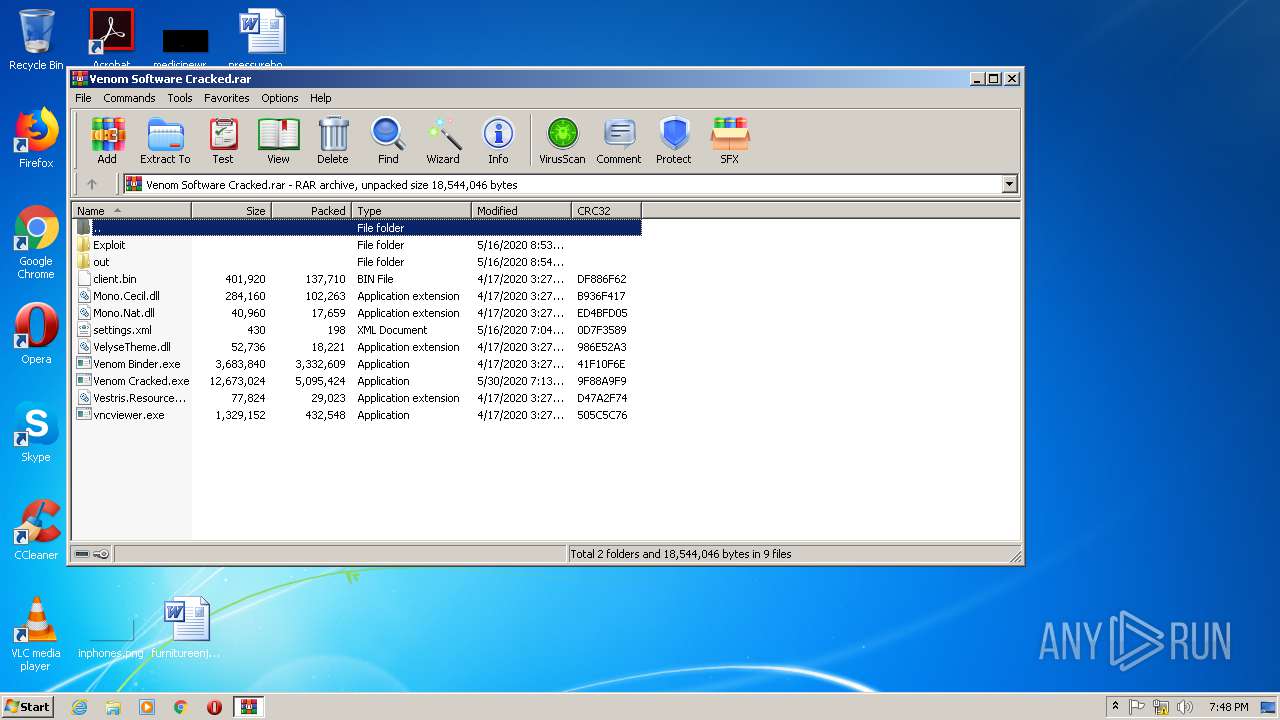
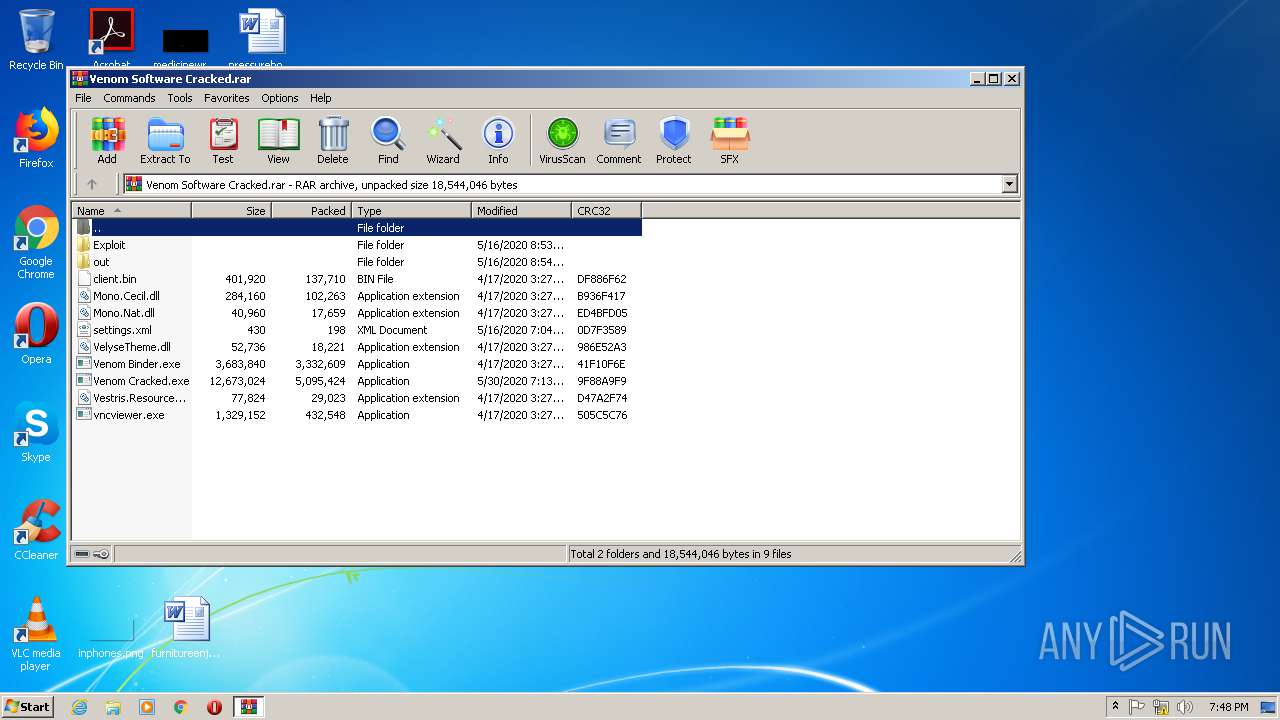
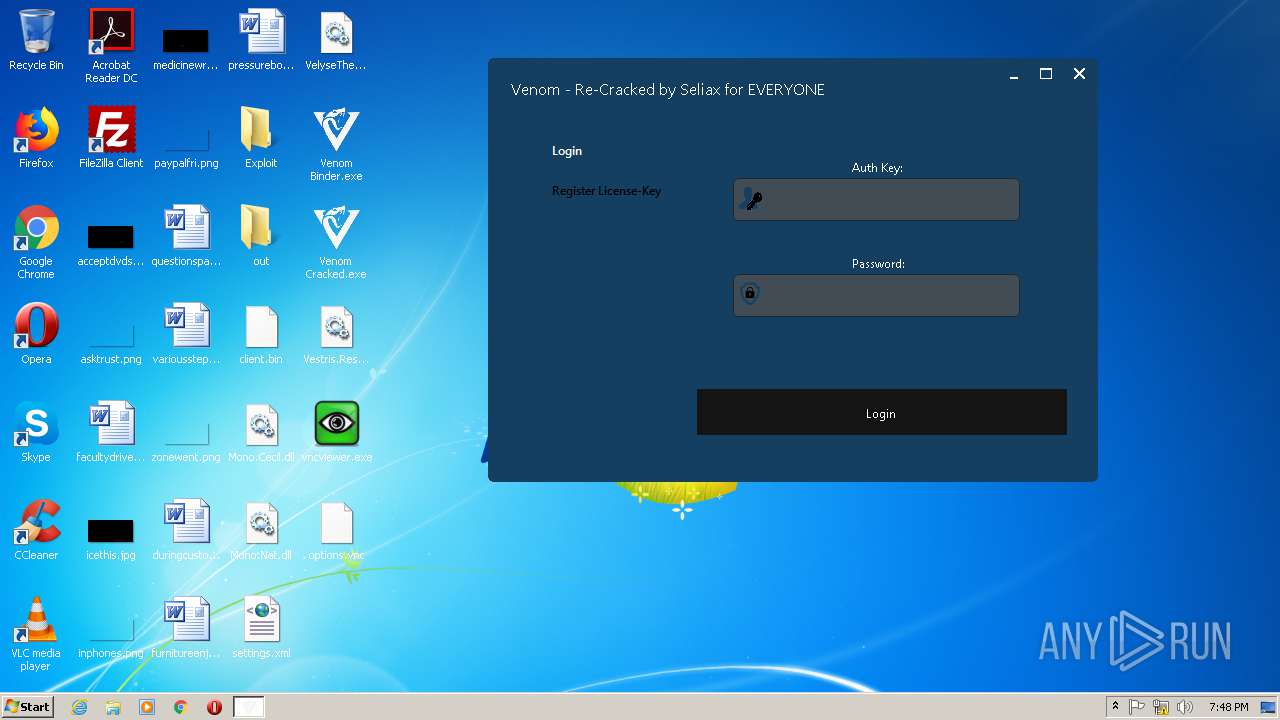
| File name: | Venom Software Cracked.rar |
| Full analysis: | https://app.any.run/tasks/f8b6bdef-6992-4e29-bfb7-34173984d04c |
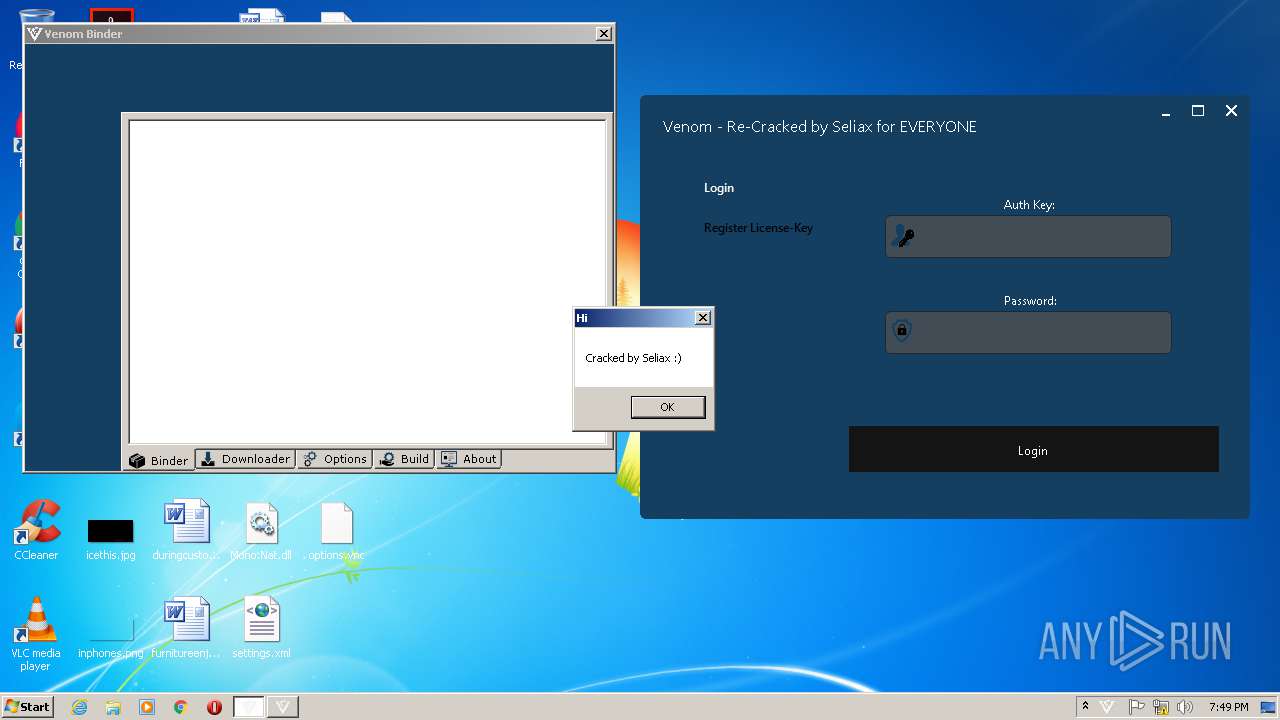
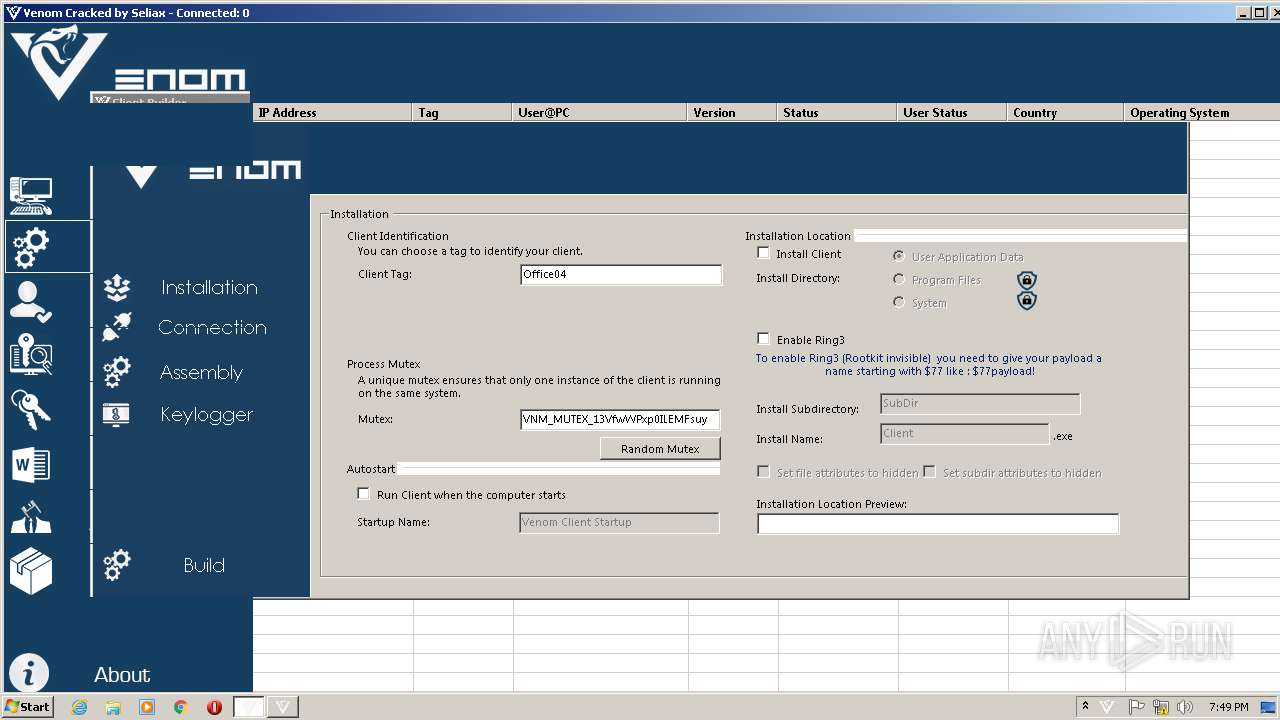
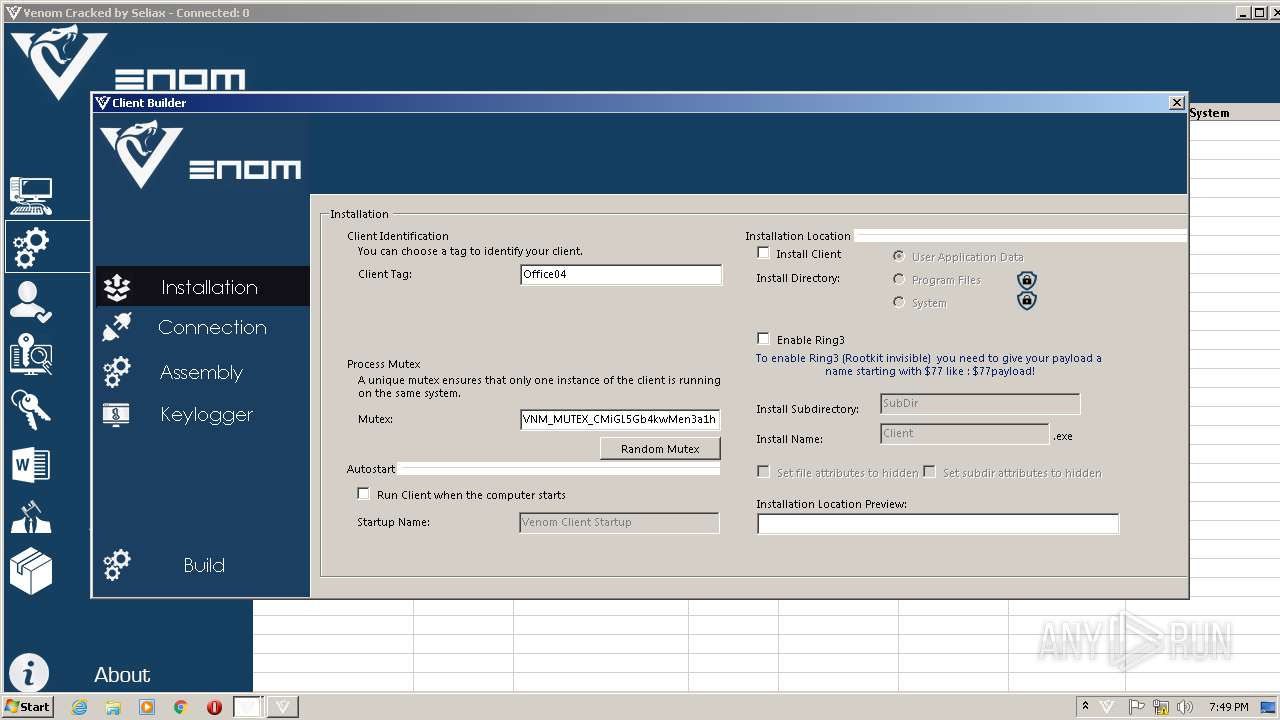
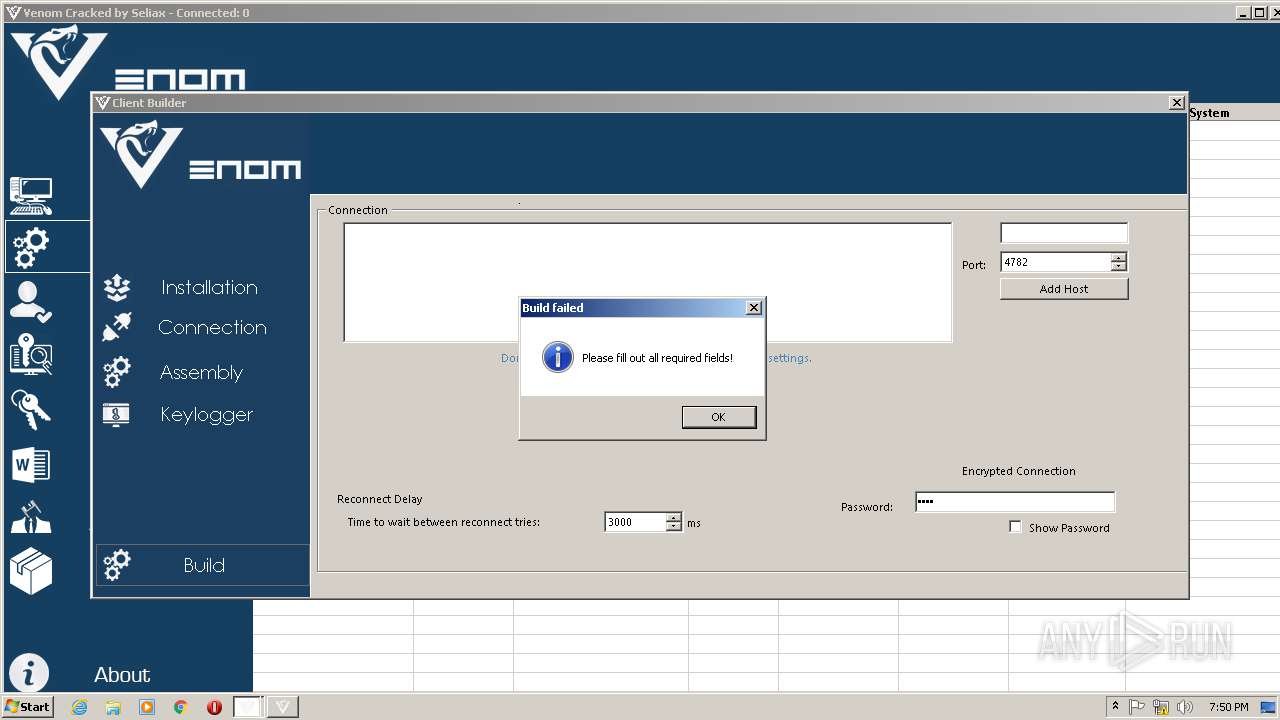
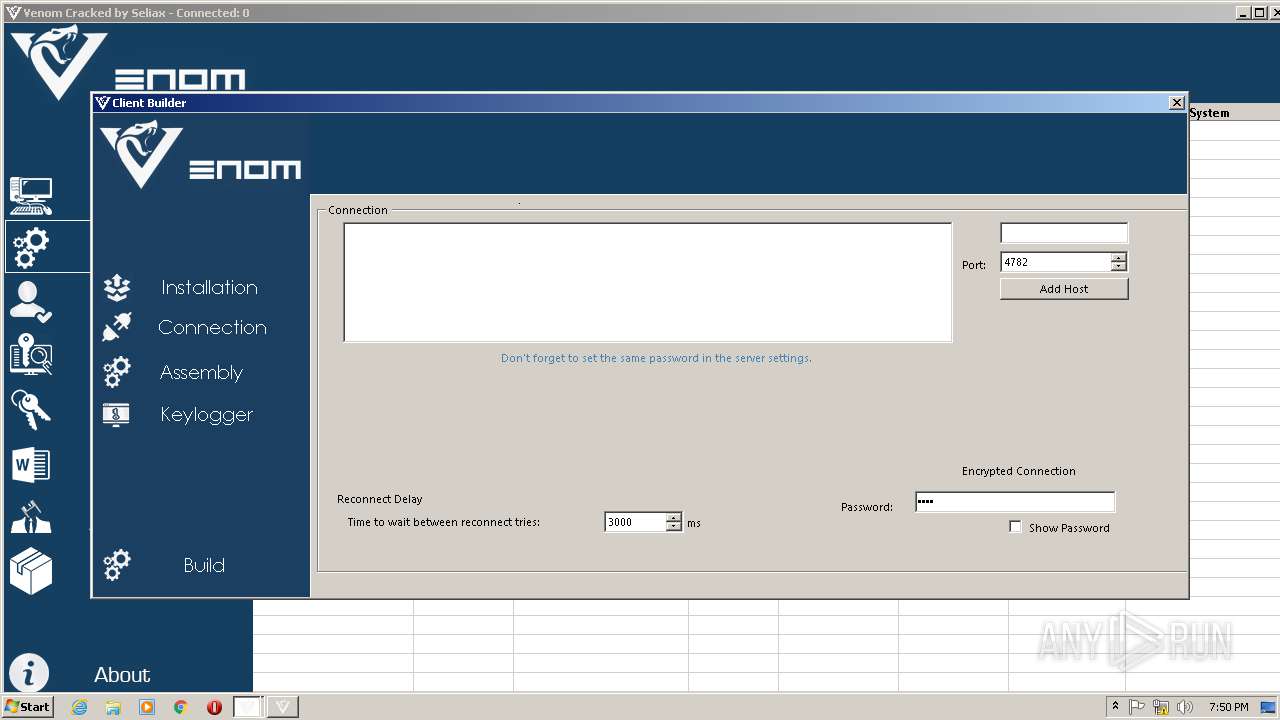
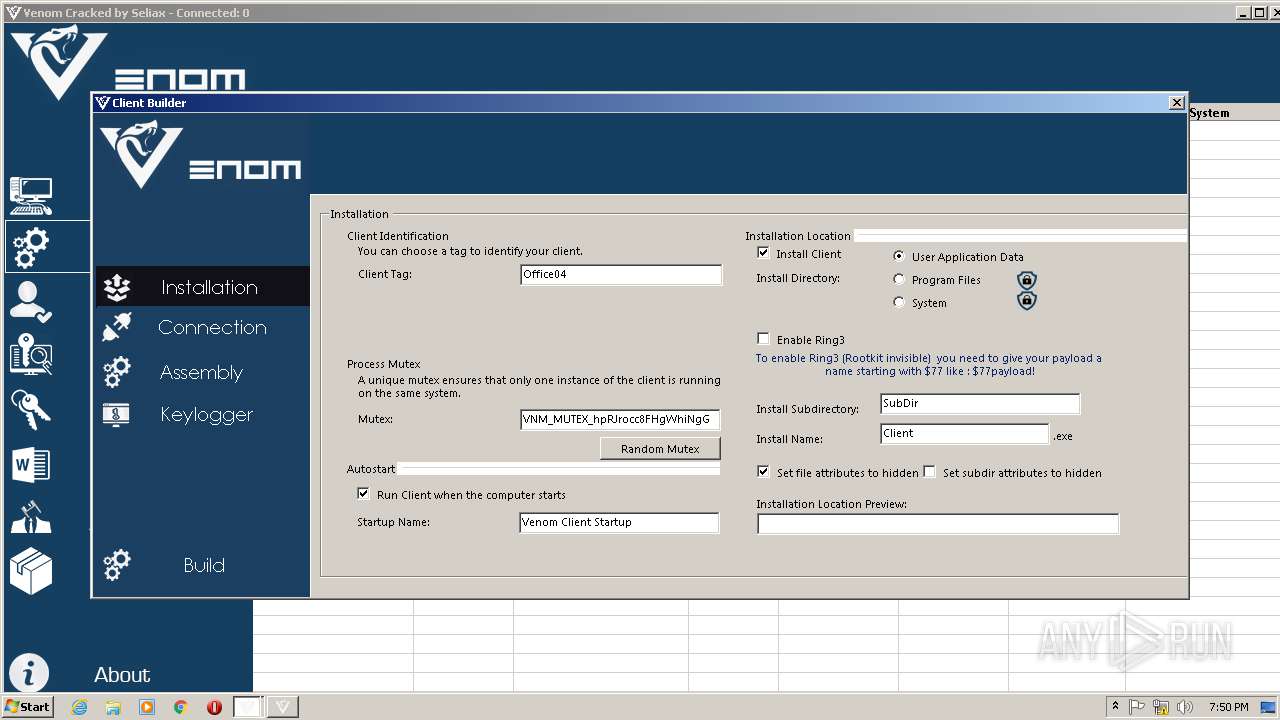
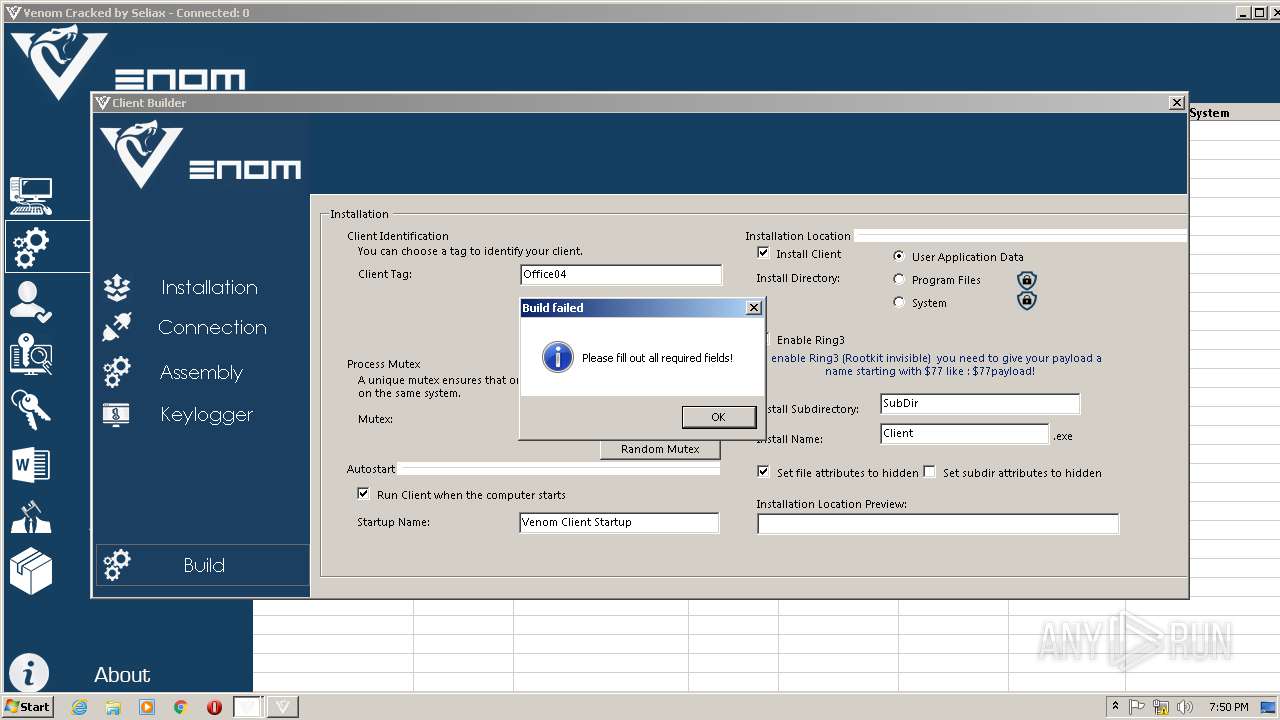
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 18:47:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F698E120B79D5F39ECD33D39E231A61A |
| SHA1: | 4F3A6F77CAC6A7E5187931161C2CE618DDAB6C3A |
| SHA256: | 0E4C8A185B8DA513D4D5071BFE52249D4C1DDCFECA03B68DD73013EEE5BD284C |
| SSDEEP: | 196608:6/i7DRo/8tgxpzBezrDIzVkqWkZpuG6CjAABA0R0g83KUx8LIJaJgVCZHlHKoISt:TzomXuvx6Cj7AANIKUCLIuDFHL6X+v |
MALICIOUS
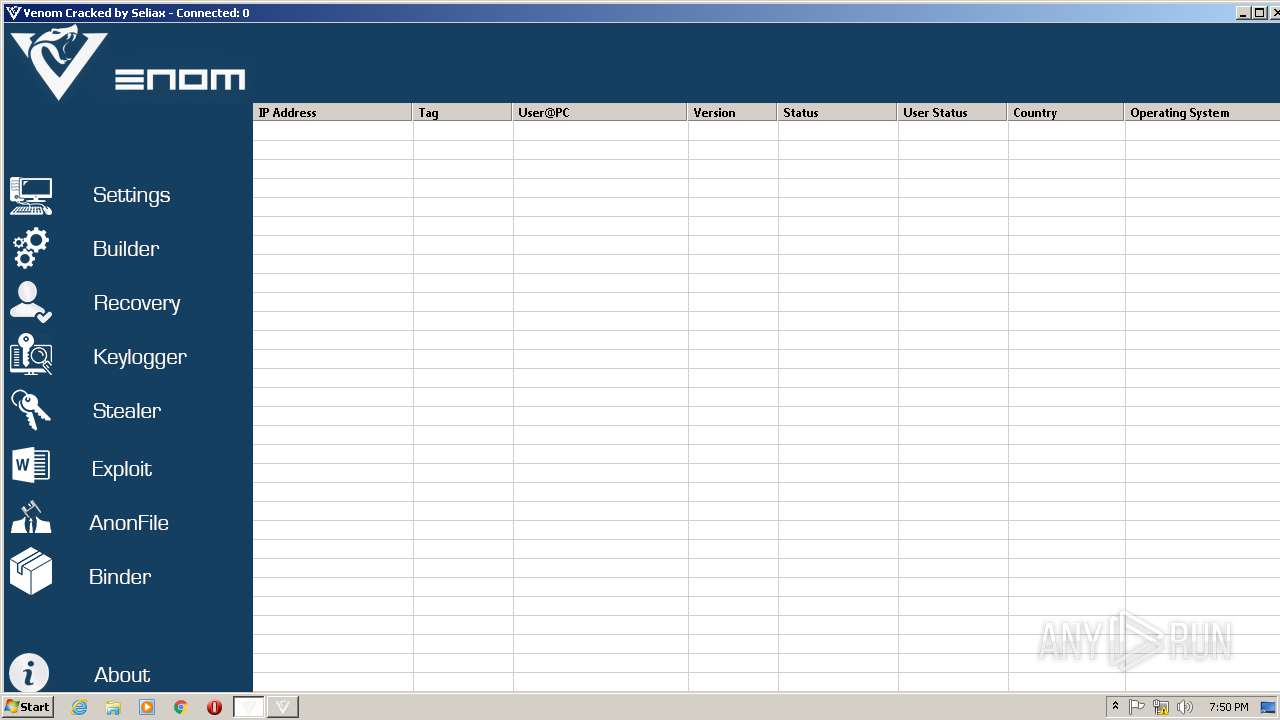
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 536)
- Venom Cracked.exe (PID: 3420)
Application was dropped or rewritten from another process
- Venom Cracked.exe (PID: 3420)
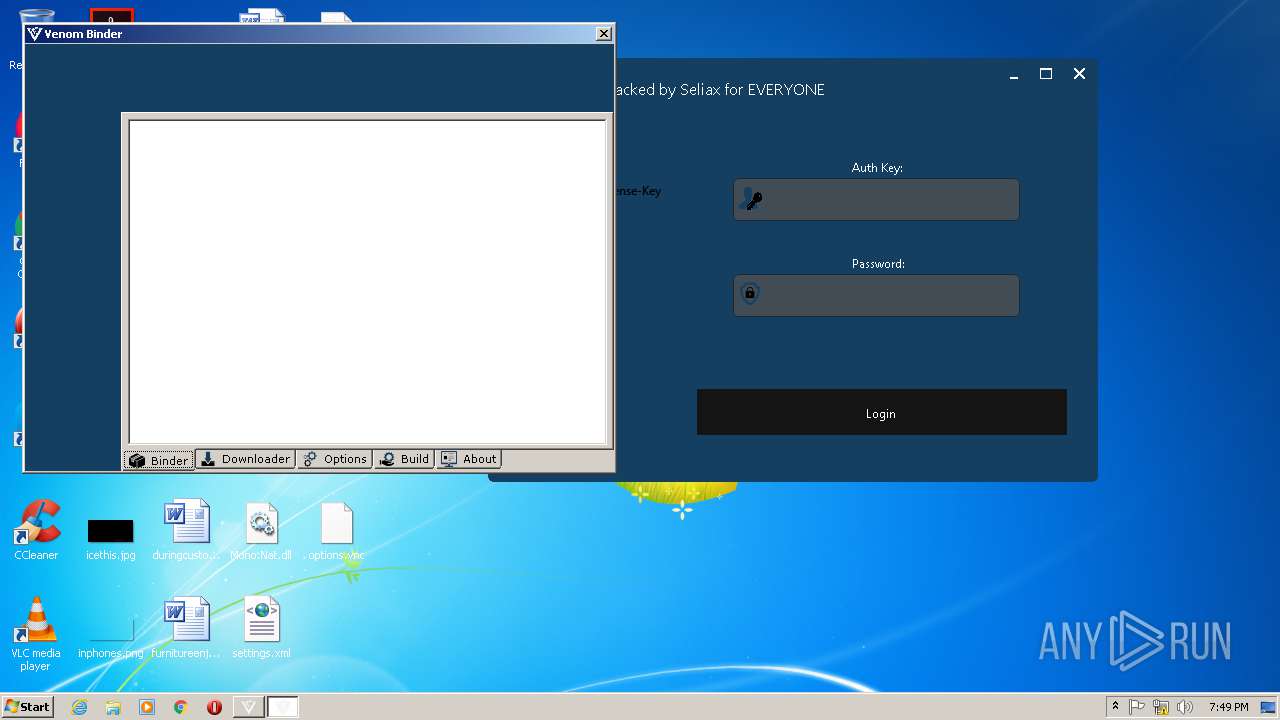
- Venom Binder.exe (PID: 2772)
- vncviewer.exe (PID: 3192)
- vncviewer.exe (PID: 2768)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3124)
INFO
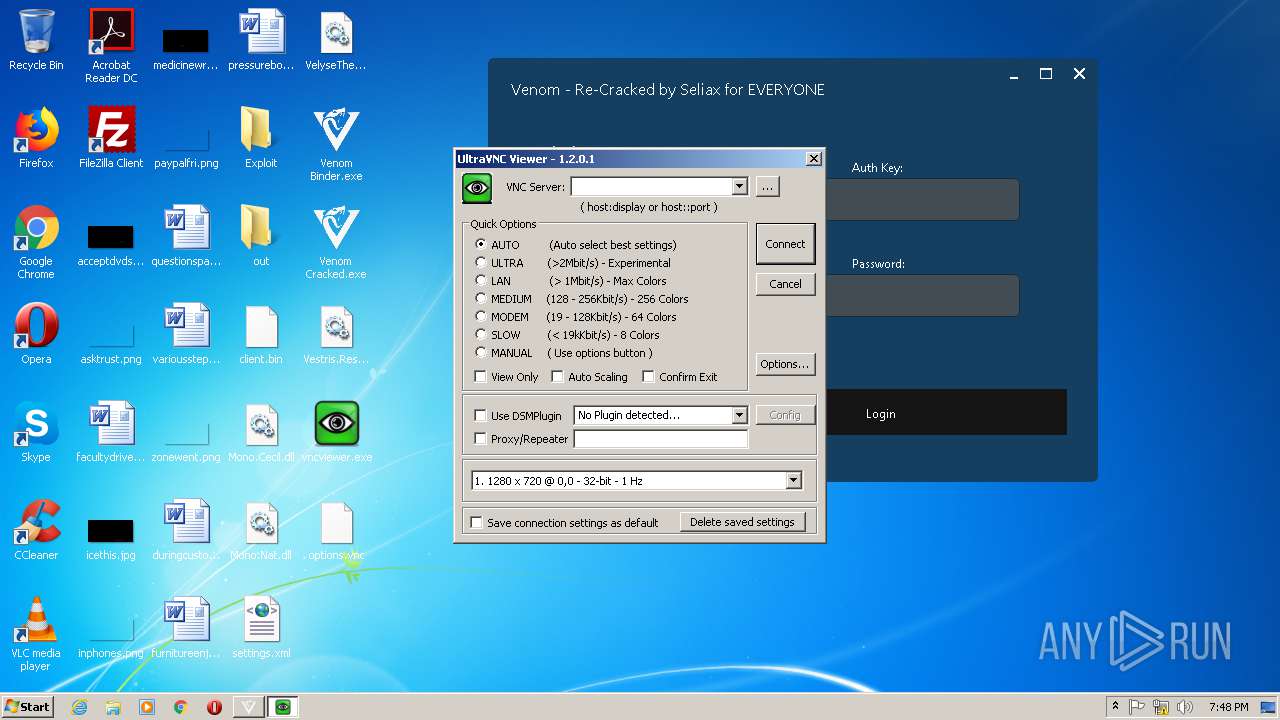
Manual execution by user
- vncviewer.exe (PID: 3192)
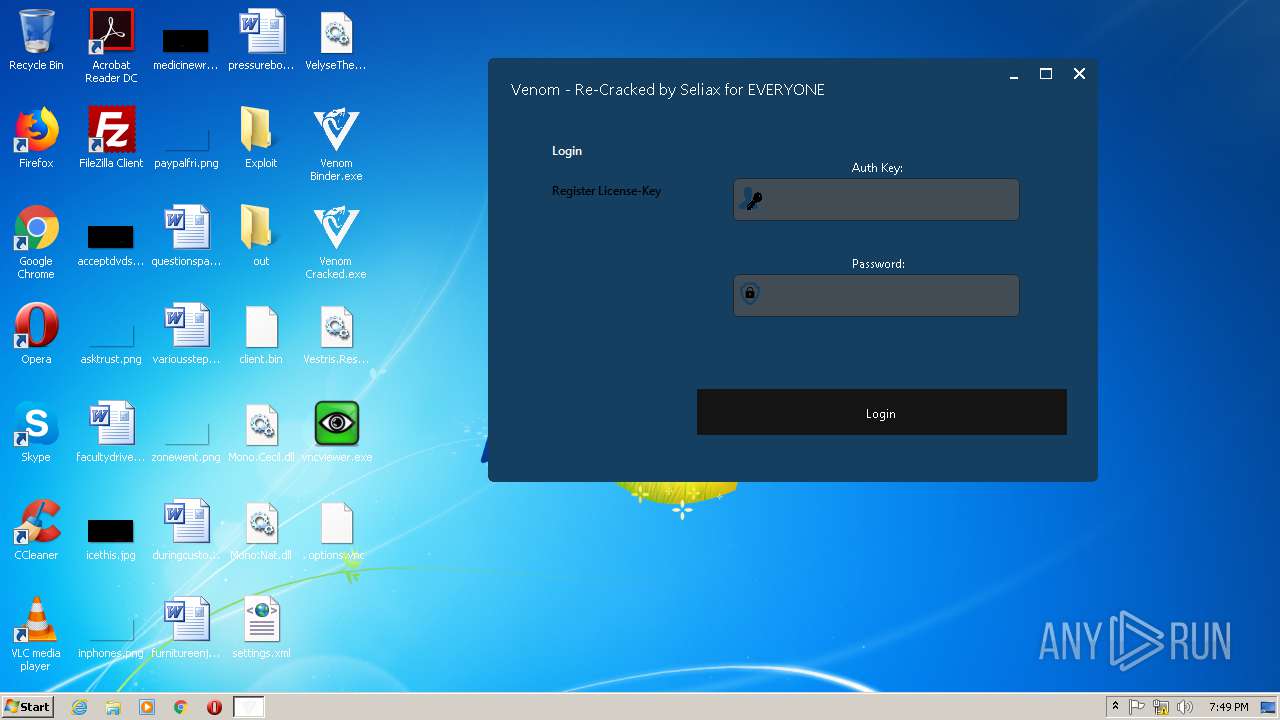
- Venom Cracked.exe (PID: 3420)
- vncviewer.exe (PID: 2768)
- Venom Binder.exe (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
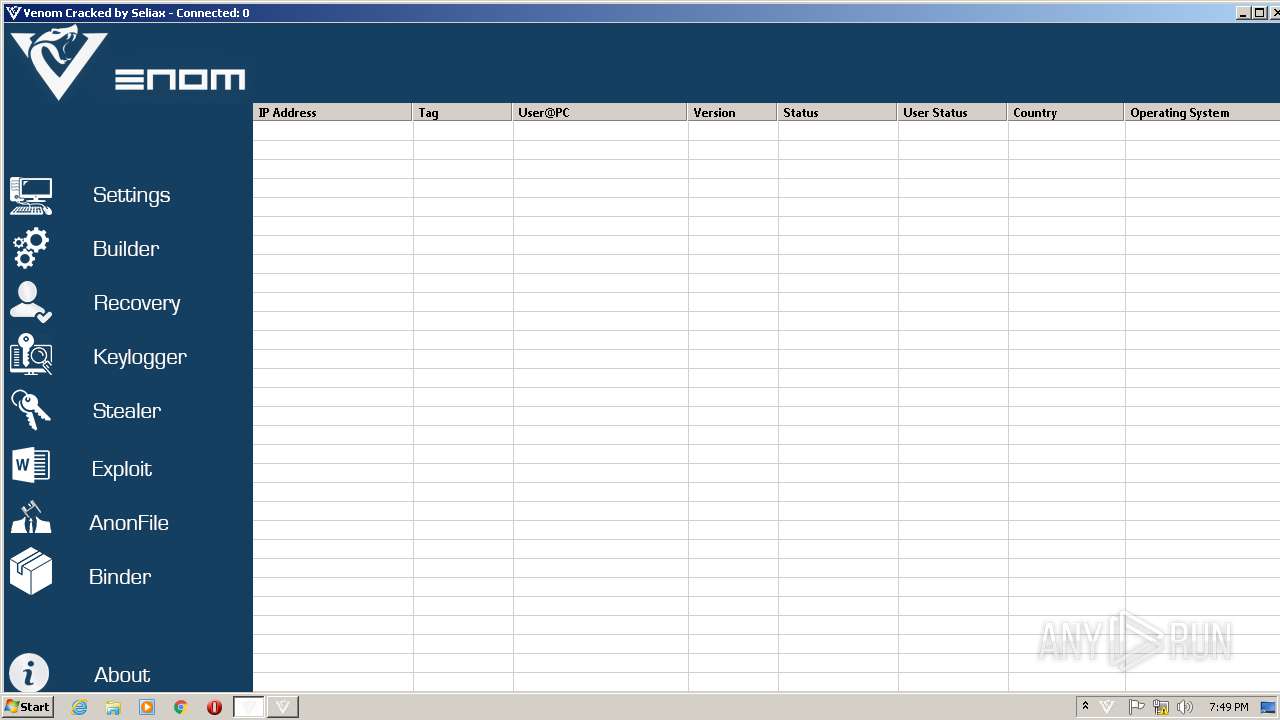
Total processes
43
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
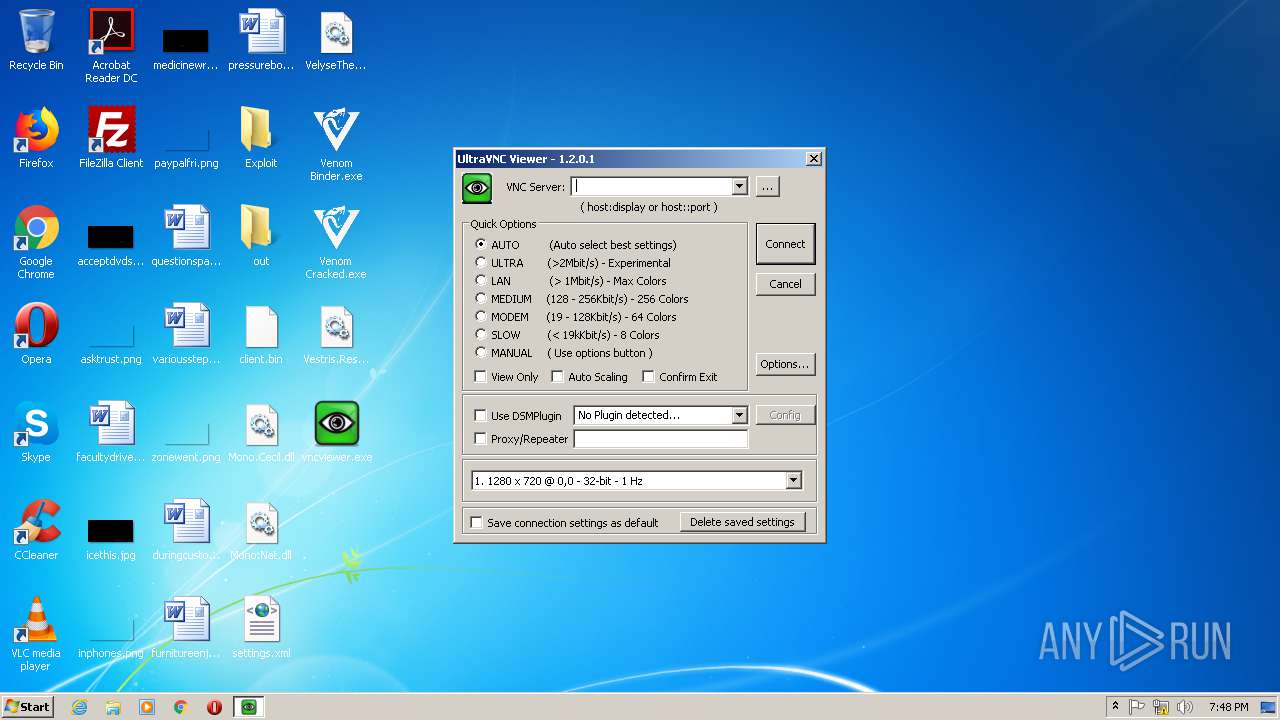
| 2768 | "C:\Users\admin\Desktop\vncviewer.exe" | C:\Users\admin\Desktop\vncviewer.exe | — | explorer.exe | |||||||||||
User: admin Company: UltraVNC Integrity Level: MEDIUM Description: VNCViewer Exit code: 0 Version: 1.2.0.1 Modules
| |||||||||||||||
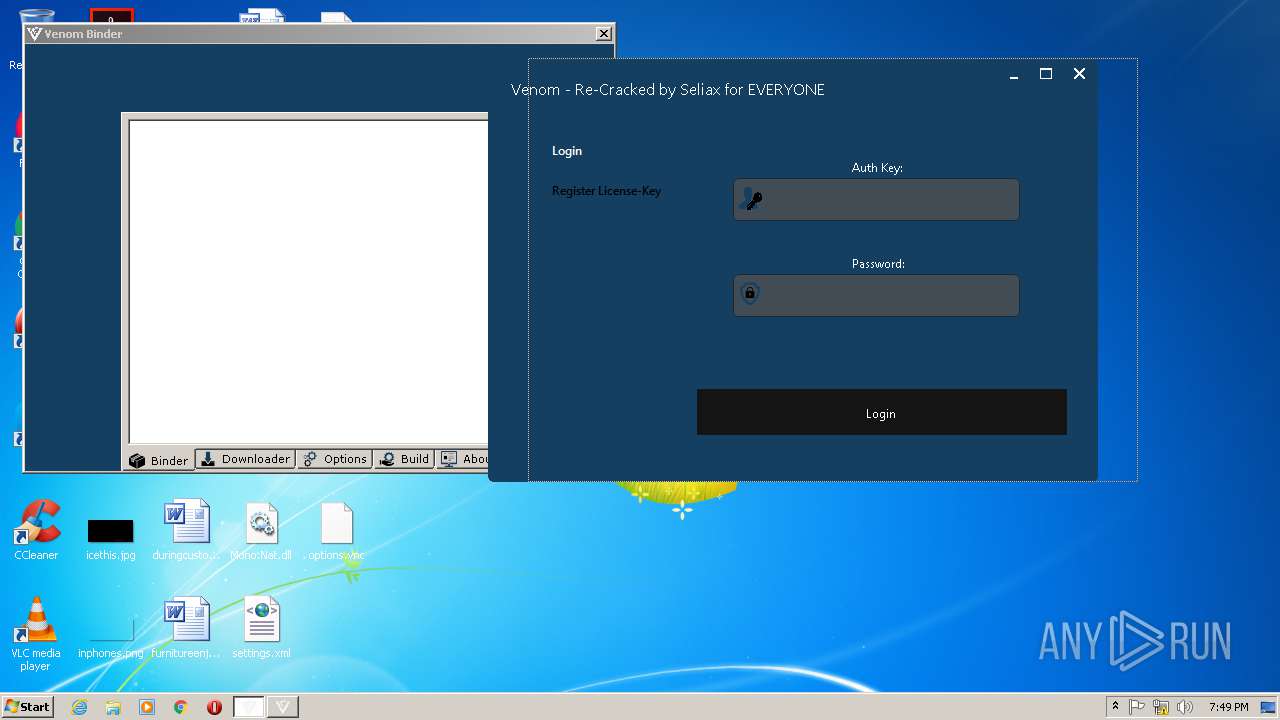
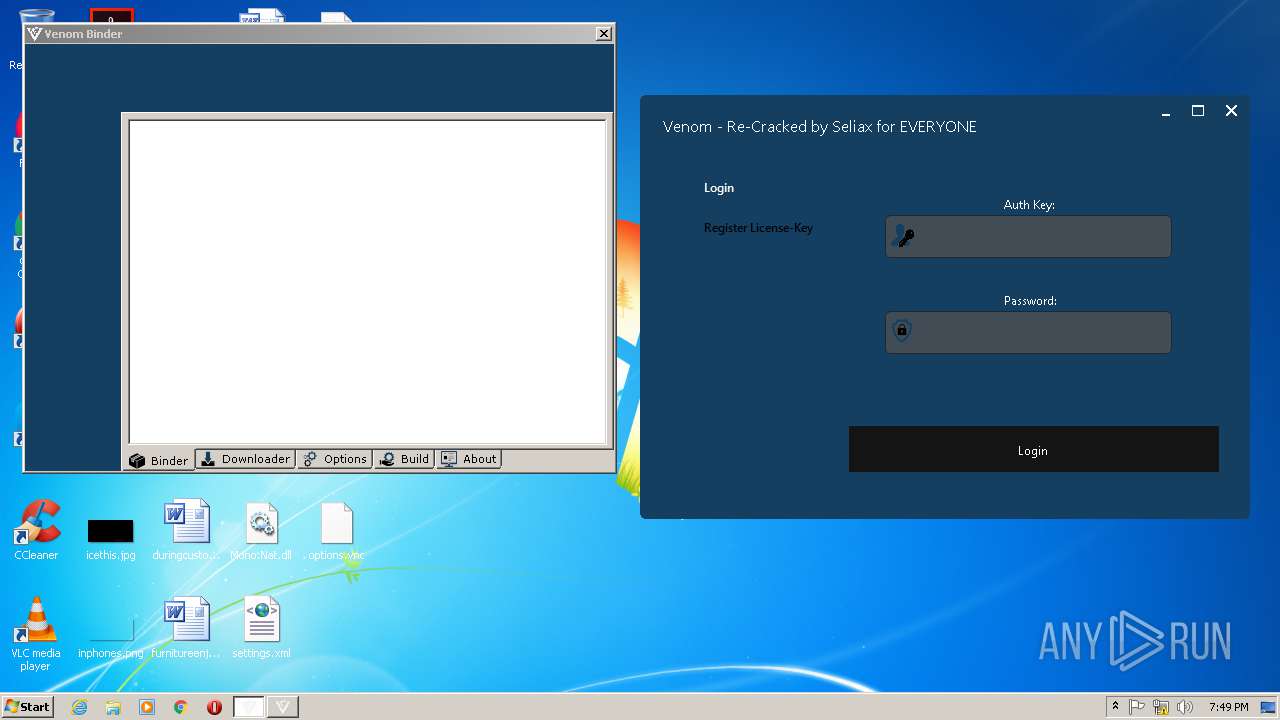
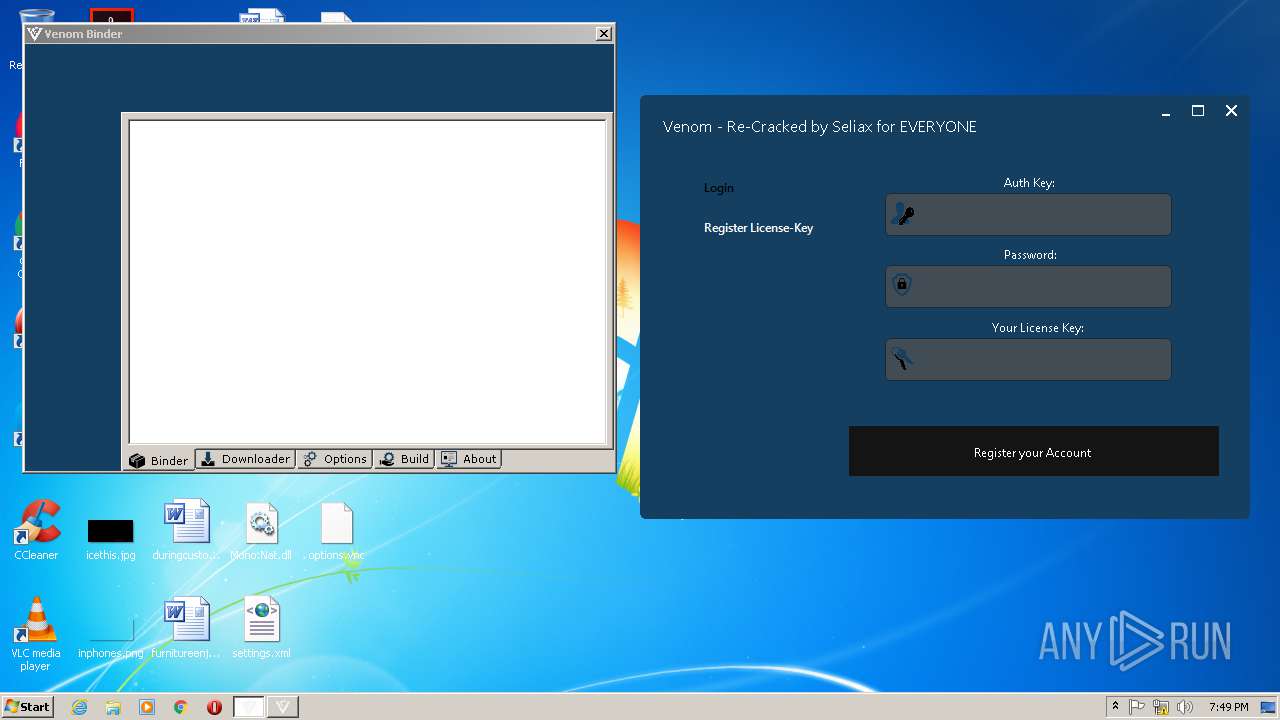
| 2772 | "C:\Users\admin\Desktop\Venom Binder.exe" | C:\Users\admin\Desktop\Venom Binder.exe | — | explorer.exe | |||||||||||
User: admin Company: D4RkKr0n0s Inc. Integrity Level: MEDIUM Description: Venom Binder Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
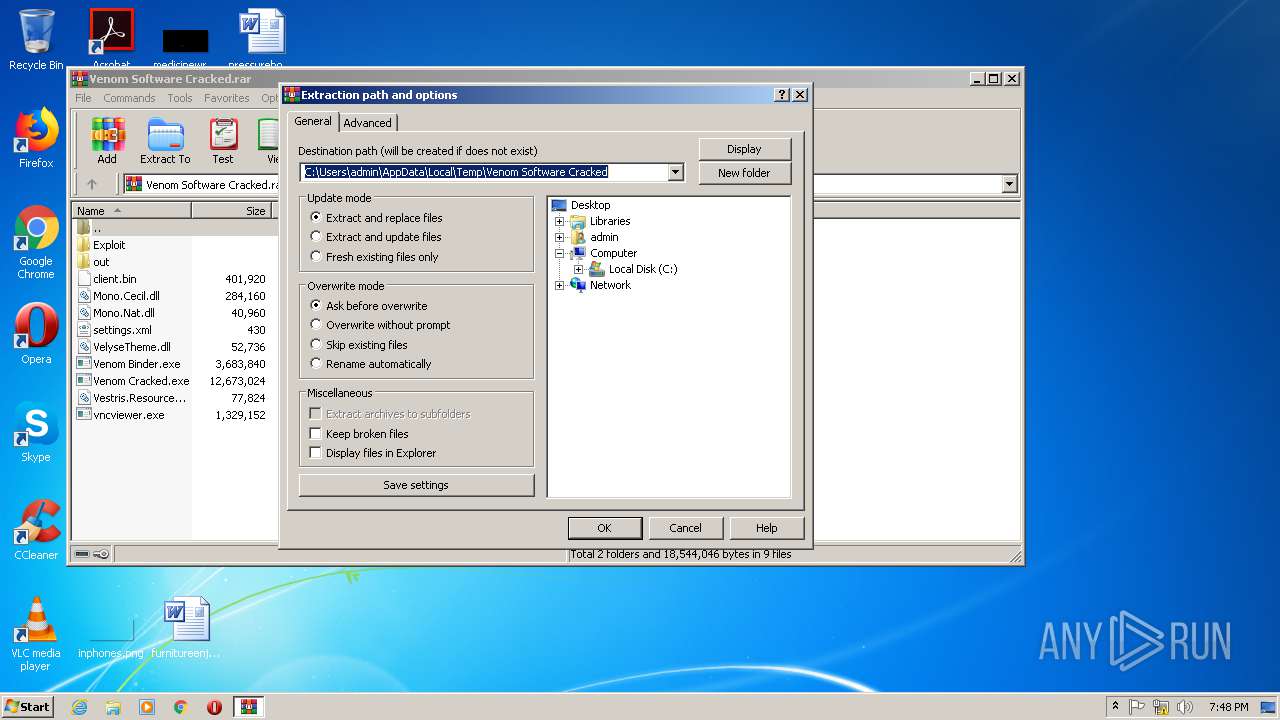
| 3124 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Venom Software Cracked.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3192 | "C:\Users\admin\Desktop\vncviewer.exe" | C:\Users\admin\Desktop\vncviewer.exe | — | explorer.exe | |||||||||||
User: admin Company: UltraVNC Integrity Level: MEDIUM Description: VNCViewer Exit code: 0 Version: 1.2.0.1 Modules
| |||||||||||||||
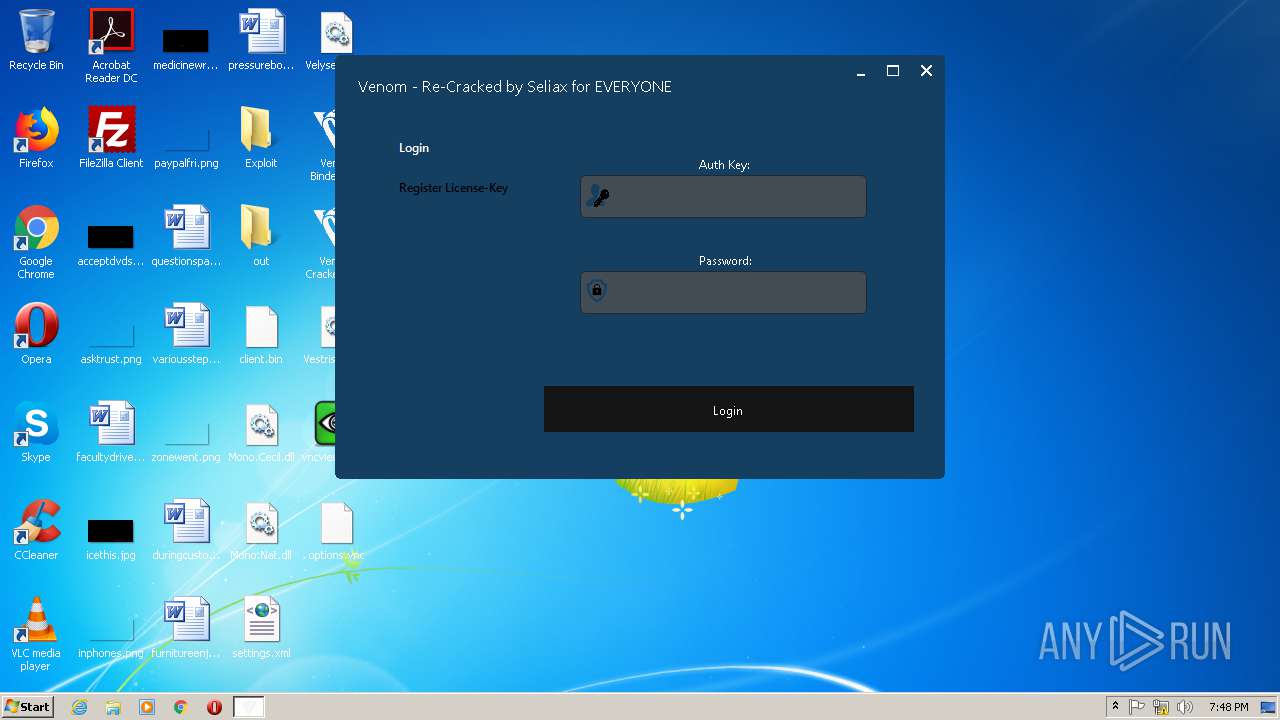
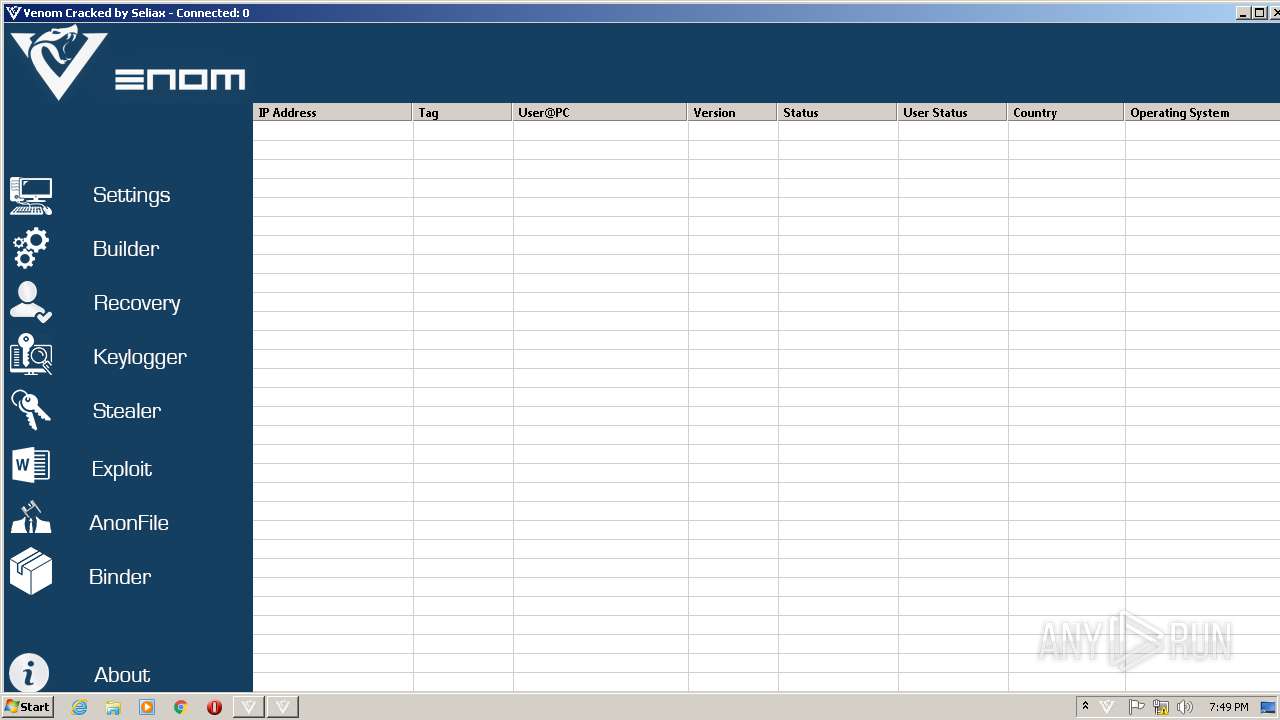
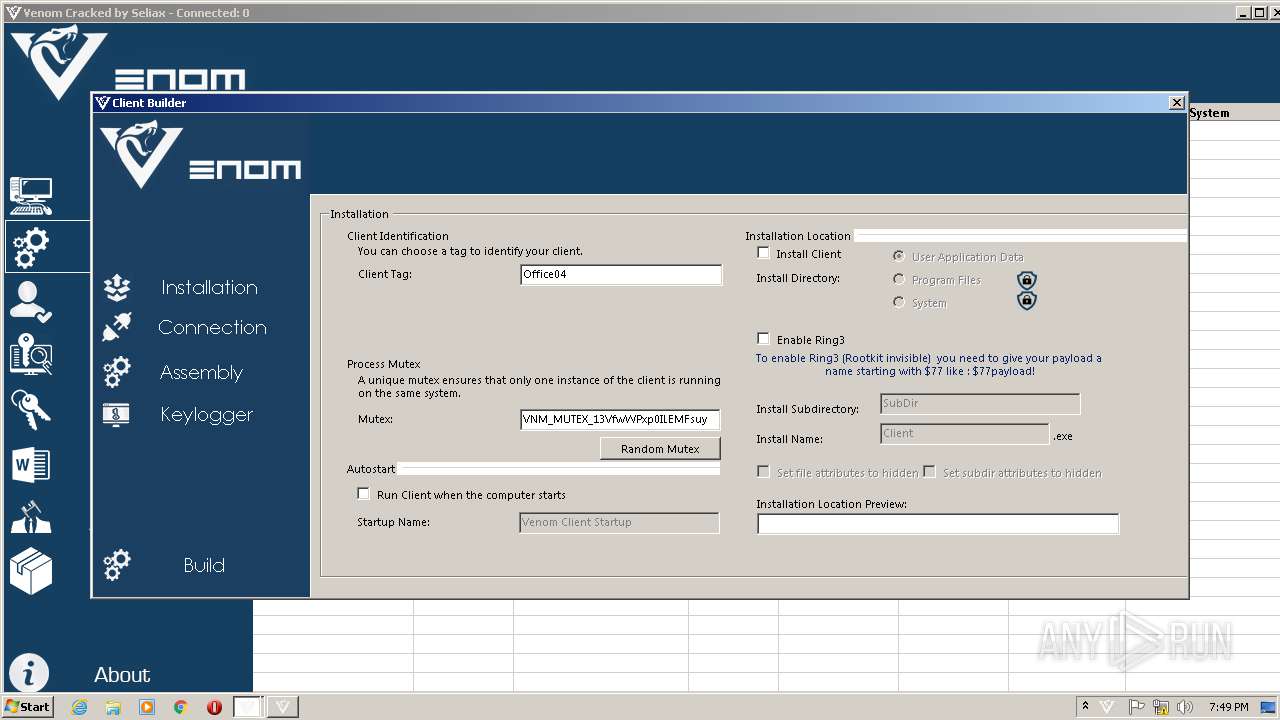
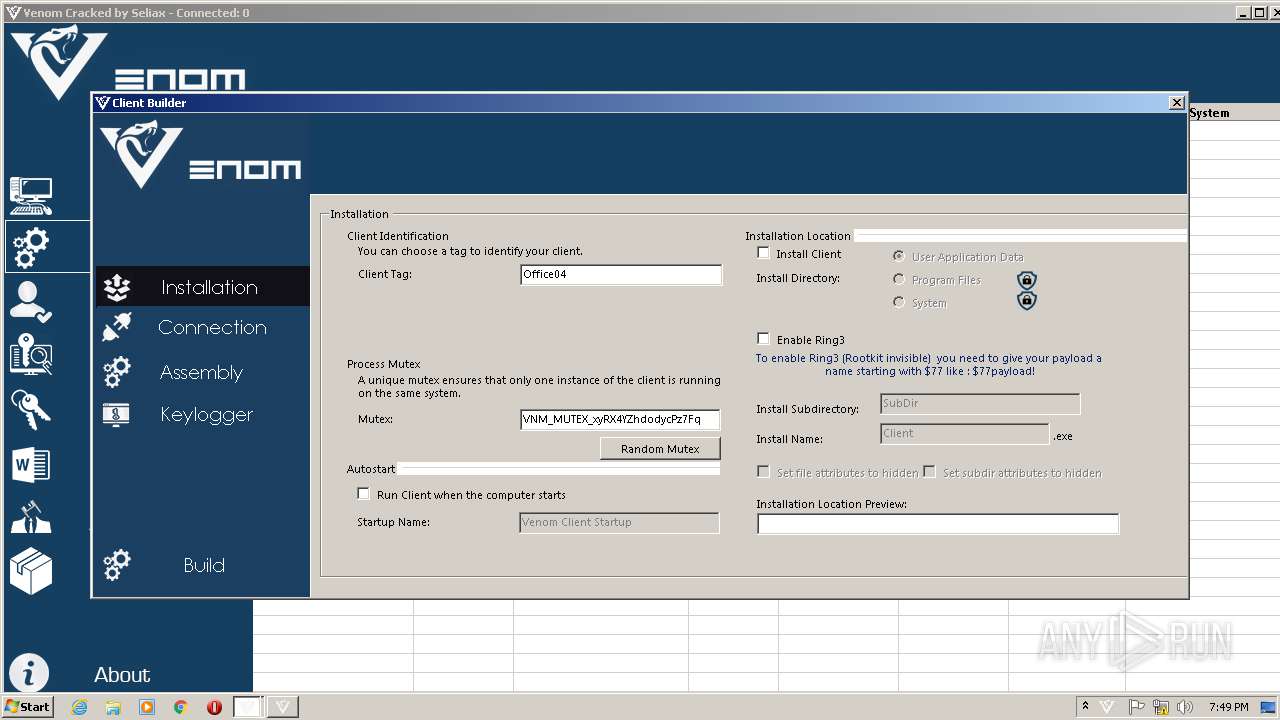
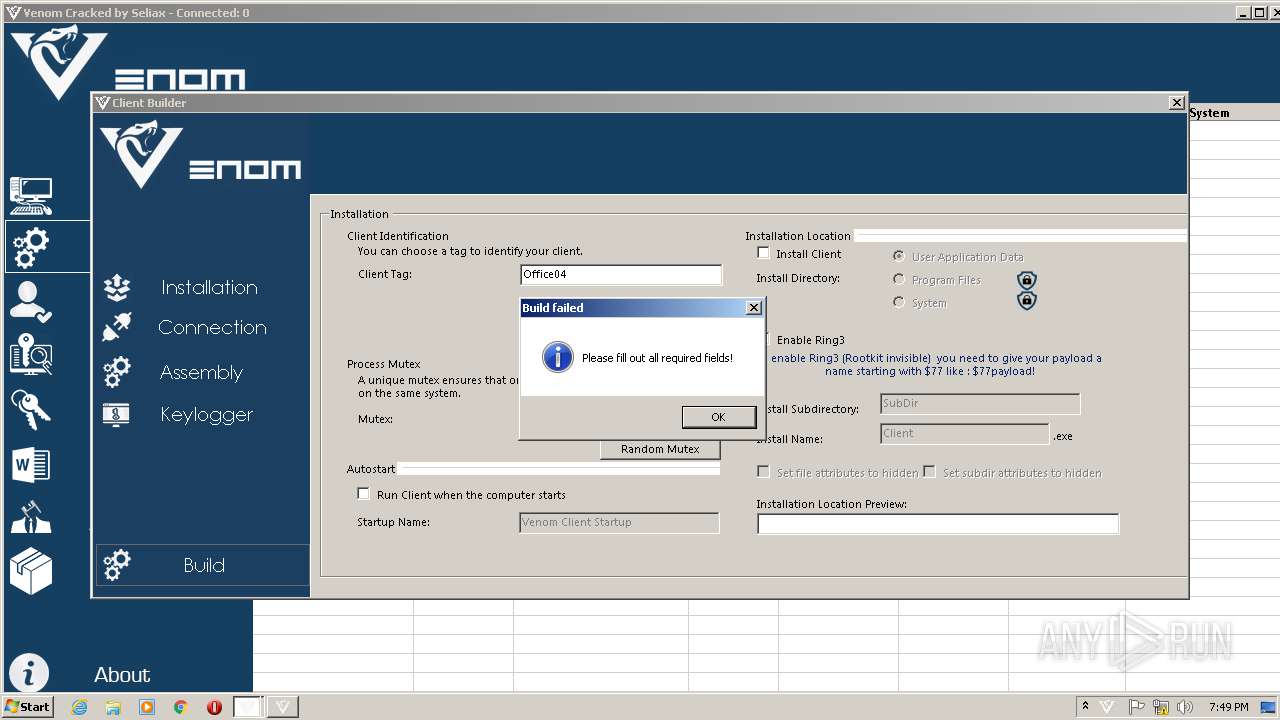
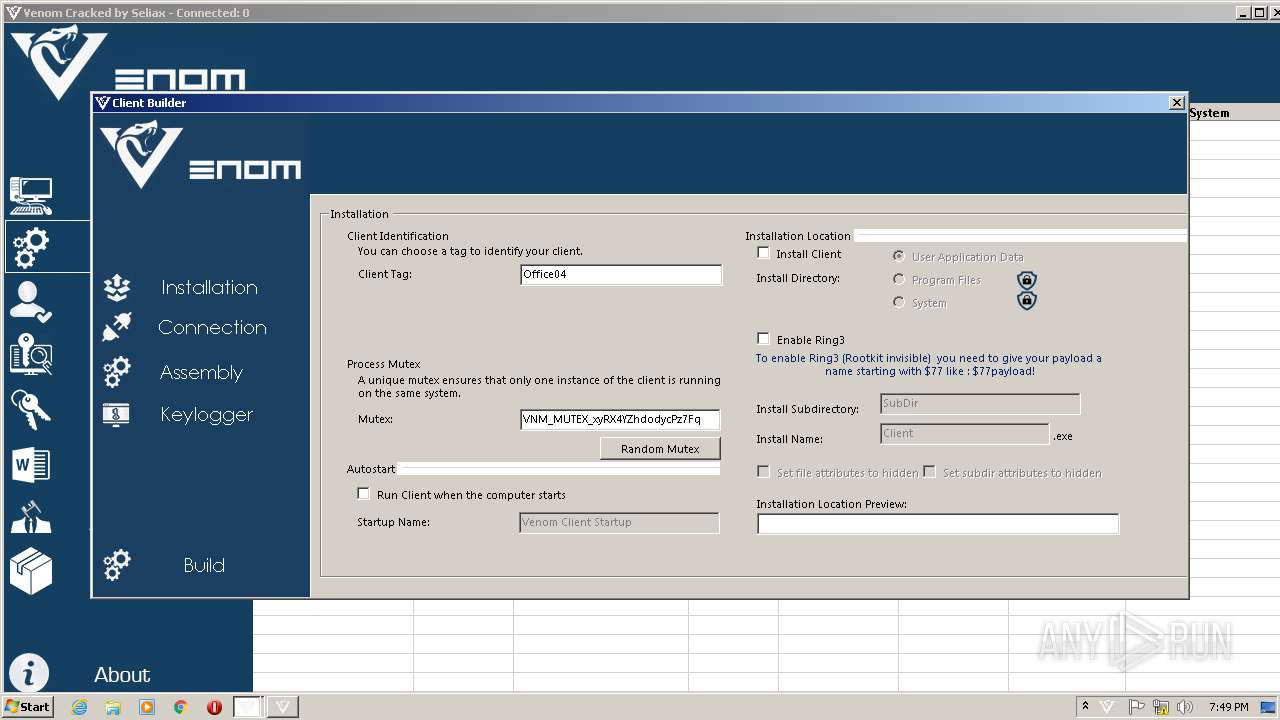
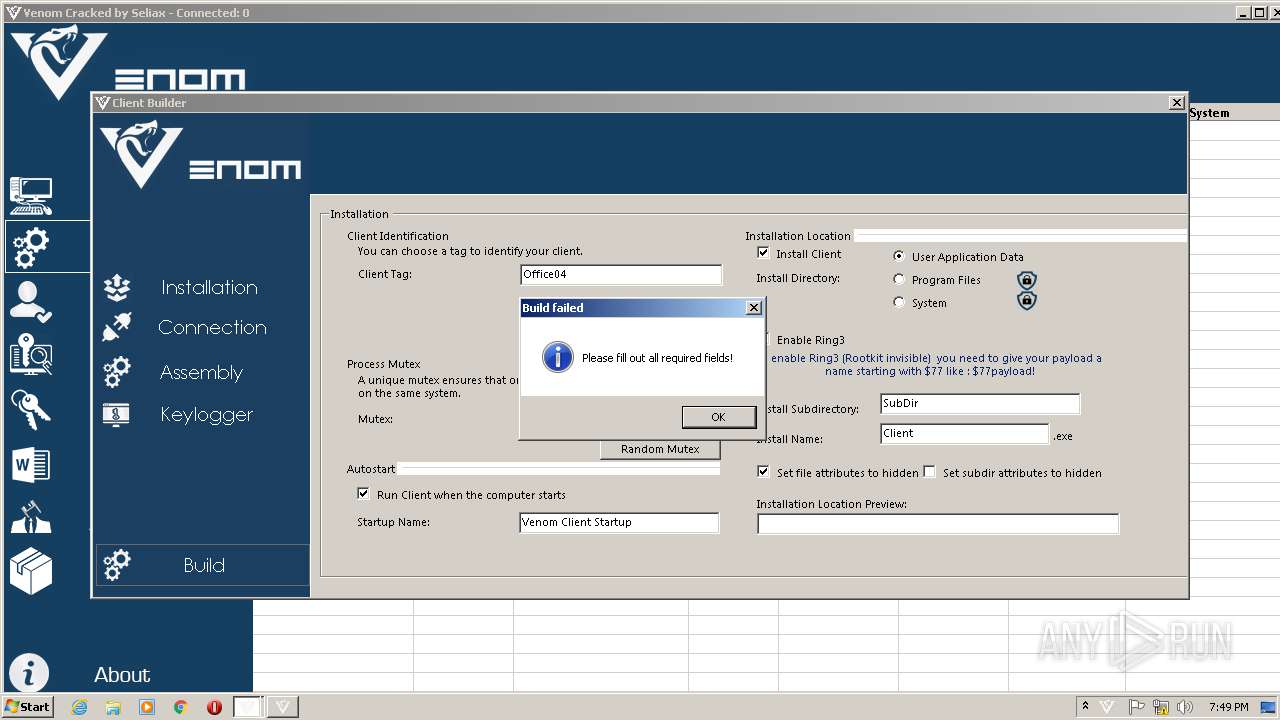
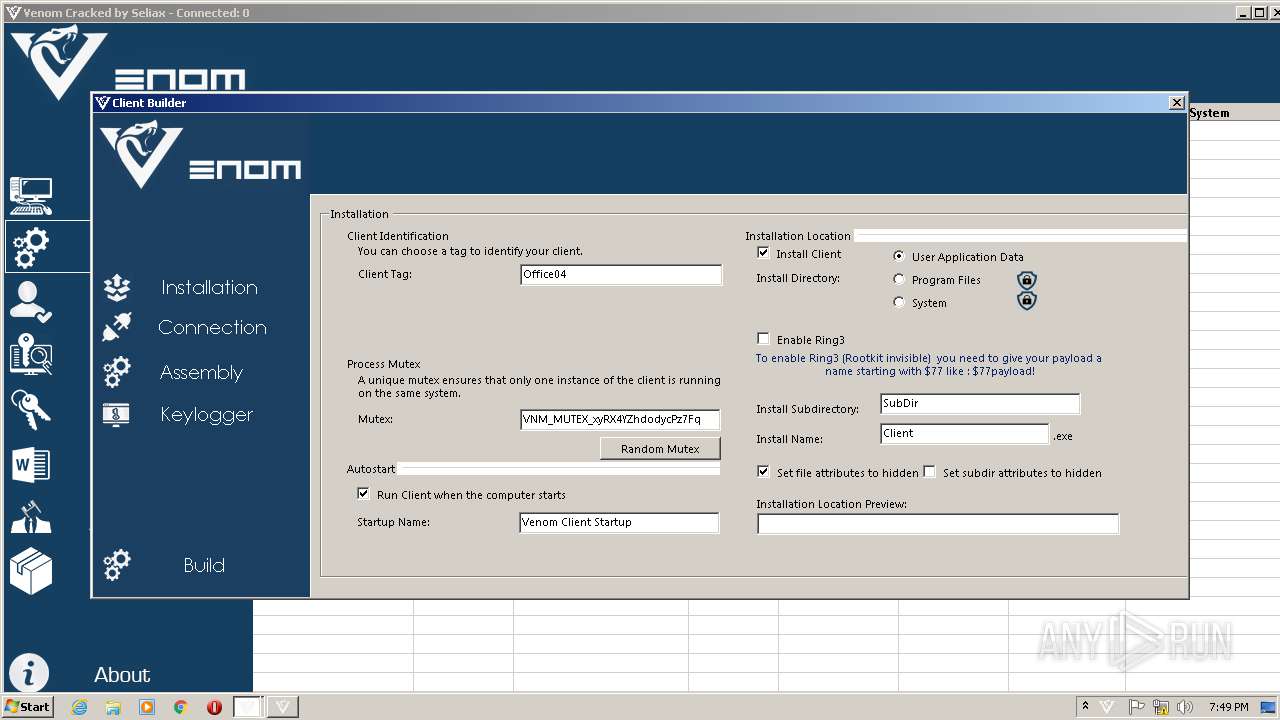
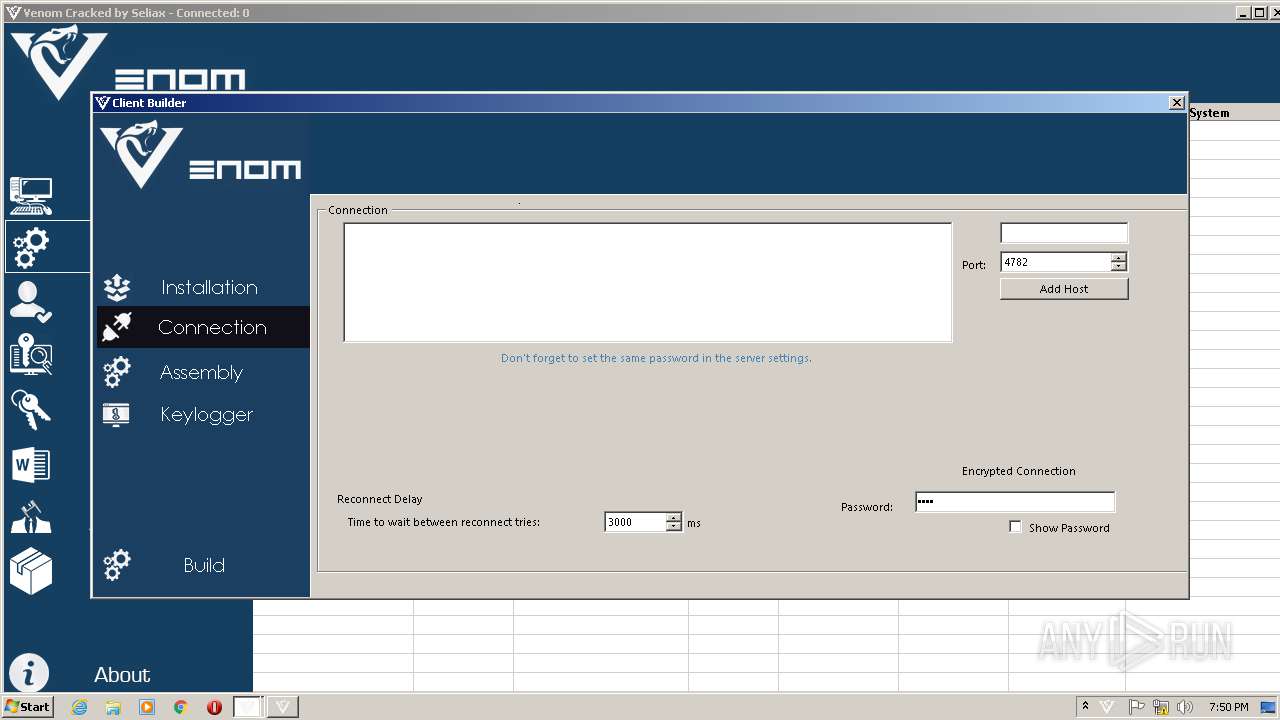
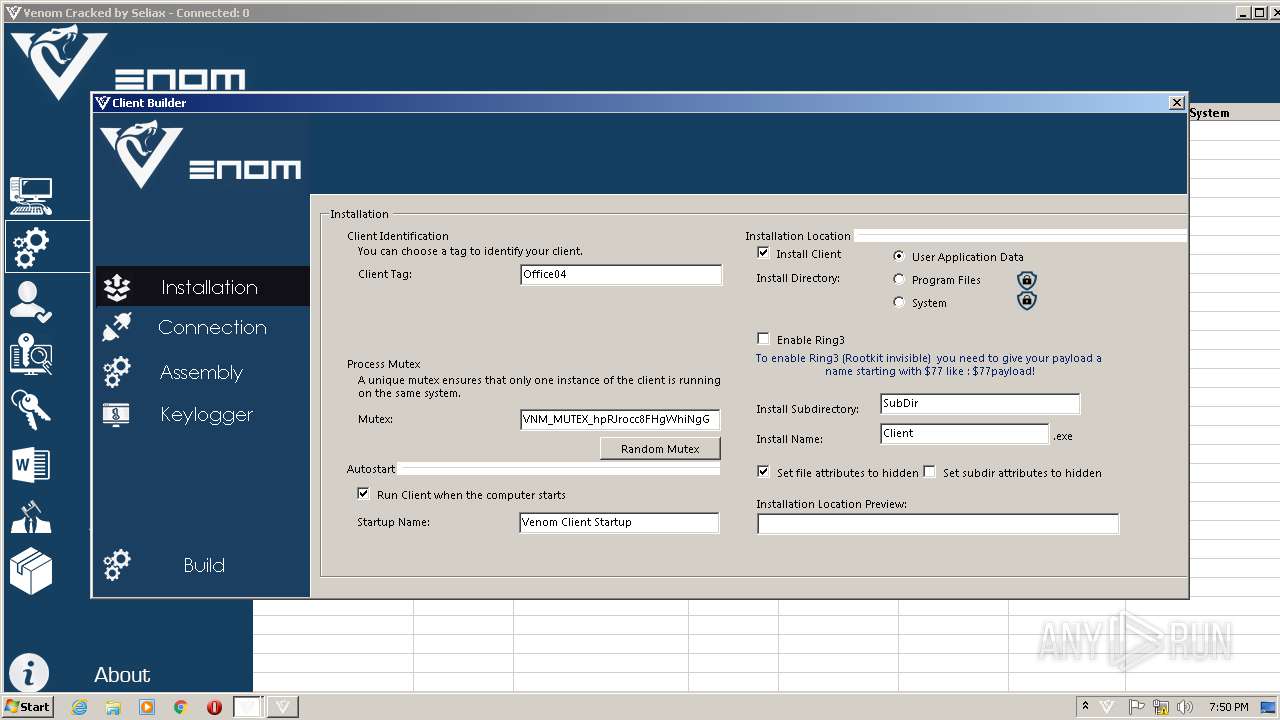
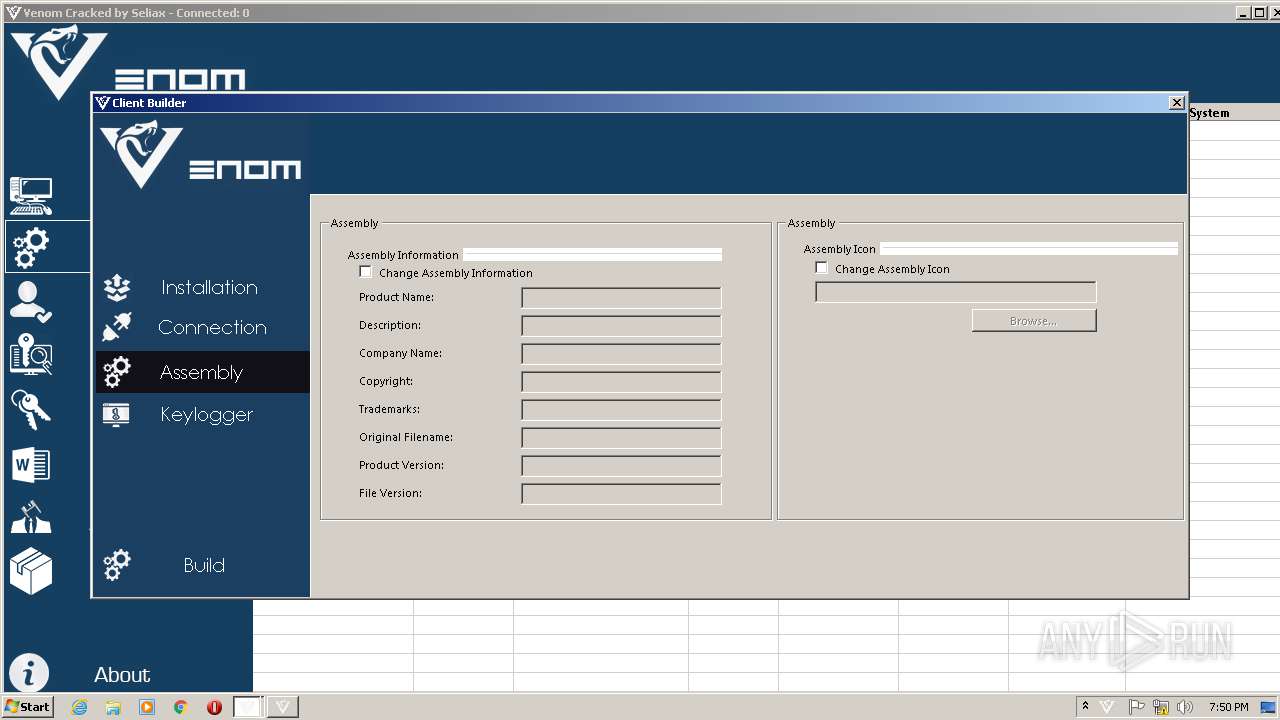
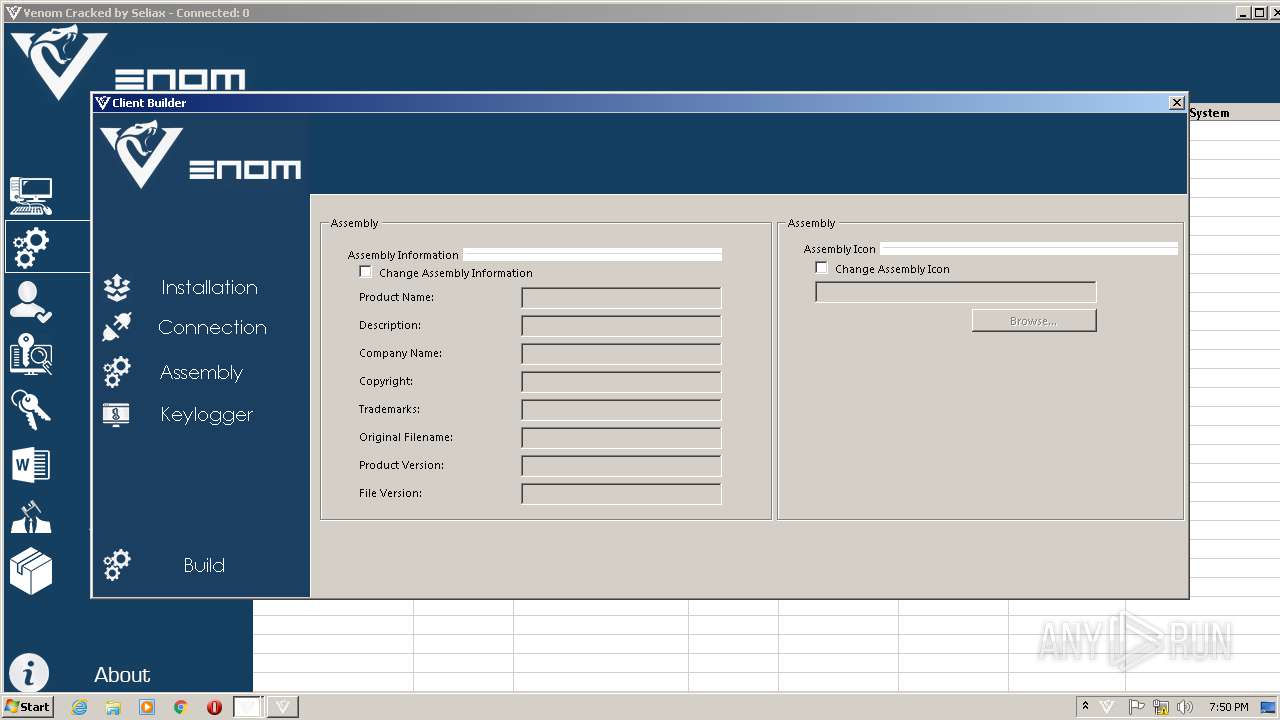
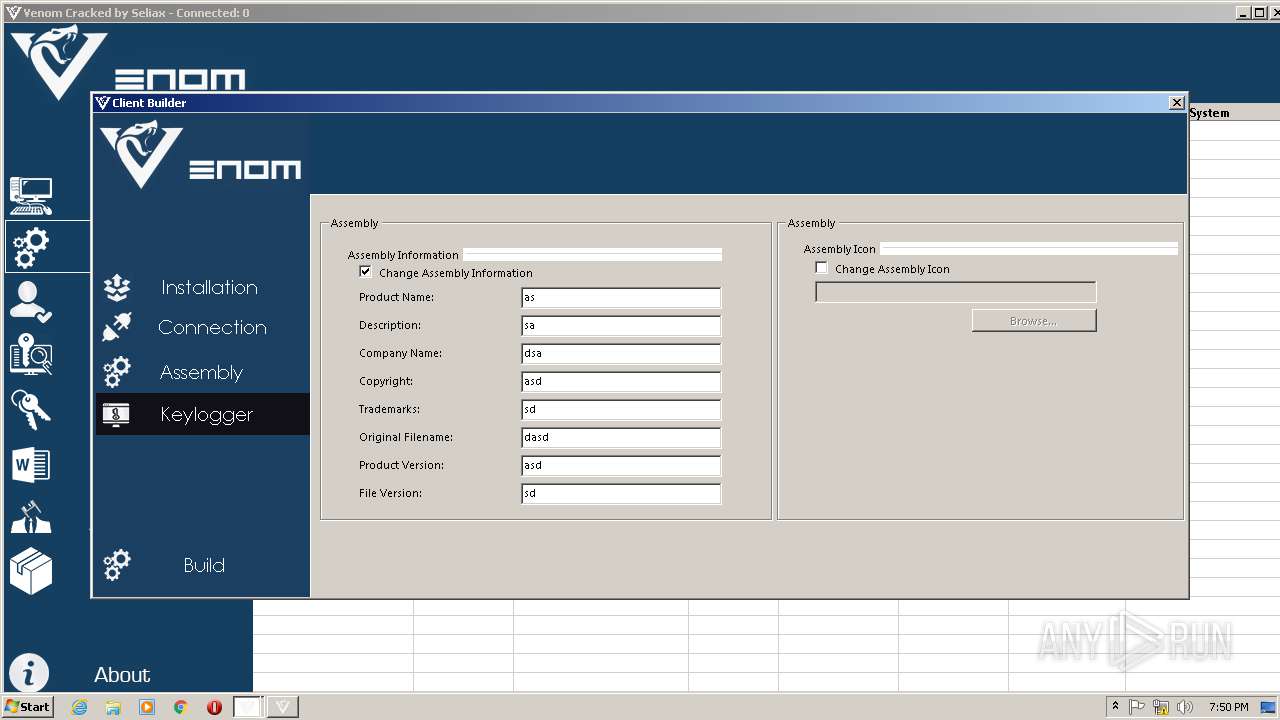
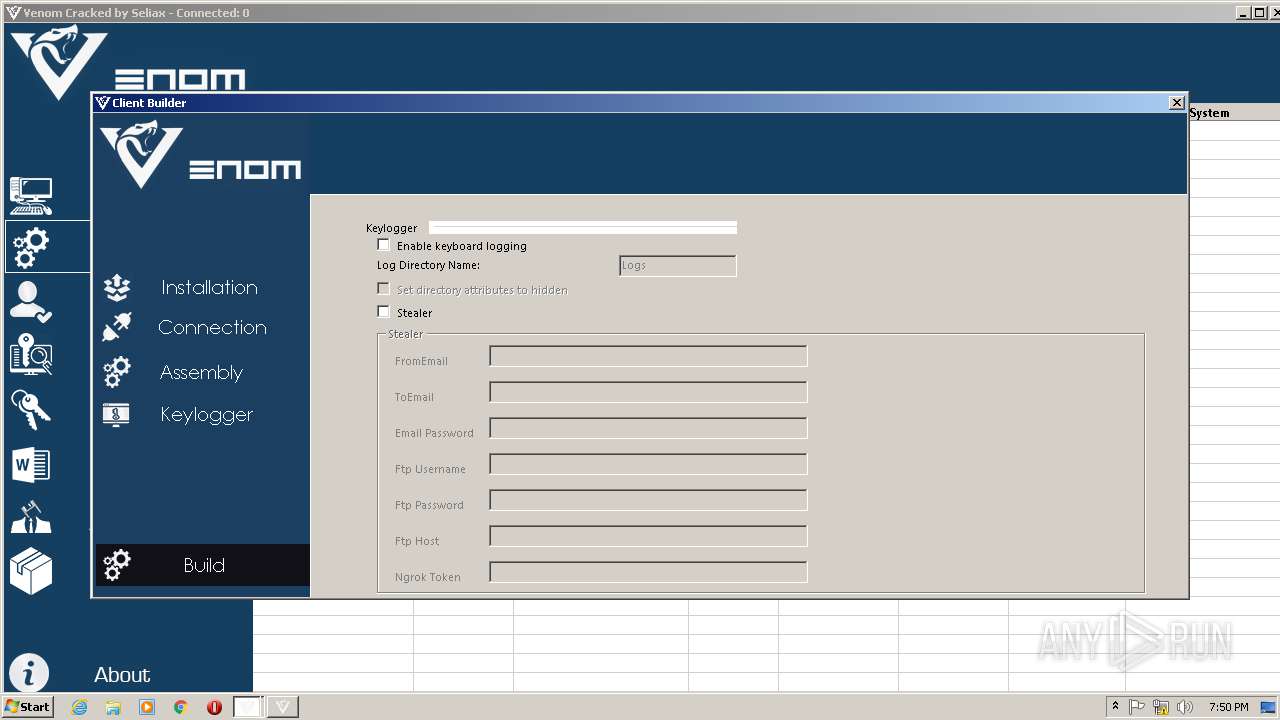
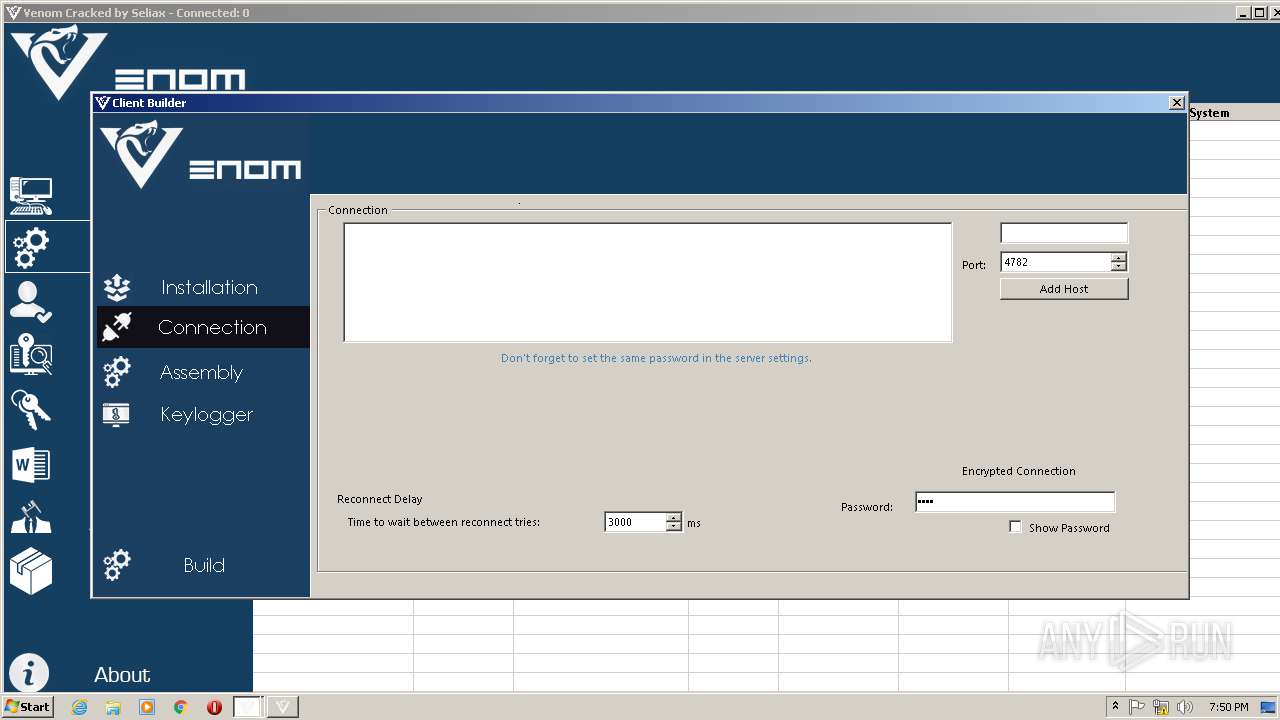
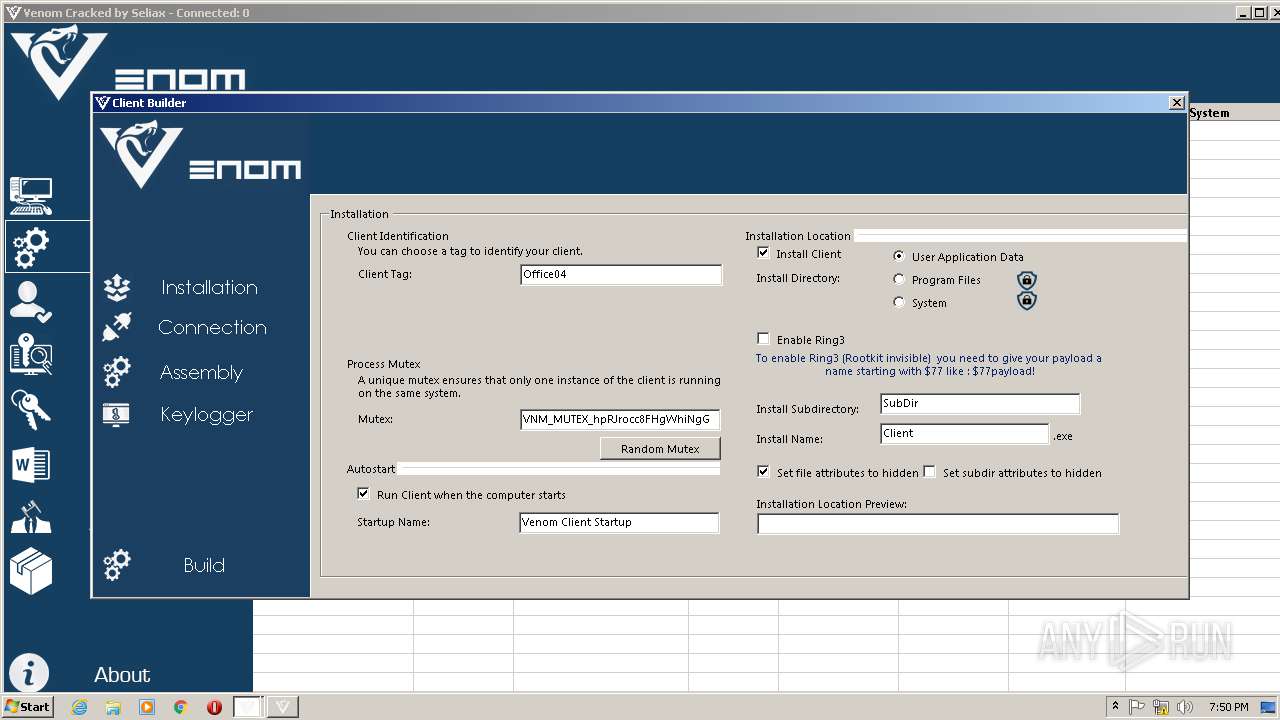
| 3420 | "C:\Users\admin\Desktop\Venom Cracked.exe" | C:\Users\admin\Desktop\Venom Cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Venom Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
Total events
847
Read events
819
Write events
28
Delete events
0
Modification events
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Venom Software Cracked.rar | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
Executable files
8
Suspicious files
0
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3124 | WinRAR.exe | C:\Users\admin\Desktop\Mono.Cecil.dll | executable | |
MD5:8DF4D6B5DC1629FCEFCDC20210A88EAC | SHA256:3E4288B32006FE8499B43A7F605BB7337931847A0AA79A33217A1D6D1A6C397E | |||
| 3124 | WinRAR.exe | C:\Users\admin\Desktop\Venom Cracked.exe | executable | |
MD5:1D0FA4545D87B727F483588E02A44E64 | SHA256:DB6BF0D28F066F069C108E2F41F98C25C27E9512BF8F1C9CAB9619D55078F78D | |||
| 3124 | WinRAR.exe | C:\Users\admin\Desktop\client.bin | executable | |
MD5:0CF92F1BF0544D71E5E9009FEF068A82 | SHA256:7128A2488B2D0084465CA1602A844EAFB191DE938FC70098D86CB65D17734778 | |||
| 3124 | WinRAR.exe | C:\Users\admin\Desktop\settings.xml | text | |
MD5:C66F9C71B325C88E4A0A37EC2F4477FF | SHA256:EBCEB1E061F55FDFB57FA685BF011CF310A06F63D14B34A52031A16380A0D236 | |||
| 3420 | Venom Cracked.exe | C:\Users\admin\Desktop\Profiles\Default.xml | text | |
MD5:— | SHA256:— | |||
| 3124 | WinRAR.exe | C:\Users\admin\Desktop\Vestris.ResourceLib.dll | executable | |
MD5:64E9CB25AEEFEEBA3BB579FB1A5559BC | SHA256:34CAB594CE9C9AF8E12A6923FC16468F5B87E168777DB4BE2F04DB883C1DB993 | |||
| 3124 | WinRAR.exe | C:\Users\admin\Desktop\vncviewer.exe | executable | |
MD5:311DE77BCDF9808908F628ECD26A098B | SHA256:DAC7F8191D05A8F2AB0F05C975BAE826A2BB4C10BD6B40B0B1BE0A260F5CD558 | |||
| 3124 | WinRAR.exe | C:\Users\admin\Desktop\VelyseTheme.dll | executable | |
MD5:52BFCE7E8DC04712CD2091C12F126F77 | SHA256:B332DAAC3B130051E8D2A5FD325D6D094CA1C9A602B45667855341F4CB9100AE | |||
| 3124 | WinRAR.exe | C:\Users\admin\Desktop\Venom Binder.exe | executable | |
MD5:D4FD9DB0EB77EFAC83278A095C28E6AA | SHA256:94DBDB36D17F7B5DC5D34763EEFB877756BBEAEDEB7D41BC35DE9E6C03BA983C | |||
| 3192 | vncviewer.exe | C:\Users\admin\Desktop\options.vnc | text | |
MD5:24F5E966D65E79745D3303B950496810 | SHA256:9B7645A27B48EC94958A9A95326860C811B9FB3B9D82901102671E7C64416D3F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report