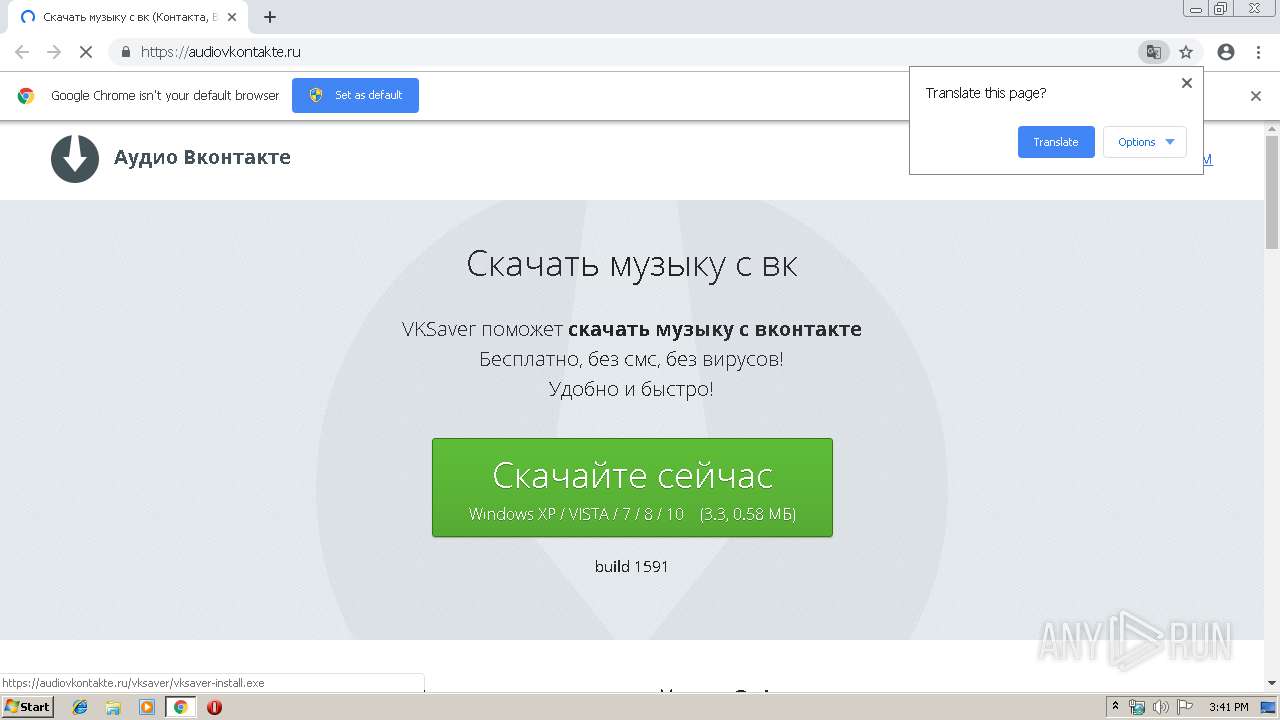
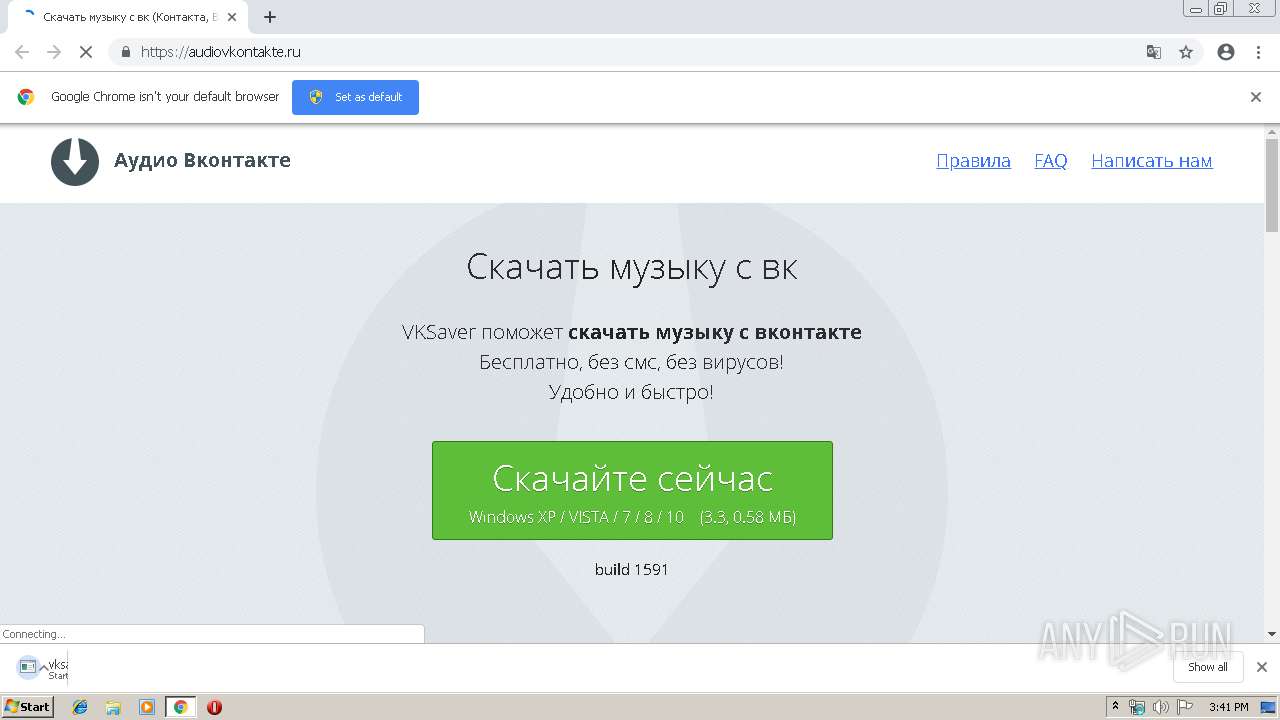
| URL: | https://audiovkontakte.ru/ |
| Full analysis: | https://app.any.run/tasks/2349ab22-0e0b-4697-acdd-fadbd185f6ca |
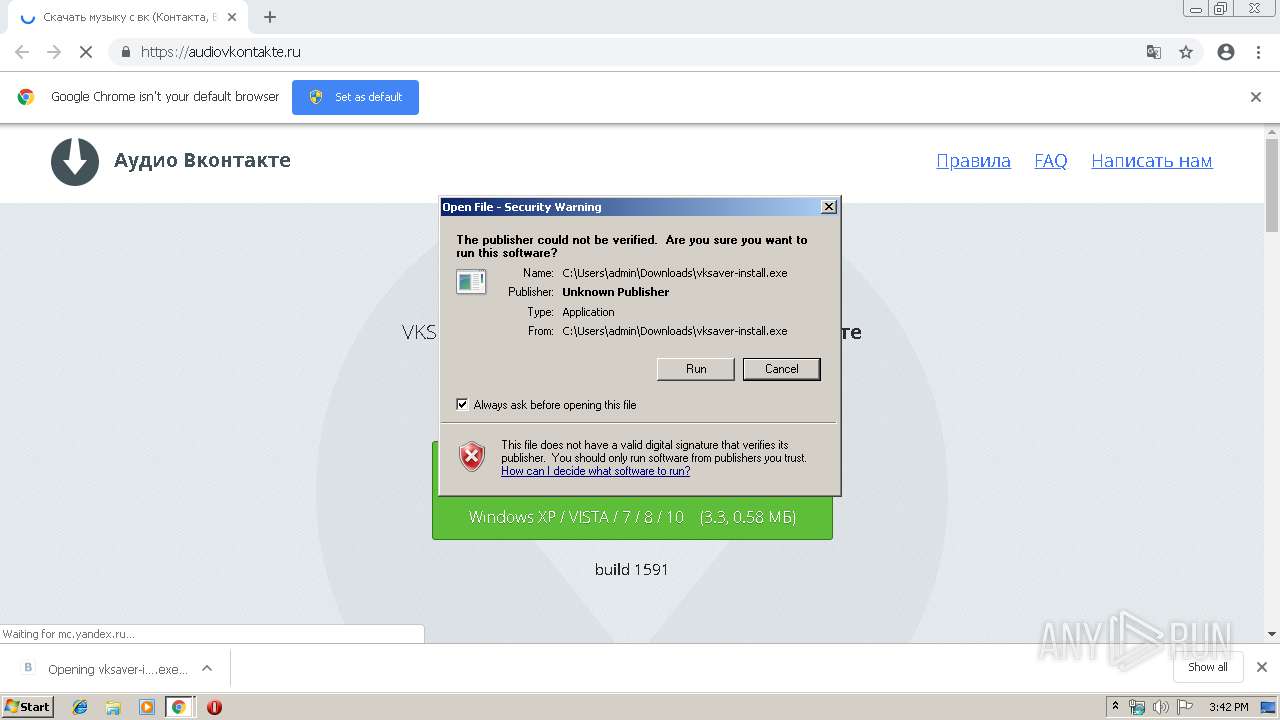
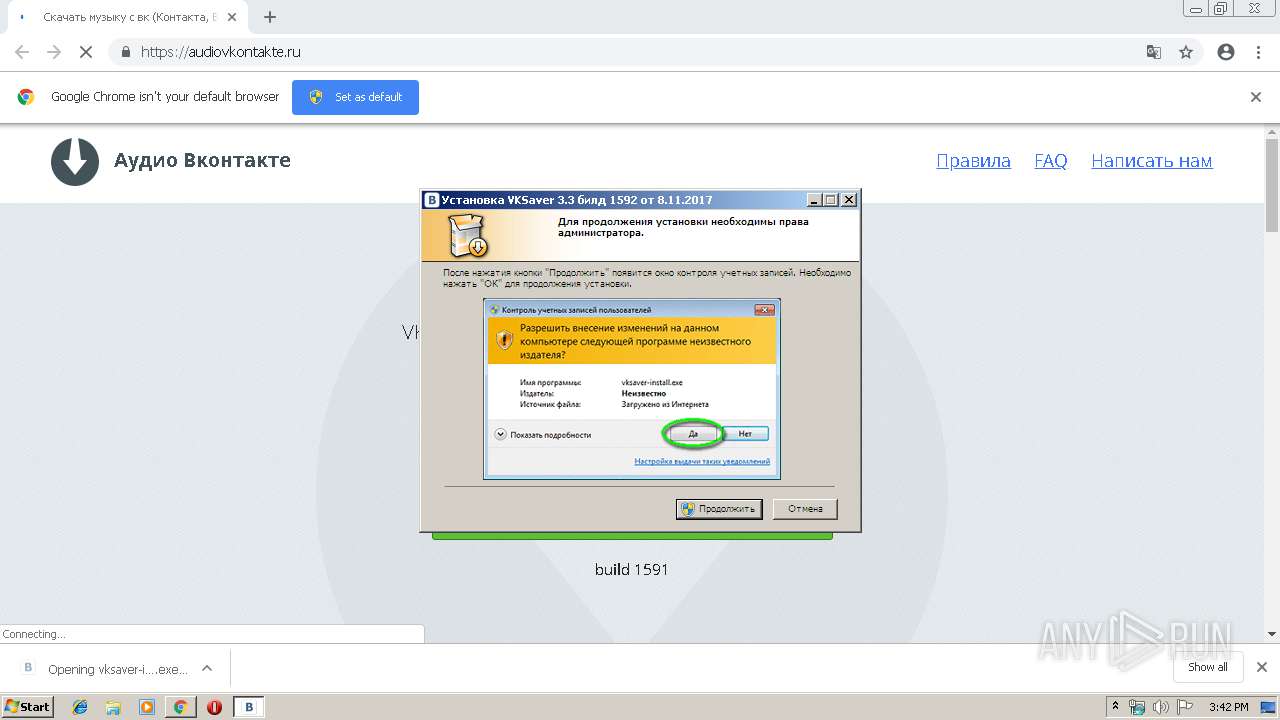
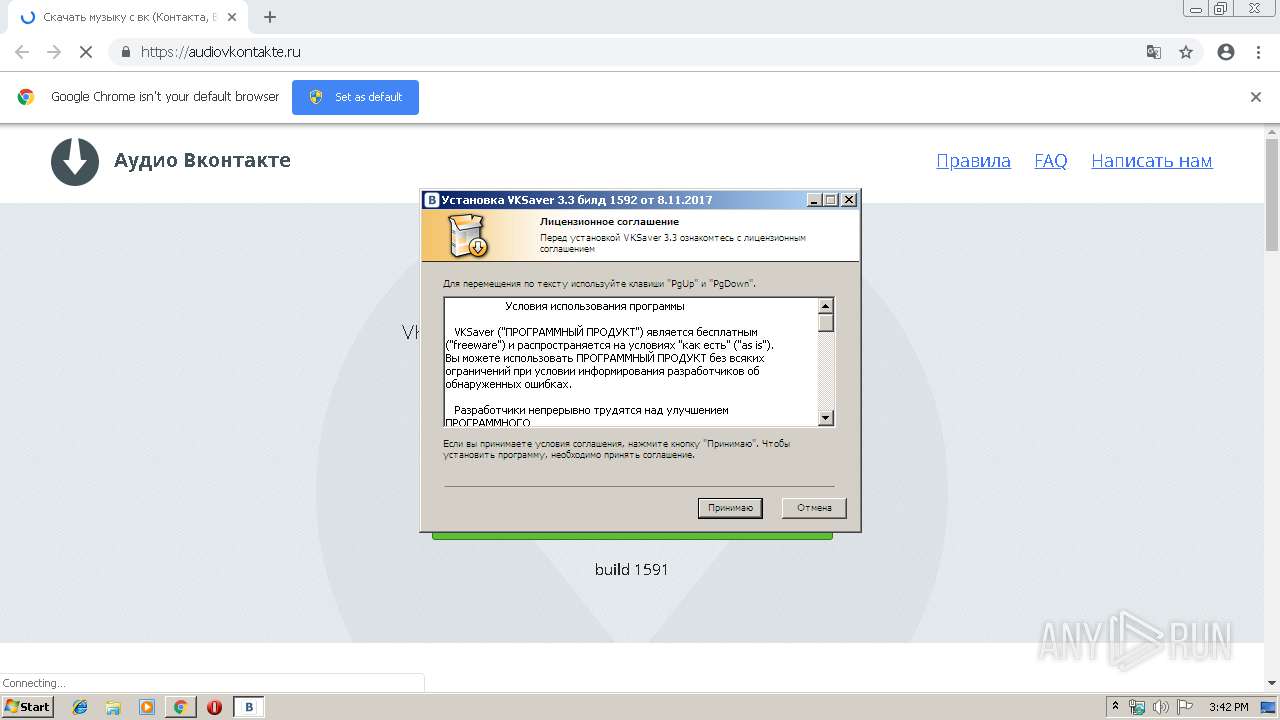
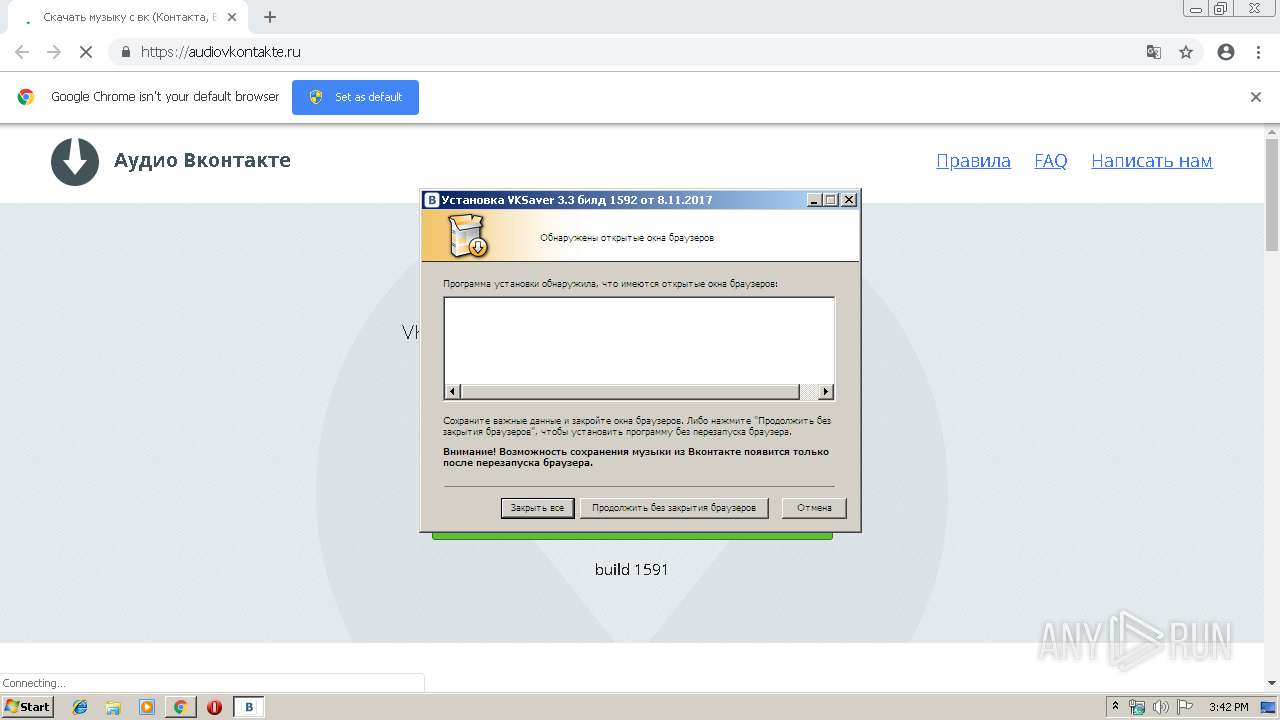
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 15:41:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8C089E95E168B1077C5D2B8D0CCE3259 |
| SHA1: | 9636A1C60D7AF6490D5E781FF93902A7EFCF83C6 |
| SHA256: | 0E501E5FB86C7F89A2800917119BC77A1B337D4868ABA5356434CA5F21F26B95 |
| SSDEEP: | 3:N89TOKLiORAsK:2IKRHK |
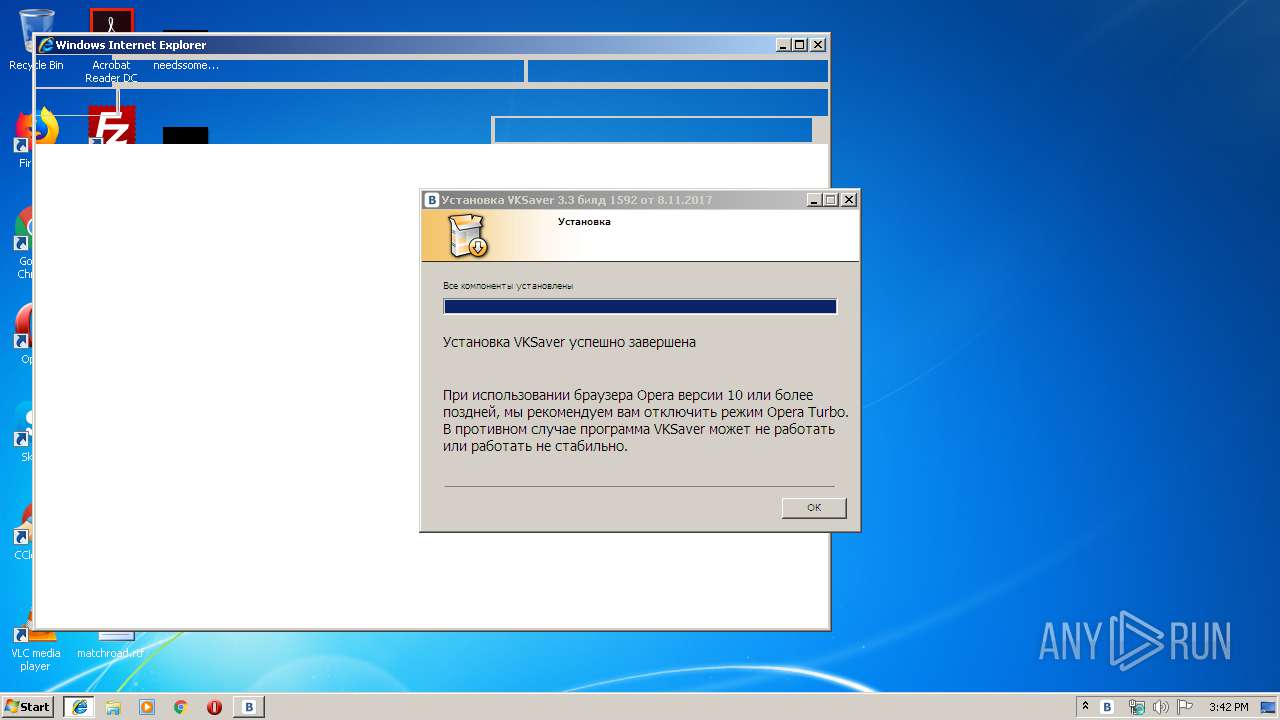
MALICIOUS
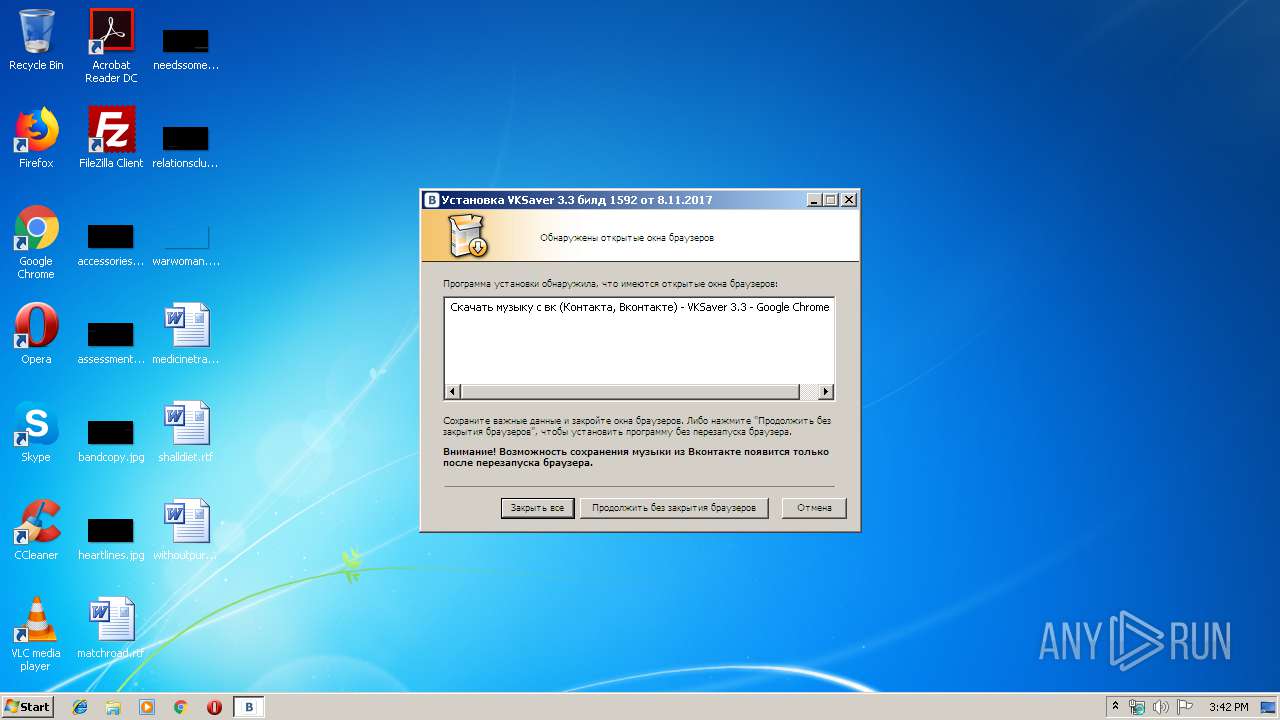
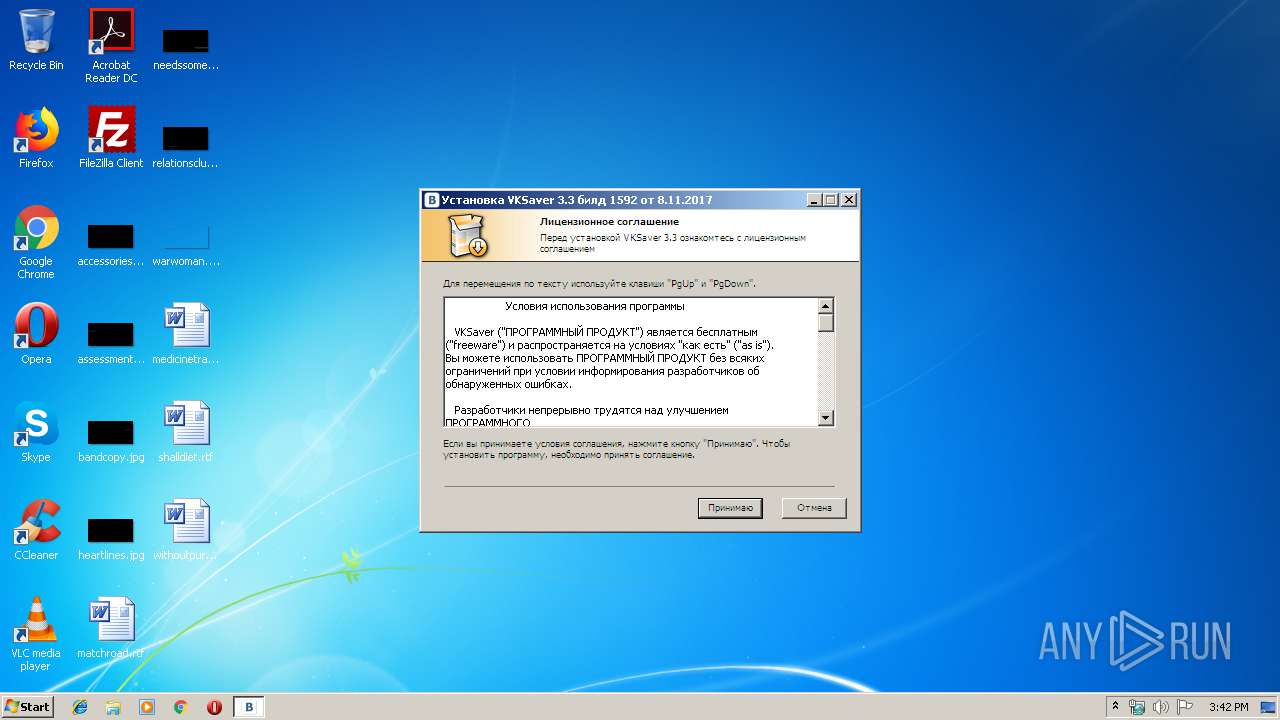
Application was dropped or rewritten from another process
- vksaver-install.exe (PID: 2092)
- vksaver-install.exe (PID: 4044)
- downloader.exe (PID: 1872)
- VKSaver.exe (PID: 4080)
- VKSaver.exe (PID: 2584)
Changes AppInit_DLLs value (autorun option)
- vksaver-install.exe (PID: 4044)
Loads dropped or rewritten executable
- VKSaver.exe (PID: 4080)
- downloader.exe (PID: 1872)
- taskeng.exe (PID: 2052)
- VKSaver.exe (PID: 2584)
- iexplore.exe (PID: 1744)
- iexplore.exe (PID: 1784)
- SearchProtocolHost.exe (PID: 2348)
Changes the autorun value in the registry
- vksaver-install.exe (PID: 4044)
Loads the Task Scheduler COM API
- vksaver-install.exe (PID: 4044)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3904)
- chrome.exe (PID: 2480)
- vksaver-install.exe (PID: 4044)
Application launched itself
- vksaver-install.exe (PID: 2092)
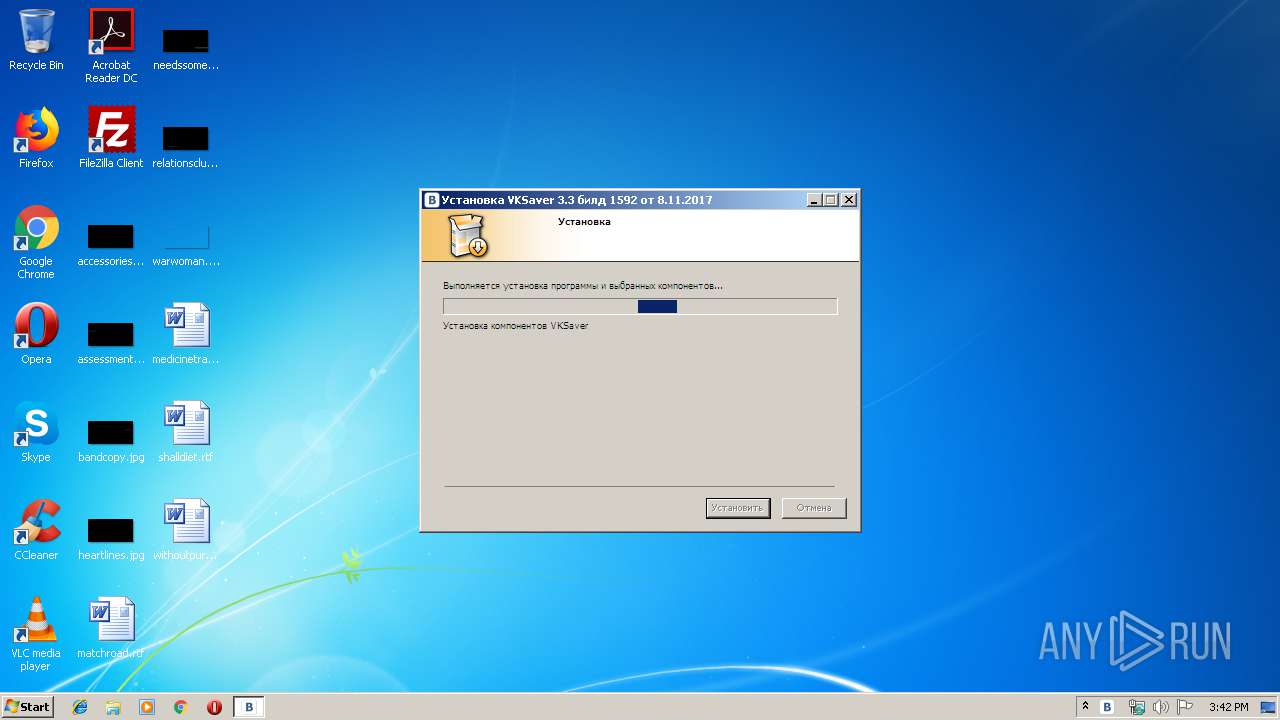
Creates files in the program directory
- vksaver-install.exe (PID: 4044)
Creates files in the Windows directory
- vksaver-install.exe (PID: 4044)
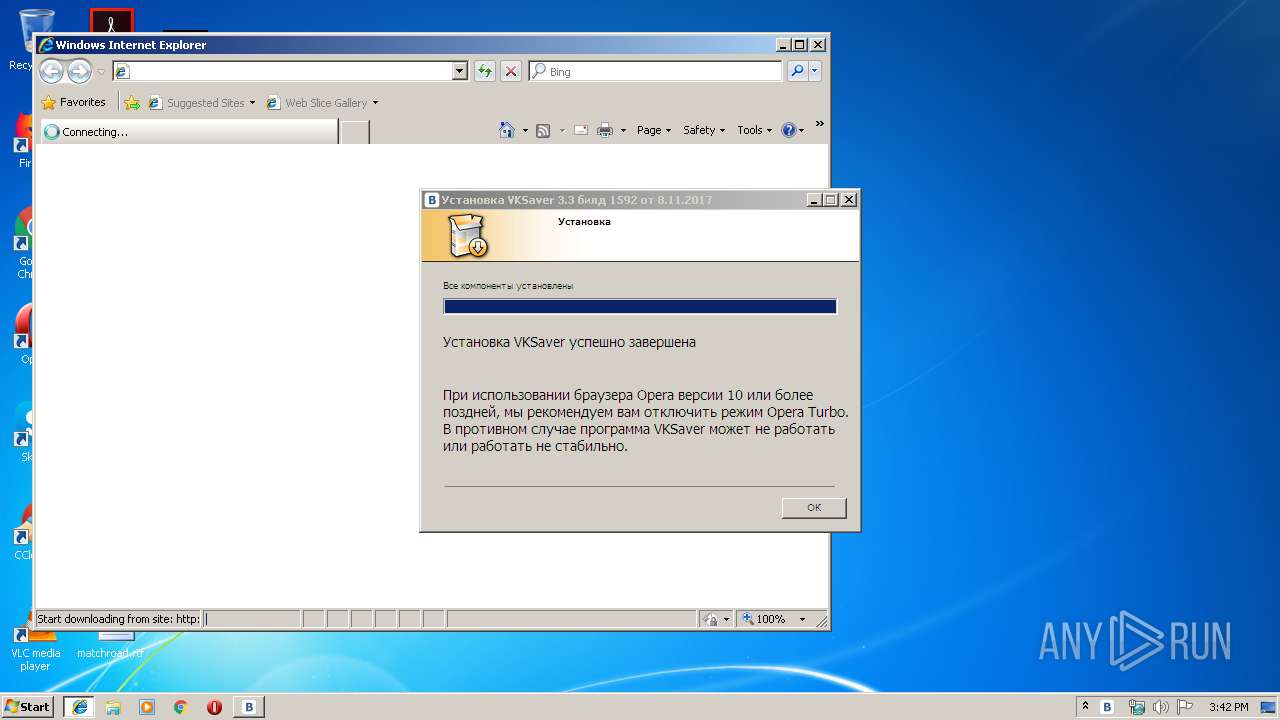
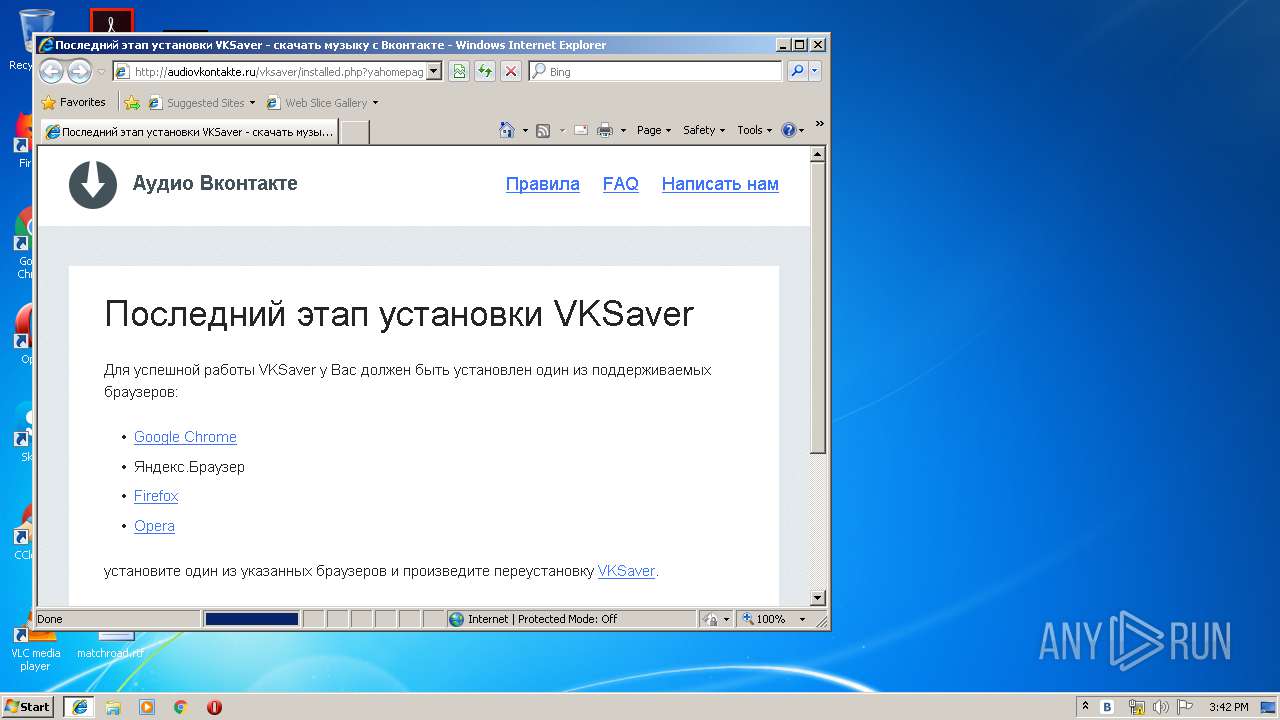
Starts Internet Explorer
- vksaver-install.exe (PID: 4044)
Creates a software uninstall entry
- vksaver-install.exe (PID: 4044)
INFO
Changes settings of System certificates
- chrome.exe (PID: 3904)
- iexplore.exe (PID: 1784)
Application launched itself
- chrome.exe (PID: 2480)
- iexplore.exe (PID: 1744)
Creates files in the user directory
- chrome.exe (PID: 2480)
- iexplore.exe (PID: 1784)
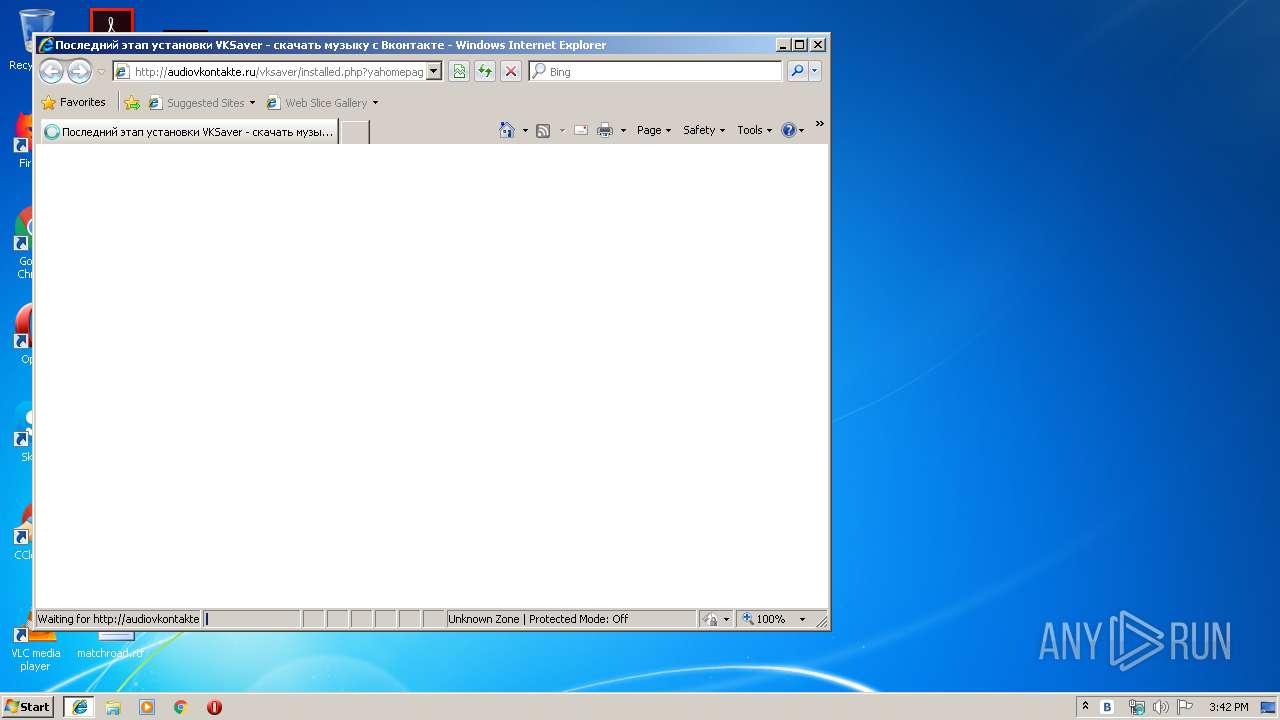
Changes internet zones settings
- iexplore.exe (PID: 1744)
Reads internet explorer settings
- iexplore.exe (PID: 1784)
Reads Internet Cache Settings
- iexplore.exe (PID: 1784)
Reads settings of System Certificates
- iexplore.exe (PID: 1784)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
17
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1088 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --service-pipe-token=8557134004426551463 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8557134004426551463 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | vksaver-install.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1744 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\AppData\Local\Temp\a9da474ecdd4dff3\downloader.exe" --partner 349532 --noaction 1 | C:\Users\admin\AppData\Local\Temp\a9da474ecdd4dff3\downloader.exe | vksaver-install.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Downloader Exit code: 0 Version: 0.1.0.32 Modules
| |||||||||||||||
| 2052 | taskeng.exe {66D51AB3-57E3-444C-93AC-3EC67E3BE39E} S-1-5-18:NT AUTHORITY\System:Service: | C:\Windows\system32\taskeng.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\Downloads\vksaver-install.exe" | C:\Users\admin\Downloads\vksaver-install.exe | — | chrome.exe | |||||||||||
User: admin Company: Audiovkontake.ru Integrity Level: MEDIUM Description: VKSaver installation bundle Exit code: 0 Version: 3.3.171108.1592 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --service-pipe-token=14603170214047455772 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14603170214047455772 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2348 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10005_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10005 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f870f18,0x6f870f28,0x6f870f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 501
Read events
1 350
Write events
148
Delete events
3
Modification events
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2480-13197656514868750 |
Value: 259 | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
6
Suspicious files
36
Text files
83
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\48f430b9-197f-4809-b8c5-b3747cdb460e.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
38
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4080 | VKSaver.exe | GET | — | 188.127.233.237:80 | http://audiovkontakte.ru/css/magnific-popup.min.css?1 | RU | — | — | whitelisted |
1872 | downloader.exe | GET | — | 77.88.21.14:80 | http://clck.yandex.ru/click/dtype=stred/pid=12/cid=72435/path=noaction/p=349532/* | RU | — | — | whitelisted |
4080 | VKSaver.exe | GET | 200 | 188.127.233.237:80 | http://audiovkontakte.ru/images/pattern.png | RU | image | 2.94 Kb | whitelisted |
4080 | VKSaver.exe | GET | 200 | 188.127.233.237:80 | http://audiovkontakte.ru/css/reset.min.css | RU | text | 358 b | whitelisted |
4080 | VKSaver.exe | GET | 200 | 188.127.233.237:80 | http://audiovkontakte.ru/css/magnific-popup.min.css?1 | RU | text | 1.61 Kb | whitelisted |
4080 | VKSaver.exe | GET | 200 | 188.127.233.237:80 | http://audiovkontakte.ru/images/logo.min.png | RU | image | 855 b | whitelisted |
4080 | VKSaver.exe | GET | 200 | 172.217.18.104:80 | http://www.googletagmanager.com/gtm.js?id=GTM-MTVK4Q | US | text | 22.9 Kb | whitelisted |
4080 | VKSaver.exe | GET | 200 | 188.127.233.237:80 | http://audiovkontakte.ru/favicon.ico | RU | image | 1.00 Kb | whitelisted |
4080 | VKSaver.exe | GET | 200 | 188.127.233.237:80 | http://audiovkontakte.ru/vksaver/installed.php?yahomepage=false&yaqsearch=false&yabm=false&yabrowser=false&version=3.3&build_date=140820&build=1591&mask=116&mask_date=160118 | RU | html | 1.95 Kb | whitelisted |
4080 | VKSaver.exe | GET | 200 | 188.127.233.237:80 | http://audiovkontakte.ru/css/jquery.bxslider.min.css?1 | RU | text | 787 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | VKSaver.exe | 172.217.18.110:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3904 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3904 | chrome.exe | 188.127.233.237:443 | audiovkontakte.ru | Telecommunication Systems, LLC | RU | suspicious |
3904 | chrome.exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
3904 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3904 | chrome.exe | 178.154.131.215:443 | yandex.st | YANDEX LLC | RU | whitelisted |
3904 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3904 | chrome.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3904 | chrome.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3904 | chrome.exe | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
audiovkontakte.ru |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
crt.comodoca.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
yandex.st |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1872 | downloader.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |