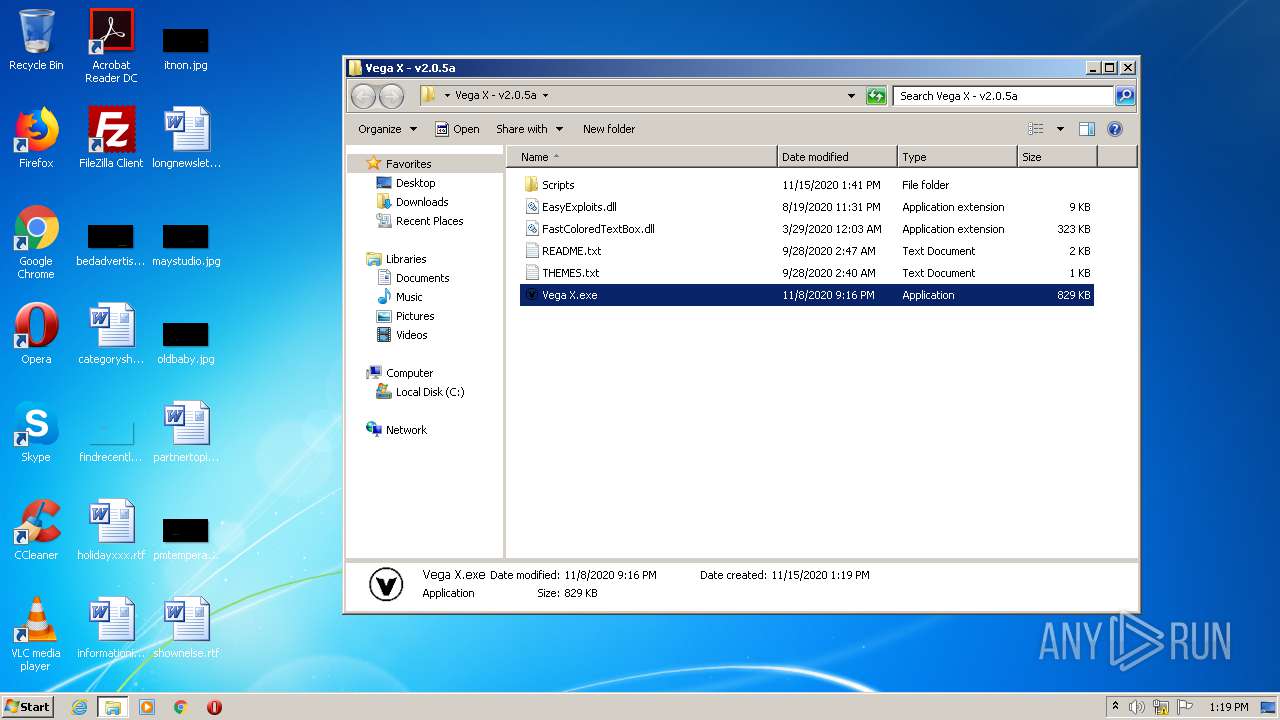
| File name: | Vega X - v2.0.5a.zip |
| Full analysis: | https://app.any.run/tasks/ccda2814-2f0f-4b37-a6a8-01edf6f7270d |
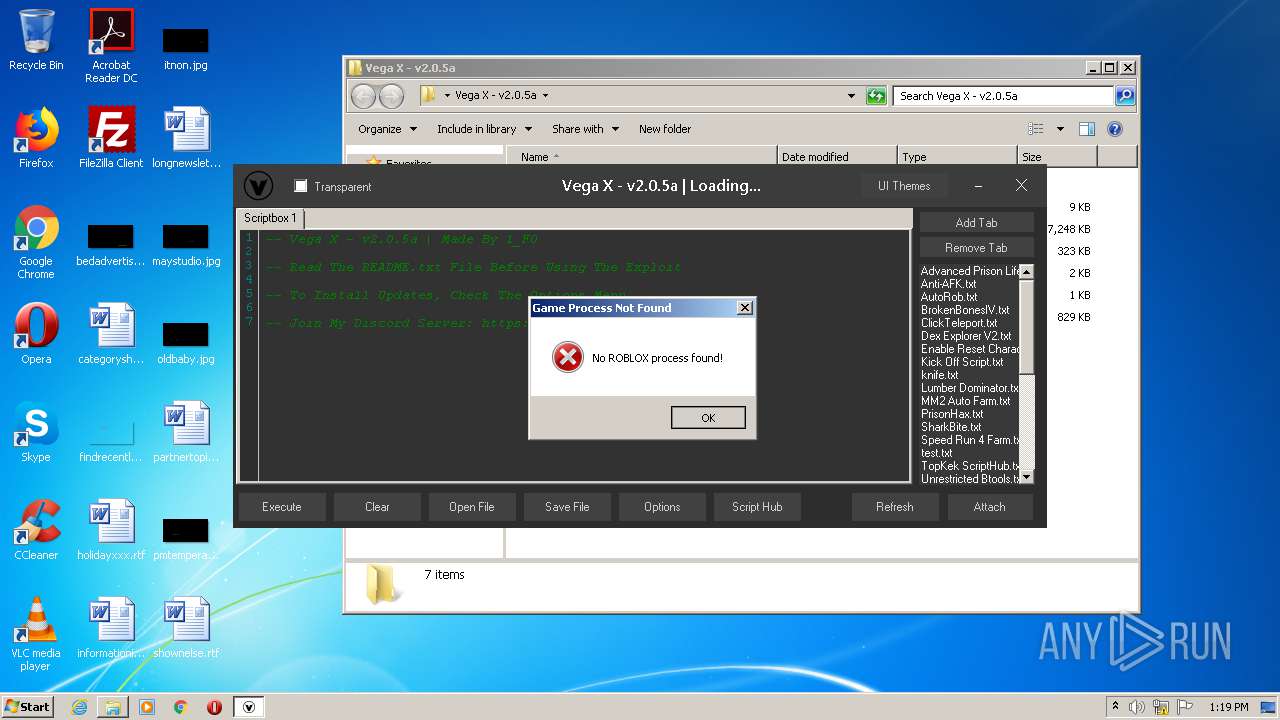
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2020, 13:18:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1CFD932C4C1AC29AF1FF9BF01715D82D |
| SHA1: | 2CAC412811917975B8F1A7D7DCB7B9E0A3284E78 |
| SHA256: | 0E191FBE872625AC5D146C078B416B0FCD1D3372942B8A5D10F3F728E0DBAFE5 |
| SSDEEP: | 24576:ouOvjqr/QJLf0nOYcK4YKi5NEuT9Czxa+TsLhpubfZcT+:oD7J+O2L9Eu8z4+T8puLKq |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3448)
- Vega X.exe (PID: 3308)
Changes settings of System certificates
- Vega X.exe (PID: 3308)
Application was dropped or rewritten from another process
- Vega X.exe (PID: 3308)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1228)
- Vega X.exe (PID: 3308)
Reads Environment values
- Vega X.exe (PID: 3308)
Adds / modifies Windows certificates
- Vega X.exe (PID: 3308)
INFO
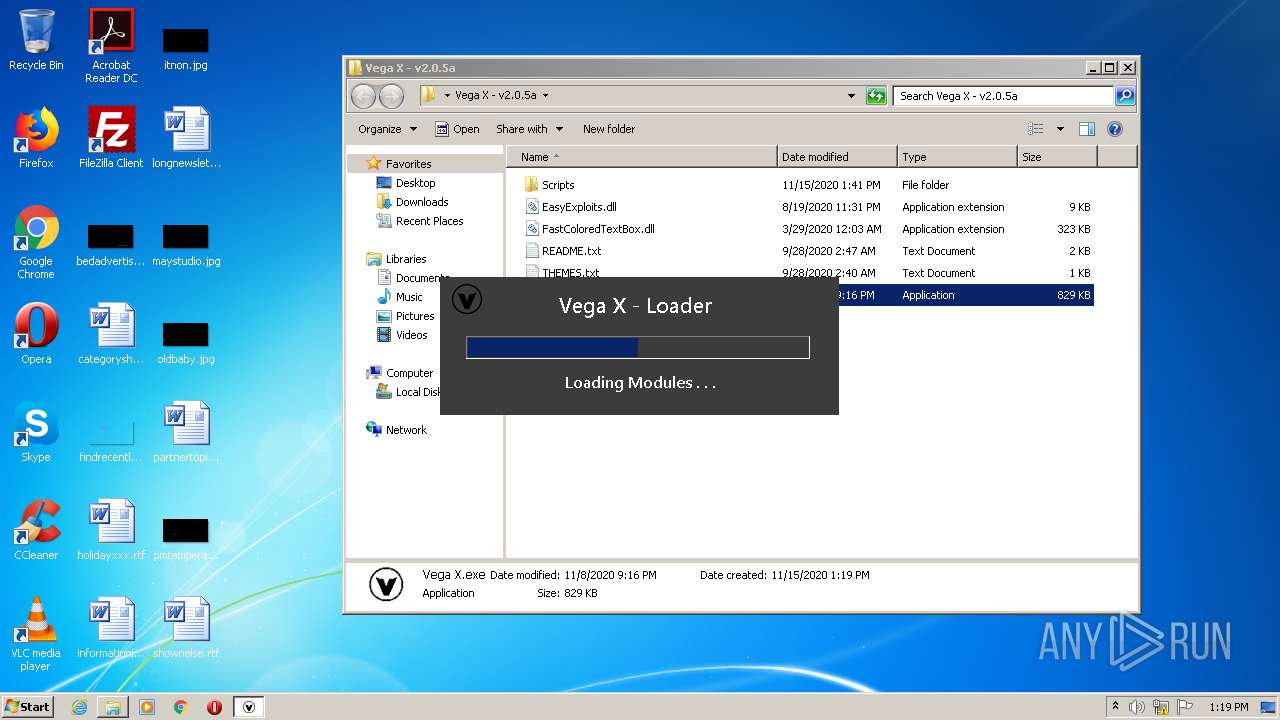
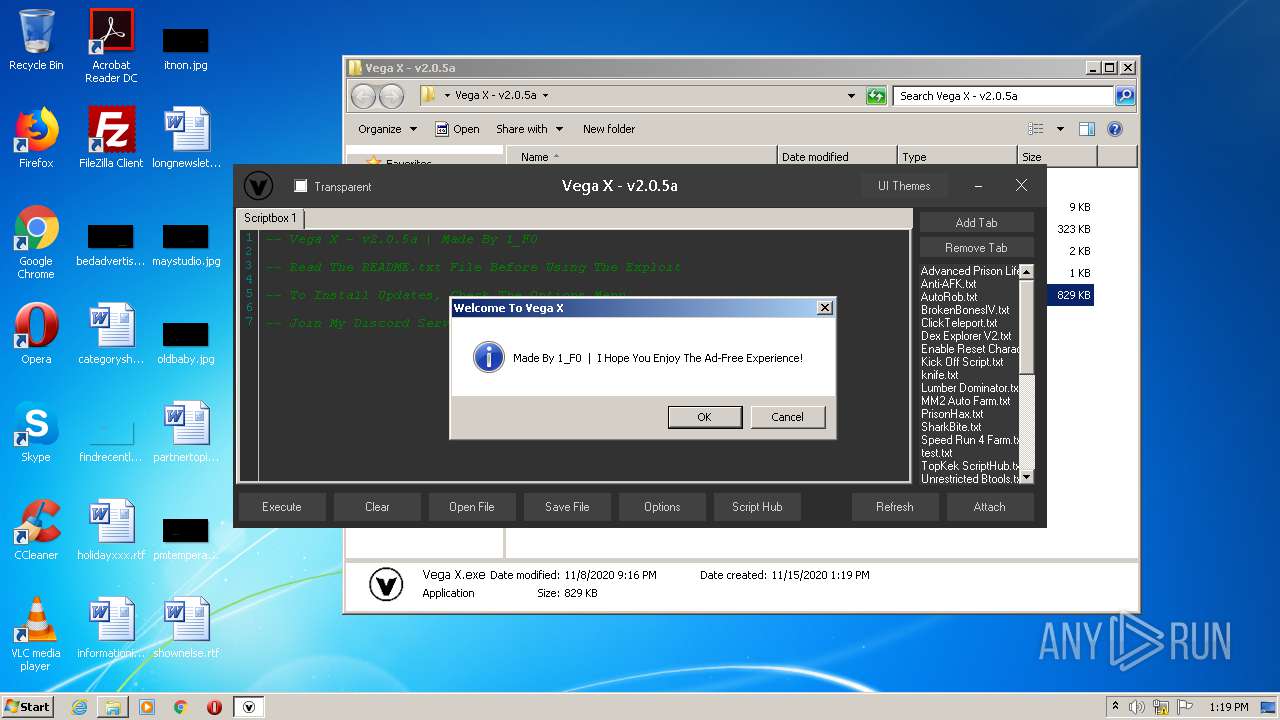
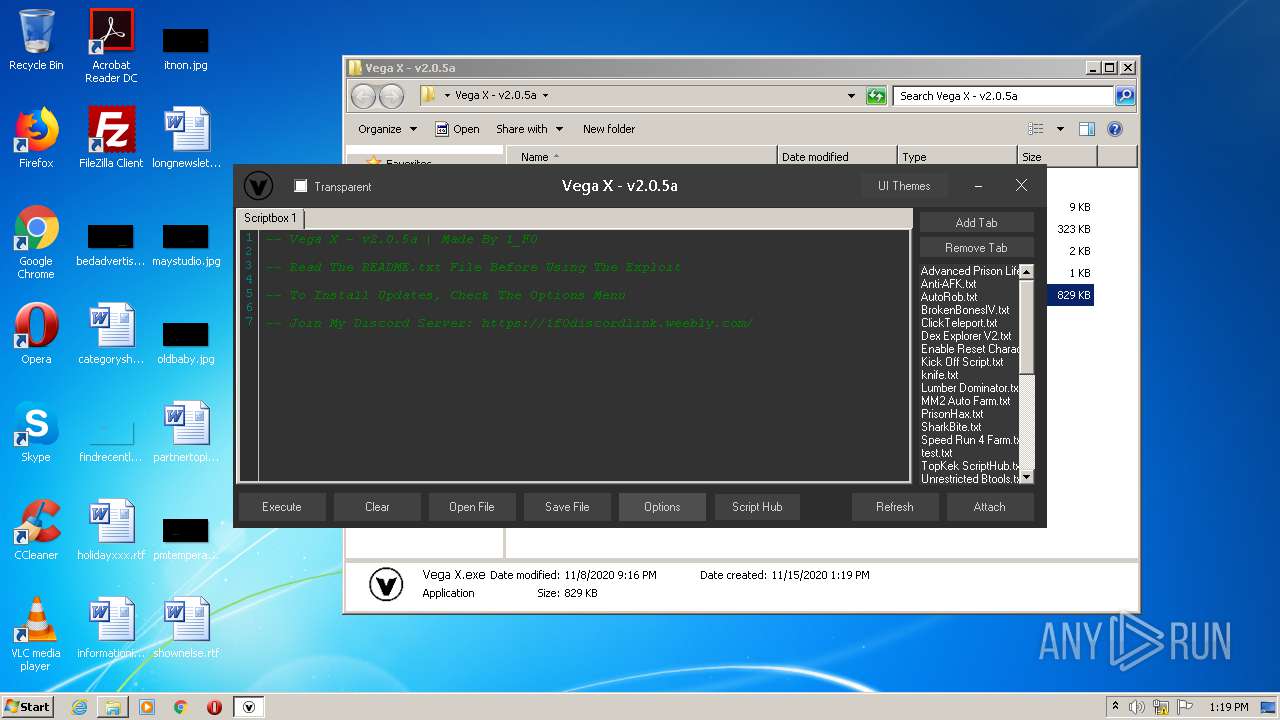
Manual execution by user
- Vega X.exe (PID: 3308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:08:19 23:31:01 |
| ZipCRC: | 0x7060561d |
| ZipCompressedSize: | 4392 |
| ZipUncompressedSize: | 9216 |
| ZipFileName: | Vega X - v2.0.5a/EasyExploits.dll |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
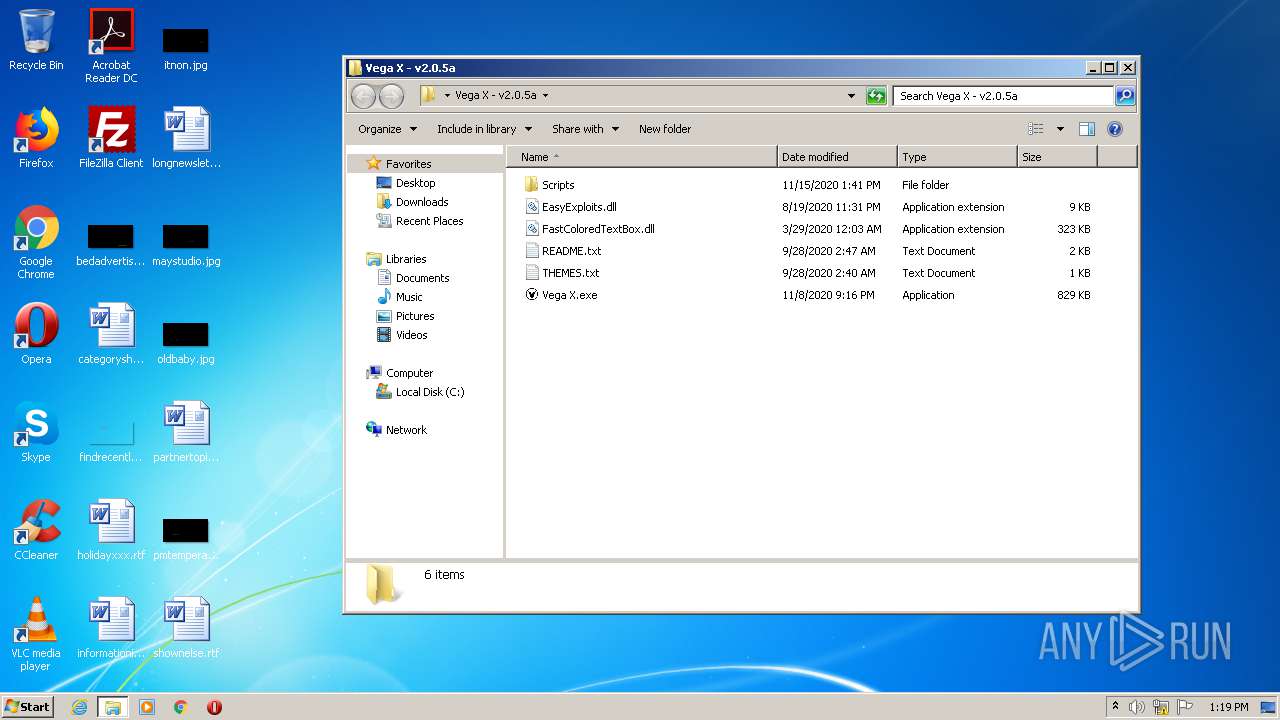
| 1228 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Vega X - v2.0.5a.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3308 | "C:\Users\admin\Desktop\Vega X - v2.0.5a\Vega X.exe" | C:\Users\admin\Desktop\Vega X - v2.0.5a\Vega X.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Vega X Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3448 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
849
Read events
796
Write events
50
Delete events
3
Modification events
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Vega X - v2.0.5a.zip | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (1228) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
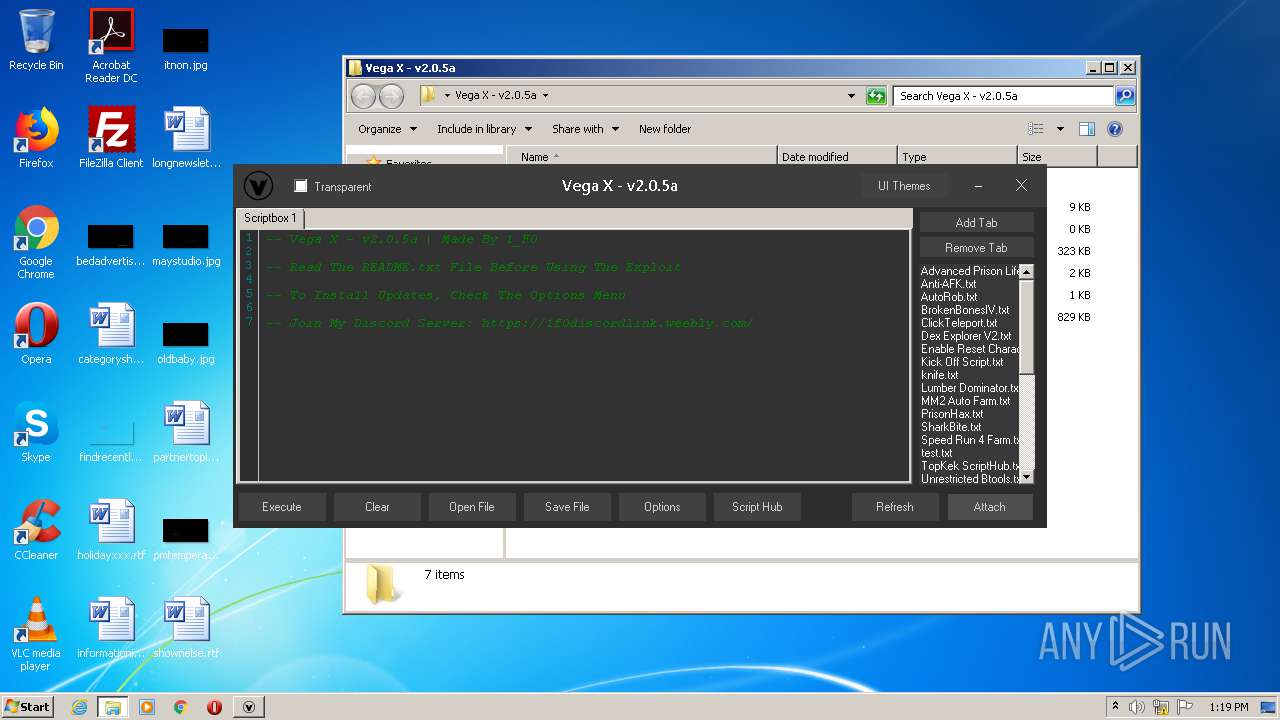
Executable files
4
Suspicious files
0
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\README.txt | text | |
MD5:— | SHA256:— | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\Scripts\[FE] E to TP.txt | text | |
MD5:4B6E92DB4DEE241F810D35C3DA29A2BD | SHA256:C0AED466EC7038CA10B252DD424FFA70C7B4E5CD9CD22E5C8A8466C1D0D72495 | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\Scripts\FPS Aimlock.lua | text | |
MD5:F0486D7D400D17A29F3A3A0A9EF8828C | SHA256:4B16D7D4542E9C181F98CBCC60976DDE82321F60DA01FE0D452AAA42B446D7F2 | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\Scripts\[[BEST]] Script LIST.txt | text | |
MD5:8B025B44D51561E71AFC4276252CEF82 | SHA256:D52EEFFE3D19BE99C34788B31EB1054D3FA21B068A1D4C2F7BCF43EE5E9F402B | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\FastColoredTextBox.dll | executable | |
MD5:8610F4D3CDC6CC50022FEDDCED9FDAEB | SHA256:AC926C92CCFC3789A5AE571CC4415EB1897D500A79604D8495241C19ACDF01B9 | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\Scripts\Anti-AFK.txt | text | |
MD5:E79F153A0CF5BADDEDD0309AD8177EF2 | SHA256:BF75DF2DD2558A5804E7E2FEAA168064B2DA3EFA652F0355E949117EB198F187 | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\Scripts\BrokenBonesIV.txt | text | |
MD5:328A2D6EE854477896ECDF75E0F1FC6E | SHA256:53F93CE6CBE9EBB909AFABF70A419823AE49B1EB55DFAE77C6C65BECF0466462 | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\Scripts\ClickTeleport.txt | text | |
MD5:CE437BB36FC9E70D7AFE7FE0C967E518 | SHA256:E41E037A673EE7A9846C75030C95B522D1A188F13F71032CF93FF23E10DAEF0D | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\Scripts\Enable Reset Character.txt | text | |
MD5:72AE47DEEEC8069BE19F0A0E2C1A269D | SHA256:E701732CB1F0E5774C9468E09BD8C1D635801AA1AB832CF85F3D4C2D34627420 | |||
| 1228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1228.18146\Vega X - v2.0.5a\Scripts\[FE] Invisible Character.lua | text | |
MD5:7054E4534BEF6396B435F5D5A9CDE9E7 | SHA256:D31901FB5608DD298FC8BAB0266A09DEFFA6E633CADA813CED2338A2A5643219 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
— | — | 162.159.135.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |
cdn.discordapp.com |
| shared |