| File name: | 点击安装纸飞机-简体中文语言包.com |
| Full analysis: | https://app.any.run/tasks/5adc3338-8759-45ff-b456-235eaf96dbe7 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 16:32:33 |
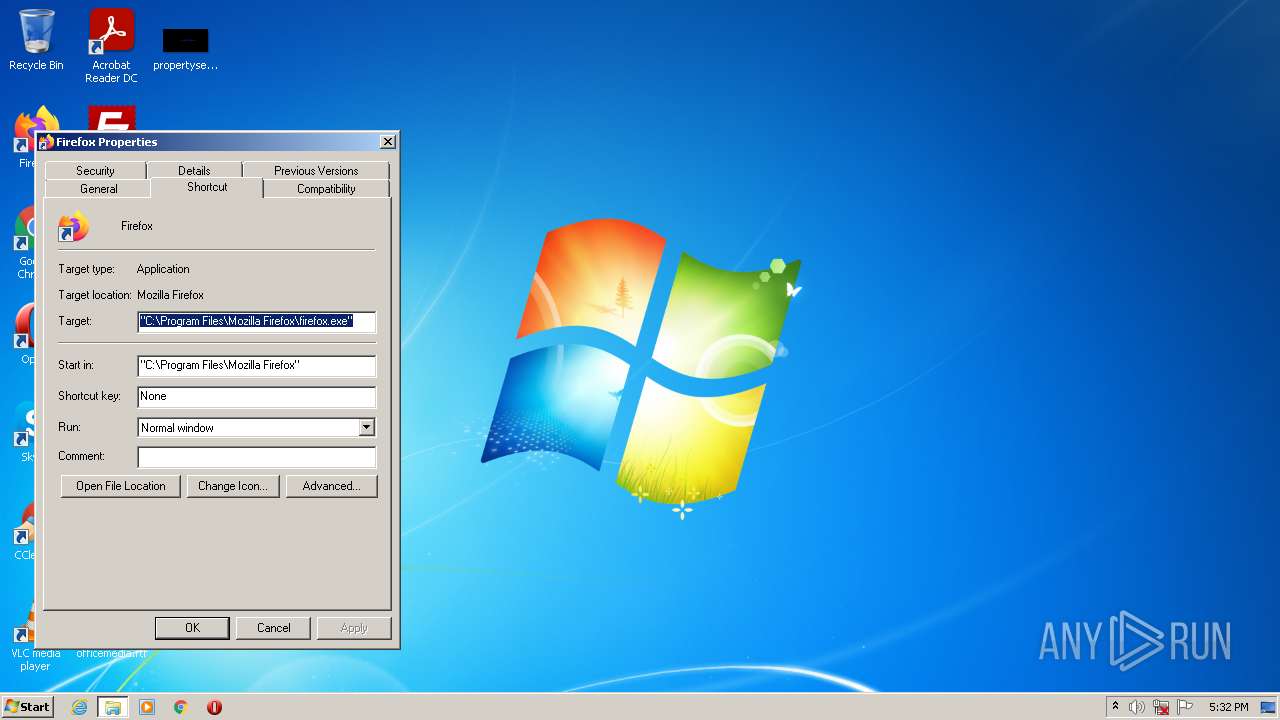
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 392CA1E33128E8BA6FE1417D5CF5569D |
| SHA1: | BAA7421C8394690736A436E036EB17C70D9B070D |
| SHA256: | 0E405E90943AA08BC9BA0F487D63D6EF1D2A1EDFB938C874D0285C3B5EDC3CAB |
| SSDEEP: | 49152:yu/pYQ+jPw/cfm9WDoQzmBo4xaKldv19I227pq0IwAfplRmf3aTzsV8sa7qCj8SW:HYQ+jPwNYhzmBo44Kldv1wq0IwCplRmw |
MALICIOUS
Application was dropped or rewritten from another process
- a2a.exe (PID: 3276)
- ApplicInetwiz.exe (PID: 3952)
Drops executable file immediately after starts
- 点击安装纸飞机-简体中文语言包.com.exe (PID: 3564)
- a2a.exe (PID: 3276)
Loads dropped or rewritten executable
- ApplicInetwiz.exe (PID: 3952)
- SearchProtocolHost.exe (PID: 3252)
Changes the autorun value in the registry
- ApplicInetwiz.exe (PID: 3952)
SUSPICIOUS
Checks supported languages
- 点击安装纸飞机-简体中文语言包.com.exe (PID: 3564)
- a2a.exe (PID: 3276)
- ApplicInetwiz.exe (PID: 3952)
Executable content was dropped or overwritten
- a2a.exe (PID: 3276)
- 点击安装纸飞机-简体中文语言包.com.exe (PID: 3564)
Executed via COM
- helppane.exe (PID: 3612)
- rundll32.exe (PID: 2336)
Reads the date of Windows installation
- helppane.exe (PID: 3612)
Reads the computer name
- 点击安装纸飞机-简体中文语言包.com.exe (PID: 3564)
- ApplicInetwiz.exe (PID: 3952)
Drops a file with a compile date too recent
- 点击安装纸飞机-简体中文语言包.com.exe (PID: 3564)
- a2a.exe (PID: 3276)
Reads Microsoft Outlook installation path
- helppane.exe (PID: 3612)
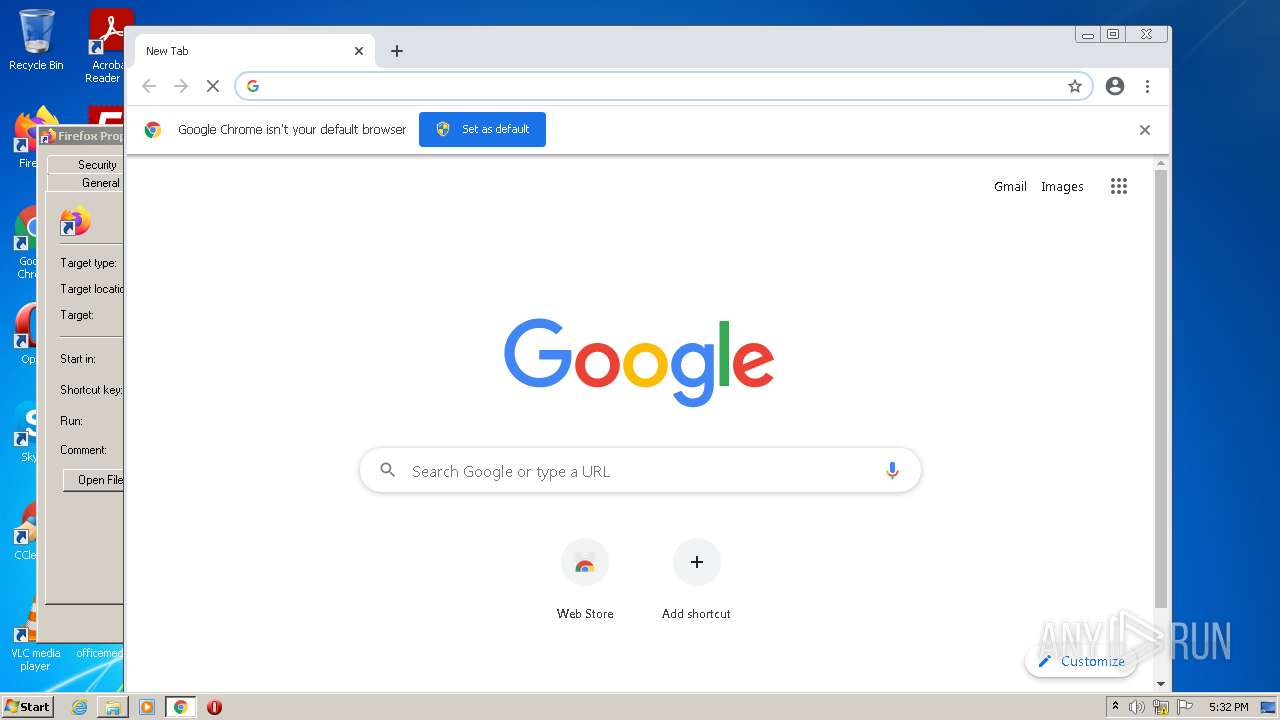
Modifies files in Chrome extension folder
- chrome.exe (PID: 844)
INFO
Reads the computer name
- helppane.exe (PID: 3612)
- chrome.exe (PID: 844)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 1516)
- chrome.exe (PID: 1624)
Checks supported languages
- helppane.exe (PID: 3612)
- rundll32.exe (PID: 2336)
- chrome.exe (PID: 844)
- chrome.exe (PID: 1624)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 884)
- chrome.exe (PID: 1516)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 920)
- chrome.exe (PID: 1776)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 3224)
Application launched itself
- chrome.exe (PID: 844)
Manual execution by user
- chrome.exe (PID: 844)
Reads the hosts file
- chrome.exe (PID: 3592)
- chrome.exe (PID: 844)
Reads settings of System Certificates
- chrome.exe (PID: 3592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.9) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (15) |
| .exe | | | Win32 Executable (generic) (2.4) |
| .exe | | | Generic Win/DOS Executable (1) |
EXIF
EXE
| ProductVersion: | 1.0.0.1 |
|---|---|
| ProductName: | TODO: <产品名> |
| OriginalFileName: | zh-cnv55.exe |
| LegalCopyright: | Copyright (C) 2022 |
| InternalName: | zh-cnv55.exe |
| FileVersion: | 1.0.0.1 |
| FileDescription: | TODO: <文件说明> |
| CompanyName: | TODO: <公司名> |
| CharacterSet: | Unicode |
| LanguageCode: | Unknown (000F) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.0.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x135d14 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1067520 |
| CodeSize: | 1416704 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2022:05:20 04:55:32+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-May-2022 02:55:32 |
| Detected languages: |
|
| CompanyName: | TODO: <公司名> |
| FileDescription: | TODO: <文件说明> |
| FileVersion: | 1.0.0.1 |
| InternalName: | zh-cnv55.exe |
| LegalCopyright: | Copyright (C) 2022 |
| OriginalFilename: | zh-cnv55.exe |
| ProductName: | TODO: <产品名> |
| ProductVersion: | 1.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-May-2022 02:55:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00159D4A | 0x00159E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5079 |
.rdata | 0x0015B000 | 0x000455AE | 0x00045600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99238 |
.data | 0x001A1000 | 0x0000F9BC | 0x00008200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.92675 |
.rsrc | 0x001B1000 | 0x0008D918 | 0x0008DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98741 |
.reloc | 0x0023F000 | 0x00029718 | 0x00029800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.02634 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05194 | 866 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.74274 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
3 | 2.34038 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
4 | 2.34004 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
5 | 2.51649 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
6 | 2.45401 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
7 | 0.38158 | 34 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 2.34505 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
9 | 2.34864 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
10 | 2.31114 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
Total processes
60
Monitored processes
23
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1024,1558975800744680922,4097654466944648101,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3056 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1024,1558975800744680922,4097654466944648101,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3068 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,1558975800744680922,4097654466944648101,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,1558975800744680922,4097654466944648101,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,1558975800744680922,4097654466944648101,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,1558975800744680922,4097654466944648101,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2228 | "C:\Users\admin\AppData\Local\Temp\点击安装纸飞机-简体中文语言包.com.exe" | C:\Users\admin\AppData\Local\Temp\点击安装纸飞机-简体中文语言包.com.exe | — | Explorer.EXE | |||||||||||
User: admin Company: TODO: <公司名> Integrity Level: MEDIUM Description: TODO: <文件说明> Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2336 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,1558975800744680922,4097654466944648101,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
10 804
Read events
10 646
Write events
157
Delete events
1
Modification events
| (PID) Process: | (3564) 点击安装纸飞机-简体中文语言包.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3564) 点击安装纸飞机-简体中文语言包.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3564) 点击安装纸飞机-简体中文语言包.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3564) 点击安装纸飞机-简体中文语言包.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3252) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3252) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (3612) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Assistance\Client\1.0\Settings |
| Operation: | write | Name: | OnlineAssist |
Value: 0 | |||
| (PID) Process: | (3612) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Assistance\Client\1.0\Settings |
| Operation: | write | Name: | ImplicitFeedback |
Value: 0 | |||
| (PID) Process: | (3612) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Assistance\Client\1.0\Settings |
| Operation: | write | Name: | FirstTimeHelppaneStartup |
Value: 0 | |||
| (PID) Process: | (3612) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Assistance\Client\1.0\Settings |
| Operation: | write | Name: | IsConnected |
Value: 0 | |||
Executable files
3
Suspicious files
116
Text files
83
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6287C2B9-34C.pma | — | |
MD5:— | SHA256:— | |||
| 3276 | a2a.exe | C:\Users\Public\Downloads\1025890\ApplicInetwiz.exe | executable | |
MD5:— | SHA256:— | |||
| 3564 | 点击安装纸飞机-简体中文语言包.com.exe | C:\Users\Public\Downloads\b.zip | compressed | |
MD5:— | SHA256:— | |||
| 844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFfdf5a.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3564 | 点击安装纸飞机-简体中文语言包.com.exe | C:\Users\Public\Downloads\a2a.exe | executable | |
MD5:94AB918D2BAF930268A84F3E4B10A83E | SHA256:092F51E25036E23162720E833EA688CBAD578C6844D041749885F5456D8FE035 | |||
| 844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3564 | 点击安装纸飞机-简体中文语言包.com.exe | C:\Users\Public\Downloads\s.lnk | lnk | |
MD5:— | SHA256:— | |||
| 844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3276 | a2a.exe | C:\Users\Public\Downloads\1025890\INETCFG.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
31
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3592 | chrome.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 591 b | whitelisted |
3592 | chrome.exe | GET | 200 | 74.125.8.104:80 | http://r3---sn-5hne6nzs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=157.97.122.7&mm=28&mn=sn-5hne6nzs&ms=nvh&mt=1653064101&mv=m&mvi=3&pl=24&rmhost=r1---sn-5hne6nzs.gvt1.com&shardbypass=sd&smhost=r1---sn-5hne6nsd.gvt1.com | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3592 | chrome.exe | 142.250.184.196:443 | www.google.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 216.58.212.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 142.250.185.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 142.250.185.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 142.250.186.99:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3592 | chrome.exe | 142.250.186.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |