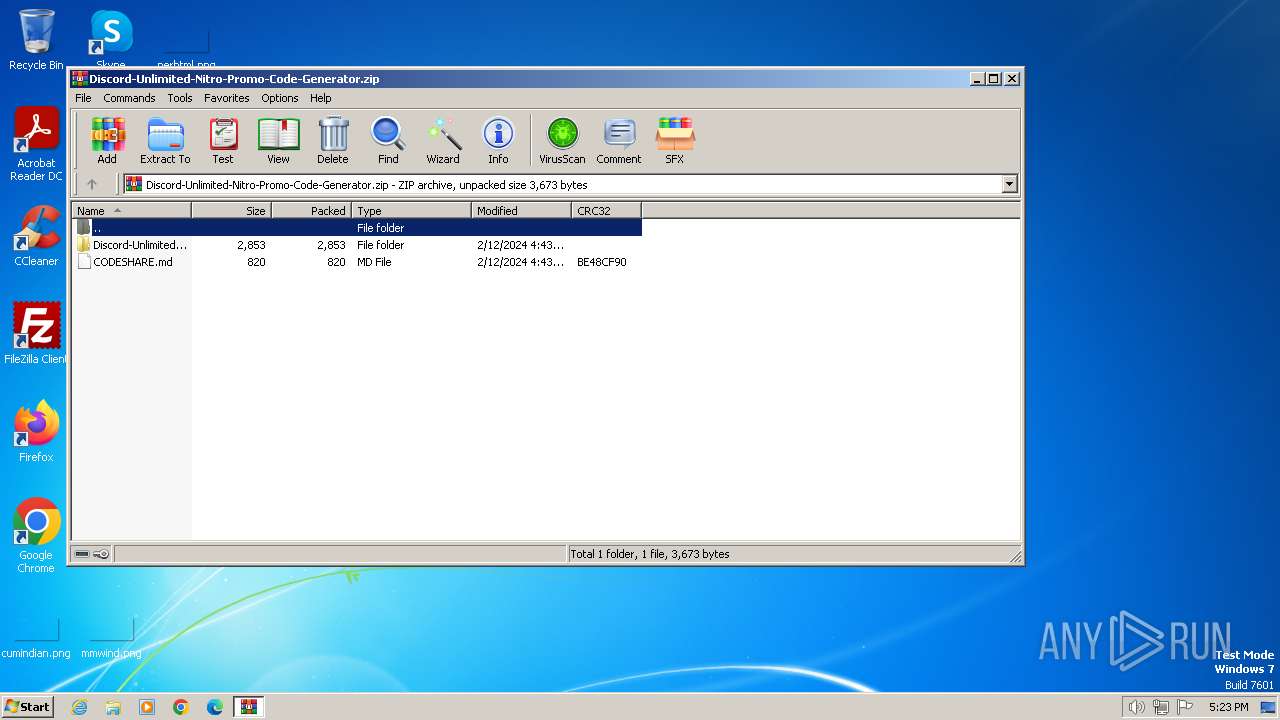
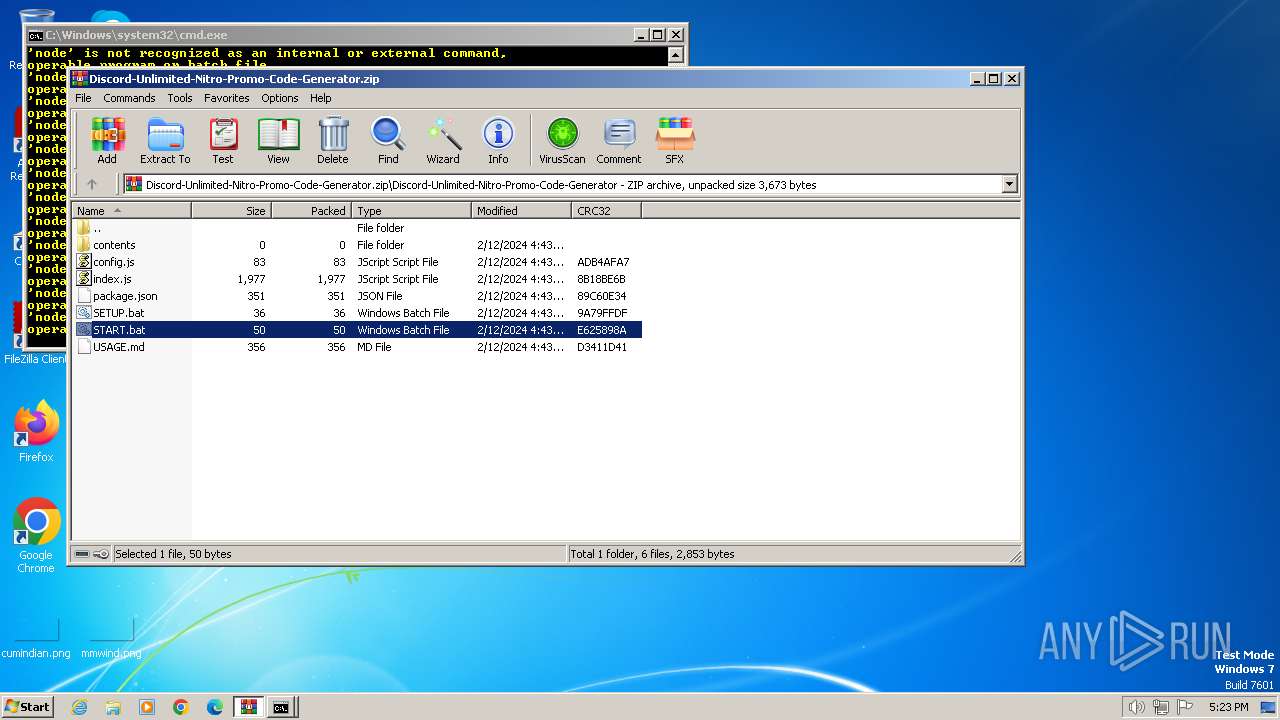
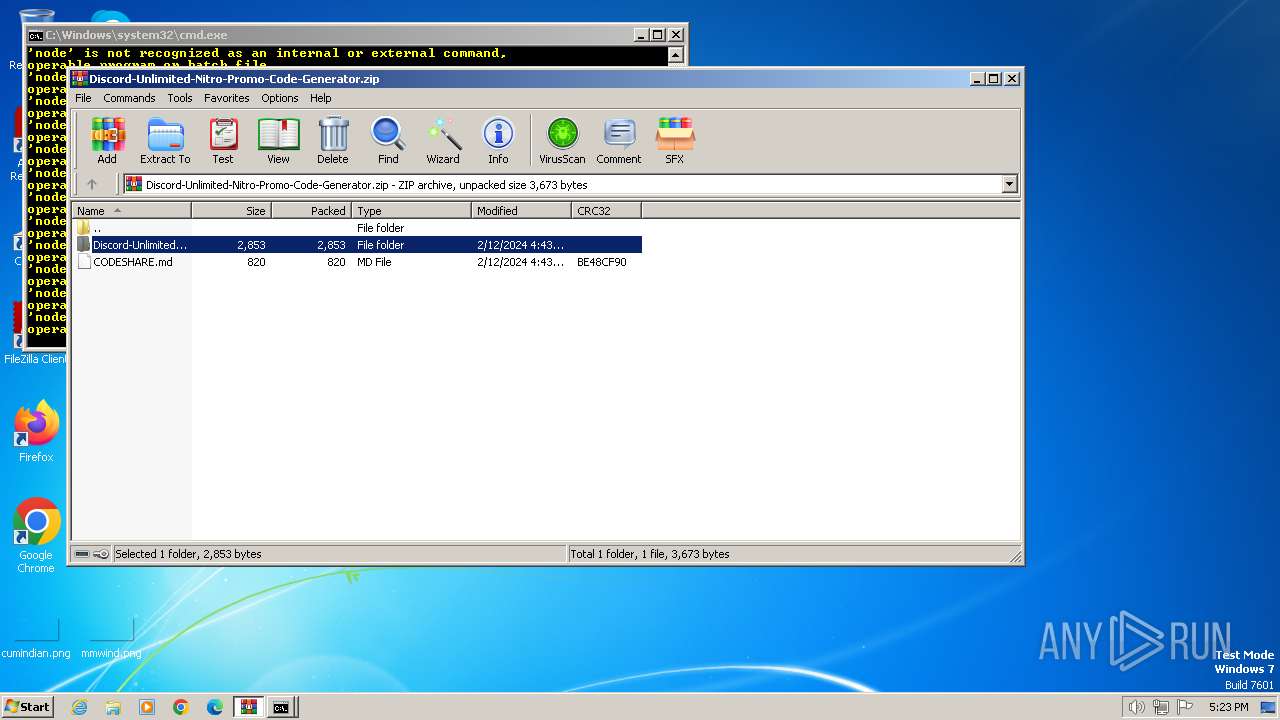
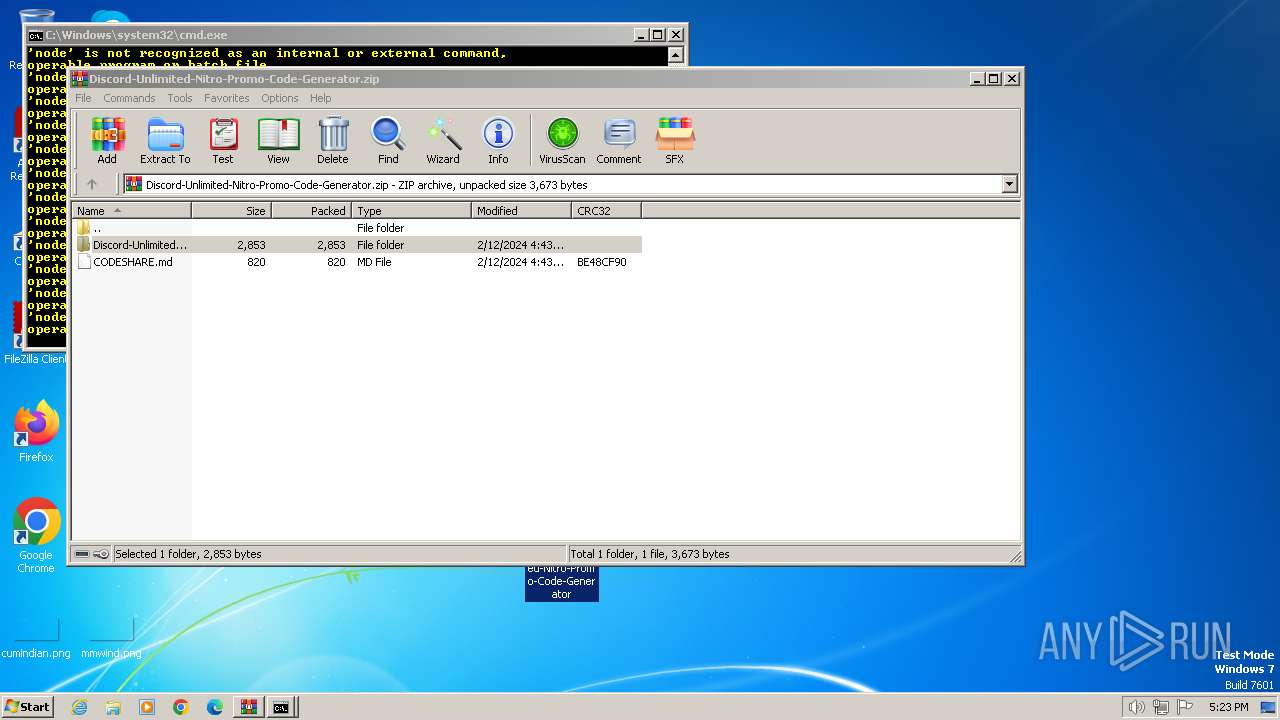
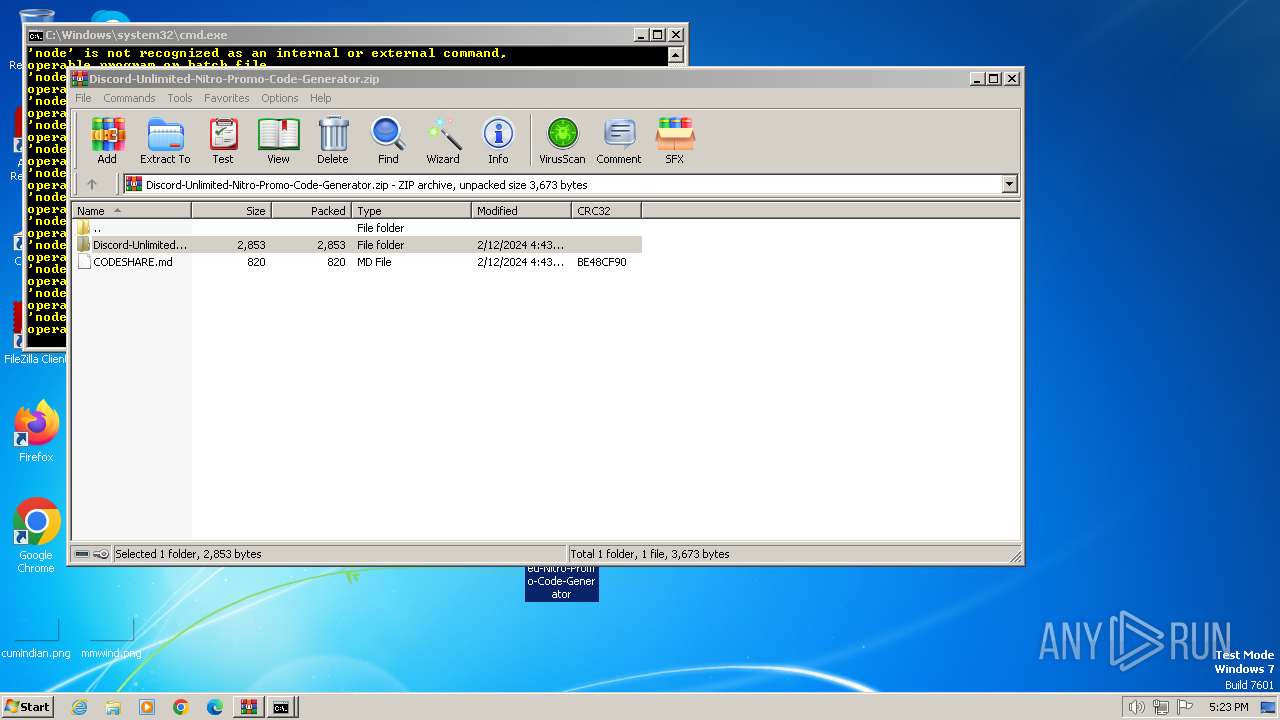
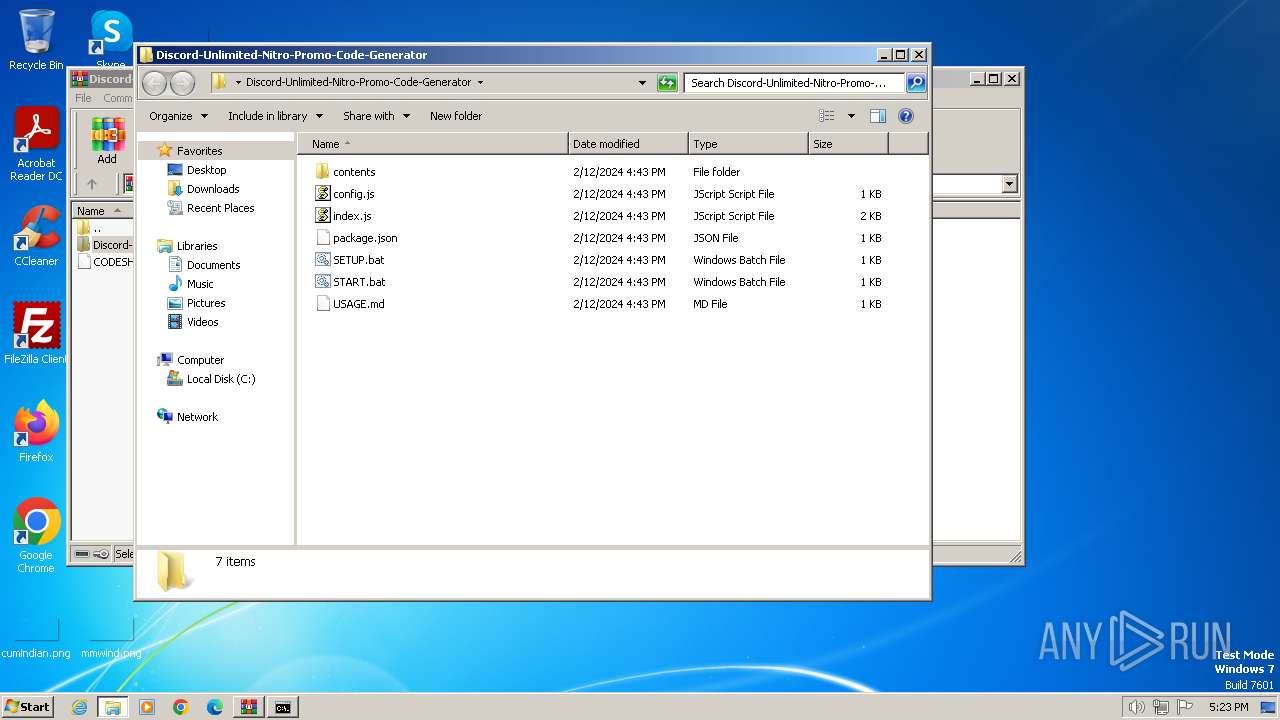
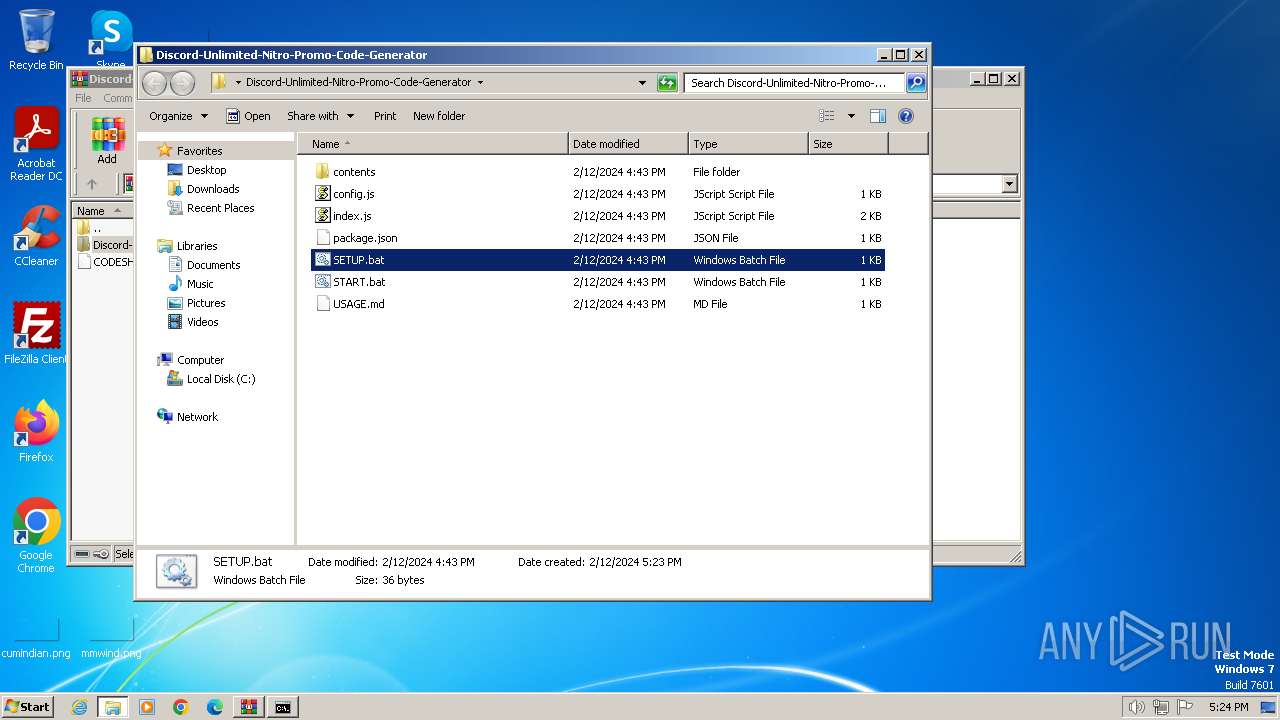
| File name: | Discord-Unlimited-Nitro-Promo-Code-Generator.zip |
| Full analysis: | https://app.any.run/tasks/9ee4d48b-3102-4b51-8326-a60254b6b695 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2024, 17:23:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 5D2674DFACF3CCEC3CDD3107FFFF744C |
| SHA1: | 399A98CC241A2B0E1B7533987A373E88DC7372E9 |
| SHA256: | 0E6BB47CB98DC33095B02A77B749346B3D620C407B5BAA638F1FE7B4E35E07F8 |
| SSDEEP: | 96:QwlPf7Vq2cY8Vnf18kshtWF8BiewWz46uGLIY9fVdWddp/rjqlt/RLolIVTGg:XVH8xMjWOBieBKG8WdWZlut |
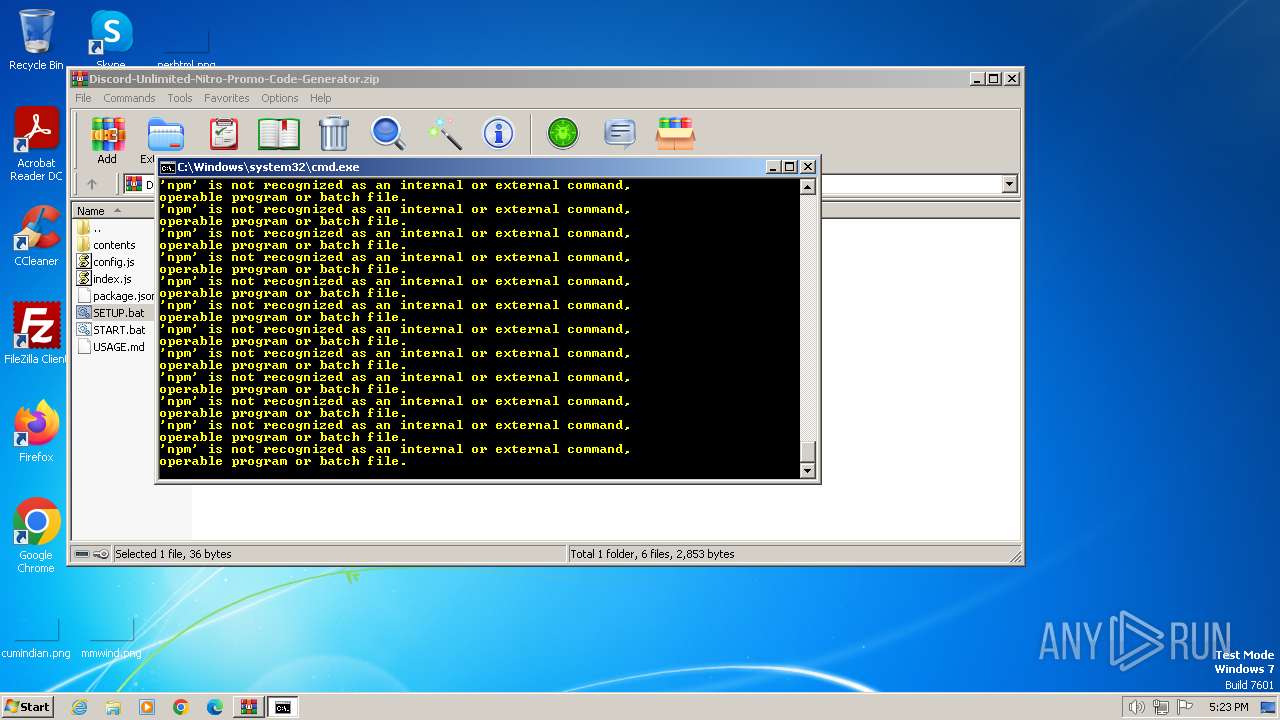
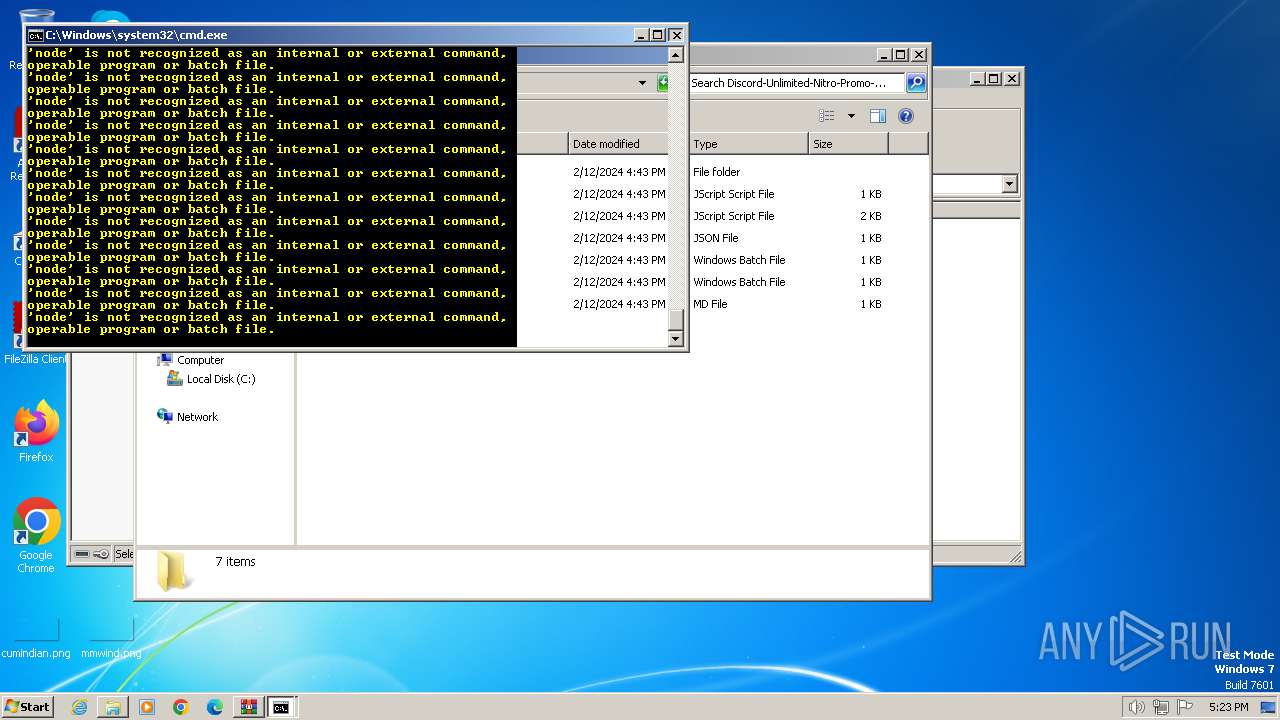
MALICIOUS
Actions looks like stealing of personal data
- WinRAR.exe (PID: 2472)
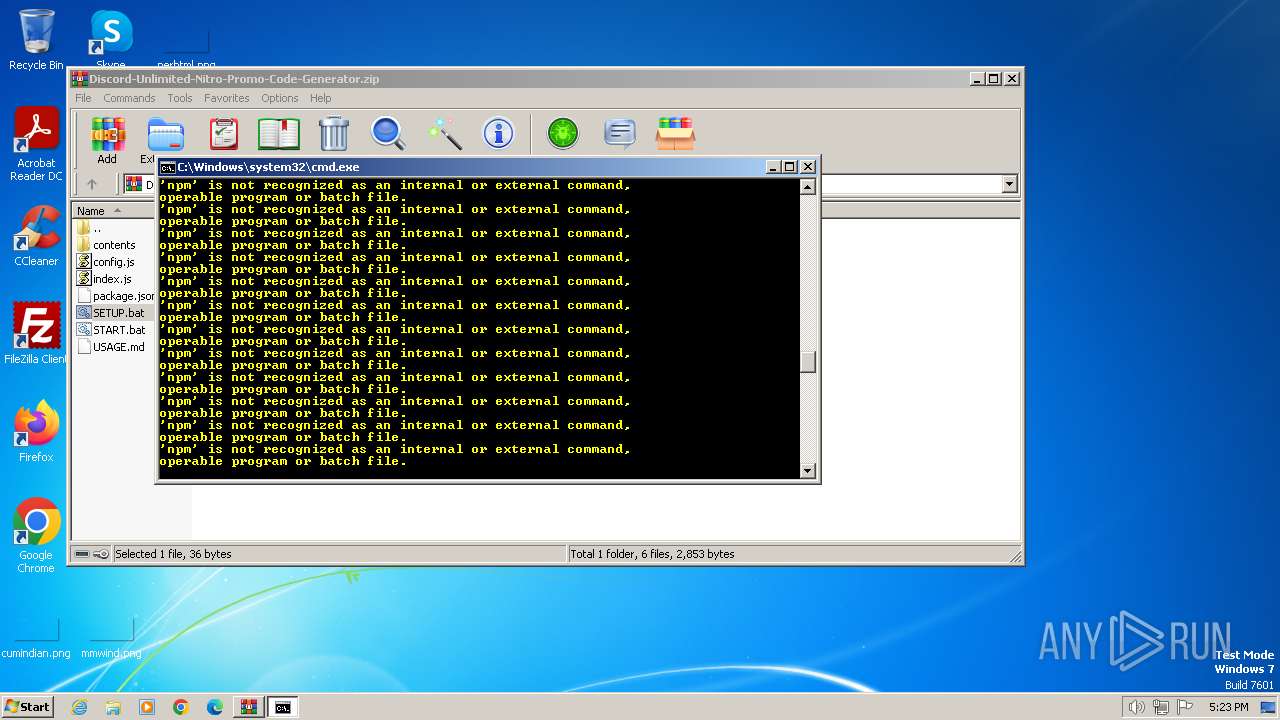
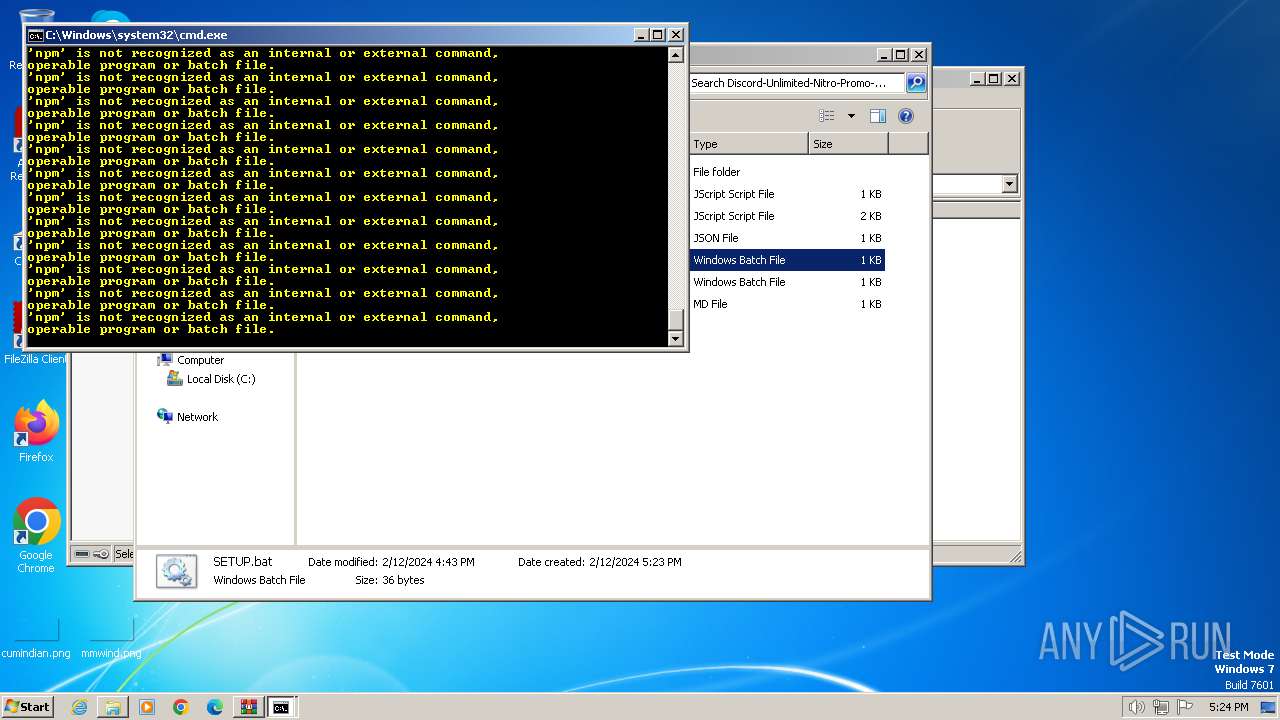
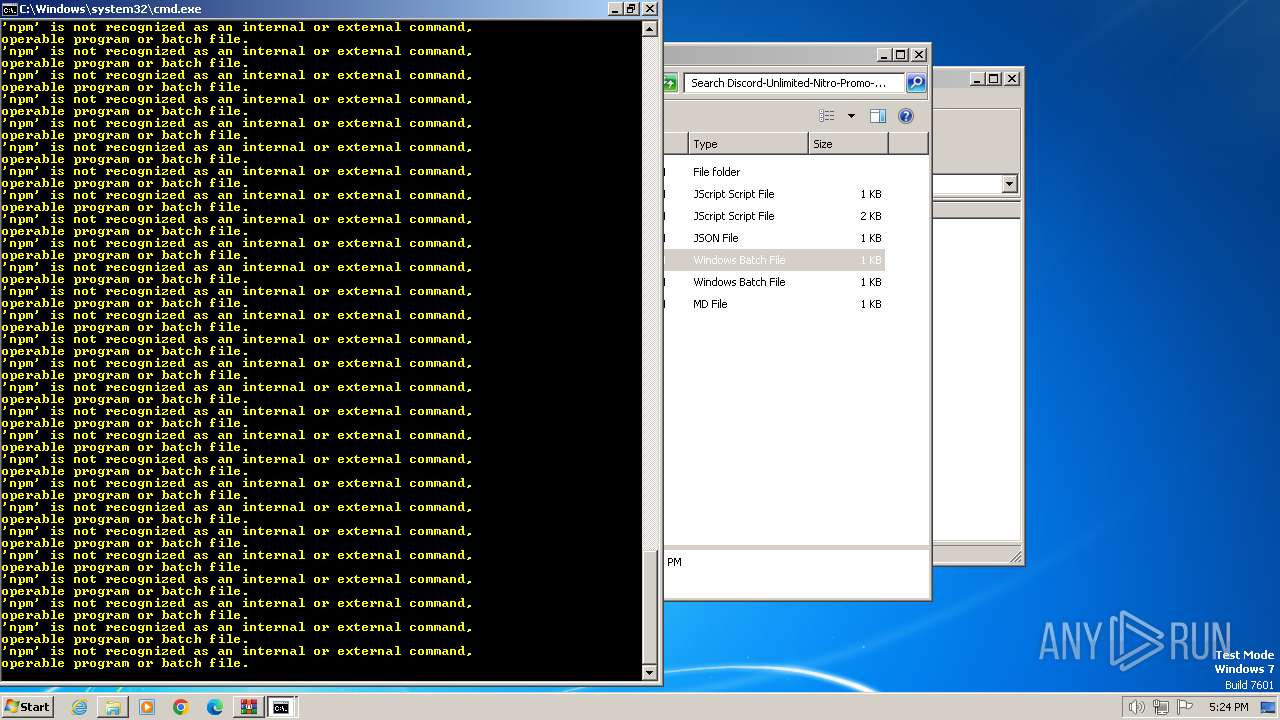
SUSPICIOUS
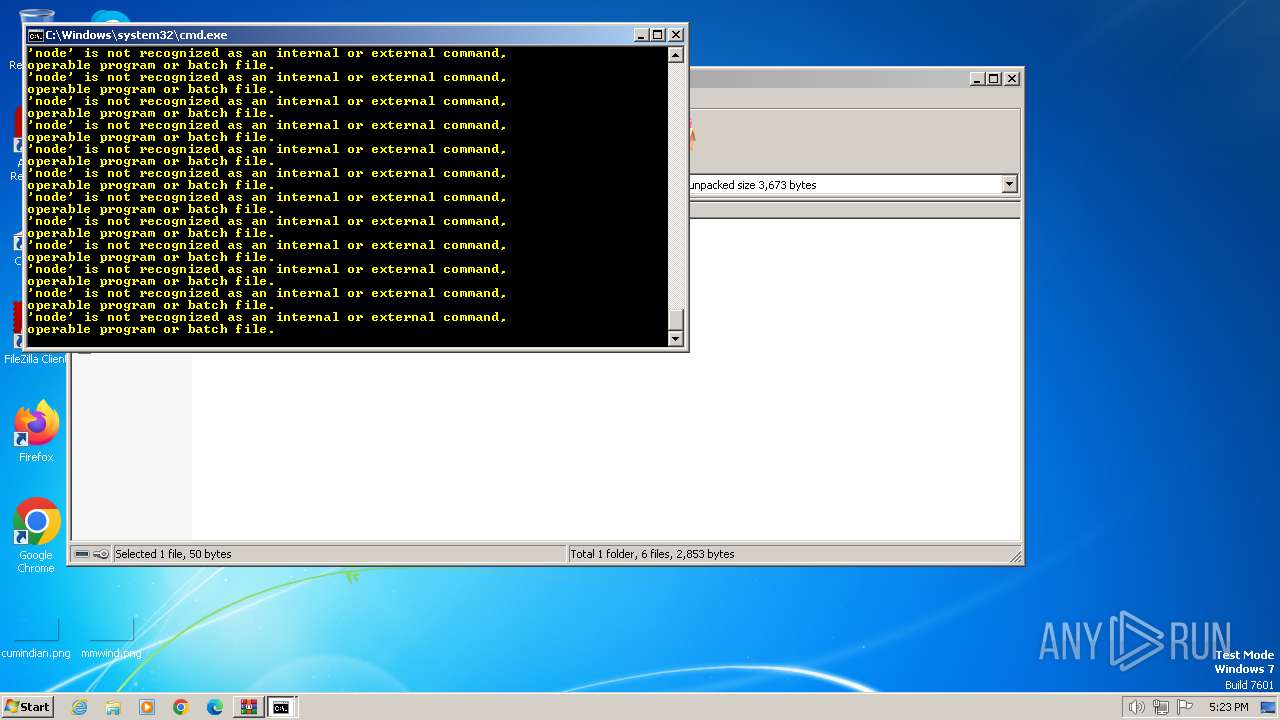
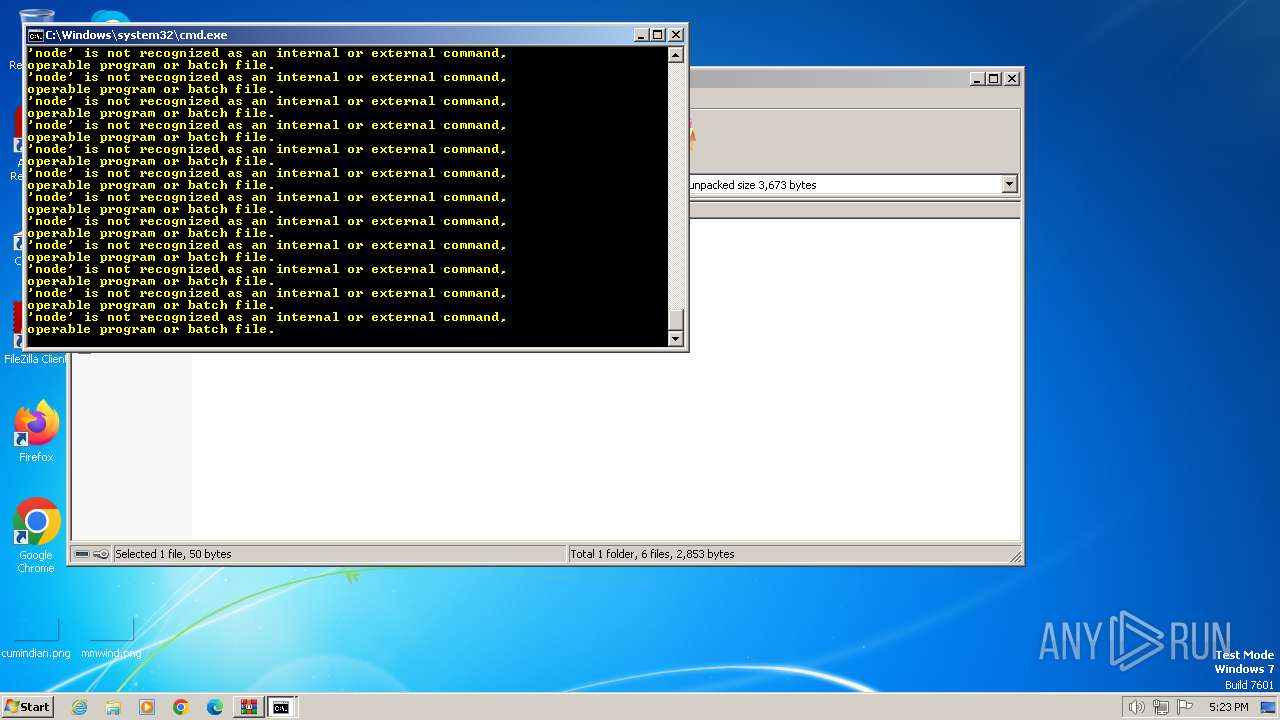
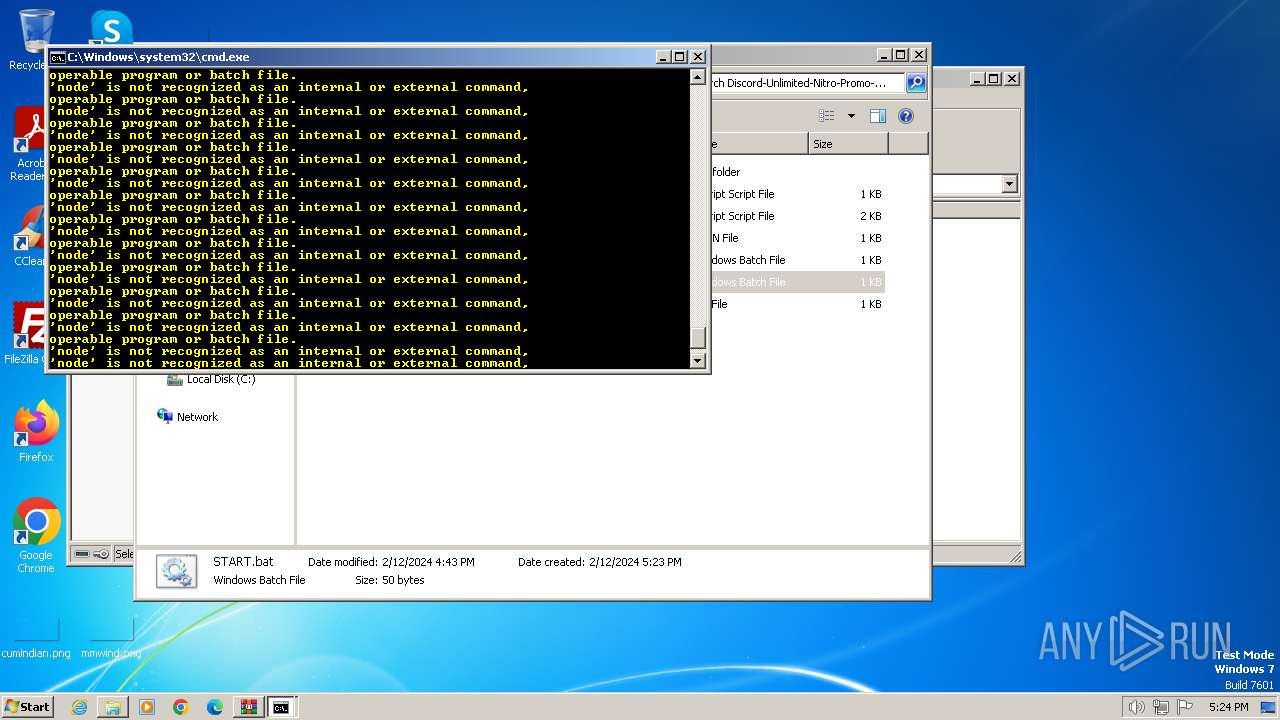
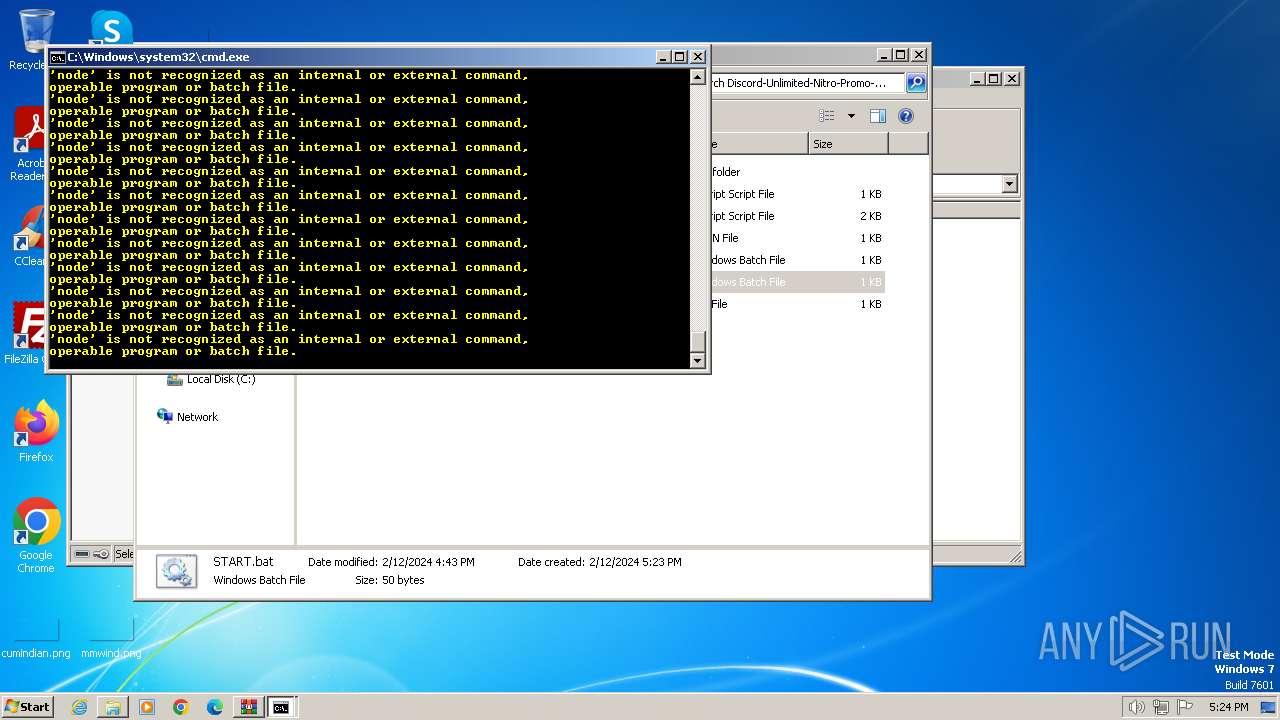
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2472)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 2472)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2472)
INFO
Manual execution by a user
- cmd.exe (PID: 3276)
- cmd.exe (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:02:12 16:43:56 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Discord-Unlimited-Nitro-Promo-Code-Generator/ |
Total processes
47
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
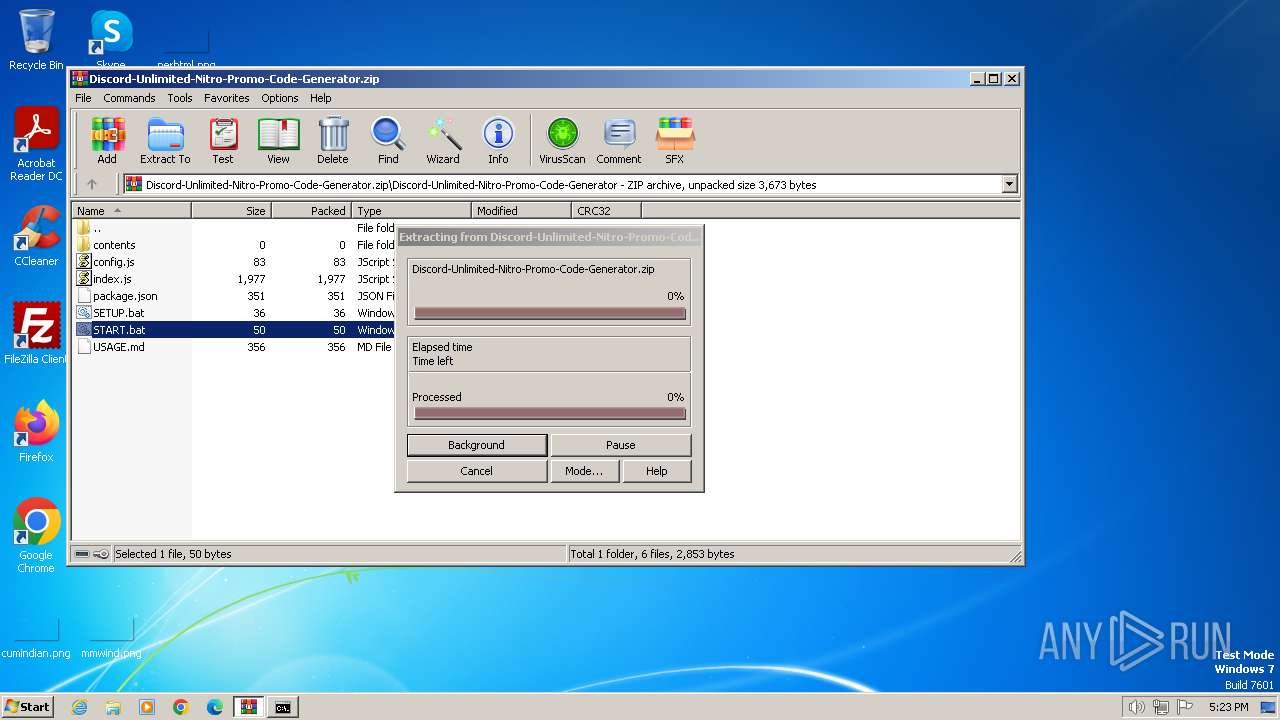
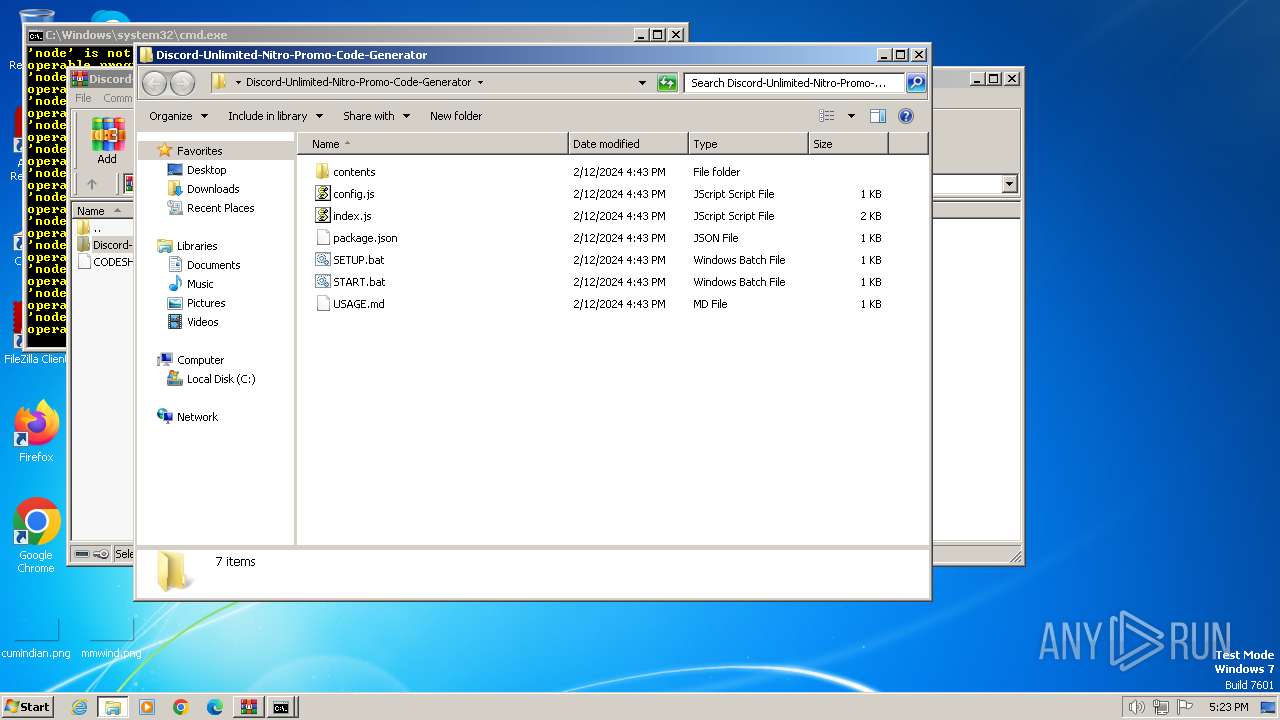
| 2472 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Discord-Unlimited-Nitro-Promo-Code-Generator.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
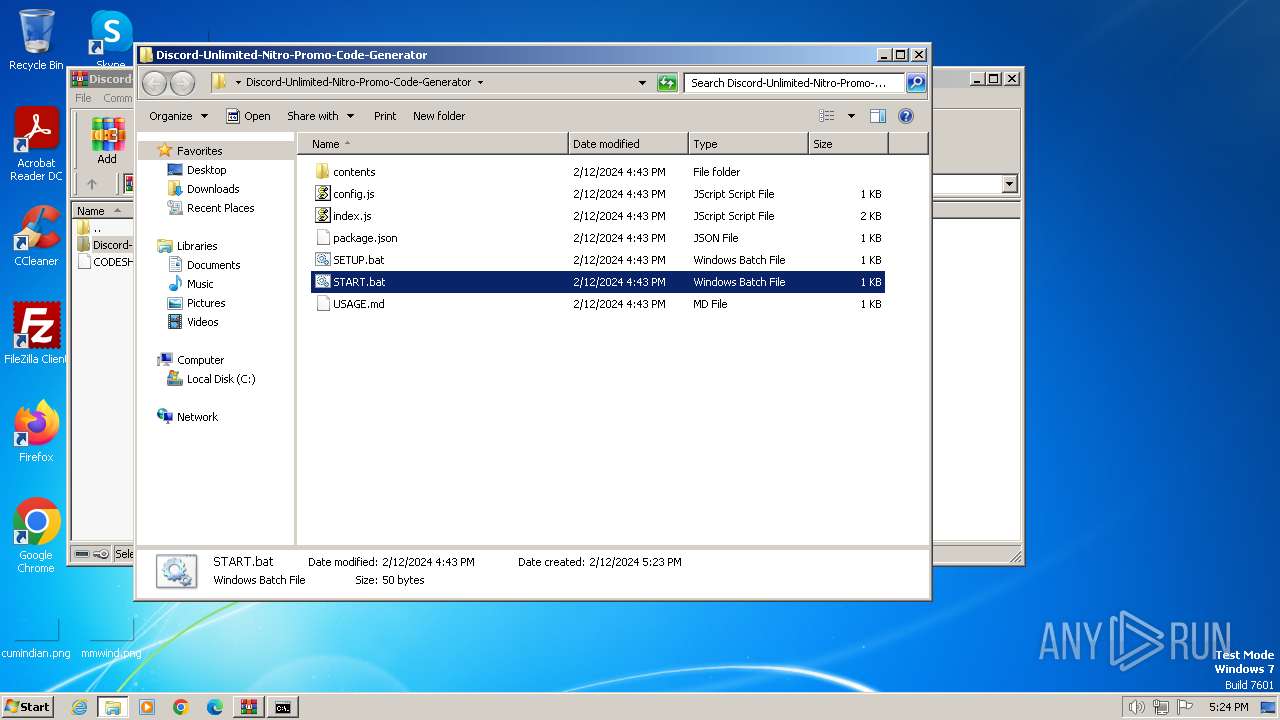
| 2636 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Discord-Unlimited-Nitro-Promo-Code-Generator\SETUP.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 2920 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2472.11042\START.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3276 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Discord-Unlimited-Nitro-Promo-Code-Generator\START.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 3536 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2472.10711\SETUP.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 614
Read events
3 591
Write events
23
Delete events
0
Modification events
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Discord-Unlimited-Nitro-Promo-Code-Generator.zip | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
1
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
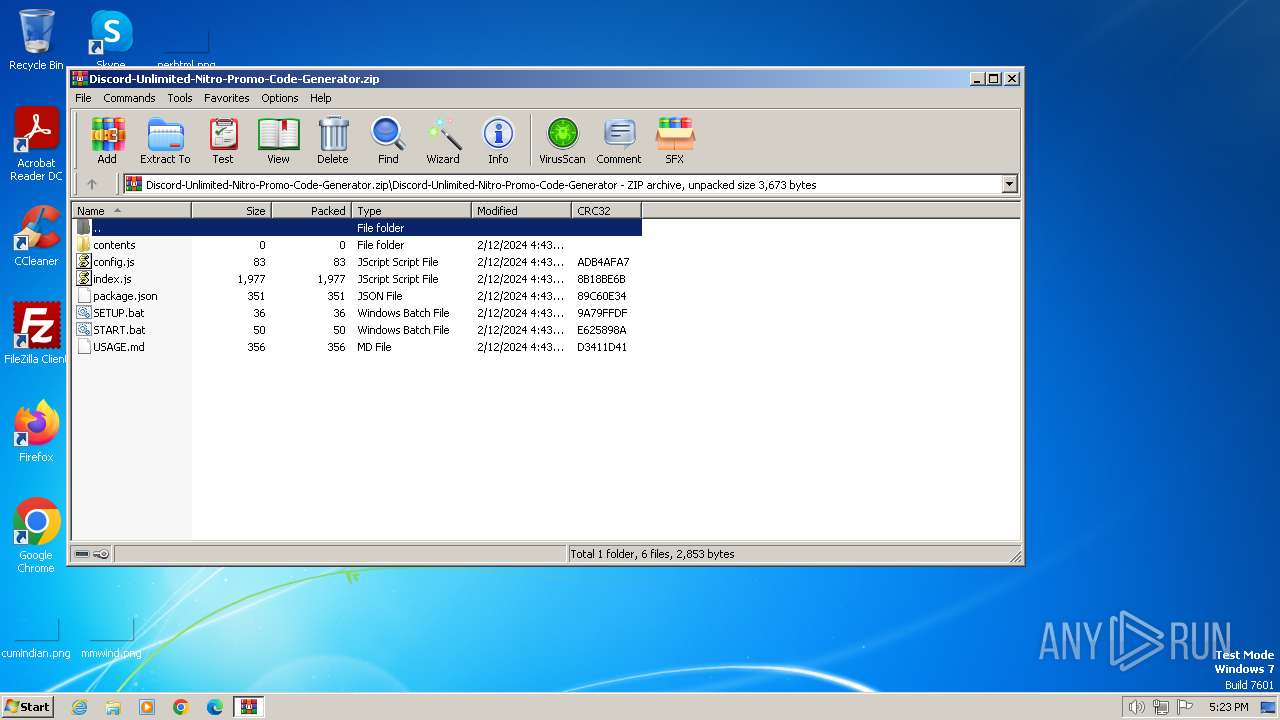
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.11836\Discord-Unlimited-Nitro-Promo-Code-Generator\index.js | text | |
MD5:5A30C959263CAC1676EDC45C516D071C | SHA256:E1C129459A553EF24ABF42347C0F869411A461ED44044FF39B46110FFE3C8A27 | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.11836\Discord-Unlimited-Nitro-Promo-Code-Generator\SETUP.bat | text | |
MD5:295D3D97C68AC5E5B7AD10BE01EAFCD2 | SHA256:58A7A0E2544117A3507C462DC39F08683291A00FCCC7FC06D1C880A451765156 | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.11836\Discord-Unlimited-Nitro-Promo-Code-Generator\package.json | binary | |
MD5:A7D7F37ABD628AA64B281CCB4846BDFF | SHA256:EDCAE434EB589D20A270F4C914521D66671547872D76027CAF9643DC93AF2934 | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2472.11042\START.bat | text | |
MD5:0C06E37A9D5C1014B4B55C56FD235AD9 | SHA256:F7D2B2B468354CF675504FDAD60B5A124FBEA0B3C5CC4943EE07AD0834467E05 | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2472.10711\SETUP.bat | text | |
MD5:295D3D97C68AC5E5B7AD10BE01EAFCD2 | SHA256:58A7A0E2544117A3507C462DC39F08683291A00FCCC7FC06D1C880A451765156 | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.11836\Discord-Unlimited-Nitro-Promo-Code-Generator\START.bat | text | |
MD5:0C06E37A9D5C1014B4B55C56FD235AD9 | SHA256:F7D2B2B468354CF675504FDAD60B5A124FBEA0B3C5CC4943EE07AD0834467E05 | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.11836\Discord-Unlimited-Nitro-Promo-Code-Generator\USAGE.md | text | |
MD5:8FC2A96C822A7A4D875E3FD76D8DE37C | SHA256:218156D854447AC70DBFAA72DF0677F49E05881DF2AE57B20FAC6C5DC37DDEFE | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.11836\Discord-Unlimited-Nitro-Promo-Code-Generator\config.js | text | |
MD5:E33FC1168A0A9377F6257A488E228BF1 | SHA256:2368B6344A706FC85F93506163DF8D95BC9241B587F4DB7EC99F46DDE0F2C889 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |