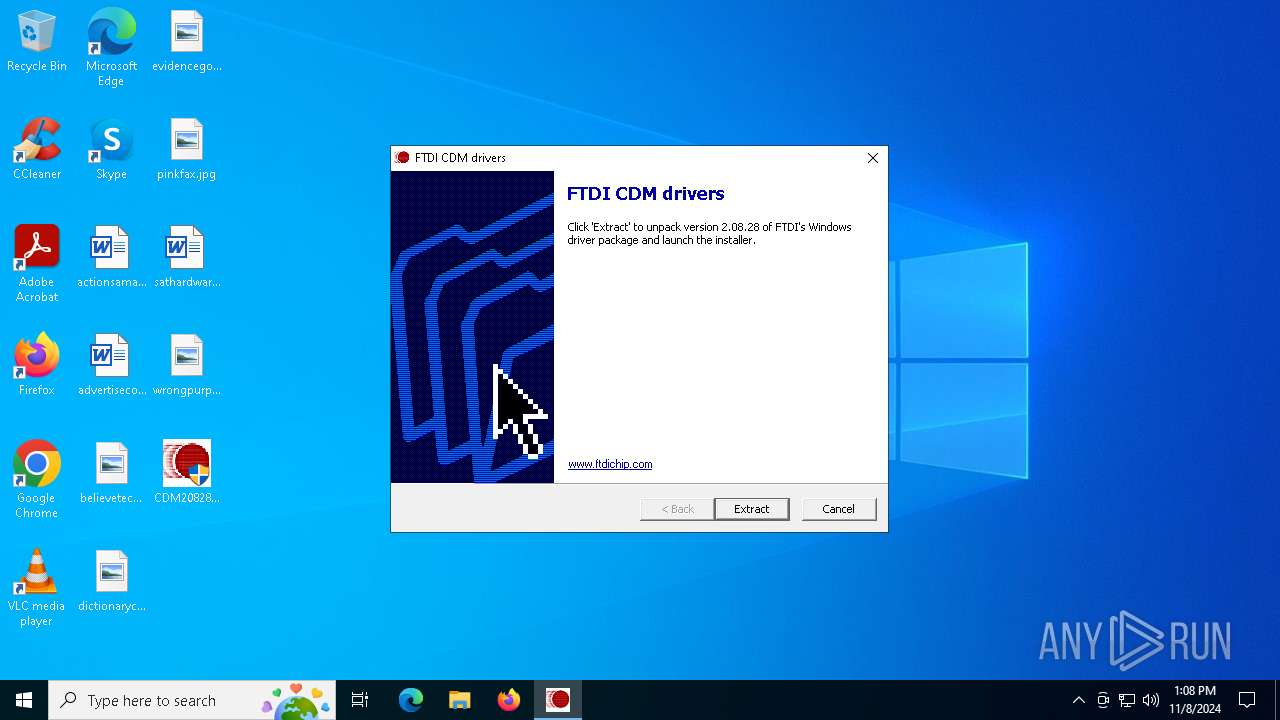
| File name: | CDM20828_Setup.exe |
| Full analysis: | https://app.any.run/tasks/21e2339d-1a2e-497b-97cf-c979520684ef |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2024, 13:08:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 8C51A8EC1FD9F3B84DF8F1F8969BEDDD |
| SHA1: | E49446E5B0A2923A2F0D148786CEFCEBCA0573F9 |
| SHA256: | 0E4ACF0D8517906BC1B77177CB6B4C835A8FFFB4ECB33FC3BEEF03B017643A89 |
| SSDEEP: | 49152:nhq29Cn5CKYIxGTSfJCiaFR/X6DsRDnE:nhqaC5PYEQSfGRisRw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts a Microsoft application from unusual location
- dpinst-amd64.exe (PID: 7152)
Process drops legitimate windows executable
- CDM20828_Setup.exe (PID: 6564)
Drops a system driver (possible attempt to evade defenses)
- CDM20828_Setup.exe (PID: 6564)
Executable content was dropped or overwritten
- CDM20828_Setup.exe (PID: 6564)
INFO
UPX packer has been detected
- CDM20828_Setup.exe (PID: 6564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:03:20 06:35:57+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Aggressive working-set trim, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 77824 |
| EntryPoint: | 0x19200 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
127
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
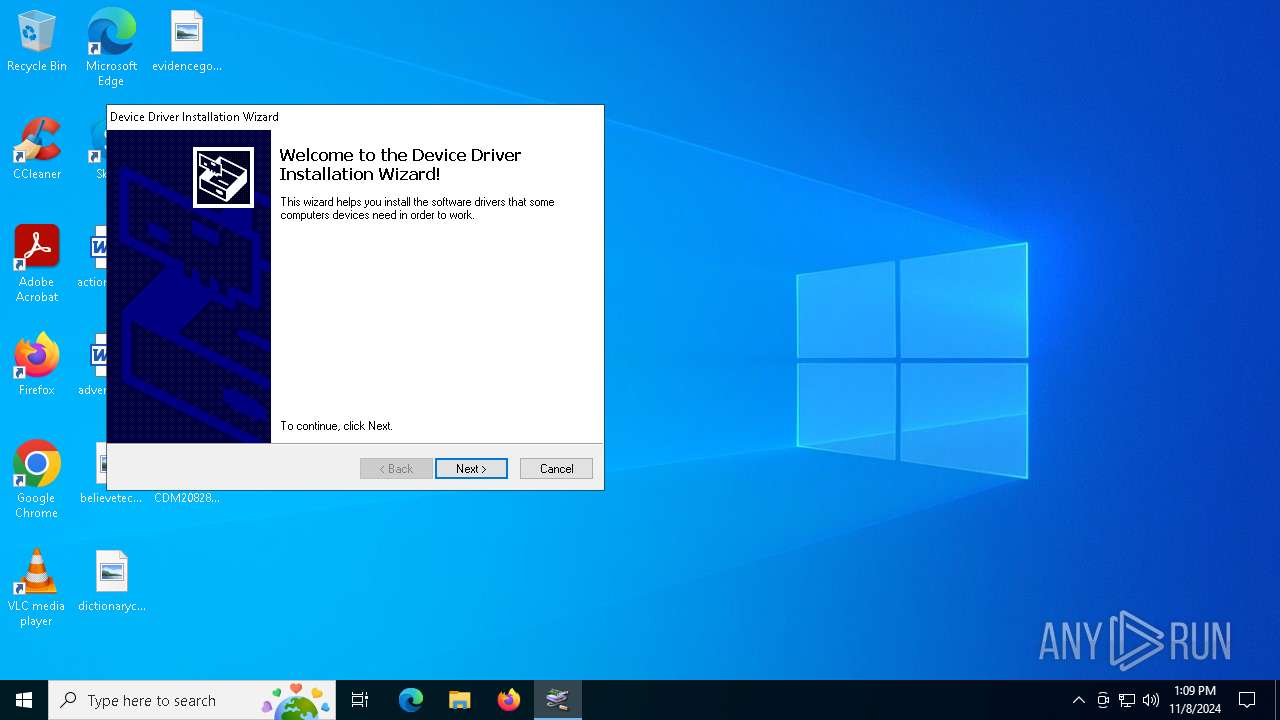
| 4076 | "C:\Users\admin\Desktop\CDM20828_Setup.exe" | C:\Users\admin\Desktop\CDM20828_Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4680 | C:\Users\admin\AppData\Local\Temp\CDM20828\dp-chooser.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\dp-chooser.exe | — | CDM20828_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6564 | "C:\Users\admin\Desktop\CDM20828_Setup.exe" | C:\Users\admin\Desktop\CDM20828_Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7152 | C:\Users\admin\AppData\Local\Temp\CDM20828\dpinst-amd64 | C:\Users\admin\AppData\Local\Temp\CDM20828\dpinst-amd64.exe | — | dp-chooser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Version: 2.1 Modules
| |||||||||||||||
Total events
68
Read events
68
Write events
0
Delete events
0
Modification events
Executable files
17
Suspicious files
8
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\amd64\ftcserco.dll | executable | |
MD5:7B4E1B9DF517BD3B496917E29F2907D8 | SHA256:B352762B9119994793594FA5A7E5455CEF7EDDEB1FE2CBD0E22C5F3490060E28 | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\amd64\ftser2k.sys | executable | |
MD5:787BBE2466C36B2E36B4A41BB788E2A2 | SHA256:A8B2480CBD350B7B89C0801C1F8C6B1504F964CE0B627B76885A682164060DA3 | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\Static\amd64\ftd2xx.lib | binary | |
MD5:A65102BDC371895D2062E6A3D337425F | SHA256:5732EB82A1985CE569E24D11361EC434B3E01A6C990FED68D1E9E26698A8DB20 | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\amd64\ftbusui.dll | executable | |
MD5:02CBAE0ECB056B9106A05E771198F338 | SHA256:A482D9CC15BDD682947B1F1C72EFF1917069828A92D47C40C9722A0B3321D434 | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\amd64\ftd2xx64.dll | executable | |
MD5:BD52F897F3413834E0FE41A183D679E8 | SHA256:E71C6827BBD708040109C4B17CD291A4750026F05C25390891913B5811692A1F | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\FEC3F5.tmp | text | |
MD5:6D51ED0972804B3CBD6C8D0AD340F8B3 | SHA256:138D6CE8BA5BC3241A3F73BB5DAEC0C4C9237BC7258477976546289513018EEC | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\amd64\ftd2xx.lib | binary | |
MD5:E9732A1FE90D44F5B08A5141730C3D16 | SHA256:8541DD69DC87251B887F84D0CCA821CDEED803E1BF5680C4942E1B9031CE1BBC | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\amd64\ftlang.dll | executable | |
MD5:41F0D8F295670F3391284F27000641C8 | SHA256:EFD6593347ED1E30732DACA68FB0C547526CD81A819A364E4767F29FE3B062AE | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\amd64\ftdibus.sys | executable | |
MD5:F16370F37CCA72ED2C21C230333C2C11 | SHA256:F8CA56AE1FA3A45EBEBA2536063B9141803DE3E61EE4D9999DCC941A6B3B7869 | |||
| 6564 | CDM20828_Setup.exe | C:\Users\admin\AppData\Local\Temp\CDM20828\i386\ftd2xx.dll | executable | |
MD5:02FCC97F500D50D543610B8C860BF4B2 | SHA256:0F635C52339255F10C3E995A2C9F309121919A43E3C625F1908ED6265D0F03DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
21
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.164.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
1584 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1584 | RUXIMICS.exe | GET | 200 | 2.16.164.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
6944 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1584 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 2.16.164.43:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1584 | RUXIMICS.exe | 2.16.164.43:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.43:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1584 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |