| File name: | request.doc |
| Full analysis: | https://app.any.run/tasks/2a243aa2-1033-4406-8277-c7f41b530dc7 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2021, 17:50:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 42F66731F39893D2BEDAF80C03F11811 |
| SHA1: | 8097A366659C9A12ED144C9D29657EEFA4CDB015 |
| SHA256: | 0E5991D269C5D709BC832931174F264F2D7C46452A55D649017CB07A2D25EFF0 |
| SSDEEP: | 1536:kxaktWp/QV1AQ07yz9eDlQt5HrWYDQhlPfiolVtAJTeS6g:kxC/skiwU5ka5itg |
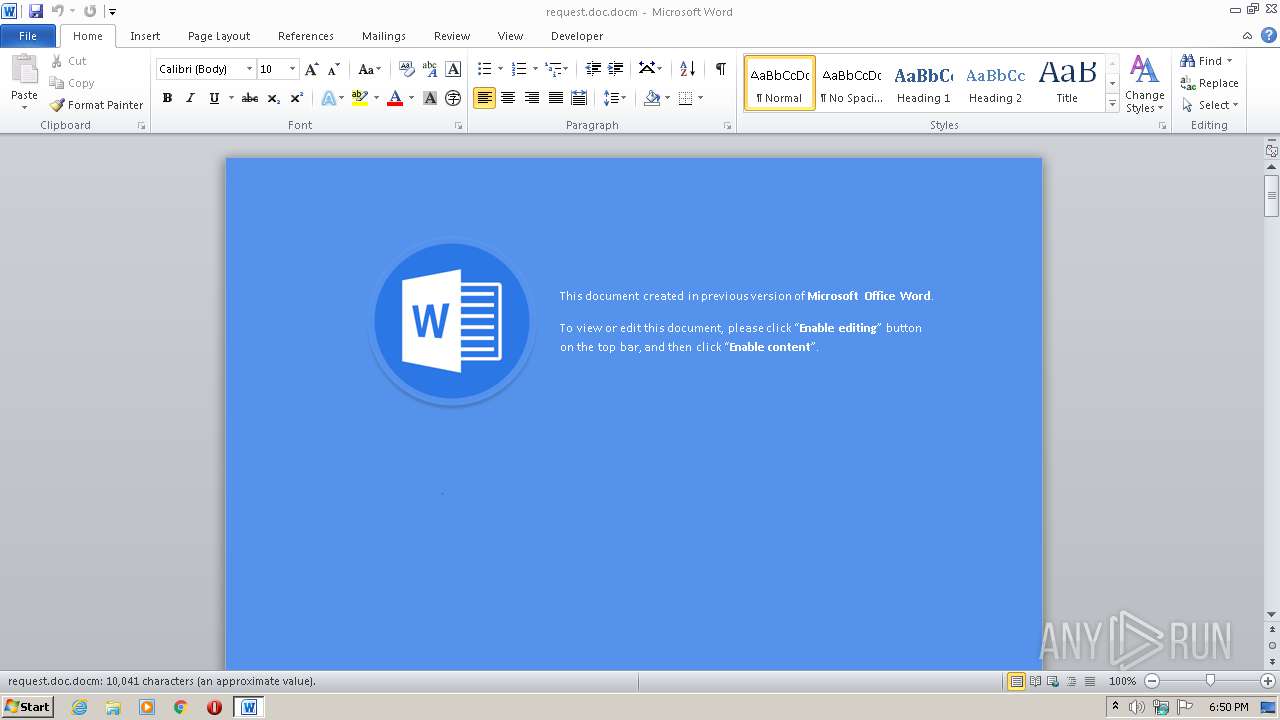
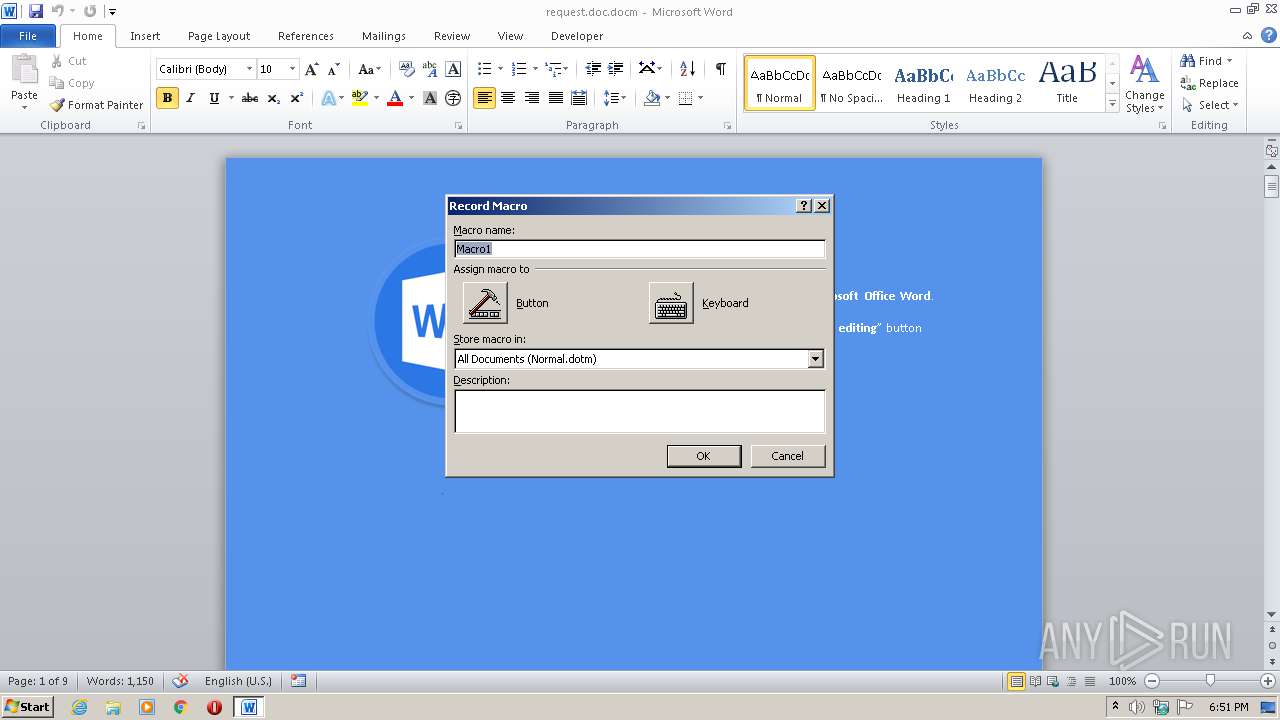
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3720)
Starts MSHTA.EXE for opening HTA or HTMLS files
- WINWORD.EXE (PID: 3720)
SUSPICIOUS
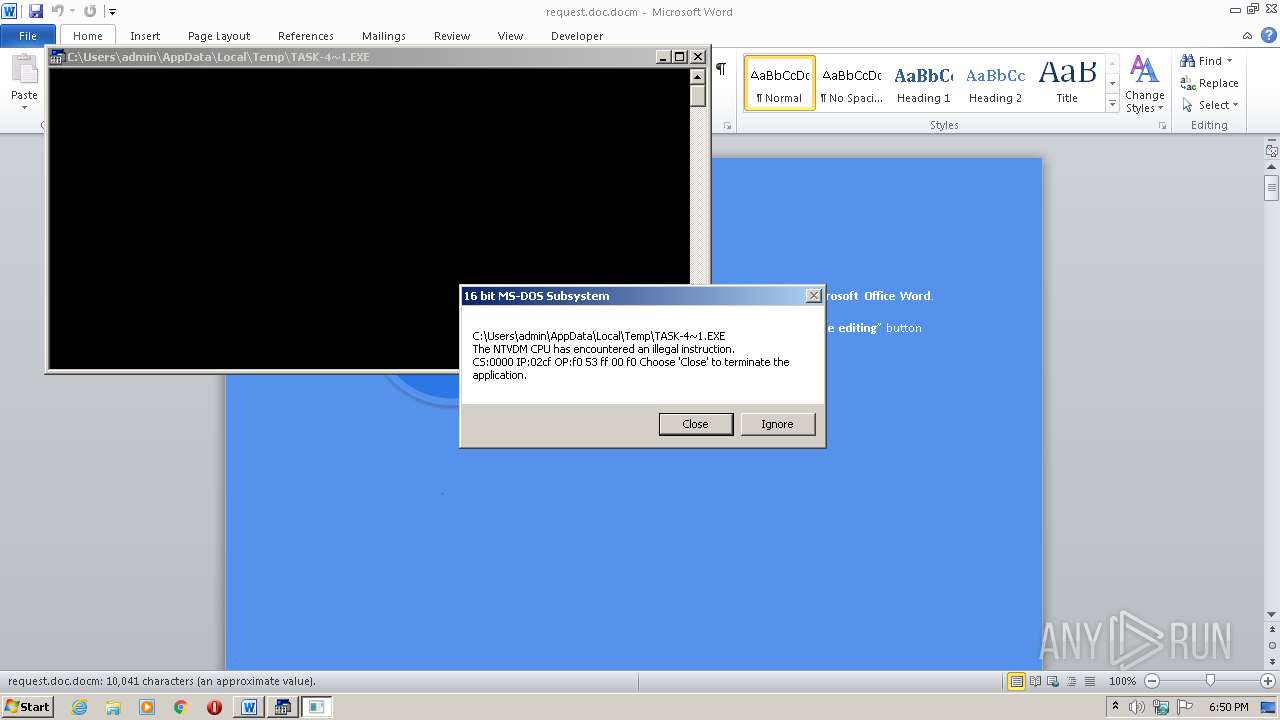
Executes application which crashes
- mshta.exe (PID: 1660)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3720)
Reads internet explorer settings
- mshta.exe (PID: 1660)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3720)
Dropped object may contain Bitcoin addresses
- WINWORD.EXE (PID: 3720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
XMP
| Creator: | Windows User |
|---|
XML
| Tag00sfhcrhaexjcg8gfovtxgrf: | xs0nzbgamlpmzlsiyfaj3lr |
|---|---|
| ModifyDate: | 2021:05:17 08:52:00Z |
| CreateDate: | 2020:11:10 17:00:00Z |
| RevisionNumber: | 33 |
| LastModifiedBy: | Windows User |
| AppVersion: | 16 |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| CharactersWithSpaces: | 12154 |
| LinksUpToDate: | No |
| Company: | - |
| TitlesOfParts: | - |
| HeadingPairs: |
|
| ScaleCrop: | No |
| Paragraphs: | 24 |
| Lines: | 86 |
| DocSecurity: | None |
| Application: | Microsoft Office Word |
| Characters: | 10361 |
| Words: | 1817 |
| Pages: | 3 |
| TotalEditTime: | 1.9 hours |
| Template: | Normal |
ZIP
| ZipFileName: | [Content_Types].xml |
|---|---|
| ZipUncompressedSize: | 1729 |
| ZipCompressedSize: | 432 |
| ZipCRC: | 0x28edbaef |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0006 |
| ZipRequiredVersion: | 20 |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1660 | mshta.exe "about:<script language=VBScript>moveTo 0,-9999:Execute(CreateObject("Scripting.FileSystemObject").GetStandardStream(0).ReadAll()):sub window_onload:Close:End Sub</script><hta:application showintaskbar=no />" | C:\Windows\system32\mshta.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2540 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3720 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\request.doc.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 152
Read events
1 360
Write events
660
Delete events
132
Modification events
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | - 3 |
Value: 2D203300880E0000010000000000000000000000 | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3720) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF4AD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\30BAF74B.wmf | — | |
MD5:— | SHA256:— | |||
| 3720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1E5970D0.wmf | — | |
MD5:— | SHA256:— | |||
| 2540 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs259.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs269.tmp | — | |
MD5:— | SHA256:— | |||
| 3720 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$quest.doc.docm | pgc | |
MD5:— | SHA256:— | |||
| 3720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\WMPLib.exd | tlb | |
MD5:— | SHA256:— | |||
| 1660 | mshta.exe | C:\Users\admin\AppData\Local\Temp\task-4509.exe | html | |
MD5:— | SHA256:— | |||
| 3720 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1660 | mshta.exe | GET | 404 | 144.168.197.36:80 | http://144.168.197.36/ts/KS8qyPL1yA-fh8c8BXwFfnOGiWotKKIvqQ~~/t6q4Lknm9T-M1FiPi5sCy2xtzZ27J7KabQ~~/ | US | html | 275 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1660 | mshta.exe | 184.30.215.136:443 | docs.microsoft.com | Akamai International B.V. | NL | suspicious |
1660 | mshta.exe | 104.111.245.157:443 | www.trendmicro.com | Akamai International B.V. | NL | suspicious |
1660 | mshta.exe | 144.168.197.36:80 | — | B2 Net Solutions Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
docs.microsoft.com |
| whitelisted |
www.trendmicro.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1660 | mshta.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1660 | mshta.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |