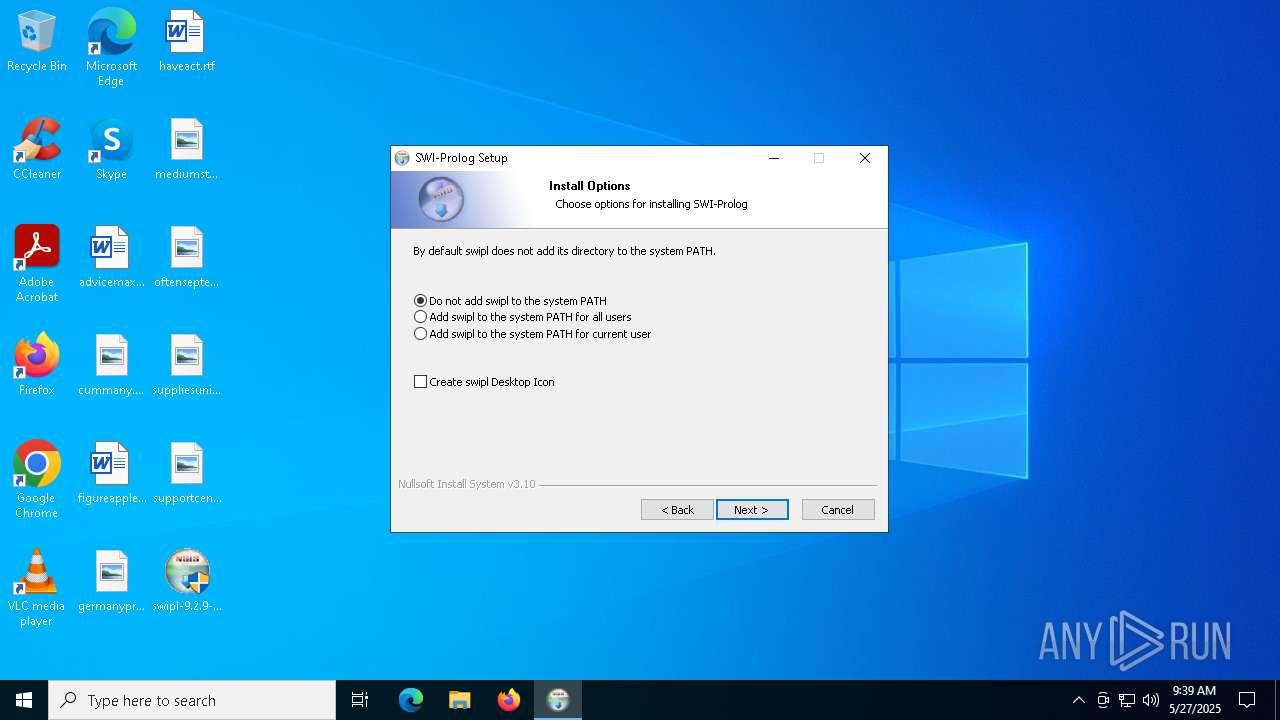
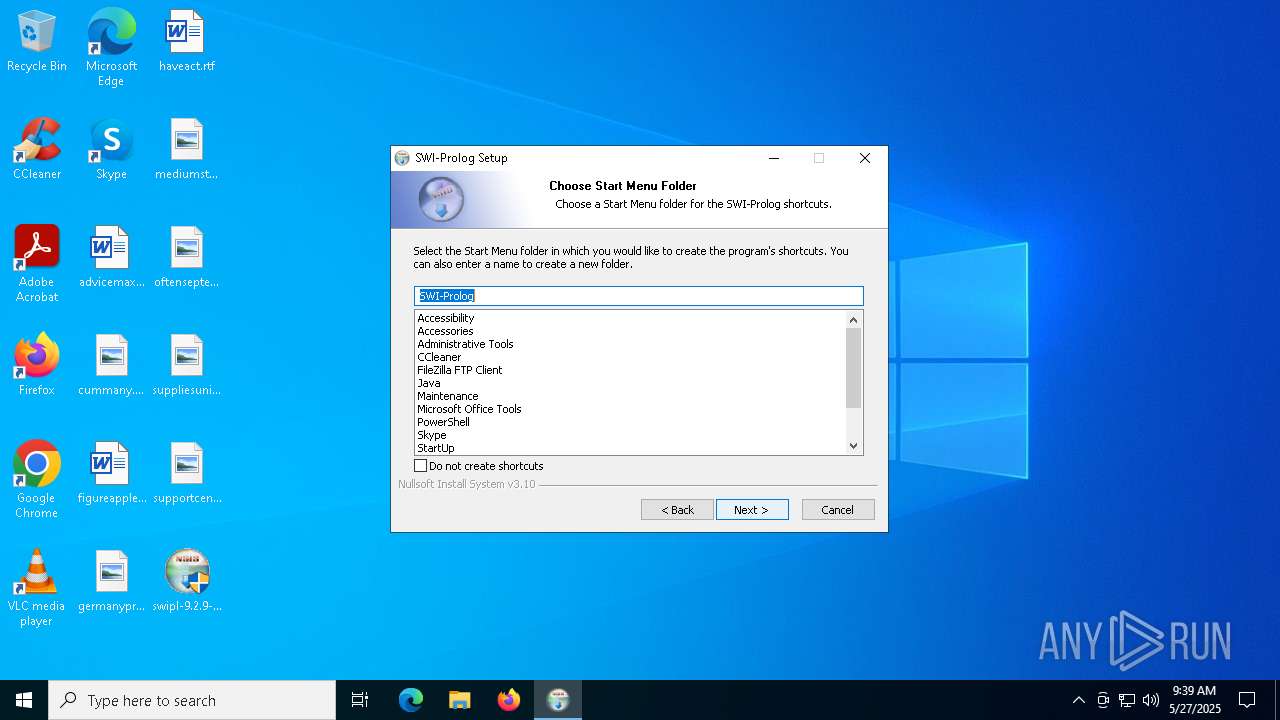
Modification events
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\swipl\bin\swipl-win.exe | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl |
| Operation: | write | Name: | URLInfoAbout |
Value: https://swi-prolog.org | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl |
| Operation: | write | Name: | StartMenu |
Value: SWI-Prolog | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl |
| Operation: | write | Name: | DoNotAddToPath |
Value: 1 | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl\Components\Core_packages |
| Operation: | write | Name: | Installed |
Value: 1 | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl\Components\ODBC_interface |
| Operation: | write | Name: | Installed |
Value: 1 | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl\Components\OpenSSL_interface |
| Operation: | write | Name: | Installed |
Value: 1 | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl\Components\Perl_regex |
| Operation: | write | Name: | Installed |
Value: 1 | |||
| (PID) Process: | (7616) swipl-9.2.9-1.x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\swipl\Components\Python_interface |
| Operation: | write | Name: | Installed |
Value: 1 | |||
Executable files
69
Suspicious files
329
Text files
1 713
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7616 | swipl-9.2.9-1.x64.exe | C:\Program Files\swipl\library\ext\bdb\INDEX.pl | text | |
MD5:D2162545B33E6B927656C926D393B611 | SHA256:1CADBF435A5CFDEF7ECFB4E46D5531F22C66CBC1E8AF93A6A5425136ACC7F025 | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Program Files\swipl\bin\bdb4pl.dll | executable | |
MD5:C54ECACFA7E33594B42B31F749AAEC08 | SHA256:172B7AC0DF2A05BA54D4B55196DD7A6DA9C43801A74D856EF75B6152EC4BF35B | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Program Files\swipl\bin\libdb-6.1.dll | executable | |
MD5:BBD0DD8320FA362C3B85F9F1B956C715 | SHA256:5F208752CB31363C426CBF48A6814809ECEA108A4FB0D187A46A0C1E10F9755D | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Users\admin\AppData\Local\Temp\nscBCBB.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Users\admin\AppData\Local\Temp\nscBCBB.tmp\StartMenu.dll | executable | |
MD5:F8BD9E054AC831D93BB8D336E00DC9F0 | SHA256:F4D49F43331875D8464B64FC62871C9805CC0C878EE494EFDB5A980DBAAC33BE | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Users\admin\AppData\Local\Temp\nscBCBB.tmp\InstallOptions.dll | executable | |
MD5:18E9B202006C091E287E97BF8E04323C | SHA256:27818BE279CD5434BBA4A054C6B6CB50D015B1485045B9EEC36F4FB1768BCAF9 | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Users\admin\AppData\Local\Temp\nscBCBB.tmp\ioSpecial.ini | ini | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Users\admin\AppData\Local\Temp\nscBCBB.tmp\NSIS.InstallOptions.ini | text | |
MD5:0BF80B7E5F03F8A42B6586F0DE586C12 | SHA256:5D472CC6F3FCA39108A57950055C082E85D745907EE98317EA18A3504DE863A4 | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Users\admin\AppData\Local\Temp\nscBCBB.tmp\UserInfo.dll | executable | |
MD5:D7A616C4D7689BC0C9F607CB8F32B4BF | SHA256:CFA509AAD8867B1B58C863894E477A0F1F19C9B1FB1D2CB6F395198702955C8B | |||
| 7616 | swipl-9.2.9-1.x64.exe | C:\Program Files\swipl\library\ext\archive\INDEX.pl | text | |
MD5:EAA220E104F8F4CCB9691C013B4E6B57 | SHA256:A7F6BB12F1AF60F586EBB298CC172224BE7A2EE391A87F6F0690025411B544B2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
47
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5796 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5796 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5568 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.129:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
5568 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.129:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.64:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
7884 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5568 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5796 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5796 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5568 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5796 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5568 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |