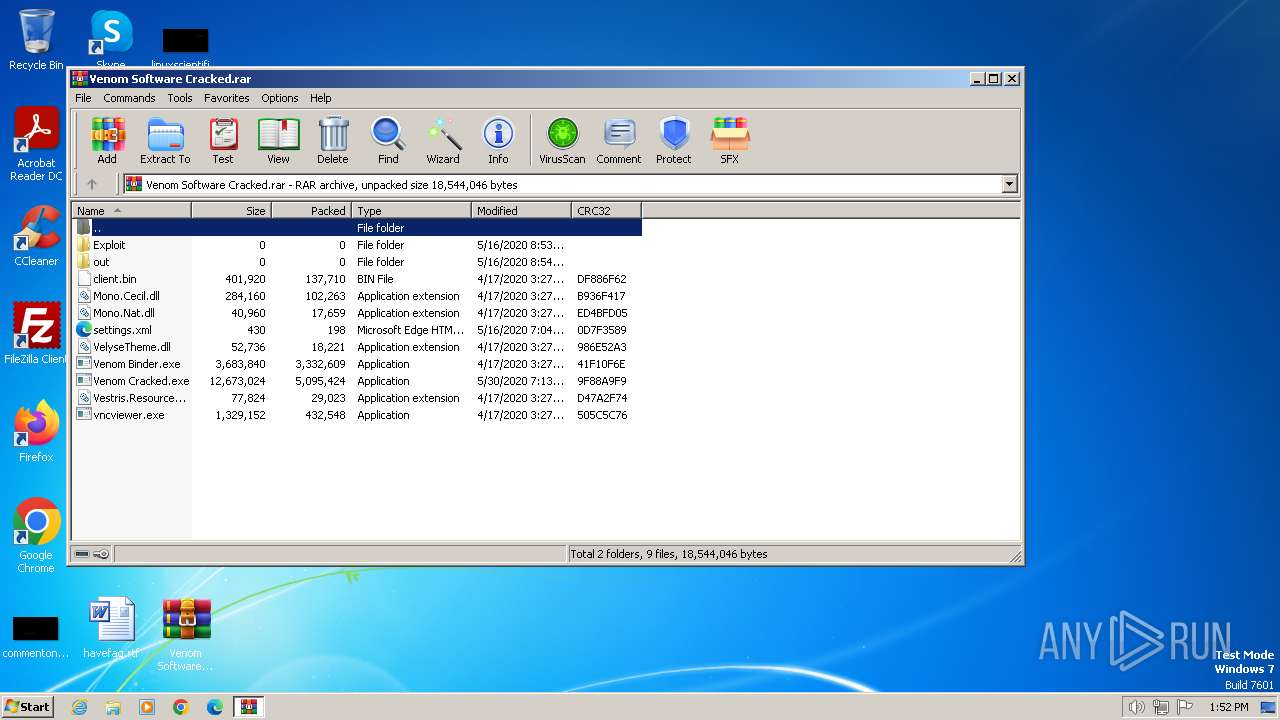
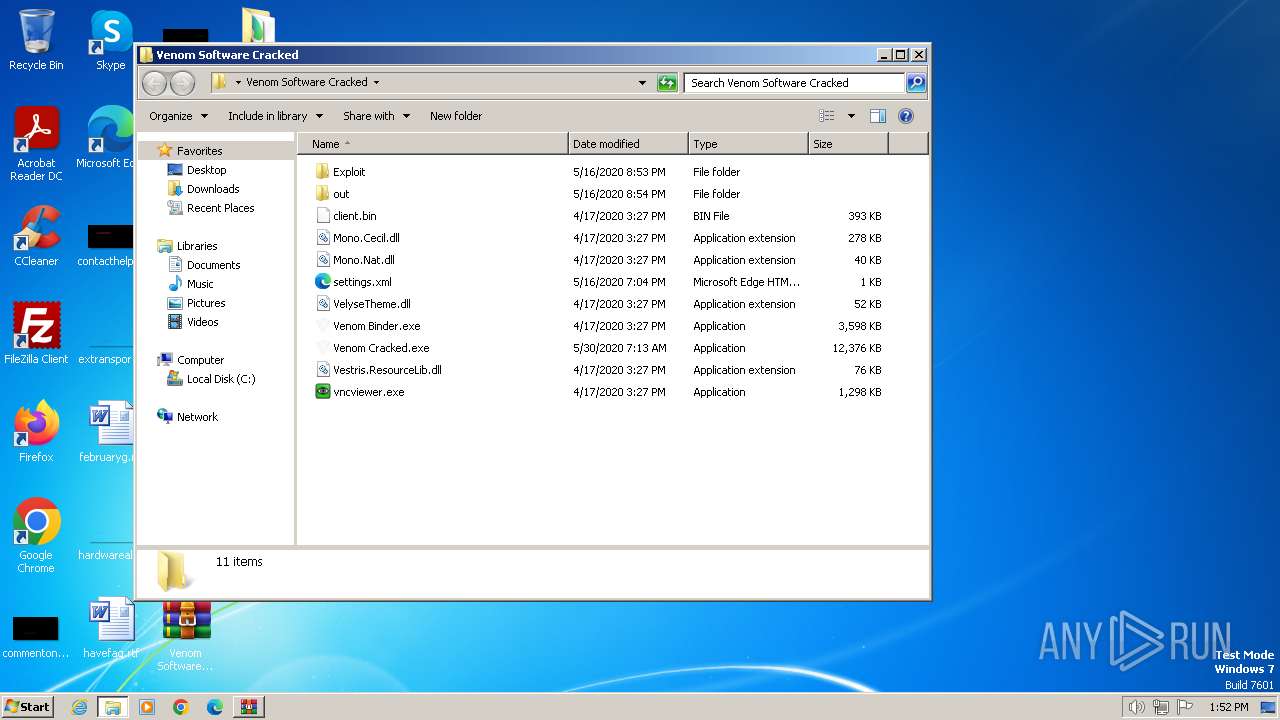
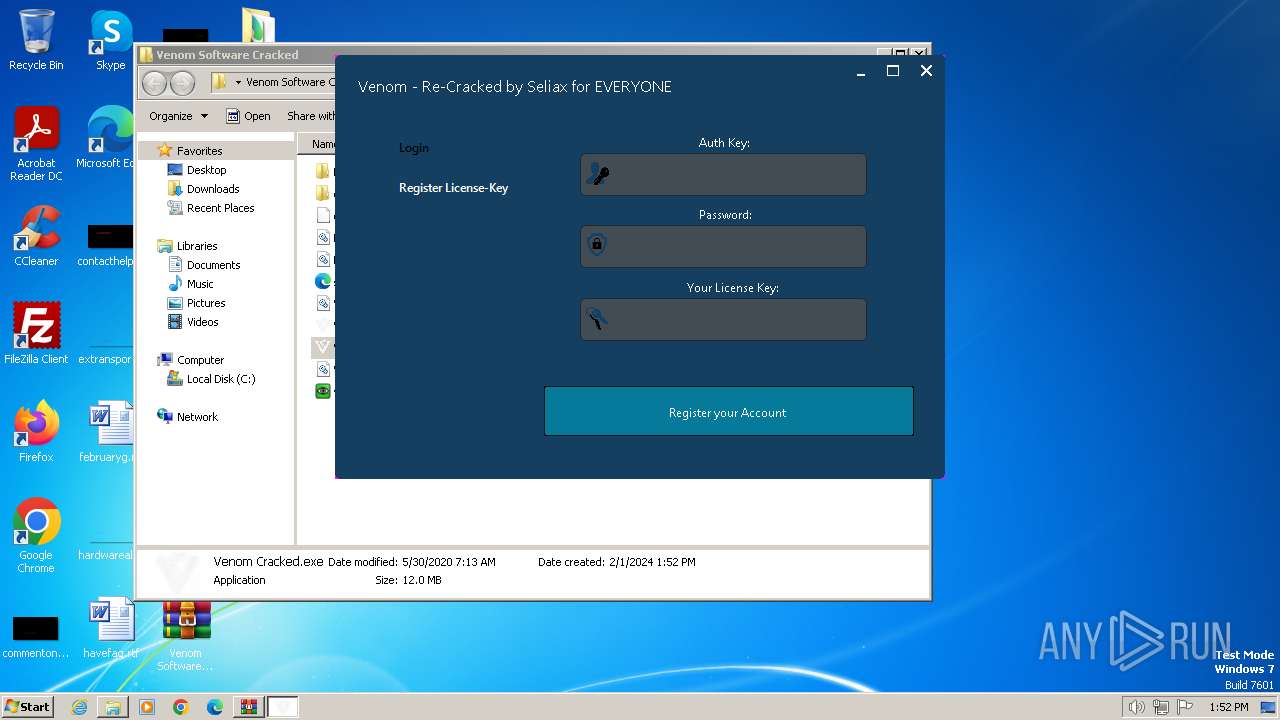
| File name: | Venom Software Cracked.rar |
| Full analysis: | https://app.any.run/tasks/7aec3c45-937d-4495-960b-af628aa6b2ef |
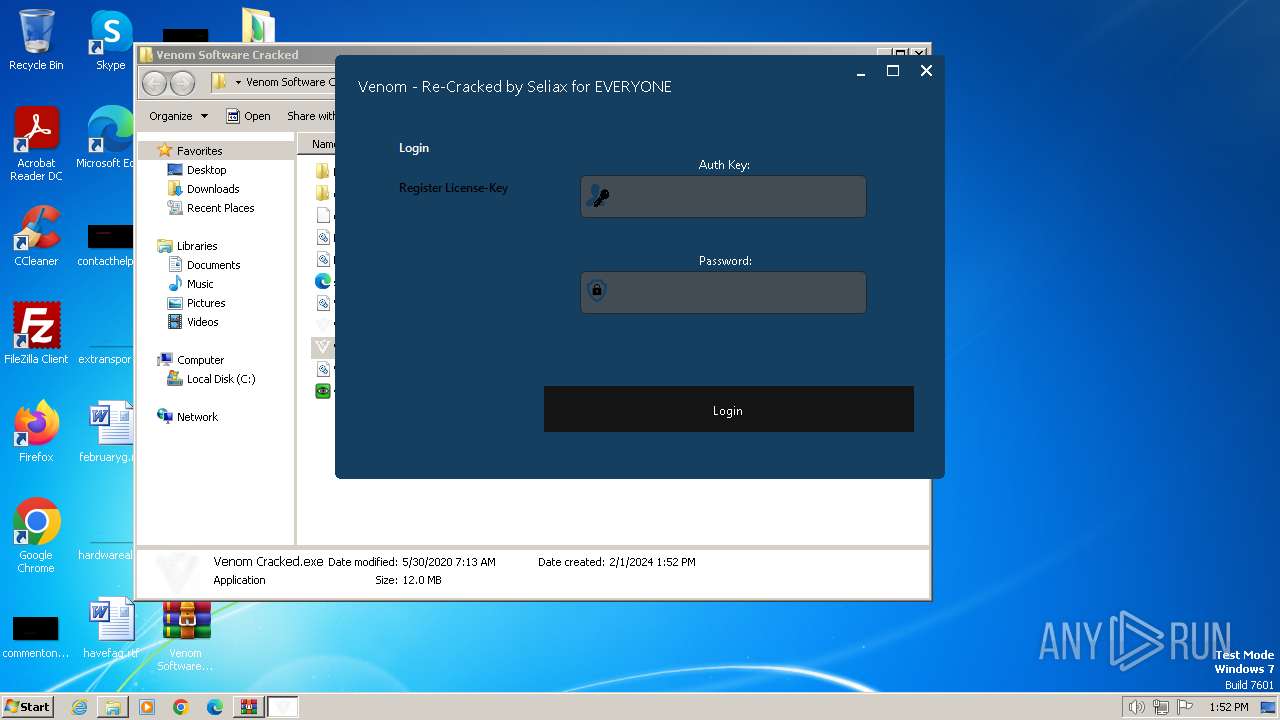
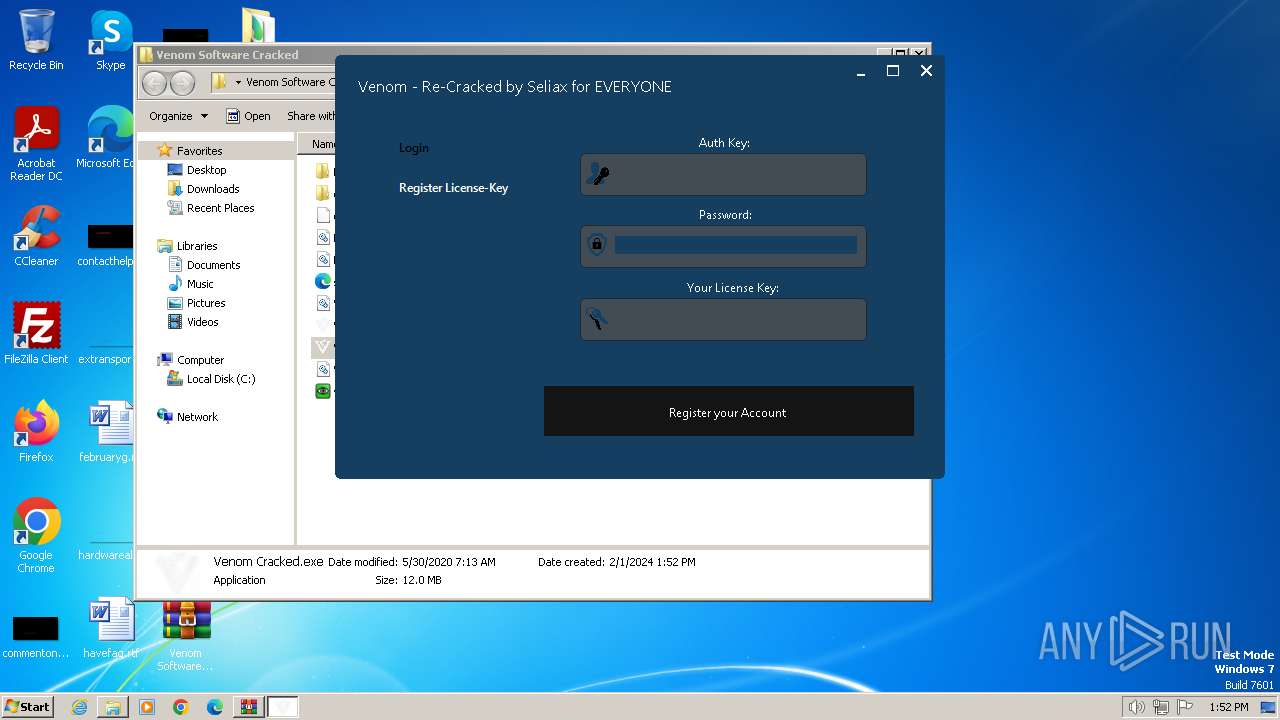
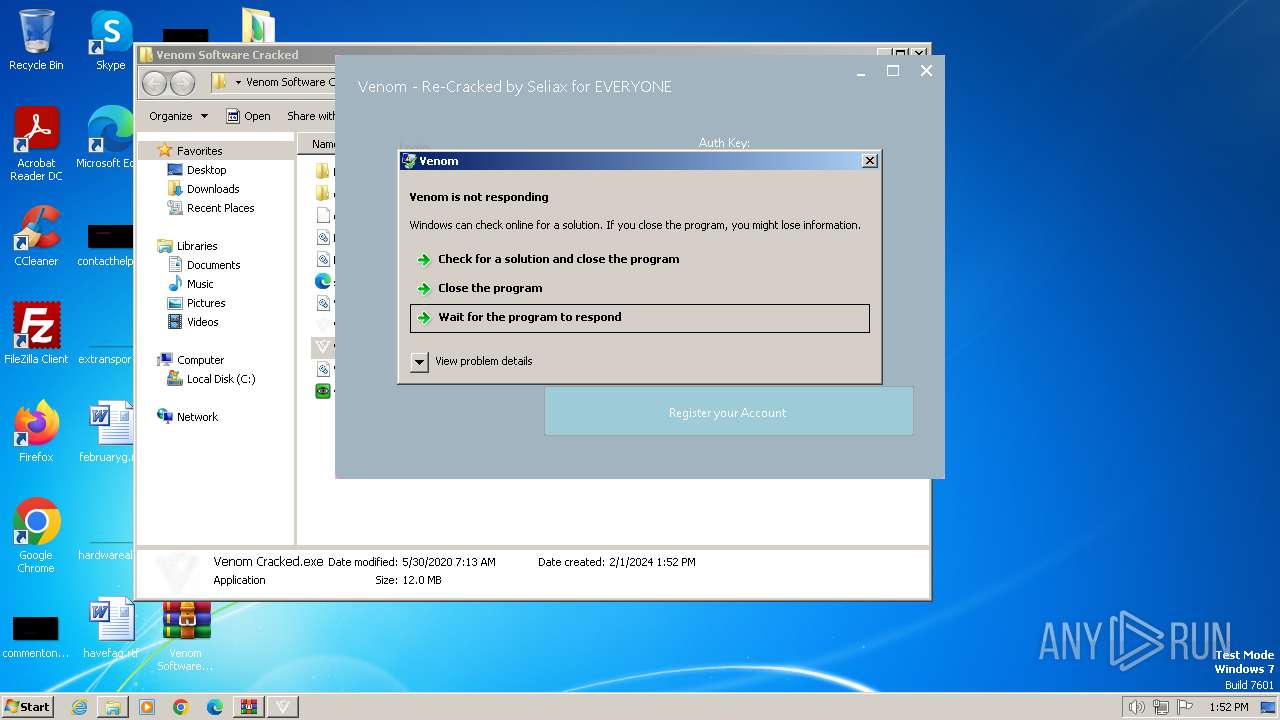
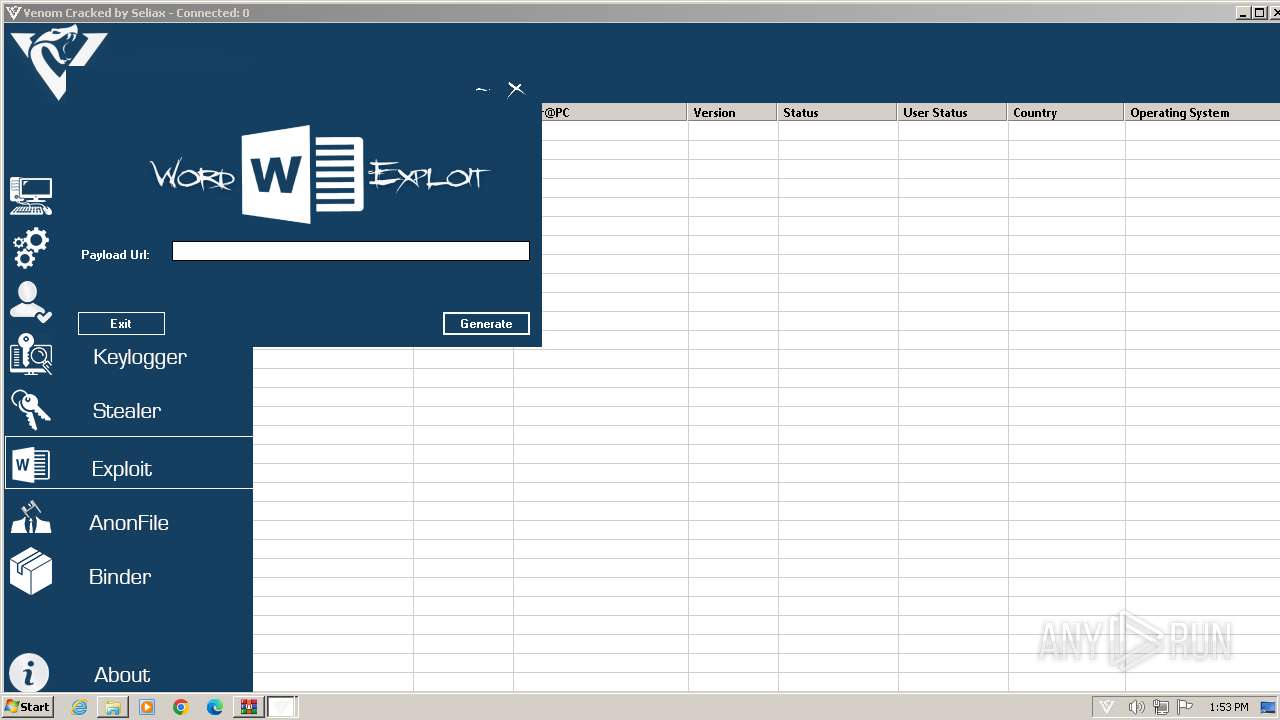
| Verdict: | Malicious activity |
| Analysis date: | February 01, 2024, 13:52:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F698E120B79D5F39ECD33D39E231A61A |
| SHA1: | 4F3A6F77CAC6A7E5187931161C2CE618DDAB6C3A |
| SHA256: | 0E4C8A185B8DA513D4D5071BFE52249D4C1DDCFECA03B68DD73013EEE5BD284C |
| SSDEEP: | 98304:os9InPj6BdHmCOTiCDgcSF5OgoH0e8o1NgjNmsLe3855hYVWeQCfS+c1mwlU016z:oL9EuaX6 |
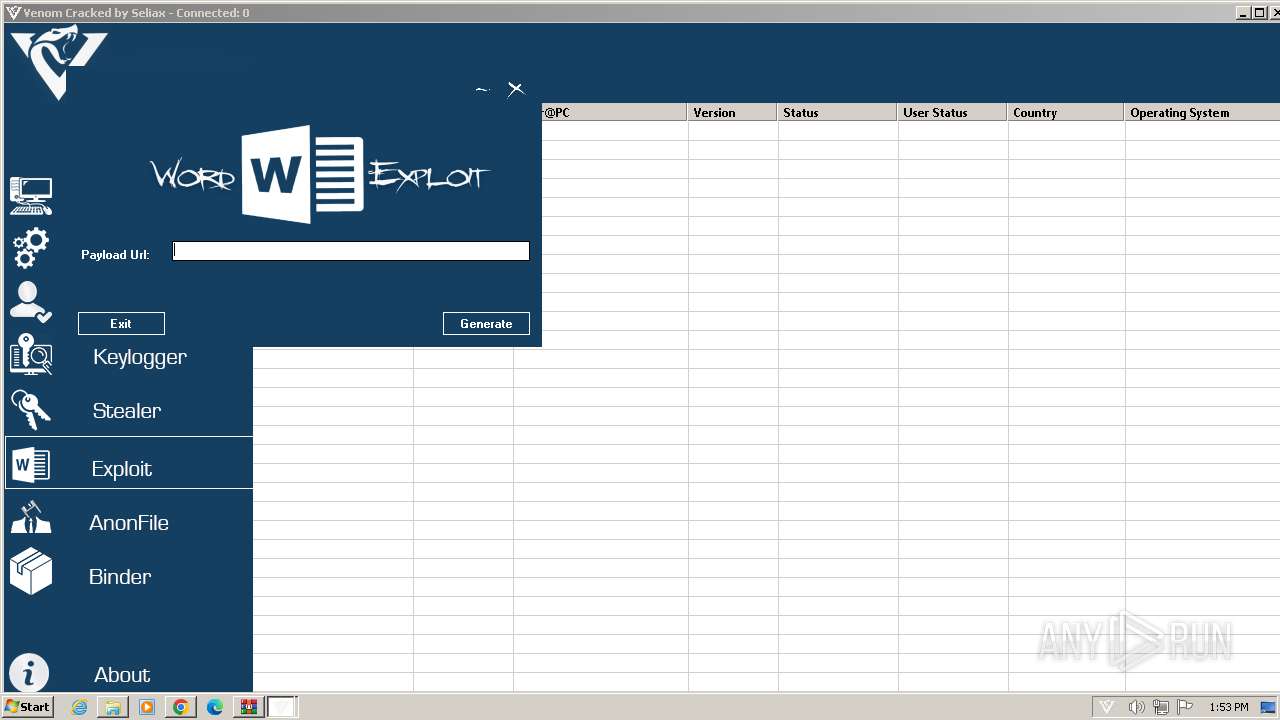
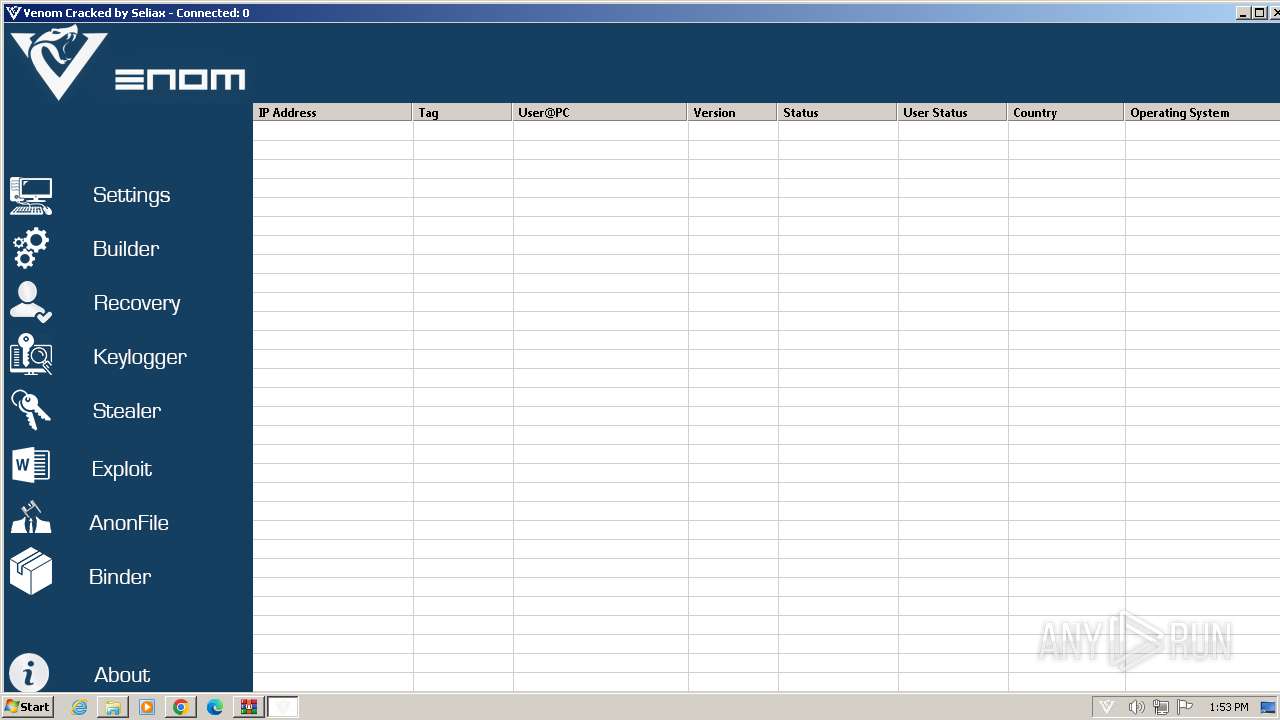
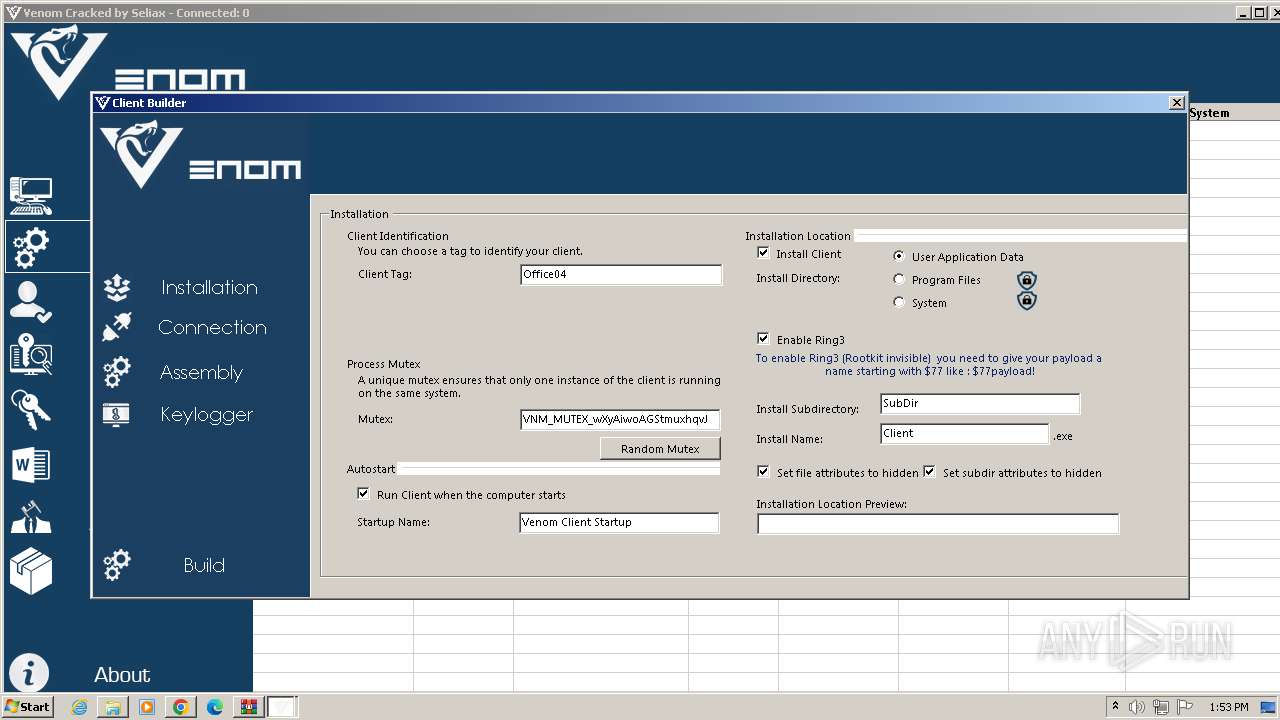
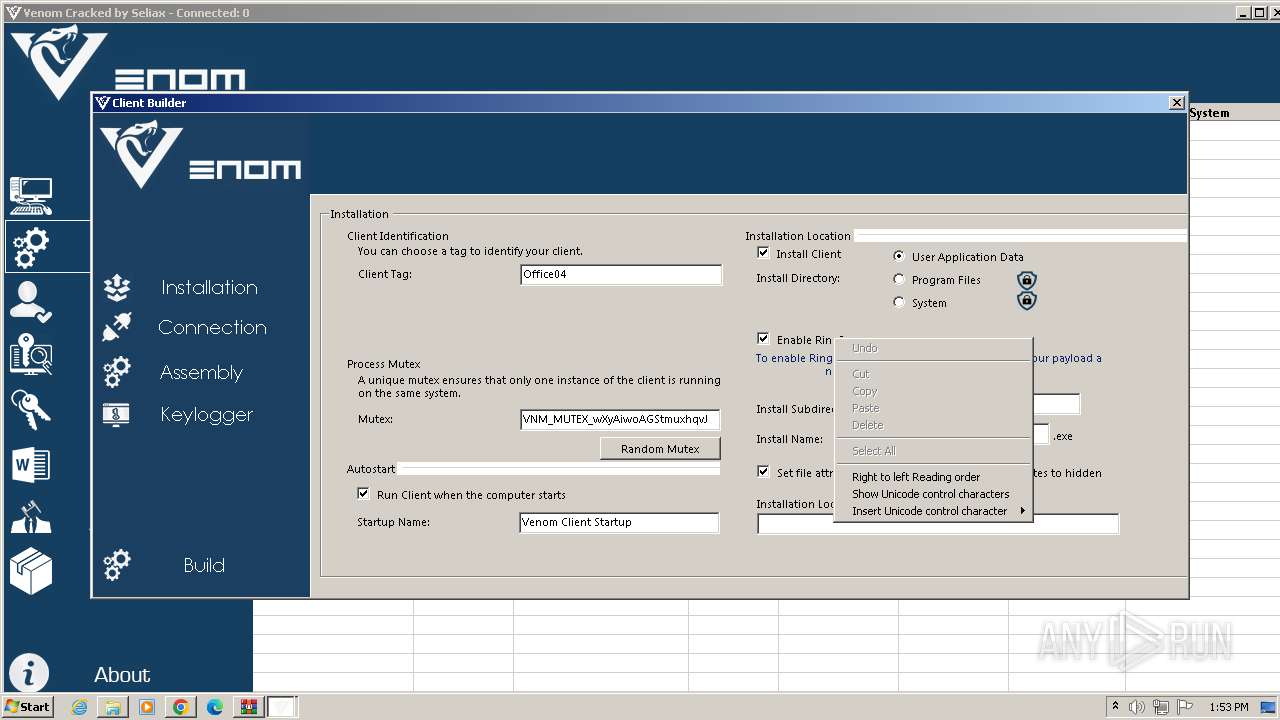
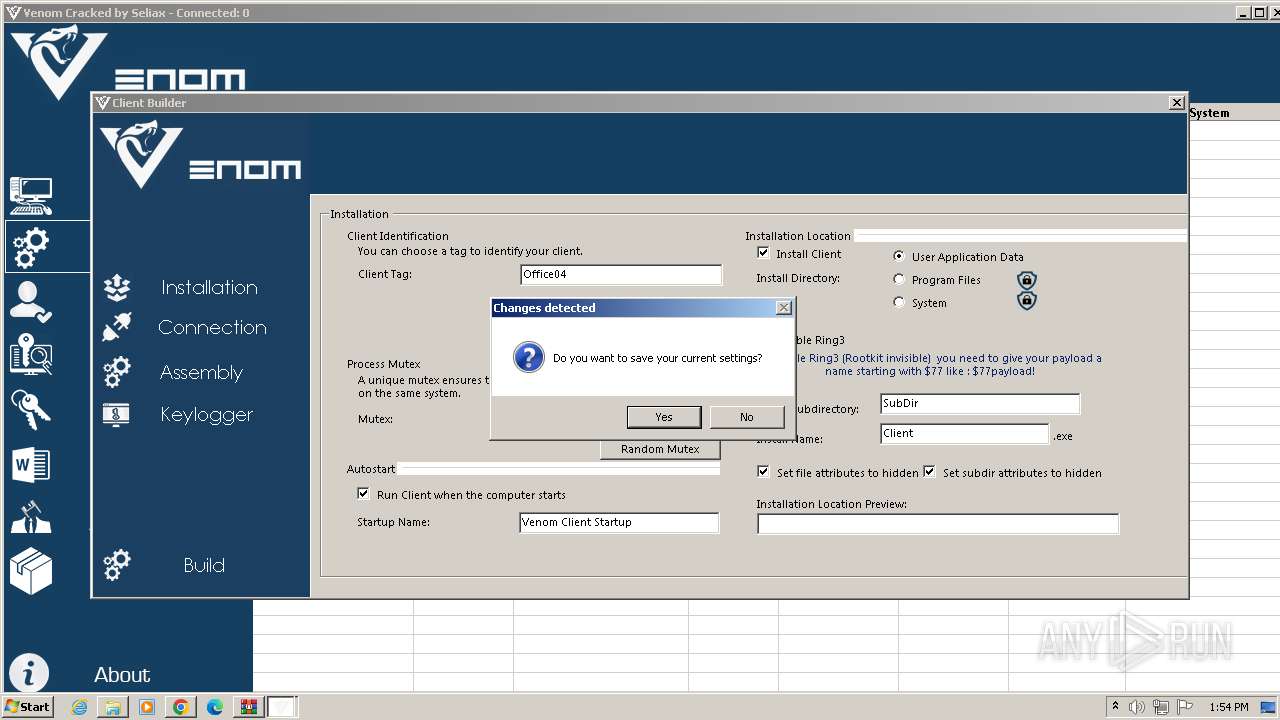
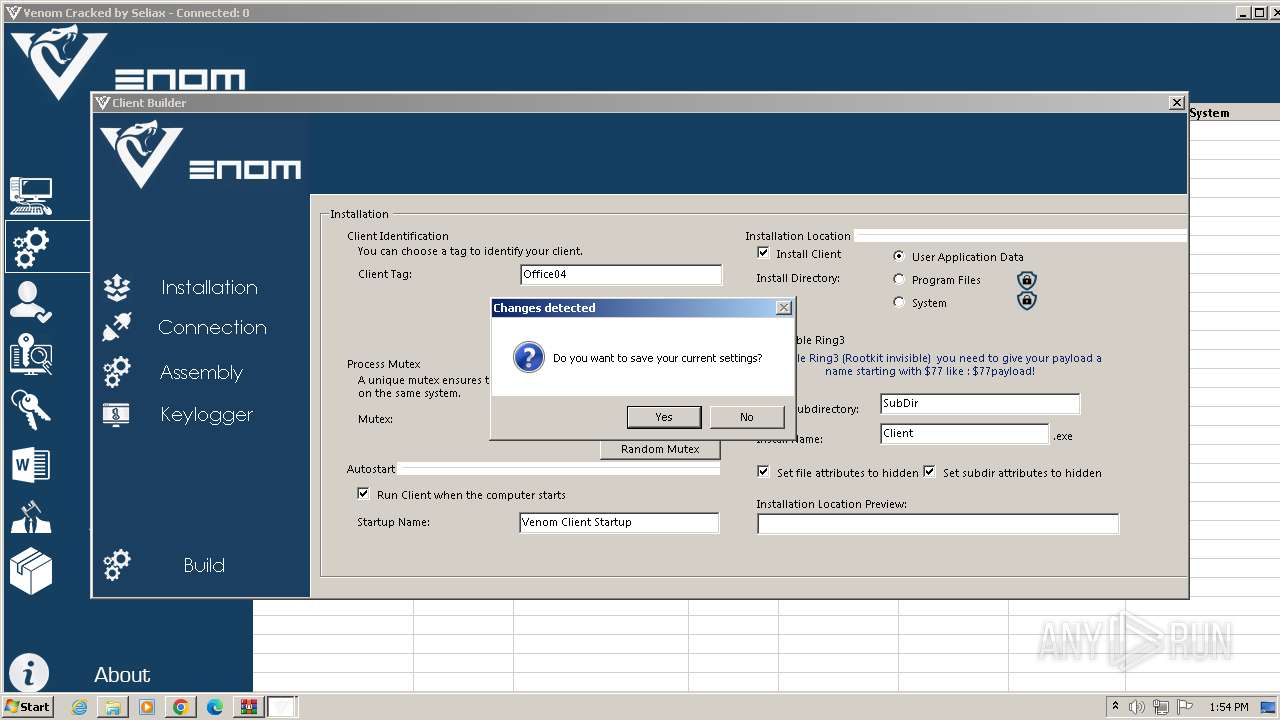
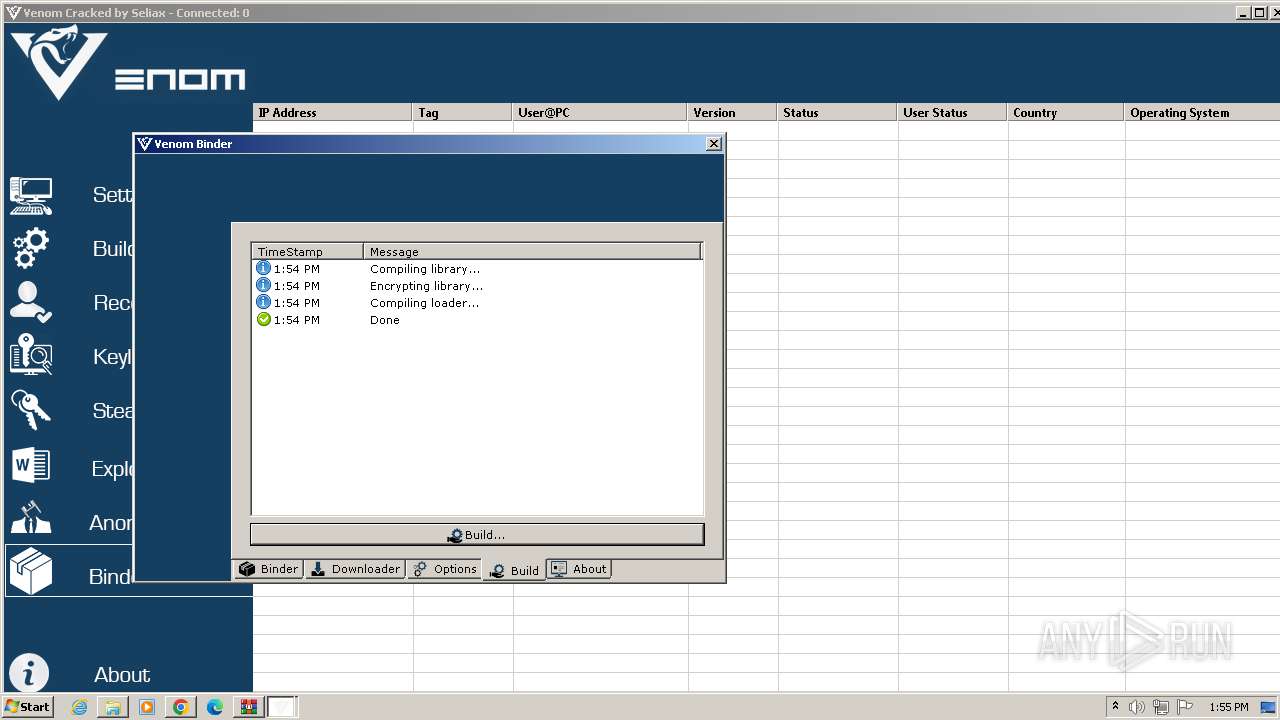
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1588)
- csc.exe (PID: 1796)
- csc.exe (PID: 2876)
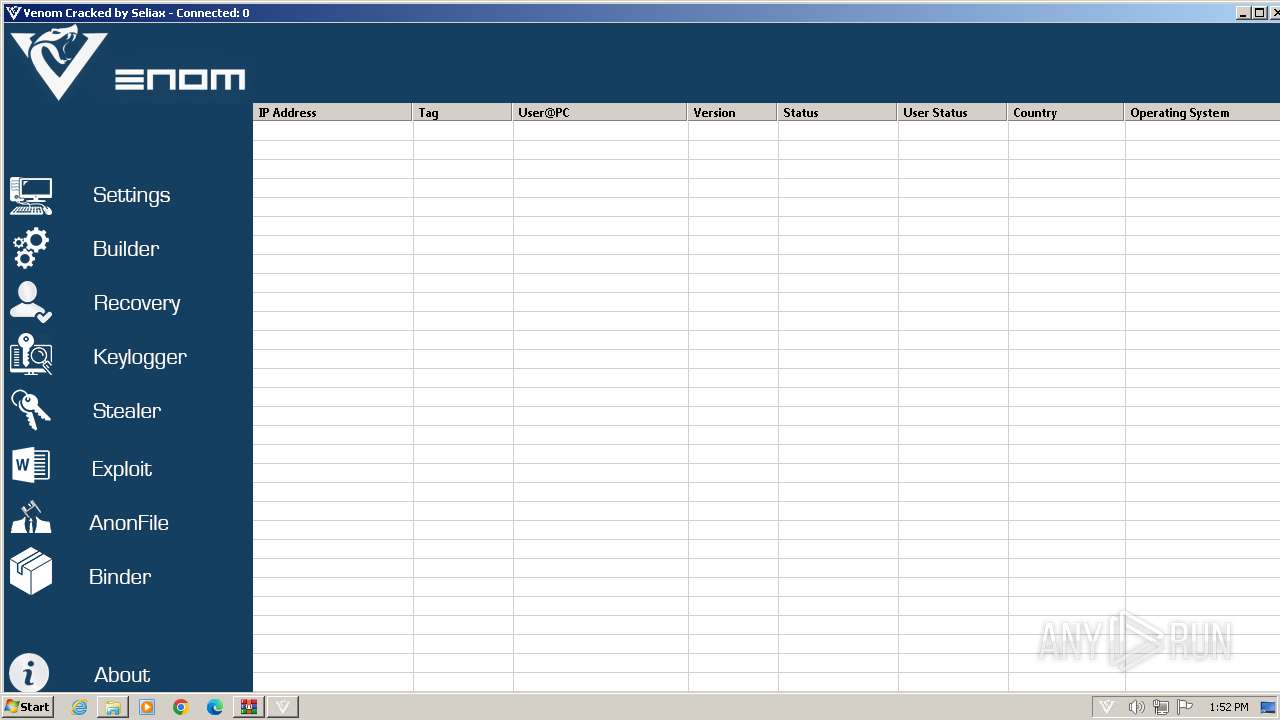
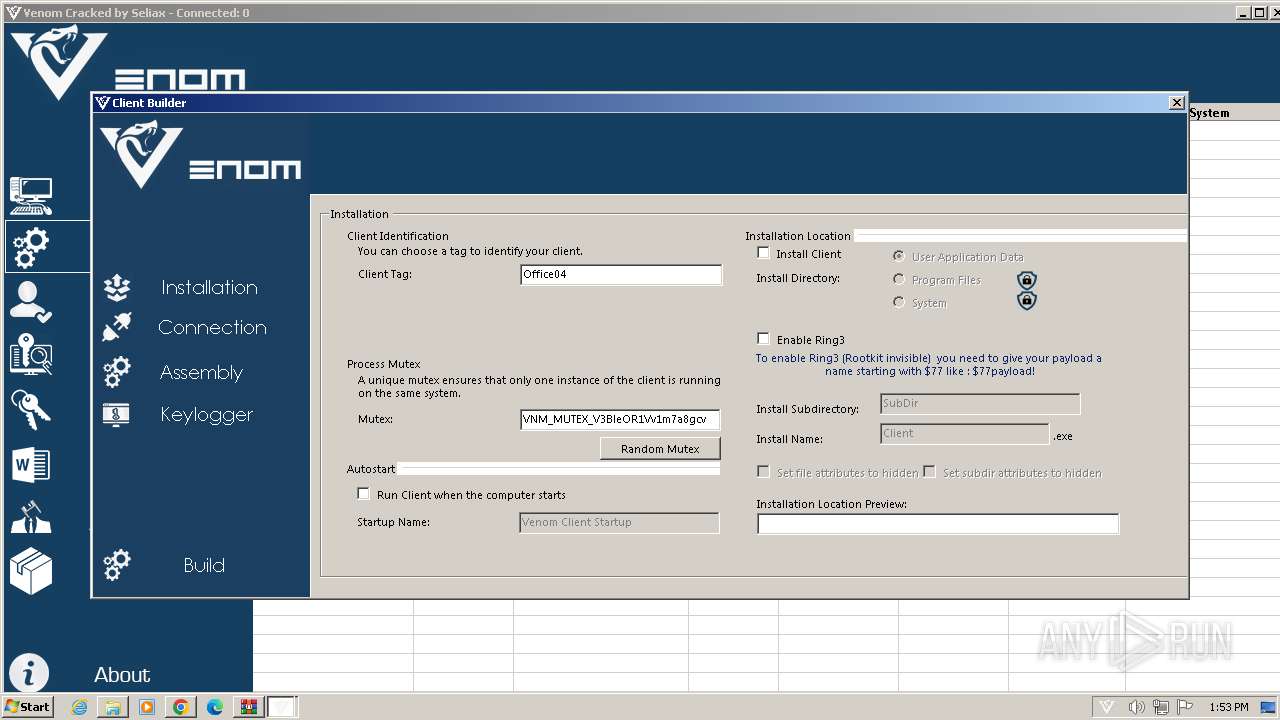
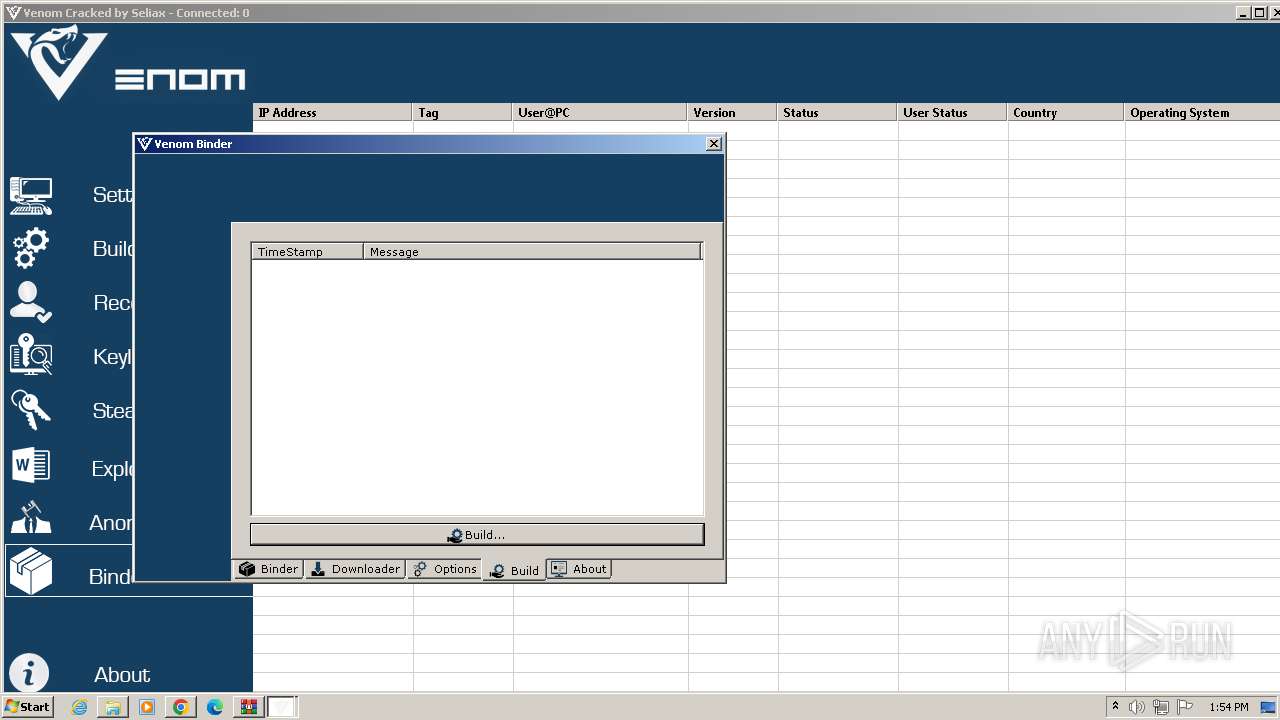
Starts Visual C# compiler
- Venom Cracked.exe (PID: 3360)
SUSPICIOUS
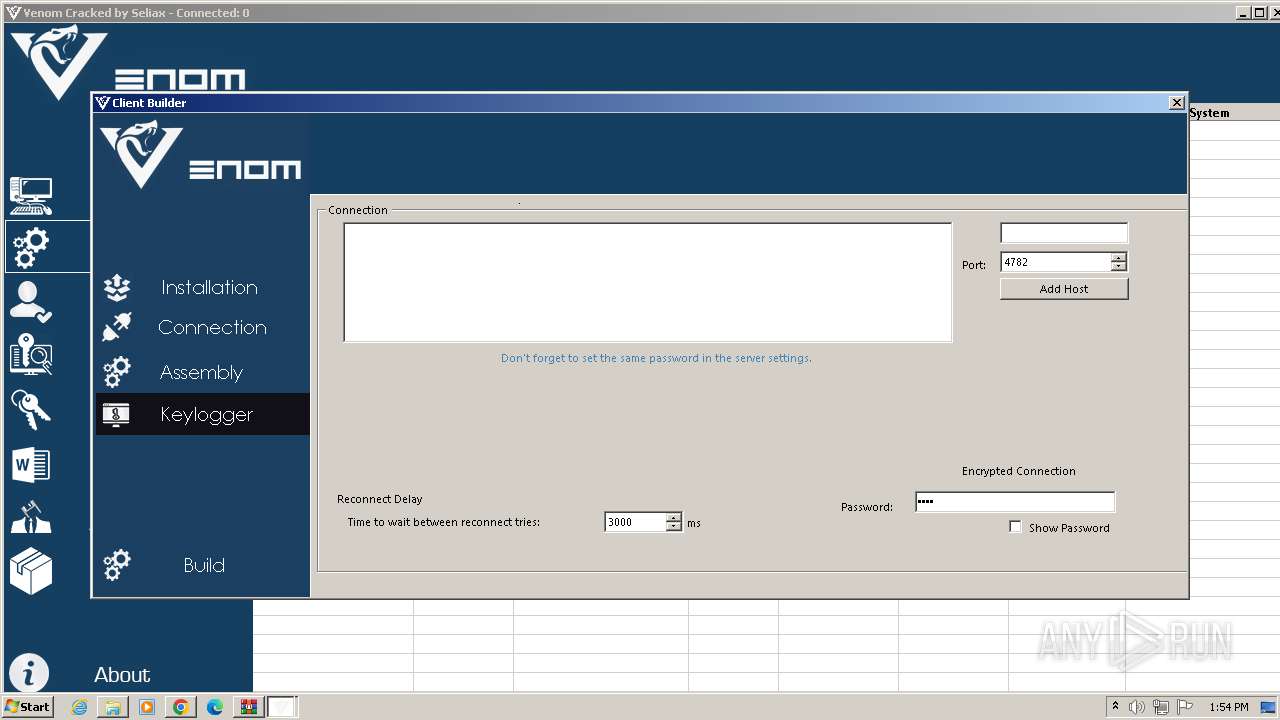
Connects to unusual port
- Venom Cracked.exe (PID: 2380)
Executable content was dropped or overwritten
- csc.exe (PID: 1796)
- csc.exe (PID: 2876)
Uses .NET C# to load dll
- Venom Cracked.exe (PID: 3360)
Reads the Internet Settings
- Venom Cracked.exe (PID: 3360)
INFO
Checks supported languages
- Venom Cracked.exe (PID: 2380)
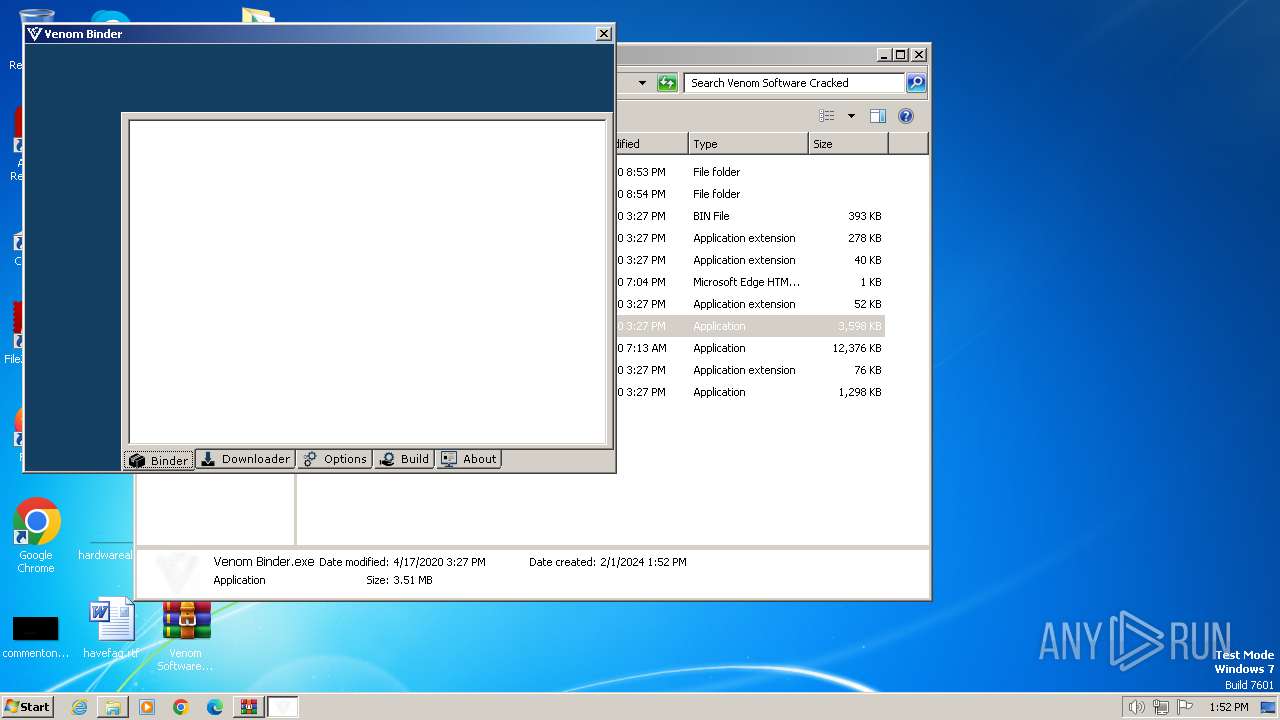
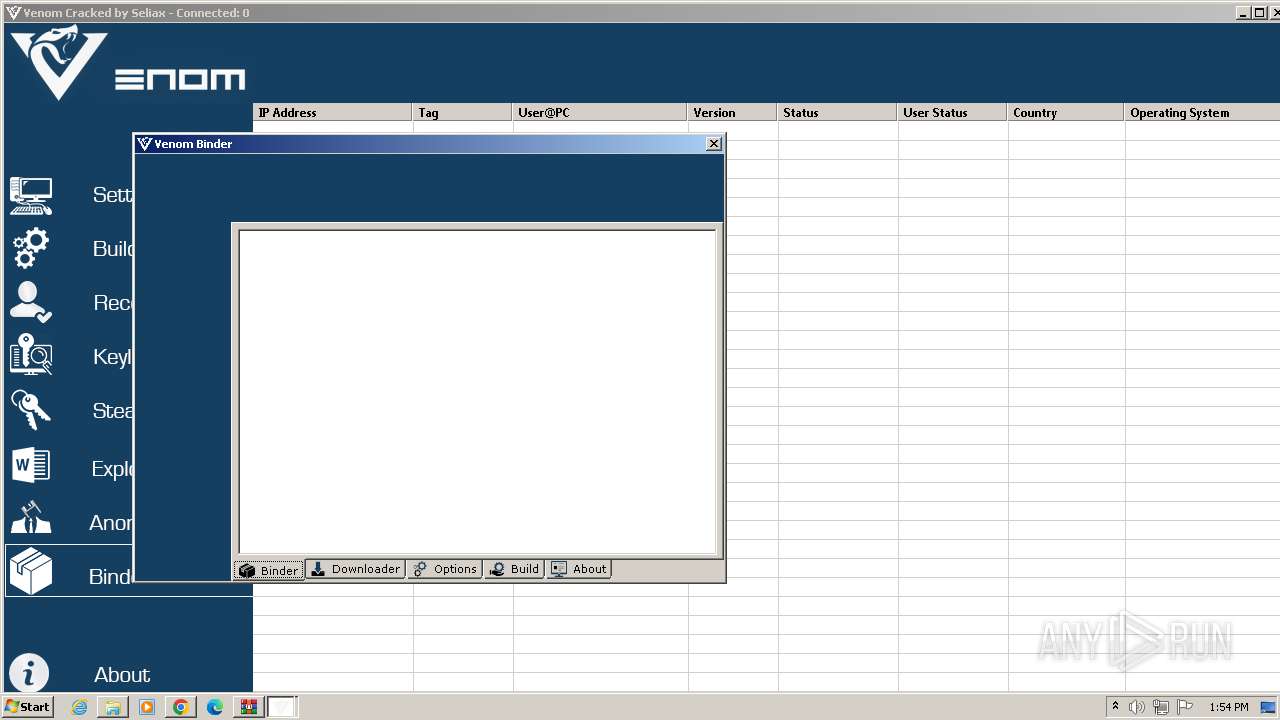
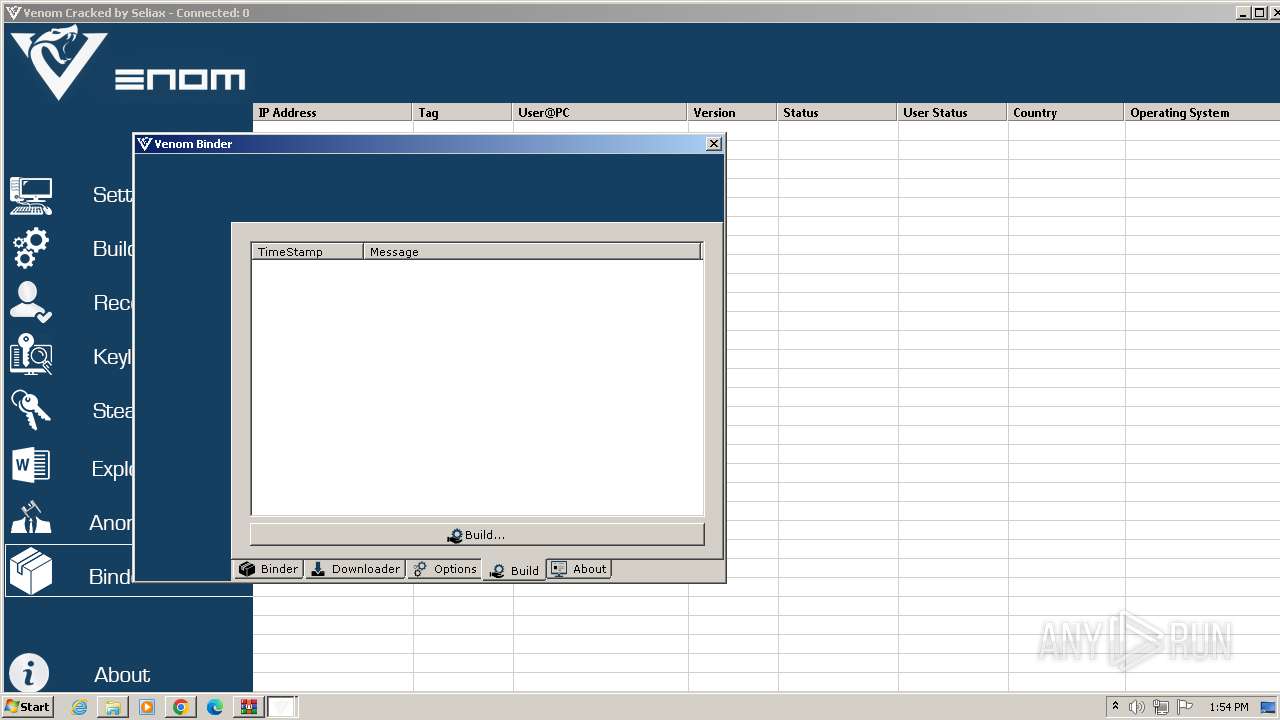
- Venom Binder.exe (PID: 3572)
- Venom Cracked.exe (PID: 3360)
- csc.exe (PID: 1796)
- cvtres.exe (PID: 1792)
- csc.exe (PID: 2876)
- cvtres.exe (PID: 2880)
Reads the computer name
- Venom Cracked.exe (PID: 2380)
- Venom Binder.exe (PID: 3572)
- Venom Cracked.exe (PID: 3360)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1588)
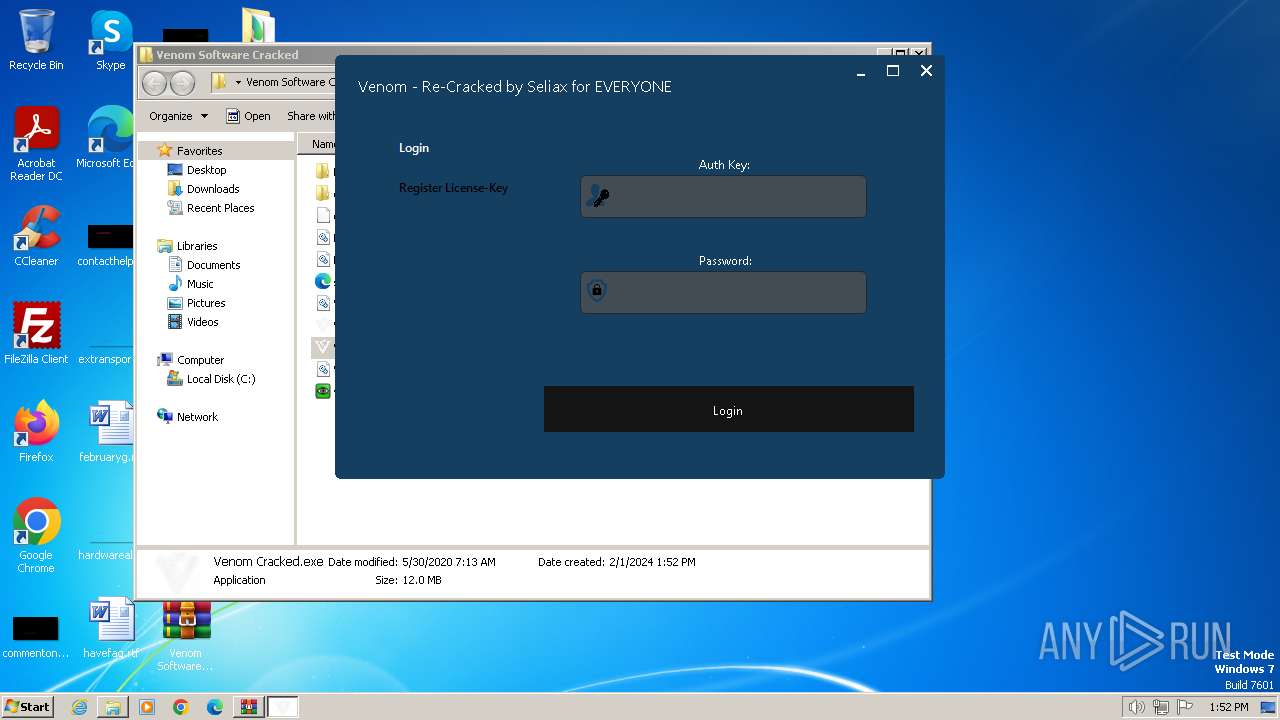
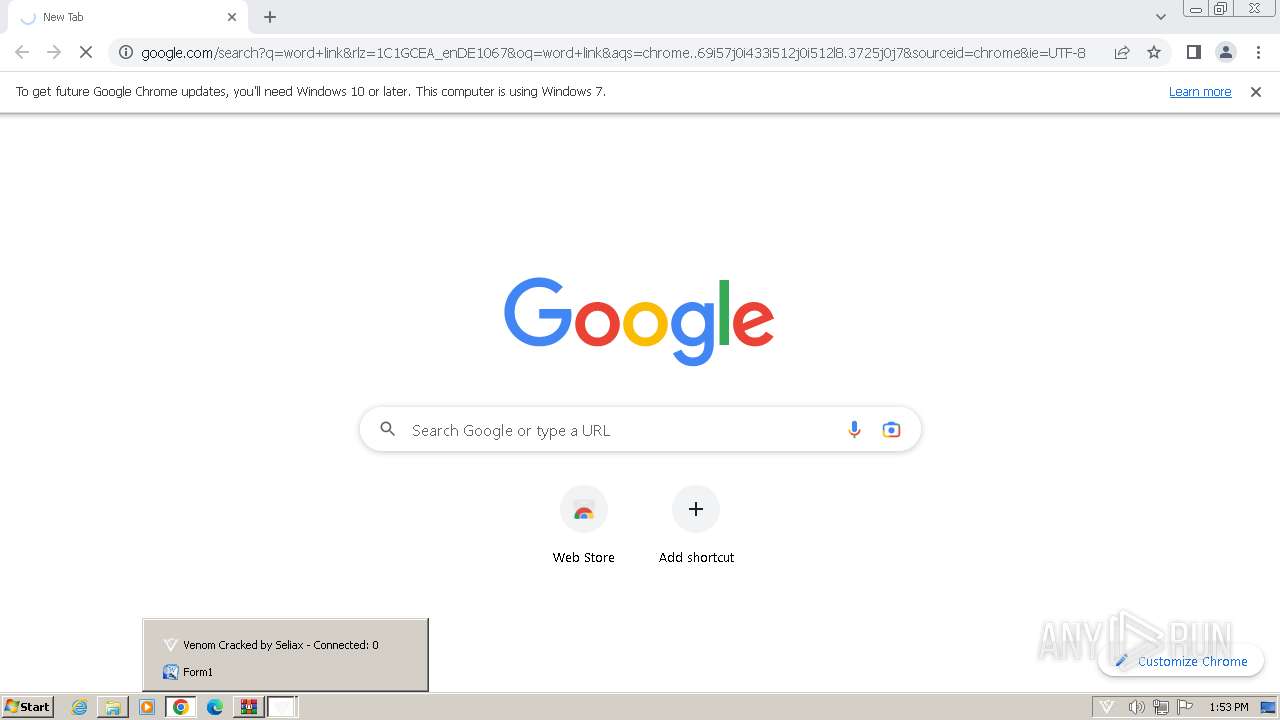
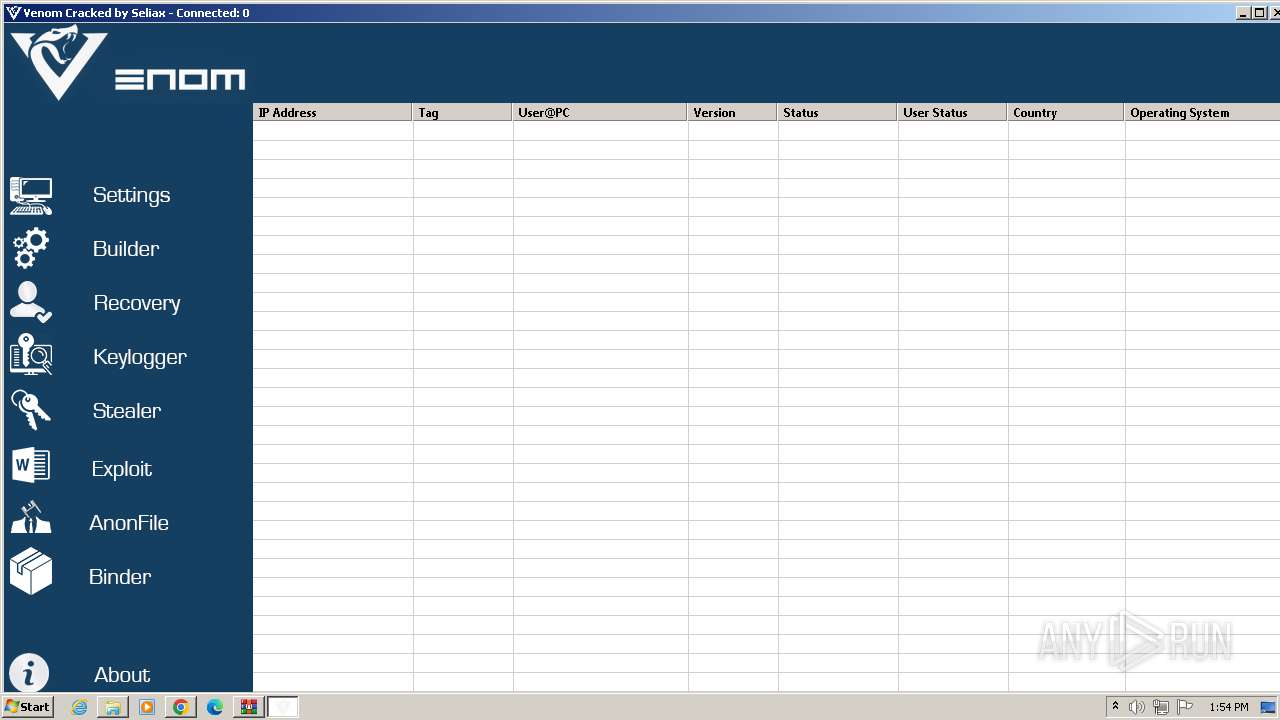
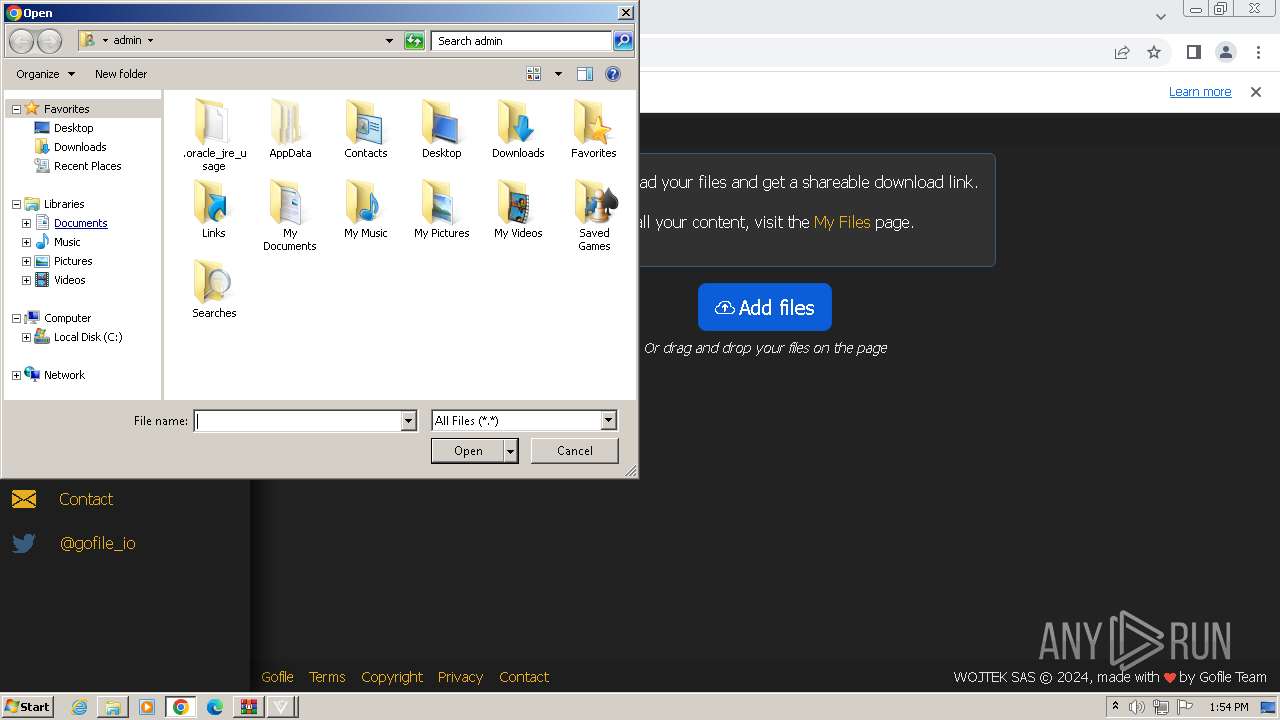
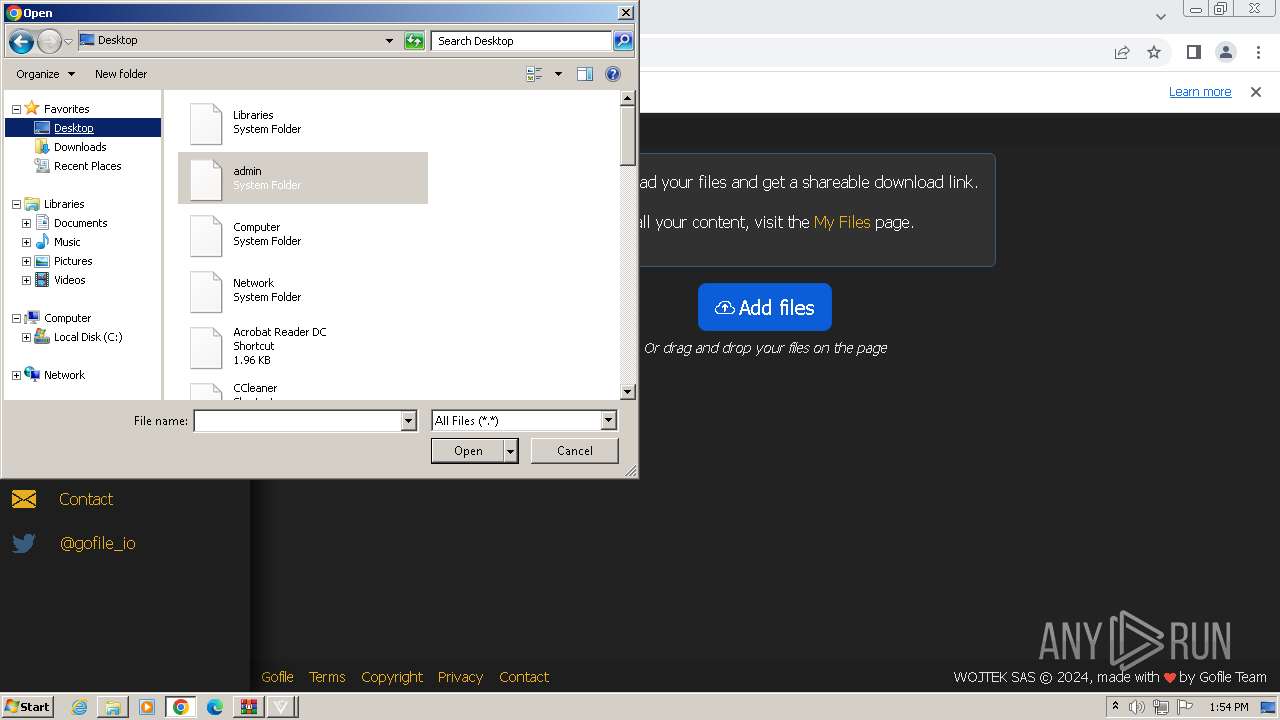
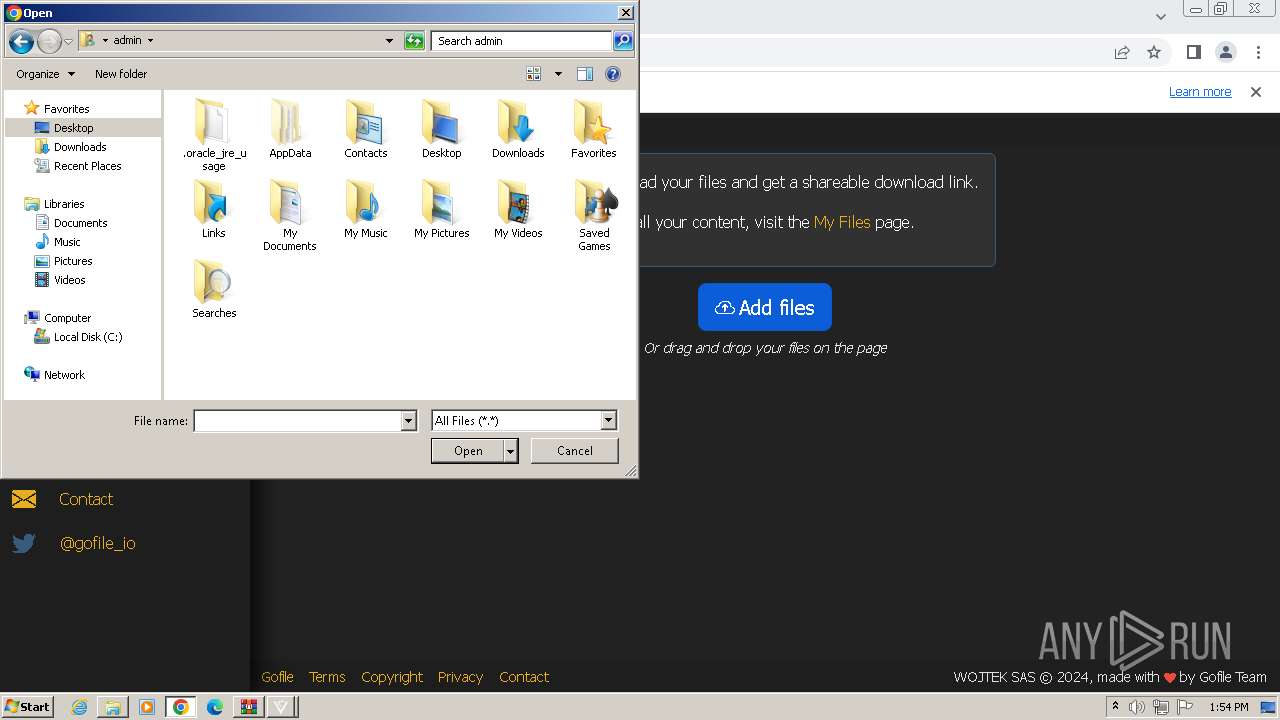
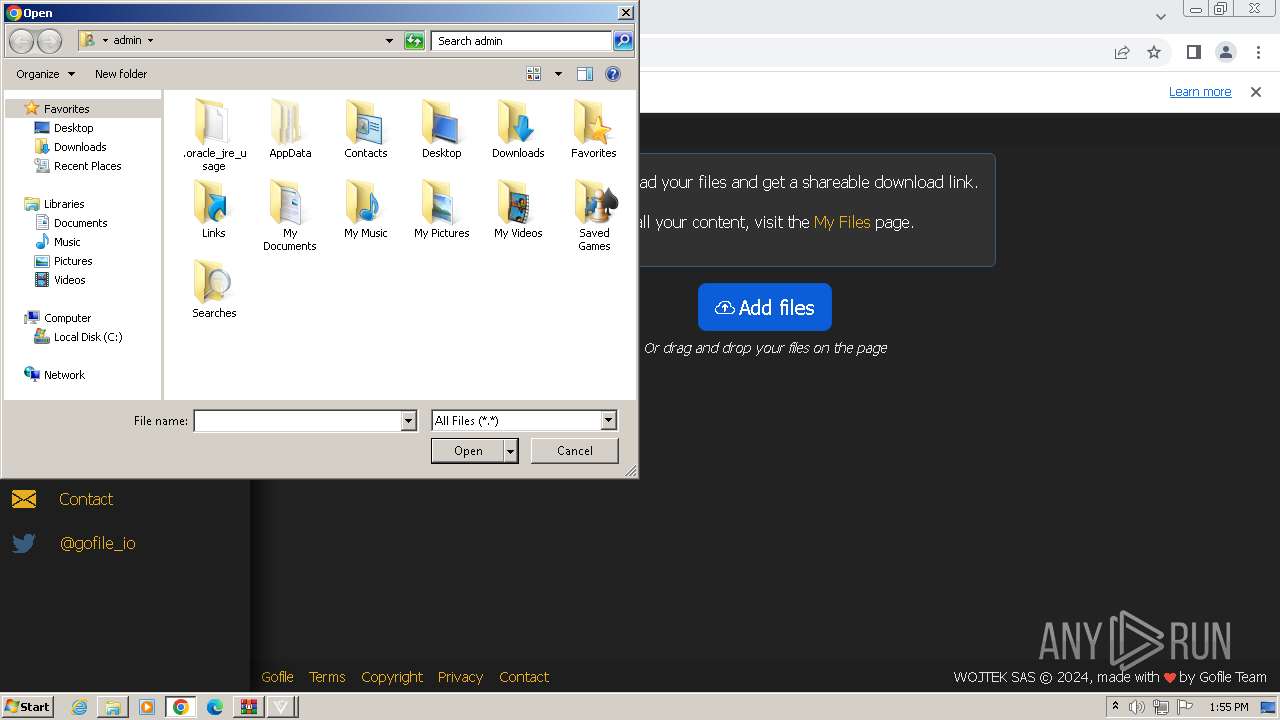
Manual execution by a user
- Venom Cracked.exe (PID: 2380)
- Venom Binder.exe (PID: 3572)
- Venom Cracked.exe (PID: 3360)
- chrome.exe (PID: 4056)
Reads the machine GUID from the registry
- Venom Cracked.exe (PID: 2380)
- Venom Binder.exe (PID: 3572)
- cvtres.exe (PID: 1792)
- csc.exe (PID: 2876)
- Venom Cracked.exe (PID: 3360)
- csc.exe (PID: 1796)
- cvtres.exe (PID: 2880)
Create files in a temporary directory
- cvtres.exe (PID: 1792)
- cvtres.exe (PID: 2880)
Application launched itself
- chrome.exe (PID: 4056)
Drops the executable file immediately after the start
- chrome.exe (PID: 4056)
Reads Microsoft Office registry keys
- chrome.exe (PID: 3356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
75
Monitored processes
29
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3308 --field-trial-handle=1160,i,16927777975484403103,1462306562715352291,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3408 --field-trial-handle=1160,i,16927777975484403103,1462306562715352291,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=2368 --field-trial-handle=1160,i,16927777975484403103,1462306562715352291,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Venom Software Cracked.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1792 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES79AF.tmp" "c:\Users\admin\Desktop\Venom Software Cracked\CSCB80A745375DB44319B6439D41692803.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 1796 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\Desktop\Venom Software Cracked\temp\k3x03uet.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | Venom Cracked.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1304 --field-trial-handle=1160,i,16927777975484403103,1462306562715352291,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=1944 --field-trial-handle=1160,i,16927777975484403103,1462306562715352291,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1344 --field-trial-handle=1160,i,16927777975484403103,1462306562715352291,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=4028 --field-trial-handle=1160,i,16927777975484403103,1462306562715352291,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
12 857
Read events
12 577
Write events
273
Delete events
7
Modification events
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
10
Suspicious files
144
Text files
27
Unknown types
0
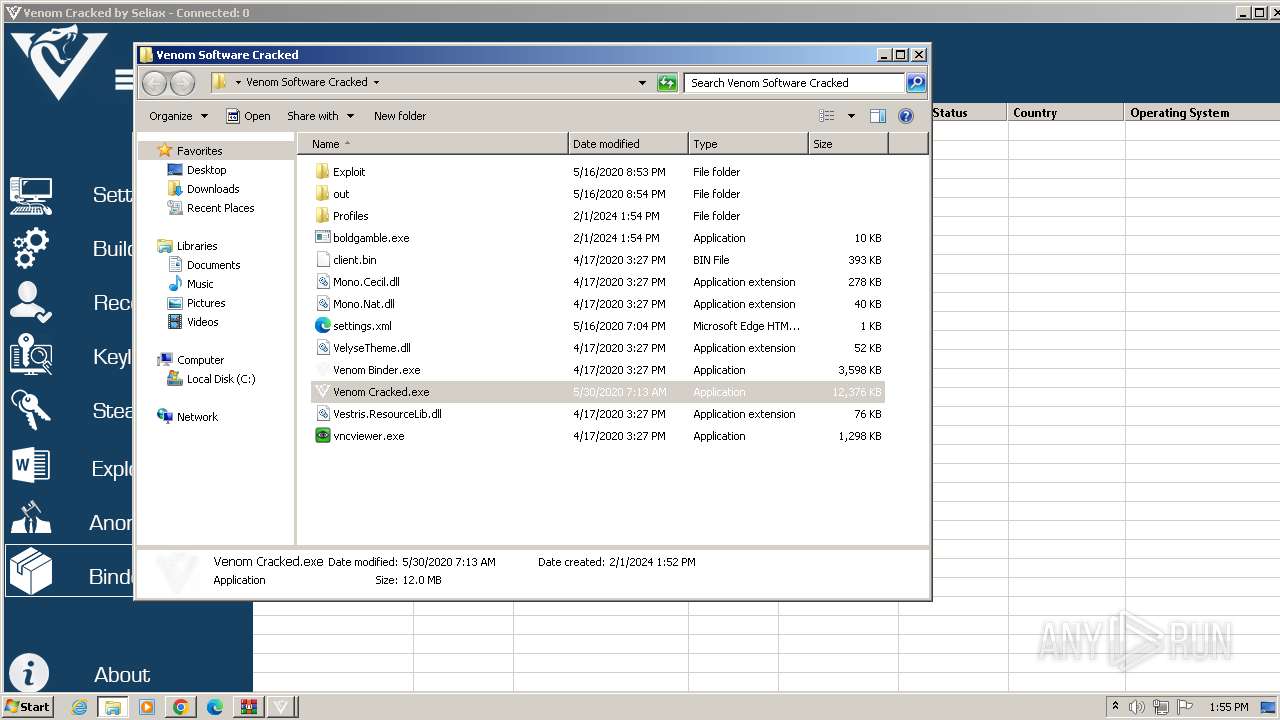
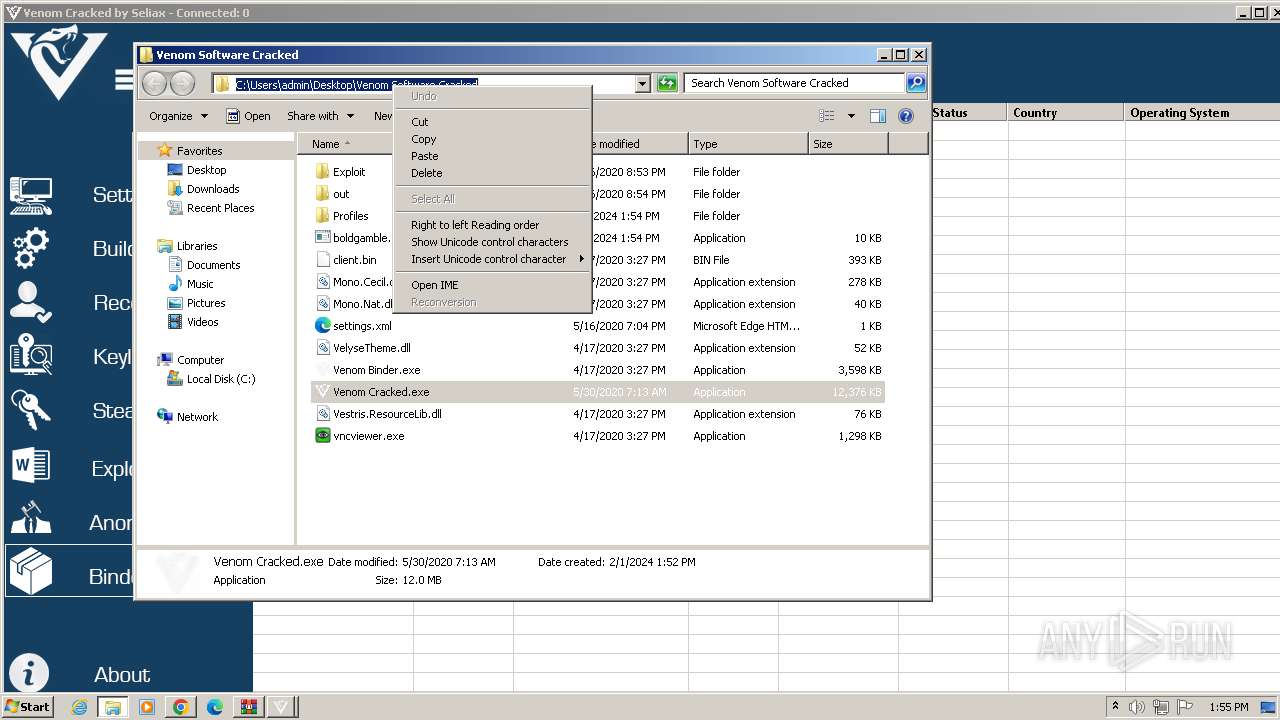
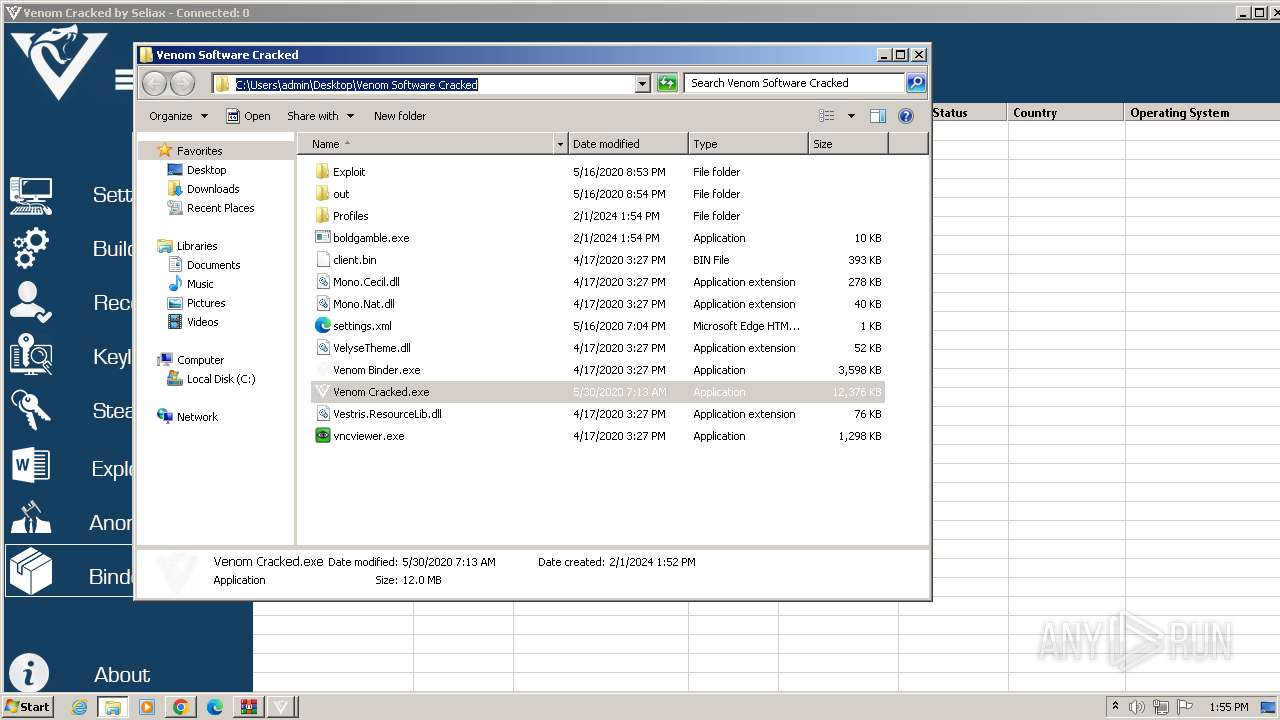
Dropped files
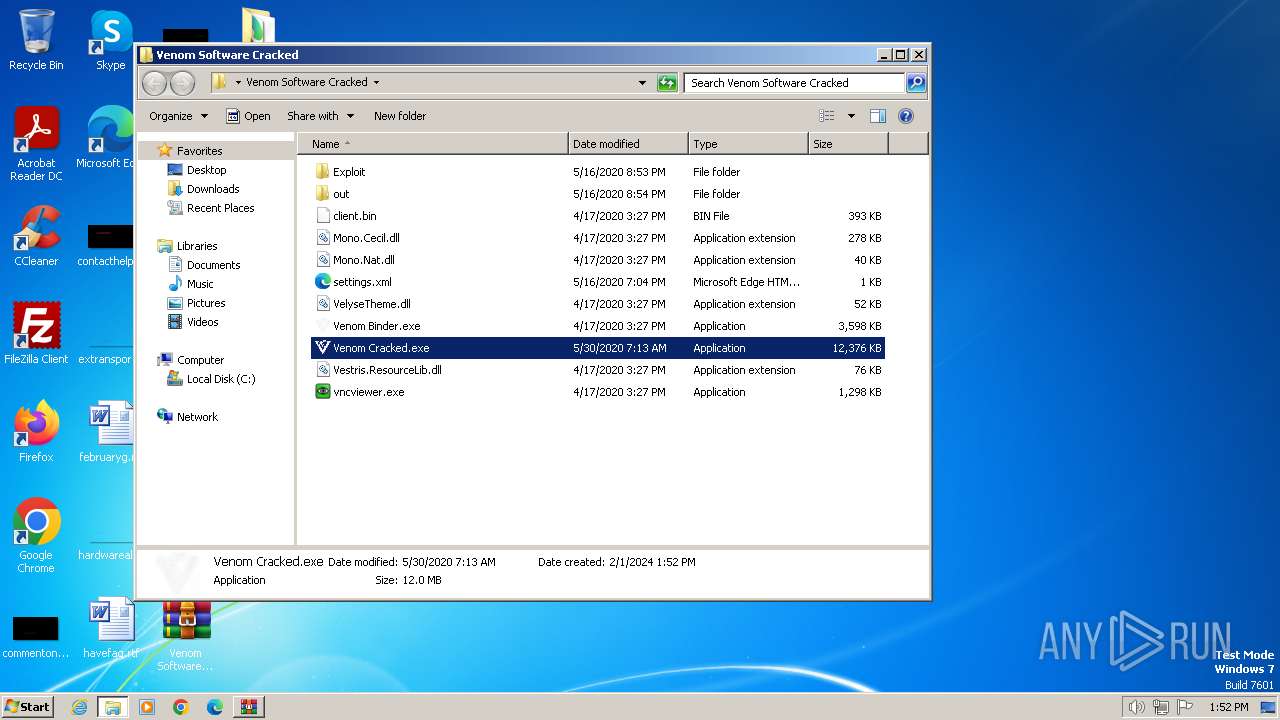
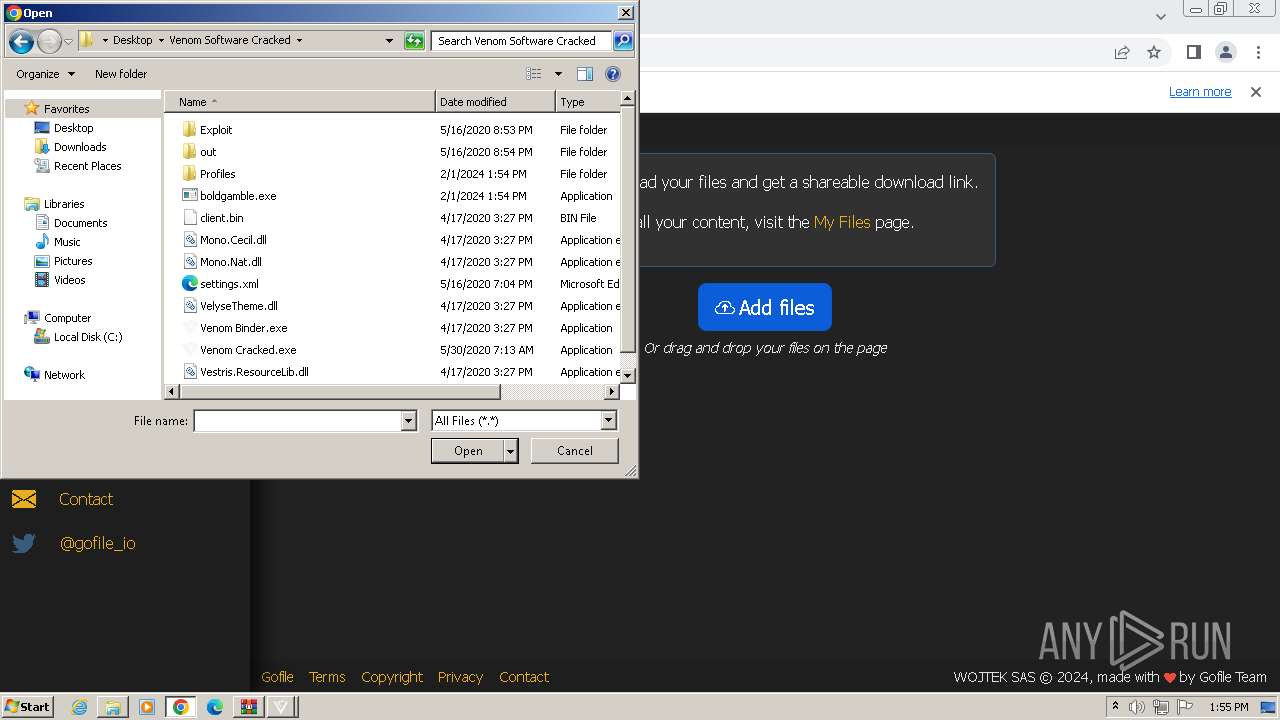
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF16fef6.TMP | — | |
MD5:— | SHA256:— | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
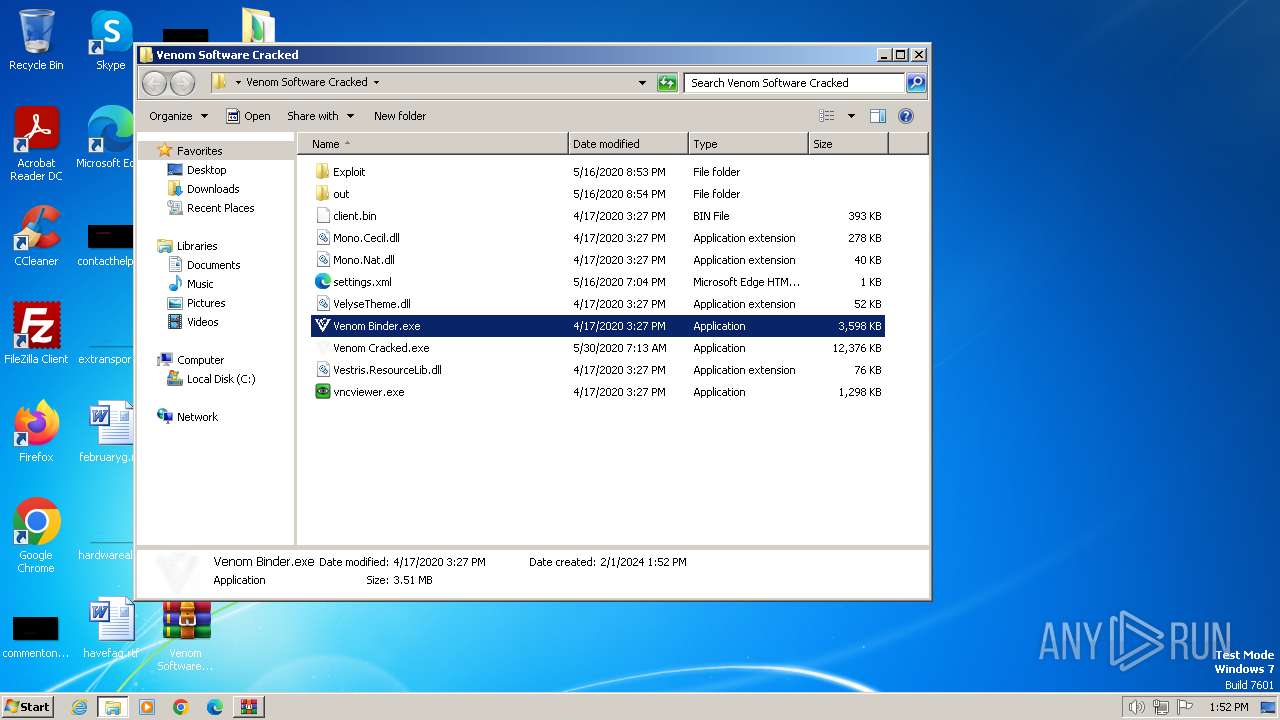
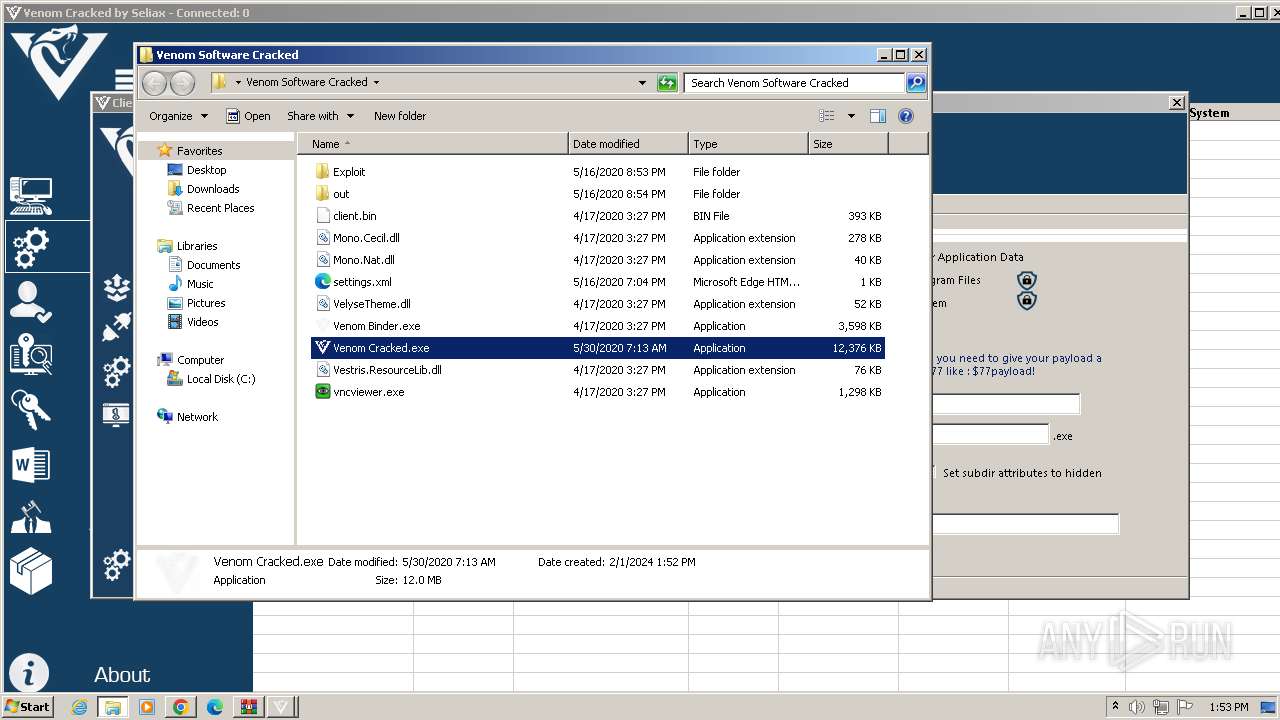
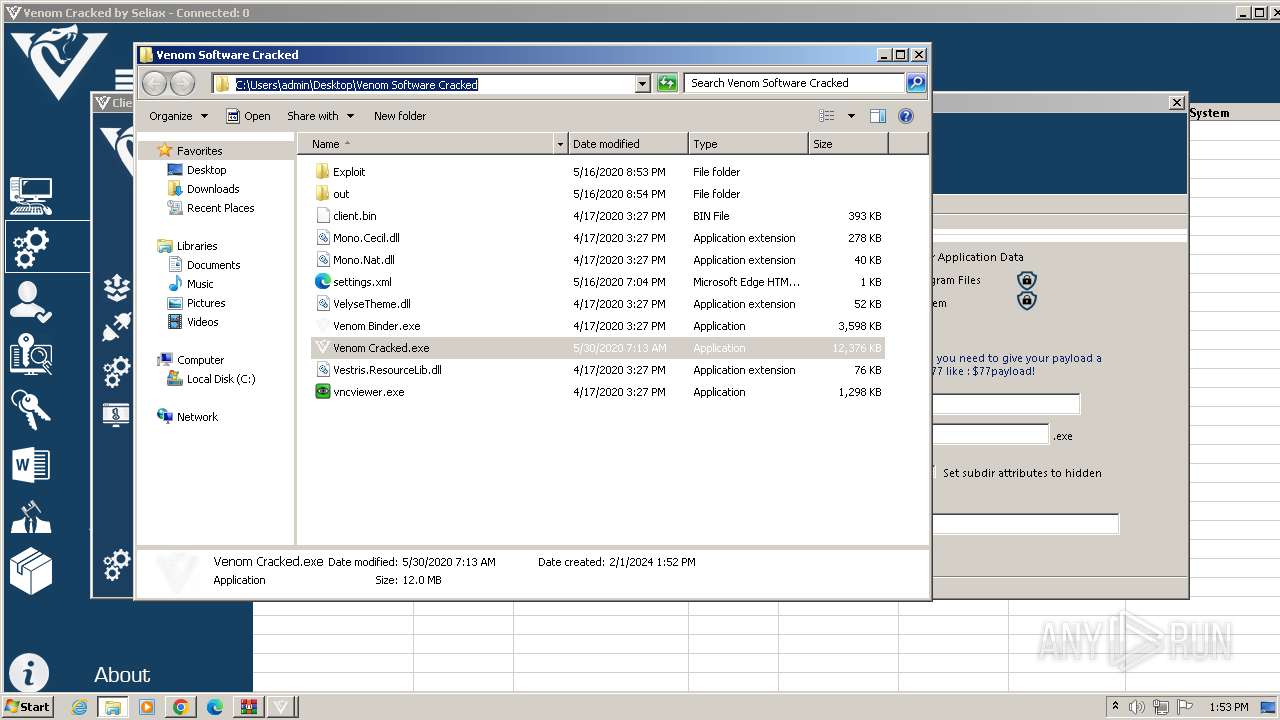
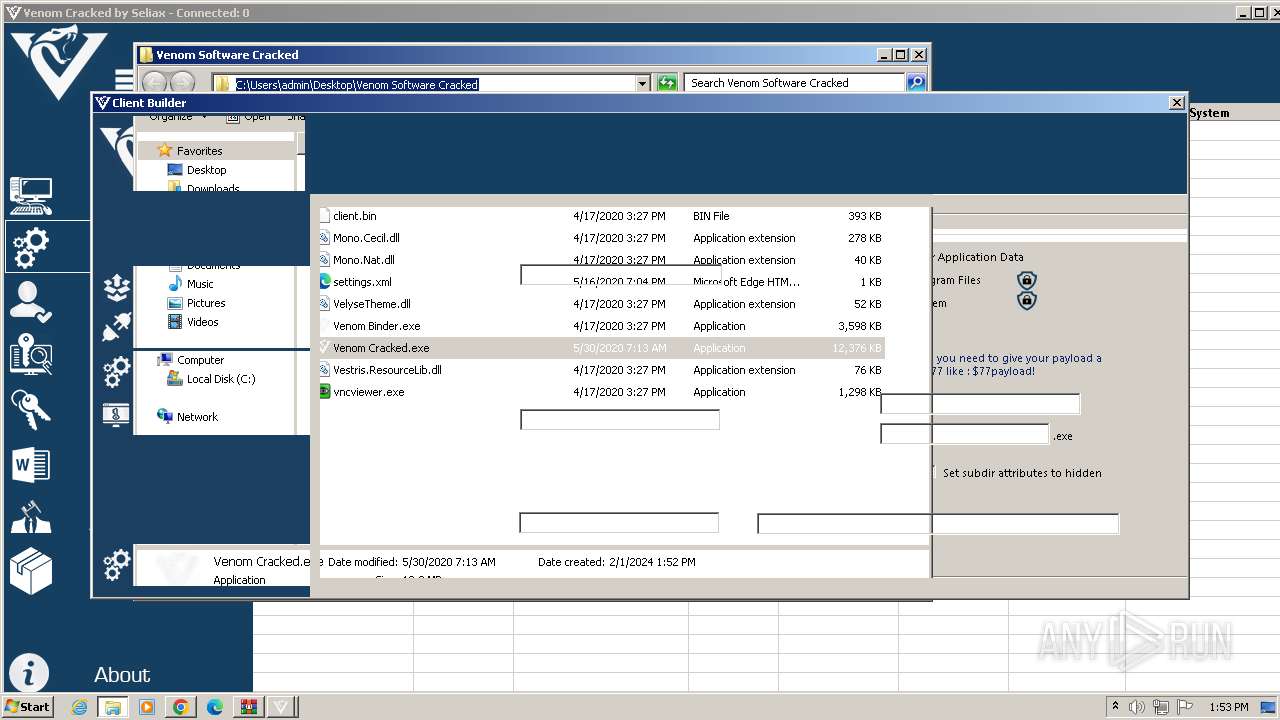
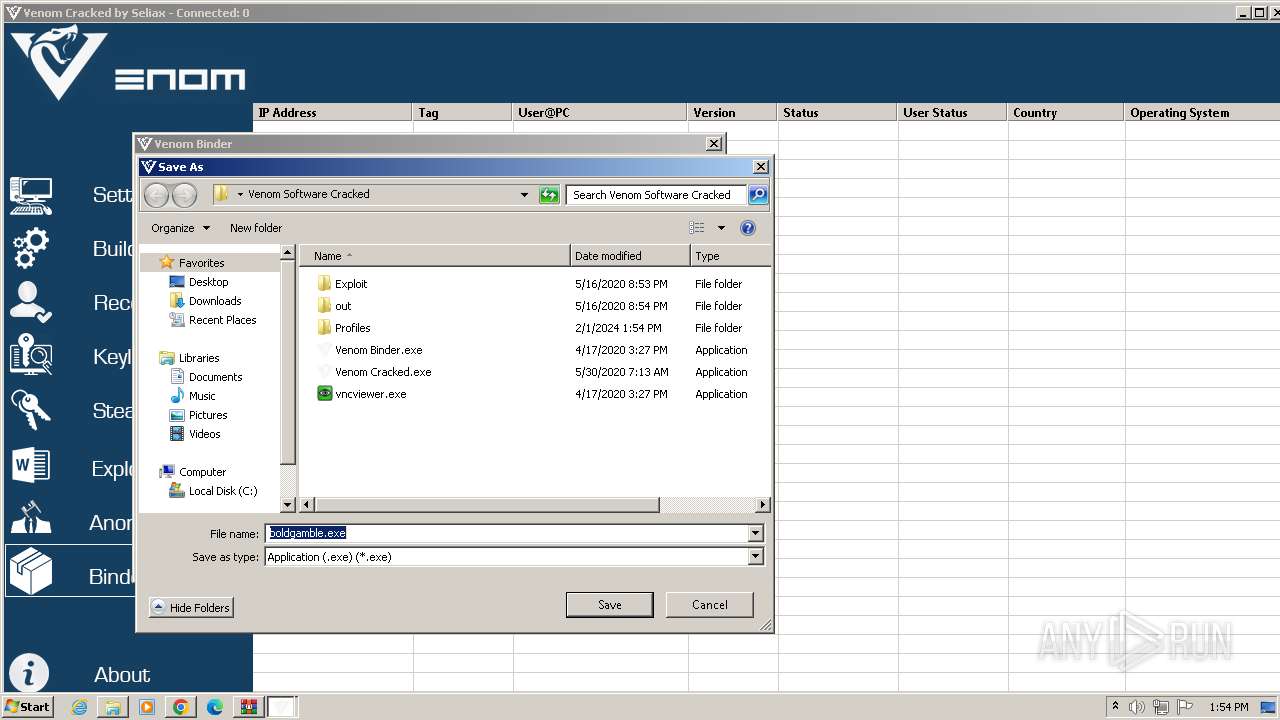
| 1588 | WinRAR.exe | C:\Users\admin\Desktop\Venom Software Cracked\client.bin | executable | |
MD5:0CF92F1BF0544D71E5E9009FEF068A82 | SHA256:7128A2488B2D0084465CA1602A844EAFB191DE938FC70098D86CB65D17734778 | |||
| 1588 | WinRAR.exe | C:\Users\admin\Desktop\Venom Software Cracked\Mono.Cecil.dll | executable | |
MD5:8DF4D6B5DC1629FCEFCDC20210A88EAC | SHA256:3E4288B32006FE8499B43A7F605BB7337931847A0AA79A33217A1D6D1A6C397E | |||
| 1588 | WinRAR.exe | C:\Users\admin\Desktop\Venom Software Cracked\VelyseTheme.dll | executable | |
MD5:52BFCE7E8DC04712CD2091C12F126F77 | SHA256:B332DAAC3B130051E8D2A5FD325D6D094CA1C9A602B45667855341F4CB9100AE | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1588 | WinRAR.exe | C:\Users\admin\Desktop\Venom Software Cracked\Mono.Nat.dll | executable | |
MD5:BF929442B12D4B5F9906B29834BF7DB1 | SHA256:B33435AC7CDEFCF7C2ADF96738C762A95414EB7A4967EF6B88DCDA14D58BFEE0 | |||
| 1588 | WinRAR.exe | C:\Users\admin\Desktop\Venom Software Cracked\vncviewer.exe | executable | |
MD5:311DE77BCDF9808908F628ECD26A098B | SHA256:DAC7F8191D05A8F2AB0F05C975BAE826A2BB4C10BD6B40B0B1BE0A260F5CD558 | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 4056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
41
DNS requests
34
Threats
16
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
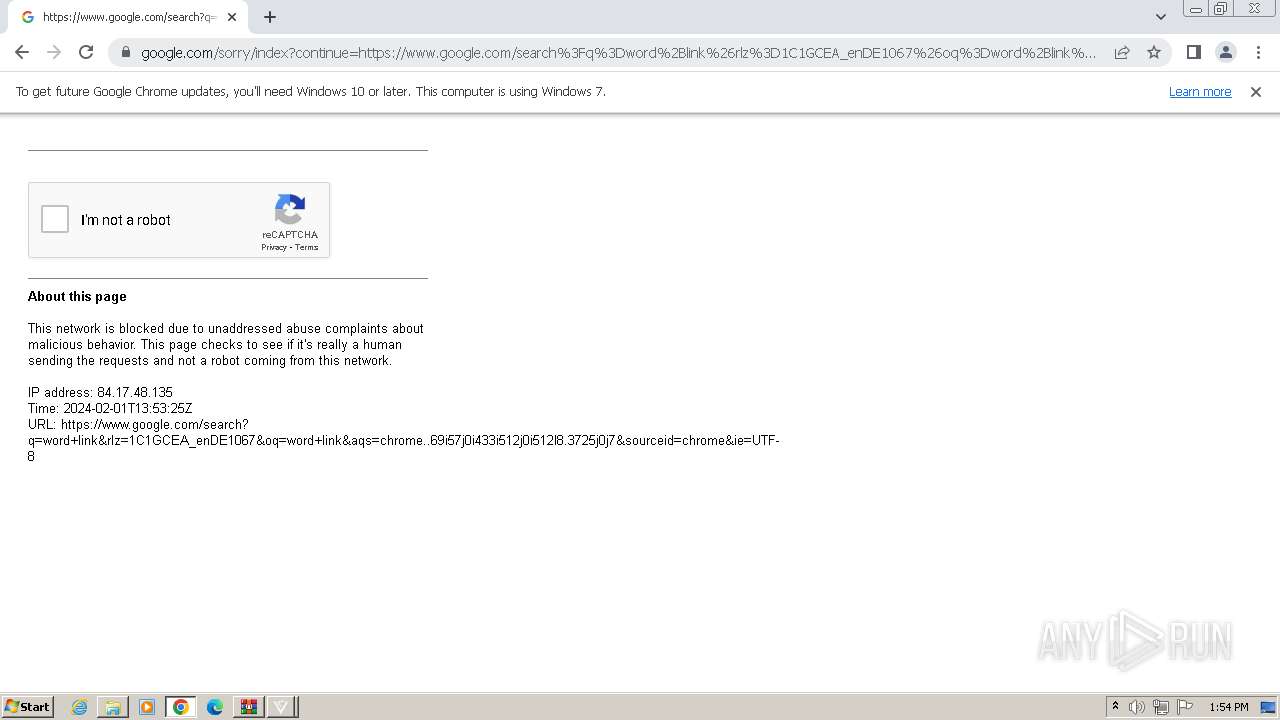
2380 | Venom Cracked.exe | 91.134.207.16:9008 | — | OVH SAS | FR | unknown |
3360 | Venom Cracked.exe | 239.255.255.250:1900 | — | — | — | unknown |
3360 | Venom Cracked.exe | 192.168.100.2:5351 | — | — | — | whitelisted |
2132 | chrome.exe | 142.250.186.163:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
4056 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2132 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
2132 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
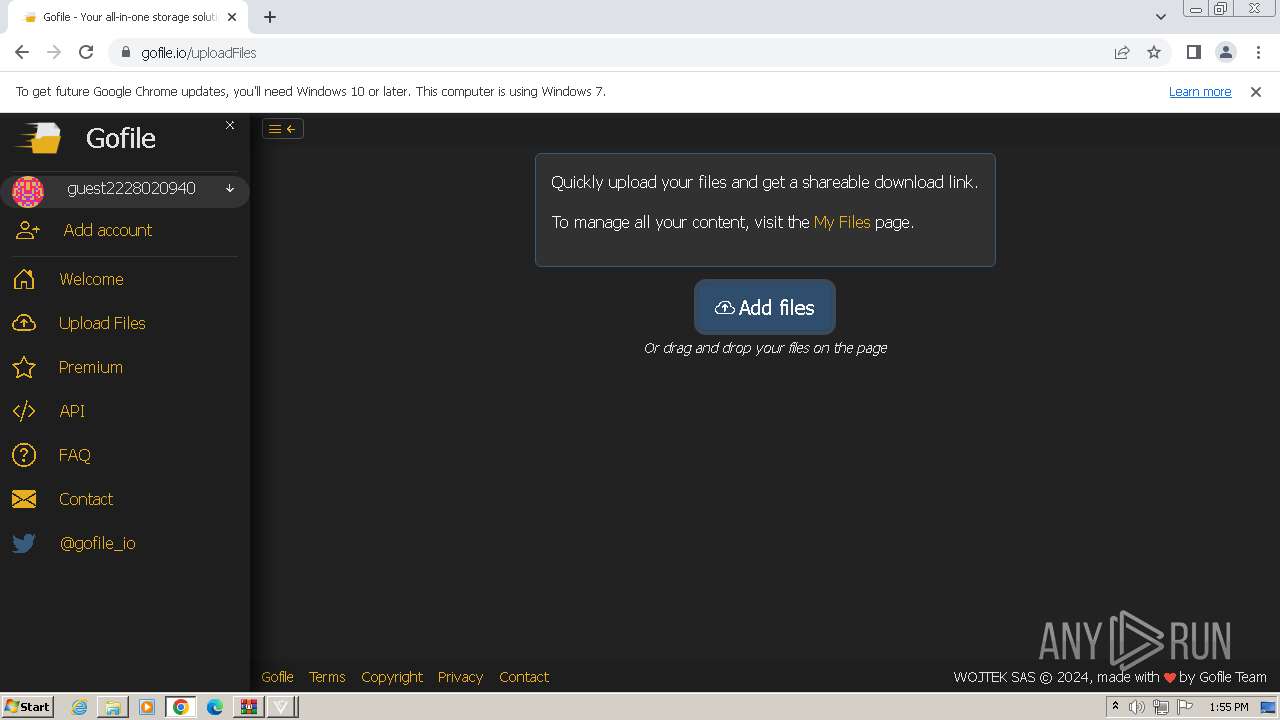
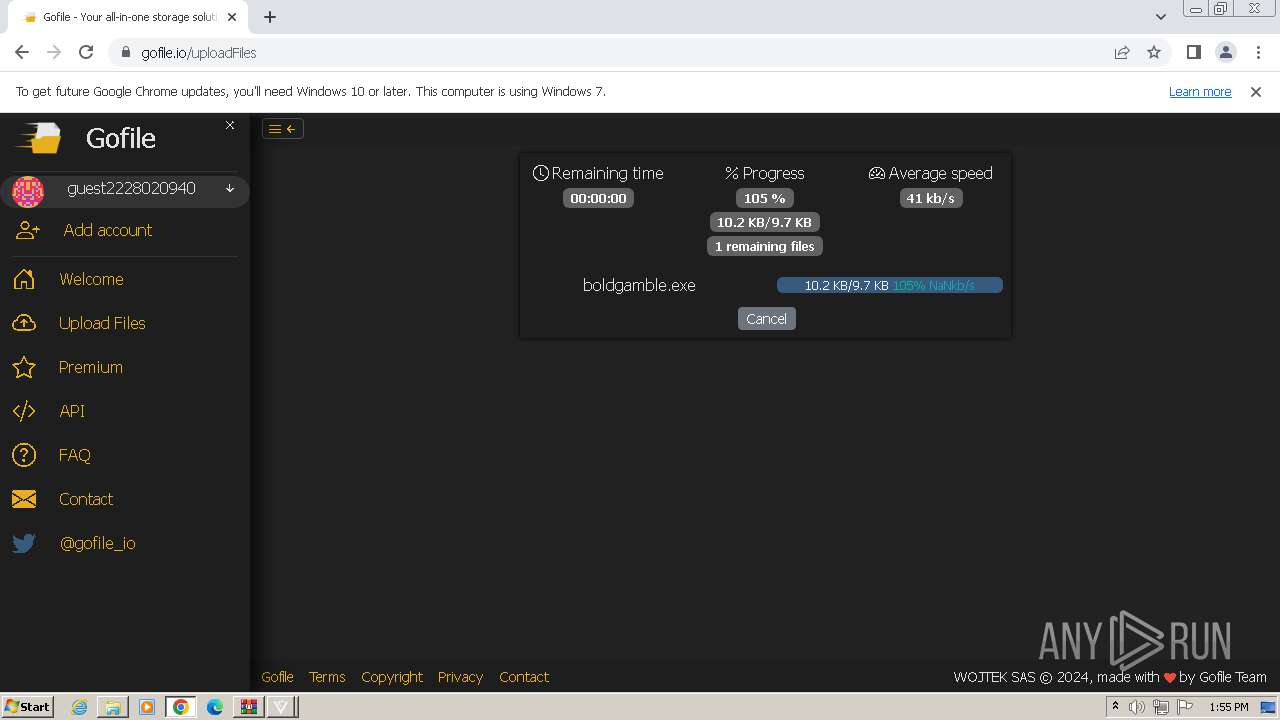
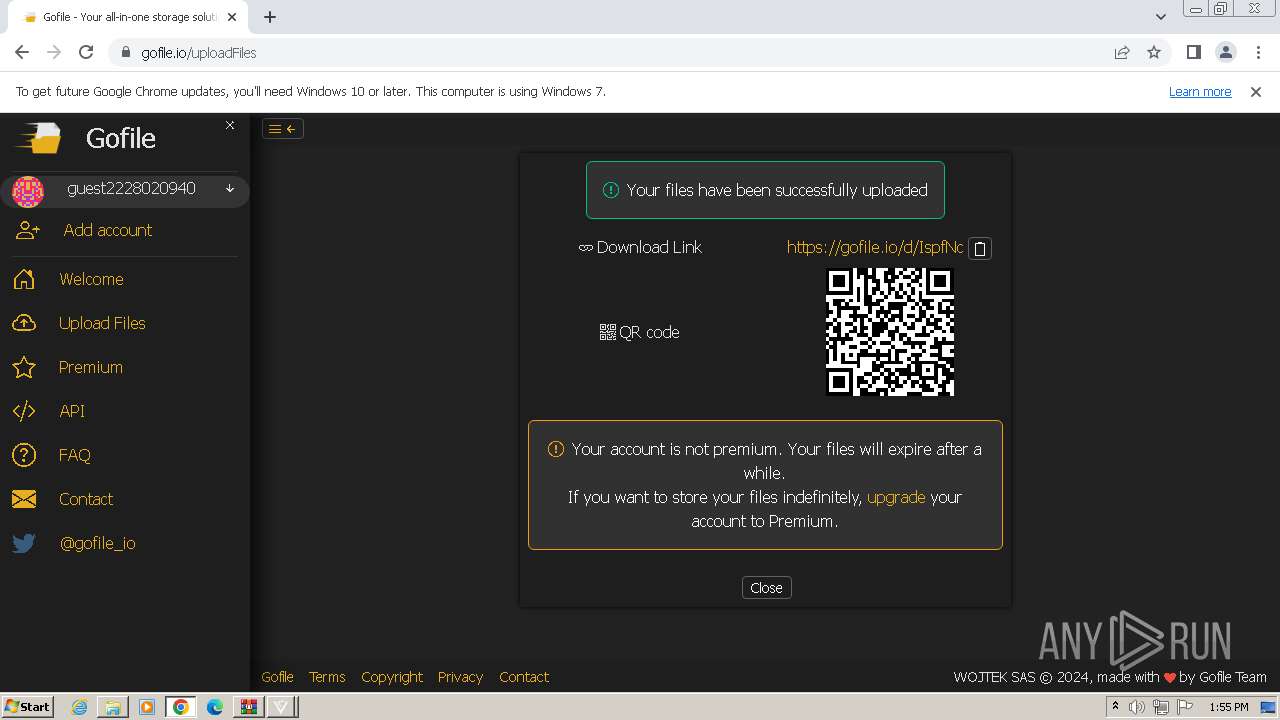
Threats
PID | Process | Class | Message |
|---|---|---|---|
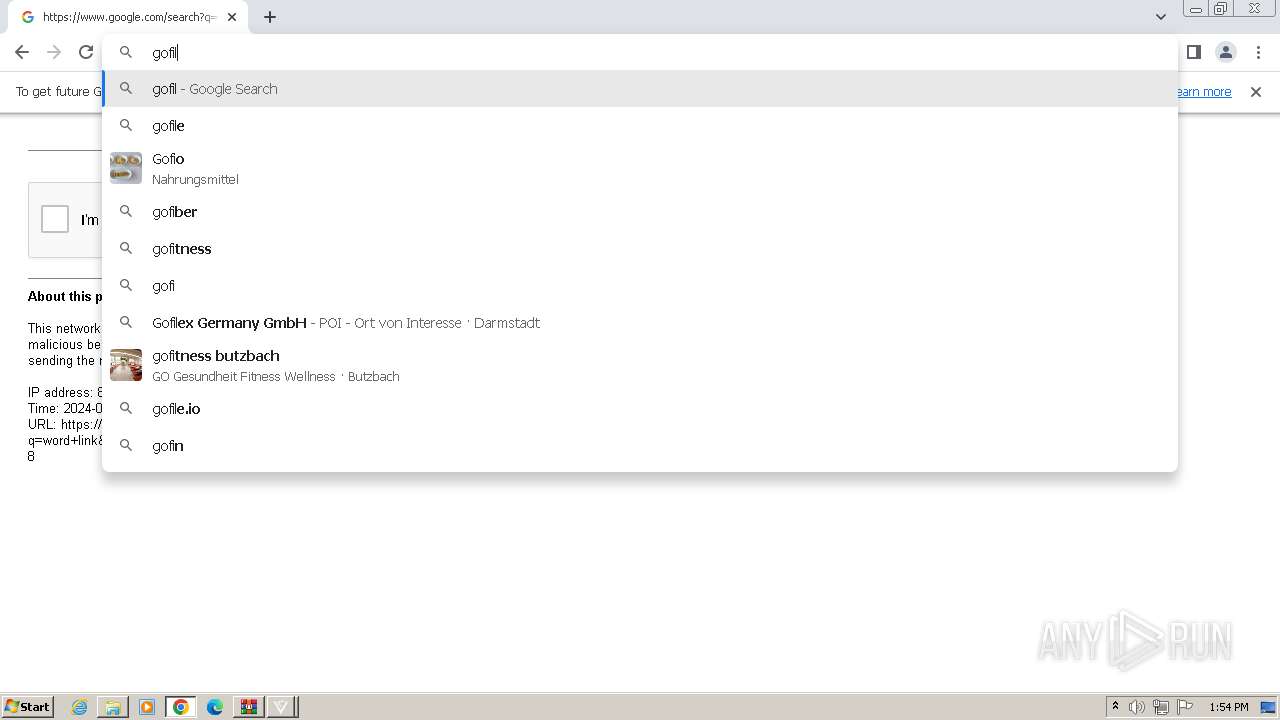
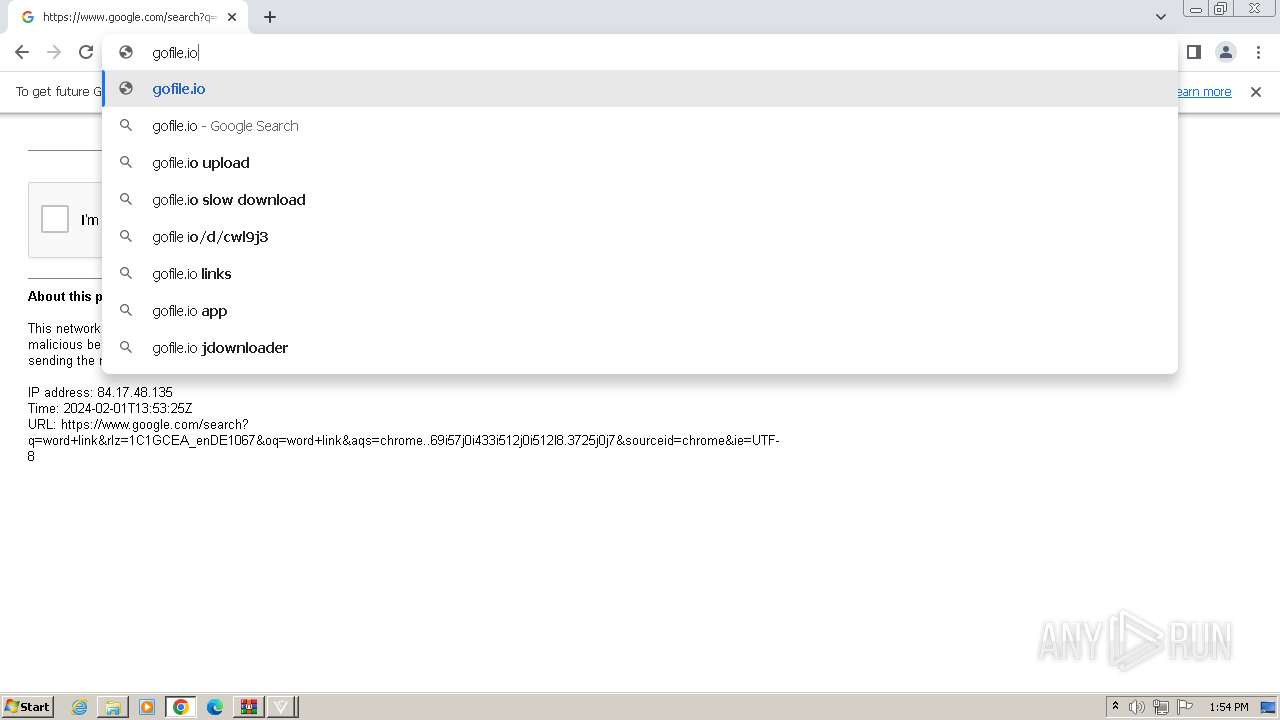
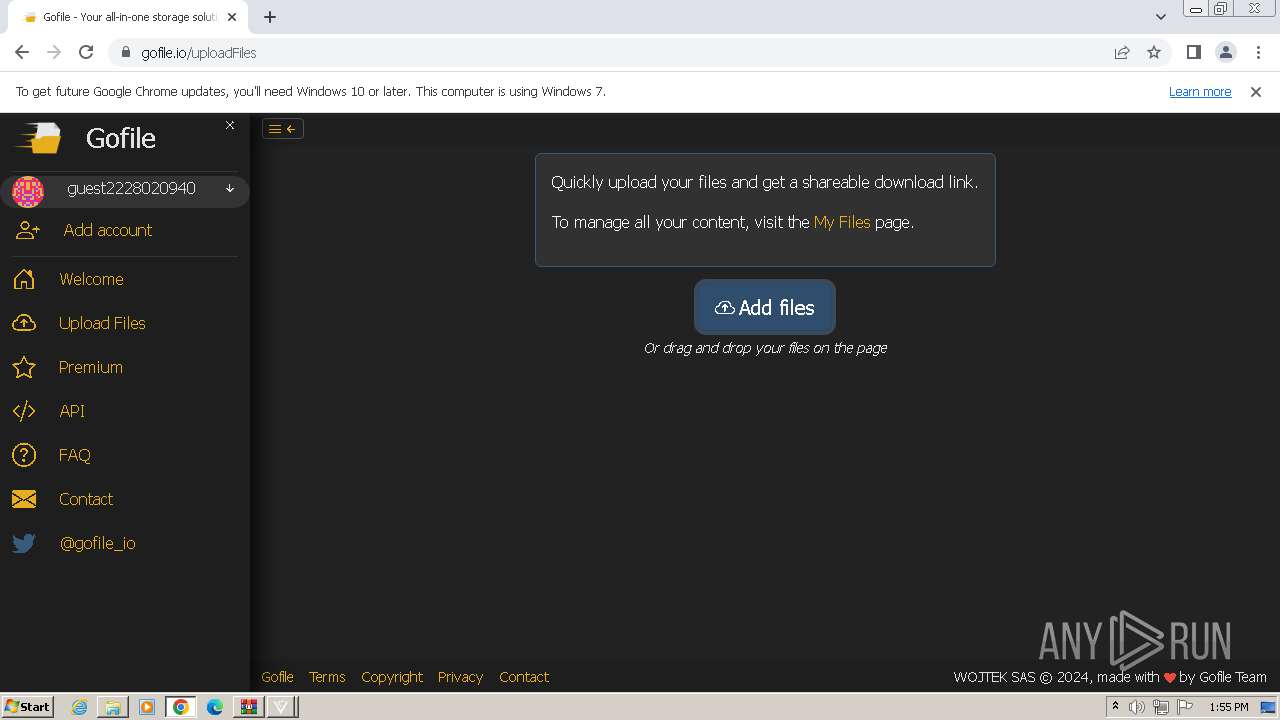
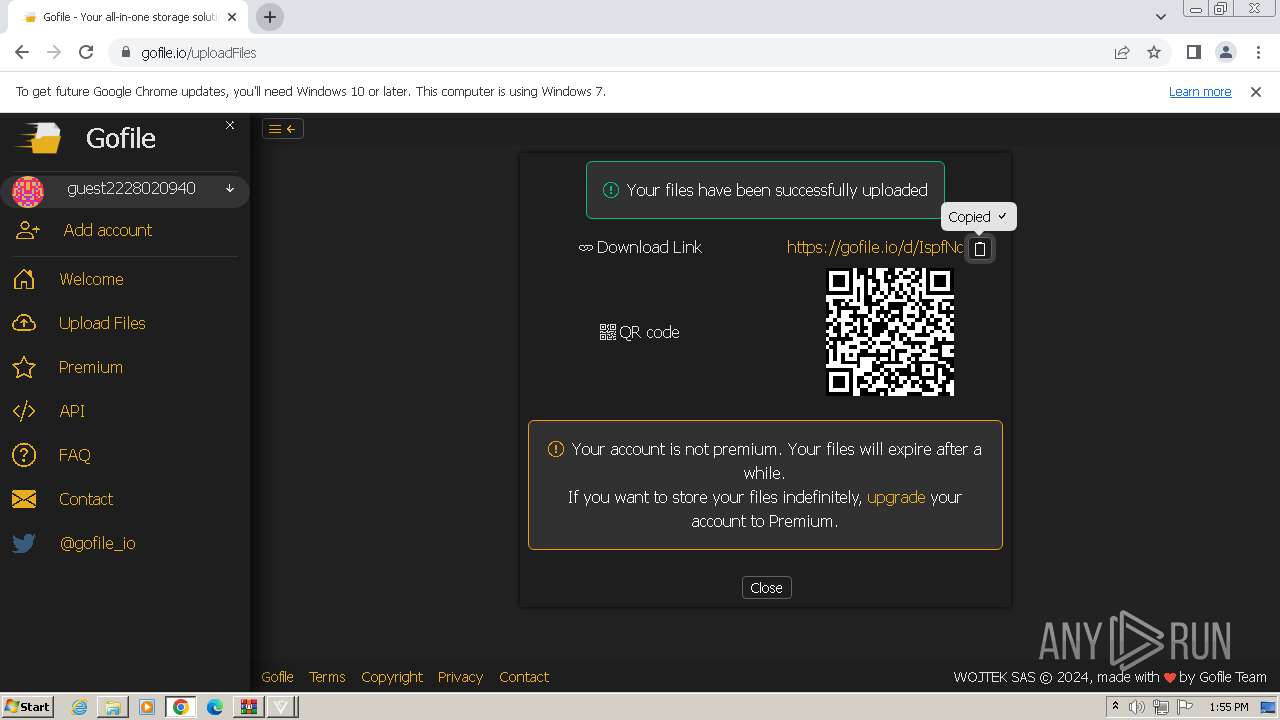
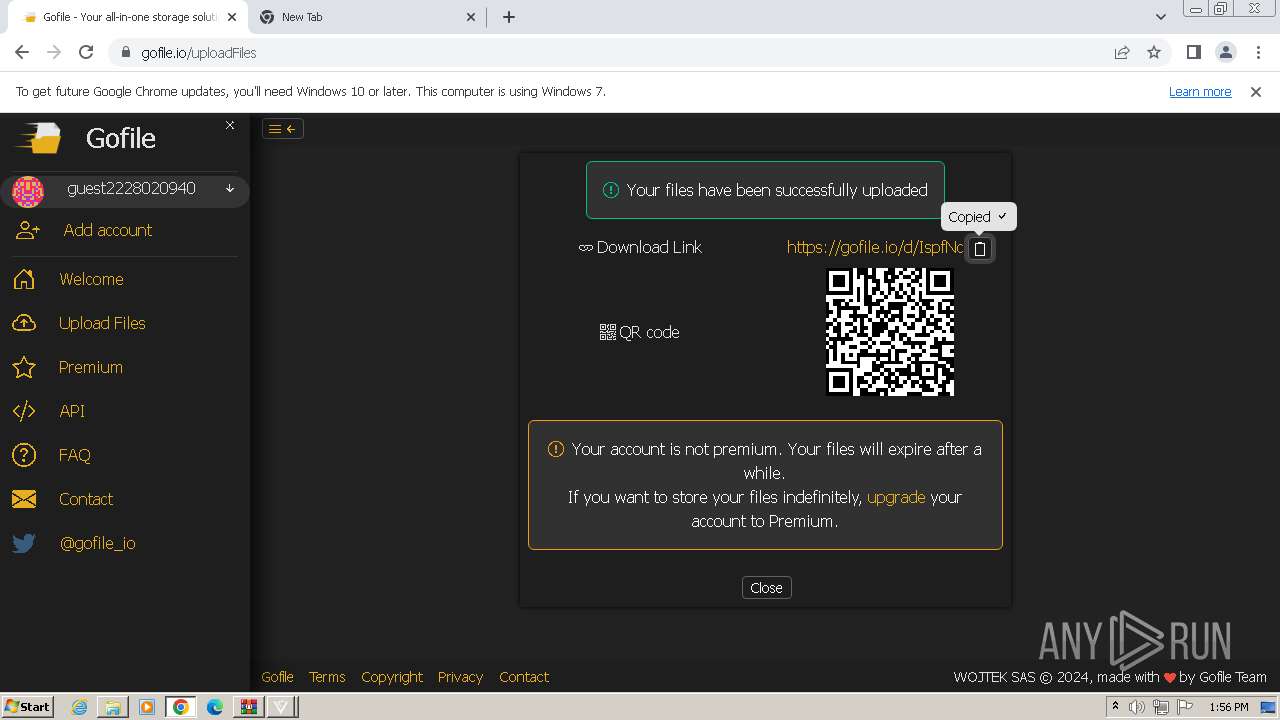
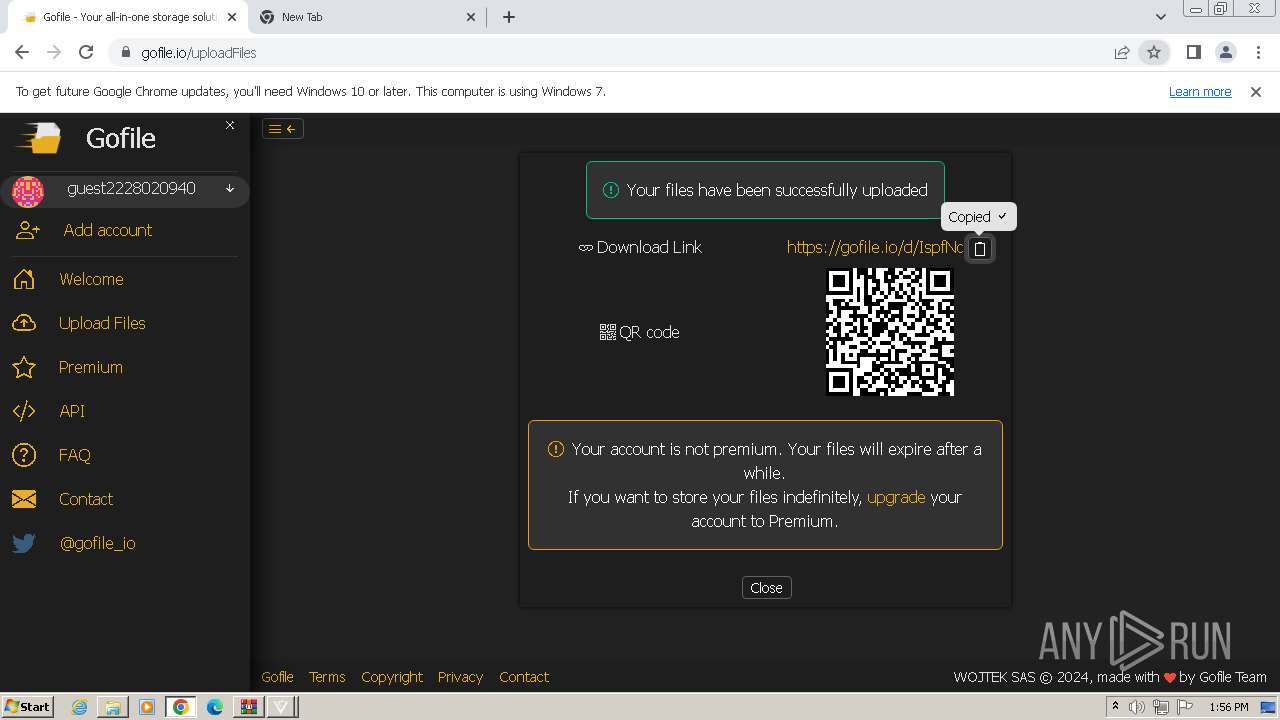
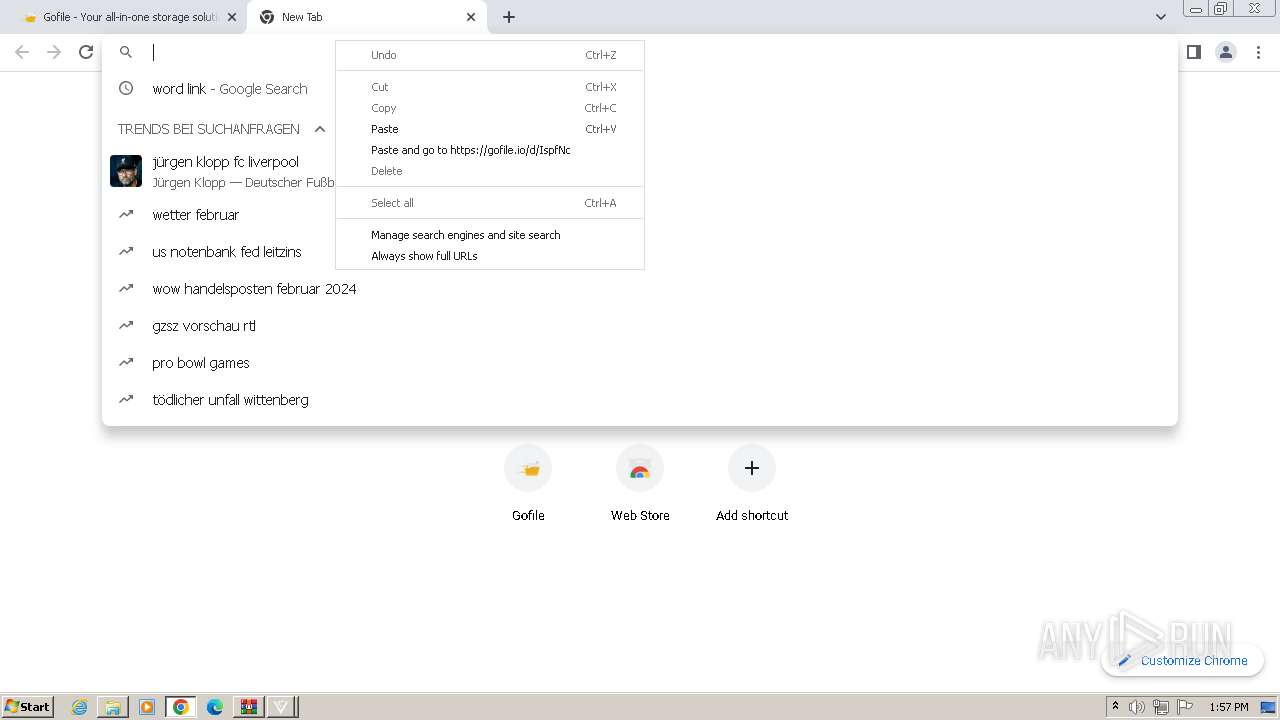
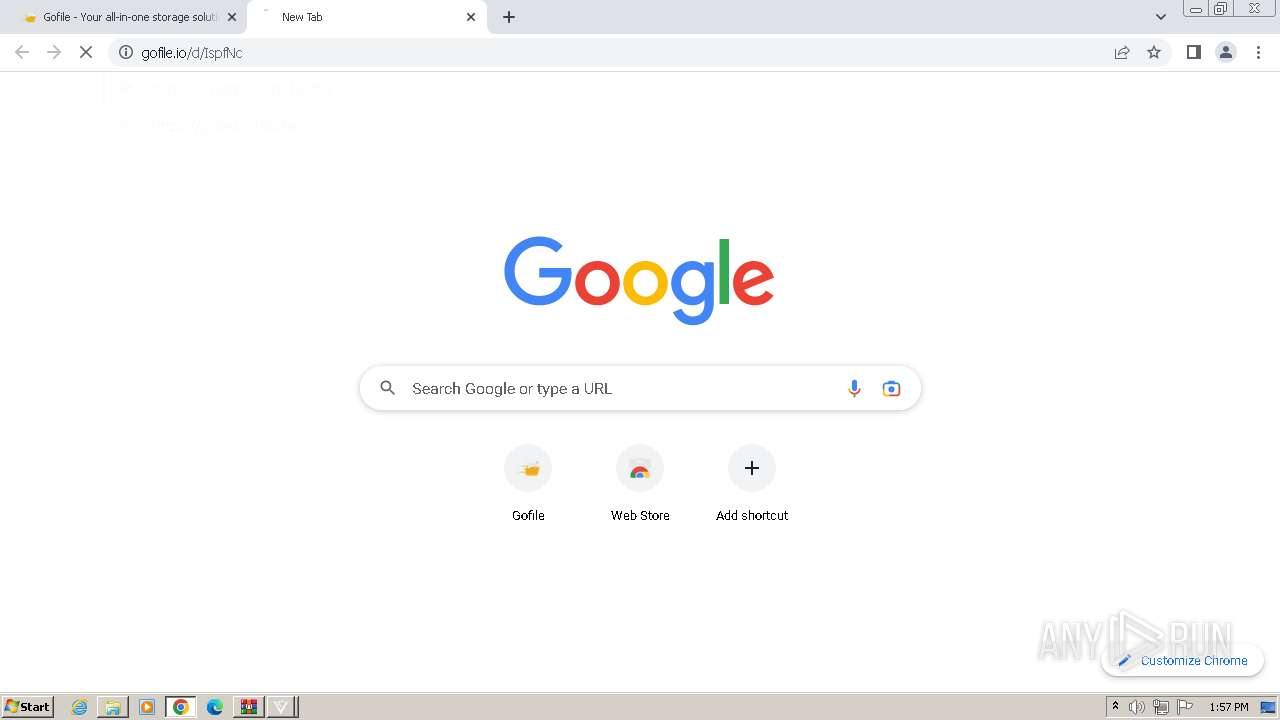
2132 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2132 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2132 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
2132 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
2132 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2132 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2132 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
2132 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2132 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2132 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |