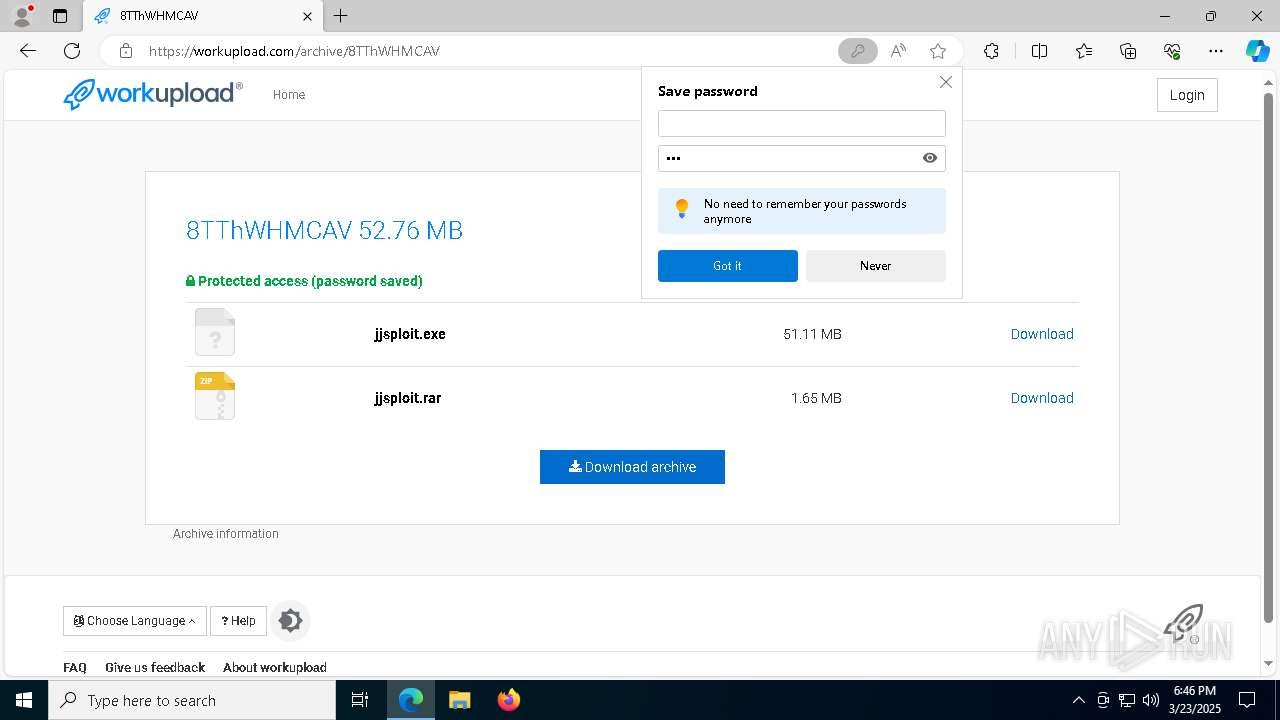
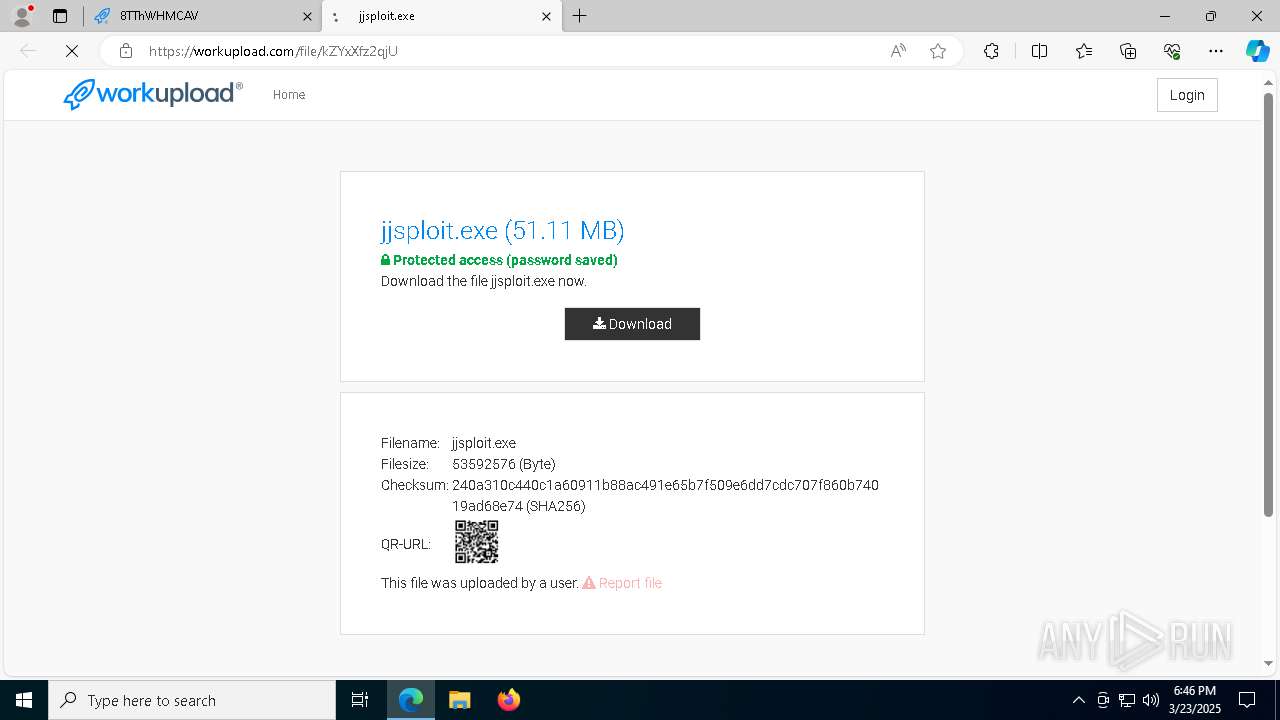
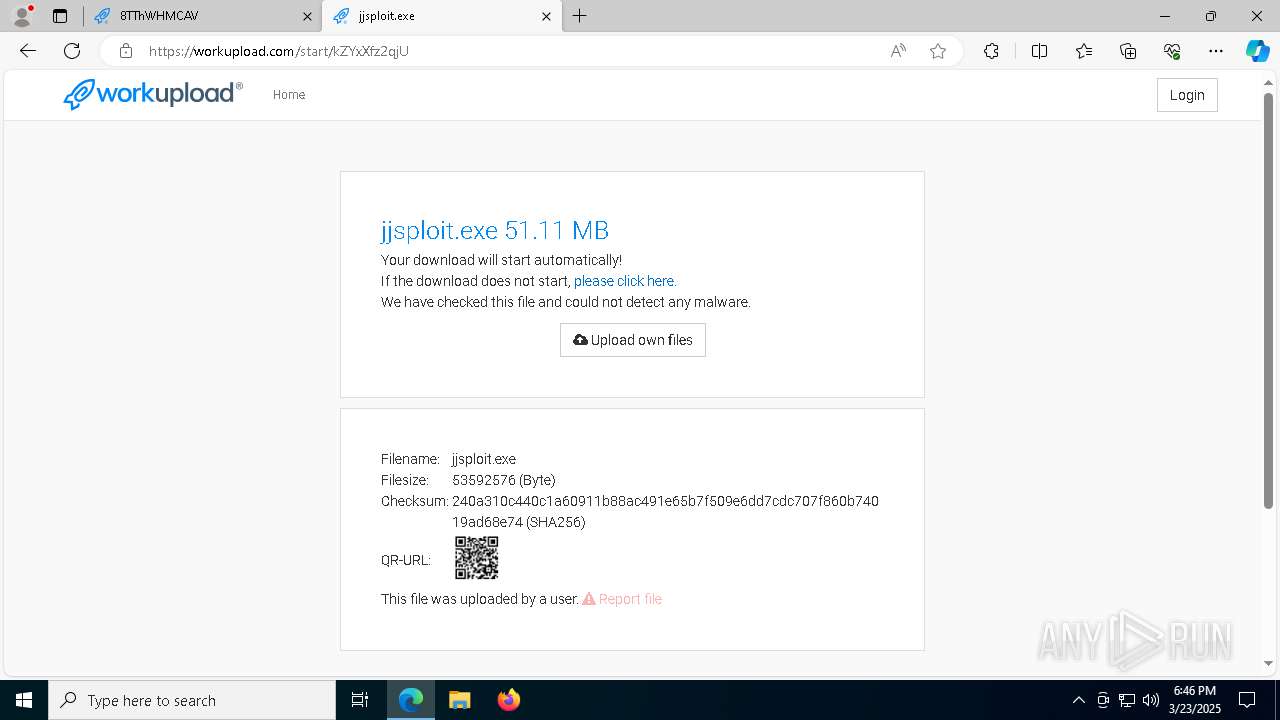
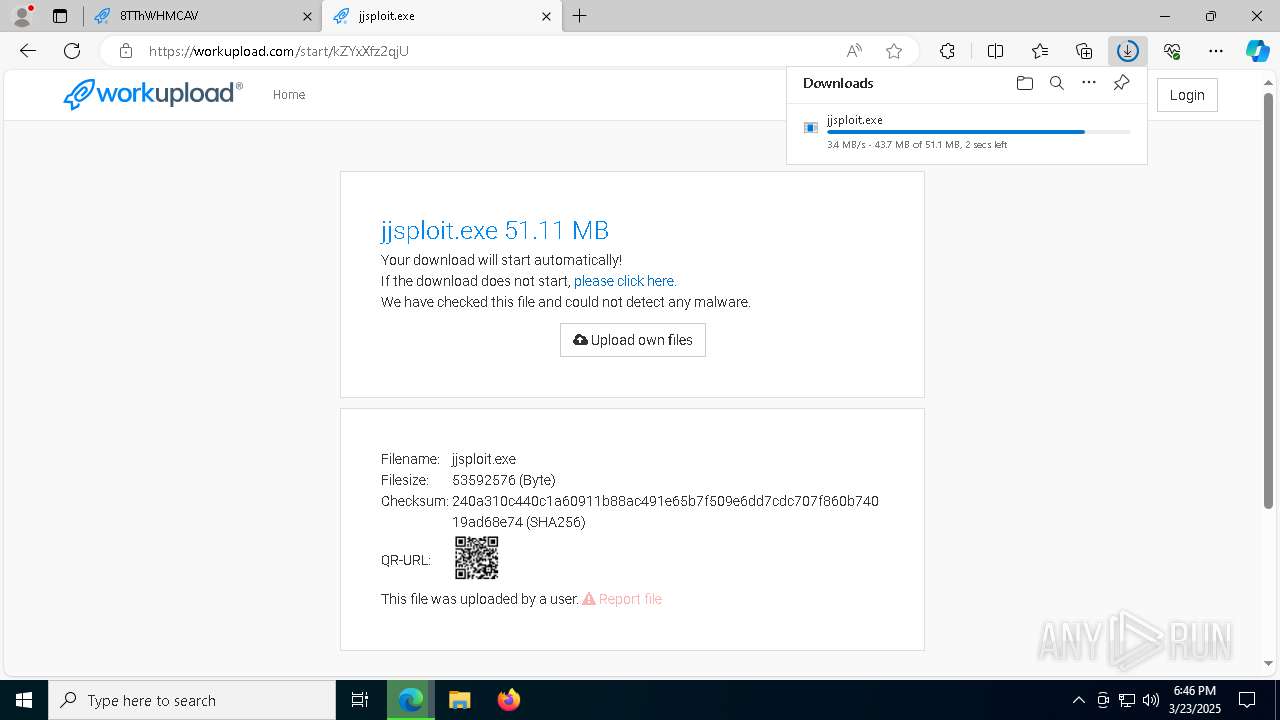
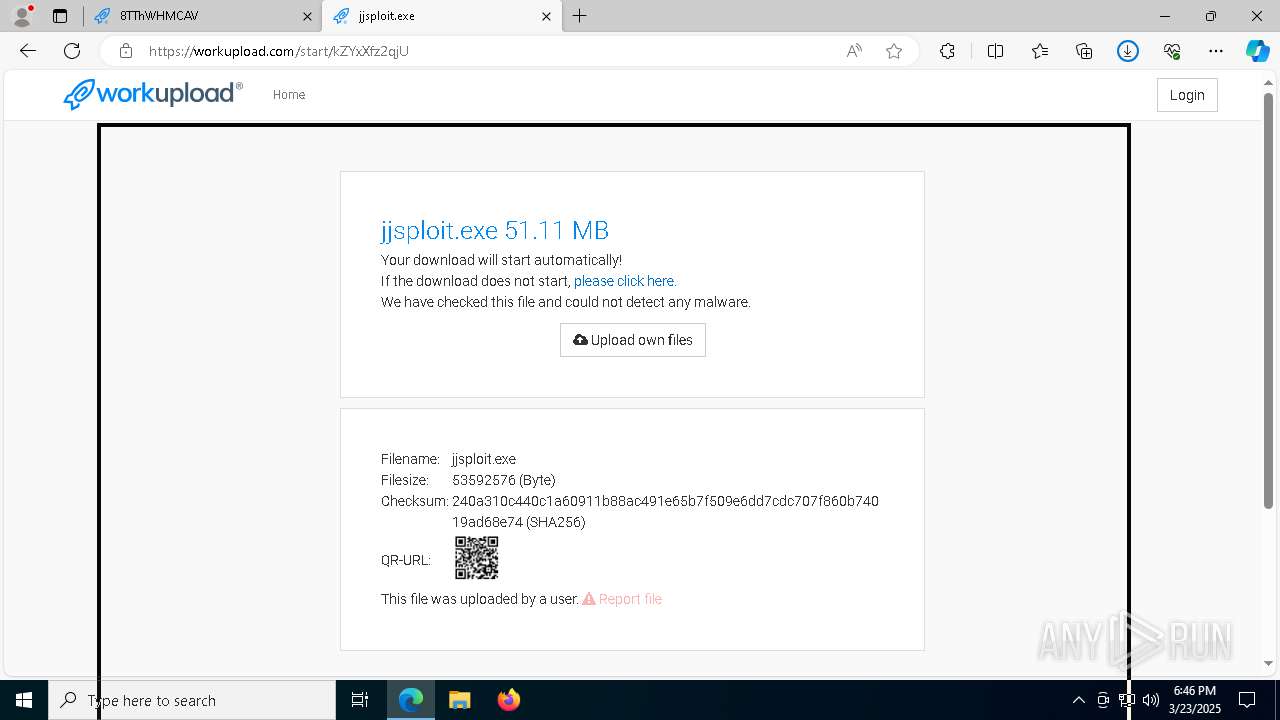
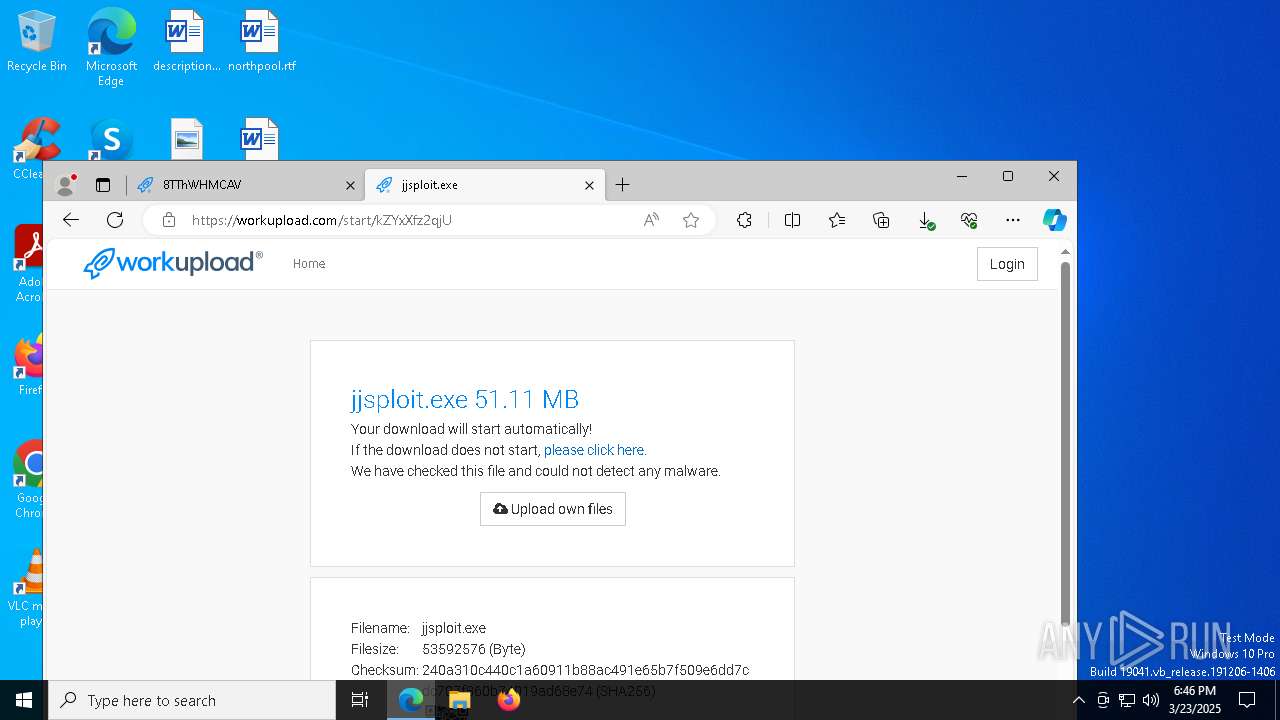
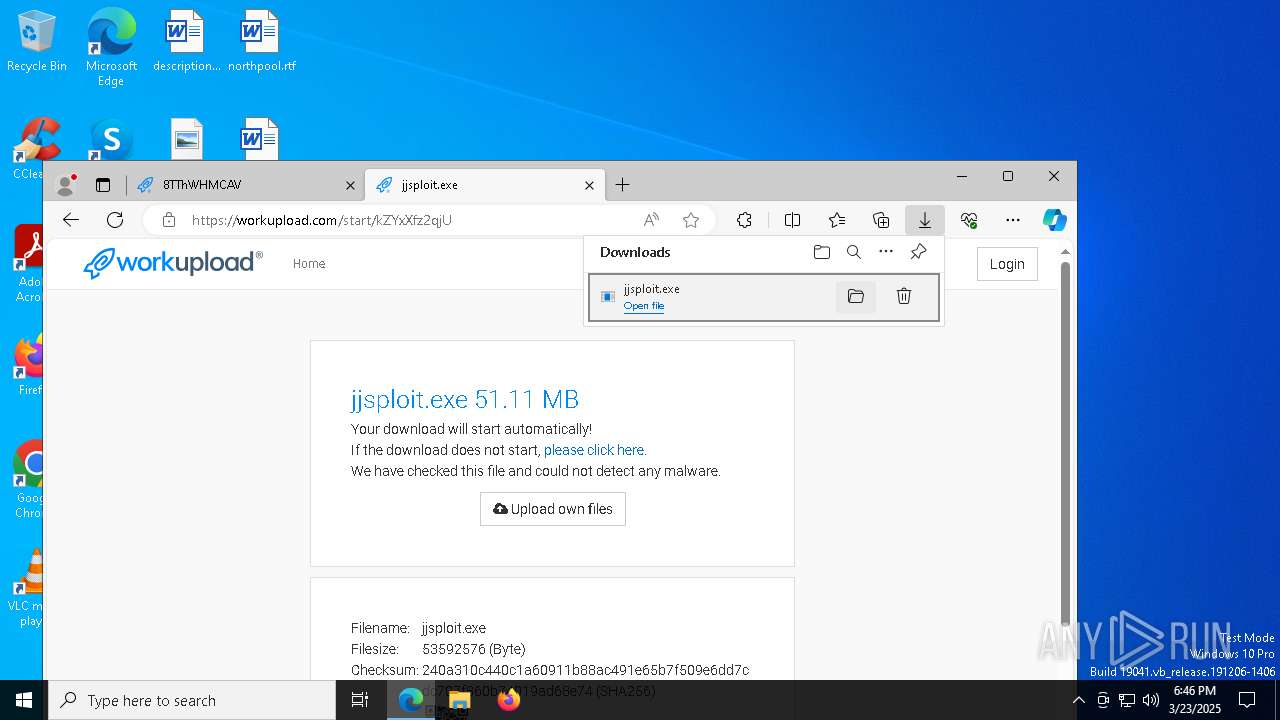
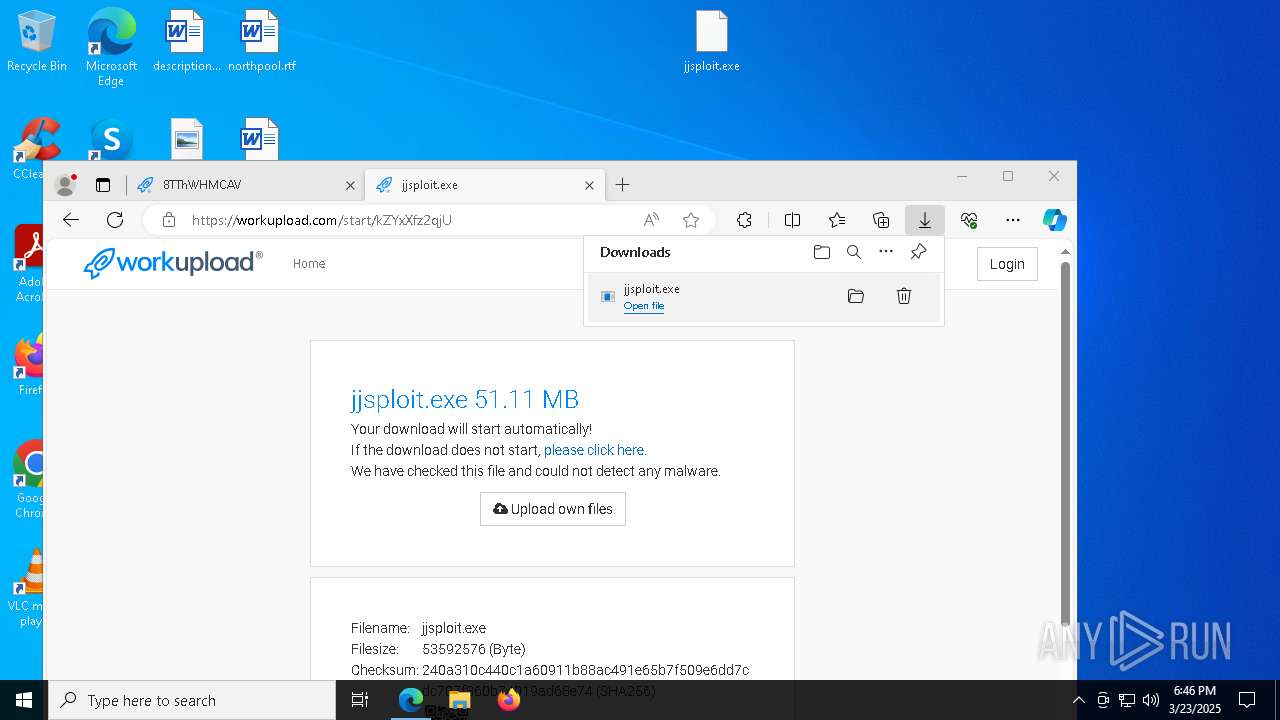
| URL: | https://workupload.com/archive/8TThWHMCAV |
| Full analysis: | https://app.any.run/tasks/e5b785d6-6e31-474d-9d58-a220c2847c49 |
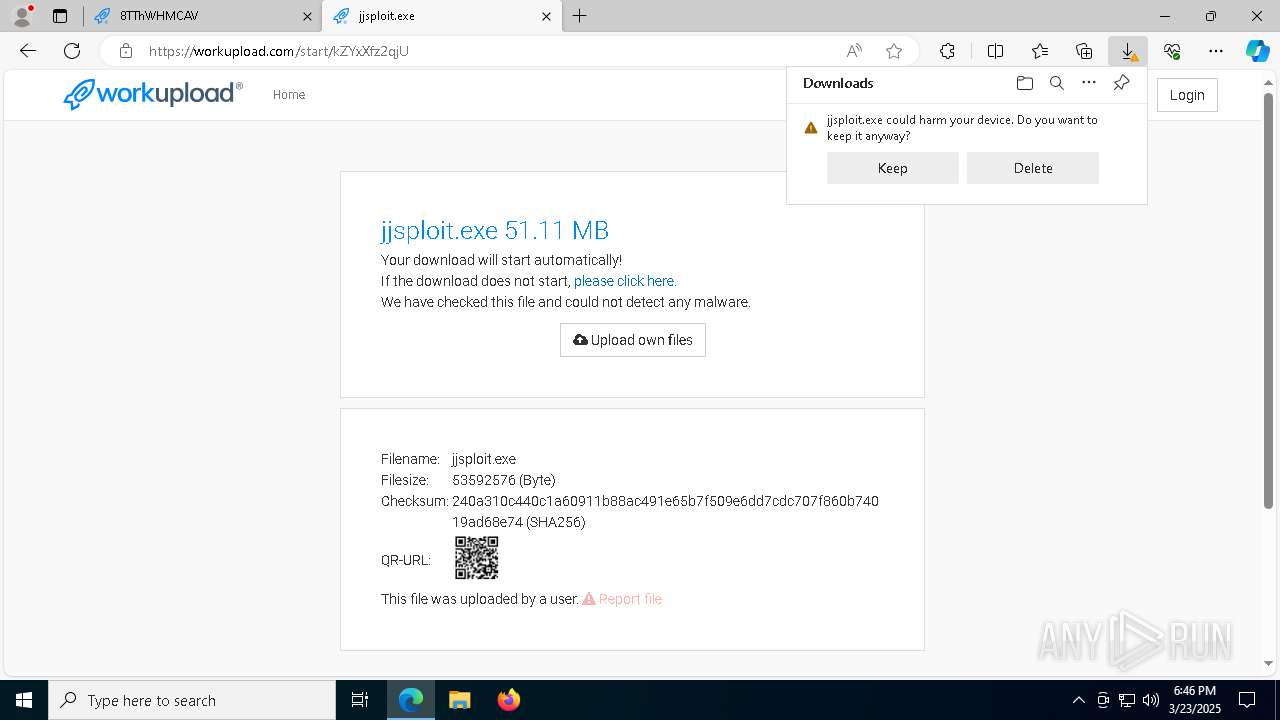
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | March 23, 2025, 18:46:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 43D90A81FD2D7150037E53B0B6562BFC |
| SHA1: | DC69EBD7BD3670835E380CF1BD955BE67C63E7E8 |
| SHA256: | 0E103F6102125233ED707B39B78159EF3D19D8D3E5DCC7FF2A22BC988D25C9EA |
| SSDEEP: | 3:N8bXOrZOMLDm6:2itOMnm6 |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 732)
- wscript.exe (PID: 6584)
- wscript.exe (PID: 8132)
- wscript.exe (PID: 1272)
- wscript.exe (PID: 10156)
- wscript.exe (PID: 7780)
- wscript.exe (PID: 7216)
- wscript.exe (PID: 10088)
- wscript.exe (PID: 4448)
- wscript.exe (PID: 9620)
- wscript.exe (PID: 8156)
- wscript.exe (PID: 8632)
- wscript.exe (PID: 8032)
- wscript.exe (PID: 4736)
- wscript.exe (PID: 9428)
- wscript.exe (PID: 3828)
- wscript.exe (PID: 10076)
- wscript.exe (PID: 7588)
Disables task manager
- reg.exe (PID: 8196)
- reg.exe (PID: 6208)
- reg.exe (PID: 3192)
Changes the autorun value in the registry
- PerfDll.exe (PID: 2140)
Changes the login/logoff helper path in the registry
- PerfDll.exe (PID: 2140)
Adds path to the Windows Defender exclusion list
- PerfDll.exe (PID: 2140)
Changes Windows Defender settings
- PerfDll.exe (PID: 2140)
DARKCRYSTAL has been detected (SURICATA)
- fontdrvhost.exe (PID: 9236)
Connects to the CnC server
- fontdrvhost.exe (PID: 9236)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 6208)
- reg.exe (PID: 3192)
SUSPICIOUS
Reads security settings of Internet Explorer
- jjsploit.exe (PID: 4464)
- CATLAVAN.exe (PID: 2420)
- PerfDll.exe (PID: 2140)
- msedge.exe (PID: 9540)
- msedge.exe (PID: 9548)
- jjsploit.exe (PID: 7368)
- CATLAVAN.exe (PID: 9972)
- jjsploit.exe (PID: 10084)
- CATLAVAN.exe (PID: 6752)
- jjsploit.exe (PID: 9320)
- CATLAVAN.exe (PID: 8796)
- msedge.exe (PID: 1764)
- jjsploit.exe (PID: 8612)
- CATLAVAN.exe (PID: 7572)
- jjsploit.exe (PID: 10112)
- CATLAVAN.exe (PID: 8672)
- jjsploit.exe (PID: 3304)
- CATLAVAN.exe (PID: 8364)
- jjsploit.exe (PID: 9172)
- CATLAVAN.exe (PID: 6876)
- jjsploit.exe (PID: 5668)
- CATLAVAN.exe (PID: 8692)
- jjsploit.exe (PID: 9180)
- CATLAVAN.exe (PID: 7512)
- jjsploit.exe (PID: 7920)
- CATLAVAN.exe (PID: 9036)
- jjsploit.exe (PID: 6620)
- CATLAVAN.exe (PID: 7340)
- jjsploit.exe (PID: 9700)
- jjsploit.exe (PID: 6904)
- CATLAVAN.exe (PID: 8196)
- CATLAVAN.exe (PID: 8784)
- jjsploit.exe (PID: 7084)
- jjsploit.exe (PID: 4724)
- CATLAVAN.exe (PID: 8612)
- jjsploit.exe (PID: 904)
- CATLAVAN.exe (PID: 1240)
- jjsploit.exe (PID: 6712)
- CATLAVAN.exe (PID: 8920)
- CATLAVAN.exe (PID: 7544)
Executing commands from a ".bat" file
- wscript.exe (PID: 732)
- PerfDll.exe (PID: 2140)
- wscript.exe (PID: 6584)
- wscript.exe (PID: 8132)
- wscript.exe (PID: 1272)
- wscript.exe (PID: 10156)
- wscript.exe (PID: 7780)
- wscript.exe (PID: 7216)
- wscript.exe (PID: 10088)
- wscript.exe (PID: 4448)
- wscript.exe (PID: 9620)
- wscript.exe (PID: 8156)
- wscript.exe (PID: 8632)
- wscript.exe (PID: 8032)
- wscript.exe (PID: 4736)
- wscript.exe (PID: 9428)
- wscript.exe (PID: 3828)
- wscript.exe (PID: 10076)
- wscript.exe (PID: 7588)
Runs shell command (SCRIPT)
- wscript.exe (PID: 732)
- wscript.exe (PID: 6584)
- wscript.exe (PID: 8132)
- wscript.exe (PID: 1272)
- wscript.exe (PID: 10156)
- wscript.exe (PID: 7780)
- wscript.exe (PID: 7216)
- wscript.exe (PID: 10088)
- wscript.exe (PID: 4448)
- wscript.exe (PID: 9620)
- wscript.exe (PID: 8156)
- wscript.exe (PID: 8632)
- wscript.exe (PID: 8032)
- wscript.exe (PID: 4736)
- wscript.exe (PID: 9428)
- wscript.exe (PID: 3828)
- wscript.exe (PID: 10076)
- wscript.exe (PID: 7588)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4428)
- cmd.exe (PID: 9752)
- cmd.exe (PID: 8400)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 9728)
- cmd.exe (PID: 9824)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 9512)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 6828)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 8528)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 732)
- PerfDll.exe (PID: 2140)
- wscript.exe (PID: 6584)
- wscript.exe (PID: 8132)
- wscript.exe (PID: 1272)
- wscript.exe (PID: 10156)
- wscript.exe (PID: 7780)
- wscript.exe (PID: 7216)
- wscript.exe (PID: 10088)
- wscript.exe (PID: 4448)
- wscript.exe (PID: 9620)
- wscript.exe (PID: 8156)
- wscript.exe (PID: 8632)
- wscript.exe (PID: 8032)
- wscript.exe (PID: 4736)
- wscript.exe (PID: 9428)
- wscript.exe (PID: 3828)
- wscript.exe (PID: 10076)
- wscript.exe (PID: 7588)
Executable content was dropped or overwritten
- PerfDll.exe (PID: 2140)
- csc.exe (PID: 8772)
- csc.exe (PID: 5552)
- csc.exe (PID: 8312)
- csc.exe (PID: 8856)
- fontdrvhost.exe (PID: 9236)
The process creates files with name similar to system file names
- PerfDll.exe (PID: 2140)
Executed via WMI
- schtasks.exe (PID: 8780)
- schtasks.exe (PID: 7792)
- schtasks.exe (PID: 7952)
- schtasks.exe (PID: 7568)
- schtasks.exe (PID: 7528)
- schtasks.exe (PID: 7492)
- schtasks.exe (PID: 8032)
- schtasks.exe (PID: 7444)
- schtasks.exe (PID: 7612)
- schtasks.exe (PID: 7644)
- schtasks.exe (PID: 7552)
- schtasks.exe (PID: 728)
- schtasks.exe (PID: 7352)
- schtasks.exe (PID: 7632)
- schtasks.exe (PID: 7412)
- schtasks.exe (PID: 7908)
- schtasks.exe (PID: 7284)
- schtasks.exe (PID: 7408)
Process drops legitimate windows executable
- PerfDll.exe (PID: 2140)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 7644)
- schtasks.exe (PID: 7552)
- schtasks.exe (PID: 7632)
- powershell.exe (PID: 6268)
Starts POWERSHELL.EXE for commands execution
- PerfDll.exe (PID: 2140)
Script adds exclusion path to Windows Defender
- PerfDll.exe (PID: 2140)
Reads the date of Windows installation
- PerfDll.exe (PID: 2140)
- msedge.exe (PID: 9548)
- msedge.exe (PID: 9540)
- msedge.exe (PID: 1764)
Starts application with an unusual extension
- cmd.exe (PID: 8588)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 8588)
INFO
Checks supported languages
- identity_helper.exe (PID: 9036)
- identity_helper.exe (PID: 8040)
- jjsploit.exe (PID: 4464)
- CATLAVAN.exe (PID: 2420)
- PerfDll.exe (PID: 2140)
- csc.exe (PID: 8772)
- cvtres.exe (PID: 7764)
- csc.exe (PID: 5552)
- cvtres.exe (PID: 8036)
- csc.exe (PID: 8856)
- cvtres.exe (PID: 8272)
- csc.exe (PID: 8312)
- cvtres.exe (PID: 776)
- chcp.com (PID: 7952)
- fontdrvhost.exe (PID: 9236)
- msedge.exe (PID: 9540)
- msedge.exe (PID: 9548)
- msedge.exe.exe (PID: 9800)
- jjsploit.exe (PID: 7368)
- PerfDll.exe (PID: 8520)
- jjsploit.exe (PID: 10084)
- CATLAVAN.exe (PID: 9972)
- CATLAVAN.exe (PID: 6752)
- PerfDll.exe (PID: 10036)
- CATLAVAN.exe (PID: 8796)
- PerfDll.exe (PID: 208)
- msedge.exe.exe (PID: 9808)
- jjsploit.exe (PID: 9320)
- msedge.exe (PID: 1764)
- msedge.exe.exe (PID: 10164)
- CATLAVAN.exe (PID: 7572)
- jjsploit.exe (PID: 8612)
- PerfDll.exe (PID: 8828)
- jjsploit.exe (PID: 10112)
- CATLAVAN.exe (PID: 8672)
- PerfDll.exe (PID: 5008)
- PerfDll.exe (PID: 2384)
- CATLAVAN.exe (PID: 8364)
- CATLAVAN.exe (PID: 6876)
- jjsploit.exe (PID: 9172)
- jjsploit.exe (PID: 5668)
- PerfDll.exe (PID: 3800)
- CATLAVAN.exe (PID: 8692)
- PerfDll.exe (PID: 9904)
- jjsploit.exe (PID: 9180)
- CATLAVAN.exe (PID: 7512)
- PerfDll.exe (PID: 8024)
- CATLAVAN.exe (PID: 9036)
- jjsploit.exe (PID: 7920)
- PerfDll.exe (PID: 7540)
- jjsploit.exe (PID: 6620)
- CATLAVAN.exe (PID: 7544)
- PerfDll.exe (PID: 9732)
- jjsploit.exe (PID: 9700)
- CATLAVAN.exe (PID: 7340)
- PerfDll.exe (PID: 9340)
- jjsploit.exe (PID: 6904)
- CATLAVAN.exe (PID: 8196)
- PerfDll.exe (PID: 9444)
- jjsploit.exe (PID: 7084)
- CATLAVAN.exe (PID: 8784)
- jjsploit.exe (PID: 4724)
- CATLAVAN.exe (PID: 8612)
- PerfDll.exe (PID: 6700)
- PerfDll.exe (PID: 5056)
- CATLAVAN.exe (PID: 1240)
- jjsploit.exe (PID: 904)
- PerfDll.exe (PID: 1180)
- CATLAVAN.exe (PID: 8920)
- PerfDll.exe (PID: 9296)
- jjsploit.exe (PID: 6712)
- jjsploit.exe (PID: 3304)
Reads Environment values
- identity_helper.exe (PID: 9036)
- identity_helper.exe (PID: 8040)
- PerfDll.exe (PID: 2140)
- fontdrvhost.exe (PID: 9236)
- msedge.exe.exe (PID: 9800)
- msedge.exe.exe (PID: 9808)
- PerfDll.exe (PID: 8520)
- PerfDll.exe (PID: 10036)
- msedge.exe.exe (PID: 10164)
- PerfDll.exe (PID: 8828)
- PerfDll.exe (PID: 5008)
- PerfDll.exe (PID: 2384)
- PerfDll.exe (PID: 3800)
- PerfDll.exe (PID: 208)
- PerfDll.exe (PID: 9904)
- PerfDll.exe (PID: 8024)
- PerfDll.exe (PID: 7540)
- PerfDll.exe (PID: 9732)
- PerfDll.exe (PID: 9340)
- PerfDll.exe (PID: 9444)
- PerfDll.exe (PID: 6700)
- PerfDll.exe (PID: 5056)
- PerfDll.exe (PID: 1180)
- PerfDll.exe (PID: 9296)
Application launched itself
- msedge.exe (PID: 1512)
- msedge.exe (PID: 9060)
Reads the computer name
- identity_helper.exe (PID: 8040)
- CATLAVAN.exe (PID: 2420)
- jjsploit.exe (PID: 4464)
- identity_helper.exe (PID: 9036)
- PerfDll.exe (PID: 2140)
- fontdrvhost.exe (PID: 9236)
- msedge.exe (PID: 9540)
- msedge.exe (PID: 9548)
- msedge.exe.exe (PID: 9808)
- msedge.exe.exe (PID: 9800)
- jjsploit.exe (PID: 7368)
- PerfDll.exe (PID: 8520)
- CATLAVAN.exe (PID: 9972)
- jjsploit.exe (PID: 10084)
- CATLAVAN.exe (PID: 6752)
- PerfDll.exe (PID: 10036)
- jjsploit.exe (PID: 9320)
- CATLAVAN.exe (PID: 8796)
- PerfDll.exe (PID: 208)
- msedge.exe (PID: 1764)
- msedge.exe.exe (PID: 10164)
- jjsploit.exe (PID: 8612)
- CATLAVAN.exe (PID: 7572)
- PerfDll.exe (PID: 8828)
- jjsploit.exe (PID: 10112)
- CATLAVAN.exe (PID: 8672)
- PerfDll.exe (PID: 5008)
- PerfDll.exe (PID: 2384)
- CATLAVAN.exe (PID: 8364)
- CATLAVAN.exe (PID: 6876)
- jjsploit.exe (PID: 9172)
- PerfDll.exe (PID: 3800)
- jjsploit.exe (PID: 5668)
- PerfDll.exe (PID: 9904)
- CATLAVAN.exe (PID: 8692)
- CATLAVAN.exe (PID: 7512)
- PerfDll.exe (PID: 8024)
- jjsploit.exe (PID: 9180)
- jjsploit.exe (PID: 7920)
- CATLAVAN.exe (PID: 9036)
- PerfDll.exe (PID: 7540)
- jjsploit.exe (PID: 6620)
- CATLAVAN.exe (PID: 7544)
- PerfDll.exe (PID: 9732)
- CATLAVAN.exe (PID: 7340)
- jjsploit.exe (PID: 9700)
- jjsploit.exe (PID: 6904)
- CATLAVAN.exe (PID: 8196)
- PerfDll.exe (PID: 9340)
- PerfDll.exe (PID: 9444)
- jjsploit.exe (PID: 7084)
- CATLAVAN.exe (PID: 8784)
- CATLAVAN.exe (PID: 8612)
- PerfDll.exe (PID: 6700)
- jjsploit.exe (PID: 4724)
- PerfDll.exe (PID: 5056)
- jjsploit.exe (PID: 904)
- PerfDll.exe (PID: 1180)
- CATLAVAN.exe (PID: 1240)
- CATLAVAN.exe (PID: 8920)
- jjsploit.exe (PID: 6712)
- PerfDll.exe (PID: 9296)
- jjsploit.exe (PID: 3304)
Autorun file from Downloads
- msedge.exe (PID: 8224)
Create files in a temporary directory
- jjsploit.exe (PID: 4464)
- PerfDll.exe (PID: 2140)
- cvtres.exe (PID: 7764)
- cvtres.exe (PID: 8036)
- cvtres.exe (PID: 8272)
- cvtres.exe (PID: 776)
- jjsploit.exe (PID: 7368)
- jjsploit.exe (PID: 10084)
- jjsploit.exe (PID: 9320)
- jjsploit.exe (PID: 8612)
- jjsploit.exe (PID: 10112)
- jjsploit.exe (PID: 3304)
- jjsploit.exe (PID: 9172)
- jjsploit.exe (PID: 5668)
- jjsploit.exe (PID: 9180)
- jjsploit.exe (PID: 7920)
- jjsploit.exe (PID: 6620)
- jjsploit.exe (PID: 9700)
- jjsploit.exe (PID: 6904)
- jjsploit.exe (PID: 7084)
- jjsploit.exe (PID: 4724)
- jjsploit.exe (PID: 904)
- jjsploit.exe (PID: 6712)
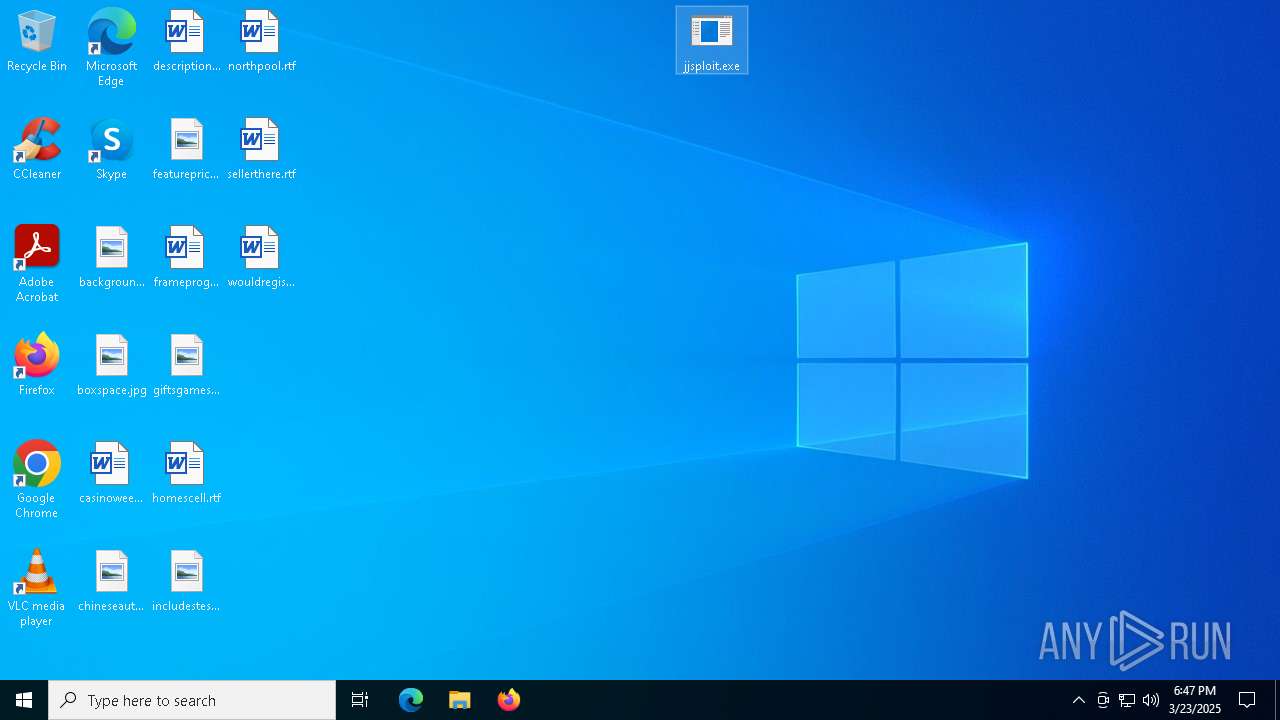
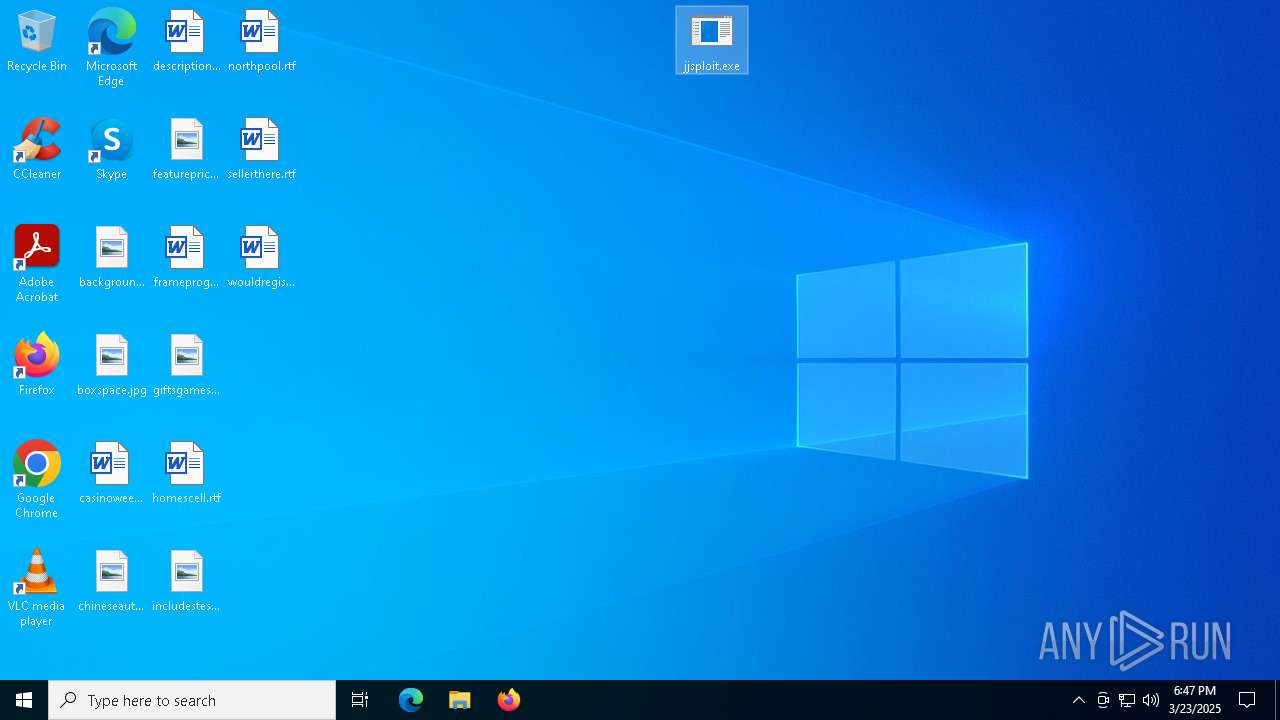
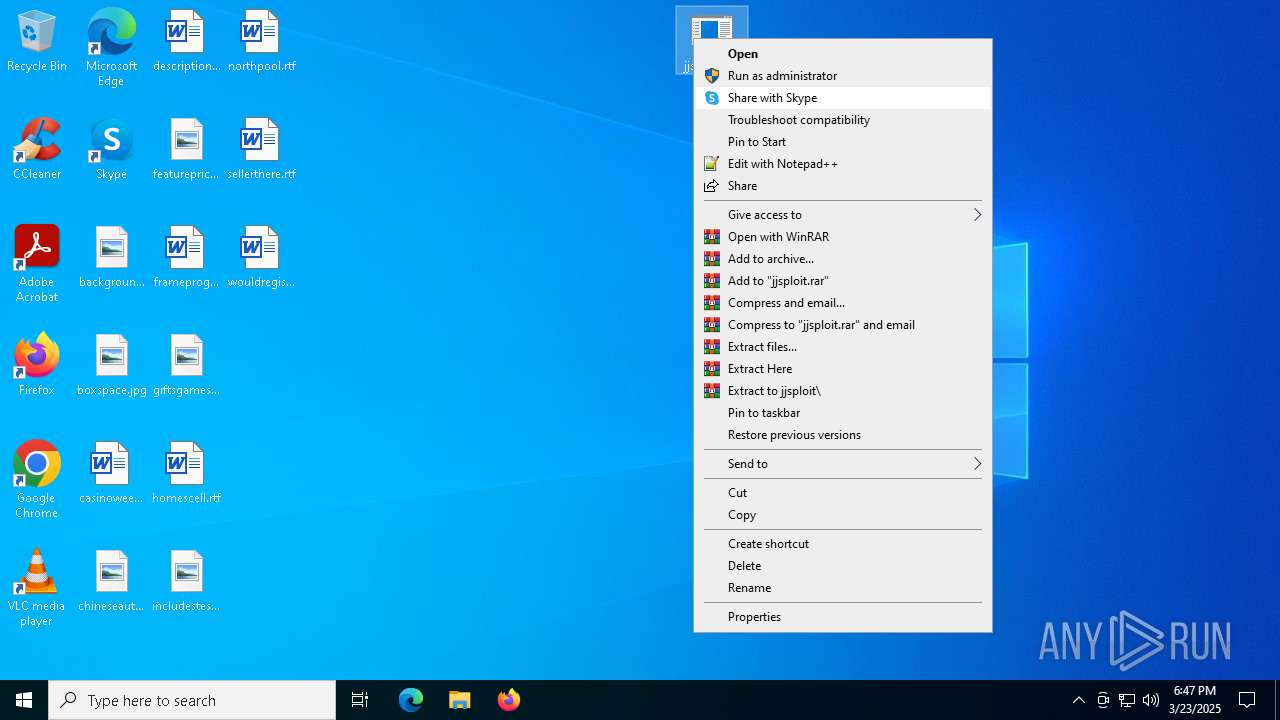
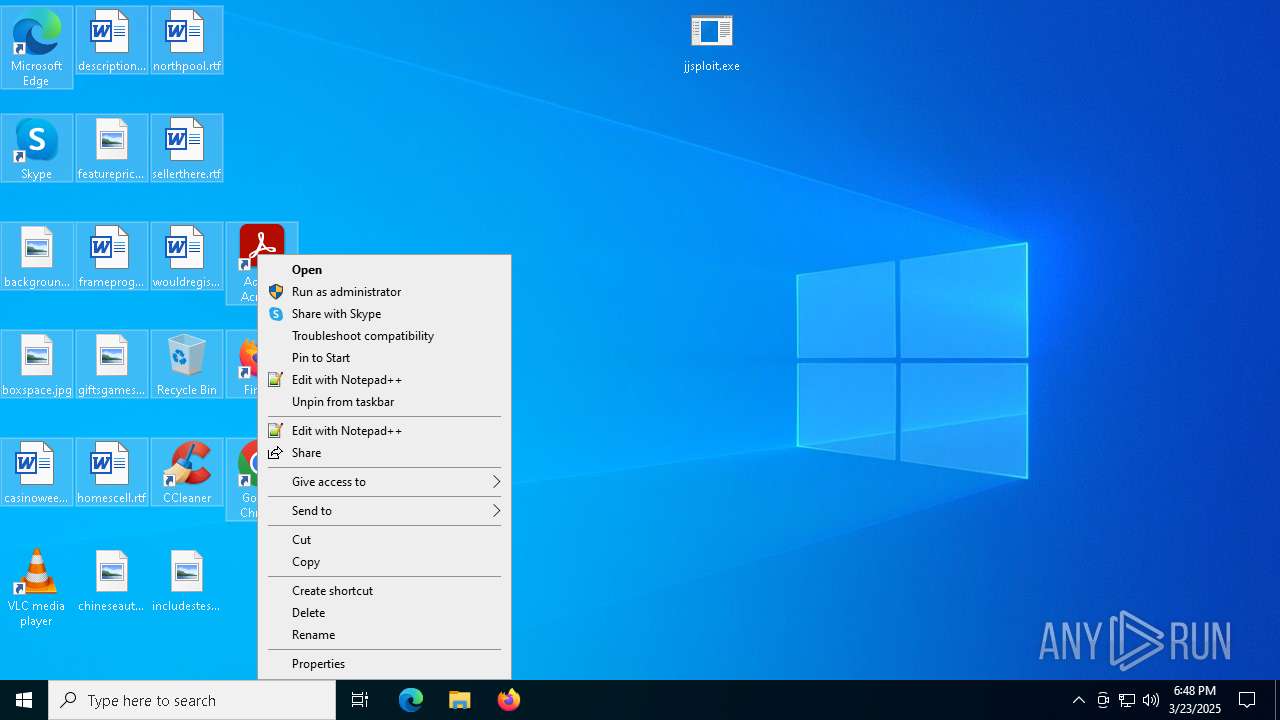
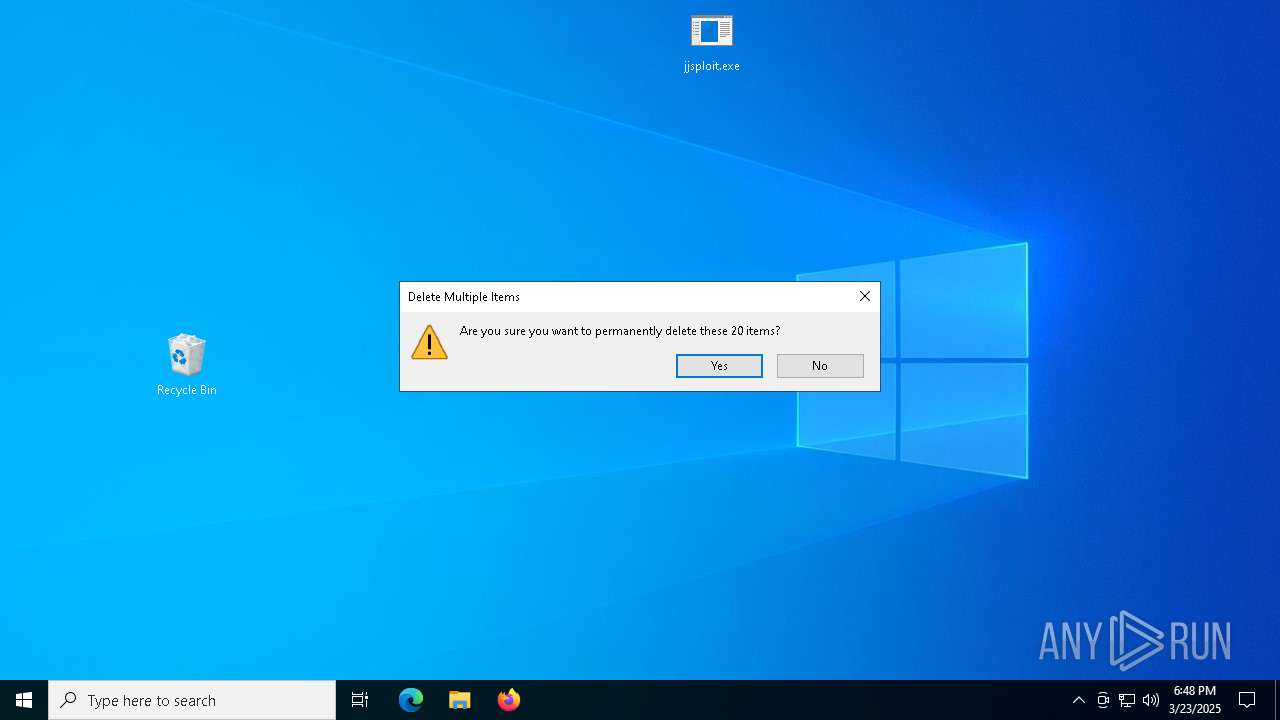
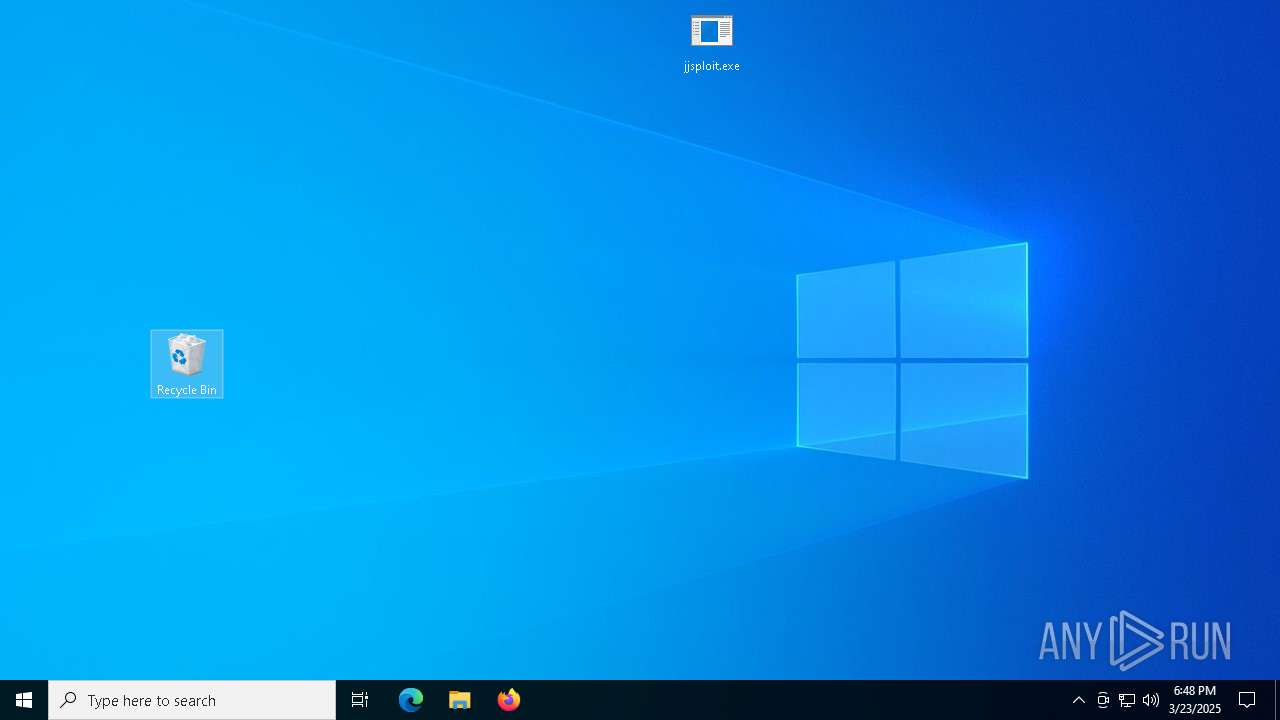
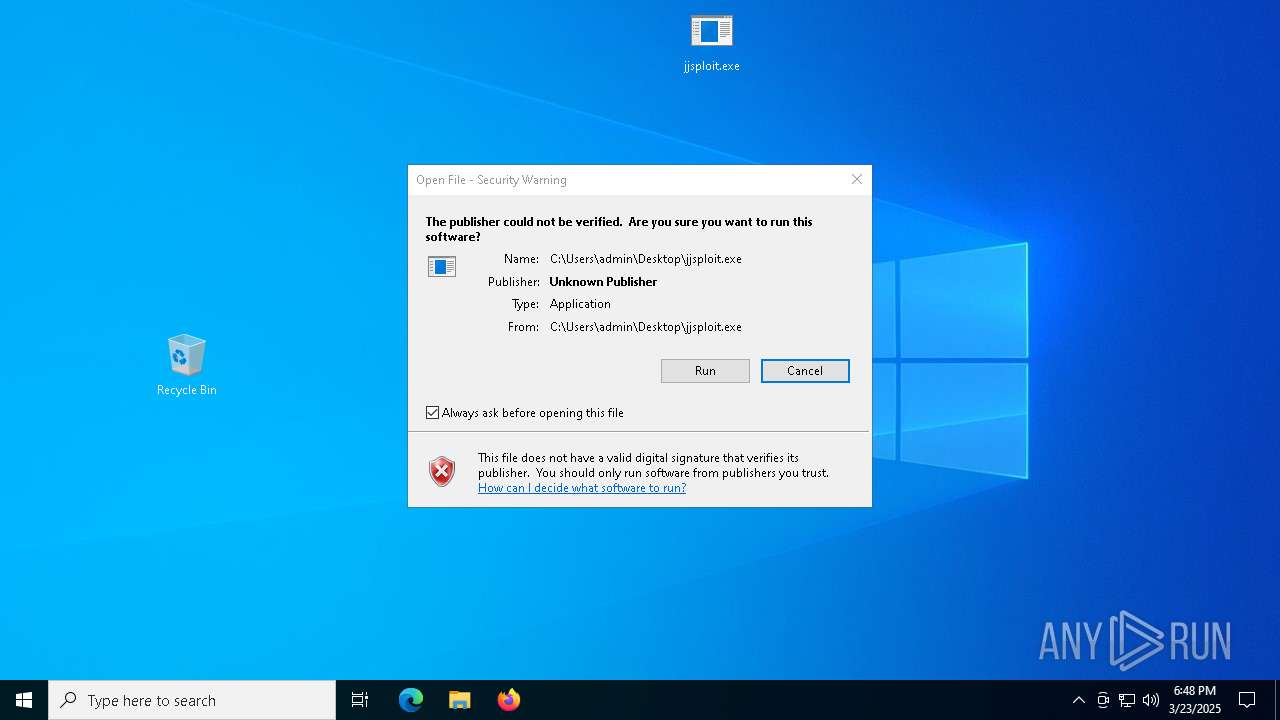
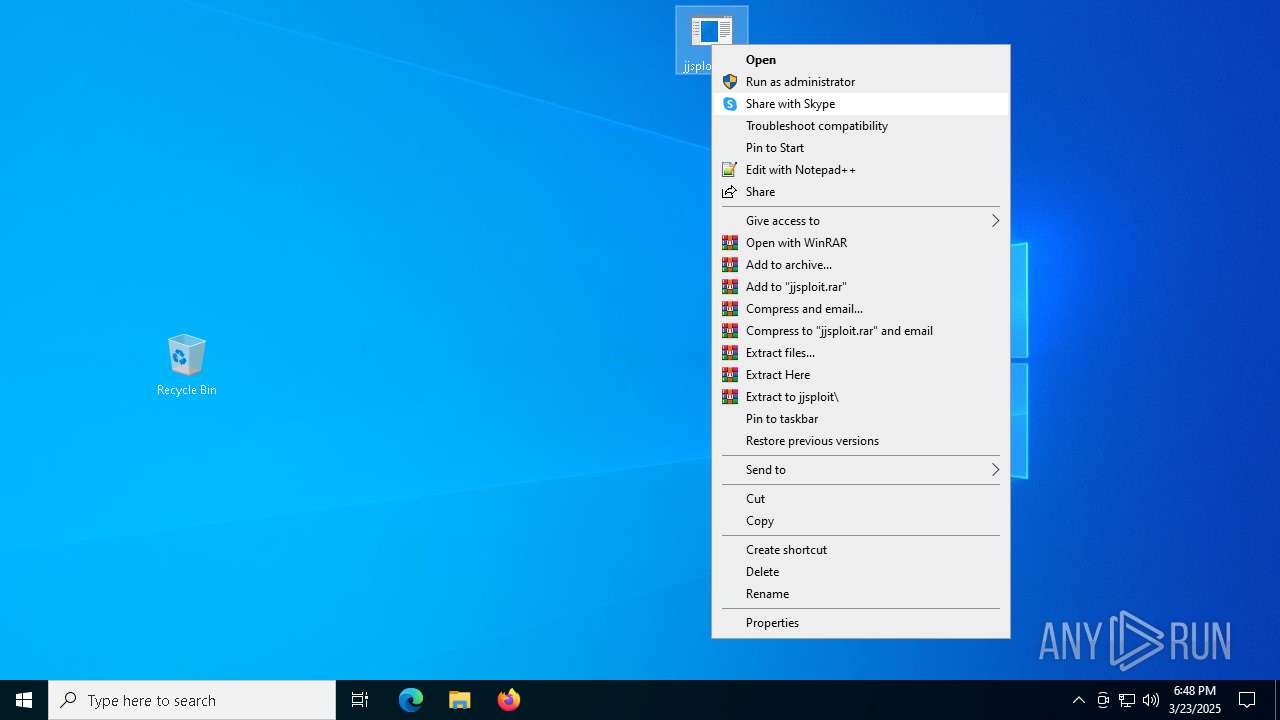
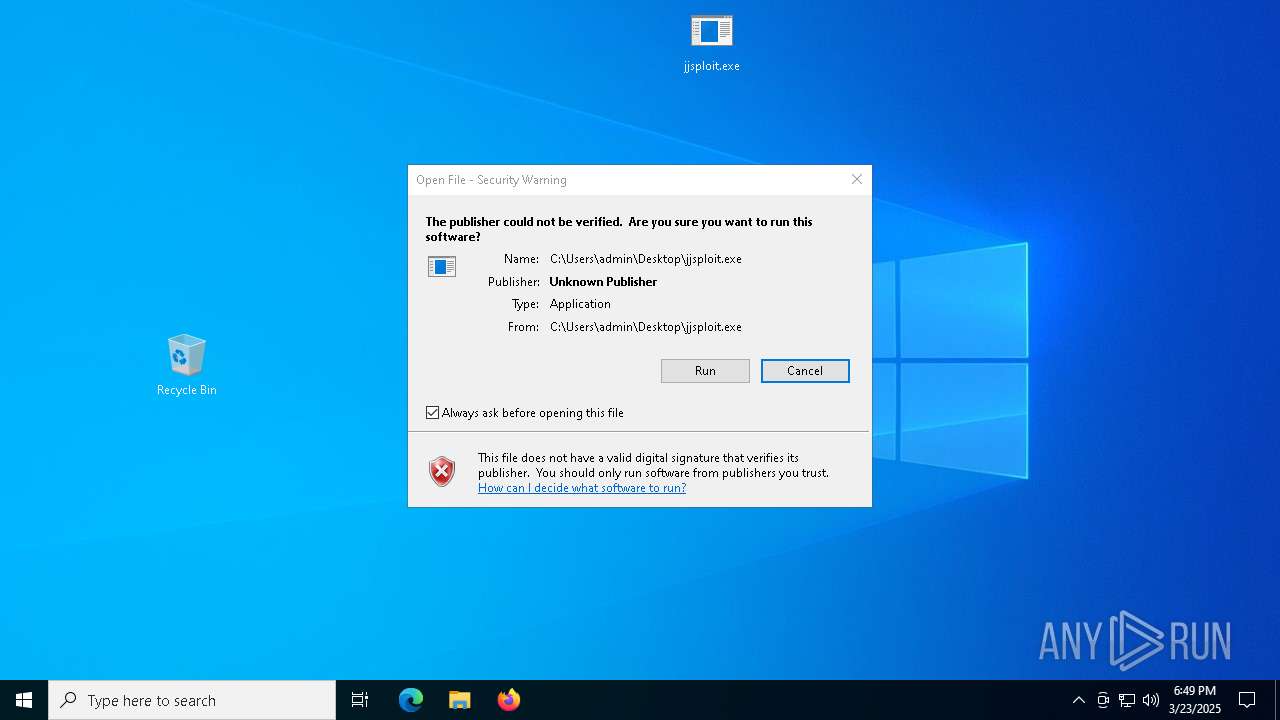
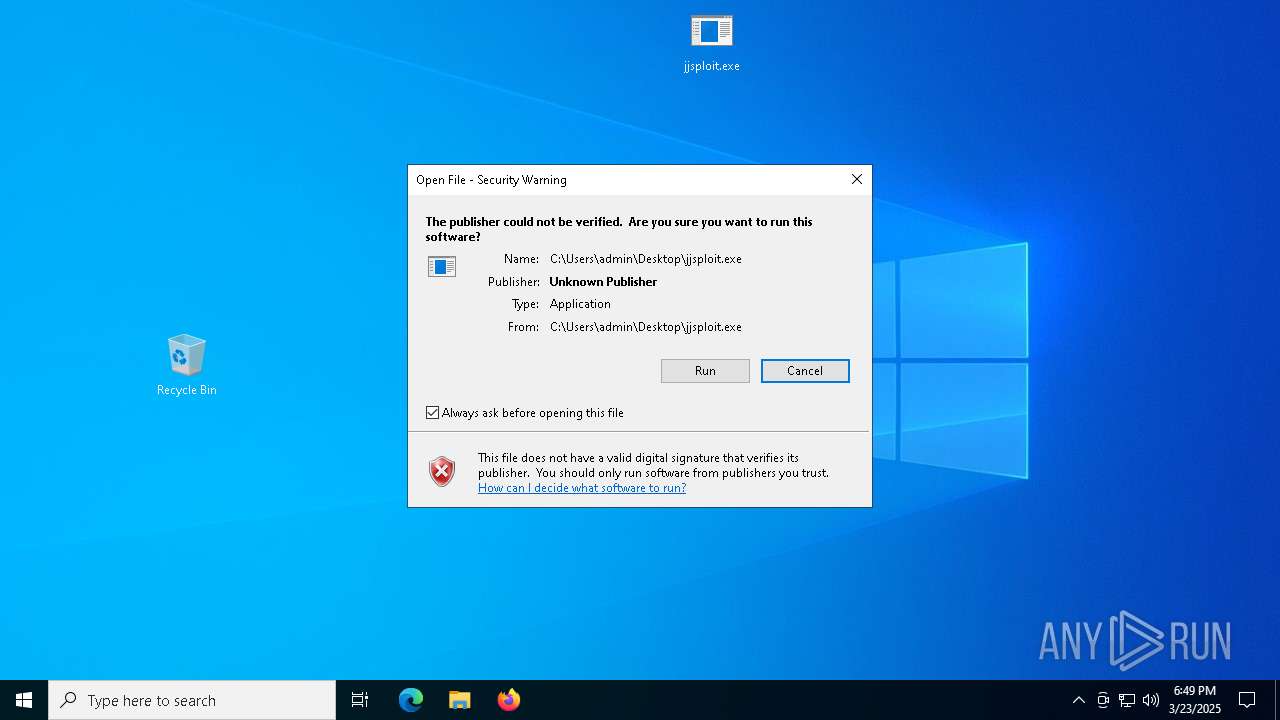
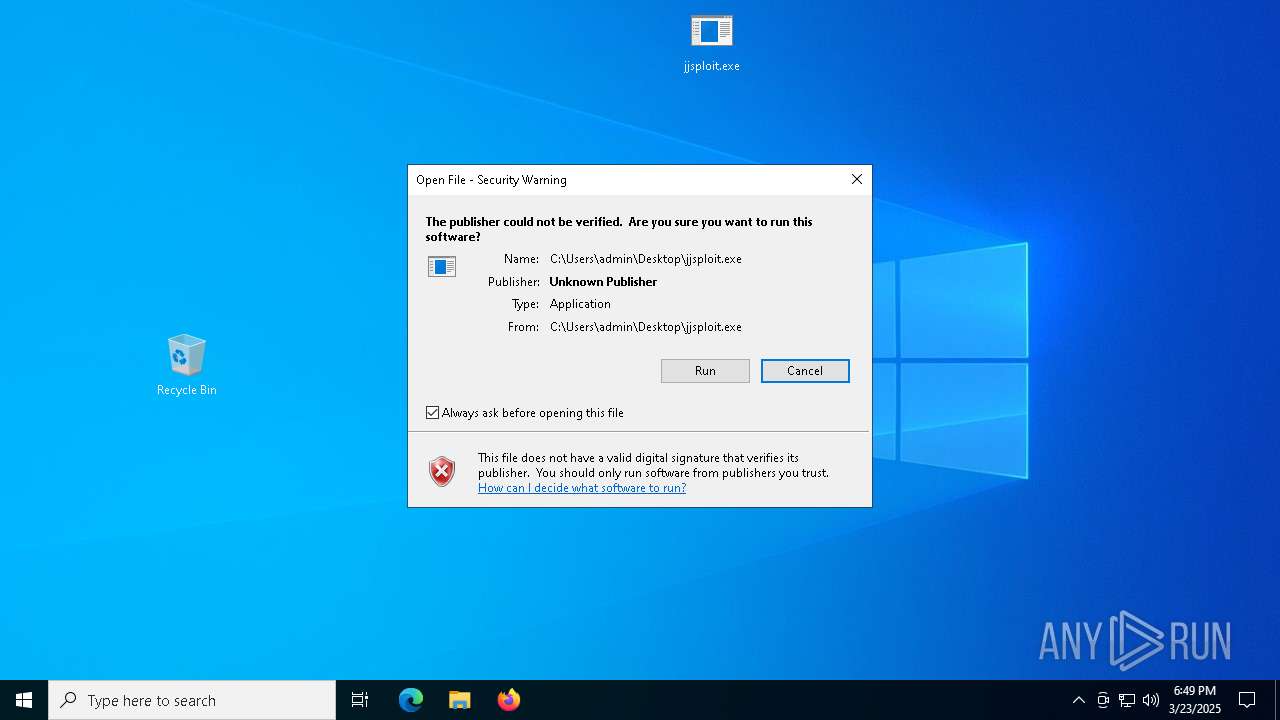
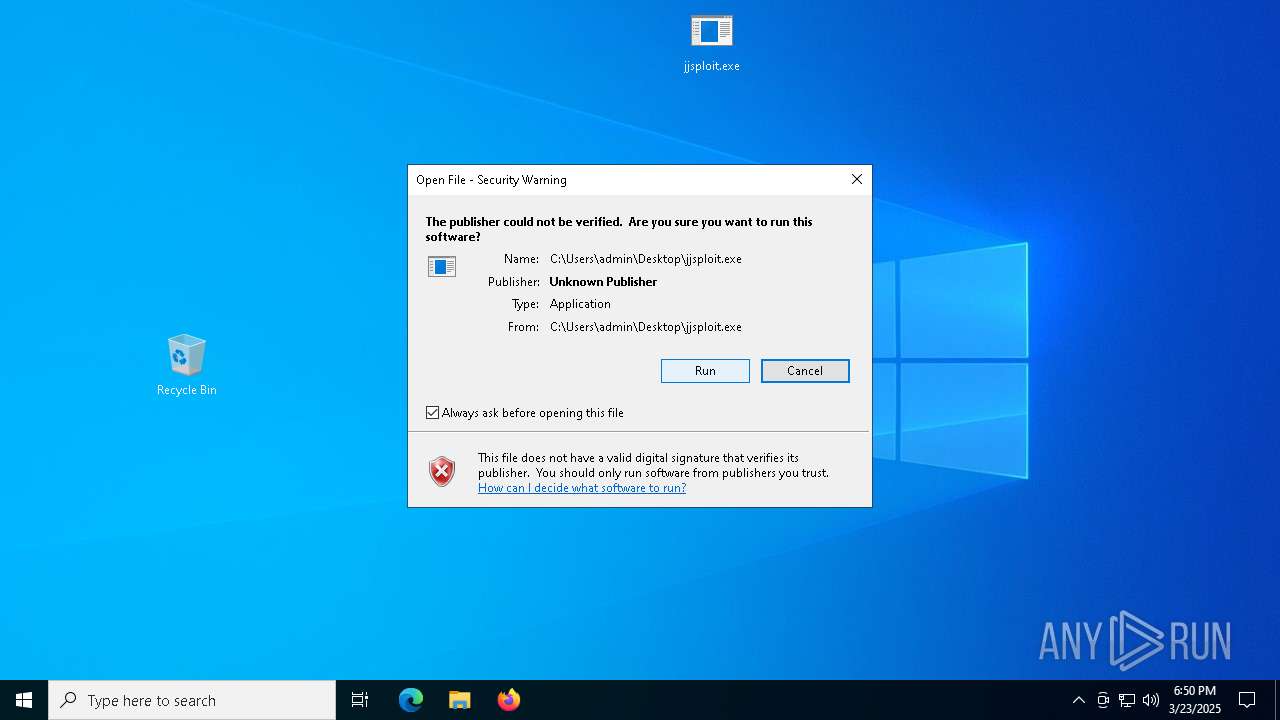
Manual execution by a user
- jjsploit.exe (PID: 4464)
- jjsploit.exe (PID: 7368)
- jjsploit.exe (PID: 10084)
- jjsploit.exe (PID: 9320)
- jjsploit.exe (PID: 8612)
- jjsploit.exe (PID: 10112)
- jjsploit.exe (PID: 3304)
- jjsploit.exe (PID: 9172)
- jjsploit.exe (PID: 5668)
- jjsploit.exe (PID: 9180)
- jjsploit.exe (PID: 7920)
- jjsploit.exe (PID: 6620)
- jjsploit.exe (PID: 9700)
- jjsploit.exe (PID: 6904)
- jjsploit.exe (PID: 7084)
- jjsploit.exe (PID: 4724)
- jjsploit.exe (PID: 904)
- jjsploit.exe (PID: 6712)
Process checks computer location settings
- jjsploit.exe (PID: 4464)
- CATLAVAN.exe (PID: 2420)
- PerfDll.exe (PID: 2140)
- msedge.exe (PID: 9548)
- msedge.exe (PID: 9540)
- jjsploit.exe (PID: 7368)
- CATLAVAN.exe (PID: 9972)
- jjsploit.exe (PID: 10084)
- CATLAVAN.exe (PID: 6752)
- jjsploit.exe (PID: 9320)
- CATLAVAN.exe (PID: 8796)
- msedge.exe (PID: 1764)
- jjsploit.exe (PID: 8612)
- CATLAVAN.exe (PID: 7572)
- jjsploit.exe (PID: 10112)
- CATLAVAN.exe (PID: 8672)
- jjsploit.exe (PID: 3304)
- CATLAVAN.exe (PID: 8364)
- CATLAVAN.exe (PID: 6876)
- jjsploit.exe (PID: 9172)
- jjsploit.exe (PID: 5668)
- CATLAVAN.exe (PID: 8692)
- jjsploit.exe (PID: 9180)
- CATLAVAN.exe (PID: 7512)
- jjsploit.exe (PID: 7920)
- CATLAVAN.exe (PID: 9036)
- jjsploit.exe (PID: 6620)
- CATLAVAN.exe (PID: 7544)
- jjsploit.exe (PID: 9700)
- CATLAVAN.exe (PID: 7340)
- jjsploit.exe (PID: 6904)
- CATLAVAN.exe (PID: 8196)
- CATLAVAN.exe (PID: 8784)
- jjsploit.exe (PID: 7084)
- jjsploit.exe (PID: 4724)
- CATLAVAN.exe (PID: 8612)
- jjsploit.exe (PID: 904)
- CATLAVAN.exe (PID: 1240)
- jjsploit.exe (PID: 6712)
- CATLAVAN.exe (PID: 8920)
Drops encrypted VBS script (Microsoft Script Encoder)
- CATLAVAN.exe (PID: 2420)
Reads the machine GUID from the registry
- PerfDll.exe (PID: 2140)
- csc.exe (PID: 8772)
- csc.exe (PID: 5552)
- csc.exe (PID: 8856)
- csc.exe (PID: 8312)
- fontdrvhost.exe (PID: 9236)
- PerfDll.exe (PID: 8520)
- PerfDll.exe (PID: 10036)
- PerfDll.exe (PID: 208)
- PerfDll.exe (PID: 8828)
- PerfDll.exe (PID: 2384)
- PerfDll.exe (PID: 3800)
- PerfDll.exe (PID: 9904)
- PerfDll.exe (PID: 8024)
- PerfDll.exe (PID: 7540)
- PerfDll.exe (PID: 9732)
- PerfDll.exe (PID: 9340)
- PerfDll.exe (PID: 9444)
- PerfDll.exe (PID: 6700)
- PerfDll.exe (PID: 5056)
- PerfDll.exe (PID: 1180)
- PerfDll.exe (PID: 9296)
- PerfDll.exe (PID: 5008)
Creates files in the program directory
- PerfDll.exe (PID: 2140)
- csc.exe (PID: 5552)
- csc.exe (PID: 8856)
- csc.exe (PID: 8312)
Creates files or folders in the user directory
- csc.exe (PID: 8772)
The sample compiled with english language support
- PerfDll.exe (PID: 2140)
Changes the display of characters in the console
- cmd.exe (PID: 8588)
Executable content was dropped or overwritten
- msedge.exe (PID: 1512)
Disables trace logs
- fontdrvhost.exe (PID: 9236)
Checks proxy server information
- fontdrvhost.exe (PID: 9236)
- slui.exe (PID: 9464)
Reads the software policy settings
- slui.exe (PID: 8352)
- slui.exe (PID: 9464)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5728)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 7652)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 7276)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 7268)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 8992)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 8920)
- powershell.exe (PID: 6268)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4040)
- powershell.exe (PID: 9080)
- powershell.exe (PID: 8432)
- powershell.exe (PID: 1348)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 8920)
- powershell.exe (PID: 1348)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 4040)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 7268)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 7276)
- powershell.exe (PID: 8992)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 7652)
- powershell.exe (PID: 6268)
- powershell.exe (PID: 8432)
- powershell.exe (PID: 5728)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 9080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
408
Monitored processes
268
Malicious processes
30
Suspicious processes
24
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\ChainReviewDriverMonitorsvc/PerfDll.exe" | C:\ChainReviewDriverMonitorsvc\PerfDll.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4208 --field-trial-handle=2376,i,13597498969345512729,18234157484882691743,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: LOW Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | schtasks.exe /create /tn "fontdrvhostf" /sc MINUTE /mo 6 /tr "'C:\Program Files (x86)\MSBuild\Microsoft\fontdrvhost.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\WINDOWS\System32\WScript.exe" "C:\ChainReviewDriverMonitorsvc\h6yNKzpnJREtJbz2rjg0KI3Jx7Z7UeDszp29mOrZk1zLA2iJ9RrOSN.vbe" | C:\Windows\SysWOW64\wscript.exe | — | CATLAVAN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 776 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES9C3D.tmp" "c:\Program Files\CCleaner\CSC1880D7A9B0244FF80DB107885BA5259.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 904 | "C:\Users\admin\Desktop\jjsploit.exe" | C:\Users\admin\Desktop\jjsploit.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\ChainReviewDriverMonitorsvc/PerfDll.exe" | C:\ChainReviewDriverMonitorsvc\PerfDll.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Version: 1.2.7.1277 Modules
| |||||||||||||||
Total events
151 427
Read events
151 322
Write events
105
Delete events
0
Modification events
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B8F9BF2F9D8F2F00 | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197224 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DDD69B2C-FEE9-41AC-A37D-34A0652CCD9C} | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197224 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AE809AA7-0737-4E41-9C10-DE23C16C2534} | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197224 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {68C6BC31-9509-4CA8-AC77-C347C8E68914} | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197224 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {952A130A-43AE-47D4-85EA-2BD5D902C741} | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1512) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2BE0AE2F9D8F2F00 | |||
Executable files
31
Suspicious files
173
Text files
118
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ca18.TMP | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ca28.TMP | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ca37.TMP | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ca37.TMP | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ca57.TMP | — | |
MD5:— | SHA256:— | |||
| 1512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
152
TCP/UDP connections
88
DNS requests
79
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | — | 471 b | whitelisted |
7192 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
1324 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 407 b | whitelisted |
1324 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
9236 | fontdrvhost.exe | POST | 200 | 77.222.40.47:80 | http://sasatysen2.temp.swtest.ru/packetasynctrafficprivate.php | RU | binary | 1.34 Kb | malicious |
9236 | fontdrvhost.exe | POST | 200 | 77.222.40.47:80 | http://sasatysen2.temp.swtest.ru/packetasynctrafficprivate.php | RU | binary | 152 b | malicious |
9236 | fontdrvhost.exe | POST | 200 | 77.222.40.47:80 | http://sasatysen2.temp.swtest.ru/packetasynctrafficprivate.php | RU | binary | 152 b | malicious |
9236 | fontdrvhost.exe | POST | 200 | 77.222.40.47:80 | http://sasatysen2.temp.swtest.ru/packetasynctrafficprivate.php | RU | binary | 152 b | malicious |
9236 | fontdrvhost.exe | POST | 200 | 77.222.40.47:80 | http://sasatysen2.temp.swtest.ru/packetasynctrafficprivate.php | RU | text | 4 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.183:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1512 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7424 | msedge.exe | 172.217.16.194:443 | pagead2.googlesyndication.com | — | — | whitelisted |
7424 | msedge.exe | 142.250.184.194:443 | googleads.g.doubleclick.net | — | — | whitelisted |
7424 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
workupload.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET TA_ABUSED_SERVICES Commonly Abused Domain Service Domain in DNS Lookup (temp .swtest .ru) |
9236 | fontdrvhost.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
9236 | fontdrvhost.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |