| File name: | C:\Users\admin\Desktop\CXSplay.exe |
| Full analysis: | https://app.any.run/tasks/fa24cf96-27a6-4de3-bacf-678f3e3b2b58 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 09:56:44 |
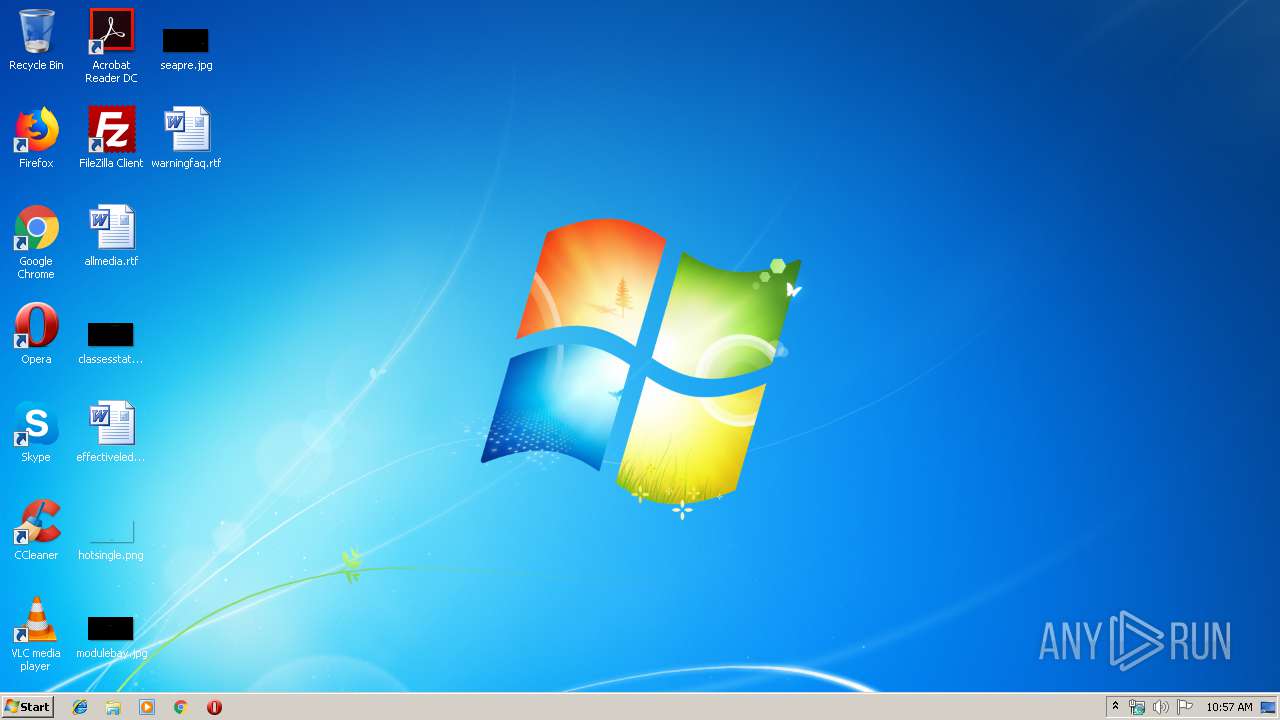
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 960A505759EF8CFA5AA6E8689D3E04BC |
| SHA1: | 93268C84F806010C09C9F3AD862B1CBB1AEA028C |
| SHA256: | 0E201DB06D2E2E58A0600C631FB5DAB0DB328A339CCD2E623C0E1D9CE75ADAB7 |
| SSDEEP: | 24576:ZcwWawXEUYBsX9mcdtMP9+rHIyghro2ZPBn2Uf92lNUfYuhgZ2pP6wGGsVYYYYYB:2wW5XEUYBsXNMF+Eh8UoloYuhI2JfqYx |
MALICIOUS
Loads dropped or rewritten executable
- CXSplay.exe (PID: 3464)
Application was dropped or rewritten from another process
- svchost.exe (PID: 2100)
- svchost.exe (PID: 3468)
- explorerr.exe (PID: 2128)
- Server.exe (PID: 2848)
SUSPICIOUS
Executable content was dropped or overwritten
- CXSplay.exe (PID: 3464)
- Server.exe (PID: 2848)
Creates files in the Windows directory
- CXSplay.exe (PID: 3464)
- Server.exe (PID: 2848)
Creates executable files which already exist in Windows
- Server.exe (PID: 2848)
Executed as Windows Service
- svchost.exe (PID: 3468)
Creates or modifies windows services
- Server.exe (PID: 2848)
- svchost.exe (PID: 2100)
Application launched itself
- svchost.exe (PID: 3468)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:13 08:45:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1200128 |
| InitializedDataSize: | 212992 |
| UninitializedDataSize: | 724992 |
| EntryPoint: | 0x1d5c70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | 应用程序 |
| ProductName: | 易语言程序 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Nov-2018 07:45:46 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | 应用程序 |
| ProductName: | 易语言程序 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Nov-2018 07:45:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x000B1000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x000B2000 | 0x00125000 | 0x00124A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99972 |
.rsrc | 0x001D7000 | 0x00034000 | 0x00033400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.19484 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02094 | 697 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 3.5232 | 10344 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.84212 | 2664 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.96536 | 1640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.82603 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.69679 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 3.07507 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 5.07349 | 19496 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 5.70457 | 5672 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WINSPOOL.DRV |
WS2_32.dll |
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2100 | C:\Windows\svchost.exe Win7 | C:\Windows\svchost.exe | svchost.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: 5555 MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2128 | C:\Windows\explorerr.exe | C:\Windows\explorerr.exe | — | CXSplay.exe | |||||||||||
User: admin Integrity Level: HIGH Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2848 | C:\Windows\Server.exe | C:\Windows\Server.exe | CXSplay.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 5555 MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\Downloads\CXSplay.exe" | C:\Users\admin\Downloads\CXSplay.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 应用程序 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3464 | "C:\Users\admin\Downloads\CXSplay.exe" | C:\Users\admin\Downloads\CXSplay.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 应用程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3468 | C:\Windows\svchost.exe | C:\Windows\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: 5555 MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
50
Read events
31
Write events
19
Delete events
0
Modification events
| (PID) Process: | (2848) Server.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Opqrst |
| Operation: | write | Name: | Description |
Value: Opqrstuv Xyabcdefg Ijklmno Qrstuvwx Abc | |||
| (PID) Process: | (2848) Server.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Opqrst |
| Operation: | write | Name: | Group |
Value: Default | |||
| (PID) Process: | (2848) Server.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Opqrst |
| Operation: | write | Name: | InstallTime |
Value: 2019-07-18 10:57 | |||
| (PID) Process: | (2848) Server.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Windows\system32\1554437.bak | |||
| (PID) Process: | (2100) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Opqrst |
| Operation: | write | Name: | MarkTime |
Value: 2019-07-18 10:57 | |||
| (PID) Process: | (3464) CXSplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CXSplay_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3464) CXSplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CXSplay_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3464) CXSplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CXSplay_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3464) CXSplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CXSplay_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3464) CXSplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\CXSplay_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
6
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3464 | CXSplay.exe | C:\Users\admin\AppData\Local\Temp\1553125\TemporaryFile | — | |
MD5:— | SHA256:— | |||
| 3464 | CXSplay.exe | C:\Users\admin\AppData\Local\Temp\1553125\....\TemporaryFile | executable | |
MD5:— | SHA256:— | |||
| 2848 | Server.exe | C:\Windows\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 2848 | Server.exe | C:\Windows\system32\1554437.bak | executable | |
MD5:— | SHA256:— | |||
| 3464 | CXSplay.exe | C:\Windows\explorerr.exe | executable | |
MD5:— | SHA256:— | |||
| 3464 | CXSplay.exe | C:\Users\admin\Downloads\1.dll | executable | |
MD5:— | SHA256:— | |||
| 3464 | CXSplay.exe | C:\Windows\Server.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
Server.exe | ½øÈëDLLMain |
svchost.exe | ½øÈëDLLMain |
svchost.exe | ½øÈëDLLMain |