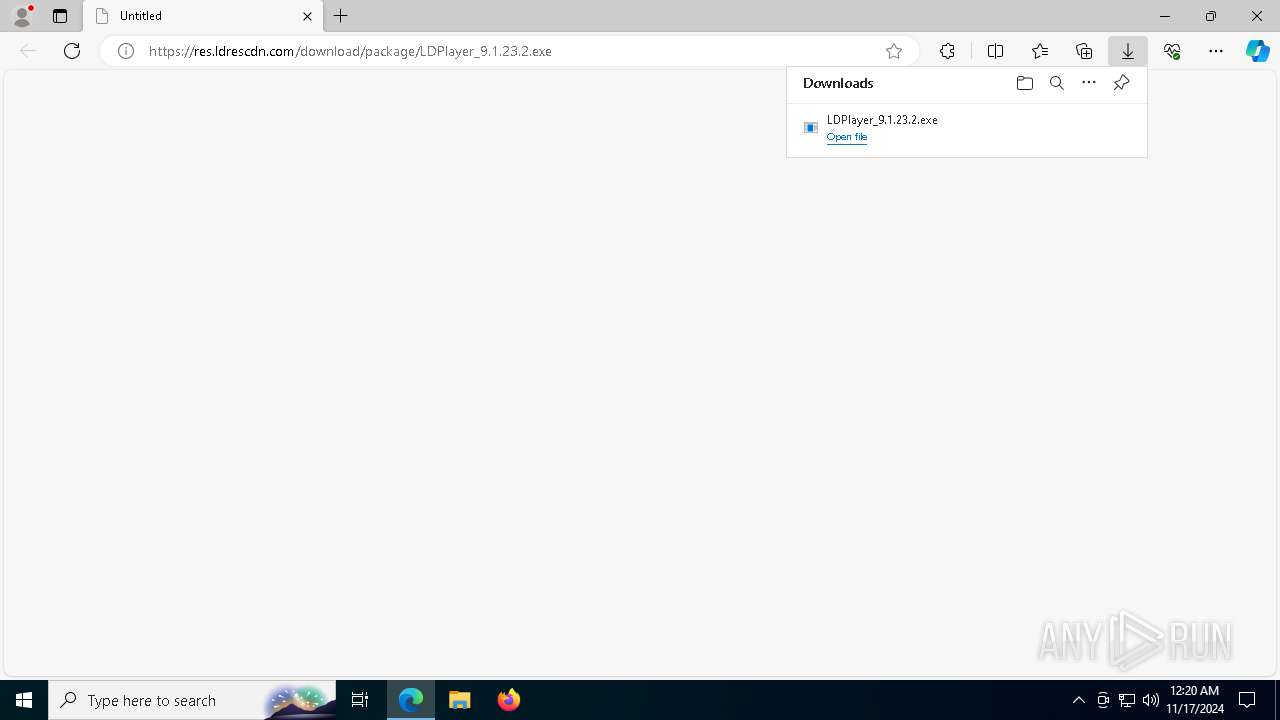
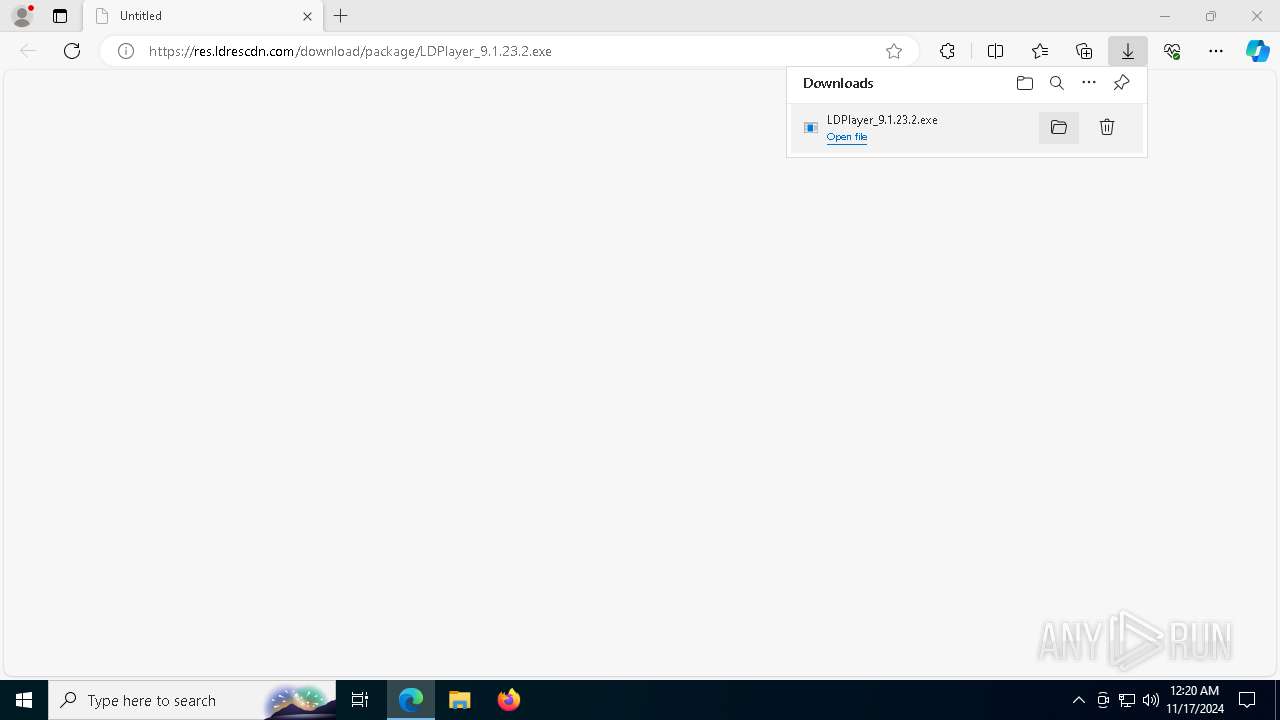
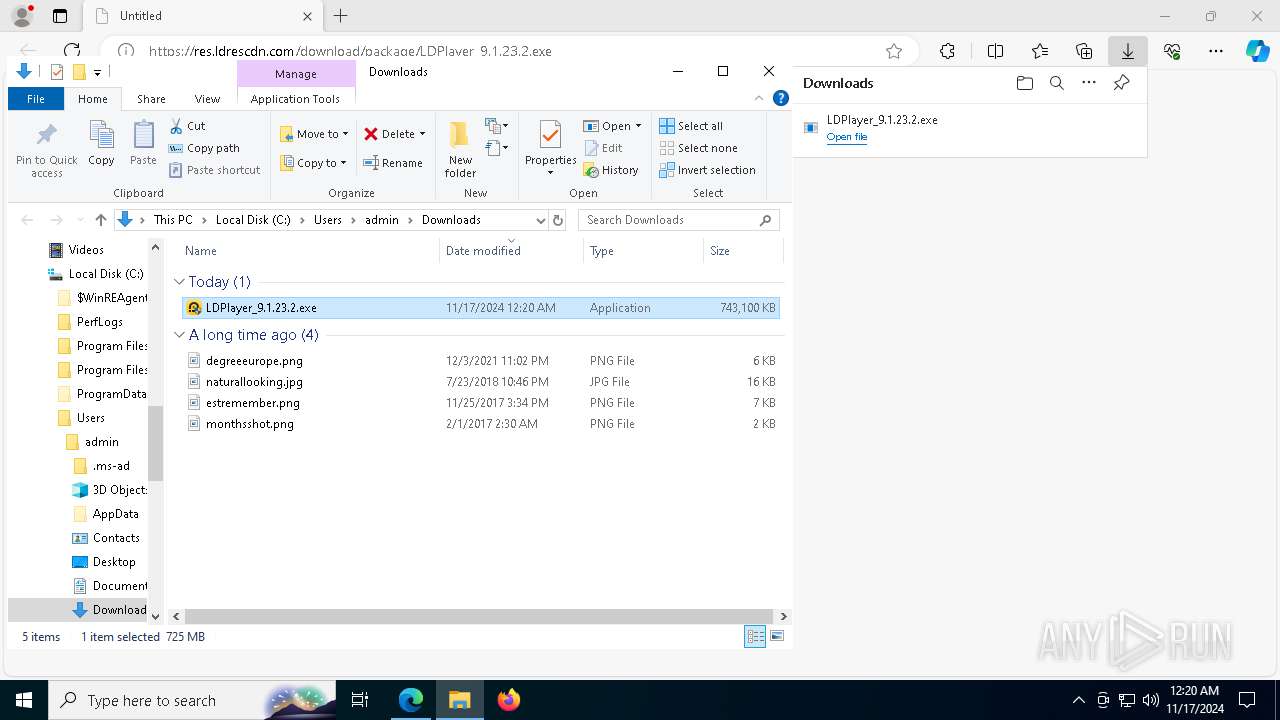
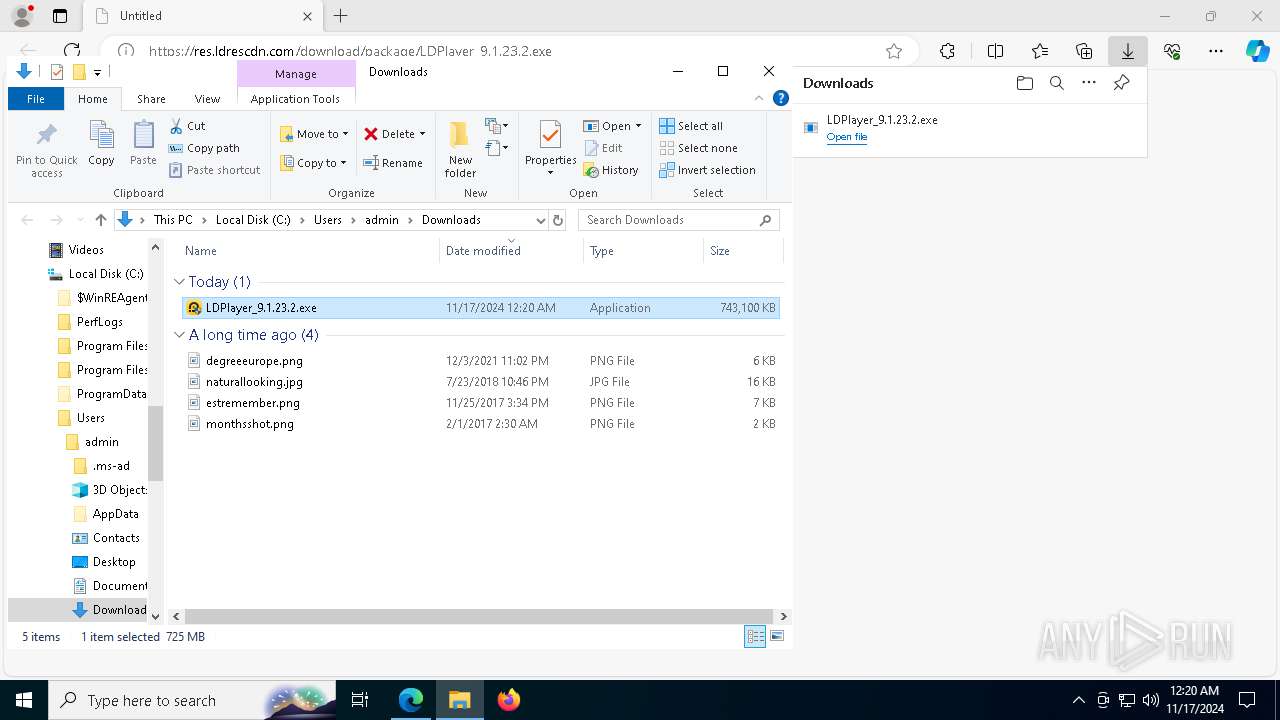
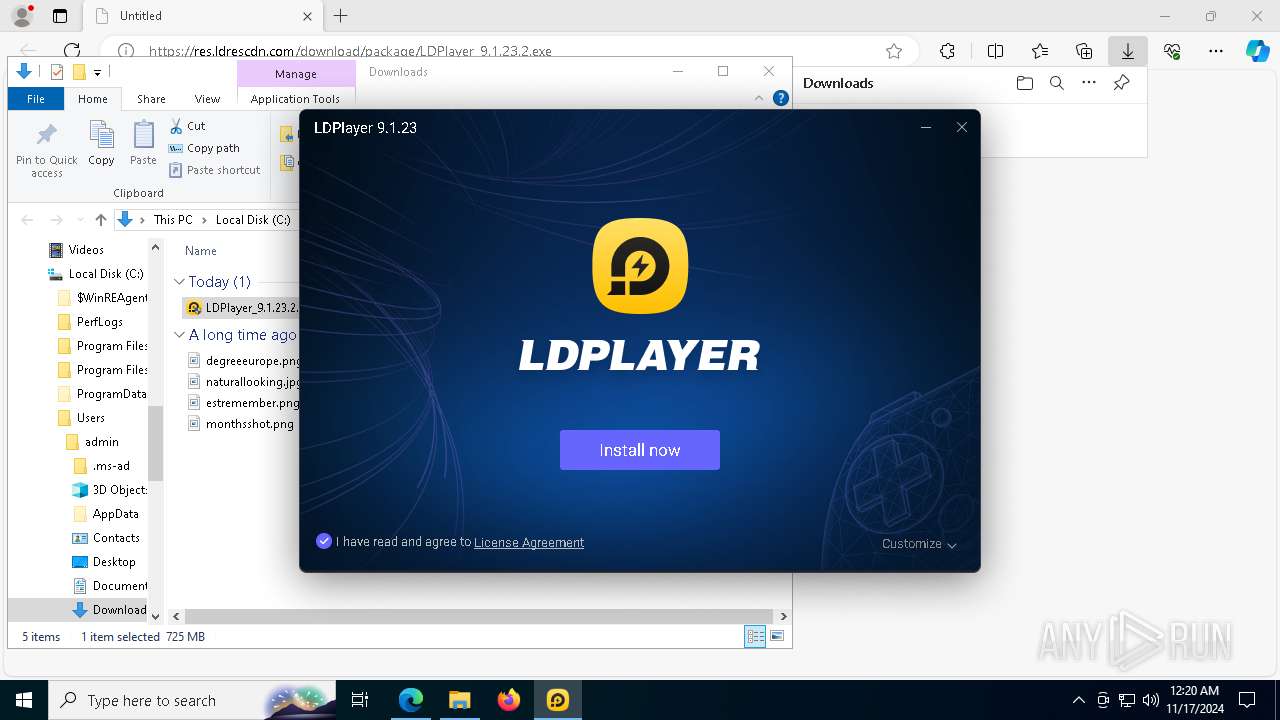
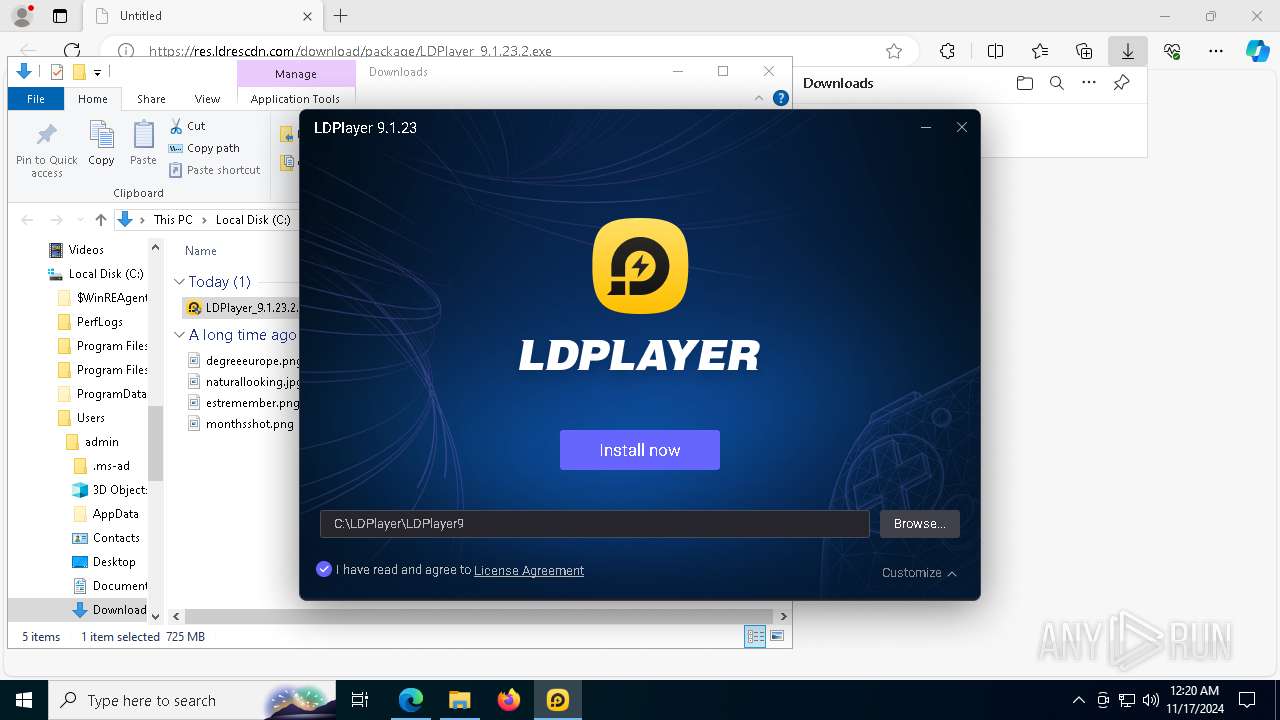
| URL: | https://res.ldrescdn.com/download/package/LDPlayer_9.1.23.2.exe |
| Full analysis: | https://app.any.run/tasks/ad178dd0-8edd-4db7-aa00-20e100a08b23 |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2024, 00:17:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 6F5F37CE87E87929D6D5B9709D552407 |
| SHA1: | 9963E329D1240847614E78403CAB69C641564A19 |
| SHA256: | 0E5D373AA26D00410778A8AB5D812DB03634B7DA2F2B6BE227396D3AAD02B0ED |
| SSDEEP: | 3:N8F71aKLJrWbExq/LXrA:2t8jjU |
MALICIOUS
Starts NET.EXE for service management
- dnrepairer.exe (PID: 7012)
- net.exe (PID: 1048)
Registers / Runs the DLL via REGSVR32.EXE
- dnrepairer.exe (PID: 7012)
SUSPICIOUS
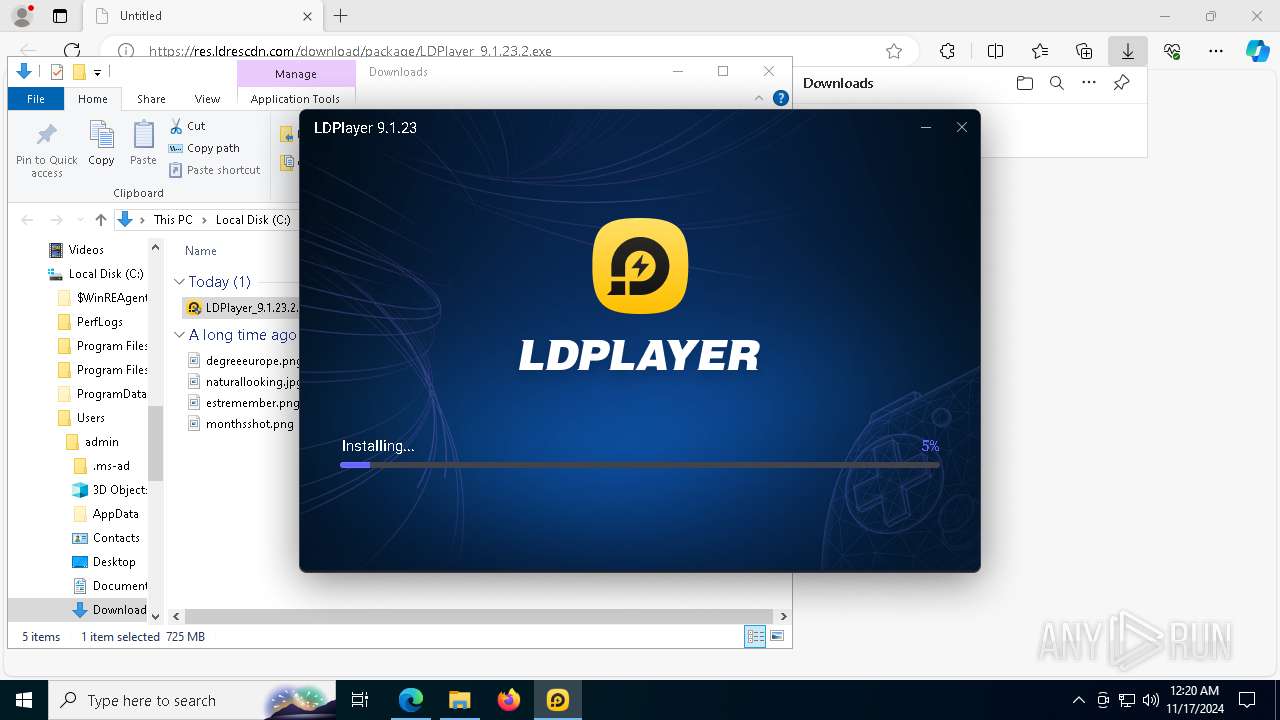
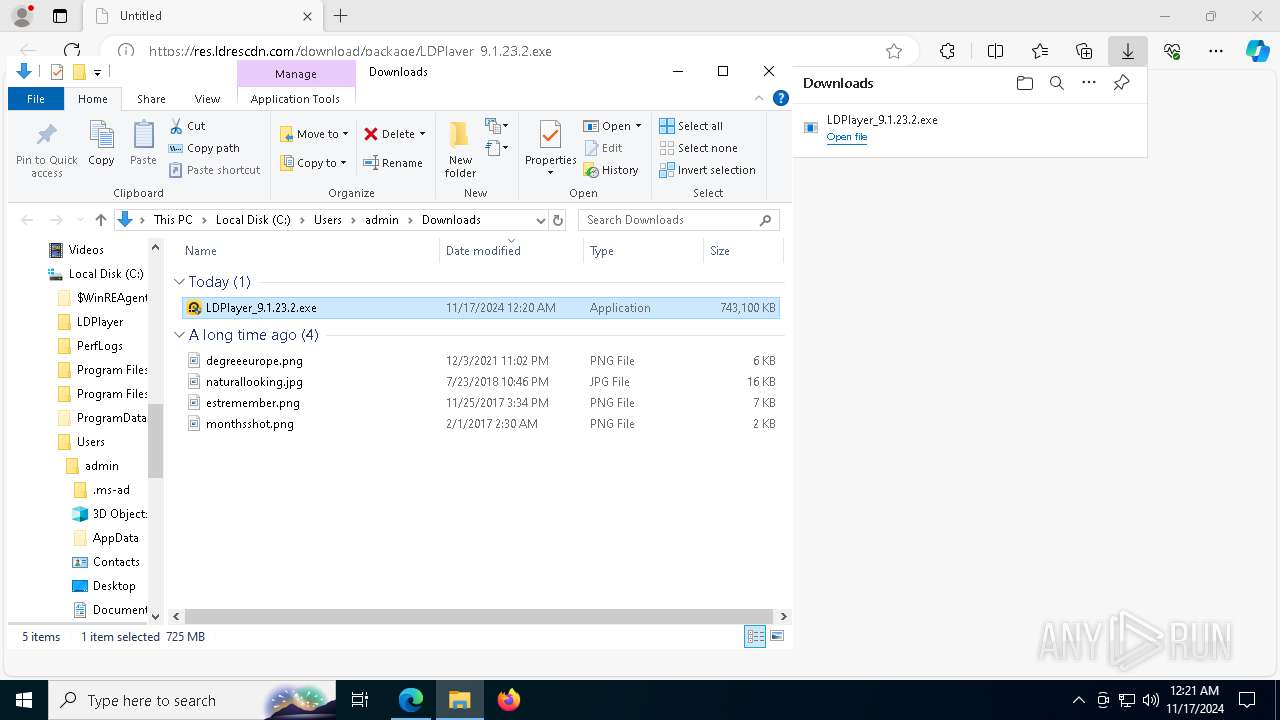
Executable content was dropped or overwritten
- LDPlayer_9.1.23.2.exe (PID: 7452)
- Dism.exe (PID: 6384)
- dnplayer.exe (PID: 6128)
- dnrepairer.exe (PID: 7012)
Drops 7-zip archiver for unpacking
- LDPlayer_9.1.23.2.exe (PID: 7452)
The process drops C-runtime libraries
- LDPlayer_9.1.23.2.exe (PID: 7452)
- dnrepairer.exe (PID: 7012)
- dnplayer.exe (PID: 6128)
Process drops legitimate windows executable
- LDPlayer_9.1.23.2.exe (PID: 7452)
- dnrepairer.exe (PID: 7012)
- dnplayer.exe (PID: 6128)
Takes ownership (TAKEOWN.EXE)
- dnrepairer.exe (PID: 7012)
- LDPlayer_9.1.23.2.exe (PID: 7452)
Uses ICACLS.EXE to modify access control lists
- dnrepairer.exe (PID: 7012)
- LDPlayer_9.1.23.2.exe (PID: 7452)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 8112)
Drops a system driver (possible attempt to evade defenses)
- dnrepairer.exe (PID: 7012)
Starts POWERSHELL.EXE for commands execution
- dnrepairer.exe (PID: 7012)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 6428)
- msedge.exe (PID: 8132)
Checks supported languages
- identity_helper.exe (PID: 7972)
Reads the computer name
- identity_helper.exe (PID: 7972)
Reads Environment values
- identity_helper.exe (PID: 7972)
The process uses the downloaded file
- msedge.exe (PID: 3972)
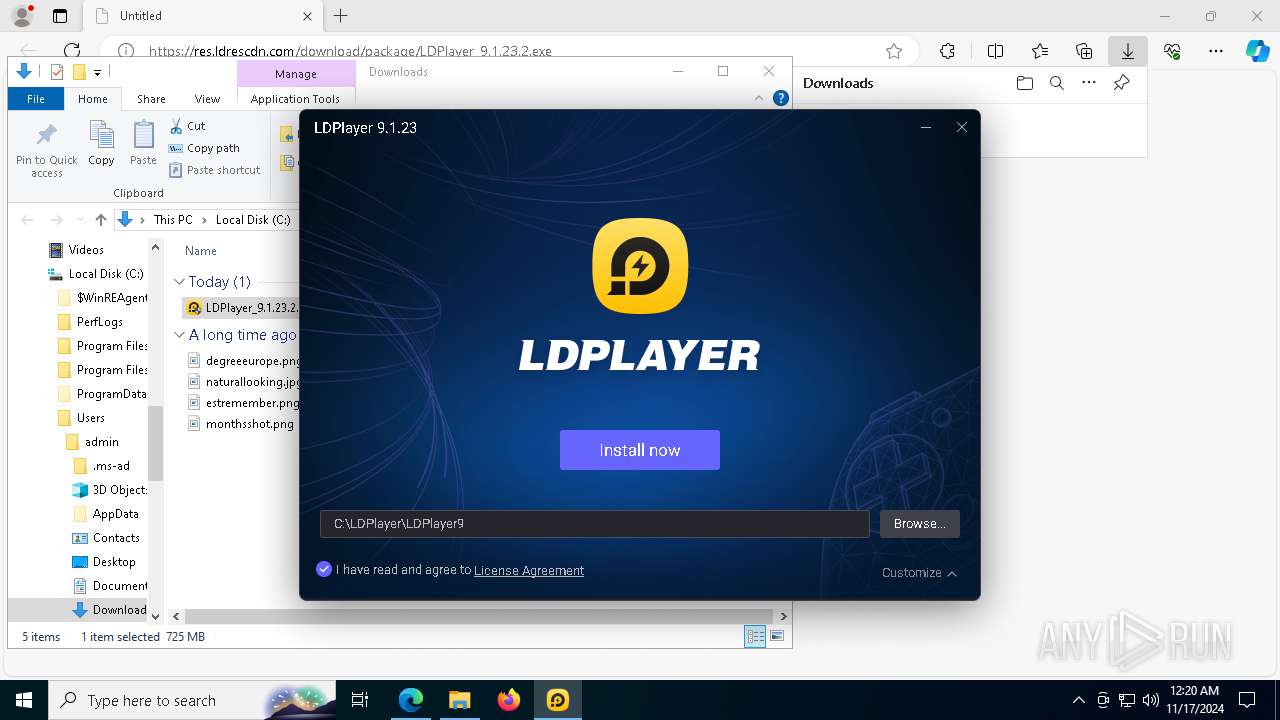
Manual execution by a user
- LDPlayer_9.1.23.2.exe (PID: 7240)
- LDPlayer_9.1.23.2.exe (PID: 7452)
Sends debugging messages
- Dism.exe (PID: 6384)
- DismHost.exe (PID: 8112)
- dnplayer.exe (PID: 6128)
- Ld9BoxHeadless.exe (PID: 3076)
- Ld9BoxHeadless.exe (PID: 6604)
- Ld9BoxHeadless.exe (PID: 6268)
- Ld9BoxHeadless.exe (PID: 7380)
- Ld9BoxHeadless.exe (PID: 7568)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3952)
- powershell.exe (PID: 6448)
- powershell.exe (PID: 2660)
Application launched itself
- msedge.exe (PID: 6428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
287
Monitored processes
142
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2656 --field-trial-handle=2400,i,13904137239428808302,9756324638474373667,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | "regsvr32" Wintrust.dll /s | C:\Windows\SysWOW64\regsvr32.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 696 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=50 --mojo-platform-channel-handle=3028 --field-trial-handle=2400,i,13904137239428808302,9756324638474373667,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 848 | "icacls" "C:\LDPlayer\LDPlayer9\vms" /grant everyone:F /t | C:\Windows\SysWOW64\icacls.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | "net" start cryptsvc | C:\Windows\SysWOW64\net.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6372 --field-trial-handle=2400,i,13904137239428808302,9756324638474373667,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1200 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1584 | "takeown" /f C:\LDPlayer\ldmutiplayer\ /r /d y | C:\Windows\SysWOW64\takeown.exe | — | LDPlayer_9.1.23.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
69 373
Read events
68 870
Write events
474
Delete events
29
Modification events
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AB4C7F01A7852F00 | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 148D8901A7852F00 | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262888 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B737C3EE-A2A8-46B4-B12C-8E87328B6128} | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 34BFB301A7852F00 | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
486
Suspicious files
740
Text files
227
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b07c.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b07c.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b09c.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b09c.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b0bb.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
221
DNS requests
206
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | SE | binary | 1.01 Kb | whitelisted |
6704 | msedge.exe | GET | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1731865031&P2=404&P3=2&P4=JhQiRV%2bzkxKQJwAdjpFu7SmgM5rckHSAaMQRcqvnv6avoQ0pMIZQifkbgG6r80rDuveQONcf8vrpWqcWp2d2cQ%3d%3d | DE | binary | 1.32 Kb | whitelisted |
4676 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
4676 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6704 | msedge.exe | GET | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1731865031&P2=404&P3=2&P4=Eczmge7FN%2fzb%2f4HH9M6Xc5K7clpZstIov4veUrItZ2tq%2bKSnbxO2CBka6h4jrFvPgQWhV%2b37IldVzOcfwPyDwA%3d%3d | DE | binary | 1.60 Mb | whitelisted |
6704 | msedge.exe | GET | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/75a7a2f7-7a99-4b37-9d2a-dfb661115d14?P1=1731998229&P2=404&P3=2&P4=lK9YkEBfKqU8oUeF7X91609YVIewC6g%2bm%2fcjblmuIO0a3ySgv28xF8WVBTOWyvA1hoYtEIF4vKFkyJrXvi5n0w%3d%3d | DE | binary | 75.3 Kb | whitelisted |
7672 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7048 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6704 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6428 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6704 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6704 | msedge.exe | 142.250.185.163:443 | update.googleapis.com | GOOGLE | US | whitelisted |
6704 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6704 | msedge.exe | 23.50.131.74:443 | bzib.nelreports.net | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
res.ldrescdn.com |
| unknown |
business.bing.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6704 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6704 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
Process | Message |
|---|---|
Dism.exe | PID=6384 TID=6344 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=6384 TID=6344 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=6384 TID=6344 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=6384 TID=6344 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=6384 TID=6344 Loading Provider from location C:\WINDOWS\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=6384 TID=6344 Connecting to the provider located at C:\WINDOWS\System32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |
DismHost.exe | PID=8112 TID=6964 Disconnecting Provider: DISMLogger - CDISMProviderStore::Internal_DisconnectProvider |
DismHost.exe | PID=8112 TID=6964 Encountered a loaded provider DISMLogger. - CDISMProviderStore::Internal_DisconnectProvider |
DismHost.exe | PID=8112 TID=6964 Disconnecting the provider store - CDISMImageSession::Final_OnDisconnect |
Dism.exe | PID=6384 TID=6344 Disconnecting Provider: DISMLogger - CDISMProviderStore::Internal_DisconnectProvider |