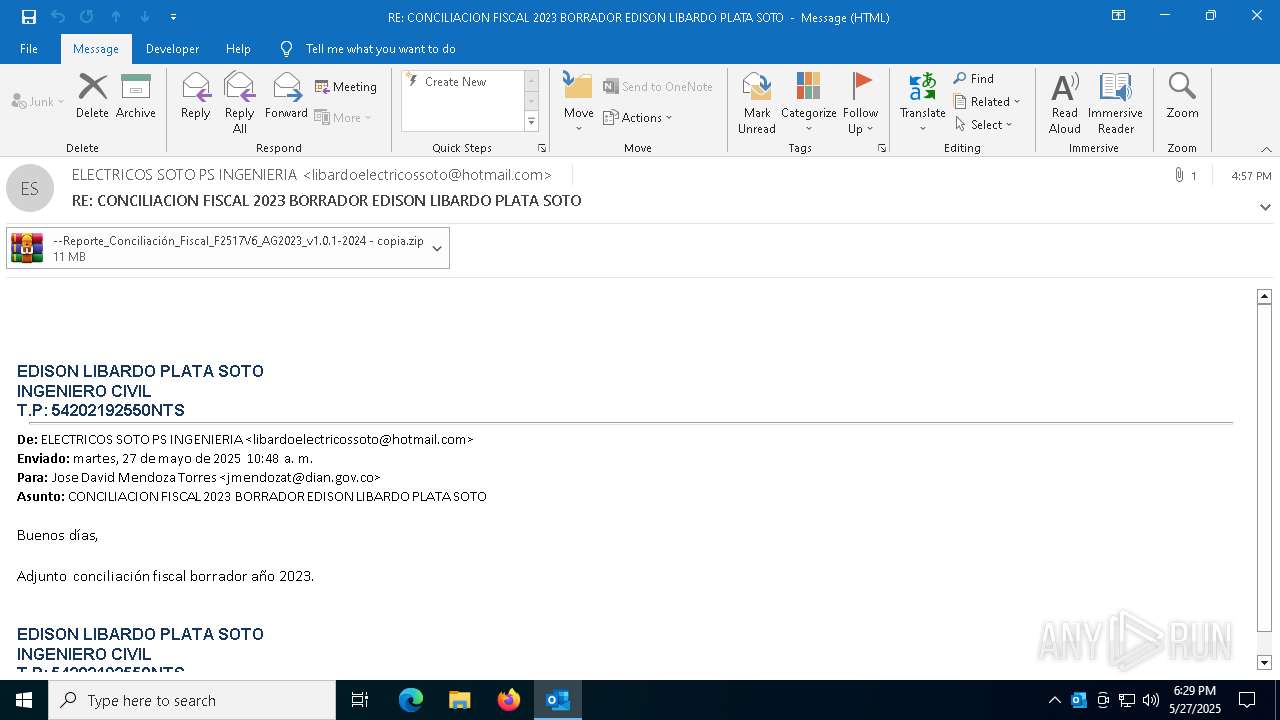
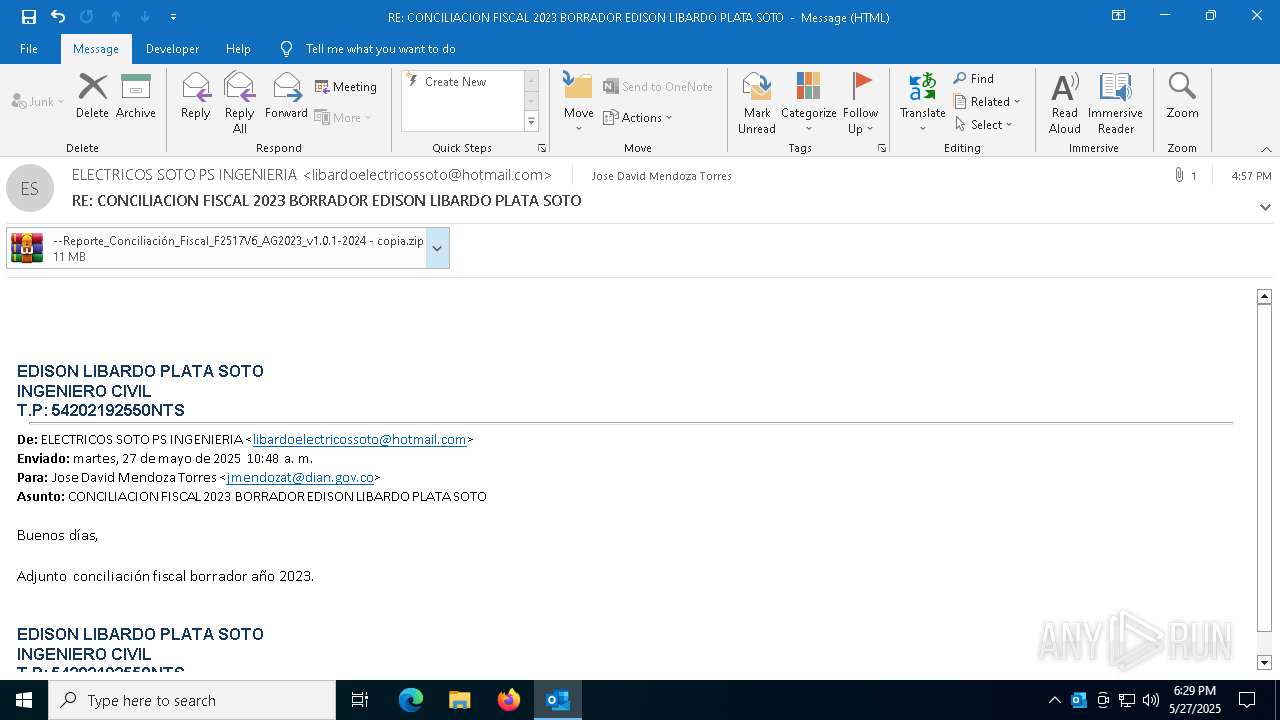
| File name: | RE_ CONCILIACION FISCAL 2023 BORRADOR EDISON LIBARDO PLATA SOTO.eml |
| Full analysis: | https://app.any.run/tasks/9f1c9ccb-fad7-4228-82be-6ae3335c8821 |
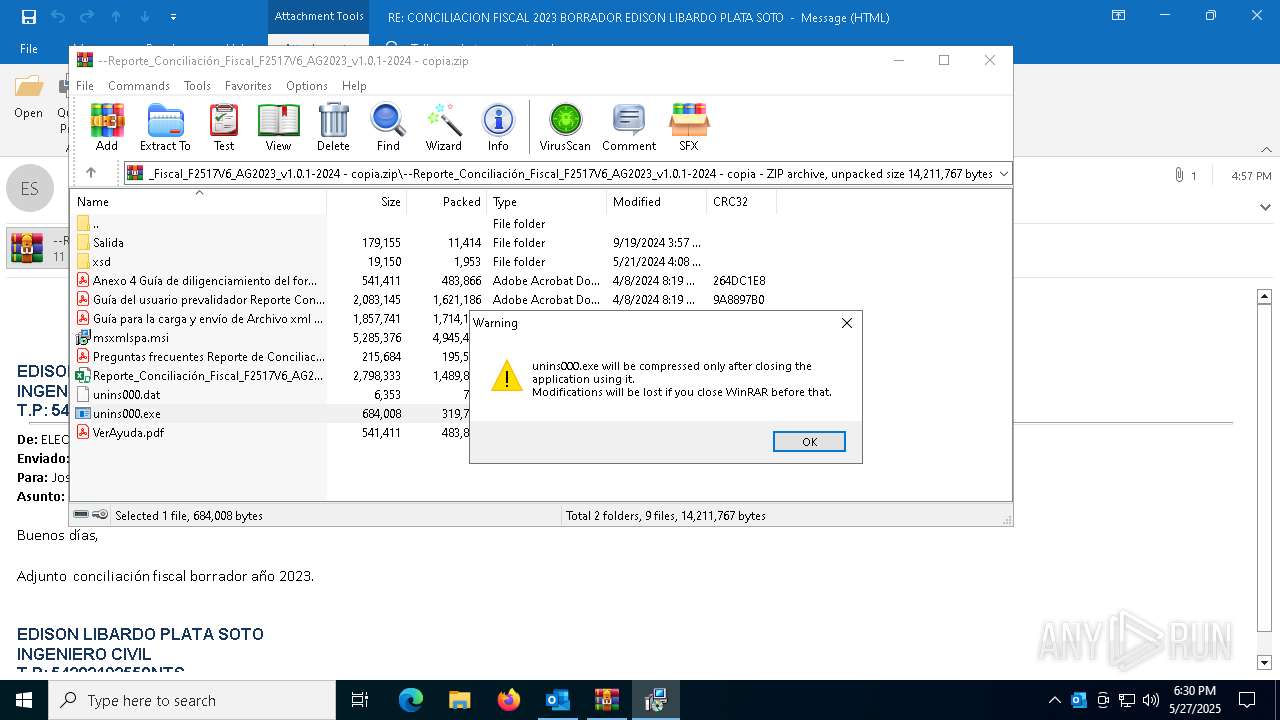
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2025, 18:29:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (729), with CRLF line terminators |
| MD5: | 108F97A9AAEF05F14DF225DF3D695CDF |
| SHA1: | 9A04A3A2257A479E6944BB077FEAE30ADBFC8DB2 |
| SHA256: | 0E56502C0578F137B9E778769DCD77E6EEA990438A876FF6C8306C429900502C |
| SSDEEP: | 49152:iI+vwscN6/MvLjmT6GgnCr8Xc24jVCy9hGSHkOhcqHhbK2BcHsbUV1/u+NHd++sr:Q |
MALICIOUS
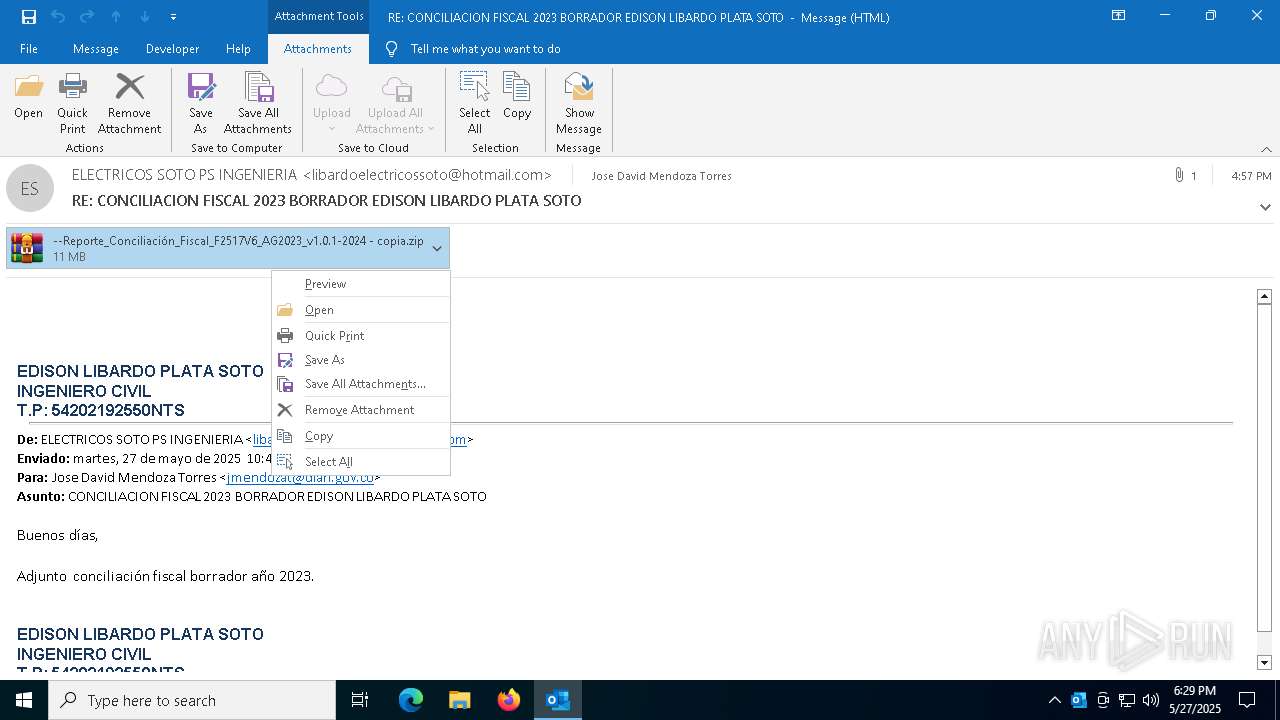
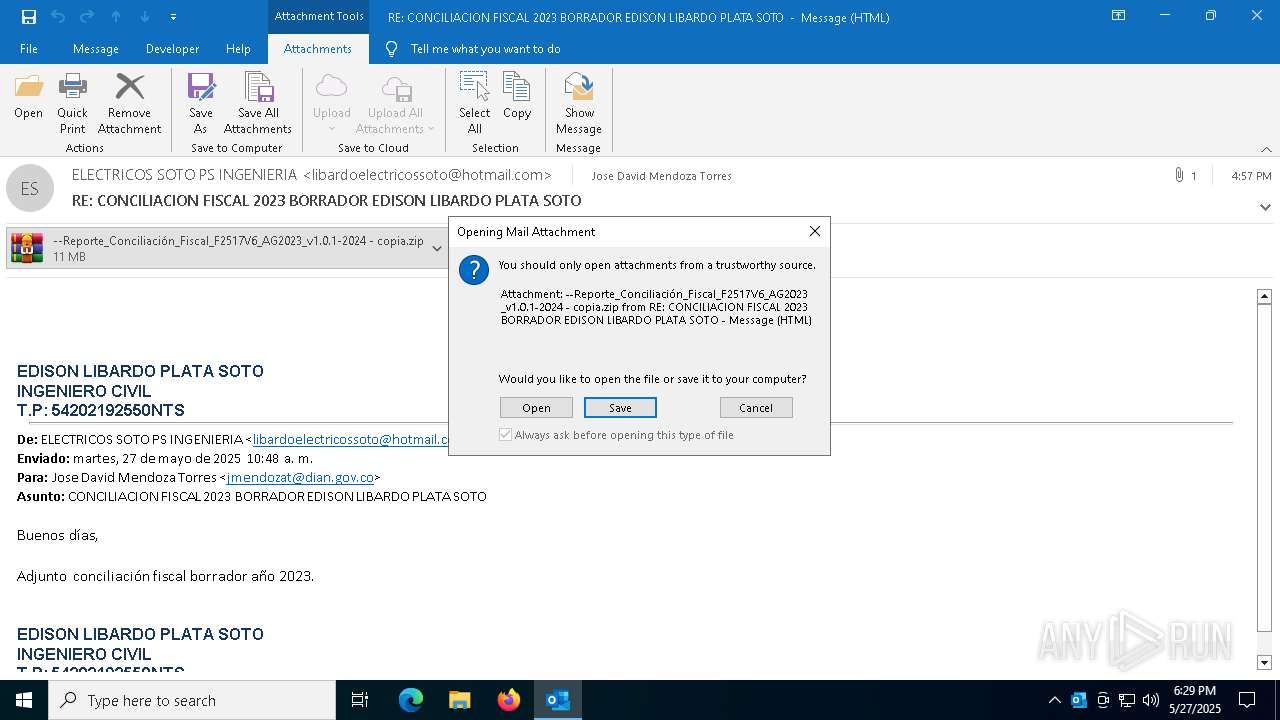
Generic archive extractor
- OUTLOOK.EXE (PID: 7296)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1764)
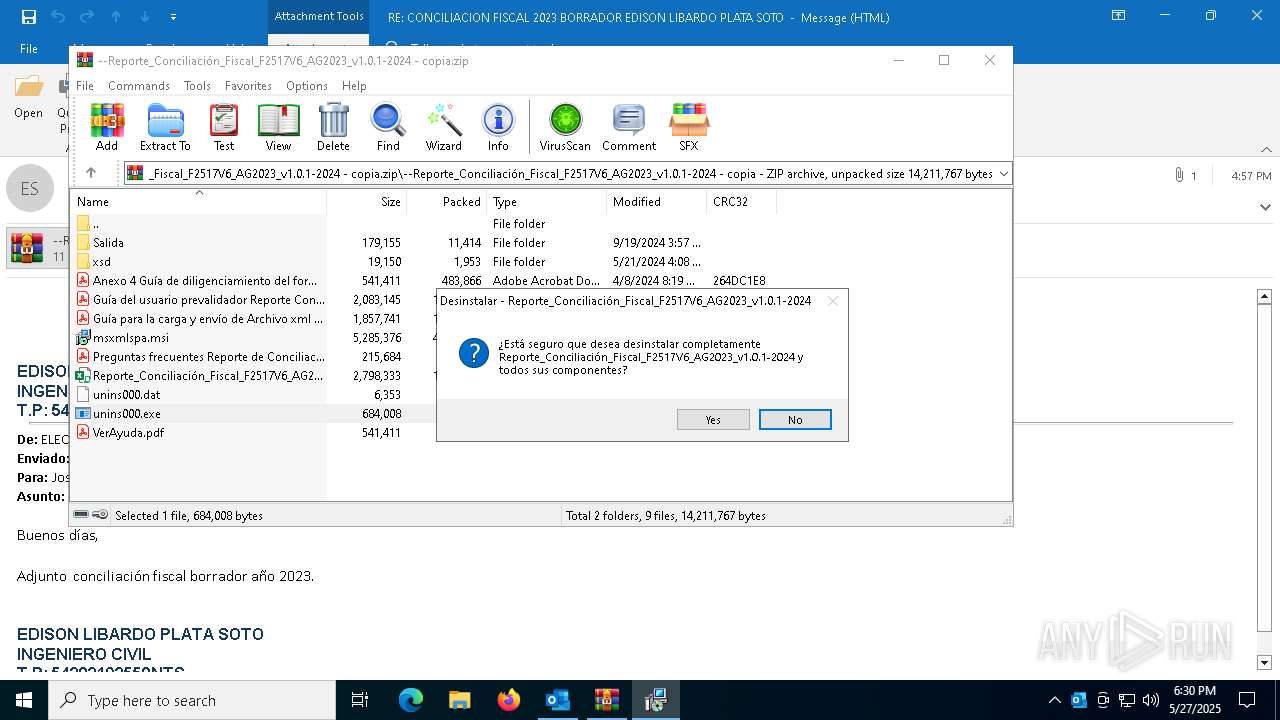
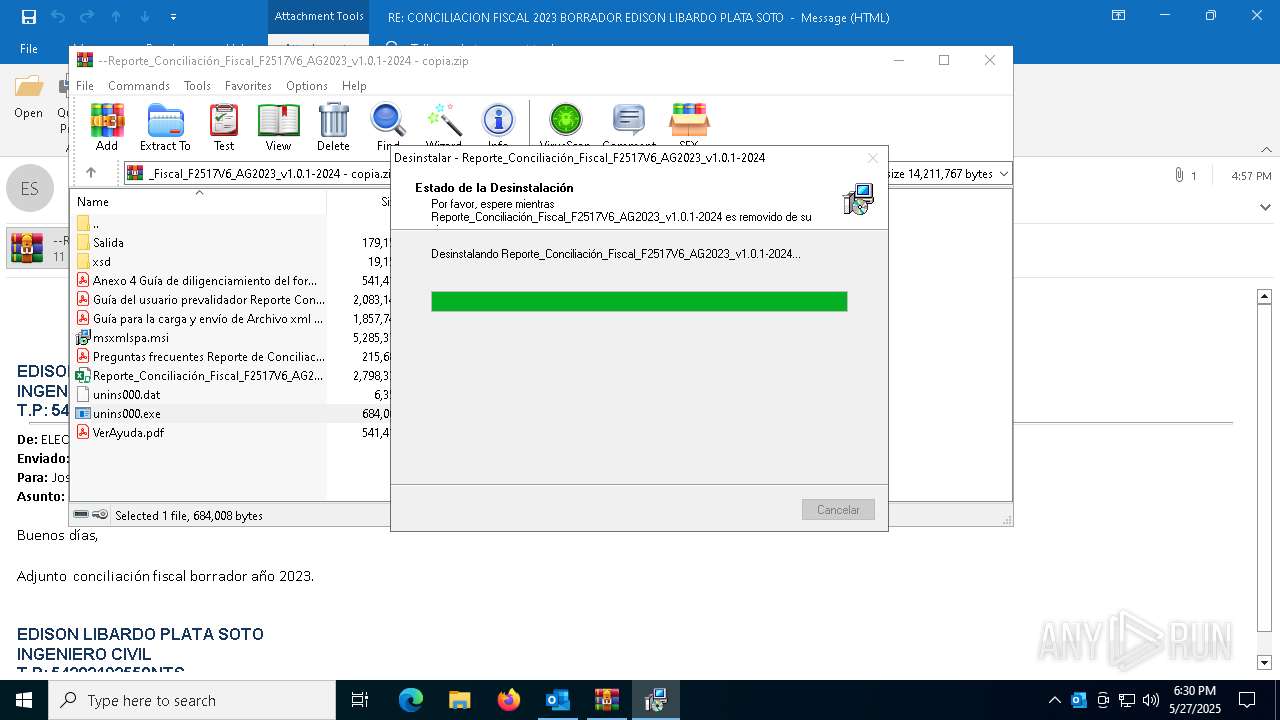
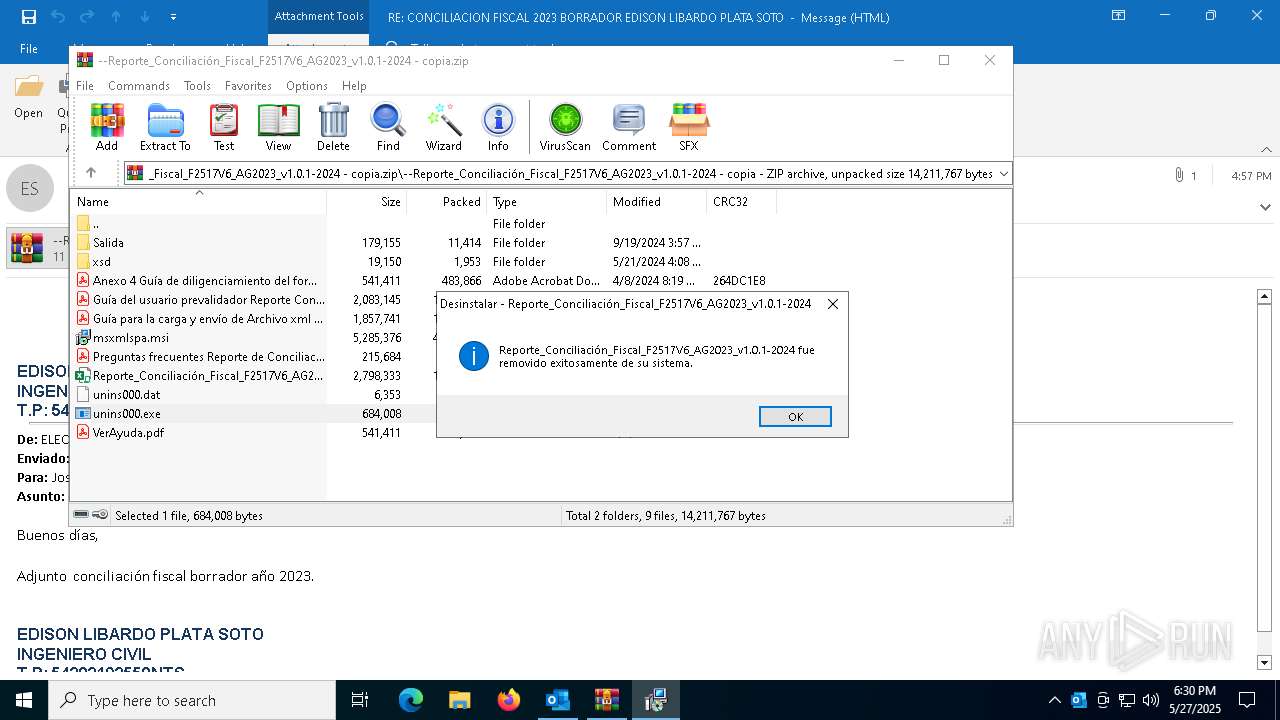
Starts itself from another location
- unins000.exe (PID: 1020)
Starts application with an unusual extension
- unins000.exe (PID: 1020)
Executable content was dropped or overwritten
- unins000.exe (PID: 1020)
- _iu14D2N.tmp (PID: 1228)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 1764)
- OUTLOOK.EXE (PID: 7296)
- unins000.exe (PID: 1020)
Checks supported languages
- unins000.exe (PID: 1020)
- _iu14D2N.tmp (PID: 1228)
Reads the computer name
- unins000.exe (PID: 1020)
- _iu14D2N.tmp (PID: 1228)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1764)
Create files in a temporary directory
- unins000.exe (PID: 1020)
- _iu14D2N.tmp (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 3) (100) |
|---|
Total processes
135
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
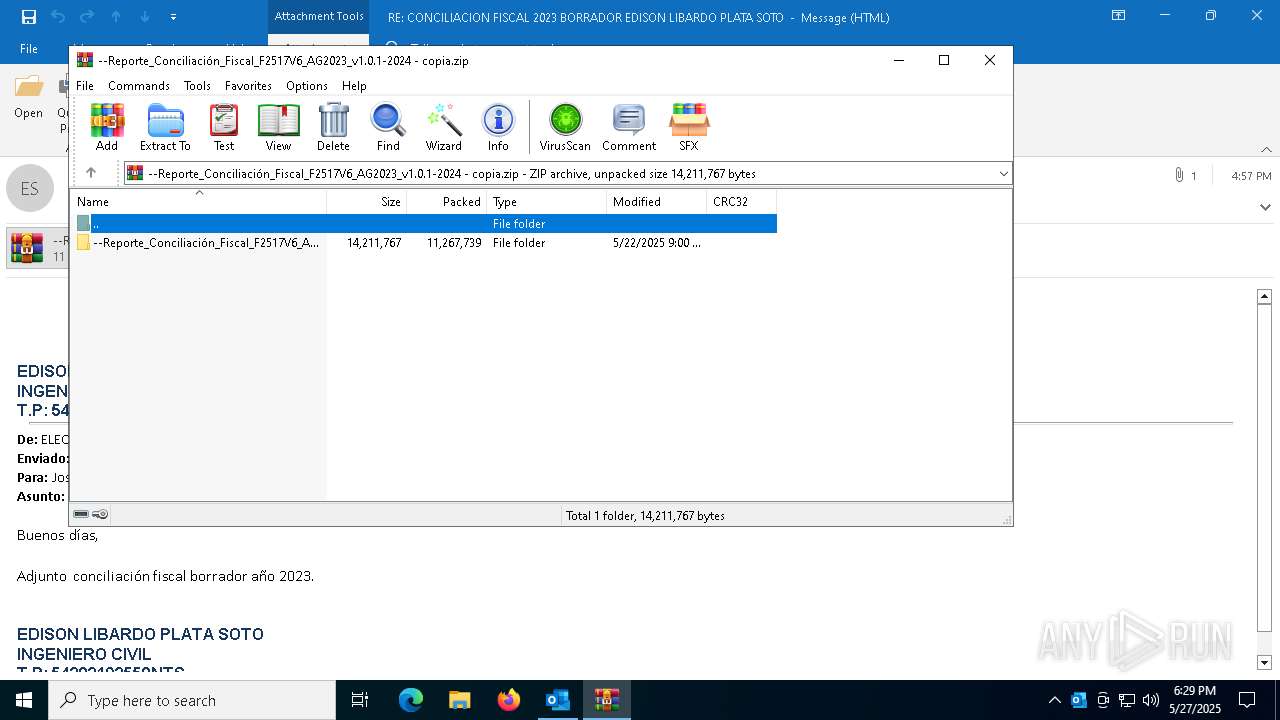
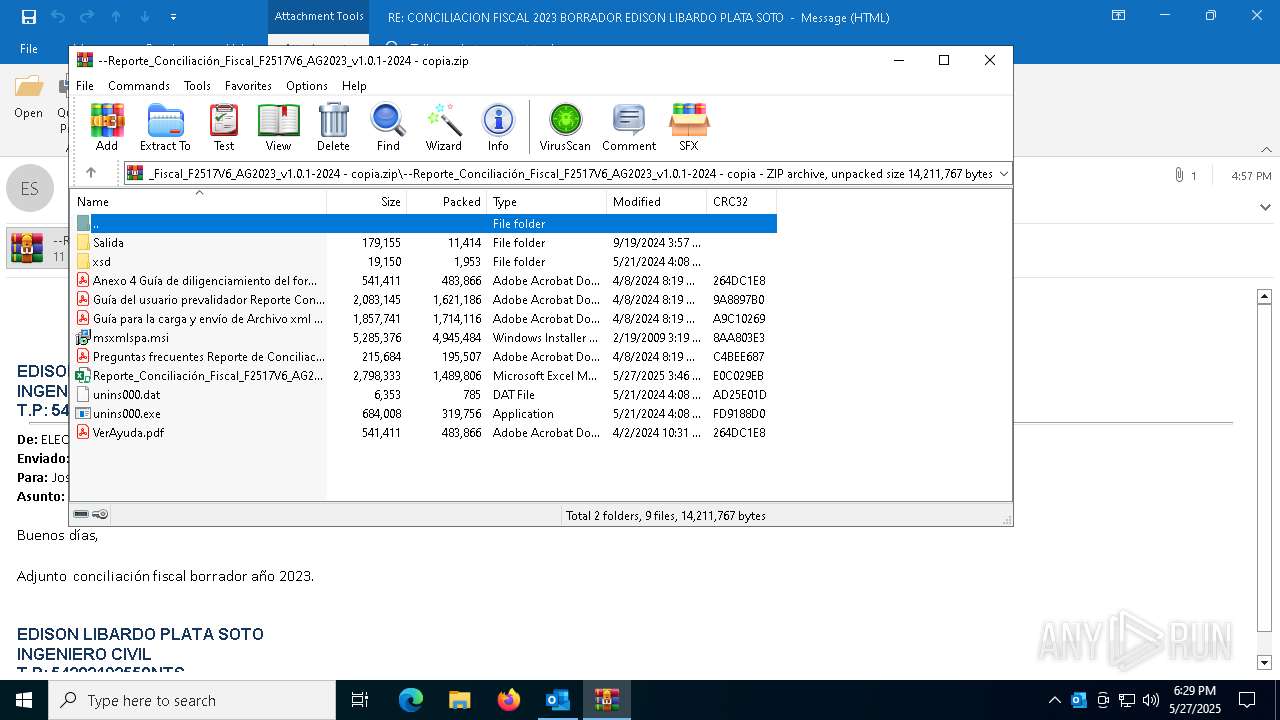
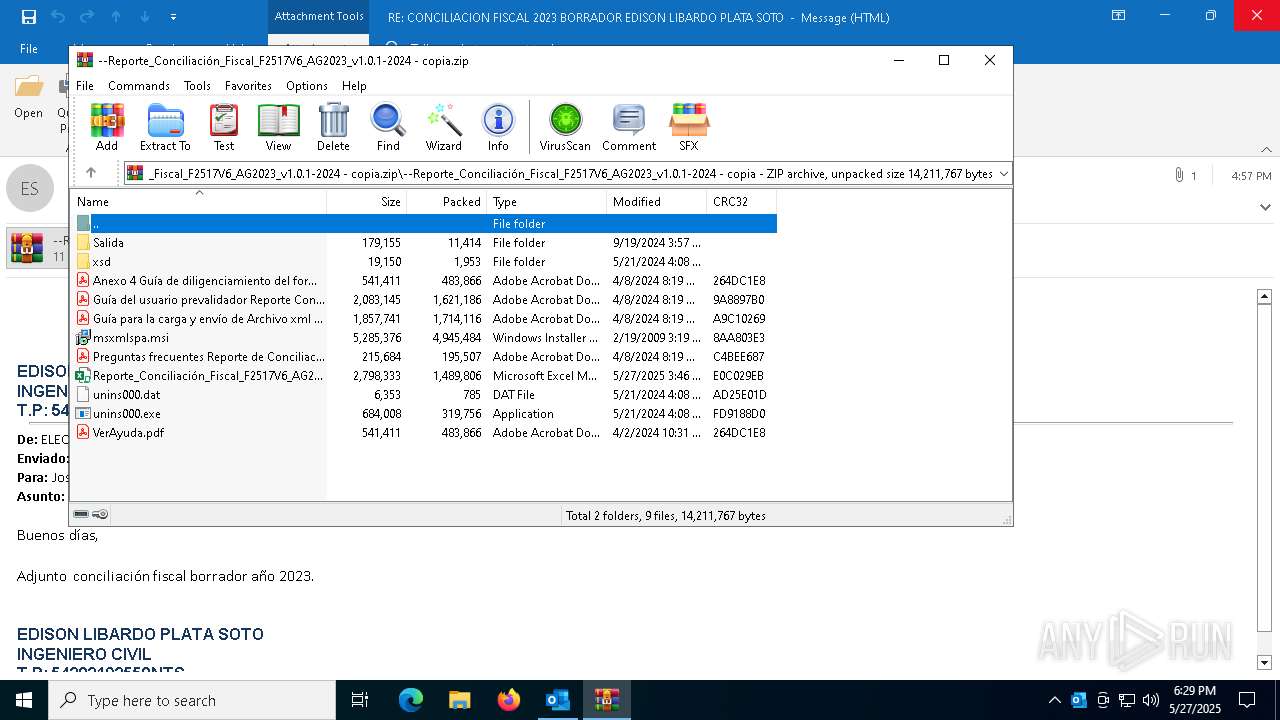
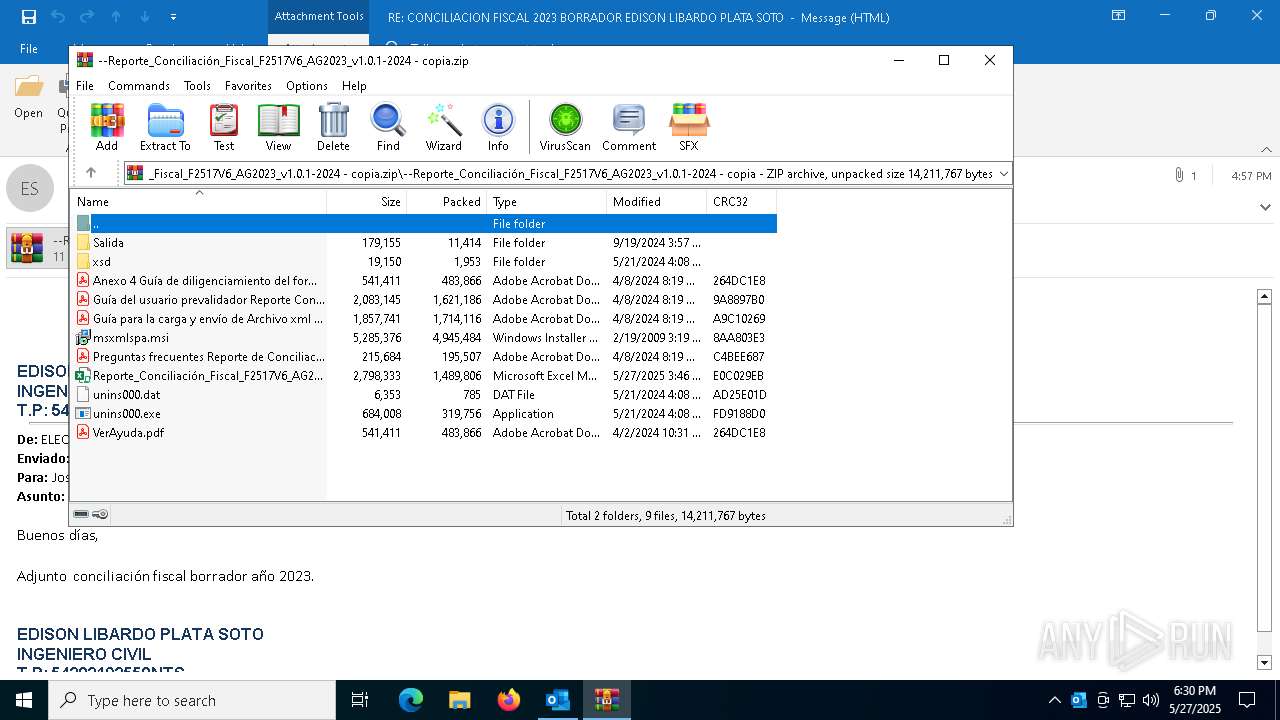
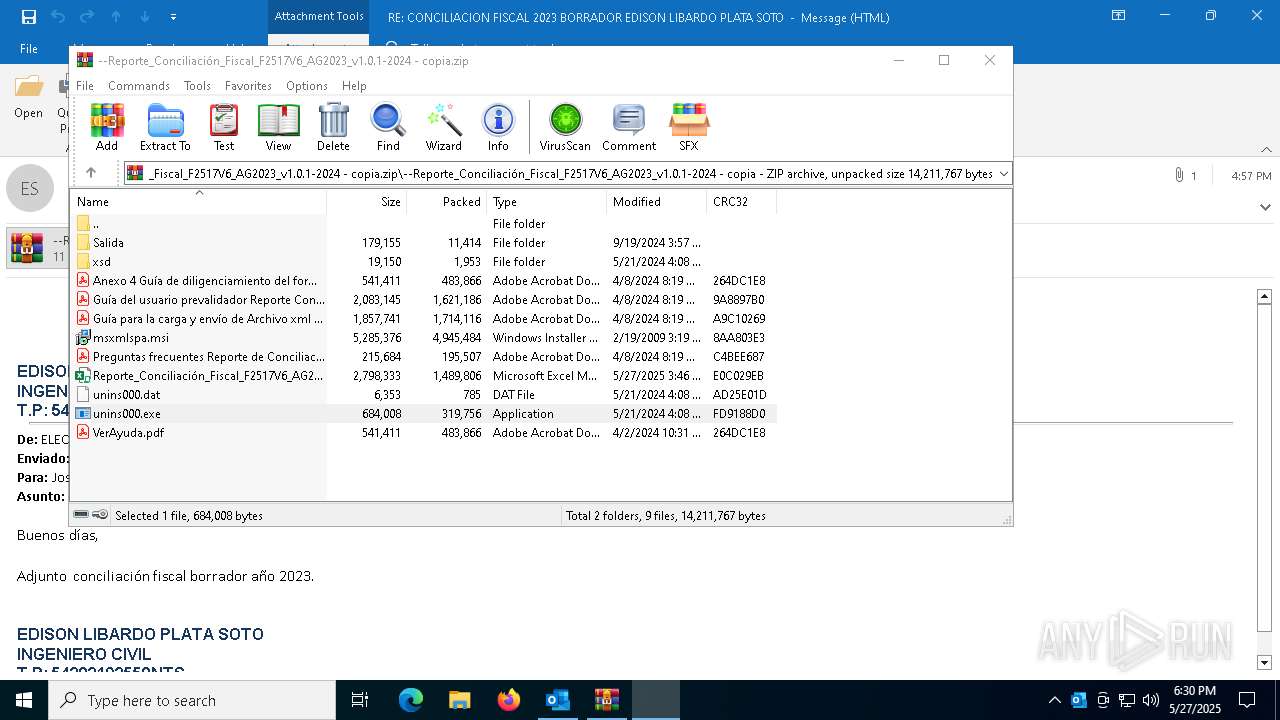
| 1020 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\unins000.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\unins000.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.44.0.0 Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\unins000.exe" /FIRSTPHASEWND=$203FE | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.44.0.0 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\B9WMB6CE\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia.zip" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7084 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\unins000.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\unins000.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 3221226540 Version: 51.44.0.0 Modules
| |||||||||||||||
| 7296 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\RE_ CONCILIACION FISCAL 2023 BORRADOR EDISON LIBARDO PLATA SOTO.eml" | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7844 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "562AD179-E777-477E-9AEC-3B187D0E3725" "514470A3-150B-4EC1-8EF3-7B617C5F3B0B" "7296" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
Total events
14 195
Read events
13 057
Write events
1 017
Delete events
121
Modification events
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ~t- |
Value: 7E742D00801C00000400000000000000BF0E584635CFDB0196000000010000008E000000430043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C0045006D00610069006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Resiliency\StartupItems |
| Operation: | delete value | Name: | ~t- |
Value: 瑾-ᲀ | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Resiliency\StartupItems |
| Operation: | delete value | Name: | {j- |
Value: 橻-ᲀ | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Resiliency\StartupItems |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Resiliency |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\7296 |
| Operation: | write | Name: | 0 |
Value: 0B0E10BABD8F33ABA7E243A4C5338944E46BC8230046B1FDF7A5D4E6F3ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C5118039D2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (7296) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
4
Suspicious files
12
Text files
10
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7296 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7296 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\olkCB70.tmp | — | |
MD5:— | SHA256:— | |||
| 1764 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\msxmlspa.msi | — | |
MD5:— | SHA256:— | |||
| 7296 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\05A71122-E9AF-47C8-9179-F011B2AE522C | xml | |
MD5:4068C57C73142A6A99A2F7A6C6326325 | SHA256:72ABD966057FD504AD224FF56F314729260E97DDBBDEA1EDA746B5C4EFF3204C | |||
| 1764 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\Guía para la carga y envío de Archivo xml formato 2517v6 AG2023.pdf | ||
MD5:D44BB35E343864B9BB615D3984299109 | SHA256:2D07A6A39999421D348FD7F835F422CF5657B2C32A32D13AF065FB80B30D9873 | |||
| 7296 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:3A4067E664FA6480A5837B0BEB5F400F | SHA256:E8CE8D6D91B8534E753E6F6E47E7D96F33A8B3951CCC58C57A16E1B87F8A91D1 | |||
| 1764 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\unins000.dat | dat | |
MD5:6A09202840385658A74934CC2C6C2DD3 | SHA256:4027CEE136CF8829B91B6C3EFB8A6DCE83CFE62125236AF5908B6393504C7CD4 | |||
| 7296 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\B9WMB6CE\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia (002).zip | compressed | |
MD5:35E25CE99CB839B09D034A64FCD57539 | SHA256:833231726112DBD2654FC5E102593C09C9D81FBC766F802BEC6D39E183713E1D | |||
| 1764 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1764.41239\--Reporte_Conciliación_Fiscal_F2517V6_AG2023_v1.0.1-2024 - copia\Anexo 4 Guía de diligenciamiento del formato 2517 v4.pdf | ||
MD5:DA46CA7674D6F68AF7382E448A6596CD | SHA256:2CEF4DC5F4CFDC801569BCDD41EA77373468D4DE676CCB6B2C3FC28913993EB1 | |||
| 7296 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:510A142E11A3BF741045584EF78B1710 | SHA256:500B6798348441E342BC68AA9FFB00F19DA67A5495CBDC7F38F41EFB2FA81DE0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
29
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 868 b | whitelisted |
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
7296 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7296 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | DE | binary | 471 b | whitelisted |
8176 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
8176 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6668 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7296 | OUTLOOK.EXE | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7296 | OUTLOOK.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
login.live.com |
| whitelisted |