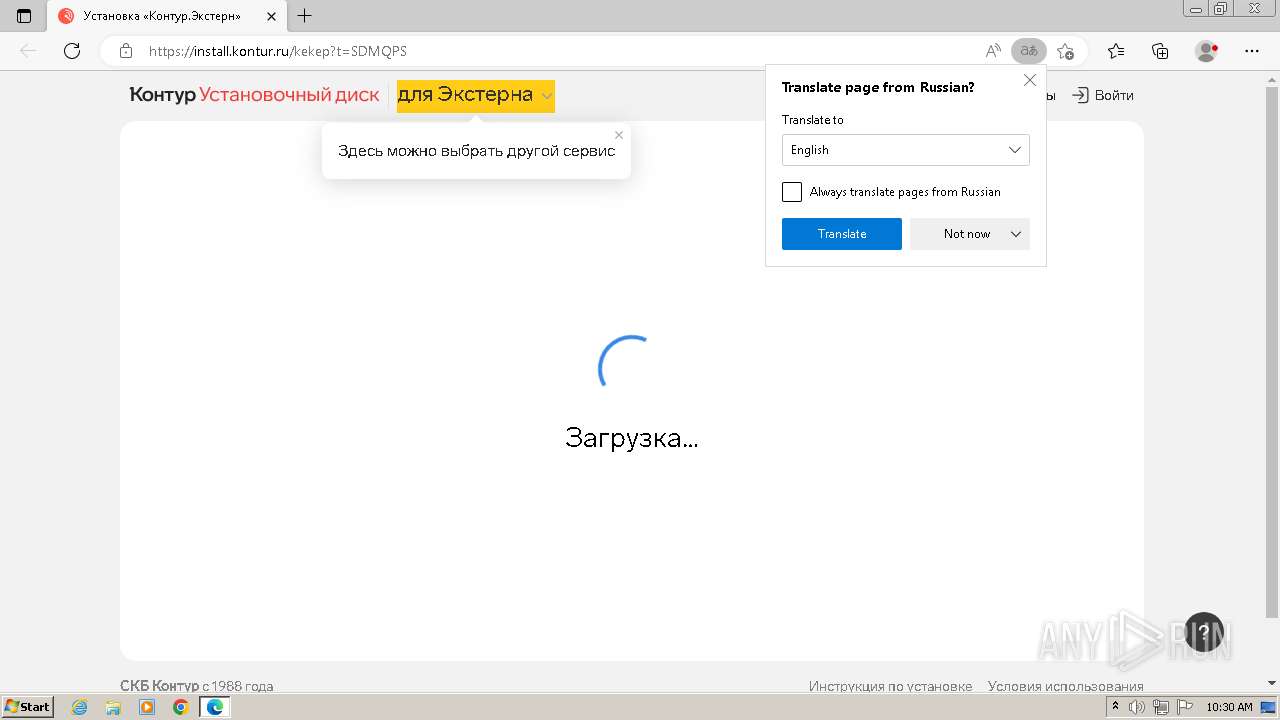
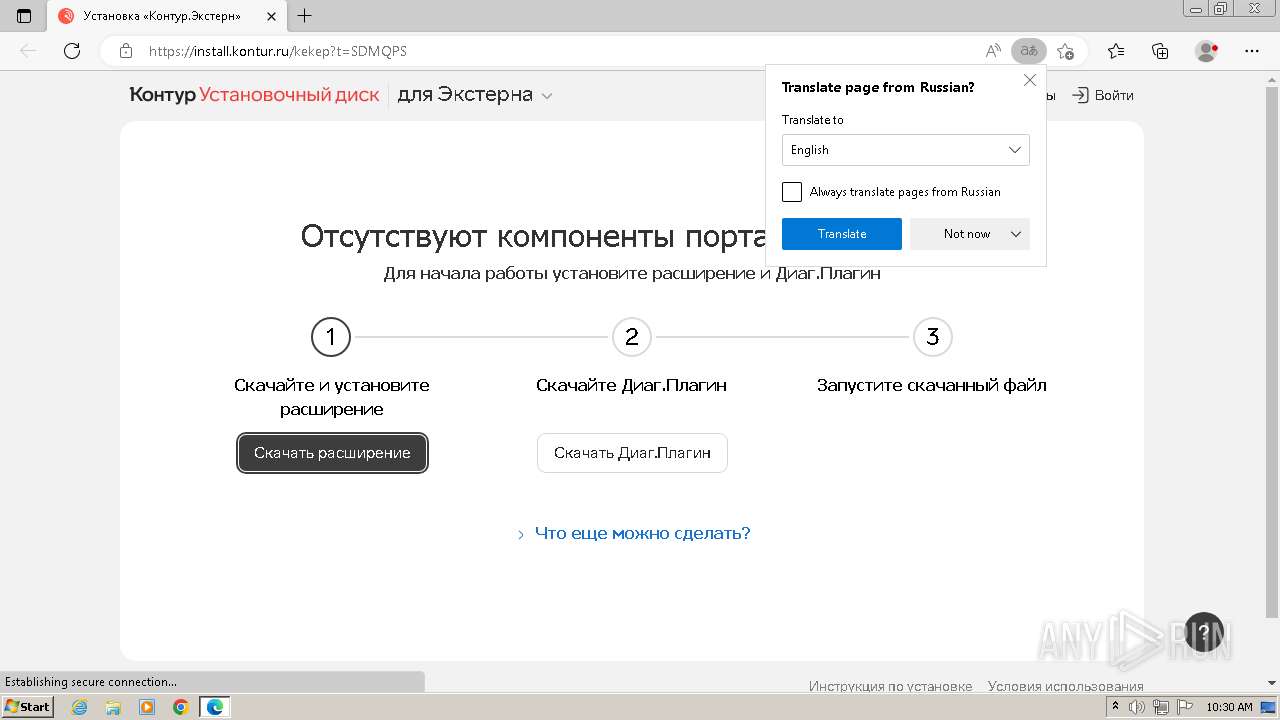
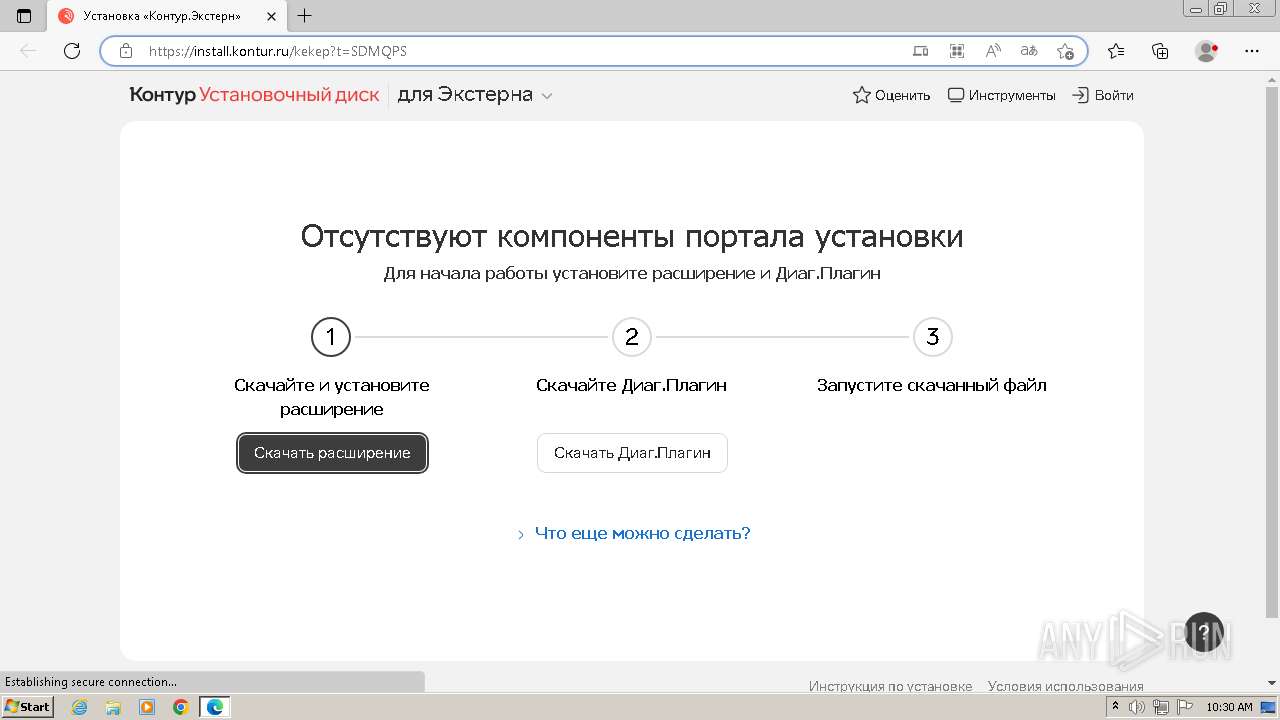
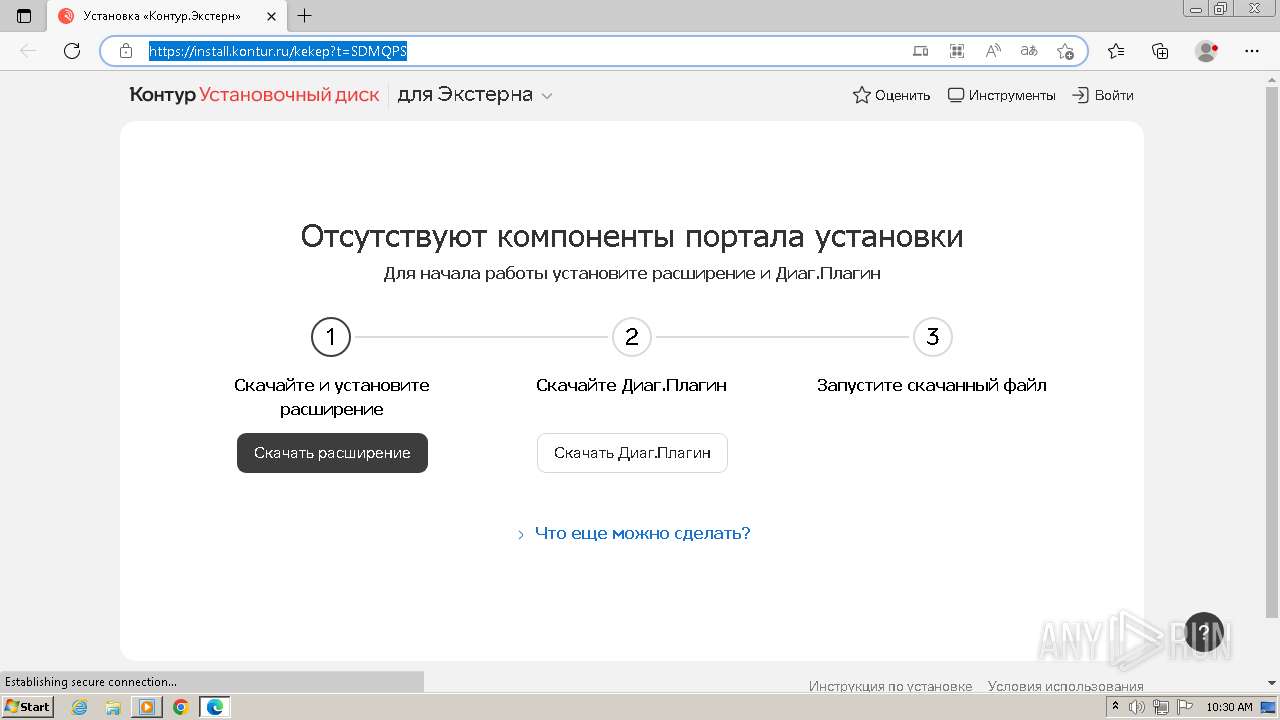
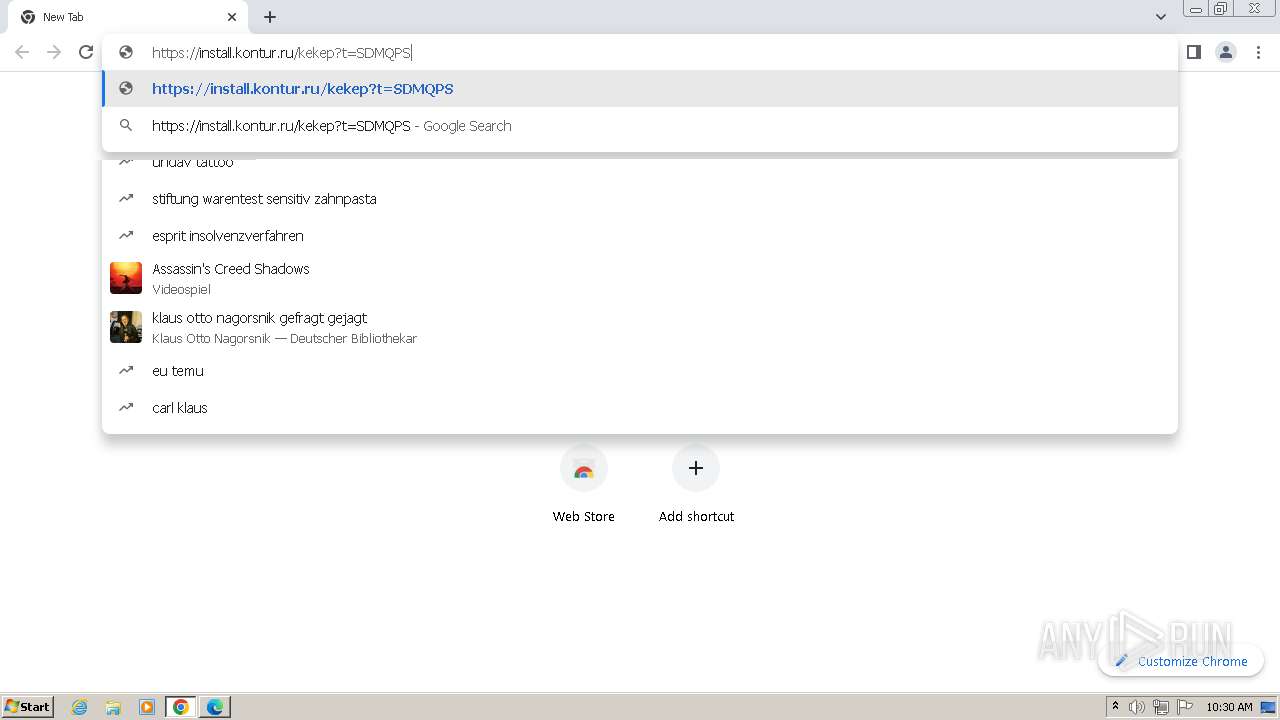
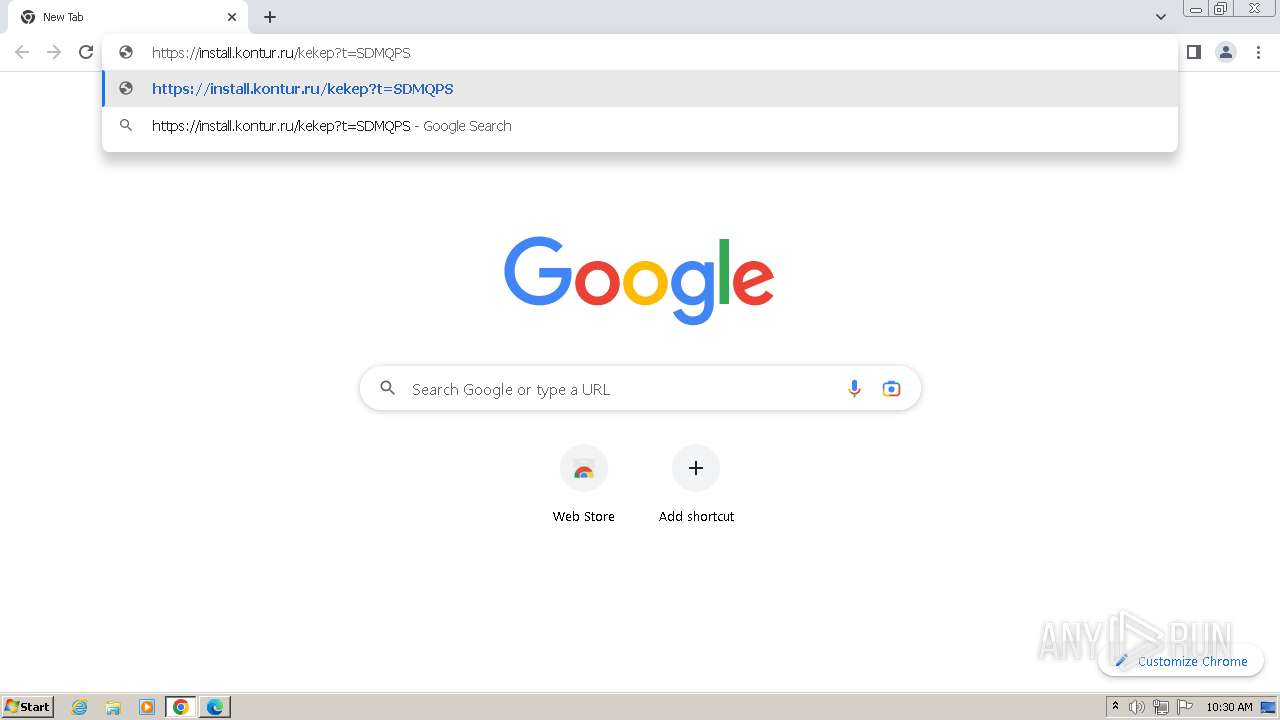
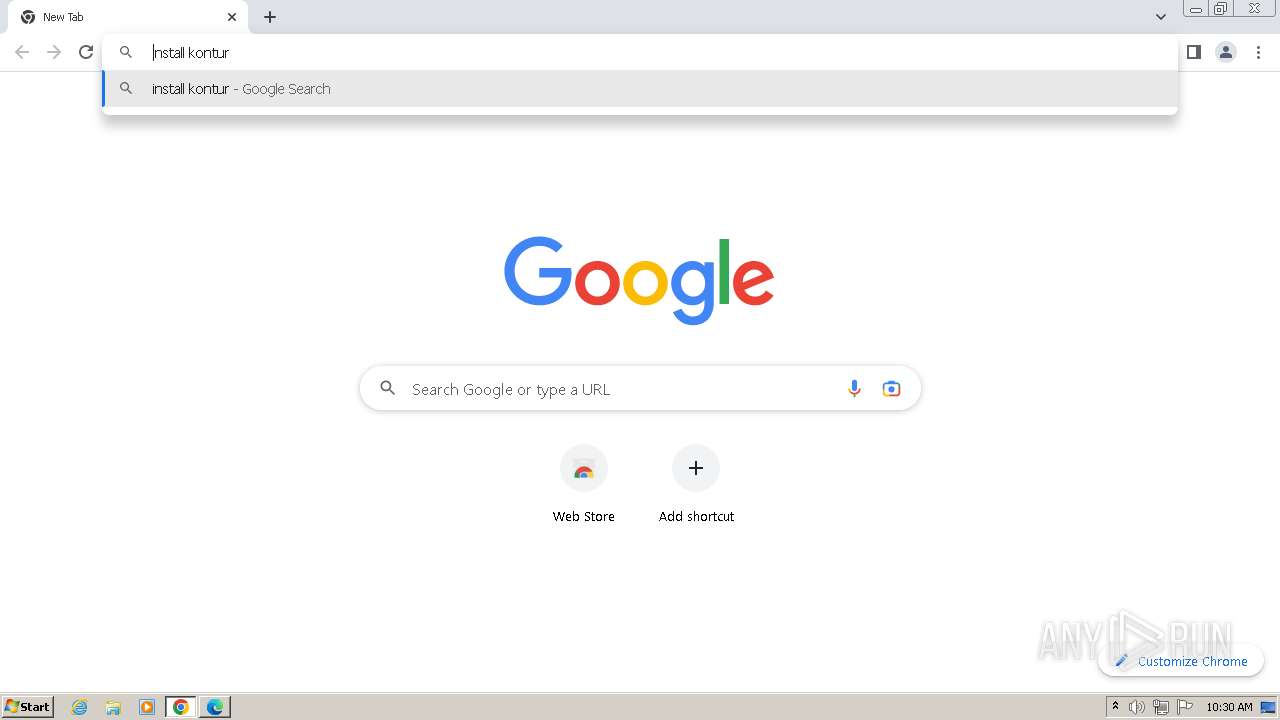
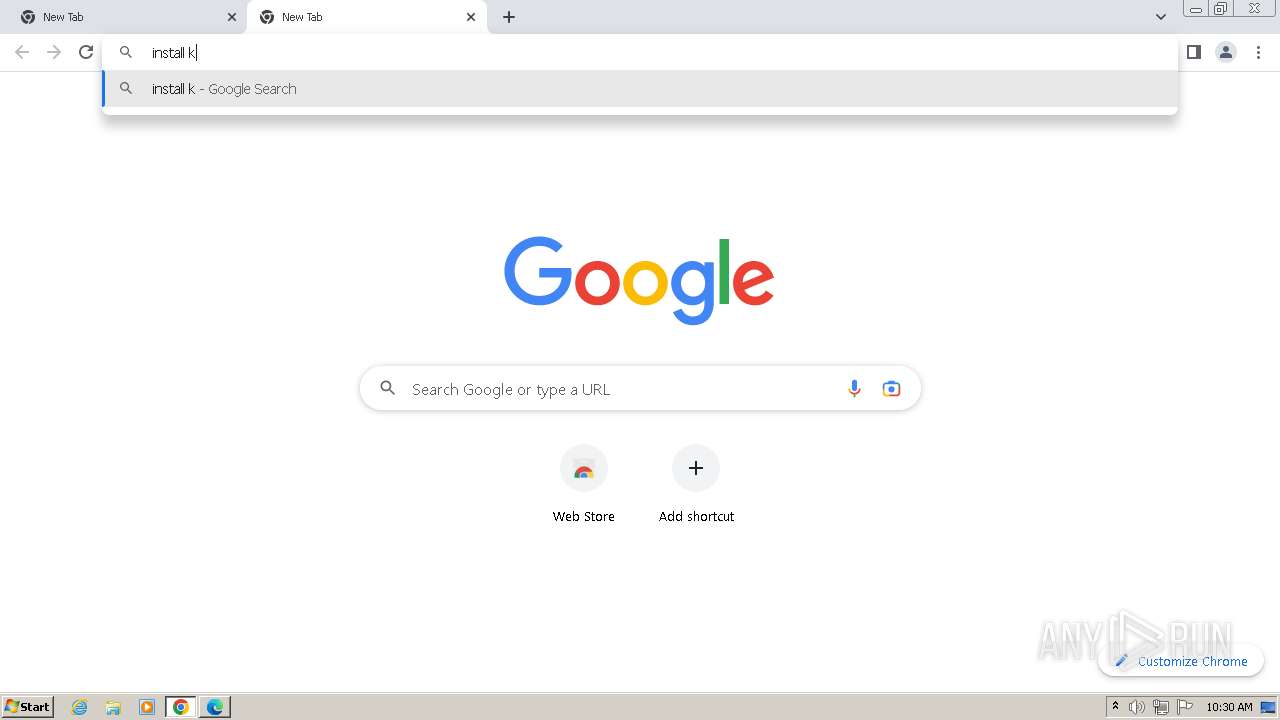
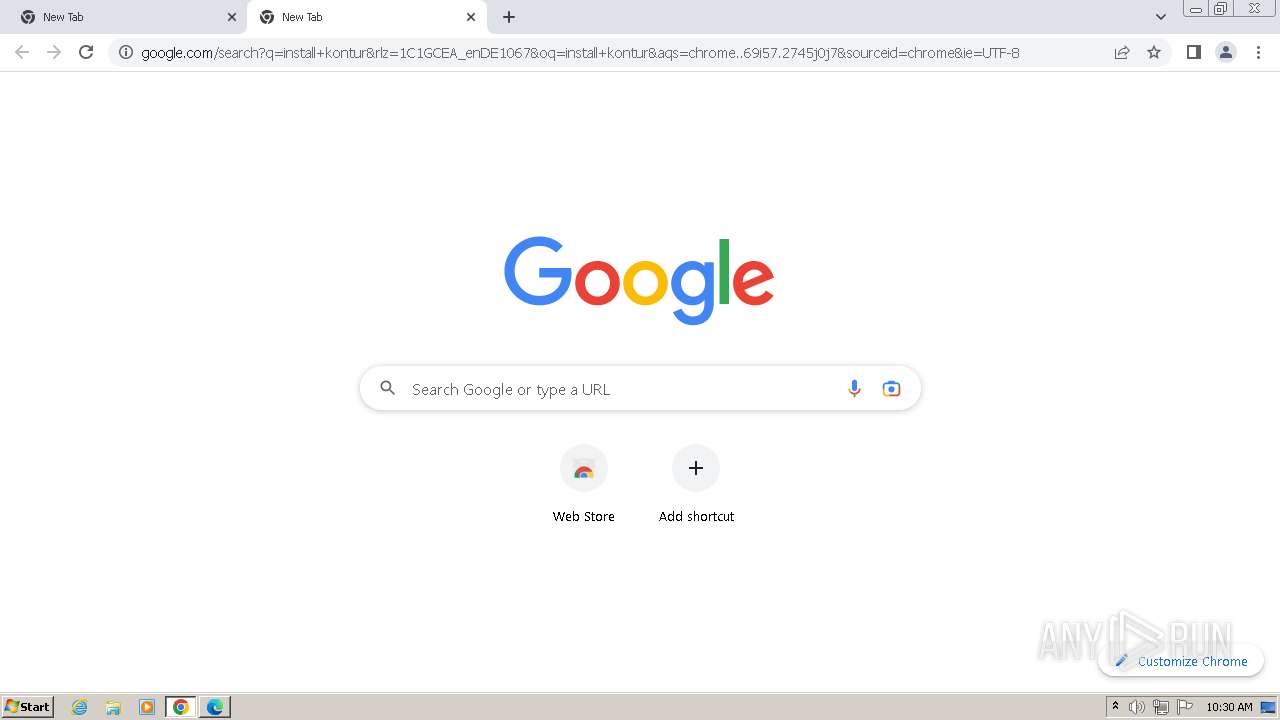
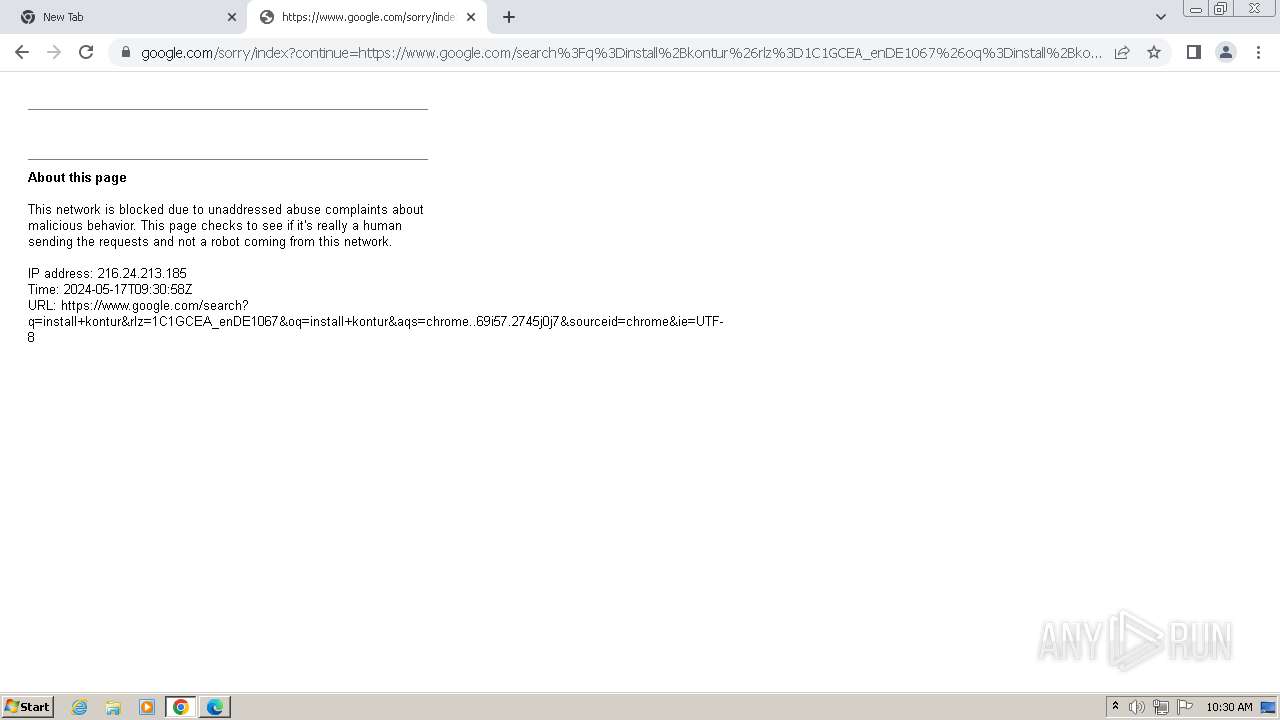
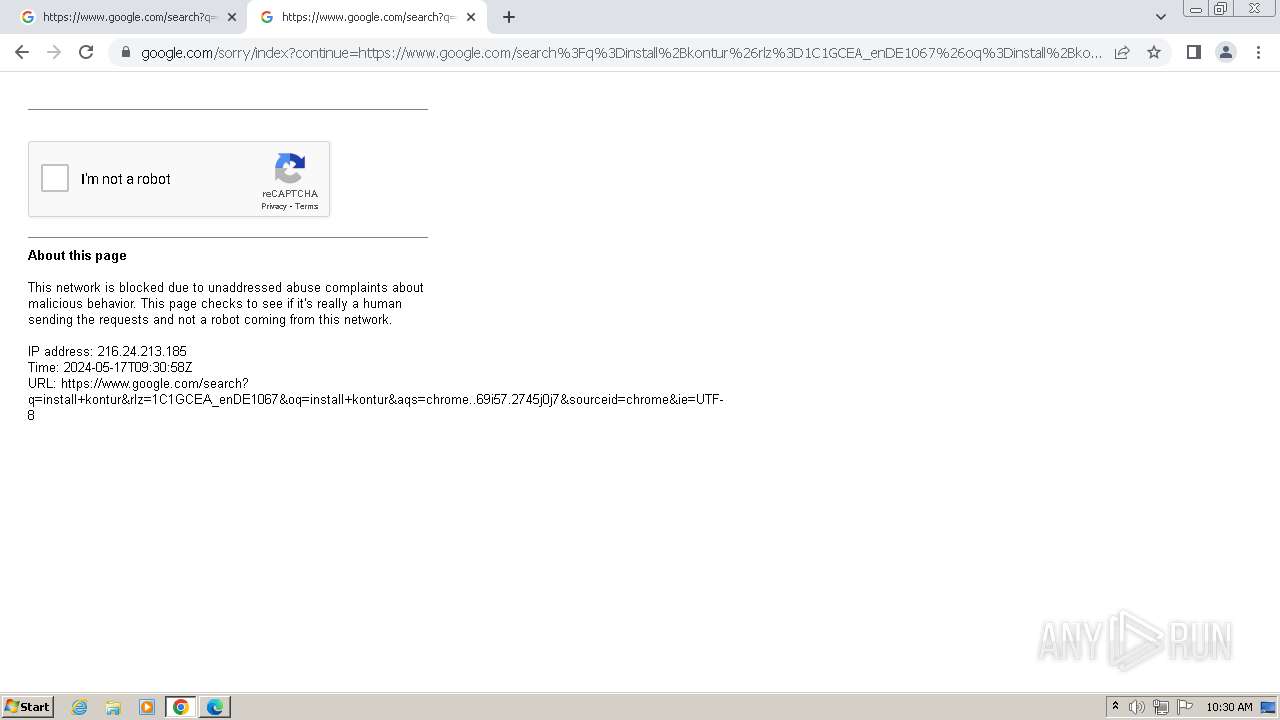
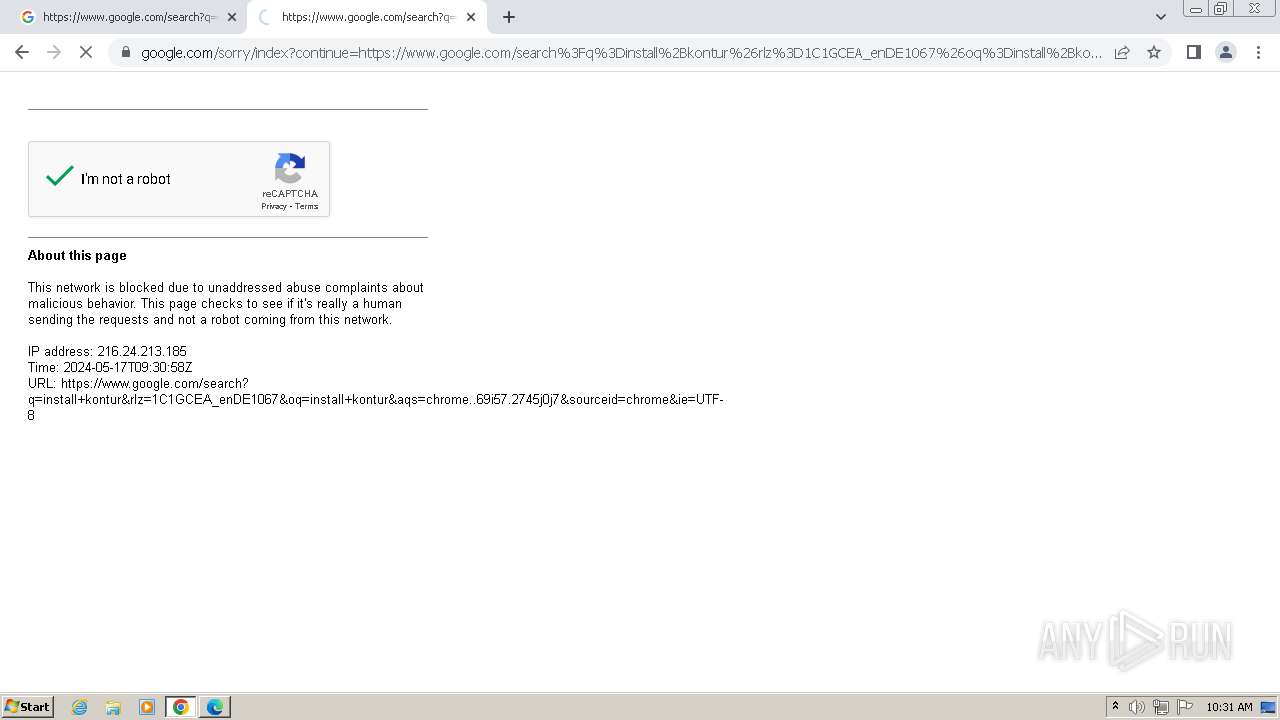
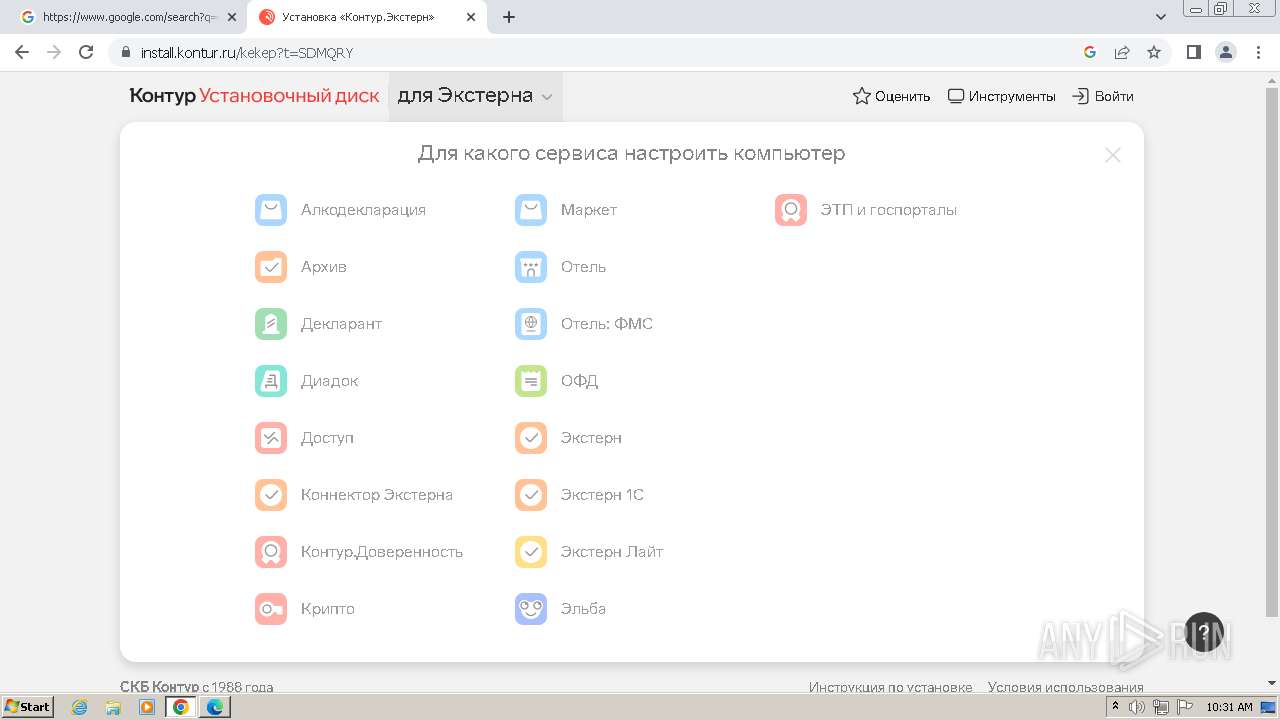
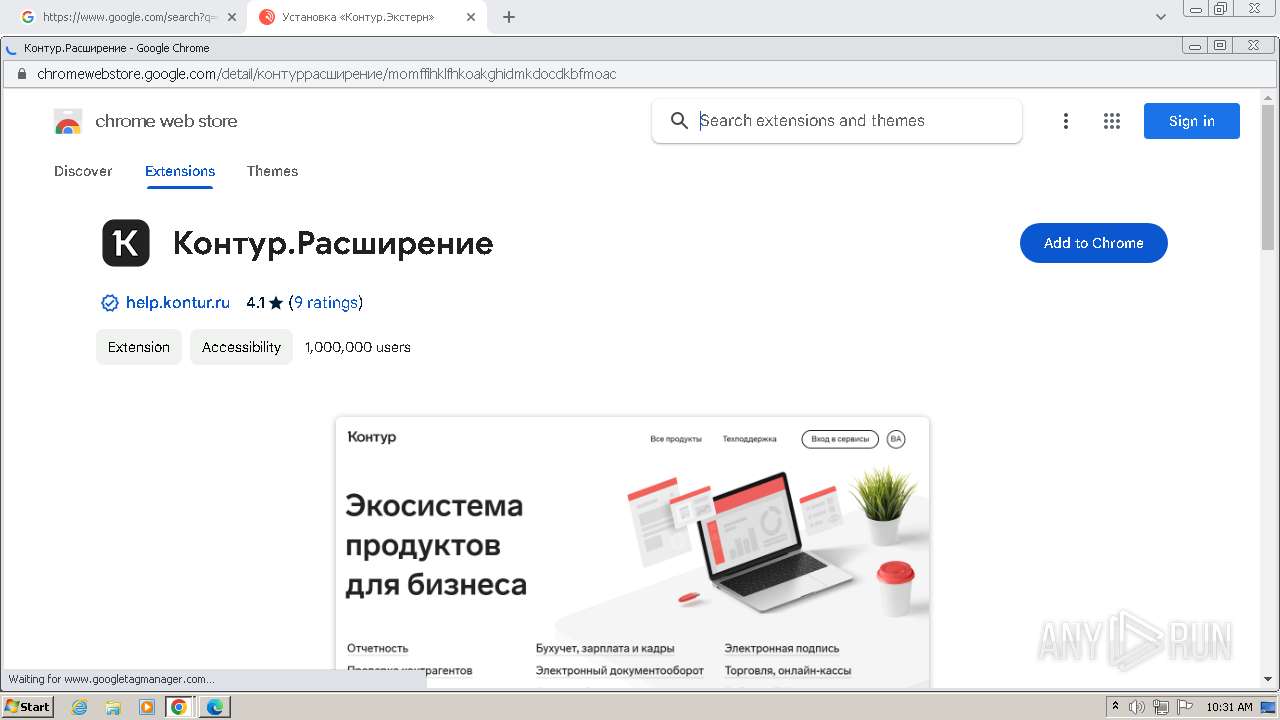
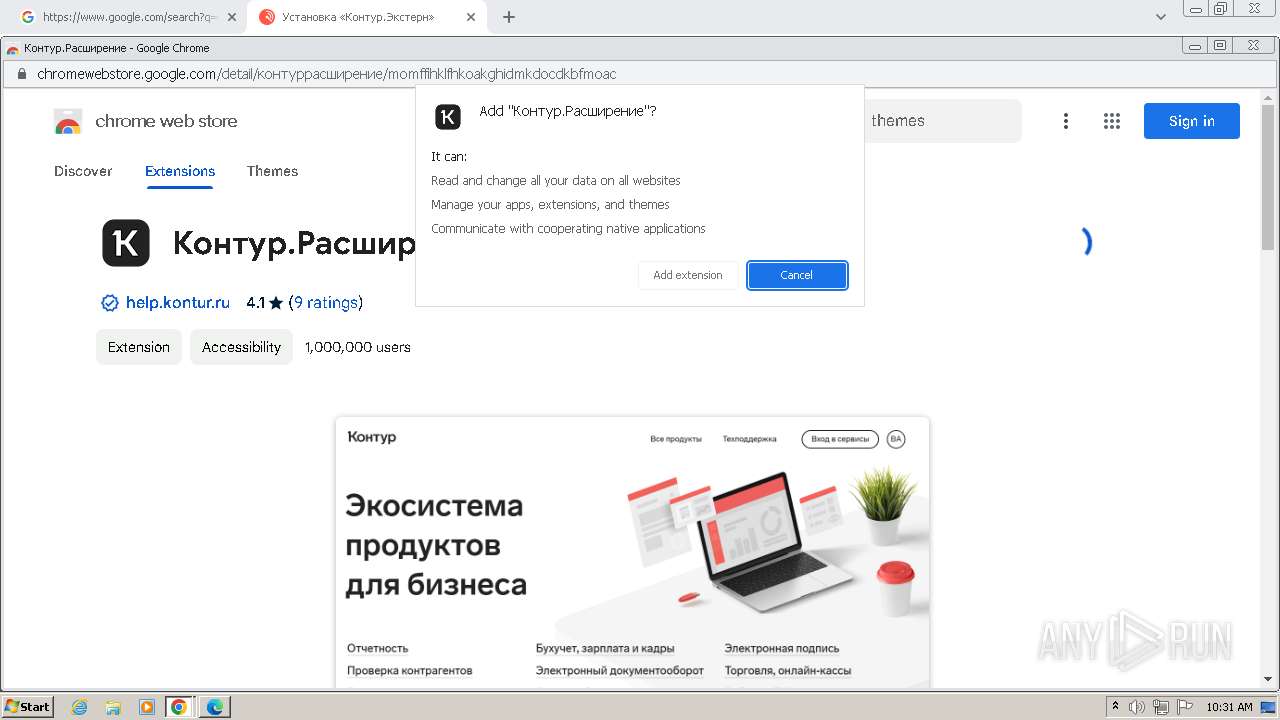
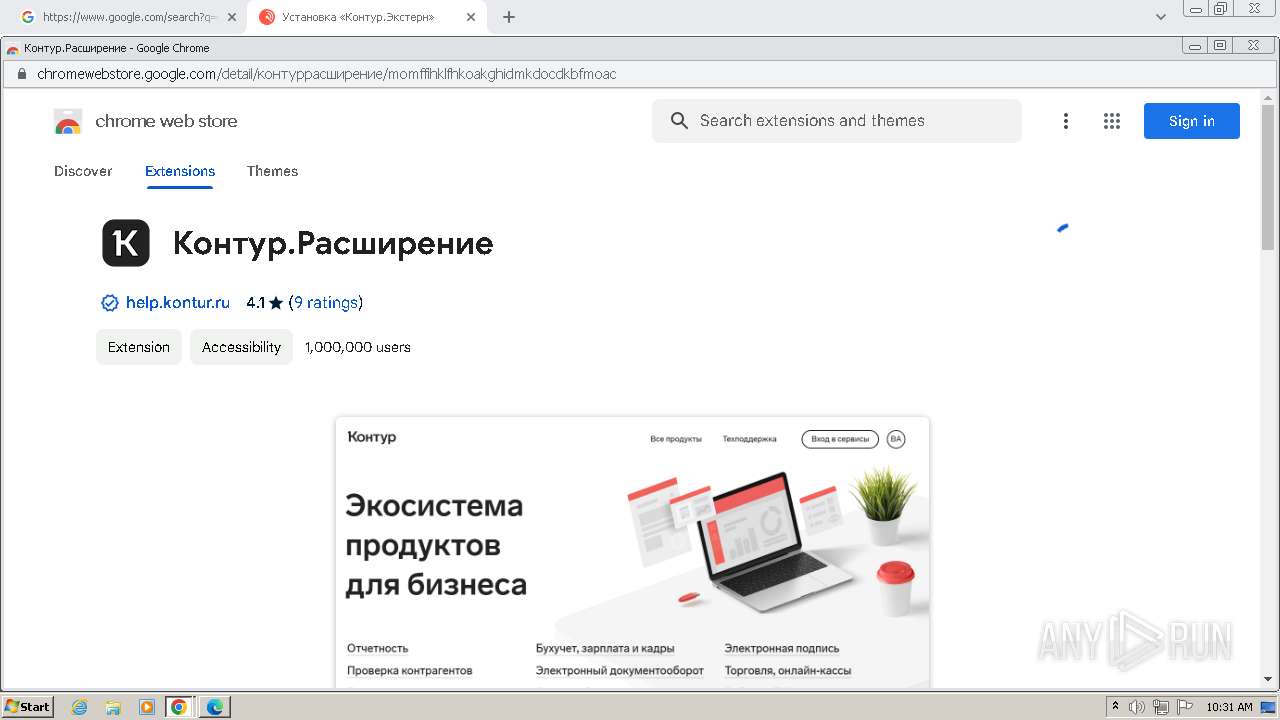
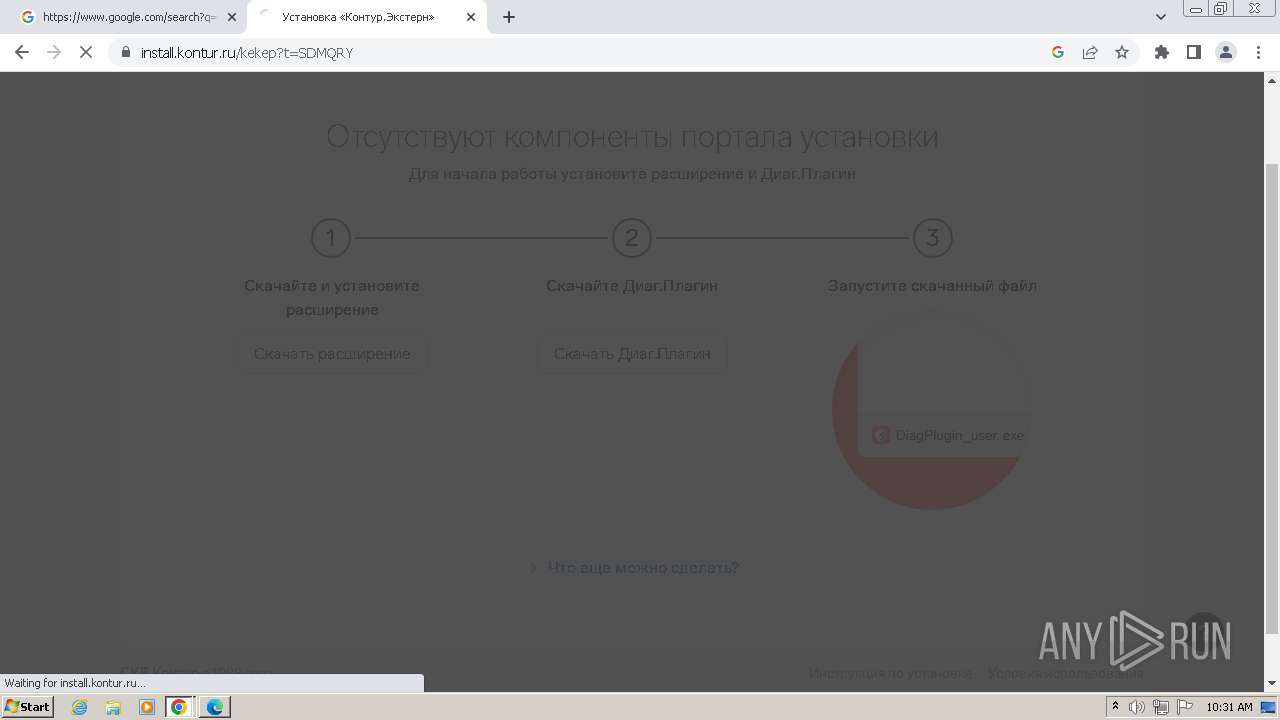
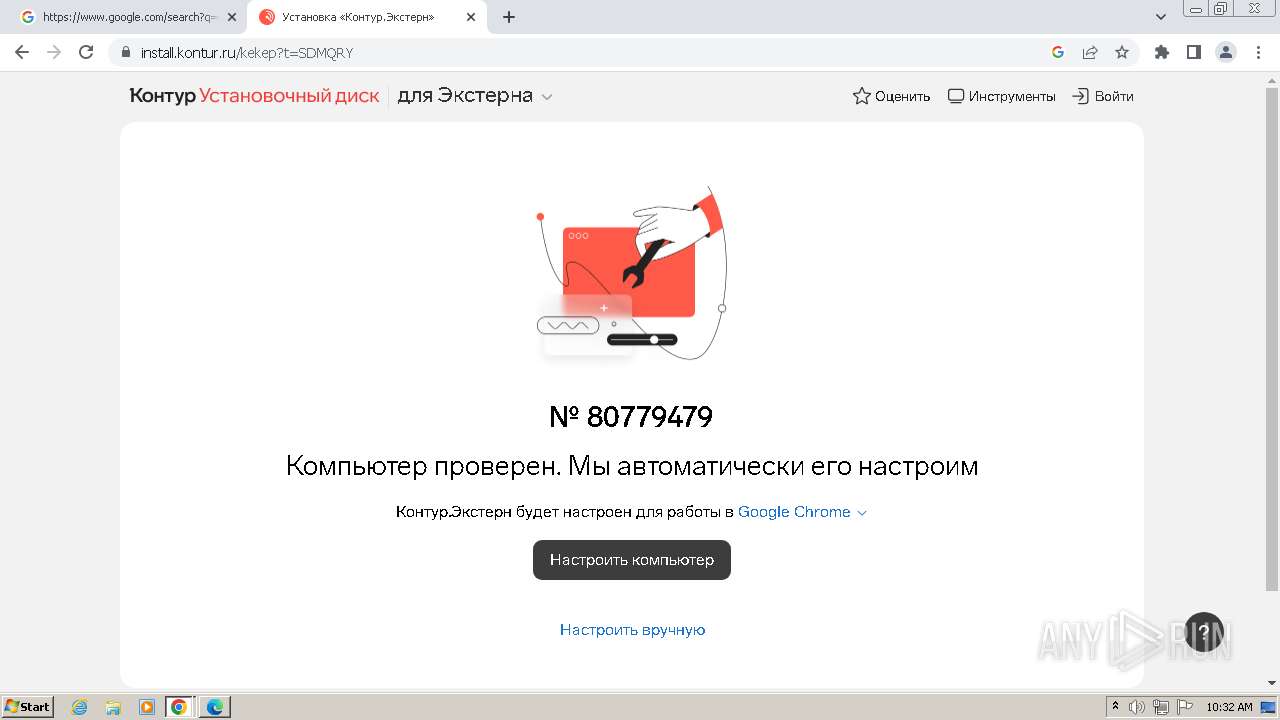
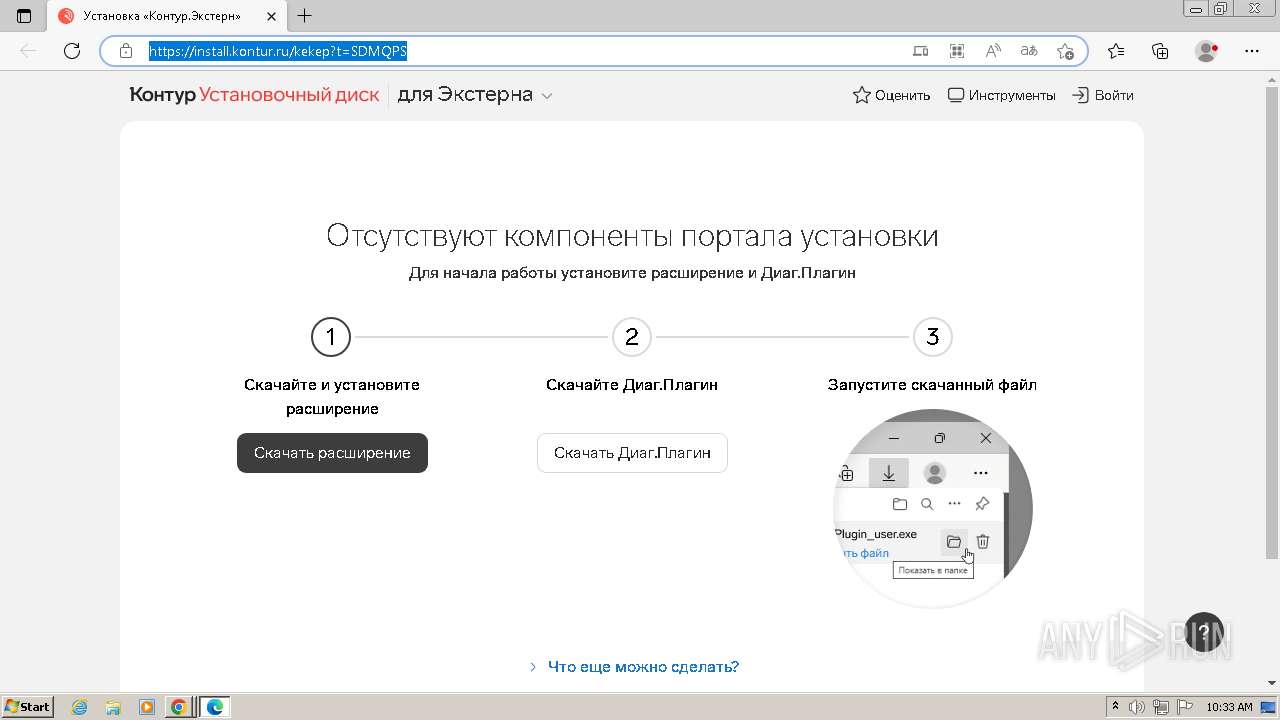
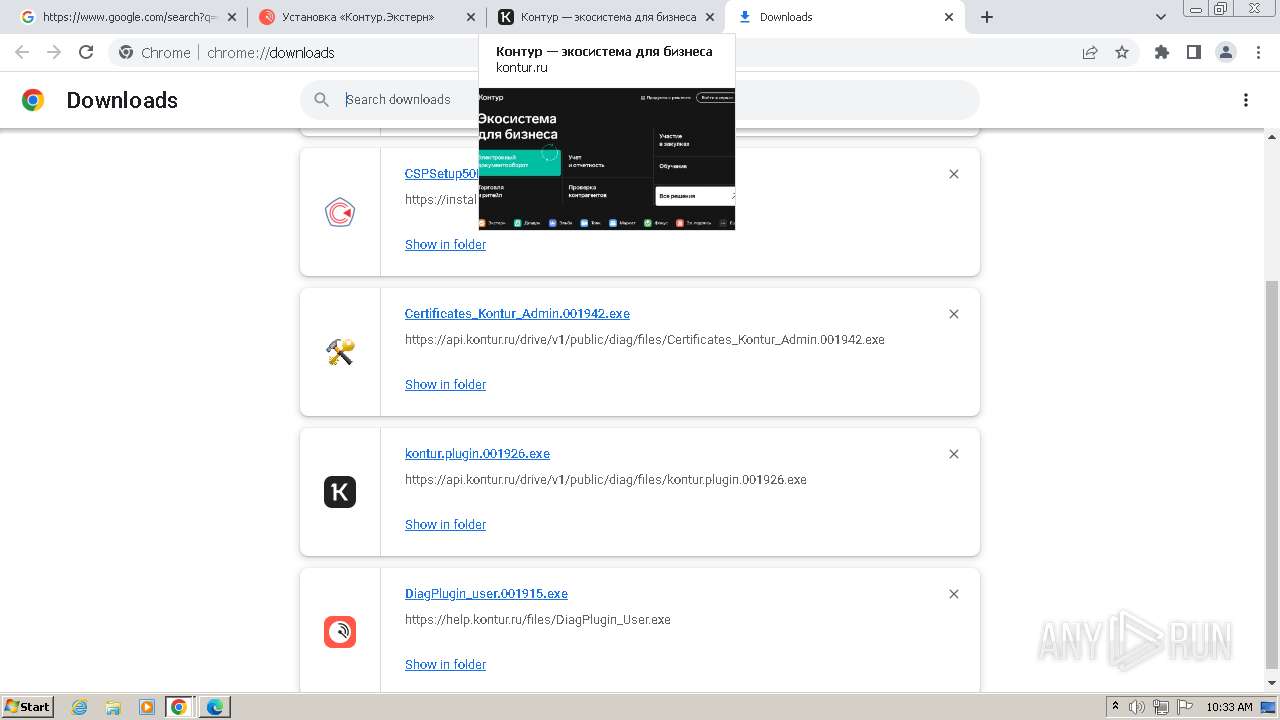
| URL: | https://install.kontur.ru |
| Full analysis: | https://app.any.run/tasks/d1407ae2-e48f-4cb6-a5ee-fe5e94716afa |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2024, 09:29:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F3A014949A1618E609C25BE511B97A58 |
| SHA1: | 3DDED06EAF863576D7B5FE8AEDEAD198145E96AD |
| SHA256: | 0E1D6EB699821E5E8D2B48E638FE760ABD3F59B1AA6996F7187149D36A7D2D46 |
| SSDEEP: | 3:N8LREJFlL2Xsn:2lgzLNn |
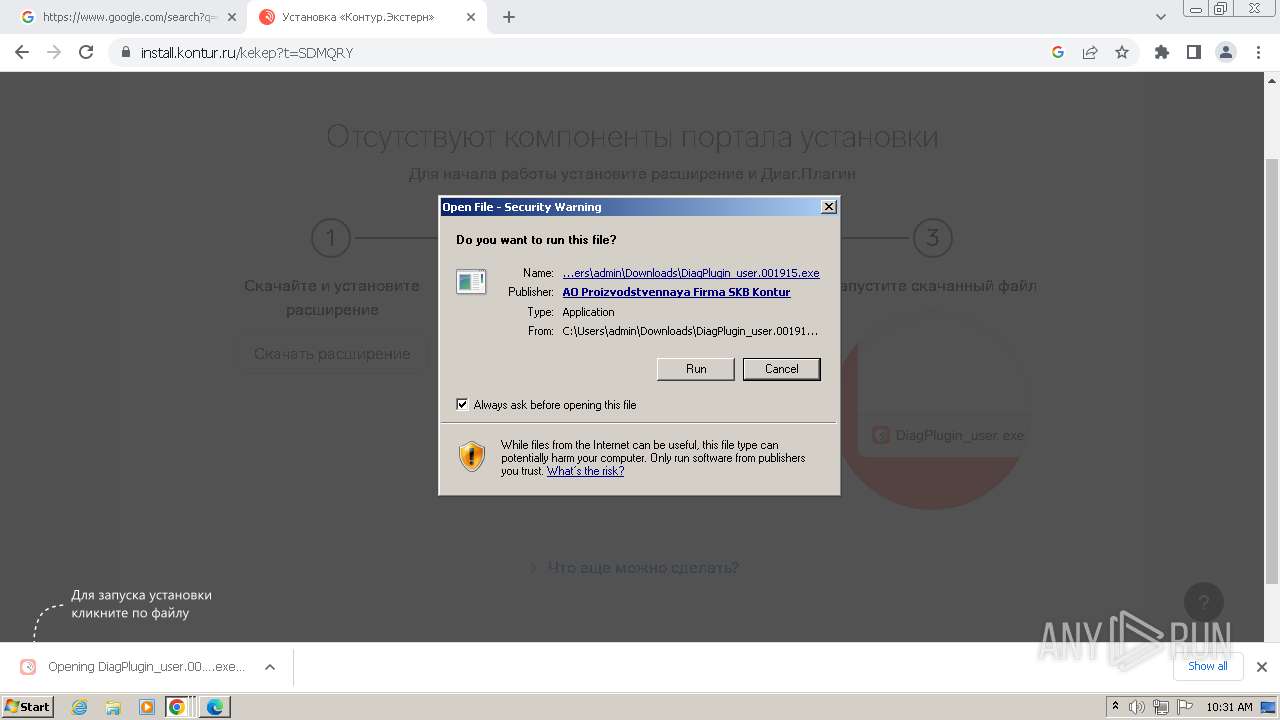
MALICIOUS
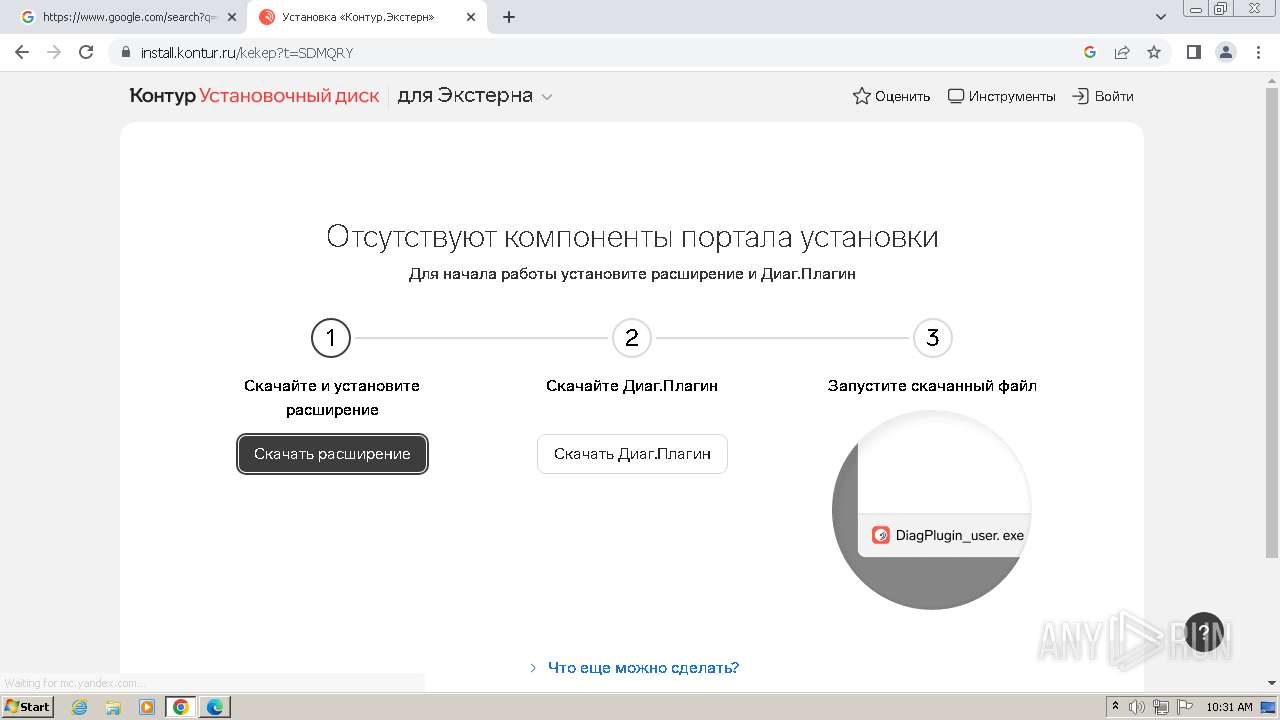
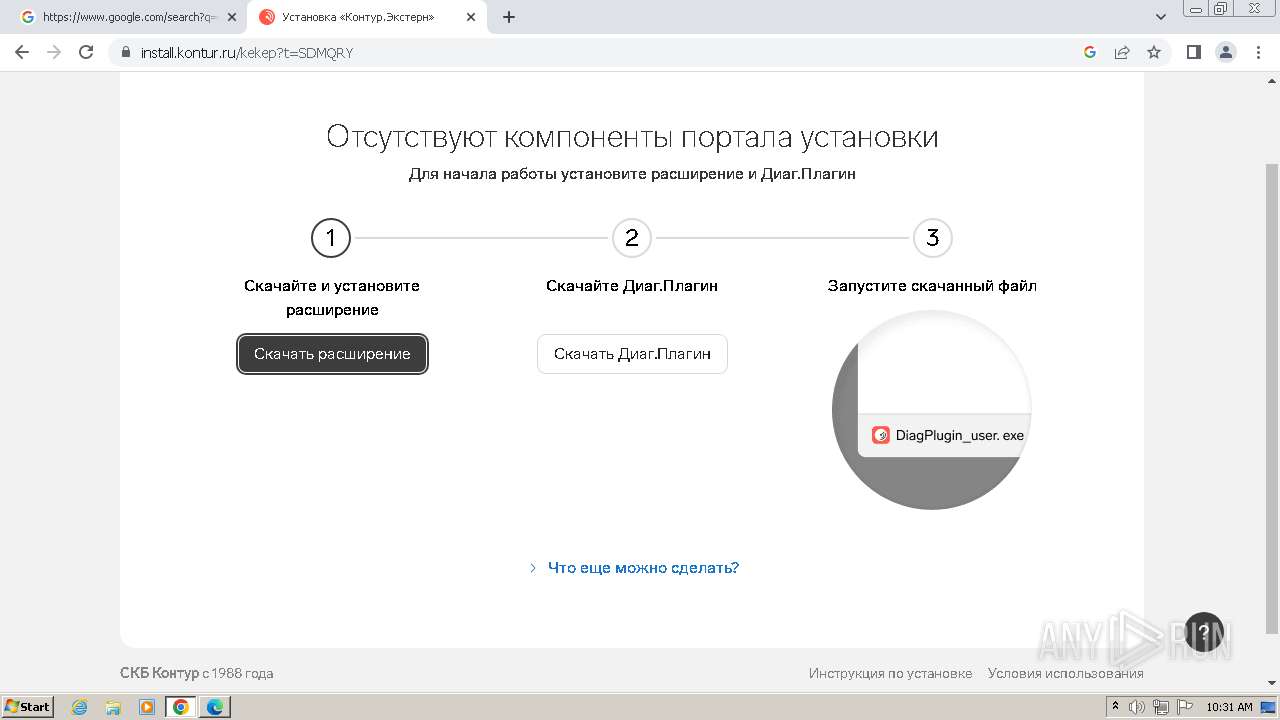
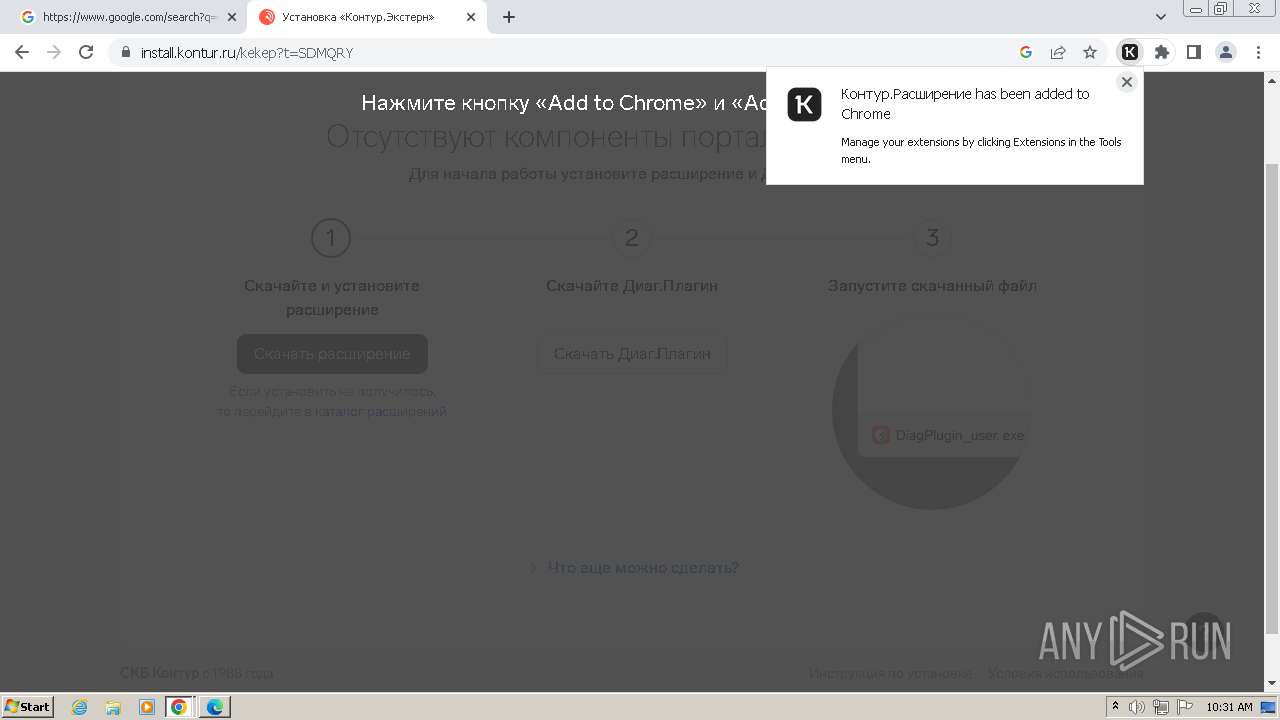
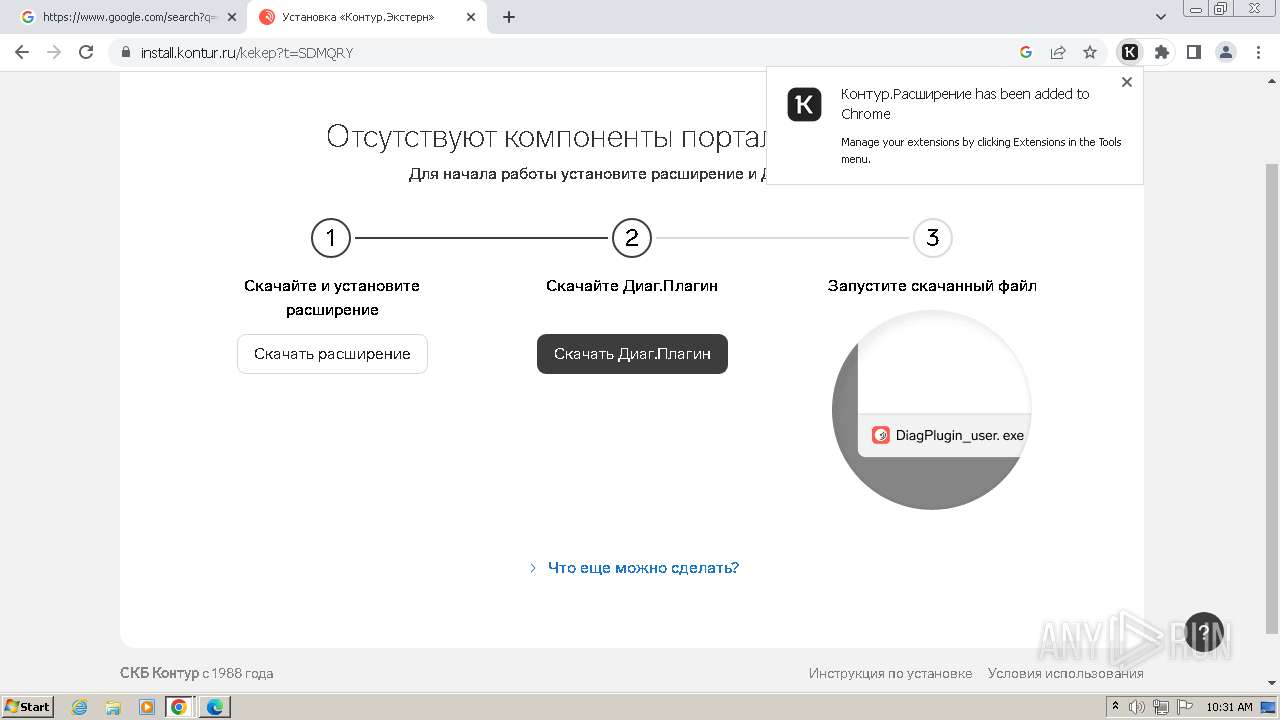
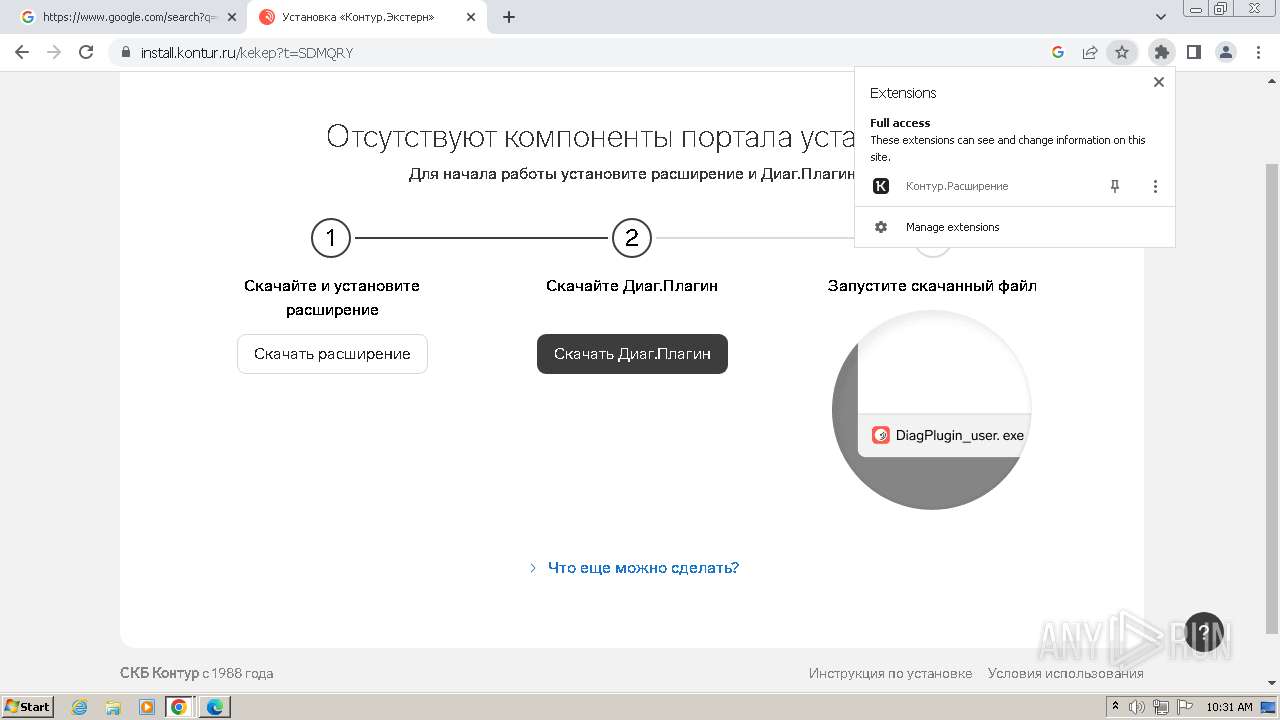
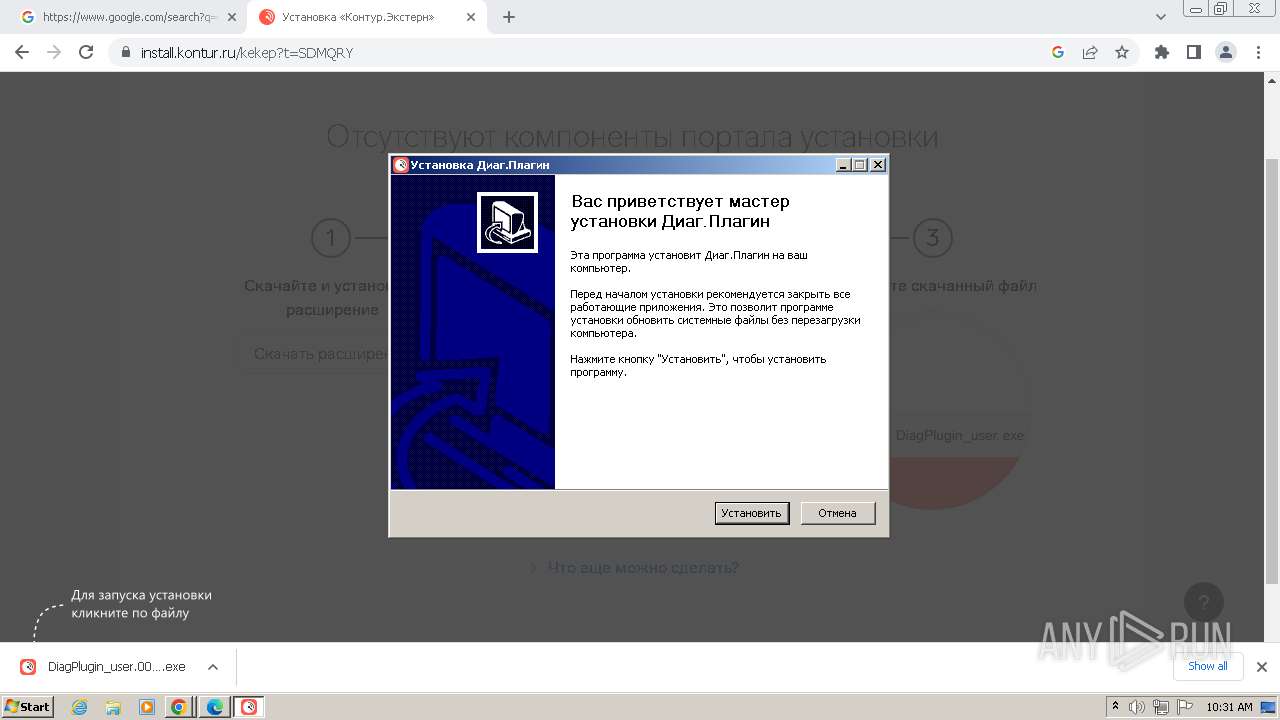
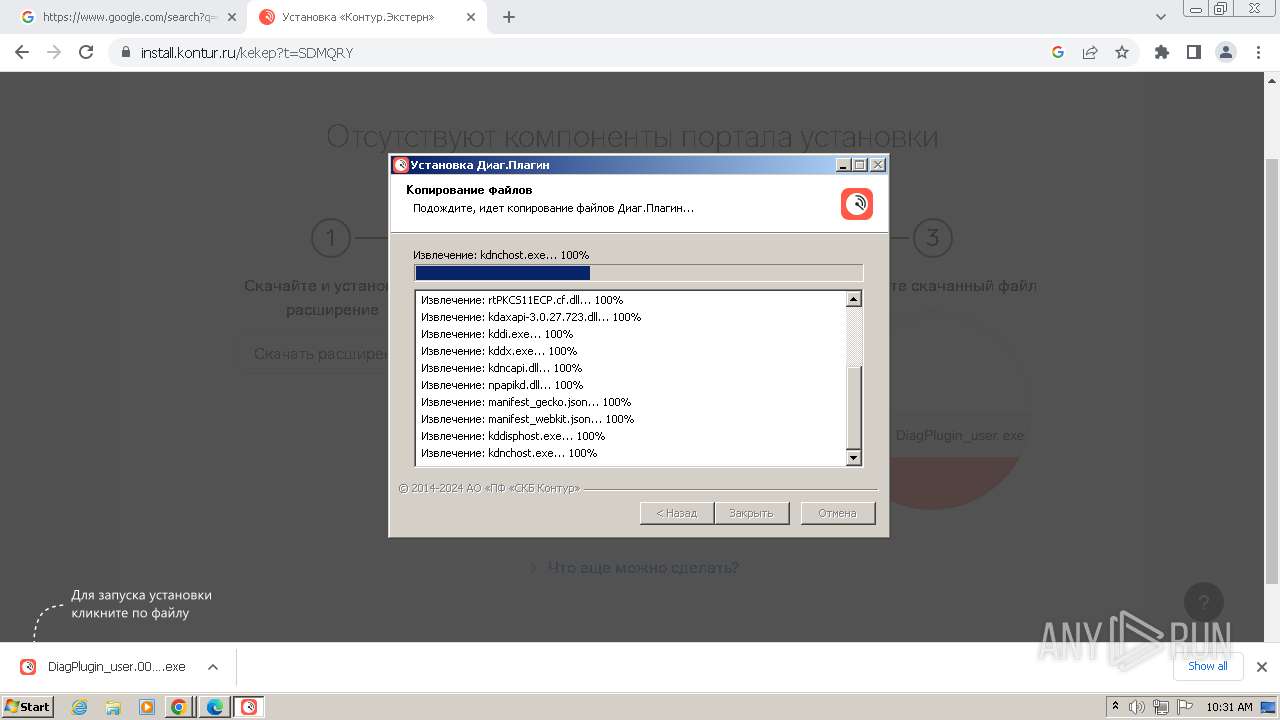
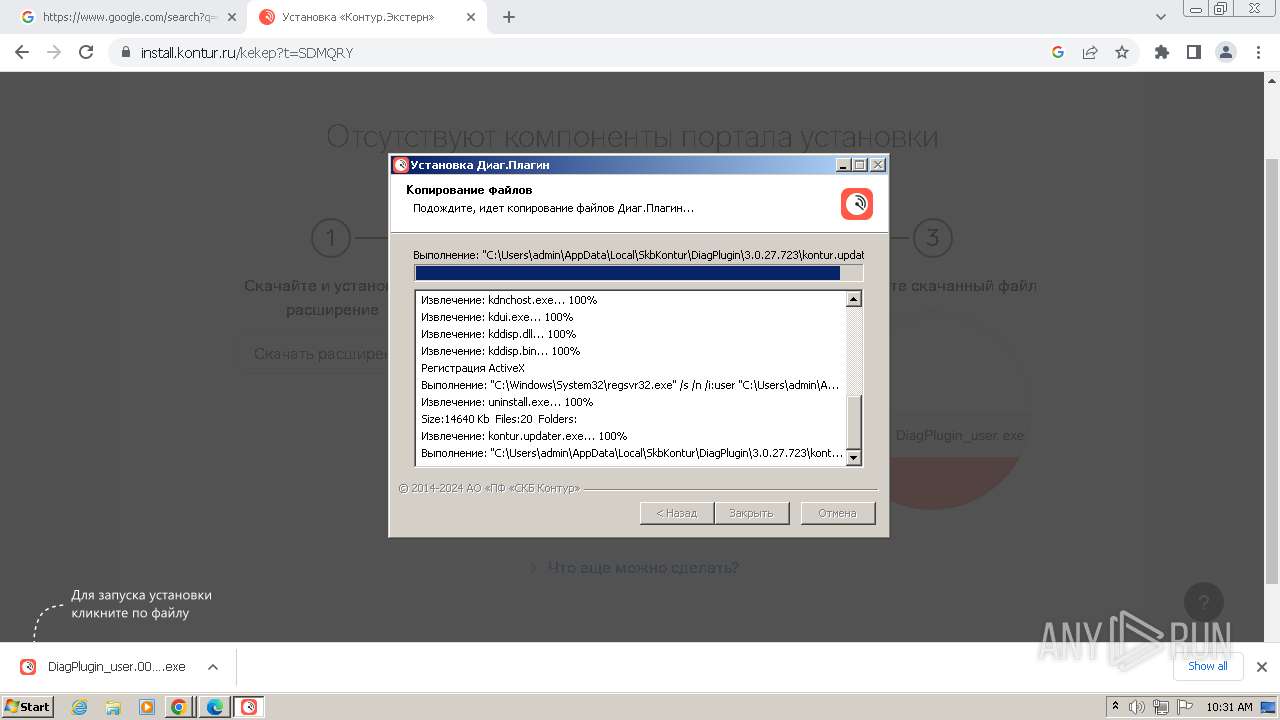
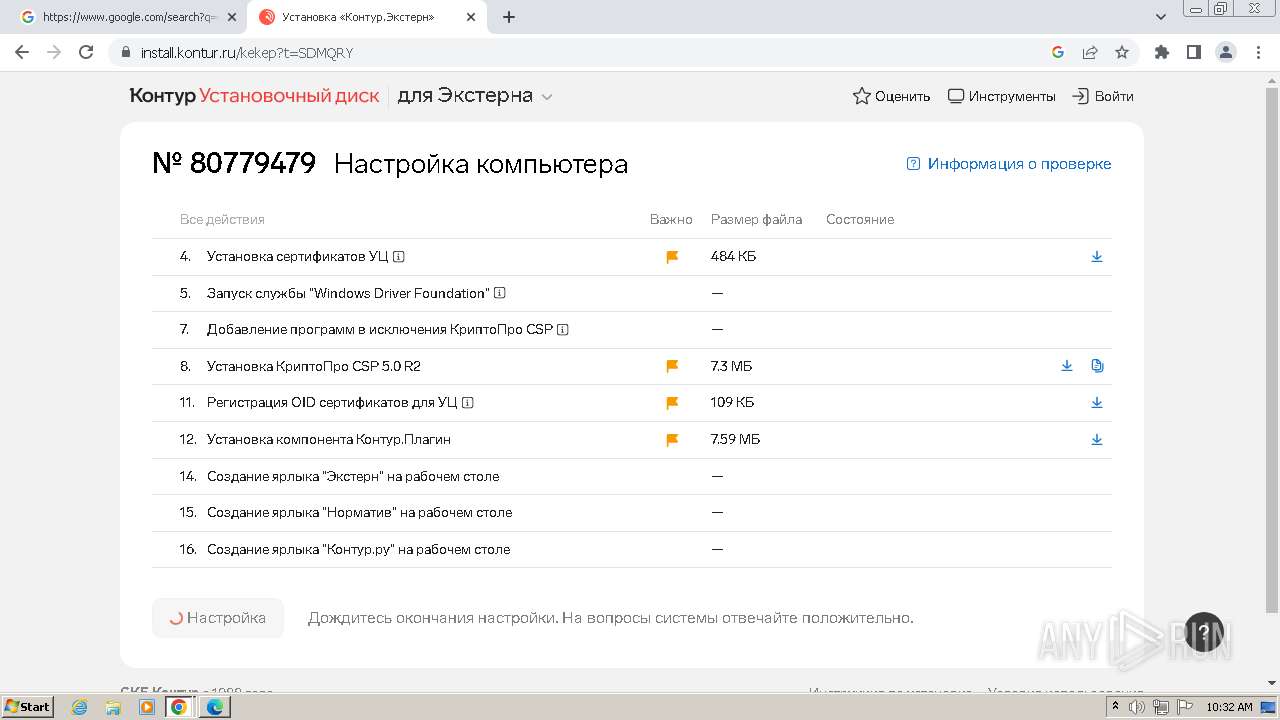
Drops the executable file immediately after the start
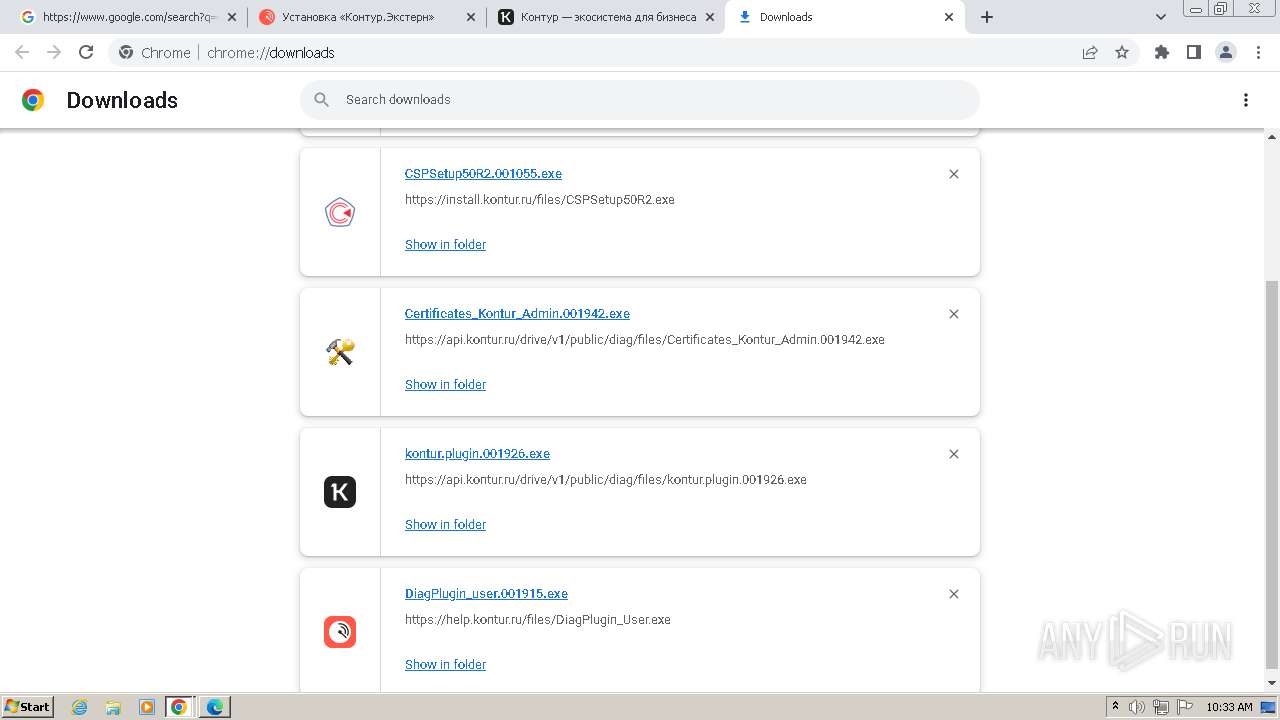
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- kdnchost.exe (PID: 3248)
- RegOids.exe (PID: 2340)
- CSPSetup50R2.exe (PID: 2824)
- msiexec.exe (PID: 3464)
- msiexec.exe (PID: 2852)
- drvinst.exe (PID: 1532)
- kontur.plugin.exe (PID: 5264)
Registers / Runs the DLL via REGSVR32.EXE
- DiagPlugin_user.001915.exe (PID: 336)
Starts CMD.EXE for commands execution
- chrome.exe (PID: 2616)
Actions looks like stealing of personal data
- kdnchost.exe (PID: 3248)
Steals credentials from Web Browsers
- kdnchost.exe (PID: 3248)
Creates a writable file in the system directory
- msiexec.exe (PID: 2852)
- drvinst.exe (PID: 1532)
- msiexec.exe (PID: 3464)
Reads a specific registry key of the VM
- msiexec.exe (PID: 2852)
SUSPICIOUS
The process creates files with name similar to system file names
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- RegOids.exe (PID: 2340)
- kontur.plugin.exe (PID: 5264)
Malware-specific behavior (creating "System.dll" in Temp)
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- RegOids.exe (PID: 2340)
- kontur.plugin.exe (PID: 5264)
Executable content was dropped or overwritten
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- CSPSetup50R2.exe (PID: 2824)
- kdnchost.exe (PID: 3248)
- RegOids.exe (PID: 2340)
- drvinst.exe (PID: 1532)
- kontur.plugin.exe (PID: 5264)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 952)
- msiexec.exe (PID: 2304)
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 3464)
- kontur.plugin.exe (PID: 5264)
Creates a software uninstall entry
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.plugin.exe (PID: 5264)
Starts application with an unusual extension
- kontur.updater.exe (PID: 3364)
- kontur.plugin.exe (PID: 5264)
Changes internet zones settings
- DiagPlugin_user.001915.exe (PID: 336)
The executable file from the user directory is run by the CMD process
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3248)
- kdnchost.exe (PID: 3008)
- kontur.plugin.host.exe (PID: 5596)
Checks Windows Trust Settings
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- kddisphost.exe (PID: 3700)
- msiexec.exe (PID: 2852)
- drvinst.exe (PID: 1532)
Reads security settings of Internet Explorer
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- kddisphost.exe (PID: 3700)
Reads the Internet Settings
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- kddisphost.exe (PID: 3700)
Reads settings of System Certificates
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- CertFix_Host.exe (PID: 1696)
- kddisphost.exe (PID: 3700)
- Certificates_Kontur_Admin.exe (PID: 3372)
Adds/modifies Windows certificates
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3248)
- CertFix_Host.exe (PID: 1696)
- kddisphost.exe (PID: 3700)
- Certificates_Kontur_Admin.exe (PID: 3372)
- msiexec.exe (PID: 2852)
- Setup.exe (PID: 3972)
- msiexec.exe (PID: 3464)
Searches for installed software
- kdnchost.exe (PID: 3248)
Reads the Windows owner or organization settings
- kdnchost.exe (PID: 3248)
- Setup.exe (PID: 3972)
- msiexec.exe (PID: 2852)
Reads Internet Explorer settings
- kdnchost.exe (PID: 3248)
Potential Corporate Privacy Violation
- kdnchost.exe (PID: 3248)
Process drops legitimate windows executable
- CSPSetup50R2.exe (PID: 2824)
Drops a system driver (possible attempt to evade defenses)
- CSPSetup50R2.exe (PID: 2824)
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 3464)
- drvinst.exe (PID: 1532)
Creates files in the driver directory
- drvinst.exe (PID: 1532)
- msiexec.exe (PID: 3464)
Executes as Windows Service
- VSSVC.exe (PID: 2784)
INFO
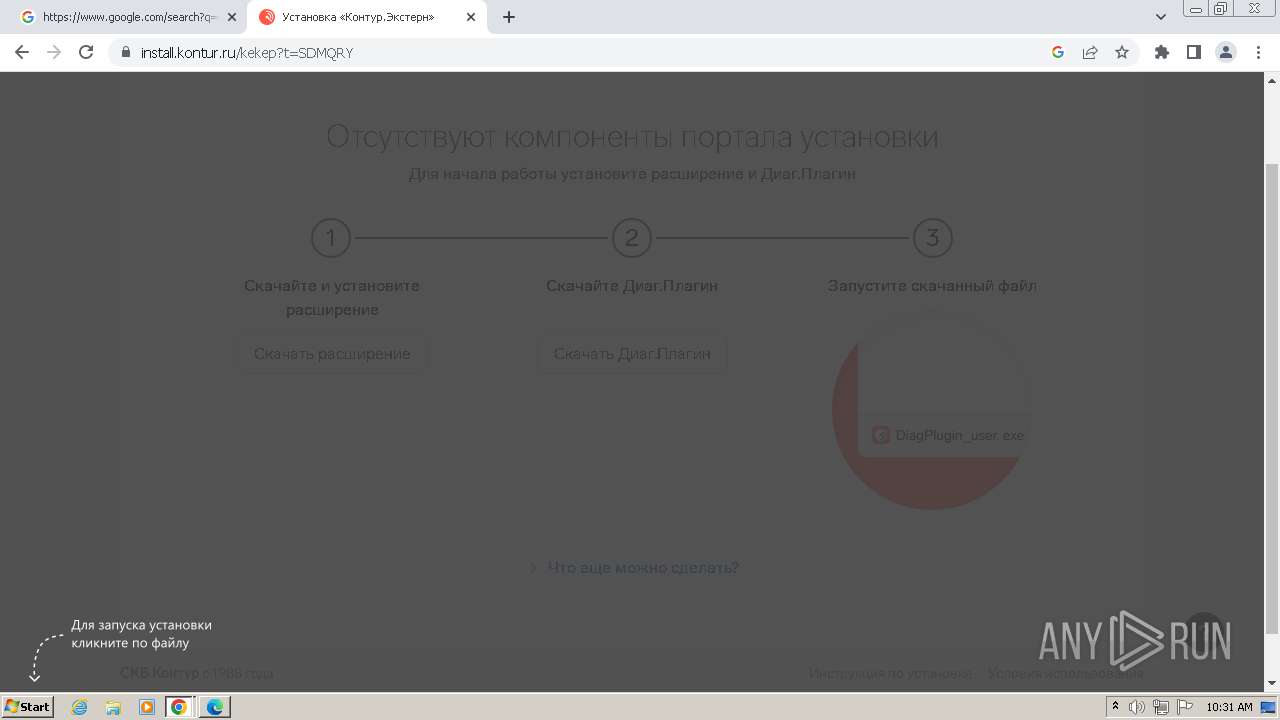
Manual execution by a user
- wmpnscfg.exe (PID: 2172)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 6028)
Checks supported languages
- wmpnscfg.exe (PID: 2172)
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- ns38D0.tmp (PID: 3656)
- ns3852.tmp (PID: 3848)
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- CertFix_Host.exe (PID: 1696)
- kddisphost.exe (PID: 3700)
- Certificates_Kontur_Admin.exe (PID: 3372)
- RegOids.exe (PID: 2340)
- cpverify.exe (PID: 3016)
- CSPSetup50R2.exe (PID: 2824)
- Setup.exe (PID: 3972)
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 2304)
- msiexec.exe (PID: 3464)
- drvinst.exe (PID: 1532)
- cpverify.exe (PID: 4380)
- cpverify.exe (PID: 4280)
- cpverify.exe (PID: 4312)
- cpverify.exe (PID: 4396)
- cpverify.exe (PID: 4368)
- cpverify.exe (PID: 4412)
- csptest.exe (PID: 4860)
- kontur.plugin.exe (PID: 5264)
- cpverify.exe (PID: 4336)
- cpverify.exe (PID: 4300)
- csptest.exe (PID: 4828)
- kontur.updater.exe (PID: 5284)
- ns484B.tmp (PID: 5308)
- ns48C9.tmp (PID: 5356)
- ns4BD7.tmp (PID: 5404)
- pkcs11check.exe (PID: 5428)
- ns4CB3.tmp (PID: 5460)
- ns4D21.tmp (PID: 5508)
- pkcs11check.exe (PID: 5488)
- pkcs11check.exe (PID: 5532)
- kontur.plugin.host.exe (PID: 5596)
Application launched itself
- msedge.exe (PID: 3988)
- chrome.exe (PID: 2616)
- msiexec.exe (PID: 2852)
- chrome.exe (PID: 6028)
Reads the computer name
- wmpnscfg.exe (PID: 2172)
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- CertFix_Host.exe (PID: 1696)
- kddisphost.exe (PID: 3700)
- RegOids.exe (PID: 2340)
- Setup.exe (PID: 3972)
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 3464)
- msiexec.exe (PID: 2304)
- drvinst.exe (PID: 1532)
- kontur.plugin.exe (PID: 5264)
- kontur.updater.exe (PID: 5284)
- pkcs11check.exe (PID: 5428)
- pkcs11check.exe (PID: 5532)
- kontur.plugin.host.exe (PID: 5596)
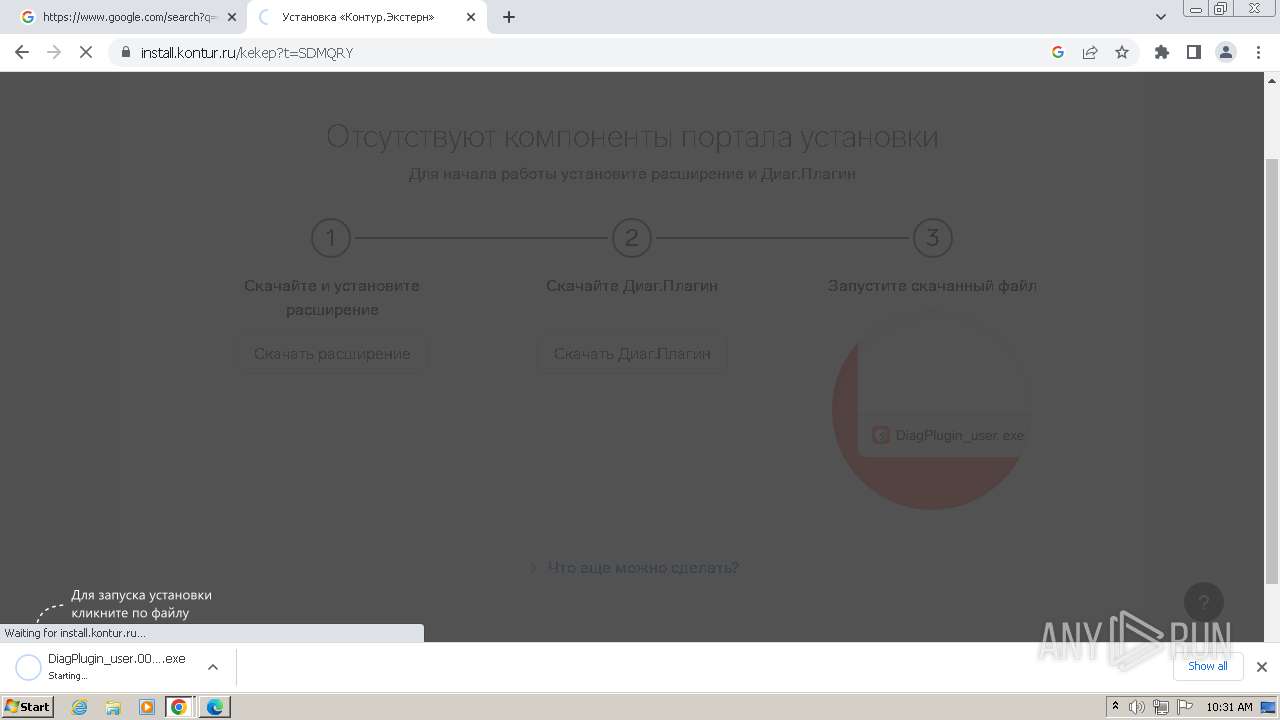
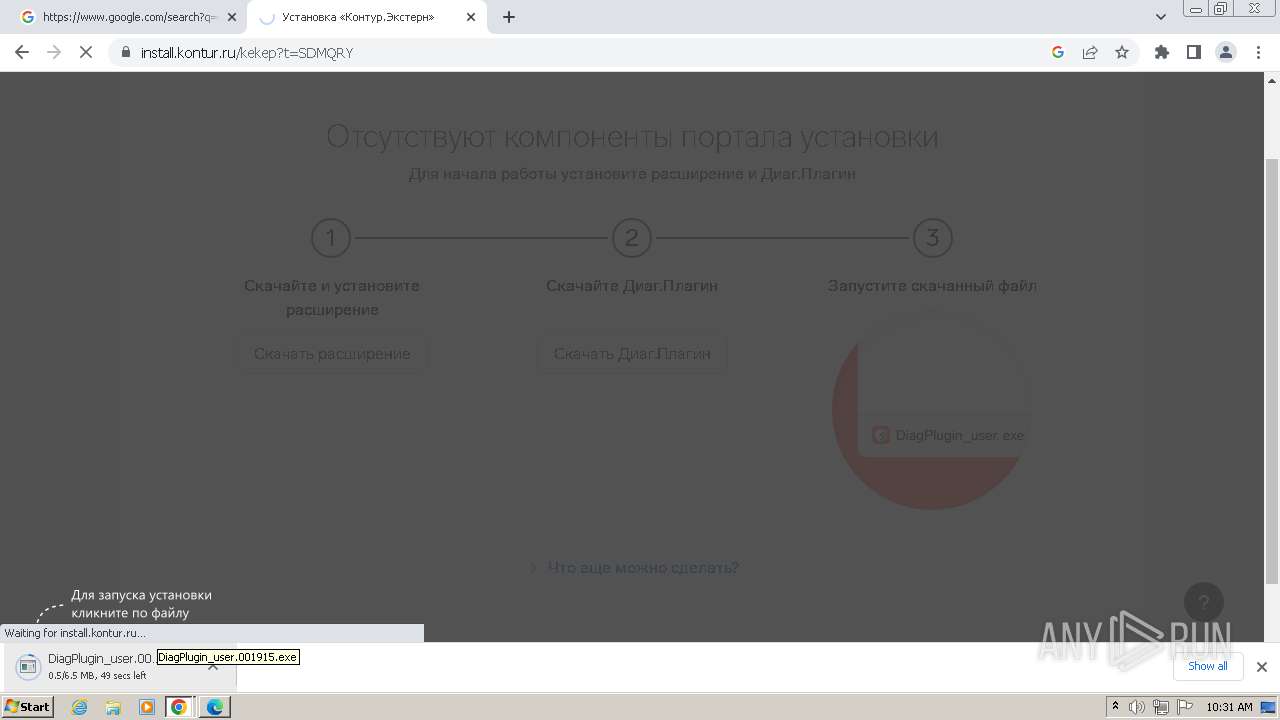
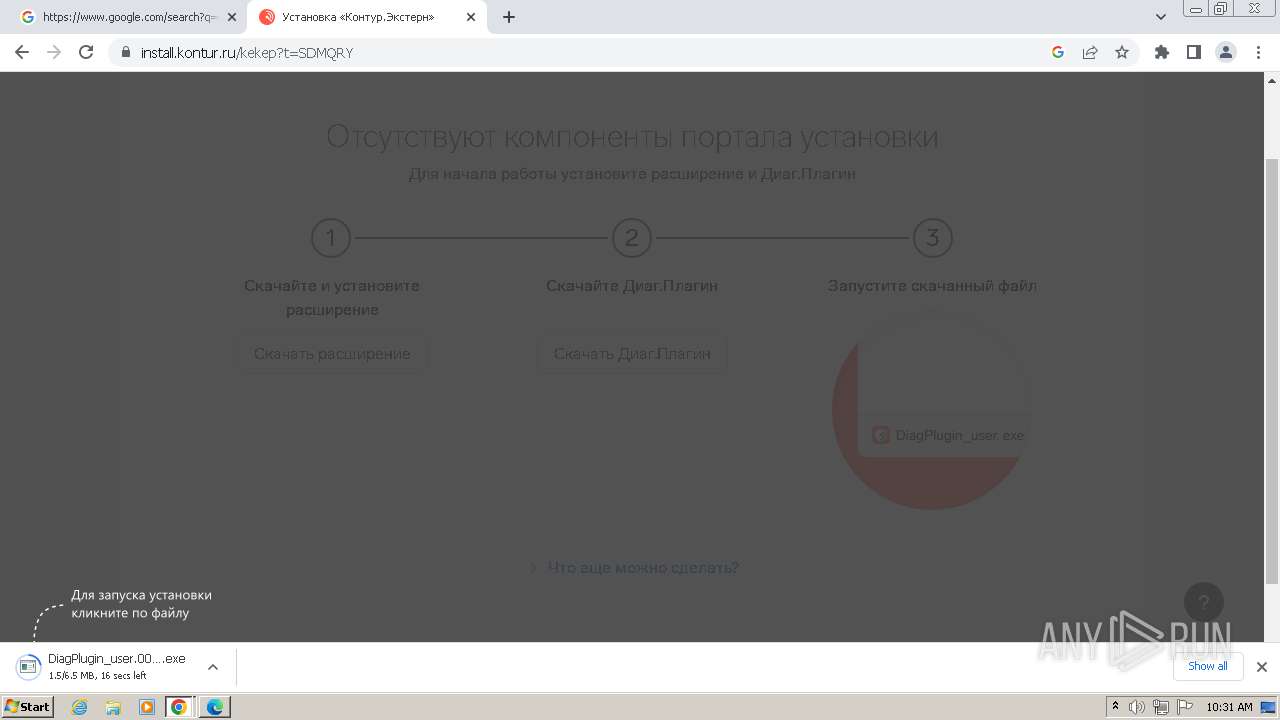
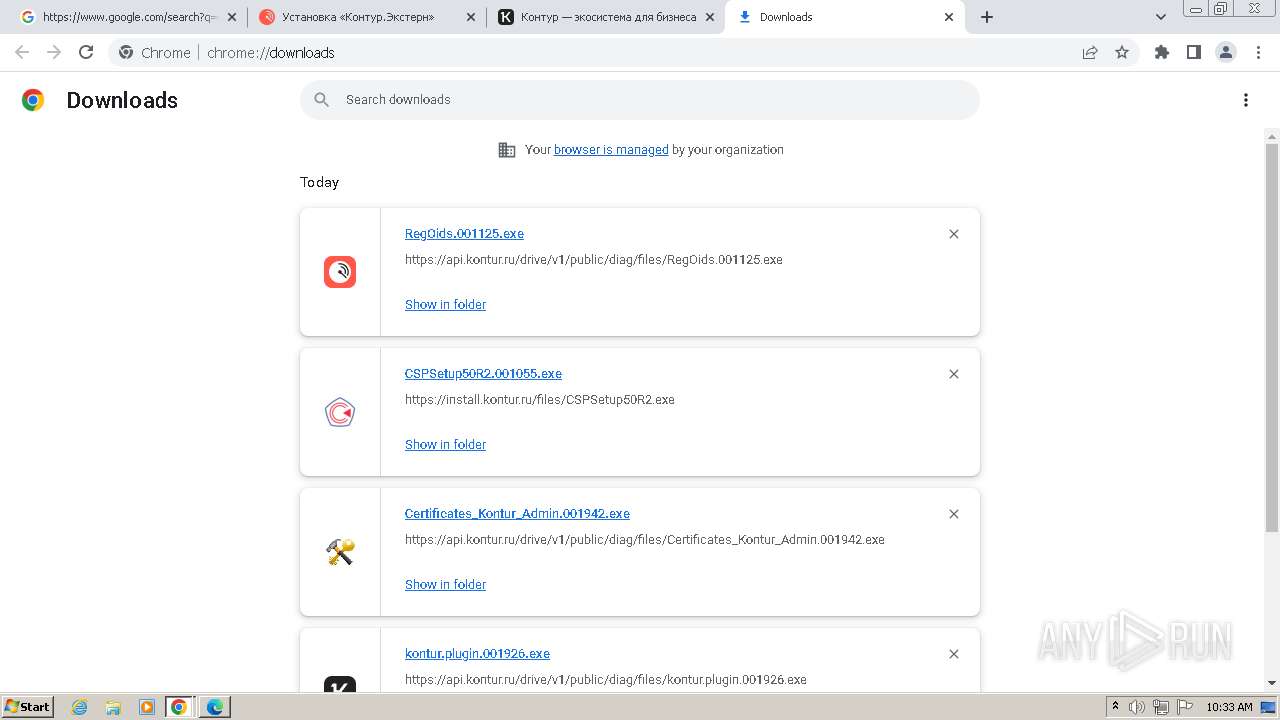
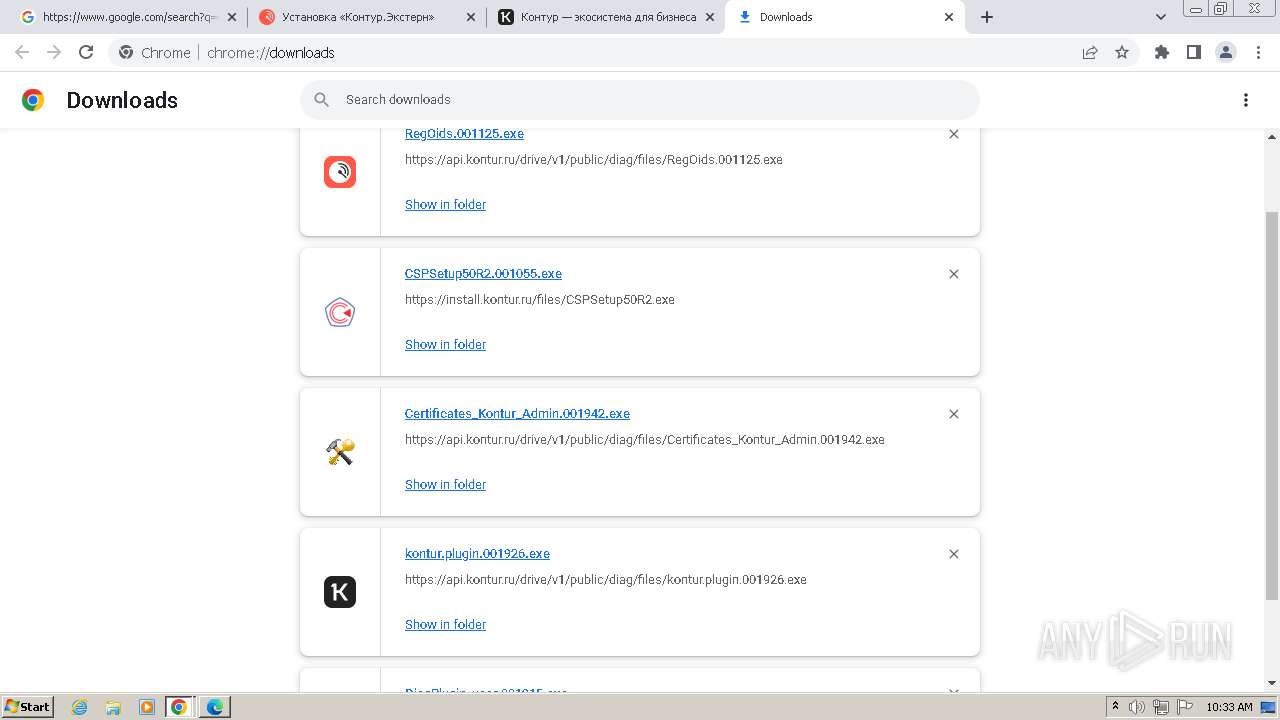
The process uses the downloaded file
- chrome.exe (PID: 2616)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 324)
Executable content was dropped or overwritten
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2732)
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 3464)
Drops the executable file immediately after the start
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2732)
Create files in a temporary directory
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- kdnchost.exe (PID: 3248)
- CertFix_Host.exe (PID: 1696)
- kddisphost.exe (PID: 3700)
- RegOids.exe (PID: 2340)
- msiexec.exe (PID: 3472)
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 3464)
- kontur.plugin.exe (PID: 5264)
- kontur.updater.exe (PID: 5284)
- kontur.plugin.host.exe (PID: 5596)
Creates files or folders in the user directory
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- kdnchost.exe (PID: 3248)
- kontur.plugin.exe (PID: 5264)
Reads Environment values
- DiagPlugin_user.001915.exe (PID: 336)
- kontur.updater.exe (PID: 3364)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- kontur.plugin.exe (PID: 5264)
- kontur.updater.exe (PID: 5284)
Reads the machine GUID from the registry
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- CertFix_Host.exe (PID: 1696)
- kddisphost.exe (PID: 3700)
- Setup.exe (PID: 3972)
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 3464)
- msiexec.exe (PID: 2304)
- drvinst.exe (PID: 1532)
Reads the software policy settings
- kdnchost.exe (PID: 3408)
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- CertFix_Host.exe (PID: 1696)
- kddisphost.exe (PID: 3700)
- msiexec.exe (PID: 2852)
- drvinst.exe (PID: 1532)
Process checks whether UAC notifications are on
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
- kddisphost.exe (PID: 3700)
Reads product name
- kdnchost.exe (PID: 3008)
- kdnchost.exe (PID: 3248)
Reads CPU info
- kdnchost.exe (PID: 3248)
Checks proxy server information
- kdnchost.exe (PID: 3248)
Process checks Internet Explorer phishing filters
- kdnchost.exe (PID: 3248)
Creates files in the program directory
- CSPSetup50R2.exe (PID: 2824)
Creates a software uninstall entry
- msiexec.exe (PID: 3464)
- msiexec.exe (PID: 2852)
Reads Microsoft Office registry keys
- msiexec.exe (PID: 2852)
Adds/modifies Windows certificates
- drvinst.exe (PID: 1532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
198
Monitored processes
137
Malicious processes
18
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4576 --field-trial-handle=1168,i,3993000143496483049,12472391293687733067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4260 --field-trial-handle=1168,i,3993000143496483049,12472391293687733067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4748 --field-trial-handle=1168,i,3993000143496483049,12472391293687733067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 336 | "C:\Users\admin\Downloads\DiagPlugin_user.001915.exe" | C:\Users\admin\Downloads\DiagPlugin_user.001915.exe | chrome.exe | ||||||||||||
User: admin Company: АО «ПФ «СКБ Контур» Integrity Level: MEDIUM Description: Установка Диаг.Плагин Exit code: 0 Version: 3.0.27.723 Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4484 --field-trial-handle=1168,i,3993000143496483049,12472391293687733067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2236 --field-trial-handle=1168,i,3993000143496483049,12472391293687733067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1076 --field-trial-handle=1168,i,3993000143496483049,12472391293687733067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 952 | "C:\Windows\System32\regsvr32.exe" /s /n /i:user "C:\Users\admin\AppData\Local\SkbKontur\DiagPlugin\3.0.27.723\kdaxapi-3.0.27.723.dll" | C:\Windows\System32\regsvr32.exe | — | DiagPlugin_user.001915.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=5072 --field-trial-handle=1168,i,3993000143496483049,12472391293687733067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3524 --field-trial-handle=1232,i,5675037518379154068,1311549252598336498,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
180 346
Read events
176 232
Write events
3 306
Delete events
808
Modification events
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 28B5DD4639772F00 | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3988) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
349
Suspicious files
541
Text files
171
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\c1d58f68-c546-4a8f-b60a-161b51058af3.tmp | — | |
MD5:— | SHA256:— | |||
| 3988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1044ea.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF104529.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF104632.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:A6EBC0D32A7B9304824D19DB63B4E37A | SHA256:E991057C2B1718A151C5FD06E1C153F57130D195454A1F94C8C4C20971697093 | |||
| 4012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma~RF1039af.TMP | binary | |
MD5:886E82F2CA62ECCCE64601B30592078A | SHA256:E5E13D53601100FF3D6BB71514CBCCC4C73FE9B7EF5E930100E644187B42948E | |||
| 4012 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:C612E96CBFAC63232FC2062E15600FB1 | SHA256:DB3C05D5EC0B6719A73E7F0BE84BCE9342772DA70567E7CE08CF6573480B38FF | |||
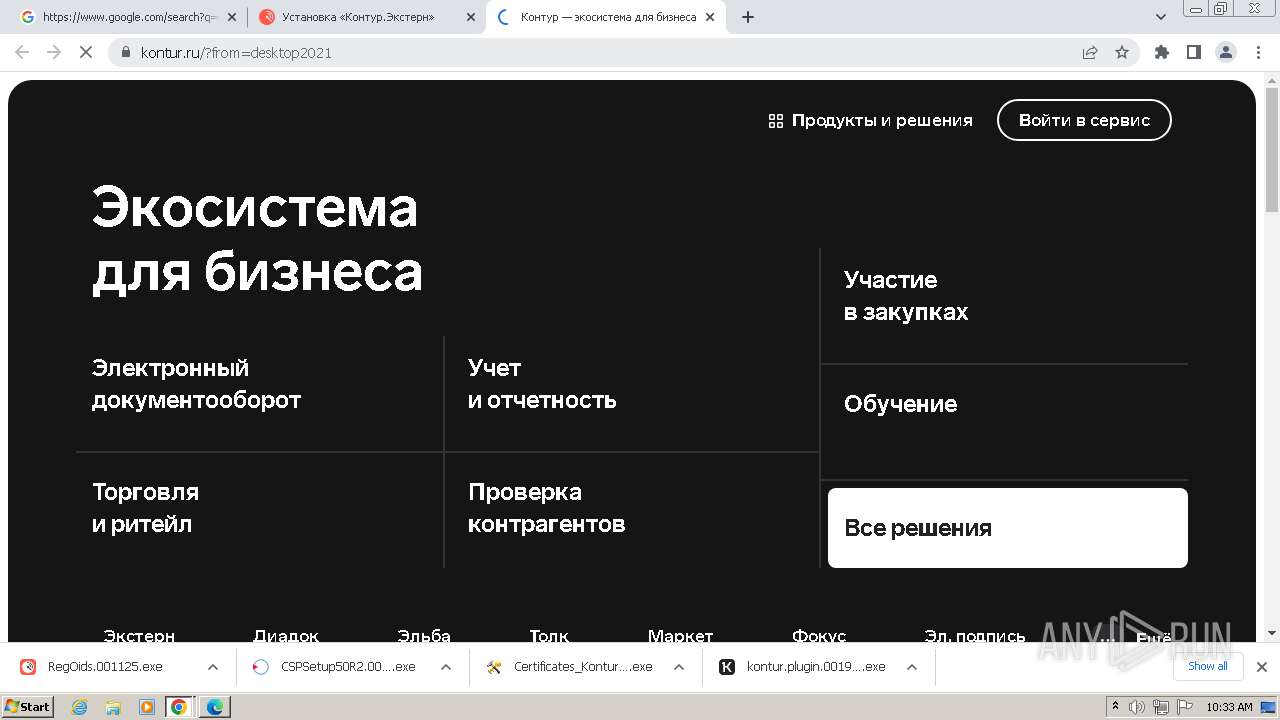
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
205
DNS requests
238
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1696 | CertFix_Host.exe | GET | 404 | 149.126.77.156:80 | http://fedir.comsign.co.il/crl/ComSignSecuredCA.crl | DE | html | 1.35 Kb | unknown |
1696 | CertFix_Host.exe | GET | 200 | 104.18.38.233:80 | http://crl.usertrust.com/UTN-USERFirst-Object.crl | unknown | binary | 74.4 Kb | unknown |
1696 | CertFix_Host.exe | GET | 200 | 212.62.45.130:80 | http://sertifikati.ca.posta.rs/crl/PostaCARoot.crl | RS | binary | 1.05 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 10.3 Kb | unknown |
2616 | chrome.exe | GET | 200 | 104.18.21.226:80 | http://secure.globalsign.com/cacert/codesigningrootr45.crt | unknown | binary | 1.37 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 5.98 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 5.40 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 12.5 Kb | unknown |
2616 | chrome.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?176c1fff8b810343 | US | compressed | 68.3 Kb | unknown |
1696 | CertFix_Host.exe | GET | 200 | 193.150.24.51:80 | http://crl2.postsignum.cz/crl/psrootqca4.crl | CZ | binary | 776 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2036 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3988 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
2036 | msedge.exe | 46.17.203.51:443 | install.kontur.ru | JSC SKB Kontur production | RU | unknown |
2036 | msedge.exe | 131.253.33.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2036 | msedge.exe | 87.250.250.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
2036 | msedge.exe | 46.17.203.72:443 | s.kontur.ru | JSC SKB Kontur production | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
install.kontur.ru |
| unknown |
edge.microsoft.com |
| whitelisted |
s.kontur.ru |
| unknown |
mc.yandex.ru |
| whitelisted |
www.bing.com |
| whitelisted |
help.kontur.ru |
| unknown |
tp.kontur.ru |
| unknown |
metrika.kontur.ru |
| unknown |
mc.yandex.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2732 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2732 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2732 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_PROCESS_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
msiexec.exe | <cng>0xa00:UnregisterInterface!BCryptRemoveContextFunctionProvider failed with error code 0xc0000225 (:734)
|