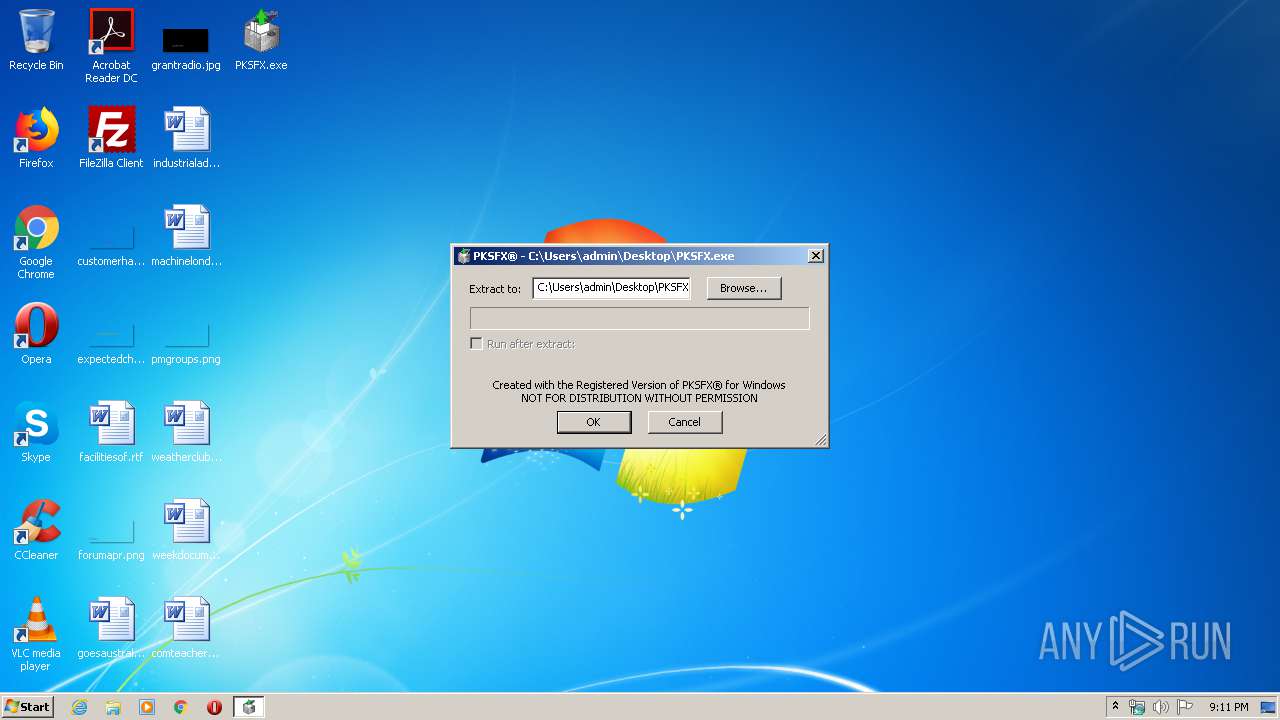
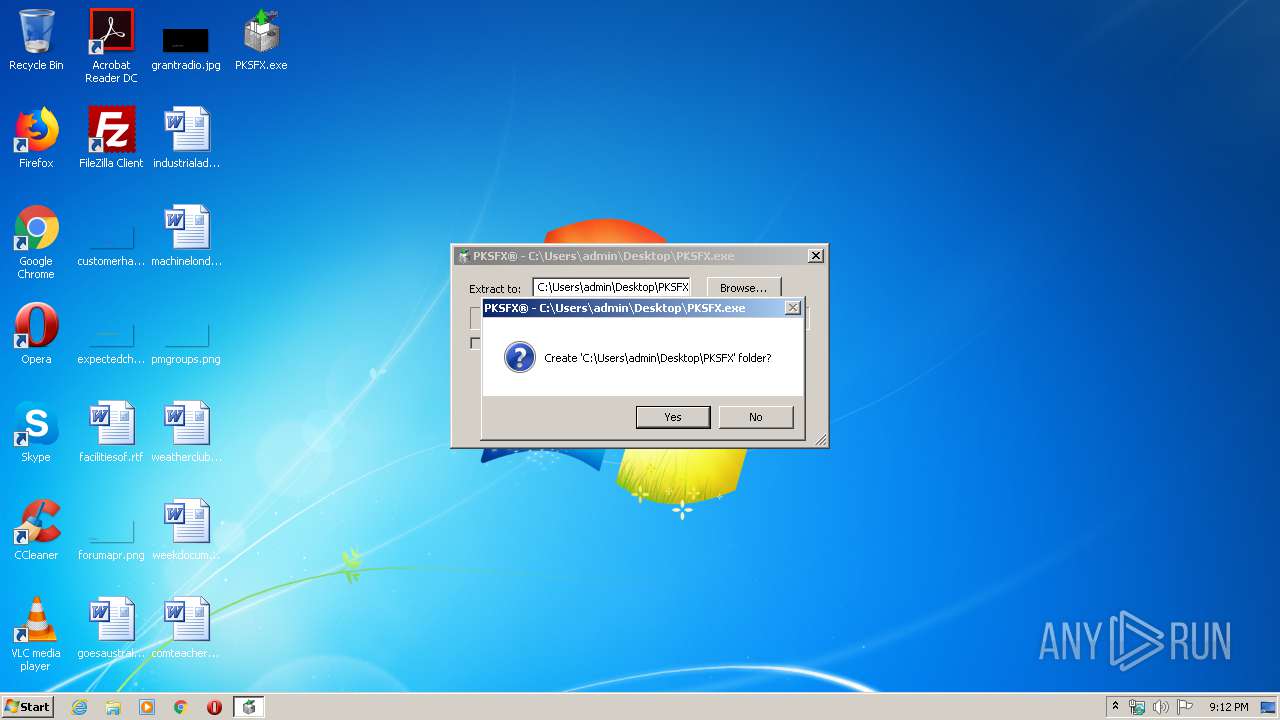
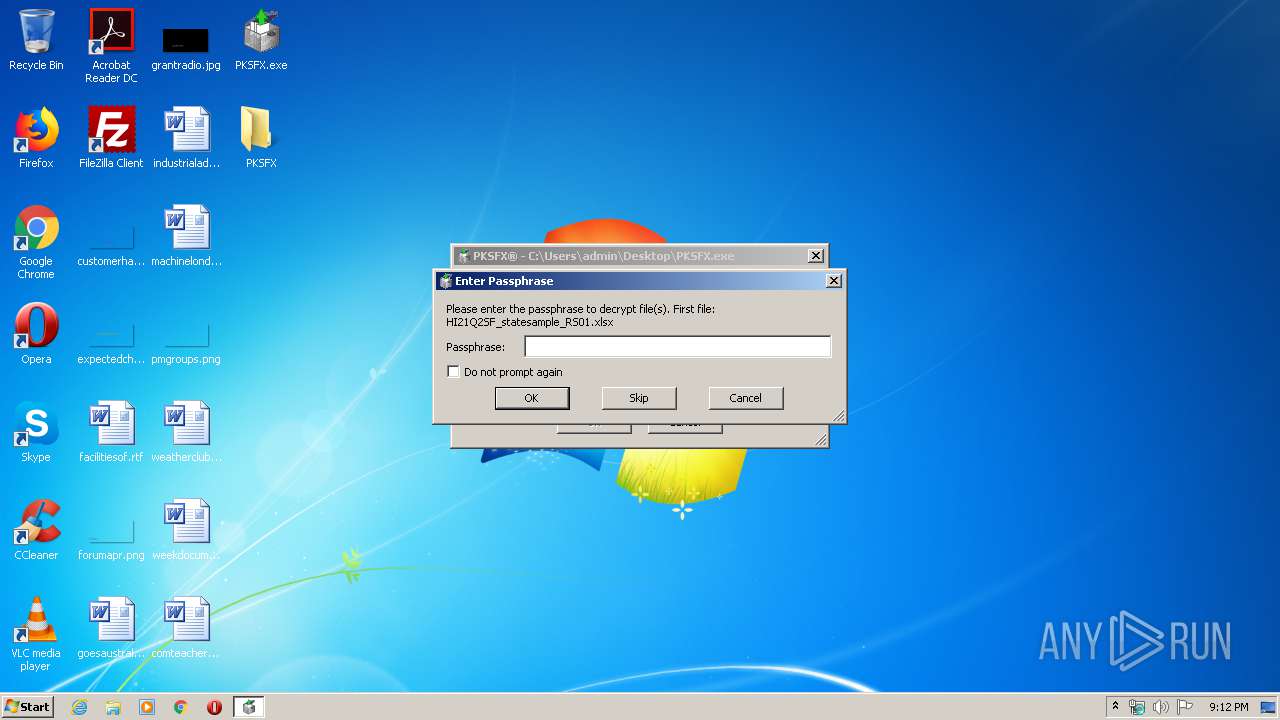
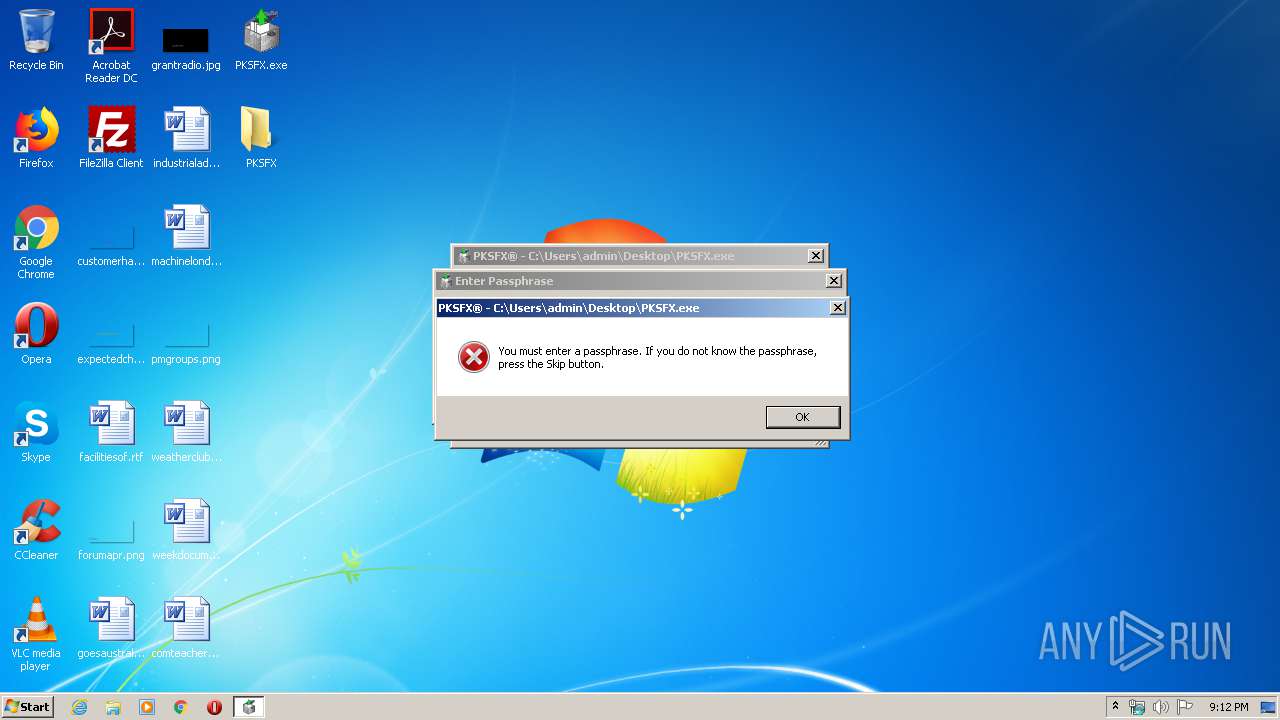
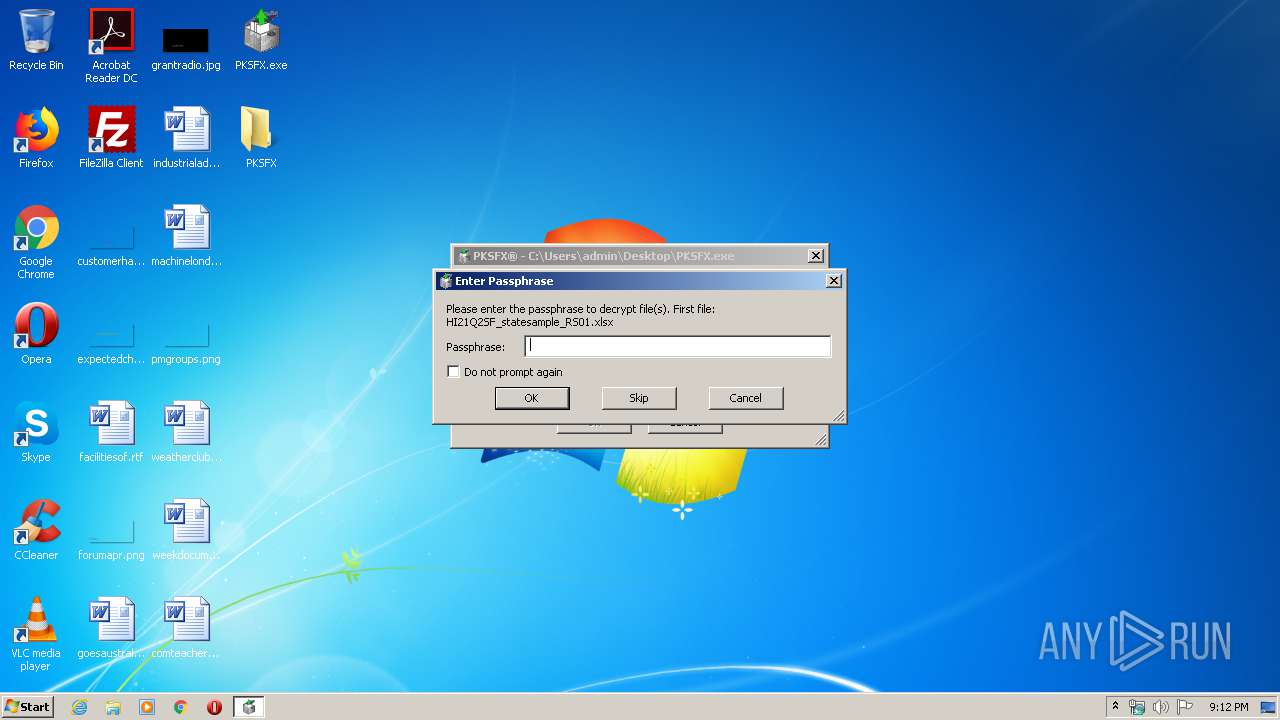
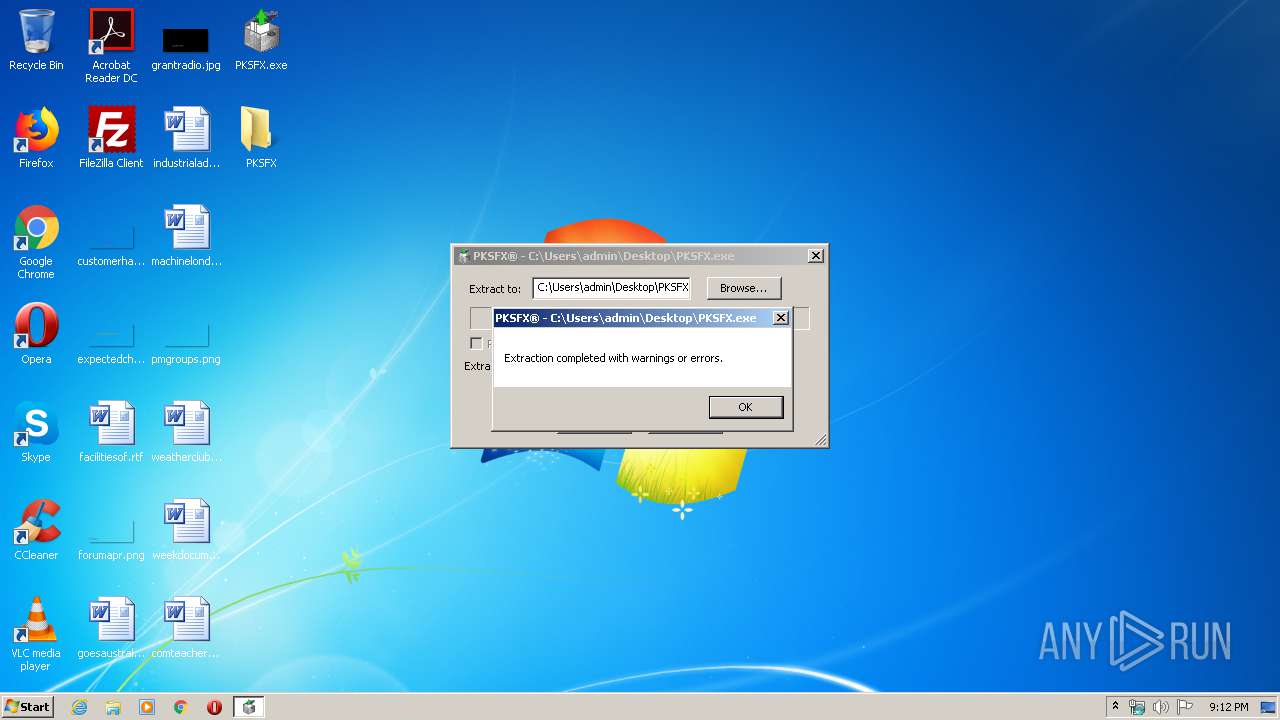
| File name: | PKSFX.exe |
| Full analysis: | https://app.any.run/tasks/2045a3c8-21fb-4264-b84b-c37d035c2a87 |
| Verdict: | No threats detected |
| Analysis date: | March 09, 2020, 21:11:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 13DC33C733FD463624B184D5AAE8D380 |
| SHA1: | 6D36F75025008B7FD6D2DAC0F49BFADBA310F597 |
| SHA256: | 0E18FB9DD810EA253B0A76F81B4EB67D3EF92A88E1474578471B97D88490E2D3 |
| SSDEEP: | 12288:gYTYexrC0udq0Mr9EXoy4j9JtZOK2A7vVMLx3Qa0:JTYexG0u8r9EXoZRJvrux3Qa0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:11:20 04:55:03+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 339968 |
| InitializedDataSize: | 266240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd4000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.3.1026.0 |
| ProductVersionNumber: | 12.30.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | PKWARE, Inc. |
| FileDescription: | PKWARE SFX for Windows (Unicode) |
| FileVersion: | 12.3.1026.0 |
| InternalName: | PKSFX.exe |
| LegalCopyright: | Portions copyright (C) 2001-2008 PKWARE, Inc. |
| LegalTrademarks: | PKWARE, PKZIP, PKUNZIP, PKSFX, and SecureZIP are registered trademarks of PKWARE, Inc. |
| OriginalFileName: | PKSFX.exe |
| ProductName: | PKWARE SFX for Windows |
| ProductVersion: | 12.30.0002 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Nov-2008 03:55:03 |
| Detected languages: |
|
| CompanyName: | PKWARE, Inc. |
| FileDescription: | PKWARE SFX for Windows (Unicode) |
| FileVersion: | 12.3.1026.0 |
| InternalName: | PKSFX.exe |
| LegalCopyright: | Portions copyright (C) 2001-2008 PKWARE, Inc. |
| LegalTrademarks: | PKWARE, PKZIP, PKUNZIP, PKSFX, and SecureZIP are registered trademarks of PKWARE, Inc. |
| OriginalFilename: | PKSFX.exe |
| ProductName: | PKWARE SFX for Windows |
| ProductVersion: | 12.30.0002 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 20-Nov-2008 03:55:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008B733 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0008D000 | 0x0002A1C2 | 0x0002B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.51552 |
.data | 0x000B8000 | 0x00014E08 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000CD000 | 0x0000661C | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.29047 |
.pklstb | 0x000D4000 | 0x00057000 | 0x00053000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99114 |
.relo2 | 0x0012B000 | 0x0000003C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.14179 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04894 | 360 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.13615 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.76741 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.0352 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.41766 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.26721 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.43093 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 1.76939 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.16955 | 44 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 0 | 282 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
36
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1456 | "C:\Users\admin\Desktop\PKSFX.exe" | C:\Users\admin\Desktop\PKSFX.exe | — | explorer.exe | |||||||||||
User: admin Company: PKWARE, Inc. Integrity Level: MEDIUM Description: PKWARE SFX for Windows (Unicode) Exit code: 1 Version: 12.3.1026.0 Modules
| |||||||||||||||
Total events
1
Read events
1
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report